by Contributed | Mar 5, 2021 | Technology
This article is contributed. See the original author and article here.
Azure Information Protection (AIP) unified labeling in Microsoft 365 provides organizations an integrated and consistent approach to creating, configuring, and applying labels and policies to protect information worker data across all locations. Workloads that can leverage unified labeling such as AIP unified labeling client and scanner, Office 365 apps, Office for web, SharePoint, OneDrive, MCAS and many more can apply these policies in a consistent manner. The AIP classic client and label management in the AIP Portal will be deprecated for sovereign clouds on September 30, 2021, therefore it is highly encouraged that administrators move their environment to unified labeling.
AIP unified labeling is generally available to Government Community Cloud High (GCC-H) environments and this release brings data discovery, classification, and protection capabilities to government Microsoft 365 instances.
Activating unified labeling for GCC-H is quite different from commercial and regular GCC environments. Commercial and regular GCC environments require administrators to navigate to the AIP blade in the Azure Portal to activate unified labeling. “Activating unified labeling” is not relevant to GCC-H tenants. All GCC-H tenants are already enabled for unified labeling; therefore, this step is not required.
Once unified labeling is enabled, commercial and GCC clouds can migrate their AIP classic client labels directly to the Security and Compliance Center, whereas this is not applicable to GCC-H tenants. GCC-H tenants require a manual migration of their AIP labels and protection templates to the Security and Compliance Center.
The benefits of migrating your labels from one portal to the next provides continuity and consistency of labels from your AIP classic environment to your Microsoft Information Protection ecosystem. Ideally, your end users will be using the same label name, label template and (optionally) protection template.
This blog gives an end-to-end use case example on how a GCC-H admin can migrate their parent label and sublabel with its corresponding protection template from the AIP Portal to the Security and Compliance Center. Additional information about label migration can be found in our official documentation.
Note: For new GCC-H tenants, label migration is not applicable. Please create new labels directly in the Security and Compliance Center.
Label Migration at a High Level
At a high level, below are the following steps to migrate AIP labels from the AIP Portal to the Security and Compliance Center:
1. Retrieve label(s) properties from the AIP Portal
2. Migrate label(s) from the AIP Classic Portal to the Security Compliance Center
3. Verify labels has been migrated to the Security and Compliance Center
Retrieve Label Properties from the AIP Portal
In this exercise, we will be migrating the parent label “Highly Confidential” with its corresponding sub label “All Employees”. First, we will retrieve the label properties and settings from the AIP Portal.
Note: When doing this exercise, administrators can retrieve all labels policies at one time.
Instructions:
- Navigate to the AIP Management Page within the Azure Portal
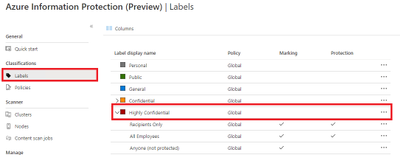
- Under Classifications, select “Labels”
- Select the parent label that you want to migrate. In this example we are migrating the label “Highly Confidential”
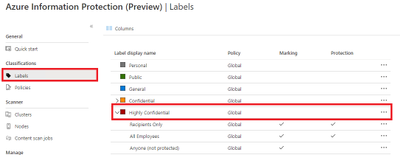
Figure 1: Selecting parent label to migrate
- Document parent label properties and settings using a spreadsheet, notepad, etc. This information will be used later in PowerShell

Figure 2: Parent label properties and settings
Parent Label Property
|
Value
|
Name (internal name; must be unique)
|
Highly Confidential
|
Tooltip
|
Very sensitive business data that would cause damage to the business if it was shared with unauthorized people. Examples include employee and customer information, passwords, source code, and pre-announced financial reports.
|
Display Name (displayed to end users)
|
Highly Confidential
|
Identity
|
06960349-c5b2-465e-8d31-1652e5969da4
|
Parent ID
|
|
EncryptionEnabled
|
|
EncryptionProtectionType
|
|
EncryptionTemplateId
|
|
EncryptionAipTemplateScopes
|
|
Table 1: Parent label settings and properties
- Under Classifications, select “Labels” again
- Select the sub label that you want to migrate. In this example we are migrating sub label “All Employees”
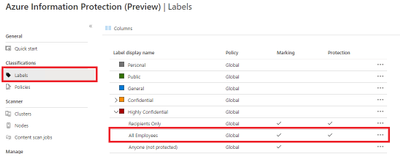
Figure 3: Selecting sub label to migrate
- Document sub label properties and settings using a spreadsheet, notepad, etc. This information will be used later for PowerShell

Figure 4: Sub label properties and settings
- (Optional) If your sub label has encryption, you will need to get the protection ID. Select Protection in your sub label properties.
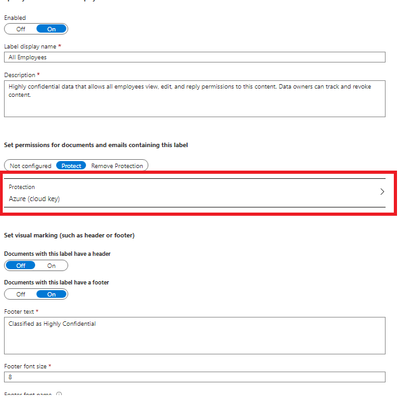
Figure 5: Sub label protection selection
- (Optional) Document sub label protection template ID using a spreadsheet, notepad, etc. This information will be used later for PowerShell.
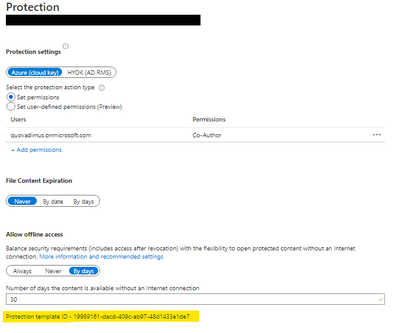
Figure 5: Sub label protection template ID
Sub Label Property
|
Value
|
Name (internal name; must be unique)
|
All Employees
|
Tooltip
|
Highly confidential data that allows all employees view, edit, and reply permissions to this content. Data owners can track and revoke content.
|
Display Name (displayed to end users)
|
All Employees
|
Identity
|
d90363e7-f9a6-43b6-b83f-ac66df2c3c01
|
Parent ID
|
06960349-c5b2-465e-8d31-1652e5969da4
|
EncryptionEnabled
|
True
|
EncryptionProtectionType
|
Template
|
EncryptionTemplateId
|
19989161-dacd-409c-ab97-48d1433e1de7
|
EncryptionAipTemplateScopes
|
allcompany@contoso.onmicrosoft.com
|
Table 2: Parent label settings and properties
Migrate AIP Labels to the Security and Compliance Center
In this section, we will be connecting to the Security and Compliance Center PowerShell module to migrate our AIP labels to the new management portal.
- Open PowerShell in administrative mode
- Import Security and Compliance PowerShell Module
Import-Module ExchangeOnlineManagement
- Connect to Security and Compliance Center for GCC-H
Connect-IPPSSession -UserPrincipalName -ConnectionUri https://ps.compliance.protection.office365.us/powershell-liveid/
Example:
Connect-IPPSSession -admin@contoso.onmicrosoft.com -ConnectionUri https://ps.compliance.protection.office365.us/powershell-liveid/
- Migrate parent Label from Azure Portal to Security and Compliance Center using ‘New-Label’ cmdlt in PowerShell
New-Label -Name 'aipscopetest' -Tooltip 'aipscopetest' -Comment 'admin notes' -DisplayName 'aipscopetest' -Identity 'b342447b-eab9-ea11-8360-001a7dda7113'
Example: Migrate parent label “Highly Confidential” from Azure Portal to Compliance Center using the parent label properties.
Parent Label Property
|
Value
|
Name (internal name; must be unique)
|
Highly Confidential
|
Tooltip
|
Very sensitive business data that would cause damage to the business if it was shared with unauthorized people. Examples include employee and customer information, passwords, source code, and pre-announced financial reports.
|
Comment
|
Highly Confidential Parent Label
|
Display Name (displayed to end users)
|
Highly Confidential
|
Identity
|
06960349-c5b2-465e-8d31-1652e5969da4
|
Parent ID
|
|
EncryptionEnabled
|
|
EncryptionProtectionType
|
|
EncryptionTemplateId
|
|
EncryptionAipTemplateScopes
|
|
New-Label -Name 'Highly Confidential' -Tooltip 'Very sensitive business data that would cause damage to the business if it was shared with unauthorized people. Examples include employee and customer information, passwords, source code, and pre-announced financial reports.' -Comment 'High Confidential Parent Label' -DisplayName 'Highly Confidential' -Identity ‘06960349-c5b2-465e-8d31-1652e5969da4'
- Migrate sub label from Azure Portal to Security and Compliance Center using ‘New-Label’ cmdlt in PowerShell
New-Label -Name 'aipscopetest' -Tooltip 'aipscopetest' -Comment 'admin notes' -DisplayName 'aipscopetest' -Identity 'b342447b-eab9-ea11-8360-001a7dda7113' -EncryptionEnabled $true -EncryptionProtectionType 'template' -EncryptionTemplateId 'a32027d7-ea77-4ba8-b2a9-7101a4e44d89' -EncryptionAipTemplateScopes "['allcompany@labelaction.onmicrosoft.com','admin@labelaction.onmicrosoft.com']"
Example: Migrate sub label “All Employees” from Azure Portal to Compliance Center using the sub label properties.
Property
|
Value
|
Name (internal name; must be unique)
|
All Employees
|
Tooltip
|
Highly confidential data that allows all employees view, edit, and reply permissions to this content. Data owners can track and revoke content.
|
Comment
|
Highly Confidential All Employees sub label
|
Display Name (displayed to end users)
|
All Employees
|
Identity
|
d90363e7-f9a6-43b6-b83f-ac66df2c3c01
|
ParentID
|
06960349-c5b2-465e-8d31-1652e5969da4
|
EncryptionEnabled
|
True
|
EncryptionProtectionType
|
Template
|
EncryptionTemplateId
|
19989161-dacd-409c-ab97-48d1433e1de7
|
EncryptionAipTemplateScopes
|
contoso@contoso.onmicrosoft.com
|
New-Label -Name 'Highly Confidential All Employees' -Tooltip ' Highly confidential data that allows all employees view, edit, and reply permissions to this content. Data owners can track and revoke content.' -Comment 'Highly Confidential All Employees sub label' -DisplayName 'All Employees' -Identity 'b342447b-eab9-ea11-8360-001a7dda7113'-ParentId ‘06960349-c5b2-465e-8d31-1652e5969da4’ -EncryptionEnabled $true -EncryptionProtectionType 'template' -EncryptionTemplateId ‘19989161-dacd-409c-ab97-48d1433e1de7' -EncryptionAipTemplateScopes "['allcompany@contoso.onmicrosoft.com']"
Verify labels has been migrated to the Security and Compliance Center
Finally, we will verify that our labels have been migrated from the AIP Portal by navigating to the new label management portal, the Security and Compliance Center.
- Sign in to the Security and Compliance Center for GCC-H
- Go to your Information Protection tab
- Verify your new labels has been created
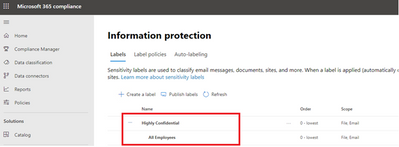
Figure 6: Security and Compliance Center label management
Note: Policies are not migrated from the AIP Portal to the Security and Compliance Center. Administrators will have to create new label policies in the Security and Compliance Center.
Sunsetting Label Management in the Azure Portal and AIP client (classic)
We have a plan to sunset label management in Azure Portal and AIP client (classic) for Government Cloud Customers. Meanwhile, Government Cloud Customers who own licenses for AIP will receive continued support for the classic client for 12 months after the general availability of unified labeling for Government Cloud. Government Cloud Customers who may need features that are not yet in the latest release of the unified labeling client can ask for additional extended support for the classic client here before September 30, 2021.
Azure Information Protection’s classic client and Label Management in the Azure Portal will be deprecated on September 30, 2021 for Government Community Cloud customers. For information on admin experience post deprecation date, check out this blog.
Note: AIP UL scanner management will still be available on AIP portal and will not be deprecated.

by Contributed | Mar 5, 2021 | Technology
This article is contributed. See the original author and article here.

