by Scott Muniz | Feb 28, 2022 | Security, Technology
This article is contributed. See the original author and article here.
accesspress_themes — plugins_and_themes
|
Numerous Plugins and Themes from the AccessPress Themes (aka Access Keys) vendor are backdoored due to their website being compromised. Only plugins and themes downloaded via the vendor website are affected, and those hosted on wordpress.org are not. However, all of them were updated or removed to avoid any confusion |
2022-02-21 |
not yet calculated |
CVE-2021-24867
MISC
MISC |
accounting_journal_management — accounting_journal_management
|
Accounting Journal Management 1.0 is vulnerable to XSS-PHPSESSID-Hijacking. The parameter manage_user from User lists is vulnerable to XSS-Stored and PHPSESSID attacks. The malicious user can attack the system by using the already session which he has from inside and outside of the network. |
2022-02-24 |
not yet calculated |
CVE-2022-24582
MISC |
ad_inserter — ad_inserter
|
The Ad Inserter WordPress plugin before 2.7.10, Ad Inserter Pro WordPress plugin before 2.7.10 do not sanitise and escape the html_element_selection parameter before outputting it back in the page, leading to a Reflected Cross-Site Scripting |
2022-02-21 |
not yet calculated |
CVE-2022-0288
MISC |
advanced_database_cleaner — advanced_database_cleaner
|
The Advanced Database Cleaner WordPress plugin before 3.0.4 does not sanitise and escape $_GET keys and values before outputting them back in attributes, leading to Reflected Cross-Site Scripting issues |
2022-02-21 |
not yet calculated |
CVE-2021-24921
MISC |
alecto — camera
|
Settings/network settings/wireless settings on the Alecto DVC-215IP camera version 63.1.1.173 and below shows the Wi-Fi passphrase hidden, but by editing/removing the style of the password field the password becomes visible which grants access to an internal network connected to the camera. |
2022-02-24 |
not yet calculated |
CVE-2022-24610
MISC |
alluxio — alluxio
|
In Alluxio before 2.7.3, the logserver does not validate the input stream. NOTE: this is not the same as the CVE-2021-44228 Log4j vulnerability. |
2022-02-20 |
not yet calculated |
CVE-2022-23848
CONFIRM |
amazon — echo_dot
|
Improper Neutralization of audio output from 3rd and 4th Generation Amazon Echo Dot devices allows arbitrary voice command execution on these devices via a malicious skill (in the case of remote attackers) or by pairing a malicious Bluetooth device (in the case of physically proximate attackers), aka an “Alexa versus Alexa (AvA)” attack. |
2022-02-24 |
not yet calculated |
CVE-2022-25809
MISC |
anti-malware_security_and_brute-force_firewall — anti-malware_security_and_brute-force_firewall
|
The Anti-Malware Security and Brute-Force Firewall WordPress plugin before 4.20.94 does not sanitise and escape the POST data before outputting it back in attributes of an admin page, leading to a Reflected Cross-Site scripting. Due to the presence of specific parameter value, available to admin users, this can only be exploited by an admin against another admin user. |
2022-02-21 |
not yet calculated |
CVE-2021-25101
MISC |
| anuko — time_tracker |
Anuko Time Tracker is an open source, web-based time tracking application written in PHP. ttUser.class.php in Time Tracker versions prior to 1.20.0.5646 was not escaping primary group name for display. Because of that, it was possible for a logged in user to modify primary group name with elements of JavaScript. Such script could then be executed in user browser on subsequent requests on pages where primary group name was displayed. This is vulnerability has been fixed in version 1.20.0.5646. Users who are unable to upgrade may modify ttUser.class.php to use an additional call to htmlspecialchars when printing group name. |
2022-02-24 |
not yet calculated |
CVE-2022-24708
MISC
CONFIRM |
anuko — time_tracker
|
Anuko Time Tracker is an open source, web-based time tracking application written in PHP. UNION SQL injection and time-based blind injection vulnerabilities existed in Time Tracker Puncher plugin in versions of anuko timetracker prior to 1.20.0.5642. This was happening because the Puncher plugin was reusing code from other places and was relying on an unsanitized date parameter in POST requests. Because the parameter was not checked, it was possible to craft POST requests with malicious SQL for Time Tracker database. This issue has been resolved in in version 1.20.0.5642. Users unable to upgrade are advised to add their own checks to input. |
2022-02-24 |
not yet calculated |
CVE-2022-24707
MISC
CONFIRM |
anycomment — anycomment
|
The AnyComment WordPress plugin before 0.2.18 does not have CSRF checks in the Import and Revert HyperComments features, allowing attackers to make logged in admin perform such actions via a CSRF attack |
2022-02-21 |
not yet calculated |
CVE-2022-0134
MISC |
anycomment — anycomment
|
The AnyComment WordPress plugin before 0.2.18 is affected by a race condition when liking/disliking a comment/reply, which could allow any authenticated user to quickly raise their rating or lower the rating of other users |
2022-02-21 |
not yet calculated |
CVE-2022-0279
MISC |
| apache — airflow |
In Apache Airflow, prior to version 2.2.4, some example DAGs did not properly sanitize user-provided params, making them susceptible to OS Command Injection from the web UI. |
2022-02-25 |
not yet calculated |
CVE-2022-24288
MISC |
apache — airflow
|
It was discovered that the “Trigger DAG with config” screen was susceptible to XSS attacks via the `origin` query argument. This issue affects Apache Airflow versions 2.2.3 and below. |
2022-02-25 |
not yet calculated |
CVE-2021-45229
MISC |
apache — apache_jspwiki
|
A carefully crafted user preferences for submission could trigger an XSS vulnerability on Apache JSPWiki, related to the user preferences screen, which could allow the attacker to execute javascript in the victim’s browser and get some sensitive information about the victim. Apache JSPWiki users should upgrade to 2.11.2 or later. |
2022-02-25 |
not yet calculated |
CVE-2022-24948
MISC
MLIST |
apache — apache_jspwiki
|
Apache JSPWiki user preferences form is vulnerable to CSRF attacks, which can lead to account takeover. Apache JSPWiki users should upgrade to 2.11.2 or later. |
2022-02-25 |
not yet calculated |
CVE-2022-24947
MISC
MLIST |
atlassian — jira_service_management_server_and_data_center
|
Affected versions of Atlassian Jira Service Management Server and Data Center allow attackers with administrator privileges to inject arbitrary HTML or JavaScript via a Cross-Site Scripting (XSS) vulnerability in the “Object Schema” field of /secure/admin/InsightDefaultCustomFieldConfig.jspa. The affected versions are before version 4.21.0. |
2022-02-24 |
not yet calculated |
CVE-2021-43943
N/A |
audio_file_library — audio_file_library
|
In autofile Audio File Library 0.3.6, there exists one memory leak vulnerability in printfileinfo, in printinfo.c, which allows an attacker to leak sensitive information via a crafted file. The printfileinfo function calls the copyrightstring function to get data, however, it dosn’t use zero bytes to truncate the data. |
2022-02-24 |
not yet calculated |
CVE-2022-24599
MISC |
awful_salmonella_tar — awful_salmonella_tar
|
A ..%2F path traversal vulnerability exists in the path handler of awful-salmonella-tar before 0.0.4. Attackers can only list directories (not read files). This occurs because the safe-path? Scheme predicate is not used for directories. |
2022-02-18 |
not yet calculated |
CVE-2022-25358
MISC
MISC |
b2-sdk-python — b2-sdk-python
|
b2-sdk-python is a python library to access cloud storage provided by backblaze. Linux and Mac releases of the SDK version 1.14.0 and below contain a key disclosure vulnerability that, in certain conditions, can be exploited by local attackers through a time-of-check-time-of-use (TOCTOU) race condition. SDK users of the SqliteAccountInfo format are vulnerable while users of the InMemoryAccountInfo format are safe. The SqliteAccountInfo saves API keys (and bucket name-to-id mapping) in a local database file ($XDG_CONFIG_HOME/b2/account_info, ~/.b2_account_info or a user-defined path). When first created, the file is world readable and is (typically a few milliseconds) later altered to be private to the user. If the directory containing the file is readable by a local attacker then during the brief period between file creation and permission modification, a local attacker can race to open the file and maintain a handle to it. This allows the local attacker to read the contents after the file after the sensitive information has been saved to it. Consumers of this SDK who rely on it to save data using SqliteAccountInfo class should upgrade to the latest version of the SDK. Those who believe a local user might have opened a handle using this race condition, should remove the affected database files and regenerate all application keys. Users should upgrade to b2-sdk-python 1.14.1 or later. |
2022-02-23 |
not yet calculated |
CVE-2022-23651
MISC
MISC
CONFIRM |
b2_command-line_tool — b2_command_line_tool
|
B2 Command Line Tool is the official command line tool for the backblaze cloud storage service. Linux and Mac releases of the B2 command-line tool version 3.2.0 and below contain a key disclosure vulnerability that, in certain conditions, can be exploited by local attackers through a time-of-check-time-of-use (TOCTOU) race condition. The command line tool saves API keys (and bucket name-to-id mapping) in a local database file (`$XDG_CONFIG_HOME/b2/account_info`, `~/.b2_account_info` or a user-defined path) when `b2 authorize-account` is first run. This happens regardless of whether a valid key is provided or not. When first created, the file is world readable and is (typically a few milliseconds) later altered to be private to the user. If the directory is readable by a local attacker and the user did not yet run `b2 authorize-account` then during the brief period between file creation and permission modification, a local attacker can race to open the file and maintain a handle to it. This allows the local attacker to read the contents after the file after the sensitive information has been saved to it. Users that have not yet run `b2 authorize-account` should upgrade to B2 Command-Line Tool v3.2.1 before running it. Users that have run `b2 authorize-account` are safe if at the time of the file creation no other local users had read access to the local configuration file. Users that have run `b2 authorize-account` where the designated path could be opened by another local user should upgrade to B2 Command-Line Tool v3.2.1 and remove the database and regenerate all application keys. Note that `b2 clear-account` does not remove the database file and it should not be used to ensure that all open handles to the file are invalidated. If B2 Command-Line Tool cannot be upgraded to v3.2.1 due to a dependency conflict, a binary release can be used instead. Alternatively a new version could be installed within a virtualenv, or the permissions can be changed to prevent local users from opening the database file. |
2022-02-23 |
not yet calculated |
CVE-2022-23653
CONFIRM
MISC |
baicloud-cms — baicloud-cms
|
BaiCloud-cms v2.5.7 was discovered to contain multiple SQL injection vulnerabilities via the tongji and baidu_map parameters in /user/ztconfig.php. |
2022-02-19 |
not yet calculated |
CVE-2021-44302
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. Crafted data in a DGN file can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15507. |
2022-02-18 |
not yet calculated |
CVE-2021-46635
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. Crafted data in a DGN file can trigger a read past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15508. |
2022-02-18 |
not yet calculated |
CVE-2021-46636
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a stack-based buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15510. |
2022-02-18 |
not yet calculated |
CVE-2021-46638
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. Crafted data in a DGN file can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15511. |
2022-02-18 |
not yet calculated |
CVE-2021-46639
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of BMP images. Crafted data in a BMP image can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15531. |
2022-02-18 |
not yet calculated |
CVE-2021-46645
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15537. |
2022-02-18 |
not yet calculated |
CVE-2021-46651
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15535. |
2022-02-18 |
not yet calculated |
CVE-2021-46649
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JT files. Crafted data in a JT file can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15464. |
2022-02-18 |
not yet calculated |
CVE-2021-46634
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15509. |
2022-02-18 |
not yet calculated |
CVE-2021-46637
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a heap-based buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15534. |
2022-02-18 |
not yet calculated |
CVE-2021-46648
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of BMP images. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a heap-based buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15533. |
2022-02-18 |
not yet calculated |
CVE-2021-46647
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. Crafted data in a DGN file can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15532. |
2022-02-18 |
not yet calculated |
CVE-2021-46646
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15536. |
2022-02-18 |
not yet calculated |
CVE-2021-46650
MISC
MISC |
bentley — microstation_connect
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. Crafted data in a DGN file can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15530. |
2022-02-18 |
not yet calculated |
CVE-2021-46644
MISC
MISC |
bentley — microstation_connect
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of PDF files. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15463. |
2022-02-18 |
not yet calculated |
CVE-2021-46633
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a stack-based buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15515. |
2022-02-18 |
not yet calculated |
CVE-2021-46643
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DXF files. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15457. |
2022-02-18 |
not yet calculated |
CVE-2021-46627
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of BMP images. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15459. |
2022-02-18 |
not yet calculated |
CVE-2021-46629
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of FBX files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15460. |
2022-02-18 |
not yet calculated |
CVE-2021-46630
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of TIF images. The issue results from the lack of proper initialization of memory prior to accessing it. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15461. |
2022-02-18 |
not yet calculated |
CVE-2021-46631
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JP2 images. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15462. |
2022-02-18 |
not yet calculated |
CVE-2021-46632
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JT files. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15630. |
2022-02-18 |
not yet calculated |
CVE-2021-46655
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of JT files. The issue results from the lack of validating the existence of an object prior to performing further free operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15455. |
2022-02-18 |
not yet calculated |
CVE-2021-46625
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DWG files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15454. |
2022-02-18 |
not yet calculated |
CVE-2021-46624
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JT files. Crafted data in a JT file can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15631. |
2022-02-18 |
not yet calculated |
CVE-2021-46656
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of 3DS files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15453. |
2022-02-18 |
not yet calculated |
CVE-2021-46623
MISC
MISC |
| bentley — view |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of BMP images. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15458. |
2022-02-18 |
not yet calculated |
CVE-2021-46628
MISC
MISC |
bentley — view
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. Crafted data in a DGN file can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15538. |
2022-02-18 |
not yet calculated |
CVE-2021-46652
MISC
MISC |
bentley — view
|
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15540. |
2022-02-18 |
not yet calculated |
CVE-2021-46654
MISC
MISC |
bentley — view
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of BMP images. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a heap-based buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15539. |
2022-02-18 |
not yet calculated |
CVE-2021-46653
MISC
MISC |
bentley — view
|
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15514. |
2022-02-18 |
not yet calculated |
CVE-2021-46642
MISC
MISC |
bentley — view
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of J2K images. Crafted data in a J2K image can trigger a read past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15456. |
2022-02-18 |
not yet calculated |
CVE-2021-46626
MISC
MISC |
bentley — view
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN file. Crafted data in a DNG file can trigger a read past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15513. |
2022-02-18 |
not yet calculated |
CVE-2021-46641
MISC
MISC |
bentley — view
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley View 10.15.0.75. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DGN files. Crafted data in a DGN file can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15512. |
2022-02-18 |
not yet calculated |
CVE-2021-46640
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of TIF images. The issue results from the lack of proper initialization of memory prior to accessing it. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15411. |
2022-02-18 |
not yet calculated |
CVE-2021-46617
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of JT files. The issue results from the lack of validating the existence of an object prior to performing further free operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15415. |
2022-02-18 |
not yet calculated |
CVE-2021-46621
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of BMP images. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15410. |
2022-02-18 |
not yet calculated |
CVE-2021-46616
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of FBX files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15414. |
2022-02-18 |
not yet calculated |
CVE-2021-46620
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of PDF files. Crafted data in a PDF file can trigger a read past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15413. |
2022-02-18 |
not yet calculated |
CVE-2021-46619
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of PNG images. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15412. |
2022-02-18 |
not yet calculated |
CVE-2021-46618
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of J2K images. Crafted data in a J2K image can trigger a read past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15416. |
2022-02-18 |
not yet calculated |
CVE-2021-46622
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of BMP images. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15409. |
2022-02-18 |
not yet calculated |
CVE-2021-46615
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of PDF files. Crafted data in a PDF file can trigger a read past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15406. |
2022-02-18 |
not yet calculated |
CVE-2021-46612
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JP2 images. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15405. |
2022-02-18 |
not yet calculated |
CVE-2021-46611
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JT files. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15404. |
2022-02-18 |
not yet calculated |
CVE-2021-46610
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DXF files. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15407. |
2022-02-18 |
not yet calculated |
CVE-2021-46613
MISC
MISC |
| bentley — microstation_connect |
Bentley MicroStation CONNECT 10.16.0.80 J2K File Parsing Out-Of-Bounds Read Remote Code Execution Vulnerability. This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of J2K images. Crafted data in a J2K image can trigger a read past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15408. |
2022-02-18 |
not yet calculated |
CVE-2021-46614
MISC
MISC |
| bentley — microstation_connect |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Bentley MicroStation CONNECT 10.16.0.80. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of PDF files. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15403. |
2022-02-18 |
not yet calculated |
CVE-2021-46609
MISC
MISC |
blender — blender
|
An integer overflow in the processing of loaded 2D images leads to a write-what-where vulnerability and an out-of-bounds read vulnerability, allowing an attacker to leak sensitive information or achieve code execution in the context of the Blender process when a specially crafted image file is loaded. This flaw affects Blender versions prior to 2.83.19, 2.93.8 and 3.1. |
2022-02-24 |
not yet calculated |
CVE-2022-0545
MISC |
blender — blender
|
An integer underflow in the DDS loader of Blender leads to an out-of-bounds read, possibly allowing an attacker to read sensitive data using a crafted DDS image file. This flaw affects Blender versions prior to 2.83.19, 2.93.8 and 3.1. |
2022-02-24 |
not yet calculated |
CVE-2022-0544
MISC |
blender — blender
|
A missing bounds check in the image loader used in Blender 3.x and 2.93.8 leads to out-of-bounds heap access, allowing an attacker to cause denial of service, memory corruption or potentially code execution. |
2022-02-24 |
not yet calculated |
CVE-2022-0546
MISC |
| bloofoxcms — bloofoxcms |
Multiple SQL Injection vulnerabilities exist in bloofoxCMS 0.5.2.1 – 0.5.1 via the (1) URLs, (2) lang_id, (3) tmpl_id, (4) mod_rewrite (5) eta_doctype. (6) meta_charset, (7) default_group, and (8) page group parameters in the settings mode in admin/index.php. |
2022-02-24 |
not yet calculated |
CVE-2021-44610
MISC |
bloofoxcms — bloofoxcms
|
Multiple Cross Site Scripting (XSS) vulnerabilities exists in bloofoxCMS 0.5.2.1 – 0.5.1 via the (1) file parameter and (2) type parameter in an edit action in index.php. |
2022-02-24 |
not yet calculated |
CVE-2021-44608
MISC |
bmc_tracki-it! — bmc_track-it!
|
This vulnerability allows remote attackers to bypass authentication on affected installations of BMC Track-It! 20.21.01.102. Authentication is not required to exploit this vulnerability. The specific flaw exists within the authorization of HTTP requests. The issue results from the lack of authentication prior to allowing access to functionality. An attacker can leverage this vulnerability to bypass authentication on the system. Was ZDI-CAN-14618. |
2022-02-18 |
not yet calculated |
CVE-2022-24047
MISC
MISC |
brocade — fabric_os
|
Brocade Fabric OS before Brocade Fabric OS v8.2.1c, v8.1.2h, and all versions of Brocade Fabric OS v8.0.x and v7.x contain documented hard-coded credentials, which could allow attackers to gain access to the system. |
2022-02-21 |
not yet calculated |
CVE-2021-27797
MISC |
brocade — fabric_os
|
A vulnerability in Brocade Fabric OS versions before Brocade Fabric OS v8.0.1b, v7.4.1d could allow an authenticated attacker within the restricted shell environment (rbash) as either the “user” or “factory” account, to read the contents of any file on the filesystem utilizing one of a few available binaries. |
2022-02-21 |
not yet calculated |
CVE-2021-27796
MISC |
| bsafe — bsafe |
Only customers with active BSAFE maintenance contracts can receive details about this vulnerability. Public disclosure of the vulnerability details will be shared at a later date. |
2022-02-23 |
not yet calculated |
CVE-2022-24409
CONFIRM |
buffer_button — buffer_button
|
The Buffer Button WordPress plugin through 1.0 was vulnerable to Authenticated Stored Cross Site Scripting (XSS) within the Twitter username to mention text field. |
2022-02-21 |
not yet calculated |
CVE-2021-25058
MISC |
c-dataonu4ferw — c-dataonu4ferw
|
A command injection vulnerability in the function formImportOMCIShell of C-DATA ONU4FERW V2.1.13_X139 allows attackers to execute arbitrary commands via a crafted file. |
2022-02-25 |
not yet calculated |
CVE-2021-44132
MISC |
capsule_operator — capsule_operator
|
capsule-proxy is a reverse proxy for Capsule Operator which provides multi-tenancy in Kubernetes. In versions prior to 0.2.1 an attacker with a proper authentication mechanism may use a malicious `Connection` header to start a privilege escalation attack towards the Kubernetes API Server. This vulnerability allows for an exploit of the `cluster-admin` Role bound to `capsule-proxy`. There are no known workarounds for this issue. |
2022-02-22 |
not yet calculated |
CVE-2022-23652
MISC
CONFIRM
MISC |
| checkmk — checkmk |
In Checkmk <=2.0.0p19 fixed in 2.0.0p20 and Checkmk <=1.6.0p27 fixed in 1.6.0p28, the title of a Predefined condition is not properly escaped when shown as condition, which can result in Cross Site Scripting (XSS). |
2022-02-24 |
not yet calculated |
CVE-2022-24566
MISC |
checkmk — checkmk
|
Checkmk <=2.0.0p19 contains a Cross Site Scripting (XSS) vulnerability. While creating or editing a user attribute, the Help Text is subject to HTML injection, which can be triggered for editing a user. |
2022-02-21 |
not yet calculated |
CVE-2022-24564
MISC |
checkmk — checkmk
|
Checkmk <=2.0.0p19 Fixed in 2.0.0p20 and Checkmk <=1.6.0p27 Fixed in 1.6.0p28 are affected by a Cross Site Scripting (XSS) vulnerability. The Alias of a site was not properly escaped when shown as condition for notifications. |
2022-02-24 |
not yet calculated |
CVE-2022-24565
MISC |
| chocobozzz — peertube |
Improper Authorization in GitHub repository chocobozzz/peertube prior to 4.1.0. |
2022-02-23 |
not yet calculated |
CVE-2022-0726
CONFIRM
MISC |
chocobozzz — peertube
|
Improper Access Control in GitHub repository chocobozzz/peertube prior to 4.1.0. |
2022-02-23 |
not yet calculated |
CVE-2022-0727
MISC
CONFIRM |
cimplicity — cimplicity
|
The affected product is vulnerable due to cleartext transmission of credentials seen in the CIMPLICITY network, which can be easily spoofed and used to log in to make operational changes to the system. |
2022-02-25 |
not yet calculated |
CVE-2022-21798
MISC |
cimplicity — cimplicity
|
Exploitation of this vulnerability may result in local privilege escalation and code execution. GE maintains exploitation of this vulnerability is only possible if the attacker has login access to a machine actively running CIMPLICITY, the CIMPLICITY server is not already running a project, and the server is licensed for multiple projects. |
2022-02-25 |
not yet calculated |
CVE-2022-23921
MISC |
cisco — nx-os_software
|
A vulnerability in the NX-API feature of Cisco NX-OS Software could allow an authenticated, remote attacker to execute arbitrary commands with root privileges. The vulnerability is due to insufficient input validation of user supplied data that is sent to the NX-API. An attacker could exploit this vulnerability by sending a crafted HTTP POST request to the NX-API of an affected device. A successful exploit could allow the attacker to execute arbitrary commands with root privileges on the underlying operating system. Note: The NX-API feature is disabled by default. |
2022-02-23 |
not yet calculated |
CVE-2022-20650
CISCO |
| cisco — nxos_software |
A vulnerability in the rate limiter for Bidirectional Forwarding Detection (BFD) traffic of Cisco NX-OS Software for Cisco Nexus 9000 Series Switches could allow an unauthenticated, remote attacker to cause BFD traffic to be dropped on an affected device. This vulnerability is due to a logic error in the BFD rate limiter functionality. An attacker could exploit this vulnerability by sending a crafted stream of traffic through the device. A successful exploit could allow the attacker to cause BFD traffic to be dropped, resulting in BFD session flaps. BFD session flaps can cause route instability and dropped traffic, resulting in a denial of service (DoS) condition. This vulnerability applies to both IPv4 and IPv6 traffic. |
2022-02-23 |
not yet calculated |
CVE-2022-20623
CISCO |
| cisco — nxos_software |
A vulnerability in the Cisco Fabric Services over IP (CFSoIP) feature of Cisco NX-OS Software could allow an unauthenticated, remote attacker to cause a denial of service (DoS) condition on an affected device. This vulnerability is due to insufficient validation of incoming CFSoIP packets. An attacker could exploit this vulnerability by sending crafted CFSoIP packets to an affected device. A successful exploit could allow the attacker to cause the affected device to reload, resulting in a DoS condition. |
2022-02-23 |
not yet calculated |
CVE-2022-20624
CISCO |
cisco — nxos_software
|
A vulnerability in the Cisco Discovery Protocol service of Cisco FXOS Software and Cisco NX-OS Software could allow an unauthenticated, adjacent attacker to cause the service to restart, resulting in a denial of service (DoS) condition. This vulnerability is due to improper handling of Cisco Discovery Protocol messages that are processed by the Cisco Discovery Protocol service. An attacker could exploit this vulnerability by sending a series of malicious Cisco Discovery Protocol messages to an affected device. A successful exploit could allow the attacker to cause the Cisco Discovery Protocol service to fail and restart. In rare conditions, repeated failures of the process could occur, which could cause the entire device to restart. |
2022-02-23 |
not yet calculated |
CVE-2022-20625
CISCO |
| cobbler — cobbler |
An issue was discovered in Cobbler before 3.3.1. In the templar.py file, the function check_for_invalid_imports can allow Cheetah code to import Python modules via the “#from MODULE import” substring. (Only lines beginning with #import are blocked.) |
2022-02-19 |
not yet calculated |
CVE-2021-45082
MISC
MISC |
| cobbler — cobbler |
An issue was discovered in Cobbler before 3.3.1. Files in /etc/cobbler are world readable. Two of those files contain some sensitive information that can be exposed to a local user who has non-privileged access to the server. The users.digest file contains the sha2-512 digest of users in a Cobbler local installation. In the case of an easy-to-guess password, it’s trivial to obtain the plaintext string. The settings.yaml file contains secrets such as the hashed default password. |
2022-02-20 |
not yet calculated |
CVE-2021-45083
MISC
MISC |
cobbler — cobbler
|
An issue was discovered in Cobbler through 3.3.1. Routines in several files use the HTTP protocol instead of the more secure HTTPS. |
2022-02-20 |
not yet calculated |
CVE-2021-45081
MISC
MLIST |
| coming_soon_and_maintenance — coming_soon_and_maintenance |
The Coming soon and Maintenance mode WordPress plugin before 3.6.8 does not have CSRF check in its coming_soon_send_mail AJAX action, allowing attackers to make logged in admin to send arbitrary emails to all subscribed users via a CSRF attack |
2022-02-21 |
not yet calculated |
CVE-2022-0199
CONFIRM
MISC |
coming_soon_and_maintenance — coming_soon_and_maintenance
|
The Coming soon and Maintenance mode WordPress plugin before 3.6.8 does not have authorisation and CSRF checks in its coming_soon_send_mail AJAX action, allowing any authenticated users, with a role as low as subscriber to send arbitrary emails to all subscribed users |
2022-02-21 |
not yet calculated |
CVE-2022-0164
MISC
CONFIRM |
corenlp — corenlp
|
An Incorrect Access Control vulnerability exists in CoreNLP 4.3.2 via the classifier in NERServlet.java (lines 158 and 159). |
2022-02-24 |
not yet calculated |
CVE-2021-44550
MISC |
cosign — cosign
|
Cosign provides container signing, verification, and storage in an OCI registry for the sigstore project. Prior to version 1.5.2, Cosign can be manipulated to claim that an entry for a signature exists in the Rekor transparency log even if it doesn’t. This requires the attacker to have pull and push permissions for the signature in OCI. This can happen with both standard signing with a keypair and “keyless signing” with Fulcio. If an attacker has access to the signature in OCI, they can manipulate cosign into believing the entry was stored in Rekor even though it wasn’t. The vulnerability has been patched in v1.5.2 of Cosign. The `signature` in the `signedEntryTimestamp` provided by Rekor is now compared to the `signature` that is being verified. If these don’t match, then an error is returned. If a valid bundle is copied to a different signature, verification should fail. Cosign output now only informs the user that certificates were verified if a certificate was in fact verified. There is currently no known workaround. |
2022-02-18 |
not yet calculated |
CVE-2022-23649
CONFIRM
MISC |
cryptomator — cryptomator
|
Cryptomator through 1.6.5 allows DYLIB injection because, although it has the flag 0x1000 for Hardened Runtime, it has the com.apple.security.cs.disable-library-validation and com.apple.security.cs.allow-dyld-environment-variables entitlements. An attacker can exploit this by creating a malicious .dylib file that can be executed via the DYLD_INSERT_LIBRARIES environment variable. |
2022-02-19 |
not yet calculated |
CVE-2022-25366
MISC
MISC |
cuppa_cms — cuppa_cms
|
The copy function of the file manager in Cuppa CMS v1.0 allows any file to be copied to the current directory, granting attackers read access to arbitrary files. |
2022-02-24 |
not yet calculated |
CVE-2022-25401
MISC |
| cybonet — pineapp_mail_relay |
Cybonet – PineApp Mail Relay Local File Inclusion. Attacker can send a request to : /manage/mailpolicymtm/log/eml_viewer/email.content.body.php?filesystem_path=ENCDODED PATH and by doing that, the attacker can read Local Files inside the server. |
2022-02-24 |
not yet calculated |
CVE-2022-22793
MISC |
cybonet — pineapp_mail_relay
|
Cybonet – PineApp Mail Relay Unauthenticated Sql Injection. Attacker can send a request to: /manage/emailrichment/userlist.php?CUSTOMER_ID_INNER=1 /admin/emailrichment/userlist.php?CUSTOMER_ID_INNER=1 /manage/emailrichment/usersunlist.php?CUSTOMER_ID_INNER=1 /admin/emailrichment/usersunlist.php?CUSTOMER_ID_INNER=1 and by doing that, the attacker can run Remote Code Execution in one liner. |
2022-02-24 |
not yet calculated |
CVE-2022-22794
MISC |
cyrus_sasl — cyrus_sasl
|
In Cyrus SASL 2.1.17 through 2.1.27 before 2.1.28, plugins/sql.c does not escape the password for a SQL INSERT or UPDATE statement. |
2022-02-24 |
not yet calculated |
CVE-2022-24407
MLIST
CONFIRM
MISC |
database_backup — database_backup
|
The Database Backup for WordPress plugin before 2.5.1 does not properly sanitise and escape the fragment parameter before using it in a SQL statement in the admin dashboard, leading to a SQL injection issue |
2022-02-21 |
not yet calculated |
CVE-2022-0255
MISC |
docker_desktop — docker_desktop
|
Docker Desktop before 4.5.1 on Windows allows attackers to move arbitrary files. NOTE: this issue exists because of an incomplete fix for CVE-2022-23774. |
2022-02-19 |
not yet calculated |
CVE-2022-25365
MISC |
dolibarr — dolibarr
|
Improper Access Control (IDOR) in GitHub repository dolibarr/dolibarr prior to 16.0. |
2022-02-23 |
not yet calculated |
CVE-2022-0731
MISC
CONFIRM |
dolibarr — dolibarr
|
Business Logic Errors in GitHub repository dolibarr/dolibarr prior to 16.0. |
2022-02-25 |
not yet calculated |
CVE-2022-0746
CONFIRM
MISC |
download_manager — download_manager
|
The Download Manager WordPress plugin before 3.2.34 does not sanitise and escape the package_ids parameter before using it in a SQL statement, leading to a SQL injection, which can also be exploited to cause a Reflected Cross-Site Scripting issue |
2022-02-21 |
not yet calculated |
CVE-2021-25069
CONFIRM
MISC |
drogonframework/drogon — drogonframework/drogon
|
This affects the package drogonframework/drogon before 1.7.5. The unsafe handling of file names during upload using HttpFile::save() method may enable attackers to write files to arbitrary locations outside the designated target folder. |
2022-02-21 |
not yet calculated |
CVE-2022-25297
CONFIRM
CONFIRM
CONFIRM |
duck — duck
|
duck before 0.10 did not properly handle loading of untrusted code from the current directory. |
2022-02-19 |
not yet calculated |
CVE-2016-1239
MISC |
duplicate_page_or_post — duplicate_page_or_post
|
The Duplicate Page or Post WordPress plugin before 1.5.1 does not have any authorisation and has a flawed CSRF check in the wpdevart_duplicate_post_parametrs_save_in_db AJAX action, allowing any authenticated users, such as subscriber to call it and change the plugin’s settings, or perform such attack via CSRF. Furthermore, due to the lack of escaping, this could lead to Stored Cross-Site Scripting issues |
2022-02-21 |
not yet calculated |
CVE-2021-25075
MISC |
ec-cube — ec-cube
|
EC-CUBE 3.0.0 to 3.0.18-p3 and EC-CUBE 4.0.0 to 4.1.1 improperly handle HTTP Host header values, which may lead a remote unauthenticated attacker to direct the vulnerable version of EC-CUBE to send an Email with some forged reissue-password URL to EC-CUBE users. |
2022-02-24 |
not yet calculated |
CVE-2022-25355
MISC
MISC |
ec-cube — ec-cube
|
Cross-site request forgery (CSRF) vulnerability in EC-CUBE plugin ‘Mail Magazine Management Plugin’ ver4.0.0 to 4.1.1 (for EC-CUBE 4 series) and ver1.0.0 to 1.0.4 (for EC-CUBE 3 series) allows a remote unauthenticated attacker to hijack the authentication of an administrator via a specially crafted page, and Mail Magazine Templates and/or transmitted history information may be deleted unintendedly. |
2022-02-24 |
not yet calculated |
CVE-2022-21179
MISC
MISC |
ectouch — ectouch
|
ECTouch v2 suffers from arbitrary file deletion due to insufficient filtering of the filename parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25098
MISC |
emerson — openenterprise
|
Emerson OpenEnterprise versions through 3.3.4 may allow an attacker to run an arbitrary commands with system privileges or perform remote code execution via a specific communication service. |
2022-02-24 |
not yet calculated |
CVE-2020-10640
CONFIRM |
emerson — openenterprise
|
Inadequate encryption may allow the passwords for Emerson OpenEnterprise versions through 3.3.4 user accounts to be obtained. |
2022-02-24 |
not yet calculated |
CVE-2020-10636
CONFIRM |
emerson — openenterprise
|
Inadequate folder security permissions in Emerson OpenEnterprise versions through 3.3.4 may allow modification of important configuration files, which could cause the system to fail or behave in an unpredictable manner. |
2022-02-24 |
not yet calculated |
CVE-2020-10632
CONFIRM |
| envoy — envoy |
Envoy is an open source edge and service proxy, designed for cloud-native applications. Sending a locally generated response must stop further processing of request or response data. Envoy tracks the amount of buffered request and response data and aborts the request if the amount of buffered data is over the limit by sending 413 or 500 responses. However when the buffer overflows while response is processed by the filter chain the operation may not be aborted correctly and result in accessing a freed memory block. If this happens Envoy will crash resulting in a denial of service. |
2022-02-22 |
not yet calculated |
CVE-2021-43825
MISC
CONFIRM |
| envoy — envoy |
Envoy is an open source edge and service proxy, designed for cloud-native applications. Envoy’s tls allows re-use when some cert validation settings have changed from their default configuration. The only workaround for this issue is to ensure that default tls settings are used. Users are advised to upgrade. |
2022-02-22 |
not yet calculated |
CVE-2022-21654
MISC
CONFIRM |
| envoy — envoy |
Envoy is an open source edge and service proxy, designed for cloud-native applications. The envoy common router will segfault if an internal redirect selects a route configured with direct response or redirect actions. This will result in a denial of service. As a workaround turn off internal redirects if direct response entries are configured on the same listener. |
2022-02-22 |
not yet calculated |
CVE-2022-21655
CONFIRM
MISC |
| envoy — envoy |
Envoy is an open source edge and service proxy, designed for cloud-native applications. In affected versions of Envoy a crash occurs when configured for :ref:`upstream tunneling <envoy_v3_api_field_extensions.filters.network.tcp_proxy.v3.TcpProxy.tunneling_config>` and the downstream connection disconnects while the the upstream connection or http/2 stream is still being established. There are no workarounds for this issue. Users are advised to upgrade. |
2022-02-22 |
not yet calculated |
CVE-2021-43826
CONFIRM
MISC |
envoy — envoy
|