On February 26 and 27, our Student Ambassadors were invited to join the community for the first virtual Student Ambassador Summit—two days of tech demos, panel discussions, and networking opportunities—all aimed at helping them build their skills and amplify their impact in the program.
Microsoft’s Scott Hanselman (@shanselman), Partner Program Manager, helped kick off the Summit as the first keynote speaker discussing mentorship, sponsorship, and storytelling, while Dona Sarkar (@donasarkar), Principal Cloud Advocate at Microsoft, encouraged everyone to expand their comfort zone. There were an additional 11 hours of live content, covering taking community building to the next level, developing your own workshop, kickstarting your career, building on existing tech skills, and more! All our speakers were incredibly informative and engaging. We also had over 9 hours of purely fun activities including chair yoga, trivia, and a round of Among Us. A special shoutout goes to our Gold Student Ambassadors who created sessions for the community, including Microsoft trivia quizzes, panels about their journeys from the Gold milestone to Microsoft Most Valuable Professionals, speed networking, and a Summit after party!
While the Summit was a special event for our Student Ambassadors, we think all students can benefit from valuable information in our How it started vs. how it’s going: from student to career panel session. This 6-person panel features young Microsoft employees in a range of roles who offer great tips to students curious about managing the transition to a full-fledged career. We hope you find it useful.
Our Student Ambassadors are passionate about learning new skills, solving real-world problems, and building their communities. If this describes you, and you’re not yet a Student Ambassador, we’d love to have you join us! Learn more at StudentAmbassadors.microsoft.com.