Envoy is an open source edge and service proxy, designed for cloud-native applications. In affected versions Envoy does not restrict the set of certificates it accepts from the peer, either as a TLS client or a TLS server, to only those certificates that contain the necessary extendedKeyUsage (id-kp-serverAuth and id-kp-clientAuth, respectively). This means that a peer may present an e-mail certificate (e.g. id-kp-emailProtection), either as a leaf certificate or as a CA in the chain, and it will be accepted for TLS. This is particularly bad when combined with the issue described in pull request #630, in that it allows a Web PKI CA that is intended only for use with S/MIME, and thus exempted from audit or supervision, to issue TLS certificates that will be accepted by Envoy. As a result Envoy will trust upstream certificates that should not be trusted. There are no known workarounds to this issue. Users are advised to upgrade. |
2022-02-22 |
not yet calculated |
CVE-2022-21657
MISC
CONFIRM |
envoy — envoy
|
Envoy is an open source edge and service proxy, designed for cloud-native applications. The default_validator.cc implementation used to implement the default certificate validation routines has a “type confusion” bug when processing subjectAltNames. This processing allows, for example, an rfc822Name or uniformResourceIndicator to be authenticated as a domain name. This confusion allows for the bypassing of nameConstraints, as processed by the underlying OpenSSL/BoringSSL implementation, exposing the possibility of impersonation of arbitrary servers. As a result Envoy will trust upstream certificates that should not be trusted. |
2022-02-22 |
not yet calculated |
CVE-2022-21656
MISC
CONFIRM |
envoy — envoy
|
Envoy is an open source edge and service proxy, designed for cloud-native applications. In affected versions a crafted request crashes Envoy when a CONNECT request is sent to JWT filter configured with regex match. This provides a denial of service attack vector. The only workaround is to not use regex in the JWT filter. Users are advised to upgrade. |
2022-02-22 |
not yet calculated |
CVE-2021-43824
CONFIRM
MISC |
envoy — envoy
|
Envoy is an open source edge and service proxy, designed for cloud-native applications. When a cluster is deleted via Cluster Discovery Service (CDS) all idle connections established to endpoints in that cluster are disconnected. A recursion was introduced in the procedure of disconnecting idle connections that can lead to stack exhaustion and abnormal process termination when a cluster has a large number of idle connections. This infinite recursion causes Envoy to crash. Users are advised to upgrade. |
2022-02-22 |
not yet calculated |
CVE-2022-23606
MISC
CONFIRM |
eset — eset
|
Use-after-free in eset_rtp kernel module used in ESET products for Linux allows potential attacker to trigger denial-of-service condition on the system. |
2022-02-25 |
not yet calculated |
CVE-2022-0615
MISC |
essential_addons_for_elementor_life — essential_addons_for_elementor_life
|
The Essential Addons for Elementor Lite WordPress plugin is vulnerable to Cross-Site Scripting due to insufficient escaping and sanitization of the settings parameter found in the ~/includes/Traits/Helper.php file which allows attackers to inject arbitrary web scripts onto a pages that executes whenever a user clicks on a specially crafted link by an attacker. This affects versions up to and including 5.0.8. |
2022-02-24 |
not yet calculated |
CVE-2022-0683
MISC
MISC |
exportfeed — exportfeed
|
The ExportFeed WordPress plugin through 2.0.1.0 does not sanitise and escape the product_id POST parameter before using it in a SQL statement, leading to a SQL injection vulnerability exploitable by high privilege users |
2022-02-21 |
not yet calculated |
CVE-2021-4208
MISC |
eyesofnetwork — eyesofnetwork
|
An authenticated user can upload an XML file containing an XSS via the ITSM module of EyesOfNetwork 5.3.11, resulting in a stored XSS. |
2022-02-25 |
not yet calculated |
CVE-2022-24612
MISC |
| fatek_automation — fvdesigner |
The affected product is vulnerable to a stack-based buffer overflow while processing project files, which may allow an attacker to execute arbitrary code |
2022-02-25 |
not yet calculated |
CVE-2022-25170
MISC |
fatek_automation — fvdesigner
|
The affected product is vulnerable to an out-of-bounds read while processing project files, which allows an attacker to craft a project file that would allow arbitrary code execution. |
2022-02-25 |
not yet calculated |
CVE-2022-21209
MISC |
fatek_automation — fvdesigner
|
The affected product is vulnerable to an out-of-bounds write while processing project files, which allows an attacker to craft a project file that would allow arbitrary code execution. |
2022-02-25 |
not yet calculated |
CVE-2022-23985
MISC |
feedwordpress — feedwordpress
|
The FeedWordPress plugin before 2022.0123 is affected by a Reflected Cross-Site Scripting (XSS) within the “visibility” parameter. |
2022-02-21 |
not yet calculated |
CVE-2021-25055
CONFIRM
MISC |
fgribreau — node-request-retry
|
Exposure of Sensitive Information to an Unauthorized Actor in GitHub repository fgribreau/node-request-retry prior to 7.0.0. |
2022-02-23 |
not yet calculated |
CVE-2022-0654
MISC
CONFIRM |
filecloud — filecloud
|
All versions of FileCloud prior to 21.3 are vulnerable to user enumeration. The vulnerability exists in the parameter “path” passing “/SHARED/<username>”. A malicious actor could identify the existence of users by requesting share information on specified share paths. |
2022-02-24 |
not yet calculated |
CVE-2022-24633
MISC |
firstmall — firstmall
|
This issues due to insufficient verification of the various input values from user’s input. The vulnerability allows remote attackers to execute malicious code in Firstmall via navercheckout_add function. |
2022-02-25 |
not yet calculated |
CVE-2021-26617
MISC |
five_start_business_profile_schema — five_start_business_profile_schema
|
The Five Star Business Profile and Schema WordPress plugin before 2.1.7 does not have any authorisation and CSRF in its bpfwp_welcome_add_contact_page and bpfwp_welcome_set_contact_information AJAX action, allowing any authenticated users, such as subscribers, to call them. Furthermore, due to the lack of sanitisation, it also lead to Stored Cross-Site Scripting issues |
2022-02-21 |
not yet calculated |
CVE-2021-25060
MISC |
float — float
|
The Float menu WordPress plugin before 4.3.1 does not have CSRF check in place when deleting menu, which could allow attackers to make a logged in admin delete them via a CSRF attack |
2022-02-21 |
not yet calculated |
CVE-2022-0313
CONFIRM
MISC |
fortiguard — fortios
|
Failure to sanitize input in the SSL VPN web portal of FortiOS 5.2.10 through 5.2.15, 5.4.0 through 5.4.13, 5.6.0 through 5.6.14, 6.0.0 through 6.0.12, 6.2.0 through 6.2.7, 6.4.0 through 6.4.4; and FortiProxy 1.2.0 through 1.2.9, 2.0.0 through 2.0.1 may allow a remote unauthenticated attacker to perform a reflected Cross-site Scripting (XSS) attack by sending a request to the error page with malicious GET parameters. |
2022-02-24 |
not yet calculated |
CVE-2021-26092
CONFIRM |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader Foxit reader 11.0.1.0719 macOS. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the OnMouseExit method. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-14848. |
2022-02-18 |
not yet calculated |
CVE-2022-24356
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of Doc objects. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-16115. |
2022-02-18 |
not yet calculated |
CVE-2022-24368
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JP2 images. Crafted data in a JP2 image can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-16087. |
2022-02-18 |
not yet calculated |
CVE-2022-24369
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of Annotation objects. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15743. |
2022-02-18 |
not yet calculated |
CVE-2022-24357
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of AcroForms. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15853. |
2022-02-18 |
not yet calculated |
CVE-2022-24366
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of AcroForms. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15852. |
2022-02-18 |
not yet calculated |
CVE-2022-24365
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of Doc objects. By performing actions in JavaScript, an attacker can trigger a read past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15703. |
2022-02-18 |
not yet calculated |
CVE-2022-24358
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of AcroForms. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15877. |
2022-02-18 |
not yet calculated |
CVE-2022-24367
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of AcroForms. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15987. |
2022-02-18 |
not yet calculated |
CVE-2022-24362
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of Annotation objects. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15861. |
2022-02-18 |
not yet calculated |
CVE-2022-24363
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JPEG2000 images. The issue results from the lack of proper validation of user-supplied data, which can result in a write past the end of an allocated structure. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15811. |
2022-02-18 |
not yet calculated |
CVE-2022-24361
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of Doc objects. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15744. |
2022-02-18 |
not yet calculated |
CVE-2022-24360
MISC
MISC |
| foxit — pdf_reader |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of Doc objects. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15851. |
2022-02-18 |
not yet calculated |
CVE-2022-24364
MISC
MISC |
foxit — pdf_reader
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of Doc objects. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15702. |
2022-02-18 |
not yet calculated |
CVE-2022-24359
MISC
MISC |
foxit — pdf_reader
|
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Foxit PDF Reader Foxit reader 11.0.1.0719 macOS. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the handling of XFA forms. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated object. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-14819. |
2022-02-18 |
not yet calculated |
CVE-2022-24370
MISC
MISC |
foxit — pdf_reader
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Foxit PDF Reader 11.1.0.52543. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JPEG2000 images. The issue results from the lack of proper validation of user-supplied data, which can result in a read past the end of an allocated structure. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15812. |
2022-02-18 |
not yet calculated |
CVE-2022-24971
MISC
MISC |
fuel-cms — fuel-cms
|
A Cross Site Scripting (XSS) vulnerability exists in FUEL-CMS 1.5.1 in the Assets page via an SVG file. |
2022-02-24 |
not yet calculated |
CVE-2021-44607
MISC |
fuschia — fuschia
|
An issue exists in Fuchsia where VMO data can be modified through access to copy-on-write snapshots. A local attacker could modify objects in the VMO that they do not have permission to. We recommend upgrading past commit d97c05d2301799ed585620a9c5c739d36e7b5d3d or any of the listed versions. |
2022-02-25 |
not yet calculated |
CVE-2022-0247
CONFIRM |
givewp — givewp
|
The GiveWP WordPress plugin before 2.17.3 does not escape the s parameter before outputting it back in an attribute in the Donation Forms dashboard, leading to a Reflected Cross-Site Scripting |
2022-02-21 |
not yet calculated |
CVE-2021-25100
CONFIRM
MISC |
givewp — givewp
|
The GiveWP WordPress plugin before 2.17.3 does not sanitise and escape the form_id parameter before outputting it back in the response of an unauthenticated request via the give_checkout_login AJAX action, leading to a Reflected Cross-Site Scripting |
2022-02-21 |
not yet calculated |
CVE-2021-25099
MISC
CONFIRM |
givewp — givewp
|
The GiveWP WordPress plugin before 2.17.3 does not escape the json parameter before outputting it back in an attribute in the Import admin dashboard, leading to a Reflected Cross-Site Scripting |
2022-02-21 |
not yet calculated |
CVE-2022-0252
CONFIRM
MISC |
| google — fscrypt |
The PAM module for fscrypt doesn’t adequately validate fscrypt metadata files, allowing users to create malicious metadata files that prevent other users from logging in. A local user can cause a denial of service by creating a fscrypt metadata file that prevents other users from logging into the system. We recommend upgrading to version 0.3.3 or above |
2022-02-25 |
not yet calculated |
CVE-2022-25327
CONFIRM |
| google — fscrypt |
fscrypt through v0.3.2 creates a world-writable directory by default when setting up a filesystem, allowing unprivileged users to exhaust filesystem space. We recommend upgrading to fscrypt 0.3.3 or above and adjusting the permissions on existing fscrypt metadata directories where applicable. |
2022-02-25 |
not yet calculated |
CVE-2022-25326
CONFIRM |
google — fscrypt
|
The bash_completion script for fscrypt allows injection of commands via crafted mountpoint paths, allowing privilege escalation under a specific set of circumstances. A local user who has control over mountpoint paths could potentially escalate their privileges if they create a malicious mountpoint path and if the system administrator happens to be using the fscrypt bash completion script to complete mountpoint paths. We recommend upgrading to version 0.3.3 or above |
2022-02-25 |
not yet calculated |
CVE-2022-25328
CONFIRM |
harmonyos — harmonyos
|
The interface of a certain HarmonyOS module has a UAF vulnerability. Successful exploitation of this vulnerability may lead to information leakage. |
2022-02-25 |
not yet calculated |
CVE-2021-22478
MISC |
harmonyos — harmonyos
|
The interface of a certain HarmonyOS module has an integer overflow vulnerability. Successful exploitation of this vulnerability may lead to heap memory overflow. |
2022-02-25 |
not yet calculated |
CVE-2021-22480
MISC |
harmonyos — harmonyos
|
The interface of a certain HarmonyOS module has an invalid address access vulnerability. Successful exploitation of this vulnerability may lead to kernel crash. |
2022-02-25 |
not yet calculated |
CVE-2021-22479
MISC |
hashicorp — consul_and_consul_enterprise
|
HashiCorp Consul and Consul Enterprise 1.8.0 through 1.9.14, 1.10.7, and 1.11.2 has Uncontrolled Resource Consumption. |
2022-02-24 |
not yet calculated |
CVE-2022-24687
MISC
MISC |
hashicorp — terraform_enterprise
|
HashiCorp Terraform Enterprise before 202202-1 inserts Sensitive Information into a Log File. |
2022-02-25 |
not yet calculated |
CVE-2022-25374
MISC
MISC |
| hcl_software — sametime_for_android |
“Sametime Android PathTraversal Vulnerability” |
2022-02-21 |
not yet calculated |
CVE-2021-27753
MISC |
| hcl_software — sametime_for_android |
“Sametime Android potential path traversal vulnerability when using File class” |
2022-02-21 |
not yet calculated |
CVE-2021-27755
MISC |
header_footer_code_manager — header_footer_code_manager
|
The Header Footer Code Manager plugin <= 1.1.16 for WordPress is vulnerable to Reflected Cross-Site Scripting (XSS) via the $_REQUEST[‘page’] parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-0710
MISC |
| hms — hms |
An incorrect access control issue in HMS v1.0 allows unauthenticated attackers to read and modify all PHP files. |
2022-02-24 |
not yet calculated |
CVE-2022-25402
MISC |
hms — hms
|
HMS v1.0 was discovered to contain a SQL injection vulnerability via the component admin.php. |
2022-02-24 |
not yet calculated |
CVE-2022-25403
MISC |
|
home_owners_collection_management_system — home_owners_collection_management_system
|
Home Owners Collection Management System v1.0 was discovered to contain a SQL injection vulnerability via the id parameter in /members/view_member.php. |
2022-02-26 |
not yet calculated |
CVE-2022-25096
MISC |
|
home_owners_collection_management_system — home_owners_collection_management_system
|
Home Owners Collection Management System v1.0 allows unauthenticated attackers to compromise user accounts via a crafted POST request. |
2022-02-26 |
not yet calculated |
CVE-2022-25095
MISC |
|
home_owners_collection_management_system — home_owners_collection_management_system
|
Home Owners Collection Management System v1.0 was discovered to contain a remote code execution (RCE) vulnerability via the parameter “cover” in SystemSettings.php. |
2022-02-26 |
not yet calculated |
CVE-2022-25094
MISC |
| homebrew — mruby |
Out-of-bounds Read in Homebrew mruby prior to 3.2. |
2022-02-19 |
not yet calculated |
CVE-2022-0630
MISC
CONFIRM |
homebrew — mruby
|
NULL Pointer Dereference in Homebrew mruby prior to 3.2. |
2022-02-19 |
not yet calculated |
CVE-2022-0632
CONFIRM
MISC |
| honeywell — devices |
Honeywell HDZP252DI 1.00.HW02.4 and HBW2PER1 1.000.HW01.3 devices allow command spoofing (for camera control) after ARP cache poisoning has been achieved. |
2022-02-24 |
not yet calculated |
CVE-2021-39364
MISC
MISC
CONFIRM |
honeywell — devices
|
Honeywell HDZP252DI 1.00.HW02.4 and HBW2PER1 1.000.HW01.3 devices allow a video replay attack after ARP cache poisoning has been achieved. |
2022-02-24 |
not yet calculated |
CVE-2021-39363
MISC
MISC
CONFIRM |
| horizontcms — horizontcms |
A vulnerability in the component /templates/install.php of WBCE CMS v1.5.2 allows attackers to execute arbitrary code via a crafted PHP file. |
2022-02-24 |
not yet calculated |
CVE-2022-25101
MISC |
horizontcms — horizontcms
|
HorizontCMS v1.0.0-beta.2 was discovered to contain an arbitrary file download vulnerability via the component /admin/file-manager/. |
2022-02-24 |
not yet calculated |
CVE-2022-25104
MISC |
| hospital_patient_record_management_system — hospital_patient_record_management_system |
Hospital Patient Record Management System v1.0 was discovered to contain a SQL injection vulnerability via the id parameter in /admin/doctors/view_doctor.php. |
2022-02-24 |
not yet calculated |
CVE-2022-25003
MISC |
hospital_patient_record_management_system — hospital_patient_record_management_system
|
A local file inclusion in Hospital Patient Record Management System v1.0 allows attackers to execute arbitrary code via a crafted PHP file. |
2022-02-24 |
not yet calculated |
CVE-2022-24232
MISC |
hospital_patient_record_management_system — hospital_patient_record_management_system
|
Hospital Patient Record Management System v1.0 was discovered to contain a SQL injection vulnerability via the id parameter in /admin/doctors/manage_doctor.php. |
2022-02-24 |
not yet calculated |
CVE-2022-25004
MISC |
hpe — ilo_amplifier_pack
|
Multiple buffer overflow security vulnerabilities have been identified in HPE iLO Amplifier Pack version(s): Prior to 2.12. These vulnerabilities could be exploited by a highly privileged user to remotely execute code that could lead to a loss of confidentiality, integrity, and availability. HPE has provided a software update to resolve this vulnerability in HPE iLO Amplifier Pack. |