by Scott Muniz | Mar 5, 2021 | Security
This article was originally posted by the FTC. See the original article here.
Si usaste MoneyGram para enviarle dinero a un estafador entre el 1 de enero de 2013 y el 31 de diciembre de 2017, es posible que recibas pronto por correo un formulario de reclamación previamente completado. Los formularios de reclamación, de parte del administrador de reclamaciones Gilardi & Co. LLC, son el primer paso para la distribución del dinero del acuerdo resolutorio alcanzado con la FTC en 2018 por $125 millones de dólares. En ese caso, la FTC y el Departamento de Justicia de EE. UU. (DOJ) acusaron a MoneyGram de incumplir con los acuerdos para tomar medidas enérgicas para terminar con el fraude contra consumidores que involucra transferencias de dinero.
Para ser elegible para recibir un reembolso, debes remitir el formulario de reclamación dentro de los 90 días contados a partir de la fecha que figura en
el formulario.
En estos formularios de reclamación pre-completados figuran las pérdidas elegibles expresadas en dólares que se basan en los reportes de fraude presentados por la gente ante MoneyGram y las autoridades competentes. Si recibes un formulario y estás de acuerdo con el monto en dólares que figura como pérdida:
o Firma y fecha el formulario.
o Completa la información que pide el formulario.
o Devuélvelo por correo dentro del sobre que llegó junto con la carta.
Si recibes un formulario pero no estás de acuerdo con el monto en dólares indicado:
o Firma y fecha el formulario.
o Completa la información que pide el formulario.
o Envíalo por correo junto con copias de los documentos que respaldan el monto que reclamas. Puedes enviar copias de los recibos de MoneyGram, de los formularios de envío (“send” forms), o de los reportes de historial de transacciones con un número de control de transferencia de dinero (MTCN) de ocho dígitos. Puedes solicitar un reporte de historial de transacción en el sitio web de MoneyGram.
En el formulario de reclamación debes ingresar tu número de Seguro Social (SSN). Eso se debe a que el Treasury Offset Program, un programa federal de compensaciones, tiene que determinar si le debes dinero al gobierno de EE. UU. antes de que puedas obtener un pago. Y para hacerlo necesita tu número de Seguro Social.
Tú no tienes que pagar para presentar tu reclamación. Tú no necesitas un abogado para presentar una reclamación. No le pagues a nadie que se comunique contigo y te diga que te ayudará a presentar tu reclamación o a recuperar tu dinero.
A partir del 1 de junio de 2021, las personas que no hayan recibido un formulario pre-completado pueden empezar a presentar sus reclamaciones en línea en moneygramremission.com. Cuando presentas un formulario en línea, tienes que dar un número MTCN de MoneyGram. De lo contrario, podrás imprimir el formulario de reclamación y enviarlo por correo junto con copias de los recibos de MoneyGram, los formularios de envío (“send” forms) y los reportes de historial de transacciones. Si prevés presentar tu formulario de reclamación en junio, ya puedes comenzar a juntar tus recibos y demás documentación y hacer las copias necesarias. Una vez que se abra ese proceso, el plazo para presentar las reclamaciones es el 31 de agosto de 2021.
Para más información sobre la elegibilidad, el proceso de reclamación y otros temas relacionados con el caso, visita ftc.gov/moneygram y moneygramremission.com.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
by Contributed | Mar 5, 2021 | Technology
This article is contributed. See the original author and article here.
With the 2102 release of Microsoft Endpoint Manager, you can now configure the ability to send threat signals from Microsoft Defender for Endpoint to be used in your App Protection Policies (APP, also known as MAM) on Android and iOS/iPadOS.
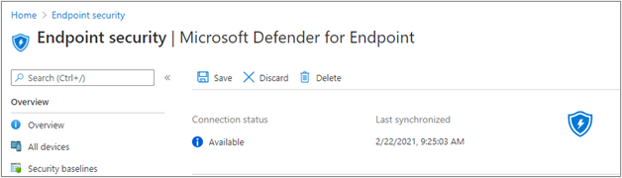
Setting up Microsoft Defender for Endpoint for unenrolled devices
- Set up the connection from your Microsoft Endpoint Manager tenant to Microsoft Defender for Endpoint. This can be done either via Tenant Administration > Connectors and tokens > Microsoft Defender for Endpoint (under Cross platform) or Endpoint Security > Microsoft Defender for Endpoint (under Setup). Once your Connection status is set to Available, proceed. If you have been using Microsoft Defender for Endpoint for device compliance assessment up until now, your connector may already be set up. At present, Microsoft Endpoint Manager supports one Mobile Threat Defense or Microsoft Defender for Endpoint connector per platform.
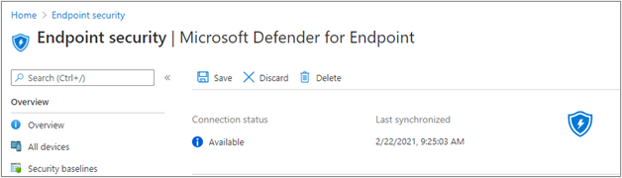 Microsoft Defender for Endpoint connector status in the MEM admin center
Microsoft Defender for Endpoint connector status in the MEM admin center
- To send threat signals from Microsoft Defender for Endpoint on targeted devices to APP, turn on the toggles under App Protection Policy Settings for the platforms you wish to configure. These capabilities are available for Android and iOS/iPadOS. Select Save. You should see Connection status is now set to Enabled.
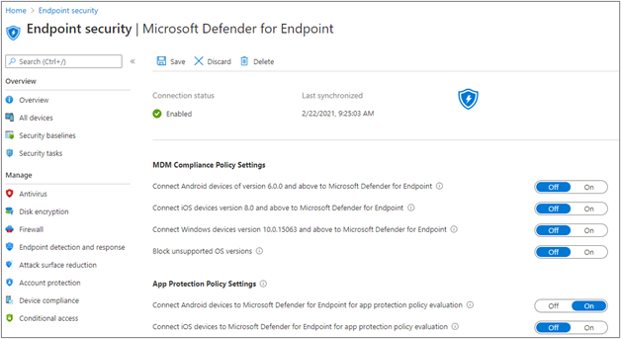 Microsoft Defender for Endpoint connector status settings in the MEM admin center
Microsoft Defender for Endpoint connector status settings in the MEM admin center
Create your App Protection Policy
- After your Microsoft Defender for Endpoint connector setup is complete, navigate to Apps > App protection policies (under Policy) to create a new policy or update an existing one.
- Select which platform, Apps, Data protection, Access requirements settings that your organization requires for your policy.
- Under Conditional launch > Device conditions, you will find the setting Max allowed device threat level. This will need to be configured to either Low, Medium, High, or Secured. The actions available to you will be Block access or Wipe data. You may see an informational dialog to make sure you have your connector set up prior to this setting take effect. If your connector is already set up, you may ignore this dialog.
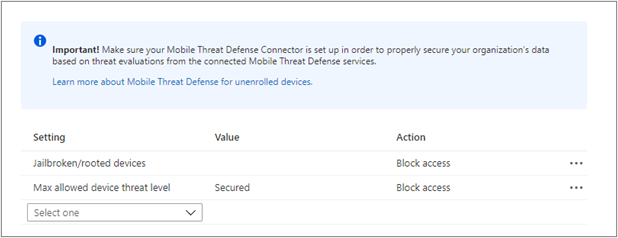 Intune APP – Mobile Threat Connector policy settings
Intune APP – Mobile Threat Connector policy settings
- Finish with Assignments and save your policy.
How to deploy the Defender app with this functionality
At present, the Microsoft Defender for Endpoint build on iOS and Android that enables the App Protection Policy scenario are found in TestFlight (for iOS/iPadOS) and beta Google Play store (for Android) as it is in preview.
iOS:
Android:
- Device Admin & Customers who are not enrolled to Intune MEM: Admins will need to create a Google Group (format: <Customername>_DefenderMAM) for users who are participating in the preview.
- Enterprise Admin Customers: Admin will need to send the Organization ID of the Google Play account, which is linked to Managed Google Play store in Intune. Followed by syncing Google Play Account in Intune.
Admin can then send the above Google groups id / Google Play account Organization ID to mdatpmobile@microsoft.com.
Threat detection capabilities
Types of threat detection available through MDE and how to turn it on:
End user experience
Once this policy is targeted to a specific user, the end user will be required to:
- Register their device with Azure Active Directory (Azure AD). This is not a device enrollment into Intune. This simply allows this device to have an Azure AD device ID which is required for this feature. If your organization has already configured Conditional Access for Android/iOS, your end users may already have Azure AD registered mobile devices.
- Install the Microsoft Defender for Endpoint app on their device.
- Activate the Microsoft Defender for Endpoint app in order to pass the condition required to access the app with their corporate account. This will involve signing into the app with corporate credentials, and accepting any required permissions.
Once activation is complete, Microsoft Defender for Endpoint will do a scan of the device to come up with a risk score. If the risk score meets the requirements set by the admin of Low, Medium, High, Secured, then the end user passes the conditions and gets access to their protected apps.
The check for if this device passes the configured conditions happens during App Protection Policy service check-in, or when the end user hits ‘Recheck’ after remediating their device.
More info and feedback
Create and deploy app protection policies
Let us know if you have any additional questions by replying to this post or reaching out to @IntuneSuppTeam on Twitter.
by Contributed | Mar 5, 2021 | Technology
This article is contributed. See the original author and article here.
In this series, Microsoft identity team members share their reasons for loving passwordless authentication (and why you should too!). Pamela Dingle closes the series with a post about the tighter security of passwordless authentication.
Here we are at the last of our Ten Reasons to Love Passwordless blog series! This last reason is more than closing the Ten Reasons blog series, it is about choosing to close a chapter on the past – because passwordless authentication means we can finally say goodbye to the password.
Password authentication has been around for over 60 years and has always been challenging. A password is supposed to act as a key to help the right person access an account while also operating as a security barrier to protect the account from attackers. However, 80% of hacking-related breaches involve either stolen or weak passwords that were easily guessed by the cybercriminals. Phishing, password spray, and credential stuffing attacks are all attacks that don’t involve an attacker using fancy math to get into your account – instead these attacks rely on you as a statistically predictable human. Attackers know that we humans will type our passwords without due care into a web page that looks mostly reputable. That we don’t set a different password at every website we use. That 1 out of 100 of us have easily guessed passwords like Spring2021! protecting a critical account at this very moment. That they can use 30 year old password attack tools and still succeed, because we use 30 year old protocols that are vulnerable to them. Attackers don’t have to be smart to make money from password theft, just opportunistic. Wouldn’t it be great if we could take that opportunity away?
Traditional multifactor authentication (aka MFA) presents a more secure way for users to access their accounts and resources – password plus another factor. Microsoft supports and encourages multiple ways to use MFA! Adding a second factor to your authentication reduces the probability of account compromise by 99.9%, because it ruins the instant effectiveness of password-based attacks. MFA makes user authentication much safer, but it does impact the user experience. MFA also leaves the oh-so-vulnerable password as part of the equation.
Passwordless authentication is a form of multifactor authentication that replaces the password with a secure alternative. One of the underlying principles of passwordless authentication is to eradicate the use of passwords and thereby eliminate their value for attackers. As I hope you have seen in many of our previous blog entries, passwordless authentication methods have protections against the types of attacks that represent easy money for criminals. Replacing passwords with passwordless authentication may not completely prevent all attacks, but we can make successful attacks much more expensive to perpetrate.
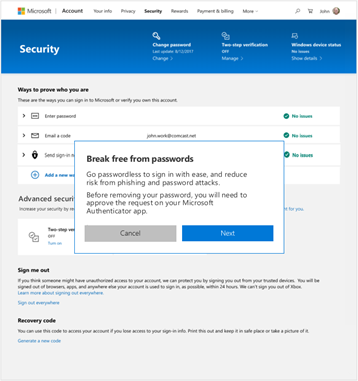
Passwordless methods don’t require users to enter their passwords anymore, but what if the account has a password attached to it, from initial setup? That password is less dangerous because it is not in use regularly, which is good, but there is a difference as a user between choosing not to use your password and knowing that nobody else can either. The most secure option would be for the password associated to an account to disappear forever! After all, it is tough to compromise an authentication method that doesn’t exist. You might ask, is there a way to make this happen, other than setting a long random password and forgetting it? There will be soon.
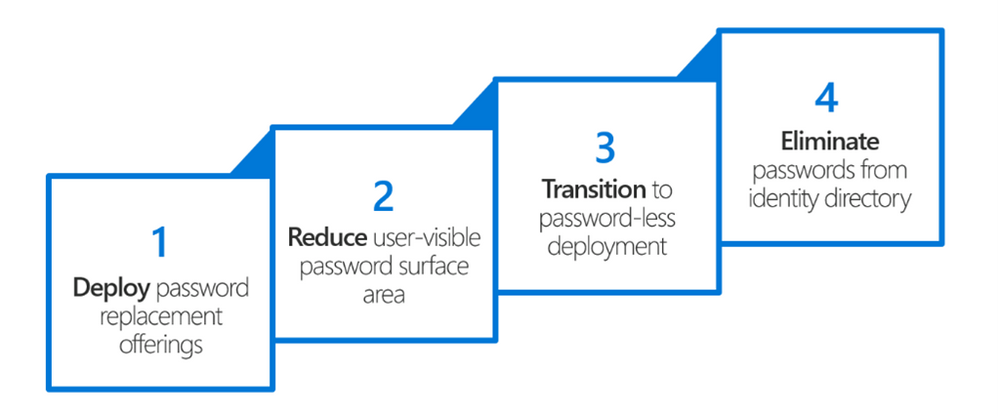
Microsoft has defined a four-step approach to end the era of passwords:
The strategy you see here seems simple, doesn’t it? But let’s just say it has been a journey. It has required singular vision, as well as collaboration both internally across many of our products and externally in our standards-based efforts. We stand today at step #3, and we are on the verge of getting to step #4. Here is a quick taste of where these steps have taken us:
Deploy password replacement offerings:
- Introduced by Microsoft in Windows 10, Windows Hello uses biometric sensors or a PIN to verify a user’s identity when signing into work or personal accounts from a PC.
- The Microsoft Authenticator app generates encrypted messages that allows users to verify their identity with a built-in biometric or a PIN when signing into their work or personal accounts from a mobile phone.
- Via the FIDO2 family of specifications, any website can request a phishing resistant credential from supported Microsoft, Apple, and Google platforms or from certified USB or NFC security keys.
Reduce user-visible password surface area:
- Login experiences across Microsoft transition to an ‘identifier-first’ flow, meaning users are no longer asked for a password at the same time they are asked for their username.
Transition to passwordless deployment:
- Legacy authentication support is replaced with modern authentication support, and hard-coded assumptions about the omnipresence of passwords are found and removed.
- Users sign into their accounts with one of the password replacement technologies and use single sign-on to access all their resources.
Eliminate passwords from identity directory (future):
- Administrators can choose whether passwords are required, allowed or simply don’t exist for a set of users, and users can choose either to not set a password when an account is created, or to remove their existing password from an account.
When Microsoft gets to step 4 in our vision, those of you who are security minded will have the power not only to use more secure authentication methods, but to eliminate less secure authentication methods. In Spring 2021, we will launch the functionality to allow password removal on Microsoft consumer accounts. Choosing to go passwordless means that instead of signing in with the Microsoft account password, users will verify sign in with the Microsoft Authenticator app. Additional forms of passwordless authentication such as Windows Hello and FIDO2 are also available to round out the options.
I can’t tell you how excited I am to see us get to these later stages of our Microsoft passwordless vision, but success in these four steps really just gets us to the starting line when it comes to living without passwords in our daily work, home, and school lives. As passwordless authentication in Azure AD is now generally available, we hope to see meaningful change in adoption rates for multifactor and passwordless authentication. We feel confident now that there are usable, meaningful alternatives to passwords available, and most importantly, the methods you see today are only the beginning. We now have the platform support, the vendor ecosystem, and the standards frameworks needed to foster new innovation and to improve our security posture over time.
I encourage you all to try passwordless authentication on for size, and I hope we have given you 10 really great reasons as to why this journey might be worthwhile. On behalf of all my co-authors, we hope this series has helped you understand passwordless authentication and has provided some useful tips for deploying in your organization. The more we can embrace passwordless as the norm the more we can protect ourselves and our organizations. And – to all of the current and past Microsoft employees who have waited for years to see our vision finally result in real day-to-day usage – we made it!
Check out the other posts in this series:
Learn more about Microsoft identity:
by Contributed | Mar 5, 2021 | Technology
This article is contributed. See the original author and article here.
Blogger: Peter Rising, MVP Office Apps and Services, Principal Consultant at Softcat PLC
Sessions: FS191, FS191-R1
Speakers: John Gruszczyk | Microsoft, Rushmi Malaviarachchi | Microsoft, Mansoor Malik | Microsoft
As the author of two books that focus on Microsoft Teams, and Microsoft Security & Compliance administration, it’s safe to say that I was looking forward to this session, and it did not disappoint.
We get underway with our host John Gruszczyk, Product Manager for Microsoft Teams, who speaks passionately about what he has to share with us on the latest security and compliance innovations in Microsoft Teams. We will learn how Microsoft Teams will help us to collaborate with confidence, while meeting regulatory and business requirements.
John begins by explaining that we have seen online communication with Microsoft Teams evolve beyond just meetings and chat. Teams has kept us connected with friends and colleagues and enabled us to get our work done remotely. However, this increase in remote working has brought more challenges to IT and Security teams who are facing increasing cyber security threats such as malicious documents and attachments, and mounting compliance obligations to protect organizational data.
A recent Harvard Business Review study shows that 77% of organizations agree that an effective security, compliance, and risk strategy is essential for business success, while 82% also acknowledge increased risks and complexities have made an effective strategy significantly more challenging.

This has made Microsoft keenly aware that it is crucial to remain focused on helping organizations enable both secure and compliant collaboration without interrupting the ways in which end users are able to collaborate with each other.
The unique advantage that Microsoft Teams provides is the fact that it is a centralized platform for collaboration. This enables organizations reduce shadow IT and the use of fragmented collaboration services which can lead to data sprawl which in turn can lead to data leaks.
John goes on to share with us some key areas where Teams has been investing, and how these investments will help organizations achieve the correct Security & Compliance strategy.
Rushmi Malaviarachchi, Partner Director of Program Management for Microsoft Teams is introduced and talks with John about how Microsoft Teams has evolved to become a content generating platform; when users work together in chat, video calls, channels, collaborating on documents, or even within custom or third-party apps, these activities create valuable business content that needs to be protected. Rushi went on to highlight the following plans and announcements for Security and Compliance in Microsoft Teams:

Adaptive cards now in scope
Microsoft recently announced that Adaptive card content generated in Teams Apps is now in scope for compliance capabilities. More than 70% of Teams apps today generate card content in Teams conversation. When an app posts a card to a chat, the content of that card will be visible in eDiscovery, can be preserved with Legal Hold, covered by retention policies, and any actions people take on that card will be available in the audit log.
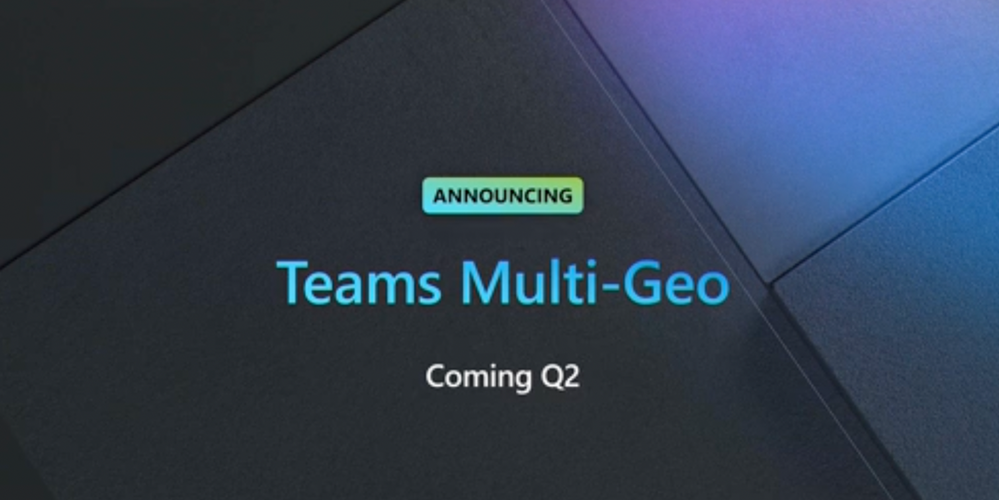
Teams Multi-Geo
Also announced in relation to the critical subject of Data residency was that Microsoft have carefully listened to customer feedback, and they are extending Microsoft 365 Multi-Geo support to include Microsoft Teams so you can specify where your Teams data at rest will sit. You will be able to set the Geo-location for both individual users and teams. The roll out of Teams Multi-Geo is planned for the 2nd quarter of this year and this is going to be welcome news for many organizations with a global footprint who have very specific data residency obligations.
Secure Score
The Microsoft Secure Score helps to prevent unwanted incidents across Microsoft 365 services including – Exchange Online, Azure Active Directory, Microsoft Defender for Endpoint, Microsoft Defender for Identity, and Cloud App Security. Microsoft Teams has recently also been brought into scope for Secure Score and more configuration best practices will be coming soon so watch this space!
Azure Sentinel
Beyond prevention, the correct systems to detect when an intrusion event is happening is of key importance. In Teams, Microsoft have been bolstering the events that are collected by the audit log, so that now the Microsoft Security Information & Event Management (SIEM) tool – Azure Sentinel, can analyze what is going on within Teams and be on the lookout for threats, and use playbooks to respond.
Customer key
Also announced was that bring your own key for Microsoft Teams will be rolling out in the second quarter of this year.
A frictionless approach
The overall theme of aiming for secure organizational collaboration was that it needs to be frictionless. The balance between security and useability is an important consideration, but these principles should not be at odds with each other.
Fritctionless cross organization collaboration will be bolstered by the introduction of shared channels which was also announced at Ignite. In conjunction with the use of technologies such as Microsoft Information Protection across the collaboration space, a label driven approach using sensitivity labels and leveraging conditional access will help to break down traditional collaboration boundaries.
Meeting safety
Next, Mansoor Malik, Principal Group Manager, Microsoft Teams discussed the hugely important subject of meeting safety in Microsoft Teams.

Meeting safety covers a wide range of criteria, which includes meeting participants, content being presented, who can present that content, what is being recorded, and who can record.
One of the big concerns that Microsoft are keenly aware of is uninvited attendees getting into meetings. Being able to control meeting intruders and disruptors, especially in the student and classroom space is crucially important, and if this subject is not correctly addressed, then mental health and wellbeing can be put at risk.
Microsoft have been working to provide brand new meeting controls, such as preventing anonymous attendees from being able to join meetings at an organization level through policy.
Restricting the ability to forward meeting invites is also a very welcome introduction.
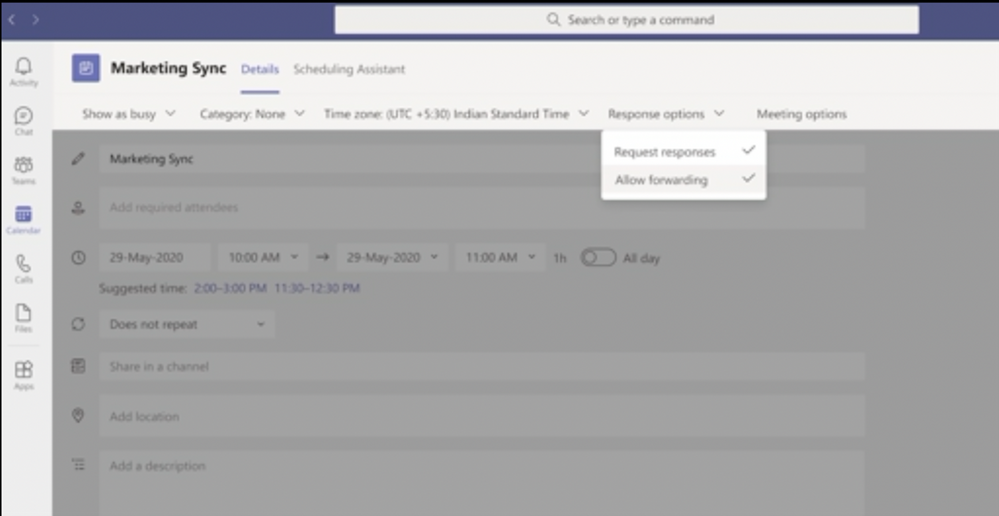
In addition, new lobby bypass setting controls will provide the ability to allow only specific invitees to bypass the lobby.
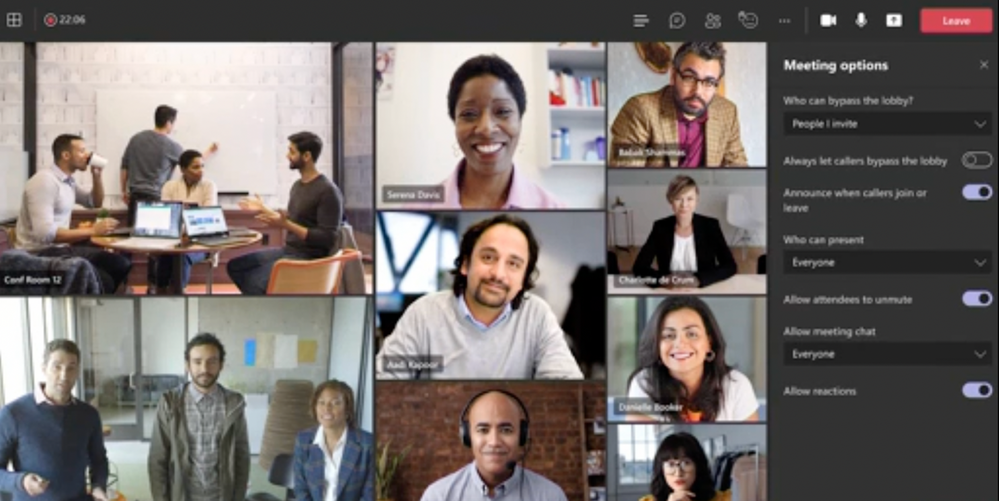
And meeting safety does not stop there. There will also be options for allowing or not allowing attendees to present, chat or unmute, and it was also announced that the ability for meeting organizers to disable video for all attendees is coming soon.
End-to-end encryption
Mansoor also talked about End-to-end encryption for Microsoft Teams. This is a new feature that is coming soon and will provide the ability in Teams to encrypt at the origin and decrypt at the destination. Initially this will only be supported in Teams 1:1 VOIP calls and only participating parties in the End-to-end encryption communication will be able to access the content. The announcement of End-to-end encryption is based on year-long feedback and Teams will be introducing the ability to use End-to-end encryption for 1:1 calls in the coming months.