2022-02-24 |
not yet calculated |
CVE-2021-29220
MISC |
hpe — integrated_lights-out_4_firmware
|
A potential remote host header injection security vulnerability has been identified in HPE Integrated Lights-Out 4 (iLO 4) firmware version(s): Prior to 2.60. This vulnerability could be remotely exploited to allow an attacker to supply invalid input to the iLO 4 webserver, causing it to respond with a redirect to an attacker-controlled domain. HPE has provided a firmware update to resolve this vulnerability in HPE Integrated Lights-Out 4 (iLO 4). |
2022-02-24 |
not yet calculated |
CVE-2022-23701
MISC |
hpe — oneview_global_dashboard
|
A remote URL redirection vulnerability was discovered in HPE OneView Global Dashboard version(s): Prior to 2.5. HPE has provided a software update to resolve this vulnerability in HPE OneView Global Dashboard. |
2022-02-24 |
not yet calculated |
CVE-2021-29217
MISC |
hpe — oneview_global_dashboard
|
A remote cross-site scripting vulnerability was discovered in HPE OneView Global Dashboard version(s): Prior to 2.5. HPE has provided a software update to resolve this vulnerability in HPE OneView Global Dashboard. |
2022-02-24 |
not yet calculated |
CVE-2021-29216
MISC |
htmldoc — htmldoc
|
A flaw was found in htmldoc in v1.9.12. Heap buffer overflow in pspdf_prepare_page(),in ps-pdf.cxx may lead to execute arbitrary code and denial of service. |
2022-02-24 |
not yet calculated |
CVE-2021-26252
MISC |
huawei — devices
|
The laser command injection vulnerability exists on AIS-BW80H-00 versions earlier than AIS-BW80H-00 9.0.3.4(H100SP13C00). The devices cannot effectively defend against external malicious interference. Attackers need the device to be visually exploitable and successful triggering of this vulnerability could execute voice commands on the device. |
2022-02-25 |
not yet calculated |
CVE-2021-40043
MISC |
huawei — products
|
Some Huawei products have an integer overflow vulnerability. Successful exploitation of this vulnerability may lead to kernel crash. |
2022-02-25 |
not yet calculated |
CVE-2021-22441
MISC |
huawei — smartphones
|
There is a DoS vulnerability in smartphones. Successful exploitation of this vulnerability may affect service availability. |
2022-02-25 |
not yet calculated |
CVE-2021-22489
MISC
MISC |
huawei — smartphones
|
There is an improper verification vulnerability in smartphones. Successful exploitation of this vulnerability may cause unauthorized read and write of some files. |
2022-02-25 |
not yet calculated |
CVE-2021-22448
MISC |
huawei — smartphones
|
There is a DoS vulnerability in smartphones. Successful exploitation of this vulnerability may affect service integrity. |
2022-02-25 |
not yet calculated |
CVE-2021-37027
MISC
MISC |
huawei — smartphones
|
There is a software integer overflow leading to a TOCTOU condition in smartphones. Successful exploitation of this vulnerability may cause random address access. |
2022-02-25 |
not yet calculated |
CVE-2021-22437
MISC |
huawei — smartphones
|
There is a memory address out of bounds vulnerability in smartphones. Successful exploitation of this vulnerability may cause malicious code to be executed. |
2022-02-25 |
not yet calculated |
CVE-2021-22434
MISC
MISC |
huawei — smartphones
|
There is a vulnerability when configuring permission isolation in smartphones. Successful exploitation of this vulnerability may cause out-of-bounds access. |
2022-02-25 |
not yet calculated |
CVE-2021-22432
MISC
MISC |
huawei — smartphones
|
There is a memory address out of bounds in smartphones. Successful exploitation of this vulnerability may cause malicious code to be executed. |
2022-02-25 |
not yet calculated |
CVE-2021-22433
MISC
MISC |
huawei — smartphones
|
There is a memory address out of bounds in smartphones. Successful exploitation of this vulnerability may cause malicious code to be executed. |
2022-02-25 |
not yet calculated |
CVE-2021-22429
MISC
MISC |
huawei — smartphones
|
There is a code injection vulnerability in smartphones. Successful exploitation of this vulnerability may affect service confidentiality. |
2022-02-25 |
not yet calculated |
CVE-2021-22395
MISC
MISC |
huawei — smartphones
|
There is a memory address out of bounds in smartphones. Successful exploitation of this vulnerability may cause malicious code to be executed. |
2022-02-25 |
not yet calculated |
CVE-2021-22426
MISC
MISC |
huawei — smartphones
|
There is an improper verification vulnerability in smartphones. Successful exploitation of this vulnerability may cause integer overflows. |
2022-02-25 |
not yet calculated |
CVE-2021-22319
MISC
MISC |
huawei — smartphones
|
There is a logic bypass vulnerability in smartphones. Successful exploitation of this vulnerability may cause code injection. |
2022-02-25 |
not yet calculated |
CVE-2021-22430
MISC
MISC |
huawei — smartphones
|
There is a vulnerability when configuring permission isolation in smartphones. Successful exploitation of this vulnerability may cause out-of-bounds access. |
2022-02-25 |
not yet calculated |
CVE-2021-22431
MISC
MISC |
huawei — smartphones
|
There is a buffer overflow vulnerability in smartphones. Successful exploitation of this vulnerability may cause DoS of the apps during Multi-Screen Collaboration. |
2022-02-25 |
not yet calculated |
CVE-2021-22394
MISC
MISC |
| huawei — wallet |
There is an improper permission management vulnerability in the Wallet apps. Successful exploitation of this vulnerability may affect service confidentiality. |
2022-02-25 |
not yet calculated |
CVE-2021-37103
MISC |
ibm — aix
|
IBM AIX 7.1, 7.2, 7.3, and VIOS 3.1 could allow a non-privileged local user to exploit a vulnerability in the AIX kernel to cause a denial of service. IBM X-Force ID: 213073. |
2022-02-24 |
not yet calculated |
CVE-2021-38995
CONFIRM
XF |
ibm — aix
|
IBM AIX 7.1, 7.2, 7.3, and VIOS 3.1 could allow a non-privileged local user to exploit a vulnerability in the AIX kernel to cause a denial of service. IBM X-Force ID: 213072. |
2022-02-24 |
not yet calculated |
CVE-2021-38994
CONFIRM
XF |
ibm — aix
|
IBM AIX 7.1, 7.2, 7.3, and VIOS 3.1 could allow a non-privileged local user to exploit a vulnerability in the smbcd daemon to cause a denial of service. IBM X-Force ID: 212962. |
2022-02-25 |
not yet calculated |
CVE-2021-38993
XF
CONFIRM |
ibm — planning_analytics
|
IBM Planning Analytics 2.0 is vulnerable to a Remote File Include (RFI) attack. User input could be passed into file include commands and the web application could be tricked into including remote files with malicious code. IBM X-Force ID: 216891. |
2022-02-21 |
not yet calculated |
CVE-2022-22308
XF
CONFIRM |
| ibm — sterling |
IBM Sterling External Authentication Server and IBM Sterling Secure Proxy 6.0.3.0, 6.0.2.0, and 3.4.3.2 could allow a remote user to consume resources causing a denial of service due to a resource leak. IBM X-Force ID: 219395. |
2022-02-23 |
not yet calculated |
CVE-2022-22336
XF
CONFIRM |
ibm — sterling
|
IBM Sterling Secure Proxy 6.0.3.0, 6.0.2.0, and 3.4.3.2 and IBM Sterling External Authentication Server are vulnerable a buffer overflow, due to the Jetty based GUI in the Secure Zone not properly validating the sizes of the form content and/or HTTP headers submitted. A local attacker positioned inside the Secure Zone could submit a specially crafted HTTP request to disrupt service. IBM X-Force ID: 219133. |
2022-02-23 |
not yet calculated |
CVE-2022-22333
XF
CONFIRM |
ibm — sterling
|
IBM Sterling External Authentication Server 3.4.3.2, 6.0.2.0, and 6.0.3.0 is vulnerable to path traversals, due to not properly validating RESTAPI configuration data. An authorized user could import invalid data which could be used for an attack. IBM X-Force ID: 220144. |
2022-02-24 |
not yet calculated |
CVE-2022-22349
XF
CONFIRM |
ibm — websphere_application_server
|
IBM WebSphere Application Server 9.0 and IBM WebSphere Application Server Liberty 17.0.0.3 through 22.0.0.2 could allow a remote attacker to hijack the clicking action of the victim. By persuading a victim to visit a malicious Web site, a remote attacker could exploit this vulnerability to hijack the victim’s click actions and possibly launch further attacks against the victim. IBM X-Force ID: 213968. |
2022-02-24 |
not yet calculated |
CVE-2021-39038
CONFIRM
XF |
image_photo_gallery_final_tiles_grid — image_photo_gallery_final_tiles_grid
|
The Image Photo Gallery Final Tiles Grid WordPress plugin before 3.5.3 does not sanitise and escape the Description field when editing a gallery, allowing users with a role as low as contributor to perform Cross-Site Scripting attacks against other users having access to the gallery dashboard |
2022-02-21 |
not yet calculated |
CVE-2022-0186
MISC |
imagemagick — imagemagick
|
A heap-based buffer overflow vulnerability was found in ImageMagick in versions prior to 7.0.11-14 in ReadTIFFImage() in coders/tiff.c. This issue is due to an incorrect setting of the pixel array size, which can lead to a crash and segmentation fault. |
2022-02-24 |
not yet calculated |
CVE-2021-3610
MISC
MISC |
imagemagick — imagemagick
|
A NULL pointer dereference flaw was found in ImageMagick in versions prior to 7.0.10-31 in ReadSVGImage() in coders/svg.c. This issue is due to not checking the return value from libxml2’s xmlCreatePushParserCtxt() and uses the value directly, which leads to a crash and segmentation fault. |
2022-02-24 |
not yet calculated |
CVE-2021-3596
MISC
MISC |
istio — istio
|
Istio is an open platform to connect, manage, and secure microservices. In affected versions the Istio control plane, `istiod`, is vulnerable to a request processing error, allowing a malicious attacker that sends a specially crafted message which results in the control plane crashing. This endpoint is served over TLS port 15012, but does not require any authentication from the attacker. For simple installations, Istiod is typically only reachable from within the cluster, limiting the blast radius. However, for some deployments, especially [multicluster](https://istio.io/latest/docs/setup/install/multicluster/primary-remote/) topologies, this port is exposed over the public internet. There are no effective workarounds, beyond upgrading. Limiting network access to Istiod to the minimal set of clients can help lessen the scope of the vulnerability to some extent. |
2022-02-22 |
not yet calculated |
CVE-2022-23635
MISC
MISC
CONFIRM |
jetbrains — hub
|
In JetBrains Hub before 2021.1.13890, integration with JetBrains Account exposed an API key with excessive permissions. |
2022-02-25 |
not yet calculated |
CVE-2022-24327
MISC
MISC |
jetbrains — hub
|
JetBrains Hub before 2021.1.14276 was vulnerable to reflected XSS. |
2022-02-25 |
not yet calculated |
CVE-2022-25259
MISC
MISC |
jetbrains — hub
|
JetBrains Hub before 2021.1.14276 was vulnerable to blind Server-Side Request Forgery (SSRF). |
2022-02-25 |
not yet calculated |
CVE-2022-25260
MISC
MISC |
jetbrains — hub
|
In JetBrains Hub before 2021.1.13956, an unprivileged user could perform DoS. |
2022-02-25 |
not yet calculated |
CVE-2022-24328
MISC
MISC |
jetbrains — hub
|
In JetBrains Hub before 2022.1.14434, SAML request takeover was possible. |
2022-02-25 |
not yet calculated |
CVE-2022-25262
MISC
MISC |
jetbrains — intellij_idea
|
In JetBrains IntelliJ IDEA before 2021.3.1, local code execution via RLO (Right-to-Left Override) characters was possible. |
2022-02-25 |
not yet calculated |
CVE-2022-24346
MISC
MISC |
jetbrains — intellij_idea
|
In JetBrains IntelliJ IDEA before 2021.2.4, local code execution (without permission from a user) upon opening a project was possible. |
2022-02-25 |
not yet calculated |
CVE-2022-24345
MISC
MISC |
jetbrains — kotlin
|
In JetBrains Kotlin before 1.6.0, it was not possible to lock dependencies for Multiplatform Gradle Projects. |
2022-02-25 |
not yet calculated |
CVE-2022-24329
MISC
MISC |
jetbrains — multiple_products
|
JetBrains IntelliJ IDEA 2021.3.1 Preview, IntelliJ IDEA 2021.3.1 RC, PyCharm Professional 2021.3.1 RC, GoLand 2021.3.1, PhpStorm 2021.3.1 Preview, PhpStorm 2021.3.1 RC, RubyMine 2021.3.1 Preview, RubyMine 2021.3.1 RC, CLion 2021.3.1, WebStorm 2021.3.1 Preview, and WebStorm 2021.3.1 RC (used as Remote Development backend IDEs) bind to the 0.0.0.0 IP address. The fixed versions are: IntelliJ IDEA 2021.3.1, PyCharm Professional 2021.3.1, GoLand 2021.3.2, PhpStorm 2021.3.1 (213.6461.83), RubyMine 2021.3.1, CLion 2021.3.2, and WebStorm 2021.3.1. |
2022-02-25 |
not yet calculated |
CVE-2021-45977
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.2.1, a redirection to an external site was possible. |
2022-02-25 |
not yet calculated |
CVE-2022-24330
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.2.1, an unauthenticated attacker can cancel running builds via an XML-RPC request to the TeamCity server. |
2022-02-25 |
not yet calculated |
CVE-2022-24336
MISC
MISC |
jetbrains — teamcity
|
JetBrains TeamCity before 2021.2.3 was vulnerable to OS command injection in the Agent Push feature configuration. |
2022-02-25 |
not yet calculated |
CVE-2022-25263
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.2.1, the Agent Push feature allowed selection of any private key on the server. |
2022-02-25 |
not yet calculated |
CVE-2022-24334
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.2, health items of pull requests were shown to users who lacked appropriate permissions. |
2022-02-25 |
not yet calculated |
CVE-2022-24337
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.2.3, environment variables of the “password” type could be logged in some cases. |
2022-02-25 |
not yet calculated |
CVE-2022-25264
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.1.4, GitLab authentication impersonation was possible. |
2022-02-25 |
not yet calculated |
CVE-2022-24331
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.2.1, XXE during the parsing of the configuration file was possible. |
2022-02-25 |
not yet calculated |
CVE-2022-24340
MISC
MISC |
jetbrains — teamcity
|
JetBrains TeamCity before 2021.2 was vulnerable to a Time-of-check/Time-of-use (TOCTOU) race-condition attack in agent registration via XML-RPC. |
2022-02-25 |
not yet calculated |
CVE-2022-24335
MISC
MISC |
jetbrains — teamcity
|
JetBrains TeamCity before 2021.2.2 was vulnerable to reflected XSS. |
2022-02-25 |
not yet calculated |
CVE-2022-25261
MISC
MISC |
jetbrains — teamcity
|
JetBrains TeamCity before 2021.2.1 was vulnerable to stored XSS. |
2022-02-25 |
not yet calculated |
CVE-2022-24339
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.2.1, editing a user account to change its password didn’t terminate sessions of the edited user. |
2022-02-25 |
not yet calculated |
CVE-2022-24341
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.2, a logout action didn’t remove a Remember Me cookie. |
2022-02-25 |
not yet calculated |
CVE-2022-24332
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.2.1, URL injection leading to CSRF was possible. |
2022-02-25 |
not yet calculated |
CVE-2022-24342
MISC
MISC |
jetbrains — teamcity
|
JetBrains TeamCity before 2021.2.1 was vulnerable to reflected XSS. |
2022-02-25 |
not yet calculated |
CVE-2022-24338
MISC
MISC |
jetbrains — teamcity
|
In JetBrains TeamCity before 2021.2, blind SSRF via an XML-RPC call was possible. |
2022-02-25 |
not yet calculated |
CVE-2022-24333
MISC
MISC |
| jetbrains — youtrack |
In JetBrains YouTrack before 2021.4.31698, a custom logo could be set by a user who has read-only permissions. |
2022-02-25 |
not yet calculated |
CVE-2022-24343
MISC
MISC |
jetbrains — youtrack
|
JetBrains YouTrack before 2021.4.40426 was vulnerable to SSTI (Server-Side Template Injection) via FreeMarker templates. |
2022-02-25 |
not yet calculated |
CVE-2022-24442
MISC
MISC |
jetbrains — youtrack
|
JetBrains YouTrack before 2021.4.31698 was vulnerable to stored XSS on the Notification templates page. |
2022-02-25 |
not yet calculated |
CVE-2022-24344
MISC
MISC |
jetbrains — youtrack
|
JetBrains YouTrack before 2021.4.36872 was vulnerable to stored XSS via a project icon. |
2022-02-25 |
not yet calculated |
CVE-2022-24347
MISC
MISC |
jquery-upload-file — jquery-upload-file
|
A cross-site scripting (XSS) vulnerability in the fileNameStr parameter of jQuery-Upload-File v4.0.11 allows attackers to execute arbitrary web scripts or HTML via a crafted file with a Javascript payload in the file name. |
2022-02-25 |
not yet calculated |
CVE-2021-37504
MISC
MISC
MISC
MISC
MISC
MISC
MISC |
karma — karma
|
The package karma before 6.3.16 are vulnerable to Open Redirect due to missing validation of the return_url query parameter. |
2022-02-25 |
not yet calculated |
CVE-2021-23495
CONFIRM
CONFIRM
CONFIRM |
kde_kcron — kde_kcron
|
KDE KCron through 21.12.2 uses a temporary file in /tmp when saving, but reuses the filename during an editing session. Thus, someone watching it be created the first time could potentially intercept the file the following time, enabling that person to run unauthorized commands. |
2022-02-26 |
not yet calculated |
CVE-2022-24986
MISC
MISC |
kuka.sim — pro
|
Simulation models for KUKA.Sim Pro version 3.1 are hosted by a server maintained by KUKA. When these devices request a model, the server transmits the model in plaintext. |
2022-02-24 |
not yet calculated |
CVE-2020-10635
CONFIRM |
laravel — fortify
|
Laravel Fortify before 1.11.1 allows reuse within a short time window, thus calling into question the “OT” part of the “TOTP” concept. |
2022-02-24 |
not yet calculated |
CVE-2022-25838
MISC |
libreoffice — libreoffice
|
LibreOffice supports digital signatures of ODF documents and macros within documents, presenting visual aids that no alteration of the document occurred since the last signing and that the signature is valid. An Improper Certificate Validation vulnerability in LibreOffice allowed an attacker to create a digitally signed ODF document, by manipulating the documentsignatures.xml or macrosignatures.xml stream within the document to contain both “X509Data” and “KeyValue” children of the “KeyInfo” tag, which when opened caused LibreOffice to verify using the “KeyValue” but to report verification with the unrelated “X509Data” value. This issue affects: The Document Foundation LibreOffice 7.2 versions prior to 7.2.5. |
2022-02-24 |
not yet calculated |
CVE-2021-25636
MISC |
libsixel — libsixel
|
In libsixel 1.8.6, sixel_encoder_output_without_macro (called from sixel_encoder_encode_frame in encoder.c) has a double free. |
2022-02-19 |
not yet calculated |
CVE-2021-46700
MISC |
libxml — libxml
|
valid.c in libxml2 before 2.9.13 has a use-after-free of ID and IDREF attributes. |
2022-02-26 |
not yet calculated |
CVE-2022-23308
MISC
CONFIRM |
limesurvey — limesurvey
|
A Remote Code Execution (RCE) vulnerabilty exists in LimeSurvey 5.2.4 via the upload and install plugins function, which could let a remote malicious user upload an arbitrary PHP code file. |