Some important considerations for End-to-end encryption:
- Both the caller and callee in the 1:1 call will need to have been enabled by administrators for End-to-end encryption
- Only voice, video and screen sharing in those 1:1 calls will be end to end encrypted.
Microsoft will continue to talk to customers about widening the scope of this crucial new feature, and you can expect to see End-to-end encryption come to Microsoft Teams meetings next. Watch out for more details available soon.
Summary
This was a fast paced and engaging session that gave us a glimpse of what is to come for Security and Compliance in Microsoft Teams. I must say that I am hugely encouraged by what this session revealed. Microsoft customers have been asking the correct questions, and Microsoft are providing some very good answers in return.
I will surely be testing and reporting on these features as they become available and if you would like to discuss any of these with me then please feel free to reach out to me in the Microsoft Technical Community.
I hope you have enjoyed this Ignite as much as I have, and I wish you a frictionless experience in your Microsoft Teams journey moving forward!
Further reading
by Contributed | Mar 5, 2021 | Technology
This article is contributed. See the original author and article here.
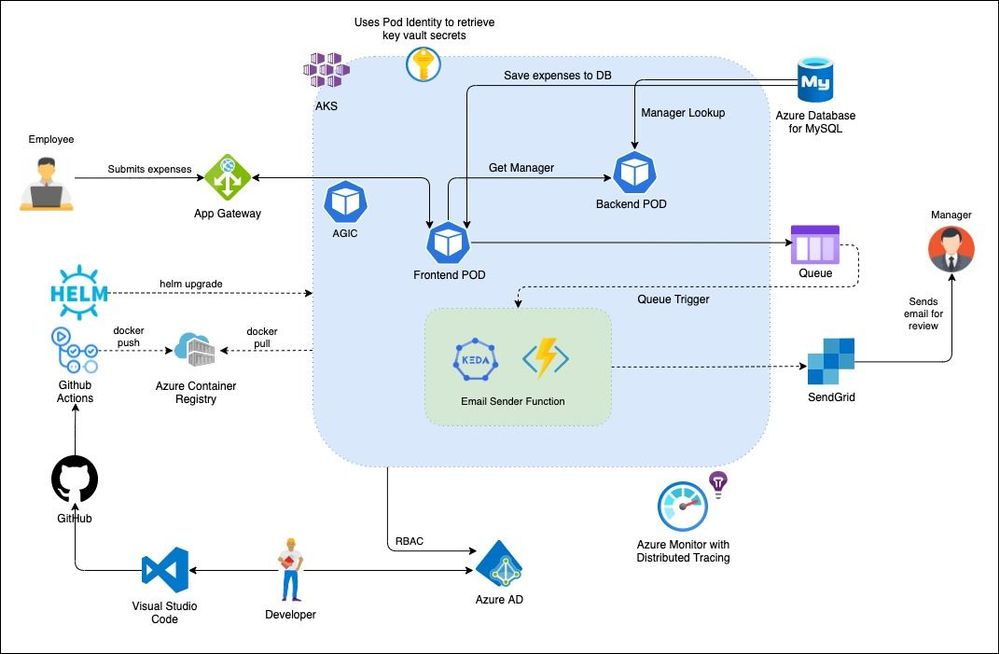
Overview
This blog demonstrates a multi-tier application deployment on to Azure Kubernetes Service along with several other Azure managed services such as Azure Database for MySQL, Azure Functions, etc.
Note: There may be few features that are used in this blog such as Azure Active Directory Pod Identity are still in preview, these features are not recommended for production deployment.
Architecture
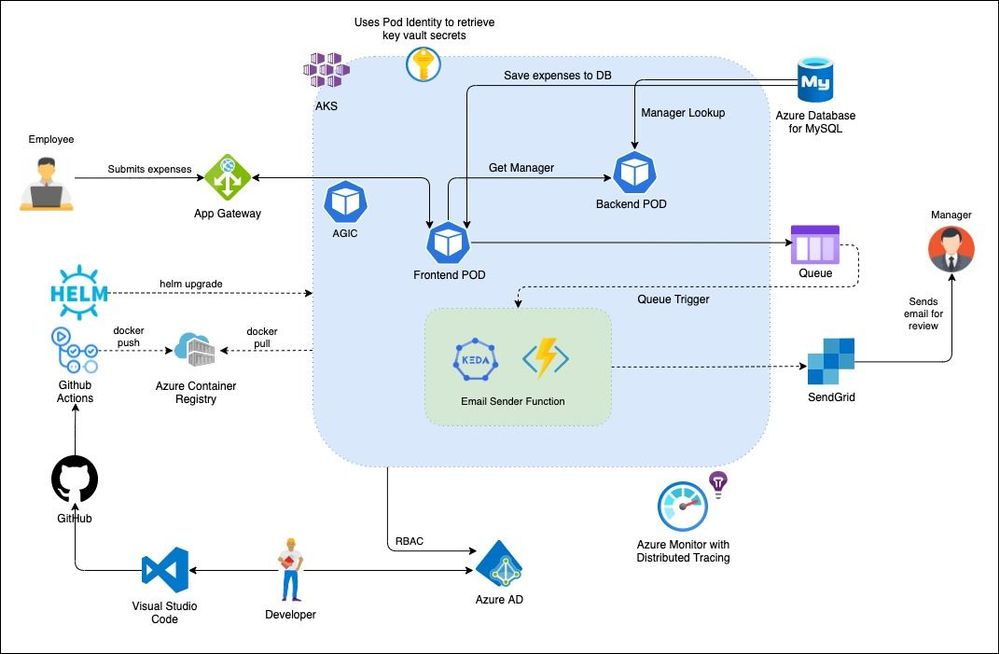
Setup
We will create and setup the infrastructure including the following services:
- Azure Container Registry for storing images
- AAD Enabled, Managed AKS Cluster with the below addons and components
- Application Gateway Ingress Controller Addon
- Monitoring Addon
- LetsEncrypt for Certificate authority
- KEDA runtime for Azure Functions on Kubernetes clusters
- Azure Database for MySQL Service
- Azure Storage Queues
- DNS Zone for custom domain
- SendGrid Account for email service
Cluster Creation
Clone repository
git clone https://github.com/ssarwa/multitiered-app-on-azure
cd multitiered-app-on-azure
# You could use script.azcli as your working file. Don’t run the script as is!
Initialize variables
# Add variables (sample values below change as required)
resourcegroupName=’CNCF-Azure-RG’
clusterName=’myaksCluster’
location=’westus’
appGtwyName=’AKSAppGtwy’
acrName=’cncfazure’
domainName=’sarwascloud.com’
dnsRG=’dns-rg’
subDomain=’expense’
mysqlSvr=’expensedbserver’
adminUser=’expenseadmin’
mysqlPwd=”
keyvaultName=’expensesvault’
# Identity name must be lower case
identityName=’exppoidentity’
# Storage name must be lower case and globally unique
storageAcc=’expensesqueue’
subscriptionId=’12bb4e89-4f7a-41e0-a38f-b22f079448b4′
tenantId=’72f988bf-86f1-41af-91ab-3d7cd011db47′
Login to Azure
az login
az account set -s $subscriptionId
Register to AKS preview features
# Follow https://docs.microsoft.com/en-us/azure/aks/use-azure-ad-pod-identity
az feature register –name EnablePodIdentityPreview –namespace Microsoft.ContainerService
az provider register -n Microsoft.ContainerService
az extension add –name aks-preview
az extension update –name aks-preview
Create Resource Group
az group create –name $resourcegroupName –location $location
Create ACR
az acr create –resource-group $resourcegroupName –name $acrName –sku Standard
Get Object ID of the AAD Group (create AAD Group and add the members, in this case: expenses-ad-azure)
This group is needed as admin group for the cluster to grant cluster admin permissions. You can use an existing Azure AD group, or create a new one. Record the object ID of your Azure AD group.
az ad group create –display-name expenses-ad-azure –mail-nickname expenses-ad-azure –description ‘Group for Managing AAD based AKS cluster’
objectId=$(az ad group list –filter “displayname eq ‘expenses-ad-azure'” –query ‘[].objectId’ -o tsv)
Create an AKS-managed Azure AD cluster with AGIC add-on and AAD Pod Identity
az aks create
-n $clusterName
-g $resourcegroupName
–network-plugin azure
–enable-managed-identity
-a ingress-appgw –appgw-name $appGtwyName
–appgw-subnet-cidr “10.2.0.0/16”
–enable-aad
–enable-pod-identity
–aad-admin-group-object-ids $objectId
–generate-ssh-keys
–attach-acr $acrName
# Enable monitoring on the cluster
az aks enable-addons -a monitoring -n $clusterName -g $resourcegroupName
Add Public IP to custom domain
# Get Node Resource Group
nodeRG=$(az aks show –resource-group $resourcegroupName –name $clusterName –query nodeResourceGroup -o tsv)
# Get Public IP created by App Gtwy in AKS created cluster
appIP=$(az network public-ip show -g $nodeRG -n $appGtwyName-appgwpip –query ipAddress -o tsv)
# Create DNS zone, if not created
az network dns zone create -g $dnsRG -n $domainName
# Once created, add Nameservers in the domain provider (eg go daddy, may take sometime to update the name servers)
az network dns record-set a add-record –resource-group $resourcegroupName –zone-name $domainName –record-set-name $subDomain –ipv4-address $appIP
Connect to the Cluster
Merge Kubeconfig
az aks get-credentials –resource-group $resourcegroupName –name $clusterName –admin
Install Cert Manager
# Install the CustomResourceDefinition resources separately
# Note: –validate=false is required per https://github.com/jetstack/cert-manager/issues/2208#issuecomment-541311021
kubectl apply -f https://raw.githubusercontent.com/jetstack/cert-manager/release-0.13/deploy/manifests/00-crds.yaml –validate=false
kubectl create namespace cert-manager
kubectl label namespace cert-manager cert-manager.io/disable-validation=true
helm repo add jetstack https://charts.jetstack.io
helm repo update
helm install cert-manager –namespace cert-manager –version v0.13.0 jetstack/cert-manager
kubectl apply -f yml/clusterissuer.yaml
# Test a sample application. The below command will deploy a Pod, Service and Ingress resource. Application Gateway will be configured with the associated rules.
sed -i “s//$domainName/g” yml/Test-App-Ingress.yaml
sed -i “s//$subDomain/g” yml/Test-App-Ingress.yaml
kubectl apply -f yml/Test-App-Ingress.yaml
# Clean up after successfully verifying AGIC
kubectl delete -f yml/Test-App-Ingress.yaml
Install KEDA runtime
helm repo add kedacore https://kedacore.github.io/charts
helm repo update
kubectl create namespace keda
helm install keda kedacore/keda –namespace keda
Install CSI Provider for Azure KeyVault
helm repo add csi-secrets-store-provider-azure https://raw.githubusercontent.com/Azure/secrets-store-csi-driver-provider-azure/master/charts
helm repo update
kubectl create namespace csi
helm install csi csi-secrets-store-provider-azure/csi-secrets-store-provider-azure –namespace csi
Assign managed identity
clientId=$(az aks show -n $clusterName -g $resourcegroupName –query identityProfile.kubeletidentity.clientId -o tsv)
scope=$(az group show -g $nodeRG –query id -o tsv)
az role assignment create –role “Managed Identity Operator” –assignee $clientId –scope $scope
Create Azure KeyVault for saving secrets and assign identity
az keyvault create –location $location –name $keyvaultName –resource-group $resourcegroupName
kvscope=$(az keyvault show -g $resourcegroupName -n $keyvaultName –query id -o tsv)
az identity create -g $resourcegroupName -n $identityName
idClientid=$(az identity show -n $identityName -g $resourcegroupName –query clientId -o tsv)
idPrincipalid=$(az identity show -n $identityName -g $resourcegroupName –query principalId -o tsv)
identityId=$(az identity show -n $identityName -g $resourcegroupName –query id -o tsv)
az role assignment create –role “Reader” –assignee $idPrincipalid –scope $kvscope
# Set permissions
az keyvault set-policy -n $keyvaultName –secret-permissions get –spn $idClientid
# Add Pod Identity
az aks pod-identity add –resource-group $resourcegroupName –cluster-name $clusterName –namespace default –name $identityName –identity-resource-id $identityId
Create MySQL managed service (basic sku) and add Kubernetes Load Balancer’s public ip in it firewall rules
aksPublicIpName=$(az network lb show -n kubernetes -g $nodeRG –query “frontendIpConfigurations[0].name” -o tsv)
aksPublicIpAddress=$(az network public-ip show -n $aksPublicIpName -g $nodeRG –query ipAddress -o tsv)
az mysql server create –resource-group $resourcegroupName –name $mysqlSvr –location $location –admin-user $adminUser –admin-password $mysqlPwd –sku-name B_Gen5_2
az mysql server firewall-rule create –name allowip –resource-group $resourcegroupName –server-name $mysqlSvr –start-ip-address $aksPublicIpAddress –end-ip-address $aksPublicIpAddress
# Replace with your Local Machine IP. You can use: https://www.whatsmyip.org/
az mysql server firewall-rule create –name devbox –resource-group $resourcegroupName –server-name $mysqlSvr –start-ip-address <Dev station ip> –end-ip-address <Dev station ip>
Login to MySQL (you may need to add you ip to firewall rules as well). # Login to MySQL Client your your local dev box: sudo apt install mysql-client-core-8.0
mysql -h $mysqlSvr.mysql.database.azure.com -u $adminUser@$mysqlSvr -p
show databases;
CREATE DATABASE conexpweb;
CREATE DATABASE conexpapi;
USE conexpapi;
CREATE TABLE CostCenters(
CostCenterId int(11) NOT NULL,
SubmitterEmail text NOT NULL,
ApproverEmail text NOT NULL,
CostCenterName text NOT NULL,
PRIMARY KEY ( CostCenterId )
);
# Insert example records
INSERT INTO CostCenters (CostCenterId, SubmitterEmail,ApproverEmail,CostCenterName) values (1, ‘ssarwa@microsoft.com’, ‘ssarwa@microsoft.com’,’123E42′);
INSERT INTO CostCenters (CostCenterId, SubmitterEmail,ApproverEmail,CostCenterName) values (2, ‘ssarwa@microsoft.com’, ‘ssarwa@microsoft.com’,’456C14′);
INSERT INTO CostCenters (CostCenterId, SubmitterEmail,ApproverEmail,CostCenterName) values (3, ‘ssarwa@microsoft.com’, ‘ssarwa@microsoft.com’,’456C14′);
# Verify Records
SELECT * FROM CostCenters;
quit
Create Storage queue
az storage account create -n $storageAcc -g $resourcegroupName -l $location –sku Standard_LRS
# Do not change queue name of contosoexpenses. KedaFunction queue trigger relies on this queue name.
az storage queue create -n contosoexpenses –account-name $storageAcc
Add corresponding secrets to the create KeyVault
- MySQL Connection strings (choose ADO.NET) – both for API and Web
- mysqlconnapi
- mysqlconnweb
- Storage Connection strings
- storageconn
- Sendgrid Key
- sendgridapi
az keyvault secret set –vault-name $KeyVault –name mysqlconnapi –value ‘<replace>Connection strings for MySQL API connection</replace>’
az keyvault secret set –vault-name $keyvaultName –name mysqlconnweb –value ‘<replace>Connection strings for MySQL Web connection</replace>’
az keyvault secret set –vault-name $keyvaultName –name storageconn –value ‘<replace>Connection strings for Storage account</replace>’
# Make sure to register for free SendGrid Account and verify identity. Visit https://sendgrid.com
az keyvault secret set –vault-name $keyvaultName –name sendgridapi –value ‘<replace>Sendgrid Key</replace>’
az keyvault secret set –vault-name $keyvaultName –name funcruntime –value ‘dotnet’
Application Deployment
registryHost=$(az acr show -n $acrName –query loginServer -o tsv)
az acr login -n $acrName
cd source/Contoso.Expenses.API
docker build -t $registryHost/conexp/api:latest .
docker push $registryHost/conexp/api:latest
cd ..
docker build -t $registryHost/conexp/web:latest -f Contoso.Expenses.Web/Dockerfile .
docker push $registryHost/conexp/web:latest
docker build -t $registryHost/conexp/emaildispatcher:latest -f Contoso.Expenses.KedaFunctions/Dockerfile .
docker push $registryHost/conexp/emaildispatcher:latest
cd ..
# Update yamls files and change identity name, keyvault name, queue name and image used refer values between <> in all files
# Create CSI Provider Class
# Use gsed for MacOS
sed -i “s/<Tenant ID>/$tenantId/g” yml/csi-sync.yaml
sed -i “s/<Cluster RG Name>/$resourcegroupName/g” yml/csi-sync.yaml
sed -i “s/<Subscription ID>/$subscriptionId/g” yml/csi-sync.yaml
sed -i “s/<Keyvault Name>/$keyvaultName/g” yml/csi-sync.yaml
kubectl apply -f yml/csi-sync.yaml
# Create API
sed -i “s/<identity name created>/$identityName/g” yml/backend.yaml
sed -i “s/<Backend image built>/$registryHost/conexp/api:latest/g” yml/backend.yaml
sed -i “s/<Keyvault Name>/$keyvaultName/g” yml/backend.yaml
kubectl apply -f yml/backend.yaml
# Create frontend
sed -i “s/<identity name created>/$identityName/g” yml/frontend.yaml
sed -i “s/<frontend image built>/$registryHost/conexp/web:latest/g” yml/frontend.yaml
sed -i “s/<Keyvault Name>/$keyvaultName/g” yml/frontend.yaml
kubectl apply -f yml/frontend.yaml
# Create ingress resource
sed -i “s/<custom domain name>/$domainName/g” yml/ingress.yaml
sed -i “s//$subDomain/g” yml/ingress.yaml
kubectl apply -f yml/ingress.yaml
# Create KEDA function
sed -i “s/<identity name created>/$identityName/g” yml/function.yaml
sed -i “s/<function image built>/$registryHost/conexp/emaildispatcher:latest/g” yml/function.yaml
kubectl apply -f yml/function.yaml
Once the ingress controller updates with new frontend deployed it may take a min for Application gateway to update.
Browse the application URL: https://subdomain.yourcustomdomain.com
Next Steps
- Implement Service Mesh (like OSM) for securing service to service communications
- Enabling managed identity to access MySQL and Storage services, thus removing Key Vault references
- Enabling Github Actions for CI/CD pipelines
by Contributed | Mar 5, 2021 | Technology
This article is contributed. See the original author and article here.
Editor’s note: This blog post was first published February 24 and updated with new information March 5.
As announced February 24, Microsoft began delivering the Windows 10 Team 2020 Update to first-generation Surface Hub 55” and 84” devices. We will continue to provide the Windows 10 Team 2020 Update to all first-generation Surface Hubs as a staged rollout. Using a staged rollout allows our engineers to investigate issues as they arise and ensure the highest quality update experience.
In response to recent customer feedback, Microsoft will throttle the March 2 rollout to investigate an issue listed in the known issues list. Additionally, Microsoft will start rolling out the Windows 10 Team 2020 Update for Surface Hub first-generation devices in the United States on March 9.
- Feb. 24: Surface Hub v1 with full telemetry enabled in Australia, New Zealand, Japan, Canada, Mexico, Belgium, Italy, Germany, the Netherlands, Switzerland, and UK.
- March 2: Surface Hub v1 with full telemetry enabled in all geographies except the U.S.
- March 9: Surface Hub v1 with full telemetry enabled in the U.S.
We will continue to provide updates as the rollout continues including devices without full telemetry enabled, as well as availability via Windows Update for Business. If you would like to start your Hub v1 feature update before it is offered via Windows Update, we encourage you to use the Surface Hub Recovery Tool. Instructions are provided below.
Note: If the Windows 10 Team 2020 Update does not appear in the list of available Windows Updates, you can temporarily turn on full telemetry (aka Windows diagnostics). After enabling full telemetry and restarting the device, it may take 24 hours or more before the update appears. To check, open the Settings app from the Start menu, login with an administrator account, and select Updates & Security > Check for updates.
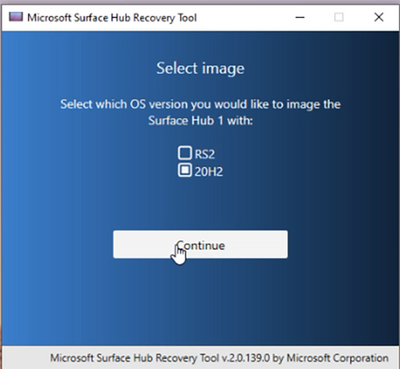
Updating via Surface Hub Recovery Tool
As an alternative to Windows Update, all first-generation Surface Hubs can be updated from Windows 10 Team, version 1703 (RS2) to the new Windows 10 Team 2020 Update with the Surface Hub Recovery Tool (SHRT) available for download (select SurfaceHub_Recovery_v2.7.139.0.msi). When you run the SHRT tool, you will be prompted to select the 2020 Update image – aka 20H2 – as shown in the following screenshot:
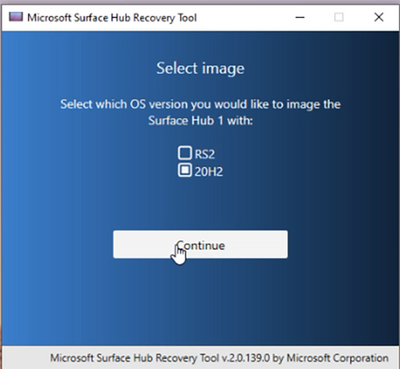
For more information about using the SHRT tool including step-by-step instructions, refer to Using the Surface Hub Recovery Tool.

by Contributed | Mar 5, 2021 | Technology
This article is contributed. See the original author and article here.
Blogger: Chris Hoard, Partner Education Lead, Vuzion (UK), MCT Regional Lead, OAS MVP
Sessions: KEY06, KEY06-R1
2020 was a year that changed everything. The way we live. The way we work. As the Covid-19 pandemic spread across borders and over continents organisations in every country of every type needed to adapt in order to survive or to function. We, as IT professionals, came into a situation where it was imperative we act as the first responders. On the one hand we needed to help our customers maintain business operations and keep their workforces secure in the face of growing cyber-attacks. On the other, we needed to support many of our colleagues in this new world of remote working helping to safeguard and ensure their mental and emotional wellbeing. As Jared rightly points out in the opening scene of Hybrid, we also needed to do both of these things whilst navigating our own personal challenges at home. When does work start? When does it stop? Where can our business conversations or activities take place without intruding on the privacy of our loved ones whose home it is as much as ours? Given these new realities, how many of us forget that throughout the pandemic many workers have still needed to go onsite each and every single day as it’s an essential requirement for their job. Think of healthcare workers and construction workers. Think of police, and firefighters, those who work in waste disposal, electricians, plumbers, vets. Think of retail and hospitality. These first-line workers have needed to be able to easily communicate with their remote colleagues whilst at the same time still be safe on the job.

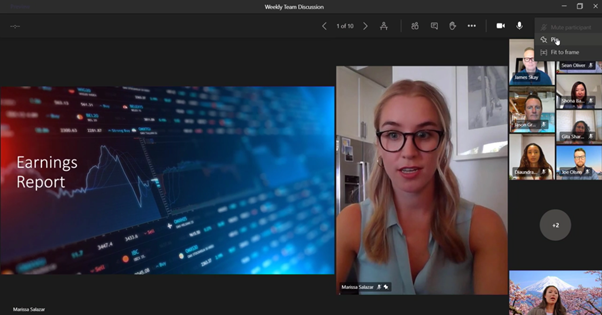
As vaccination programs roll out across the world, we now begin to think and to re-imagine how work will be as we enter a period where the pandemic becomes more manageable. What is already clear is that things are not going to return to the way they were pre-pandemic. Some of us will remain at home. Some of us will go back to working or continue to work onsite. Others may choose to work at home or onsite in a hybrid setup depending on how it makes sense to them. This is not conjecture. The statistics back this up. Over 80% of managers expect more flexible work from home policies post-pandemic; 70% of employees expect to adopt flexible work from home policies. Yet the key insight of Hybrid is this: as Jared notes, in our experience of living through the pandemic we come to understand that whilst physical spaces will always be important, we cannot rely on them or being together in person the way that we used to. Because we cannot rely on them, cloud powered technologies such as Microsoft Teams are fundamental to how businesses support working from home, working onsite or anywhere in between. Look at the numbers for Teams since the start of the pandemic – daily active usage (DAU) has rocketed to 115 million, up from 20 million at the end of 2019 when it first emerged out of China. 30 billion collaboration minutes worldwide by Microsoft 365 users in a single day. Astronomical growth.