2022-02-24 |
not yet calculated |
CVE-2021-44967
MISC
MISC |
linux — linux+kernel
|
An issue was discovered in drivers/usb/gadget/function/rndis.c in the Linux kernel before 5.16.10. The RNDIS USB gadget lacks validation of the size of the RNDIS_MSG_SET command. Attackers can obtain sensitive information from kernel memory. |
2022-02-20 |
not yet calculated |
CVE-2022-25375
MISC
MISC
MISC
MLIST |
linux — linux_kernel
|
net/netfilter/nf_dup_netdev.c in the Linux kernel 5.4 through 5.6.10 allows local users to gain privileges because of a heap out-of-bounds write. This is related to nf_tables_offload. |
2022-02-24 |
not yet calculated |
CVE-2022-25636
MISC
MISC
MLIST |
linux — linux_kernel
|
An issue was discovered in the Linux kernel through 5.16.11. The mixed IPID assignment method with the hash-based IPID assignment policy allows an off-path attacker to inject data into a victim’s TCP session or terminate that session. |
2022-02-26 |
not yet calculated |
CVE-2020-36516
MISC |
liveconfig — liveconfig
|
A Stored XSS issue exists in the admin/users user administration form in LiveConfig 2.12.2. |
2022-02-18 |
not yet calculated |
CVE-2021-40840
MISC
MISC |
| mariadb — connect |
MariaDB CONNECT Storage Engine Stack-based Buffer Overflow Privilege Escalation Vulnerability. This vulnerability allows local attackers to escalate privileges on affected installations of MariaDB. Authentication is required to exploit this vulnerability. The specific flaw exists within the processing of SQL queries. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a fixed-length stack-based buffer. An attacker can leverage this vulnerability to escalate privileges and execute arbitrary code in the context of the service account. Was ZDI-CAN-16191. |
2022-02-18 |
not yet calculated |
CVE-2022-24048
MISC
MISC |
| mariadb — connect |
MariaDB CONNECT Storage Engine Use-After-Free Privilege Escalation Vulnerability. This vulnerability allows local attackers to escalate privileges on affected installations of MariaDB. Authentication is required to exploit this vulnerability. The specific flaw exists within the processing of SQL queries. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to escalate privileges and execute arbitrary code in the context of the service account. Was ZDI-CAN-16207. |
2022-02-18 |
not yet calculated |
CVE-2022-24050
MISC
MISC |
| mariadb — connect |
MariaDB CONNECT Storage Engine Format String Privilege Escalation Vulnerability. This vulnerability allows local attackers to escalate privileges on affected installations of MariaDB. Authentication is required to exploit this vulnerability. The specific flaw exists within the processing of SQL queries. The issue results from the lack of proper validation of a user-supplied string before using it as a format specifier. An attacker can leverage this vulnerability to escalate privileges and execute arbitrary code in the context of the service account. Was ZDI-CAN-16193. |
2022-02-18 |
not yet calculated |
CVE-2022-24051
MISC
MISC |
mariadb — connect
|
MariaDB CONNECT Storage Engine Heap-based Buffer Overflow Privilege Escalation Vulnerability. This vulnerability allows local attackers to escalate privileges on affected installations of MariaDB. Authentication is required to exploit this vulnerability. The specific flaw exists within the processing of SQL queries. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a fixed-length heap-based buffer. An attacker can leverage this vulnerability to escalate privileges and execute arbitrary code in the context of the service account. Was ZDI-CAN-16190. |
2022-02-18 |
not yet calculated |
CVE-2022-24052
MISC
MISC |
mattermost — mattermost
|
Mattermost 6.3.0 and earlier fails to protect email addresses of the creator of the team via one of the APIs, which allows authenticated team members to access this information resulting in sensitive & private information disclosure. |
2022-02-21 |
not yet calculated |
CVE-2022-0708
MISC |
mediawiki — mediawiki
|
MediaWiki before 1.23.16, 1.24.x through 1.27.x before 1.27.2, and 1.28.x before 1.28.1 allows remote attackers to discover the IP addresses of Wiki visitors via a style=”background-image: attr(title url);” attack within a DIV element that has an attacker-controlled URL in the title attribute. |
2022-02-18 |
not yet calculated |
CVE-2017-0371
MISC
MISC |
| metadata-extractor — metadata-extractor |
When reading a specially crafted JPEG file, metadata-extractor up to 2.16.0 can be made to allocate large amounts of memory that finally leads to an out-of-memory error even for very small inputs. This could be used to mount a denial of service attack against services that use metadata-extractor library. |
2022-02-24 |
not yet calculated |
CVE-2022-24614
MISC |
| metadata-extractor — metadata-extractor |
metadata-extractor up to 2.16.0 can throw various uncaught exceptions while parsing a specially crafted JPEG file, which could result in an application crash. This could be used to mount a denial of service attack against services that use metadata-extractor library. |
2022-02-24 |
not yet calculated |
CVE-2022-24613
MISC |
mflow — mflow
|
Insecure Temporary File in GitHub repository mlflow/mlflow prior to 1.23.1. |
2022-02-23 |
not yet calculated |
CVE-2022-0736
CONFIRM
MISC |
| microweber — microweber |
Cross-site Scripting (XSS) – Reflected in GitHub repository microweber/microweber prior to 1.2.11. |
2022-02-26 |
not yet calculated |
CVE-2022-0723
MISC
CONFIRM |
| microweber — microweber |
Business Logic Errors in GitHub repository microweber/microweber prior to 1.3. |
2022-02-26 |
not yet calculated |
CVE-2022-0762
MISC
CONFIRM |
| microweber — microweber |
Cross-site Scripting (XSS) – Reflected in GitHub repository microweber/microweber prior to 1.3. |
2022-02-23 |
not yet calculated |
CVE-2022-0719
MISC
CONFIRM |
| microweber — microweber |
Insertion of Sensitive Information Into Debugging Code in GitHub repository microweber/microweber prior to 1.3. |
2022-02-23 |
not yet calculated |
CVE-2022-0721
CONFIRM
MISC |
microweber — microweber
|
Cross-site Scripting (XSS) – Stored in GitHub repository microweber/microweber prior to 1.3. |
2022-02-26 |
not yet calculated |
CVE-2022-0763
CONFIRM
MISC |
microweber — microweber
|
Business Logic Errors in Packagist microweber/microweber prior to 1.2.11. |
2022-02-20 |
not yet calculated |
CVE-2022-0688
MISC
CONFIRM |
microweber — microweber
|
Insecure Storage of Sensitive Information in GitHub repository microweber/microweber prior to 1.3. |
2022-02-23 |
not yet calculated |
CVE-2022-0724
CONFIRM
MISC |
modx_revolution — modx_revolution
|
MODX Revolution through 2.8.3-pl allows remote authenticated administrators to execute arbitrary code by uploading an executable file, because the Uploadable File Types setting can be changed by an administrator. |
2022-02-26 |
not yet calculated |
CVE-2022-26149
MISC |
mruby — mruby
|
Out-of-bounds Read in GitHub repository mruby/mruby prior to 3.2. |
2022-02-23 |
not yet calculated |
CVE-2022-0717
CONFIRM
MISC |
multiple_mobile_devices — multiple_mobile_devices
|
The backend infrastructure shared by multiple mobile device monitoring services does not adequately authenticate or authorize API requests, creating an IDOR (Insecure Direct Object Reference) vulnerability. |
2022-02-24 |
not yet calculated |
CVE-2022-0732
CERT-VN
CONFIRM
MISC
CERT-VN |
node.js — node.js
|
Node.js < 12.22.9, < 14.18.3, < 16.13.2, and < 17.3.1 did not handle multi-value Relative Distinguished Names correctly. Attackers could craft certificate subjects containing a single-value Relative Distinguished Name that would be interpreted as a multi-value Relative Distinguished Name, for example, in order to inject a Common Name that would allow bypassing the certificate subject verification.Affected versions of Node.js that do not accept multi-value Relative Distinguished Names and are thus not vulnerable to such attacks themselves. However, third-party code that uses node’s ambiguous presentation of certificate subjects may be vulnerable. |
2022-02-24 |
not yet calculated |
CVE-2021-44533
MISC
MISC |
node.js — node.js
|
Node.js < 12.22.9, < 14.18.3, < 16.13.2, and < 17.3.1 converts SANs (Subject Alternative Names) to a string format. It uses this string to check peer certificates against hostnames when validating connections. The string format was subject to an injection vulnerability when name constraints were used within a certificate chain, allowing the bypass of these name constraints.Versions of Node.js with the fix for this escape SANs containing the problematic characters in order to prevent the injection. This behavior can be reverted through the –security-revert command-line option. |
2022-02-24 |
not yet calculated |
CVE-2021-44532
MISC
MISC |
node.js — node.js
|
Accepting arbitrary Subject Alternative Name (SAN) types, unless a PKI is specifically defined to use a particular SAN type, can result in bypassing name-constrained intermediates. Node.js < 12.22.9, < 14.18.3, < 16.13.2, and < 17.3.1 was accepting URI SAN types, which PKIs are often not defined to use. Additionally, when a protocol allows URI SANs, Node.js did not match the URI correctly.Versions of Node.js with the fix for this disable the URI SAN type when checking a certificate against a hostname. This behavior can be reverted through the –security-revert command-line option. |
2022-02-24 |
not yet calculated |
CVE-2021-44531
MISC
MISC |
node.js — node.js
|
Due to the formatting logic of the “console.table()” function it was not safe to allow user controlled input to be passed to the “properties” parameter while simultaneously passing a plain object with at least one property as the first parameter, which could be “__proto__”. The prototype pollution has very limited control, in that it only allows an empty string to be assigned to numerical keys of the object prototype.Node.js >= 12.22.9, >= 14.18.3, >= 16.13.2, and >= 17.3.1 use a null protoype for the object these properties are being assigned to. |
2022-02-24 |
not yet calculated |
CVE-2022-21824
MISC
MISC |
npm — npm
|
@awsui/components-react is the main AWS UI package which contains React components, with TypeScript definitions designed for user interface development. Multiple components in versions before 3.0.367 have been found to not properly neutralize user input and may allow for javascript injection. Users are advised to upgrade to version 3.0.367 or later. There are no known workarounds for this issue. |
2022-02-24 |
not yet calculated |
CVE-2022-24709
CONFIRM
MISC |
| npm — url-parse |
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.8. |
2022-02-20 |
not yet calculated |
CVE-2022-0686
CONFIRM
MISC |
npm — url-parse
|
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.9. |
2022-02-21 |
not yet calculated |
CVE-2022-0691
MISC
CONFIRM |
octobercms — octobercms
|
Octobercms is a self-hosted CMS platform based on the Laravel PHP Framework. Affected versions of OctoberCMS did not validate gateway server signatures. As a result non-authoritative gateway servers may be used to exfiltrate user private keys. Users are advised to upgrade their installations to build 474 or v1.1.10. The only known workaround is to manually apply the patch (e3b455ad587282f0fbcb7763c6d9c3d000ca1e6a) which adds server signature validation. |
2022-02-24 |
not yet calculated |
CVE-2022-23655
MISC
CONFIRM |
octobercms — octobercms
|
Octobercms is a self-hosted CMS platform based on the Laravel PHP Framework. In affected versions user input was not properly sanitized before rendering. An authenticated user with the permissions to create, modify and delete website pages can exploit this vulnerability to bypass `cms.safe_mode` / `cms.enableSafeMode` in order to execute arbitrary code. This issue only affects admin panels that rely on safe mode and restricted permissions. To exploit this vulnerability, an attacker must first have access to the backend area. The issue has been patched in Build 474 (v1.0.474) and v1.1.10. Users unable to upgrade should apply https://github.com/octobercms/library/commit/c393c5ce9ca2c5acc3ed6c9bb0dab5ffd61965fe to your installation manually. |
2022-02-23 |
not yet calculated |
CVE-2022-21705
MISC
CONFIRM |
ohio_supercomputer_center — open_ondemand
|
The Job Composer app in Ohio Supercomputer Center Open OnDemand before 1.7.19 and 1.8.x before 1.8.18 allows remote authenticated users to provide crafted input in a job template. |
2022-02-26 |
not yet calculated |
CVE-2020-27958
MISC
CONFIRM
MISC |
okta — advanced_server_access_client_for_windows
|
Okta Advanced Server Access Client for Windows prior to version 1.57.0 was found to be vulnerable to command injection via a specially crafted URL. |
2022-02-21 |
not yet calculated |
CVE-2022-24295
MISC |
opencmt — opencmt
|
Openmct versions 1.3.0 to 1.7.7 are vulnerable against stored XSS via the “Web Page” element, that allows the injection of malicious JavaScript into the ‘URL’ field. This issue affects: nasa openmct 1.7.7 version and prior versions; 1.3.0 version and later versions. |
2022-02-20 |
not yet calculated |
CVE-2022-22126
CONFIRM |
openmct — openmct
|
Openmct versions 1.3.0 to 1.7.7 are vulnerable against stored XSS via the “Condition Widget” element, that allows the injection of malicious JavaScript into the ‘URL’ field. This issue affects: nasa openmct 1.7.7 version and prior versions; 1.3.0 version and later versions. |
2022-02-20 |
not yet calculated |
CVE-2022-23053
CONFIRM |
openmct — openmct
|
Openmct versions 1.3.0 to 1.7.7 are vulnerable against stored XSS via the “Summary Widget” element, that allows the injection of malicious JavaScript into the ‘URL’ field. This issue affects: nasa openmct 1.7.7 version and prior versions; 1.3.0 version and later versions. |
2022-02-20 |
not yet calculated |
CVE-2022-23054
CONFIRM |
openmrs — openmrs
|
OpenMRS is a patient-based medical record system focusing on giving providers a free customizable electronic medical record system. Affected versions are subject to arbitrary file exfiltration due to failure to sanitize request when satisfying GET requests for `/images` & `/initfilter/scripts`. This can allow an attacker to access any file on a system running OpenMRS that is accessible to the user id OpenMRS is running under. Affected implementations should update to the latest patch version of OpenMRS Core for the minor version they use. These are: 2.1.5, 2.2.1, 2.3.5, 2.4.5 and 2.5.3. As a general rule, this vulnerability is already mitigated by Tomcat’s URL normalization in Tomcat 7.0.28+. Users on older versions of Tomcat should consider upgrading their Tomcat instance as well as their OpenMRS instance. |
2022-02-22 |
not yet calculated |
CVE-2022-23612
CONFIRM
MISC
MISC
MISC |
| opensuse — libsolv |
Two heap overflow vulnerabilities exist in oenSUSE libsolv through 13 Dec 2020 in the resolve_installed function at src/solver.c: line 1728 & 1766. |
2022-02-21 |
not yet calculated |
CVE-2021-44573
MISC
MISC
MISC |
| opensuse — libsolv |
A heap overflow vulnerability exisfts in openSUSE libsolv through 13 Dec 2020 in the prefer_suggested function at src/policy.c: line 442. |
2022-02-21 |
not yet calculated |
CVE-2021-44571
MISC
MISC |
| opensuse — libsolv |
A heap-buffer openSUSE libsolv through 13 Dec 2020 exists in the solver_solve function at src/solver.c: line 3445. |
2022-02-21 |
not yet calculated |
CVE-2021-44569
MISC
MISC |
| opensuse — libsolv |
Two heap-overflow vulnerabilities exist in openSUSE libsolv through 13 Dec 2020 bugs in the propagate function at src/solver.c: line 490 and 524. |
2022-02-21 |
not yet calculated |
CVE-2021-44577
MISC
MISC
MISC |
| opensuse — libsolv |
Two memory vulnerabilities exists in openSUSE libsolv through 13 Dec 2020 in the resolve_weak function at src/solver.c: line 2222 and 2249. |
2022-02-21 |
not yet calculated |
CVE-2021-44576
MISC
MISC
MISC |
| opensuse — libsolv |
Two heap-overflow vulnerabilities exists in openSUSE/libsolv through 13 Dec 2020 in the bugs in the solver_get_recommendations funtion function at src/solver.c: line 4286 & line 4305 FOR_PROVIDES. |
2022-02-21 |
not yet calculated |
CVE-2021-44570
MISC
MISC
MISC |
| opensuse — libsolv |
Two heap-overflow vulnerabilities exists in openSUSE libsolv through 13 Dec 2020 in the makeruledecisions function at src/solver.c: line 147 and 307. |
2022-02-21 |
not yet calculated |
CVE-2021-44575
MISC
MISC
MISC |
| opensuse — libsolv |
A heap-overflow vulnerability exists in openSUSE libsolv through 13 Dec 2020 in the resolve_jobrules function at src/solver.c at line 1599. |
2022-02-21 |
not yet calculated |
CVE-2021-44574
MISC
MISC |
opensuse — libsolv
|
Two heap-overflow vulnerabilities exist in openSUSE/libsolv libsolv through 13 Dec 2020 in the decisionmap variable via the resolve_dependencies function at src/solver.c (line 1940 & line 1995), which could cause a remote Denial of Service. |
2022-02-21 |
not yet calculated |
CVE-2021-44568
MISC
MISC
MISC |
oracle — talent_acquisition_cloud-taleo_enterprise_edition
|
A potential vulnerability in the Oracle Talent Acquisition Cloud – Taleo Enterprise Edition. This high severity potential vulnerability allows attackers to perform remote code execution on Taleo Enterprise Edition system. Successful attacks of this vulnerability can result in unauthorized remote code execution within Taleo Enterprise Edition and unauthorized ability to cause a partial denial of service (partial DOS) of Oracle Talent Acquisition Cloud – Taleo Enterprise Edition. All affected customers were notified of CVE-2021-35689 by Oracle. |
2022-02-24 |
not yet calculated |
CVE-2021-35689
MISC |
paquitosoftware — notimoo
|
A cross-site scripting (XSS) vulnerability in PaquitoSoftware Notimoo v1.2 allows attackers to execute arbitrary web scripts or HTML via a crafted title or message in a notification. |
2022-02-25 |
not yet calculated |
CVE-2021-42244
MISC |
pcmanager — pcmanager
|
PCManager versions 11.1.1.95 has a privilege escalation vulnerability. Successful exploit could allow the attacker to access certain resource beyond its privilege. |
2022-02-25 |
not yet calculated |
CVE-2021-40046
MISC |
pexip — infinity
|
Pexip Infinity before 27.0 has improper WebRTC input validation. An unauthenticated remote attacker can use excessive resources, temporarily causing denial of service. |
2022-02-18 |
not yet calculated |
CVE-2022-23228
MISC |
pexip — infinity_connect
|
Pexip Infinity Connect before 1.8.0 omits certain provisioning authenticity checks. Thus, untrusted code may execute. |
2022-02-18 |
not yet calculated |
CVE-2021-29655
MISC |
pexip — infinity_connect
|
Pexip Infinity Connect before 1.8.0 mishandles TLS certificate validation. The allow list is not properly checked. |
2022-02-18 |
not yet calculated |