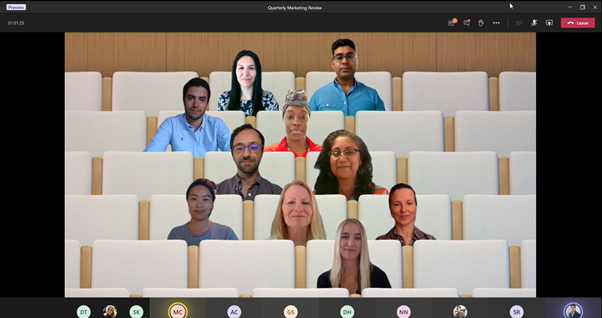
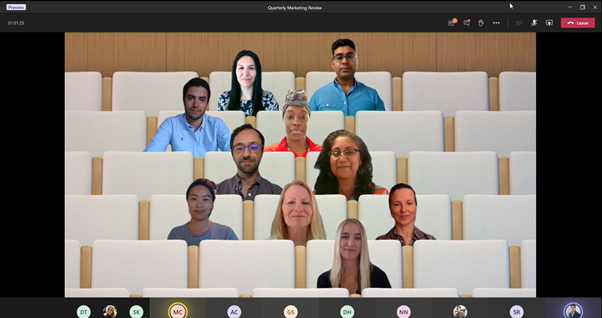
Yet growth isn’t just about Covid in-itself. Microsoft has worked hard and relentlessly over the course of 2020 to introduce over 100 new features for Microsoft Teams which has helped organisations and their users communicate and collaborate more effectively wherever they may be. Two examples that Hybrid gives to illustrate this are Large Gallery Mode which allows attendees to see more colleagues and up to 49 video feeds at the same time and Together Mode – a unique meeting experience where everyone is together within a virtual shared space designed to reduce meeting fatigue. Going beyond Jared’s examples, some of the other features introduced throughout 2020 include Breakout Rooms, Custom Backgrounds, Hard Mute, Pop Out Chat Meetings and Calling, the New File Experience and closer integration with SharePoint, Sensitivity Labels, Meeting Extensibility, the Yammer communities app, new Power Platform apps, Spotlight mode, Raise Hand, Live Captions, Presence duration and Skype Consumer Interop. It’s difficult to articulate just how much innovation has gone into Teams or do justice to all the passionate engineers and product managers who have clearly thrown themselves into this to deliver the functionality organisations have needed to succeed throughout the pandemic.
Moving onto some of the new features for Microsoft Teams which were introduced in Hybrid and which will bring a new dimension to how we will work in the hybrid workplace, we saw Endpoint transfer allowing users to seamlessly move their calls between different devices – for example from a laptop to a mobile device – without any interruption in call service or quality. Great for wanting to get up and go for a walk on that call when you’ve been sitting on that chair at home all day.

We saw Dynamic View. Dynamic view intelligently arranges the elements of your meeting for an optimal experience and lets you control who shows up alongside content that’s shared. For example, you can place the gallery at the top of the meeting screen, so people appear at the top of the meeting window enabling a more natural eye gaze with other participants. The participant gallery also auto-adjusts when the meeting window is resized. This will help to make meeting more engaging and, for many of us, help us to break out of the grid view we have become accustomed. It will be great to see colleagues’ reactions as content is shared.
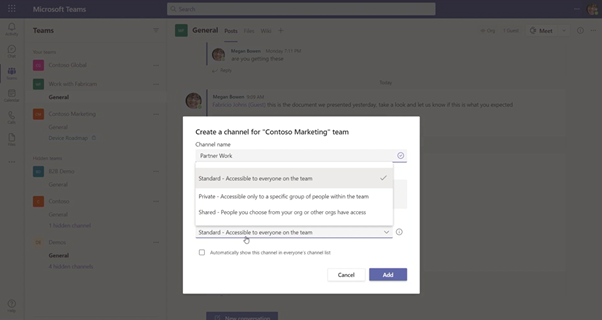
One of the features announced that will excite many Teams users is Teams Connect, otherwise known as Shared Channels. Teams Connect enables users to share channels in Teams across multiple organizations meaning you can collaborate – chat, meet, use apps, share, and co-author documents in real-time with individuals and teams that have an Azure Active Directory all without having to switch tenants – a pain point for many users and which many IT pros have flagged. Admins have access to granular security and compliance controls, allowing them to stay in control of how external users access data and information. This is a real game changer – and what is less known about Teams connect is that you can share channels across multiple Teams in your own organisation!
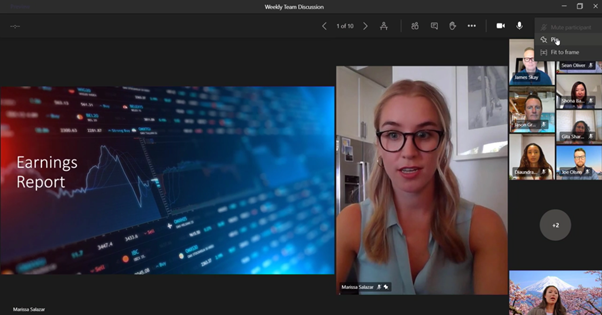
Next, we have Presenter Mode. Presenter mode empowers you as a presenter to customize how your video feed and content appear to the audience. There will be three options available. Standout which shows your video feed in front of the shared content, Reporter which has content as a visual aid above your shoulder like how a news report on television looks and Side-by-side which displays your video feed next to your content. This experience will allow you to form a much stronger connection to your audience where you can transmit your energy and personality into the presentation.

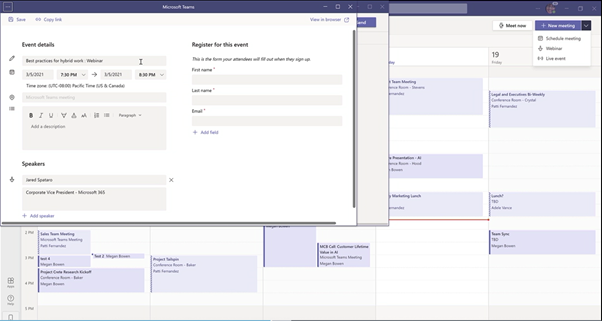
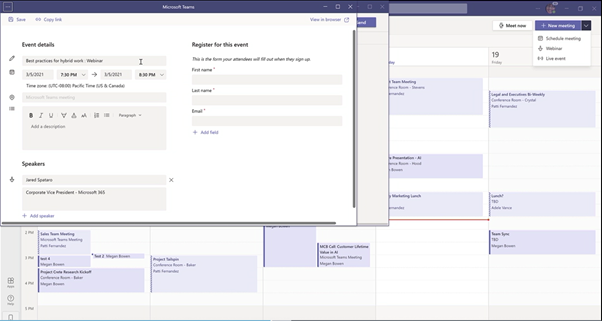
Finally, following on from the standard meeting and Live Event we will see the release of Webinars. A meeting organizer can easily add a registration page to a meeting to better manage attendance before and after any engagement. Following registration, attendees will automatically receive an email confirmation with a calendar invite for a simple join experience. Teams will support interactive webinars for up to 1,000 attendees including rich presentation options, reactions, and controls to disable chat, audio, and video. This will seamlessly scale to accommodate 10,000-person view-only broadcast experience and 20,000-person to the end of 2021 to support throughout the pandemic. Following a webinar, the organizer can use reporting to learn who attended and how long they participated. In addition, they can also upload contacts to other marketing tools to manage ongoing communication. All this will be delivered in Q1 2021. Another game changer.
Moving onto Teams Rooms, the hybrid workplace will demand an inclusive and equitable meeting experience whether remote, onsite, or even on the shop floor. Everyone needs to be seen and heard clearly no matter where they join from. Large gallery view and Together Mode in Microsoft Teams Rooms brings users together in the same form, where a second screen such as a Surface Hub 2S can be used to display and work the content.

We will also see the introduction of the intelligent speaker. The intelligent speaker brings speaker attributed captions and transcriptions to Microsoft Teams Room which enables attendees to easily follow along with what has been said and who said it. Using advanced speech recognition powered by Cortana, it can identify and differentiate the voices of up to 10 people in meeting rooms and apply their name and profile picture next to their transcripts.


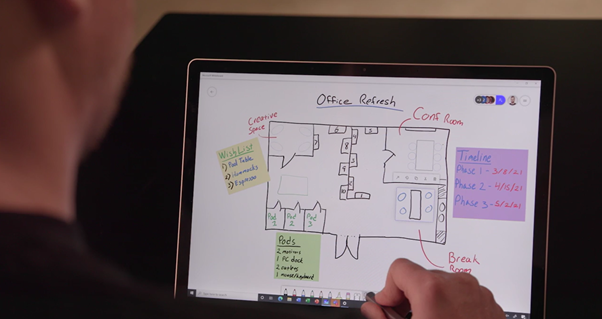
There were three reasons why this segway on teams meeting rooms was so exciting: Firstly, there was a great demonstration of Virtual Whiteboarding and how people can work together to ideate and be creative from anywhere on any device, using Surface Hub 2S and an iPad as examples. This really drives home how Teams removes location and environment as barriers to share and start a great dialogue with others on the idea we have to move things forward.
Secondly, Jared gave us a peek into how Microsoft see the new Casting to Teams Rooms evolving and how this could be leveraged to be able to share content on any screen.

Thirdly, Jared also gave us insights into how Microsoft see Microsoft Teams Rooms themselves evolving. Designing for a future of flexible working means rethinking about physical spaces. What does the meeting of future look like? Fluid, dynamic and cloud powered, where everyone feels included, engaged, and empowered to bring their best ideas.

At the conclusion of Hybrid, Jared says that Microsoft are ‘designing experiences to empower people in a work from anywhere world’ where they can work, learn, and collaborate whether that is at home, on the go, in the office, or from the manufacturing floor. Everything shown in this session has been ‘a scaffold to navigate a hybrid world’ with Teams as that organising layer. Yet Teams alone cannot give business leaders such things as ways to foster trust, build a culture and establish deep connections amongst employees – things which ultimately makes for a resilient organisation. This is the beginning of a conversation for Microsoft Viva. Built on Teams, Teams as the foundation of the employee experience as delivered by Viva.

For a session that was a little over 15 minutes, this had a significant amount of content and delivered masterfully as you would expect. But why should this session matter to us as IT Pros at all? Because it is important to understand where we are headed. Why is it important to know where we are headed? Because we need to lead and help organisations – our customers as well as our own – re-imagine how work will be as we move into a period where the pandemic becomes manageable. In our experience of living through the pandemic, we come to understand that whilst physical spaces will always be important, we cannot rely on them or being together in person the way that we used to.
And that is why we need Microsoft Teams. It’s no longer simply a tool to communicate and collaborate. When we have this organisation layer – this scaffold, this foundation upon which we can operate from anywhere – we can begin to build upon that and focus on the employee experience. By getting to where we give workers what they need wherever they may be in order to thrive in challenging times; we are developing resilience in a way we never could before.
Resilience is the reason we can never go back.
Read More here:
See great sessions on Microsoft Teams and Microsoft Viva at MS Ignite
About Chris Hoard
Blog: https://www.microsoft365pro.co.uk
Twitter: https://twitter.com/microsoft365pro

by Contributed | Mar 5, 2021 | Technology
This article is contributed. See the original author and article here.
Blogger: Chris Hoard, Partner Education Lead, Vuzion (UK), MCT Regional Lead, OAS MVP
Sessions: KEY06, KEY06-R1
2020 was a year that changed everything. The way we live. The way we work. As the Covid-19 pandemic spread across borders and over continents organisations in every country of every type needed to adapt in order to survive or to function. We, as IT professionals, came into a situation where it was imperative we act as the first responders. On the one hand we needed to help our customers maintain business operations and keep their workforces secure in the face of growing cyber-attacks. On the other, we needed to support many of our colleagues in this new world of remote working helping to safeguard and ensure their mental and emotional wellbeing. As Jared rightly points out in the opening scene of Hybrid, we also needed to do both of these things whilst navigating our own personal challenges at home. When does work start? When does it stop? Where can our business conversations or activities take place without intruding on the privacy of our loved ones whose home it is as much as ours? Given these new realities, how many of us forget that throughout the pandemic many workers have still needed to go onsite each and every single day as it’s an essential requirement for their job. Think of healthcare workers and construction workers. Think of police, and firefighters, those who work in waste disposal, electricians, plumbers, vets. Think of retail and hospitality. These first-line workers have needed to be able to easily communicate with their remote colleagues whilst at the same time still be safe on the job.

As vaccination programs roll out across the world, we now begin to think and to re-imagine how work will be as we enter a period where the pandemic becomes more manageable. What is already clear is that things are not going to return to the way they were pre-pandemic. Some of us will remain at home. Some of us will go back to working or continue to work onsite. Others may choose to work at home or onsite in a hybrid setup depending on how it makes sense to them. This is not conjecture. The statistics back this up. Over 80% of managers expect more flexible work from home policies post-pandemic; 70% of employees expect to adopt flexible work from home policies. Yet the key insight of Hybrid is this: as Jared notes, in our experience of living through the pandemic we come to understand that whilst physical spaces will always be important, we cannot rely on them or being together in person the way that we used to. Because we cannot rely on them, cloud powered technologies such as Microsoft Teams are fundamental to how businesses support working from home, working onsite or anywhere in between. Look at the numbers for Teams since the start of the pandemic – daily active usage (DAU) has rocketed to 115 million, up from 20 million at the end of 2019 when it first emerged out of China. 30 billion collaboration minutes worldwide by Microsoft 365 users in a single day. Astronomical growth.

Yet growth isn’t just about Covid in-itself. Microsoft has worked hard and relentlessly over the course of 2020 to introduce over 100 new features for Microsoft Teams which has helped organisations and their users communicate and collaborate more effectively wherever they may be. Two examples that Hybrid gives to illustrate this are Large Gallery Mode which allows attendees to see more colleagues and up to 49 video feeds at the same time and Together Mode – a unique meeting experience where everyone is together within a virtual shared space designed to reduce meeting fatigue. Going beyond Jared’s examples, some of the other features introduced throughout 2020 include Breakout Rooms, Custom Backgrounds, Hard Mute, Pop Out Chat Meetings and Calling, the New File Experience and closer integration with SharePoint, Sensitivity Labels, Meeting Extensibility, the Yammer communities app, new Power Platform apps, Spotlight mode, Raise Hand, Live Captions, Presence duration and Skype Consumer Interop. It’s difficult to articulate just how much innovation has gone into Teams or do justice to all the passionate engineers and product managers who have clearly thrown themselves into this to deliver the functionality organisations have needed to succeed throughout the pandemic.
Moving onto some of the new features for Microsoft Teams which were introduced in Hybrid and which will bring a new dimension to how we will work in the hybrid workplace, we saw Endpoint transfer allowing users to seamlessly move their calls between different devices – for example from a laptop to a mobile device – without any interruption in call service or quality. Great for wanting to get up and go for a walk on that call when you’ve been sitting on that chair at home all day.

We saw Dynamic View. Dynamic view intelligently arranges the elements of your meeting for an optimal experience and lets you control who shows up alongside content that’s shared. For example, you can place the gallery at the top of the meeting screen, so people appear at the top of the meeting window enabling a more natural eye gaze with other participants. The participant gallery also auto-adjusts when the meeting window is resized. This will help to make meeting more engaging and, for many of us, help us to break out of the grid view we have become accustomed. It will be great to see colleagues’ reactions as content is shared.
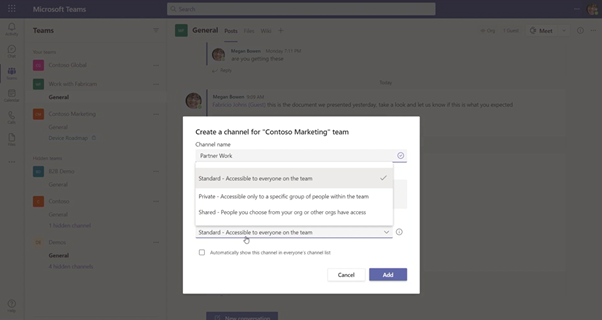
One of the features announced that will excite many Teams users is Teams Connect, otherwise known as Shared Channels. Teams Connect enables users to share channels in Teams across multiple organizations meaning you can collaborate – chat, meet, use apps, share, and co-author documents in real-time with individuals and teams that have an Azure Active Directory all without having to switch tenants – a pain point for many users and which many IT pros have flagged. Admins have access to granular security and compliance controls, allowing them to stay in control of how external users access data and information. This is a real game changer – and what is less known about Teams connect is that you can share channels across multiple Teams in your own organisation!
Next, we have Presenter Mode. Presenter mode empowers you as a presenter to customize how your video feed and content appear to the audience. There will be three options available. Standout which shows your video feed in front of the shared content, Reporter which has content as a visual aid above your shoulder like how a news report on television looks and Side-by-side which displays your video feed next to your content. This experience will allow you to form a much stronger connection to your audience where you can transmit your energy and personality into the presentation.

Finally, following on from the standard meeting and Live Event we will see the release of Webinars. A meeting organizer can easily add a registration page to a meeting to better manage attendance before and after any engagement. Following registration, attendees will automatically receive an email confirmation with a calendar invite for a simple join experience. Teams will support interactive webinars for up to 1,000 attendees including rich presentation options, reactions, and controls to disable chat, audio, and video. This will seamlessly scale to accommodate 10,000-person view-only broadcast experience and 20,000-person to the end of 2021 to support throughout the pandemic. Following a webinar, the organizer can use reporting to learn who attended and how long they participated. In addition, they can also upload contacts to other marketing tools to manage ongoing communication. All this will be delivered in Q1 2021. Another game changer.
Moving onto Teams Rooms, the hybrid workplace will demand an inclusive and equitable meeting experience whether remote, onsite, or even on the shop floor. Everyone needs to be seen and heard clearly no matter where they join from. Large gallery view and Together Mode in Microsoft Teams Rooms brings users together in the same form, where a second screen such as a Surface Hub 2S can be used to display and work the content.

We will also see the introduction of the intelligent speaker. The intelligent speaker brings speaker attributed captions and transcriptions to Microsoft Teams Room which enables attendees to easily follow along with what has been said and who said it. Using advanced speech recognition powered by Cortana, it can identify and differentiate the voices of up to 10 people in meeting rooms and apply their name and profile picture next to their transcripts.


There were three reasons why this segway on teams meeting rooms was so exciting: Firstly, there was a great demonstration of Virtual Whiteboarding and how people can work together to ideate and be creative from anywhere on any device, using Surface Hub 2S and an iPad as examples. This really drives home how Teams removes location and environment as barriers to share and start a great dialogue with others on the idea we have to move things forward.
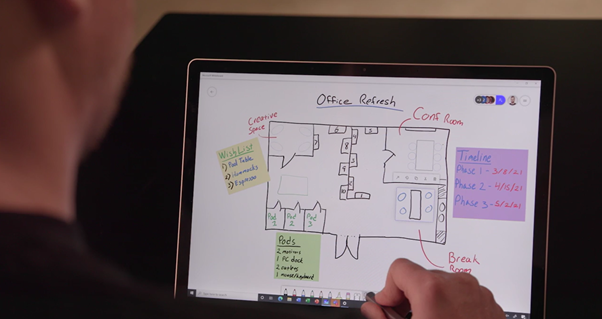
Secondly, Jared gave us a peek into how Microsoft see the new Casting to Teams Rooms evolving and how this could be leveraged to be able to share content on any screen.

Thirdly, Jared also gave us insights into how Microsoft see Microsoft Teams Rooms themselves evolving. Designing for a future of flexible working means rethinking about physical spaces. What does the meeting of future look like? Fluid, dynamic and cloud powered, where everyone feels included, engaged, and empowered to bring their best ideas.

At the conclusion of Hybrid, Jared says that Microsoft are ‘designing experiences to empower people in a work from anywhere world’ where they can work, learn, and collaborate whether that is at home, on the go, in the office, or from the manufacturing floor. Everything shown in this session has been ‘a scaffold to navigate a hybrid world’ with Teams as that organising layer. Yet Teams alone cannot give business leaders such things as ways to foster trust, build a culture and establish deep connections amongst employees – things which ultimately makes for a resilient organisation. This is the beginning of a conversation for Microsoft Viva. Built on Teams, Teams as the foundation of the employee experience as delivered by Viva.

For a session that was a little over 15 minutes, this had a significant amount of content and delivered masterfully as you would expect. But why should this session matter to us as IT Pros at all? Because it is important to understand where we are headed. Why is it important to know where we are headed? Because we need to lead and help organisations – our customers as well as our own – re-imagine how work will be as we move into a period where the pandemic becomes manageable. In our experience of living through the pandemic, we come to understand that whilst physical spaces will always be important, we cannot rely on them or being together in person the way that we used to.
And that is why we need Microsoft Teams. It’s no longer simply a tool to communicate and collaborate. When we have this organisation layer – this scaffold, this foundation upon which we can operate from anywhere – we can begin to build upon that and focus on the employee experience. By getting to where we give workers what they need wherever they may be in order to thrive in challenging times; we are developing resilience in a way we never could before.
Resilience is the reason we can never go back.
Read More here:
See great sessions on Microsoft Teams and Microsoft Viva at MS Ignite
About Chris Hoard
Blog: https://www.microsoft365pro.co.uk
Twitter: https://twitter.com/microsoft365pro




Recent Comments