CVE-2021-29656
MISC |
phpuploader — phpuploader
|
Cross-site scripting vulnerability in phpUploader v1.2 and earlier allows a remote unauthenticated attacker to inject an arbitrary script via unspecified vectors. |
2022-02-24 |
not yet calculated |
CVE-2022-24435
MISC
MISC |
phpuploader — phpuploader
|
SQL injection vulnerability in the phpUploader v1.2 and earlier allows a remote unauthenticated attacker to obtain the information in the database via unspecified vectors. |
2022-02-24 |
not yet calculated |
CVE-2022-23986
MISC
MISC |
pimcore — pimcore
|
Path Traversal in GitHub repository pimcore/pimcore prior to 10.3.2. |
2022-02-22 |
not yet calculated |
CVE-2022-0665
CONFIRM
MISC |
piwigo — piwigo
|
Piwigo version 12.2.0 is vulnerable to stored cross-site scripting (XSS), which can lead to privilege escalation. In this way, admin can steal webmaster’s cookies to get the webmaster’s access. |
2022-02-24 |
not yet calculated |
CVE-2022-24620
MISC |
pjsip — pjsip
|
PJSIP is a free and open source multimedia communication library written in C language implementing standard based protocols such as SIP, SDP, RTP, STUN, TURN, and ICE. In versions up to and including 2.11.1 when in a dialog set (or forking) scenario, a hash key shared by multiple UAC dialogs can potentially be prematurely freed when one of the dialogs is destroyed . The issue may cause a dialog set to be registered in the hash table multiple times (with different hash keys) leading to undefined behavior such as dialog list collision which eventually leading to endless loop. A patch is available in commit db3235953baa56d2fb0e276ca510fefca751643f which will be included in the next release. There are no known workarounds for this issue. |
2022-02-22 |
not yet calculated |
CVE-2022-23608
CONFIRM
MISC |
plesk — cms
|
** DISPUTED ** Plesk 18.0.37 is affected by a Cross Site Request Forgery (CSRF) vulnerability that allows an attacker to insert data on the user and admin panel. NOTE: the vendor states that this is only a site-specific problem on websites of one or more Plesk users. |
2022-02-20 |
not yet calculated |
CVE-2021-45007
MISC |
plesk — cms
|
** DISPUTED ** Plesk CMS 18.0.37 is affected by an insecure permissions vulnerability that allows privilege Escalation from user to admin rights. OTE: the vendor states that this is only a site-specific problem on websites of one or more Plesk users. |
2022-02-21 |
not yet calculated |
CVE-2021-45008
MISC |
polkit — polkit
|
There is a flaw in polkit which can allow an unprivileged user to cause polkit to crash, due to process file descriptor exhaustion. The highest threat from this vulnerability is to availability. NOTE: Polkit process outage duration is tied to the failing process being reaped and a new one being spawned |
2022-02-21 |
not yet calculated |
CVE-2021-4115
MISC
MISC
MISC |
popup_builder — popup_builder
|
The Popup Builder WordPress plugin before 4.0.7 does not validate and sanitise the sgpb_type parameter before using it in a require statement, leading to a Local File Inclusion issue. Furthermore, since the beginning of the string can be controlled, the issue can lead to RCE vulnerability via wrappers such as PHAR |
2022-02-21 |
not yet calculated |
CVE-2021-25082
MISC
CONFIRM |
popup_builder — popup_builder
|
The Popup Builder WordPress plugin before 4.0.7 does not validate and properly escape the orderby and order parameters before using them in a SQL statement in the admin dashboard, which could allow high privilege users to perform SQL injection |
2022-02-21 |
not yet calculated |
CVE-2022-0228
MISC
CONFIRM |
premid — premid
|
PreMiD 2.2.0 allows unintended access via the websocket transport. An attacker can receive events from a socket and emit events to a socket, potentially interfering with a victim’s “now playing” status on Discord. |
2022-02-20 |
not yet calculated |
CVE-2021-46701
MISC
MISC |
pritunl_client — pritunl_client
|
Pritunl Client through 1.2.3019.52 on Windows allows local privilege escalation, related to an ACL entry for CREATOR OWNER in platform_windows.go. |
2022-02-20 |
not yet calculated |
CVE-2022-25372
MISC
MISC |
processwire — cms
|
A Directory Traversal vulnerability exits in Processwire CMS before 2.7.1 via the download parameter to index.php. |
2022-02-24 |
not yet calculated |
CVE-2020-27467
MISC |
profile_builder-user_profile_and_user_registration_forms — profile_builder-user_profile_and_user_registration_forms
|
The Profile Builder – User Profile & User Registration Forms WordPress plugin is vulnerable to Cross-Site Scripting due to insufficient escaping and sanitization of the site_url parameter found in the ~/assets/misc/fallback-page.php file which allows attackers to inject arbitrary web scripts onto a pages that executes whenever a user clicks on a specially crafted link by an attacker. This affects versions up to and including 3.6.1. |
2022-02-24 |
not yet calculated |
CVE-2022-0653
MISC
MISC |
qemu — qemu
|
An off-by-one error was found in the SCSI device emulation in QEMU. It could occur while processing MODE SELECT commands in mode_sense_page() if the ‘page’ argument was set to MODE_PAGE_ALLS (0x3f). A malicious guest could use this flaw to potentially crash QEMU, resulting in a denial of service condition. |
2022-02-18 |
not yet calculated |
CVE-2021-3930
MISC
CONFIRM |
qemu — qemu
|
A flaw was found in the QEMU implementation of VMWare’s paravirtual RDMA device in versions prior to 6.1.0. The issue occurs while handling a “PVRDMA_REG_DSRHIGH” write from the guest and may result in a crash of QEMU or cause undefined behavior due to the access of an uninitialized pointer. The highest threat from this vulnerability is to system availability. |
2022-02-24 |
not yet calculated |
CVE-2021-3608
MISC
MISC |
qemu — qemu
|
An integer overflow was found in the QEMU implementation of VMWare’s paravirtual RDMA device in versions prior to 6.1.0. The issue occurs while handling a “PVRDMA_REG_DSRHIGH” write from the guest due to improper input validation. This flaw allows a privileged guest user to make QEMU allocate a large amount of memory, resulting in a denial of service. The highest threat from this vulnerability is to system availability. |
2022-02-24 |
not yet calculated |
CVE-2021-3607
MISC
MISC |
qlik — sense_enterprise
|
A vulnerability in Qlik Sense Enterprise on Windows could allow an remote attacker to enumerate domain user accounts. An attacker could exploit this vulnerability by sending authenticated requests to an affected system. A successful exploit could allow the attacker to compare the response time that are returned by the affected system to determine which accounts are valid user accounts. Affected systems are only vulnerable if they have LDAP configured. |
2022-02-21 |
not yet calculated |
CVE-2022-0564
CONFIRM
CONFIRM
CONFIRM |
qnap — device
|
A cross-site scripting (XSS) vulnerability has been reported to affect QNAP device running Proxy Server. If exploited, this vulnerability allows remote attackers to inject malicious code. We have already fixed this vulnerability in the following versions of Proxy Server: QTS 4.5.x: Proxy Server 1.4.2 ( 2021/12/30 ) and later |
2022-02-25 |
not yet calculated |
CVE-2021-34361
CONFIRM |
qnap — device
|
A cross-site scripting (XSS) vulnerability has been reported to affect QNAP device running Proxy Server. If exploited, this vulnerability allows remote attackers to inject malicious code. We have already fixed this vulnerability in the following versions of Proxy Server: QTS 4.5.x: Proxy Server 1.4.2 ( 2021/12/30 ) and later |
2022-02-25 |
not yet calculated |
CVE-2021-34359
CONFIRM |
radare2 — radare2
|
A vulnerability was found in Radare2 in versions prior to 5.6.2, 5.6.0, 5.5.4 and 5.5.2. Mapping a huge section filled with zeros of an ELF64 binary for MIPS architecture can lead to uncontrolled resource consumption and DoS. |
2022-02-24 |
not yet calculated |
CVE-2021-4021
MISC |
radareorg — radare2
|
Denial of Service in GitHub repository radareorg/radare2 prior to 5.6.4. |
2022-02-23 |
not yet calculated |
CVE-2022-0476
MISC
CONFIRM |
radareorg — radare2
|
Denial of Service in GitHub repository radareorg/radare2 prior to 5.6.4. |
2022-02-24 |
not yet calculated |
CVE-2022-0695
CONFIRM
MISC |
radareorg — radare2
|
Heap-based Buffer Overflow in GitHub repository radareorg/radare2 prior to 5.6.4. |
2022-02-22 |
not yet calculated |
CVE-2022-0713
CONFIRM
MISC |
radareorg — radare2
|
Heap-based Buffer Overflow in GitHub repository radareorg/radare2 prior to 5.6.4. |
2022-02-22 |
not yet calculated |
CVE-2022-0676
CONFIRM
MISC |
radareorg — radare2
|
NULL Pointer Dereference in GitHub repository radareorg/radare2 prior to 5.6.4. |
2022-02-22 |
not yet calculated |
CVE-2022-0712
MISC
CONFIRM |
redis — redis
|
It was discovered, that redis, a persistent key-value database, due to a packaging issue, is prone to a (Debian-specific) Lua sandbox escape, which could result in remote code execution. |
2022-02-18 |
not yet calculated |
CVE-2022-0543
MISC
DEBIAN
MISC
MLIST |
rockwell_automation — 1734-aentr
|
The web interface of the 1734-AENTR communication module mishandles authentication for HTTP POST requests. A remote, unauthenticated attacker can send a crafted request that may allow for modification of the configuration settings. |
2022-02-24 |
not yet calculated |
CVE-2020-14504
MISC |
rockwell_automation — 1734-aentr
|
The web interface of the 1734-AENTR communication module is vulnerable to stored XSS. A remote, unauthenticated attacker could store a malicious script within the web interface that, when executed, could modify some string values on the homepage of the web interface. |
2022-02-24 |
not yet calculated |
CVE-2020-14502
MISC |
rockwell_automation — factorytalk
|
The DeskLock tool provided with FactoryTalk View SE uses a weak encryption algorithm that may allow a local, authenticated attacker to decipher user credentials, including the Windows user or Windows DeskLock passwords. If the compromised user has an administrative account, an attacker could gain full access to the user’s operating system and certain components of FactoryTalk View SE. |
2022-02-24 |
not yet calculated |
CVE-2020-14481
MISC |
rockwell_automation — factorytalk
|
Due to usernames/passwords being stored in plaintext in Random Access Memory (RAM), a local, authenticated attacker could gain access to certain credentials, including Windows Logon credentials. |
2022-02-24 |
not yet calculated |
CVE-2020-14480
MISC |
rockwell_automation — factorytalk
|
A local, authenticated attacker could use an XML External Entity (XXE) attack to exploit weakly configured XML files to access local or remote content. A successful exploit could potentially cause a denial-of-service condition and allow the attacker to arbitrarily read any local file via system-level services. |
2022-02-24 |
not yet calculated |
CVE-2020-14478
MISC |
rosariosis — rosariosis
|
A Cross Site Scripting (XSS) vulnerability exists in RosarioSIS before 7.6.1 via the xss_clean function in classes/Security.php, which allows remote malicious users to inject arbitrary JavaScript or HTML. An example of affected components are all Markdown input fields. |
2022-02-24 |
not yet calculated |
CVE-2021-44565
MISC
MISC
MISC |
rosariosis — rosariosis
|
A Cross Site Scripting (XSS) vulnerability exists in RosarioSIS before 4.3 via the SanitizeMarkDown function in ProgramFunctions/MarkDownHTML.fnc.php. |
2022-02-24 |
not yet calculated |
CVE-2021-44566
MISC
MISC
MISC |
rosariosis — rosariosis
|
An unauthenticated SQL Injection vulnerability exists in RosarioSIS before 7.6.1 via the votes parameter in ProgramFunctions/PortalPollsNotes.fnc.php. |
2022-02-24 |
not yet calculated |
CVE-2021-44567
MISC
MISC
MISC
MISC |
rudloff — alltube
|
Open Redirect on Rudloff/alltube in Packagist rudloff/alltube prior to 3.0.1. |
2022-02-21 |
not yet calculated |
CVE-2022-0692
CONFIRM
MISC |
sangforcsclient.exe — sangforcsclient.exe
|
SangforCSClient.exe in Sangfor VDI Client 5.4.2.1006 allows attackers, when they are able to read process memory, to discover the contents of the Username and Password fields. |
2022-02-26 |
not yet calculated |
CVE-2022-22908
MISC |
| sante — dicom_viewer_pro |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Sante DICOM Viewer Pro 11.8.7.0. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DCM files. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15100. |
2022-02-18 |
not yet calculated |
CVE-2022-24061
MISC |
| sante — dicom_viewer_pro |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Sante DICOM Viewer Pro 11.8.7.0. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of J2K files. Crafted data in a J2K file can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15095. |
2022-02-18 |
not yet calculated |
CVE-2022-24058
MISC |
| sante — dicom_viewer_pro |
This vulnerability allows remote attackers to disclose sensitive information on affected installations of Sante DICOM Viewer Pro 11.8.7.0. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of DCM files. Crafted data in a DCM file can trigger a read past the end of an allocated buffer. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of the current process. Was ZDI-CAN-15099. |
2022-02-18 |
not yet calculated |
CVE-2022-24060
MISC |
| sante — dicom_viewer_pro |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Sante DICOM Viewer Pro 13.2.0.21165. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JP2 files. The issue results from the lack of validating the existence of an object prior to performing operations on the object. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15104. |
2022-02-18 |
not yet calculated |
CVE-2022-24062
MISC |
sante — dicom_viewer_pro
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Sante DICOM Viewer Pro 13.2.0.21165. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of JP2 files. The issue results from the lack of proper validation of user-supplied data, which can result in a memory corruption condition. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15105. |
2022-02-18 |
not yet calculated |
CVE-2022-24063
MISC |
sante — dicom_viewer_pro
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Sante DICOM Viewer Pro 11.8.8.0. User interaction is required to exploit this vulnerability in that the target must visit a malicious page or open a malicious file. The specific flaw exists within the parsing of J2K images. Crafted data in a J2K file can trigger a write past the end of an allocated buffer. An attacker can leverage this vulnerability to execute code in the context of the current process. Was ZDI-CAN-15161. |
2022-02-18 |
not yet calculated |
CVE-2022-24064
MISC |
sas — web_report_studio
|
SAS Web Report Studio 4.4 allows XSS. /SASWebReportStudio/logonAndRender.do has two parameters: saspfs_request_backlabel_list and saspfs_request_backurl_list. The first one affects the content of the button placed in the top left. The second affects the page to which the user is directed after pressing the button, e.g., a malicious web page. In addition, the second parameter executes JavaScript, which means XSS is possible by adding a javascript: URL. |
2022-02-19 |
not yet calculated |
CVE-2022-25256
MISC
MISC
CONFIRM |
scadaflex — scada_controller
|
On ICL ScadaFlex II SCADA Controller SC-1 and SC-2 1.03.07 devices, unauthenticated remote attackers can overwrite, delete, or create files. |
2022-02-26 |
not yet calculated |
CVE-2022-25359
MISC
MISC |
seatd– seatd
|
seatd-launch in seatd 0.6.x before 0.6.4 allows removing files with escalated privileges when installed setuid root. The attack vector is a user-supplied socket pathname. |
2022-02-24 |
not yet calculated |
CVE-2022-25643
MISC
MISC
MISC |
sha256crypt — sha256crypt
|
sha256crypt and sha512crypt through 0.6 allow attackers to cause a denial of service (CPU consumption) because the algorithm’s runtime is proportional to the square of the length of the password. |
2022-02-19 |
not yet calculated |
CVE-2016-20013
MISC
MISC
MISC |
shield_security — shield_security
|
The Shield Security WordPress plugin before 13.0.6 does not sanitise and escape admin notes, which could allow high privilege users to perform Cross-Site Scripting attacks even when the unfiltered_html is disallowed. |
2022-02-21 |
not yet calculated |
CVE-2022-0211
MISC |
showdoc — showdoc
|
Unrestricted Upload of File with Dangerous Type in Packagist showdoc/showdoc prior to 2.10.2. |
2022-02-19 |
not yet calculated |
CVE-2022-0409
CONFIRM
MISC |
simcenter — femap
|
A vulnerability has been identified in Simcenter Femap (All versions < V2022.1.1). Affected application contains an out of bounds write past the end of an allocated structure while parsing specially crafted NEU files. This could allow an attacker to execute code in the context of the current process. (ZDI-CAN-15048) |
2022-02-22 |
not yet calculated |
CVE-2021-46162
CONFIRM |
simcenter — femap
|
A vulnerability has been identified in Simcenter Femap (All versions < V2022.1.1). Affected application contains a stack based buffer overflow vulnerability while parsing specially crafted BDF files. This could allow an attacker to execute code in the context of the current process. (ZDI-CAN-15061) |
2022-02-22 |
not yet calculated |
CVE-2021-46699
CONFIRM |
sonos — one_speaker
|
This vulnerability allows remote attackers to execute arbitrary code on affected installations of Sonos One Speaker prior to 3.4.1 (S2 systems) and 11.2.13 build 57923290 (S1 systems). Authentication is not required to exploit this vulnerability. The specific flaw exists within the ALAC audio codec. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a stack-based buffer. An attacker can leverage this vulnerability to execute code in the context of root. Was ZDI-CAN-15798. |
2022-02-18 |
not yet calculated |
CVE-2022-24049
MISC |
sonos — one_speaker
|
This vulnerability allows network-adjacent attackers to execute arbitrary code on affected installations of Sonos One Speaker prior to 3.4.1 (S2 systems) and 11.2.13 build 57923290 (S1 systems). Authentication is not required to exploit this vulnerability. The specific flaw exists within the anacapd daemon. The issue results from the lack of proper validation of user-supplied data, which can result in an integer underflow before writing to memory. An attacker can leverage this vulnerability to execute code in the context of root. Was ZDI-CAN-15828. |
2022-02-18 |
not yet calculated |
CVE-2022-24046
MISC |
sourcegraph — sourcegraph
|
Sourcegraph is a code search and navigation engine. Sourcegraph prior to version 3.37 is vulnerable to remote code execution in the `gitserver` service. The service acts as a git exec proxy, and fails to properly restrict calling `git config`. This allows an attacker to set the git `core.sshCommand` option, which sets git to use the specified command instead of ssh when they need to connect to a remote system. Exploitation of this vulnerability depends on how Sourcegraph is deployed. An attacker able to make HTTP requests to internal services like gitserver is able to exploit it. This issue is patched in Sourcegraph version 3.37. As a workaround, ensure that requests to gitserver are properly protected. |
2022-02-18 |
not yet calculated |
CVE-2022-23642
CONFIRM
MISC |
spiffy_calendar — spiffy_calendar
|
Cross-Site Request Forgery (CSRF) vulnerability leading to event deletion was discovered in Spiffy Calendar WordPress plugin (versions <= 4.9.0). |
2022-02-21 |
not yet calculated |
CVE-2022-25599
CONFIRM
CONFIRM |
strapi — strapi
|
Arbitrary Command Injection in GitHub repository strapi/strapi prior to 4.1.0. |
2022-02-26 |
not yet calculated |
CVE-2022-0764
CONFIRM
MISC |
subrion — cms
|
A Cross Site Scripting (XSS) vulnerability exits in Subrion CMS through 4.2.1 in the Create Page functionality of the admin Account via a SGV file. |
2022-02-24 |
not yet calculated |
CVE-2021-43724
MISC |
survey_maker — survey_maker
|
Unauthenticated Stored Cross-Site Scripting (XSS) vulnerability discovered in Survey Maker WordPress plugin (versions <= 2.0.6). |
2022-02-21 |
not yet calculated |
CVE-2021-26256
CONFIRM
CONFIRM |
swtpm — swtpm
|
swtpm is a libtpms-based TPM emulator with socket, character device, and Linux CUSE interface. Versions prior to 0.5.3, 0.6.2, and 0.7.1 are vulnerable to out-of-bounds read. A specially crafted header of swtpm’s state, where the blobheader’s hdrsize indicator has an invalid value, may cause an out-of-bounds access when the byte array representing the state of the TPM is accessed. This will likely crash swtpm or prevent it from starting since the state cannot be understood. Users should upgrade to swtpm v0.5.3, v0.6.2, or v0.7.1 to receive a patch. There are currently no known workarounds. |
2022-02-18 |
not yet calculated |
CVE-2022-23645
CONFIRM
MISC
MISC
MISC
MISC |
| tenda — routers |
Tenda AC9 V15.03.2.21_cn was discovered to contain a stack overflow via the parameter NPTR. |
2022-02-24 |
not yet calculated |
CVE-2022-25414
MISC |
| tenda — routers |
Tenda AC9 V15.03.2.21_cn was discovered to contain a stack overflow via the function saveparentcontrolinfo. |
2022-02-24 |
not yet calculated |
CVE-2022-25417
MISC |
tenda — routers
|
Tenda AC9 V15.03.2.21_cn was discovered to contain a stack overflow via the function openSchedWifi. |
2022-02-24 |
not yet calculated |
CVE-2022-25418
MISC |
| tongda2000 — tongda2000 |
Tongda2000 v11.10 was discovered to contain a SQL injection vulnerability in delete_query.php via the DELETE_STR parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25406
MISC |
| tongda2000 — tongda2000 |
Tongda2000 v11.10 was discovered to contain a SQL injection vulnerability in delete.php via the DELETE_STR parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25404
MISC |
tongda2000 — tongda2000
|
Tongda2000 v11.10 was discovered to contain a SQL injection vulnerability in change_box.php via the DELETE_STR parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25405
MISC |
tor_browser — tor_browser
|
Tor Browser 9.0.7 on Windows 10 build 10586 is vulnerable to information disclosure. This could allow local attackers to bypass the intended anonymity feature and obtain information regarding the onion services visited by a local user. This can be accomplished by analyzing RAM memory even several hours after the local user used the product. This occurs because the product doesn’t properly free memory. |
2022-02-26 |
not yet calculated |
CVE-2021-46702
MISC |
| totolink — technology_routers |
A command injection vulnerability in the function setUpgradeFW of TOTOLINK Technology router T6 V3_Firmware T6_V3_V4.1.5cu.748_B20211015 allows attackers to execute arbitrary commands via a crafted MQTT packet. |
2022-02-19 |
not yet calculated |
CVE-2022-25134
MISC |
| totolink — technology_routers |
A command injection vulnerability in the function isAssocPriDevice of TOTOLINK Technology router T6 V3_Firmware T6_V3_V4.1.5cu.748_B20211015 allows attackers to execute arbitrary commands via a crafted MQTT packet. |
2022-02-19 |
not yet calculated |
CVE-2022-25133
MISC |
| totolink — technology_routers |
A command injection vulnerability in the function updateWifiInfo of TOTOLINK Technology routers T6 V3_Firmware T6_V3_V4.1.5cu.748_B20211015 and T10 V2_Firmware V4.1.8cu.5207_B20210320 allows attackers to execute arbitrary commands via a crafted MQTT packet. |
2022-02-19 |
not yet calculated |
CVE-2022-25130
MISC |
| totolink — technology_routers |
A command injection vulnerability in the function recv_mesh_info_sync of TOTOLINK Technology router T6 V3_Firmware T6_V3_V4.1.5cu.748_B20211015 allows attackers to execute arbitrary commands via a crafted MQTT packet. |
2022-02-19 |
not yet calculated |
CVE-2022-25135
MISC |
| totolink — technology_routers |
A command injection vulnerability in the function meshSlaveUpdate of TOTOLINK Technology routers T6 V3_Firmware T6_V3_V4.1.5cu.748_B20211015 and T10 V2_Firmware V4.1.8cu.5207_B20210320 allows attackers to execute arbitrary commands via a crafted MQTT packet. |
2022-02-19 |
not yet calculated |
CVE-2022-25136
MISC |
| totolink — technology_routers |
TOTOLink A810R V4.1.2cu.5182_B20201026 was discovered to contain a command injection vulnerability in the “Main” function. This vulnerability allows attackers to execute arbitrary commands via the QUERY_STRING parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25079
MISC |
| totolink — technology_routers |
A command injection vulnerability in the function recvSlaveCloudCheckStatus of TOTOLINK Technology routers T6 V3_Firmware T6_V3_V4.1.5cu.748_B20211015 and T10 V2_Firmware V4.1.8cu.5207_B20210320 allows attackers to execute arbitrary commands via a crafted MQTT packet. |
2022-02-19 |
not yet calculated |
CVE-2022-25131
MISC |
| totolink — technology_routers |
TOTOLink A3100R V4.1.2cu.5050_B20200504 was discovered to contain a command injection vulnerability in the “Main” function. This vulnerability allows attackers to execute arbitrary commands via the QUERY_STRING parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25077
MISC |
| totolink — technology_routers |
TOTOLink A800R V4.1.2cu.5137_B20200730 was discovered to contain a command injection vulnerability in the “Main” function. This vulnerability allows attackers to execute arbitrary commands via the QUERY_STRING parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25076
MISC |
| totolink — technology_routers |
TOTOLink A950RG V5.9c.4050_B20190424 and V4.1.2cu.5204_B20210112 were discovered to contain a command injection vulnerability in the “Main” function. This vulnerability allows attackers to execute arbitrary commands via the QUERY_STRING parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25082
MISC |
| totolink — technology_routers |
TOTOLink A3600R V4.1.2cu.5182_B20201102 was discovered to contain a command injection vulnerability in the “Main” function. This vulnerability allows attackers to execute arbitrary commands via the QUERY_STRING parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25078
MISC |
| totolink — technology_routers |
TOTOLink T10 V5.9c.5061_B20200511 was discovered to contain a command injection vulnerability in the “Main” function. This vulnerability allows attackers to execute arbitrary commands via the QUERY_STRING parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25081
MISC |
| totolink — technology_routers |
TOTOLink A3000RU V5.9c.2280_B20180512 was discovered to contain a command injection vulnerability in the “Main” function. This vulnerability allows attackers to execute arbitrary commands via the QUERY_STRING parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25075
MISC |
| totolink — technology_routers |
A command injection vulnerability in the function meshSlaveDlfw of TOTOLINK Technology router T6 V3_Firmware T6_V3_V4.1.5cu.748_B20211015 allows attackers to execute arbitrary commands via a crafted MQTT packet. |
2022-02-19 |
not yet calculated |
CVE-2022-25132
MISC |
| totolink — technology_routers |
TOTOLink A830R V5.9c.4729_B20191112 was discovered to contain a command injection vulnerability in the “Main” function. This vulnerability allows attackers to execute arbitrary commands via the QUERY_STRING parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25080
MISC |
totolink — technology_routers
|
TOTOLink T6 V5.9c.4085_B20190428 was discovered to contain a command injection vulnerability in the “Main” function. This vulnerability allows attackers to execute arbitrary commands via the QUERY_STRING parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25084
MISC |
totolink — technology_routers
|
TOTOLink A860R V4.1.2cu.5182_B20201027 was discovered to contain a command injection vulnerability in the “Main” function. This vulnerability allows attackers to execute arbitrary commands via the QUERY_STRING parameter. |
2022-02-24 |
not yet calculated |
CVE-2022-25083
MISC |
totolink — technology_routers
|
A command injection vulnerability in the function recvSlaveUpgstatus of TOTOLINK Technology routers T6 V3_Firmware T6_V3_V4.1.5cu.748_B20211015 and T10 V2_Firmware V4.1.8cu.5207_B20210320 allows attackers to execute arbitrary commands via a crafted MQTT packet. |
2022-02-19 |
not yet calculated |
CVE-2022-25137
MISC |
| tp-link — routers |
This vulnerability allows network-adjacent attackers to execute arbitrary code on affected installations of TP-Link AC1750 prior to 1.1.4 Build 20211022 rel.59103(5553) routers. Authentication is not required to exploit this vulnerability. The specific flaw exists within the NetUSB.ko module. The issue results from the lack of proper validation of user-supplied data, which can result in an integer overflow before allocating a buffer. An attacker can leverage this vulnerability to execute code in the context of root. Was ZDI-CAN-15835. |
2022-02-18 |
not yet calculated |
CVE-2022-24354
MISC |
| tp-link — routers |
TP-LINK TL-WR840N(ES)_V6.20_180709 was discovered to contain a remote code execution (RCE) vulnerability via the function oal_wan6_setIpAddr. |
2022-02-25 |
not yet calculated |
CVE-2022-25064
MISC
MISC
MISC |
| tp-link — routers |
TP-Link Archer A54 Archer A54(US)_V1_210111 routers were discovered to contain a stack overflow in the function DM_ Fillobjbystr(). This vulnerability allows unauthenticated attackers to execute arbitrary code. |
2022-02-24 |
not yet calculated |
CVE-2022-25072
MISC |
| tp-link — routers |
TL-WR841Nv14_US_0.9.1_4.18 routers were discovered to contain a stack overflow in the function dm_fillObjByStr(). This vulnerability allows unauthenticated attackers to execute arbitrary code. |
2022-02-24 |
not yet calculated |
CVE-2022-25073
MISC |
| tp-link — routers |
TP-LINK TL-WR840N(ES)_V6.20_180709 was discovered to contain a command injection vulnerability via the component oal_startPing. |
2022-02-25 |
not yet calculated |
CVE-2022-25060
MISC
MISC
MISC |
| tp-link — routers |
TP-LINK TL-WR840N(ES)_V6.20_180709 was discovered to contain a command injection vulnerability via the component oal_setIp6DefaultRoute. |
2022-02-25 |
not yet calculated |
CVE-2022-25061
MISC
MISC
MISC |
| tp-link — routers |
TP-LINK TL-WR840N(ES)_V6.20_180709 was discovered to contain an integer overflow via the function dm_checkString. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted HTTP request. |
2022-02-25 |
not yet calculated |
CVE-2022-25062
MISC
MISC
MISC |
tp-link — routers
|
TP-Link TL-WR902AC(US)_V3_191209 routers were discovered to contain a stack overflow in the function DM_ Fillobjbystr(). This vulnerability allows unauthenticated attackers to execute arbitrary code. |
2022-02-24 |
not yet calculated |
CVE-2022-25074
MISC |
tp-link — routers
|
This vulnerability allows network-adjacent attackers to execute arbitrary code on affected installations of TP-Link TL-WR940N 3.20.1 Build 200316 Rel.34392n (5553) routers. Authentication is not required to exploit this vulnerability. The specific flaw exists within the parsing of file name extensions. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a fixed-length stack-based buffer. An attacker can leverage this vulnerability to execute code in the context of root. Was ZDI-CAN-13910. |
2022-02-18 |
not yet calculated |
CVE-2022-24355
MISC |
translation_exchange — translation_exchange
|
The Translation Exchange WordPress plugin through 1.0.14 was vulnerable to Authenticated Stored Cross-Site Scripting (XSS) within the Project Key text field found in the plugin’s settings. |
2022-02-21 |
not yet calculated |
CVE-2021-25057
MISC |
trend_micro — antivirus_for_max
|
A link following privilege escalation vulnerability in Trend Micro Antivirus for Max 11.0.2150 and below could allow a local attacker to modify a file during the update process and escalate their privileges. Please note: an attacker must first obtain the ability to execute low-privileged code on the target system in order to exploit this vulnerability. |
2022-02-24 |
not yet calculated |
CVE-2022-24671
N/A
N/A |
trend_micro — apex_one
|
A security link following local privilege escalation vulnerability in Trend Micro Apex One, Trend Micro Apex One as a Service, Trend Micro Worry-Free Business Security 10.0 SP1 and Trend Micro Worry-Free Business Security Services agents could allow a local attacker to create a mount point and leverage this for arbitrary folder deletion, leading to escalated privileges on affected installations. Please note: an attacker must first obtain the ability to execute low-privileged code on the target system in order to exploit this vulnerability. |
2022-02-24 |
not yet calculated |
CVE-2022-24680
N/A
N/A
N/A |
| trend_micro — multiple_products |
An security agent resource exhaustion denial-of-service vulnerability in Trend Micro Apex One, Trend Micro Apex One as a Service, Trend Micro Worry-Free Business Security 10.0 SP1 and Trend Micro Worry-Free Business Security Services agents could allow an attacker to flood a temporary log location and consume all disk space on affected installations. |
2022-02-24 |
not yet calculated |
CVE-2022-24678
N/A
N/A
N/A |
trend_micro — multiple_products
|
A security link following local privilege escalation vulnerability in Trend Micro Apex One, Trend Micro Apex One as a Service, Trend Micro Worry-Free Business Security 10.0 SP1 and Trend Micro Worry-Free Business Security Services agents could allow a local attacker to create an writable folder in an arbitrary location and escalate privileges affected installations. Please note: an attacker must first obtain the ability to execute low-privileged code on the target system in order to exploit this vulnerability. |
2022-02-24 |
not yet calculated |
CVE-2022-24679
N/A
N/A
N/A |
| trend_micro — serverprotect |
Trend Micro ServerProtect 6.0/5.8 Information Server uses a static credential to perform authentication when a specific command is typed in the console. An unauthenticated remote attacker with access to the Information Server could exploit this to register to the server and perform authenticated actions. |
2022-02-24 |
not yet calculated |
CVE-2022-25329
N/A
N/A |
trend_micro — serverprotect
|
Integer overflow conditions that exist in Trend Micro ServerProtect 6.0/5.8 Information Server could allow a remote attacker to crash the process or achieve remote code execution. |
2022-02-24 |
not yet calculated |
CVE-2022-25330
N/A
N/A |
trend_micro — serverprotection
|
Uncaught exceptions that can be generated in Trend Micro ServerProtection 6.0/5.8 Information Server could allow a remote attacker to crash the process. |
2022-02-24 |
not yet calculated |
CVE-2022-25331
N/A
N/A |
tricentis — qtest
|
Tricentis qTest before 10.4 allows stored XSS by an authenticated attacker. |
2022-02-26 |
not yet calculated |
CVE-2022-26146
MISC
MISC |
trillium — notes
|
A Denial of Service vulnerabilty exists in Trilium Notes 0.48.6 in the setupPage function |
2022-02-24 |
not yet calculated |
CVE-2021-43745
MISC |
typo3 — kitodo_presentation_extension
|
An issue was discovered in the Kitodo.Presentation (aka dif) extension before 2.3.2, 3.x before 3.2.3, and 3.3.x before 3.3.4 for TYPO3. A missing access check in an eID script allows an unauthenticated user to submit arbitrary URLs to this component. This results in SSRF, allowing attackers to view the content of any file or webpage the webserver has access to. |
2022-02-19 |
not yet calculated |
CVE-2022-24980
CONFIRM
MISC |
typo3 — varnishcache_extension
|
An issue was discovered in the Varnishcache extension before 2.0.1 for TYPO3. The Edge Site Includes (ESI) content element renderer component does not include an access check. This allows an unauthenticated user to render various content elements, resulting in insecure direct object reference (IDOR), with the potential of exposing internal content elements. |
2022-02-19 |
not yet calculated |
CVE-2022-24979
CONFIRM
MISC |
usbguard — usbguard
|
An issue was discovered in USBGuard before 1.1.0. On systems with the usbguard-dbus daemon running, an unprivileged user could make USBGuard allow all USB devices to be connected in the future. |
2022-02-24 |
not yet calculated |
CVE-2019-25058
MISC
MISC
MISC |
usbredir — usbredir
|
A use-after-free vulnerability was found in usbredir in versions prior to 0.11.0 in the usbredirparser_serialize() in usbredirparser/usbredirparser.c. This issue occurs when serializing large amounts of buffered write data in the case of a slow or blocked destination. |
2022-02-24 |
not yet calculated |
CVE-2021-3700
MISC
MISC |
util-linux — util-linux
|
A flaw was found in the util-linux chfn and chsh utilities when compiled with Readline support. The Readline library uses an “INPUTRC” environment variable to get a path to the library config file. When the library cannot parse the specified file, it prints an error message containing data from the file. This flaw allows an unprivileged user to read root-owned files, potentially leading to privilege escalation. This flaw affects util-linux versions prior to 2.37.4. |
2022-02-21 |
not yet calculated |
CVE-2022-0563
MISC |
v2fly — v2ray
|
Off-by-one Error in GitHub repository v2fly/v2ray-core prior to 4.44.0. |
2022-02-23 |
not yet calculated |
CVE-2021-4070
CONFIRM
MISC |
ver — ver
|
Cross-site scripting vulnerability in a-blog cms Ver.2.8.x series versions prior to Ver.2.8.75, Ver.2.9.x series versions prior to Ver.2.9.40, Ver.2.10.x series versions prior to Ver.2.10.44, Ver.2.11.x series versions prior to Ver.2.11.42, and Ver.3.0.x series versions prior to Ver.3.0.1 allows a remote authenticated attacker to inject an arbitrary script via unspecified vectors. This vulnerability is different from CVE-2022-23916. |
2022-02-24 |
not yet calculated |
CVE-2022-24374
MISC
MISC |
ver — ver
|
Authentication bypass vulnerability in a-blog cms Ver.2.8.x series versions prior to Ver.2.8.74, Ver.2.9.x series versions prior to Ver.2.9.39, Ver.2.10.x series versions prior to Ver.2.10.43, and Ver.2.11.x series versions prior to Ver.2.11.41 allows a remote unauthenticated attacker to bypass authentication under the specific condition. |
2022-02-24 |
not yet calculated |
CVE-2022-21142
MISC
MISC |
ver — ver
|
Cross-site scripting vulnerability in a-blog cms Ver.2.8.x series versions prior to Ver.2.8.75, Ver.2.9.x series versions prior to Ver.2.9.40, Ver.2.10.x series versions prior to Ver.2.10.44, Ver.2.11.x series versions prior to Ver.2.11.42, and Ver.3.0.x series versions prior to Ver.3.0.1 allows a remote authenticated attacker to inject an arbitrary script via unspecified vectors. This vulnerability is different from CVE-2022-24374. |
2022-02-24 |
not yet calculated |
CVE-2022-23916
MISC
MISC |
ver — ver
|
Template injection (Improper Neutralization of Special Elements Used in a Template Engine) vulnerability in a-blog cms Ver.2.8.x series versions prior to Ver.2.8.75, Ver.2.9.x series versions prior to Ver.2.9.40, Ver.2.10.x series versions prior to Ver.2.10.44, Ver.2.11.x series versions prior to Ver.2.11.42, and Ver.3.0.x series versions prior to Ver.3.0.1 allows a remote authenticated attacker to obtain an arbitrary file on the server via unspecified vectors. |
2022-02-24 |
not yet calculated |
CVE-2022-23810
MISC
MISC |
vim — vim
|
Heap-based Buffer Overflow in GitHub repository vim/vim prior to 8.2.4436. |
2022-02-22 |
not yet calculated |
CVE-2022-0714
MISC
CONFIRM
FEDORA
FEDORA |
vim — vim
|
Use of Out-of-range Pointer Offset in GitHub repository vim/vim prior to 8.2.4440. |
2022-02-23 |
not yet calculated |
CVE-2022-0729
CONFIRM
MISC
FEDORA
FEDORA |
vim — vim
|
NULL Pointer Dereference in GitHub repository vim/vim prior to 8.2.4428. |
2022-02-21 |
not yet calculated |
CVE-2022-0696
MISC
CONFIRM
FEDORA |
vim — vim
|
Use of Out-of-range Pointer Offset in GitHub repository vim/vim prior to 8.2.4418. |
2022-02-20 |
not yet calculated |
CVE-2022-0685
CONFIRM
MISC
FEDORA |
visual_voice_mail — visual_voice_mail
|
** DISPUTED ** The Visual Voice Mail (VVM) application through 2022-02-24 for Android allows persistent access if an attacker temporarily controls an application that has the READ_SMS permission, and reads an IMAP credentialing message that is (by design) not displayed to the victim within the AOSP SMS/MMS messaging application. (Often, the IMAP credentials are usable to listen to voice mail messages sent before the vulnerability was exploited, in addition to new ones.) NOTE: some vendors characterize this as not a “concrete and exploitable risk.” |
2022-02-25 |
not yet calculated |
CVE-2022-23835
MISC
MISC |
waline — waline
|
In waline 1.6.1, an attacker can submit messages using X-Forwarded-For to forge any IP address. |
2022-02-25 |
not yet calculated |
CVE-2022-24594
MISC
MISC |
watchguard — firebox_and_xtm
|
WatchGuard Firebox and XTM appliances allow a remote attacker with unprivileged credentials to access the system with a privileged management session via exposed management access. This vulnerability impacts Fireware OS before 11.7.2_U1, 12.x before 12.1.3_U3, and 12.2.x through 12.5.x before 12.5.7_U3. |
2022-02-24 |
not yet calculated |
CVE-2022-23176
CONFIRM
MISC |
watchguard — firebox_and_xtm_appliances
|
WatchGuard Firebox and XTM appliances allow an authenticated remote attacker with unprivileged credentials to modify privileged management user credentials. This vulnerability impacts Fireware OS before 12.7.2_U2, 12.x before 12.1.3_U8, and 12.2.x through 12.5.x before 12.5.9_U2. |
2022-02-24 |
not yet calculated |
CVE-2022-25363
CONFIRM |
watchguard — firebox_and_xtm_appliances
|
WatchGuard Firebox and XTM appliances allow an authenticated remote attacker with unprivileged credentials to upload files to arbitrary locations. This vulnerability impacts Fireware OS before 12.7.2_U2, 12.x before 12.1.3_U8, and 12.2.x through 12.5.x before 12.5.9_U2. |
2022-02-24 |
not yet calculated |
CVE-2022-25360
CONFIRM |
| watchguard — firebox_xtm_appliances |
A wgagent stack-based buffer overflow in WatchGuard Firebox and XTM appliances allows an authenticated remote attacker to potentially execute arbitrary code by initiating a firmware update with a malicious upgrade image. This vulnerability impacts Fireware OS before 12.7.2_U2, 12.x before 12.1.3_U8, and 12.2.x through 12.5.x before 12.5.9_U2. |
2022-02-24 |
not yet calculated |
CVE-2022-25292
CONFIRM |
| watchguard — firebox_xtm_appliances |
An integer overflow in WatchGuard Firebox and XTM appliances allows an authenticated remote attacker to trigger a heap-based buffer overflow and potentially execute arbitrary code by initiating a firmware update with a malicious upgrade image. This vulnerability impacts Fireware OS before 12.7.2_U2, 12.x before 12.1.3_U8, and 12.2.x through 12.5.x before 12.5.9_U2. |
2022-02-24 |
not yet calculated |
CVE-2022-25291
CONFIRM |
| watchguard — firebox_xtm_appliances |
WatchGuard Firebox and XTM appliances allow an authenticated remote attacker with unprivileged credentials to retrieve certificate private keys. This vulnerability impacts Fireware OS before 12.7.2_U2, 12.x before 12.1.3_U8, and 12.2.x through 12.5.x before 12.5.9_U2. |
2022-02-24 |
not yet calculated |
CVE-2022-25290
CONFIRM |
watchguard — firebox_xtm_appliances
|
A systemd stack-based buffer overflow in WatchGuard Firebox and XTM appliances allows an authenticated remote attacker to potentially execute arbitrary code by initiating a firmware update with a malicious upgrade image. This vulnerability impacts Fireware OS before 12.7.2_U2, 12.x before 12.1.3_U8, and 12.2.x through 12.5.x before 12.5.9_U2. |
2022-02-24 |
not yet calculated |
CVE-2022-25293
CONFIRM |
wbce_cms — wbce_cms
|
A vulnerability in the component /languages/index.php of WBCE CMS v1.5.2 allows attackers to execute arbitrary code via a crafted PHP file. |
2022-02-24 |
not yet calculated |
CVE-2022-25099
MISC |
webankpartners — wecube-platform
|
A Directory Traversal vulnerability exists in WeBankPartners wecube-platform 3.2.1 via the file variable in PluginPackageController.java. |
2022-02-24 |
not yet calculated |
CVE-2021-45746
MISC |
weblate — weblate
|
Weblate is a copyleft software web-based continuous localization system. Versions prior to 4.11 do not properly neutralize user input used in user name and language fields. Due to this improper neutralization it is possible to perform cross-site scripting via these fields. The issues were fixed in the 4.11 release. Users unable to upgrade are advised to add their own neutralize logic. |
2022-02-25 |
not yet calculated |
CVE-2022-24710
CONFIRM
MISC
MISC
MISC |
wiki.js — wiki.js
|
Wiki.js is a wiki app built on Node.js. In affected versions an authenticated user with write access on a restricted set of paths can update a page outside the allowed paths by specifying a different target page ID while keeping the path intact. The access control incorrectly check the path access against the user-provided values instead of the actual path associated to the page ID. Commit https://github.com/Requarks/wiki/commit/411802ec2f654bb5ed1126c307575b81e2361c6b fixes this vulnerability by checking access control on the path associated with the page ID instead of the user-provided value. When the path is different than the current value, a second access control check is then performed on the user-provided path before the move operation. |
2022-02-22 |
not yet calculated |
CVE-2022-23654
CONFIRM
MISC |
wikidocs — wikidocs
|
WikiDocs version 0.1.18 has multiple reflected XSS vulnerabilities on different pages. |
2022-02-19 |
not yet calculated |
CVE-2022-23376
MISC
MISC
MISC
MISC |
wikidocs — wikidocs
|
WikiDocs version 0.1.18 has an authenticated remote code execution vulnerability. An attacker can upload a malicious file using the image upload form through index.php. |
2022-02-19 |
not yet calculated |
CVE-2022-23375
MISC
MISC
MISC
MISC |
win-911 — win-911
|
WIN-911 2021 R1 and R2 are vulnerable to a permissions misconfiguration that may allow an attacker to locally write files to the program Operator Workspace directory, which holds DLL files and executables. A low-privilege attacker could write a malicious DLL file to the Operator Workspace directory to achieve privilege escalation and the permissions of the user running the program. |
2022-02-24 |
not yet calculated |
CVE-2022-23104
CONFIRM
CONFIRM |
win-911 — win-911
|
WIN-911 2021 R1 and R2 are vulnerable to a permissions misconfiguration that may allow an attacker to locally write files to the Program Announcer directory and elevate permissions whenever the program is executed. |
2022-02-24 |
not yet calculated |
CVE-2022-23922
CONFIRM
CONFIRM |
wireguard — wireguard
|
Netmaker is a platform for creating and managing virtual overlay networks using WireGuard. Prior to versions 0.8.5, 0.9.4, and 010.0, there is a hard-coded cryptographic key in the code base which can be exploited to run admin commands on a remote server if the exploiter know the address and username of the admin. This effects the server (netmaker) component, and not clients. This has been patched in Netmaker v0.8.5, v0.9.4, and v0.10.0. There are currently no known workarounds. |
2022-02-18 |
not yet calculated |
CVE-2022-23650
MISC
MISC
MISC
CONFIRM |
wolfssl — wolfssl
|
In wolfSSL before 5.2.0, certificate validation may be bypassed during attempted authentication by a TLS 1.3 client to a TLS 1.3 server. This occurs when the sig_algo field differs between the certificate_verify message and the certificate message. |
2022-02-24 |
not yet calculated |
CVE-2022-25638
CONFIRM
MISC |
wolfssl — wolfssl
|
In wolfSSL before 5.2.0, a TLS 1.3 server cannot properly enforce a requirement for mutual authentication. A client can simply omit the certificate_verify message from the handshake, and never present a certificate. |
2022-02-24 |
not yet calculated |
CVE-2022-25640
MISC |
woocs — woocs
|
The WOOCS WordPress plugin before 1.3.7.5 does not sanitise and escape the woocs_in_order_currency parameter of the woocs_get_products_price_html AJAX action (available to both unauthenticated and authenticated users) before outputting it back in the response, leading to a Reflected Cross-Site Scripting |
2022-02-21 |
not yet calculated |
CVE-2022-0234
MISC
CONFIRM |
wp_content_copy_protection_and_no_right_click — wp_content_copy_protection_and_no_right_click
|
Cross-Site Request Forgery (CSRF) vulnerability leading to plugin Settings Update discovered in WP Content Copy Protection & No Right Click WordPress plugin (versions <= 3.4.4). |
2022-02-21 |
not yet calculated |
CVE-2022-23983
CONFIRM
CONFIRM |
| wp_statistics — wp_statistics |
The WP Statistics WordPress plugin is vulnerable to SQL Injection due to insufficient escaping and parameterization of the current_page_id parameter found in the ~/includes/class-wp-statistics-hits.php file which allows attackers without authentication to inject arbitrary SQL queries to obtain sensitive information, in versions up to and including 13.1.5. |
2022-02-24 |
not yet calculated |
CVE-2022-25148
MISC
MISC
MISC |
| wp_statistics — wp_statistics |
The WP Statistics WordPress plugin is vulnerable to Cross-Site Scripting due to insufficient escaping and sanitization of the IP parameter found in the ~/includes/class-wp-statistics-ip.php file which allows attackers to inject arbitrary web scripts onto several pages that execute when site administrators view a sites statistics, in versions up to and including 13.1.5. |
2022-02-24 |
not yet calculated |
CVE-2022-25305
MISC
MISC
MISC |
| wp_statistics — wp_statistics |
The WP Statistics WordPress plugin is vulnerable to Cross-Site Scripting due to insufficient escaping and sanitization of the browser parameter found in the ~/includes/class-wp-statistics-visitor.php file which allows attackers to inject arbitrary web scripts onto several pages that execute when site administrators view a sites statistics, in versions up to and including 13.1.5. |
2022-02-24 |
not yet calculated |
CVE-2022-25306
MISC
MISC
MISC |
wp_statistics — wp_statistics
|
The WP Statistics WordPress plugin is vulnerable to SQL Injection due to insufficient escaping and parameterization of the IP parameter found in the ~/includes/class-wp-statistics-hits.php file which allows attackers without authentication to inject arbitrary SQL queries to obtain sensitive information, in versions up to and including 13.1.5. |
2022-02-24 |
not yet calculated |
CVE-2022-25149
MISC
MISC
MISC |
wp_statistics — wp_statistics
|
The WP Statistics WordPress plugin is vulnerable to Cross-Site Scripting due to insufficient escaping and sanitization of the platform parameter found in the ~/includes/class-wp-statistics-hits.php file which allows attackers to inject arbitrary web scripts onto several pages that execute when site administrators view a sites statistics, in versions up to and including 13.1.5. |
2022-02-24 |
not yet calculated |
CVE-2022-25307
MISC
MISC
MISC |
wp_statistics — wp_statistics
|
The WP Statistics WordPress plugin is vulnerable to SQL Injection due to insufficient escaping and parameterization of the current_page_type parameter found in the ~/includes/class-wp-statistics-hits.php file which allows attackers without authentication to inject arbitrary SQL queries to obtain sensitive information, in versions up to and including 13.1.5. |
2022-02-24 |
not yet calculated |
CVE-2022-0651
MISC
MISC
MISC |
wpdiscuz — wpdiscuz
|
Sensitive information disclosure discovered in wpDiscuz WordPress plugin (versions <= 7.3.11). |
2022-02-21 |
not yet calculated |
CVE-2022-23984
CONFIRM
CONFIRM |
| xerte_project — xerte |
An Authenticated Remote Code Exection (RCE) vulnerability exists in Xerte through 3.9 in website_code/php/import/fileupload.php by uploading a maliciously crafted PHP file though the project interface disguised as a language file to bypasses the upload filters. Attackers can manipulate the files destination by abusing path traversal in the ‘mediapath’ variable. |
2022-02-24 |
not yet calculated |
CVE-2021-44664
MISC
MISC
MISC |
| xerte_project — xerte |
A Directory Traversal vulnerability exists in the Xerte Project Xerte through 3.10.3 when downloading a project file via download.php. |
2022-02-24 |
not yet calculated |
CVE-2021-44665
MISC |
| xerte_project — xerte |
A Remote Code Execution (RCE) vulnerability exists in the Xerte Project Xerte through 3.8.4 via a crafted php file through elfinder in connetor.php. |
2022-02-24 |
not yet calculated |
CVE-2021-44663
MISC
MISC
MISC |
xerte_project — xerte
|
A Site Scripting (XSS) vulnerability exists in the Xerte Project Xerte through 3.8.4 via the link parameter in print.php. |
2022-02-24 |
not yet calculated |
CVE-2021-44662
MISC
MISC
MISC |
zenario — cms
|
Zenario CMS 9.2 allows an authenticated admin user to bypass the file upload restriction by creating a new ‘File/MIME Types’ using the ‘.phar’ extension. Then an attacker can upload a malicious file, intercept the request and change the extension to ‘.phar’ in order to run commands on the server. |
2022-02-24 |
not yet calculated |
CVE-2022-23043
MISC
MISC |
zepl — notebooks
|
Zepl Notebooks before 2021-10-25 are affected by a sandbox escape vulnerability. Upon launching Remote Code Execution from the Notebook, users can then use that to subsequently escape the running context sandbox and proceed to access internal Zepl assets including cloud metadata services. |
2022-02-25 |
not yet calculated |
CVE-2021-42952
MISC
MISC |
zfaka — zfaka
|
An issue was found in Zfaka <= 1.4.5. The verification of the background file upload function check is not strict, resulting in remote command execution. |
2022-02-21 |
not yet calculated |
CVE-2022-24553
MISC
MISC |
zip4j — zip4j
|
zip4j up to 2.9.0 can throw various uncaught exceptions while parsing a specially crafted ZIP file, which could result in an application crash. This could be used to mount a denial of service attack against services that use zip4j library. |
2022-02-24 |
not yet calculated |
CVE-2022-24615
MISC |
zte — products
|
There is a directory traversal vulnerability in some home gateway products of ZTE. Due to the lack of verification of user modified destination path, an attacker with specific permissions could modify the FTP access path to access and modify the system path contents without authorization, which will cause information leak and affect device operation. |
2022-02-24 |
not yet calculated |
CVE-2022-23135
MISC |
zulip — zulip
|
Improper Access Control in GitHub repository zulip/zulip prior to 4.10. |
2022-02-26 |
not yet calculated |
CVE-2021-3967
CONFIRM
MISC |
zulip — zulip
|
Zulip is an open-source team collaboration tool with topic-based threading. Zulip Server version 2.0.0 and above are vulnerable to insufficient access control with multi-use invitations. A Zulip Server deployment which hosts multiple organizations is vulnerable to an attack where an invitation created in one organization (potentially as a role with elevated permissions) can be used to join any other organization. This bypasses any restrictions on required domains on users’ email addresses, may be used to gain access to organizations which are only accessible by invitation, and may be used to gain access with elevated privileges. This issue has been patched in release 4.10. There are no known workarounds for this issue. ### Patches _Has the problem been patched? What versions should users upgrade to?_ ### Workarounds _Is there a way for users to fix or remediate the vulnerability without upgrading?_ ### References _Are there any links users can visit to find out more?_ ### For more information If you have any questions or comments about this advisory, you can discuss them on the [developer community Zulip server](https://zulip.com/developer-community/), or email the [Zulip security team](mailto:security@zulip.com). |
2022-02-26 |
not yet calculated |
CVE-2022-21706
CONFIRM
MISC
MISC
MISC |
| zyxel — armor_firmware |
A cross-site request forgery vulnerability in the HTTP daemon of the Zyxel ARMOR Z1/Z2 firmware could allow an attacker to execute arbitrary commands if they coerce or trick a local user to visit a compromised website with malicious scripts. |
2022-02-24 |
not yet calculated |
CVE-2021-4030
CONFIRM |
zyxel — armor_firmware
|
A command injection vulnerability in the CGI program of the Zyxel ARMOR Z1/Z2 firmware could allow an attacker to execute arbitrary OS commands via a LAN interface. |
2022-02-24 |
not yet calculated |
CVE-2021-4029
CONFIRM |
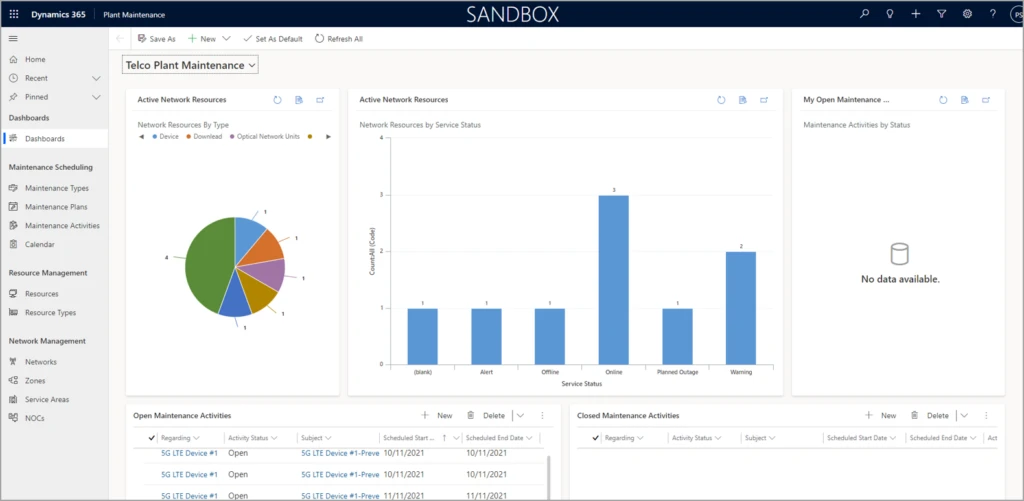
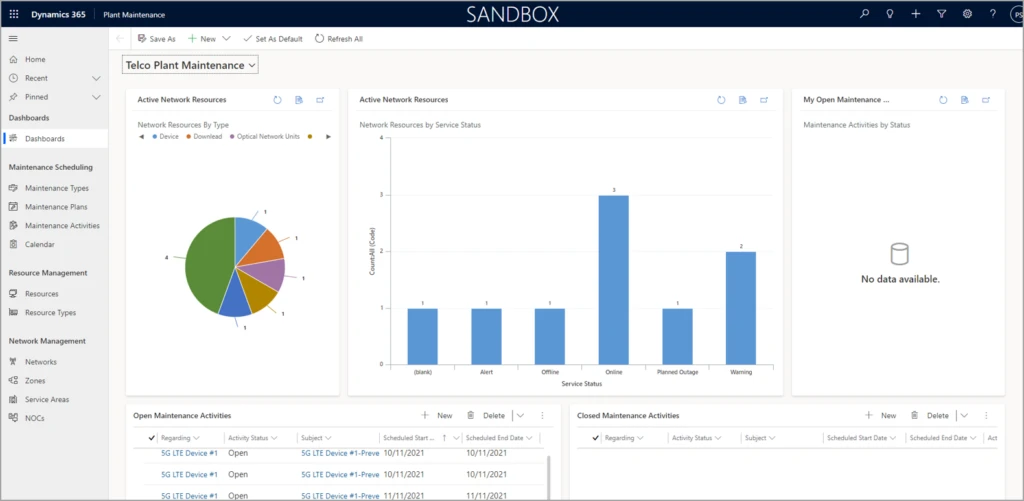
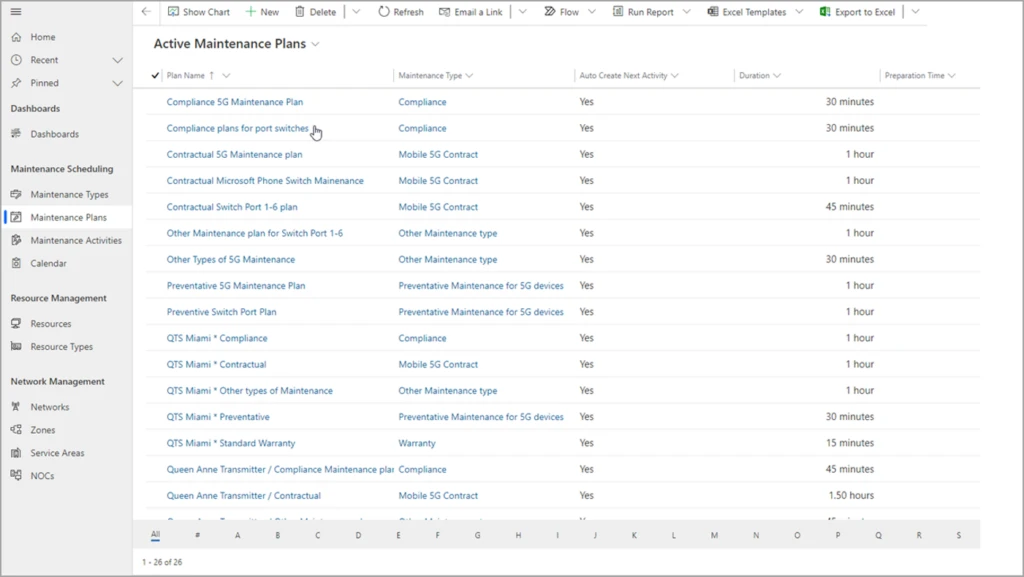
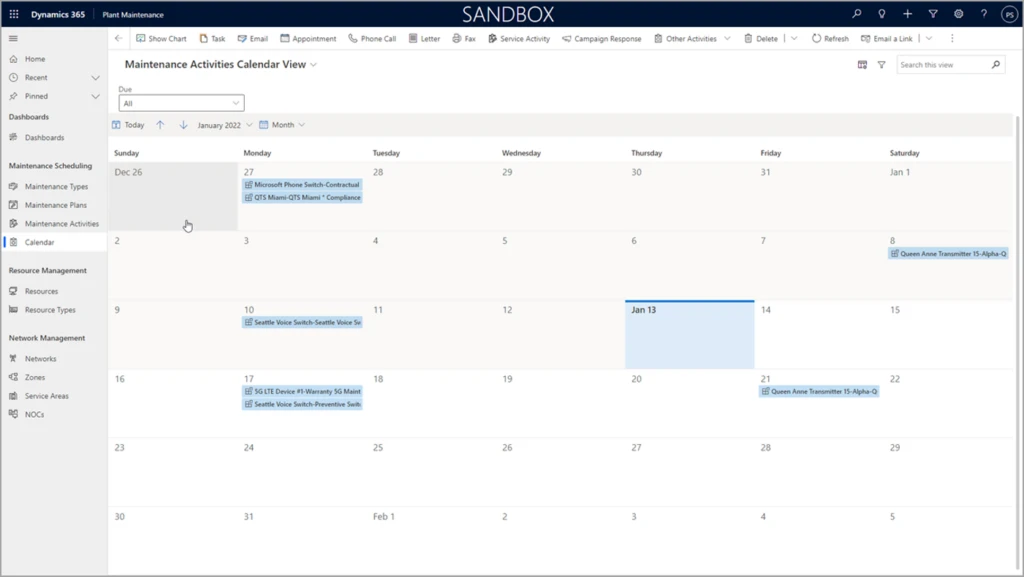




Recent Comments