by Scott Muniz | Apr 15, 2021 | Security, Technology
This article is contributed. See the original author and article here.
Juniper Networks has released security updates to address vulnerabilities in multiple products. An attacker could exploit some of these vulnerabilities to take control of an affected system.
CISA encourages users and administrators to review the Juniper Security Advisories webpage and apply the necessary updates or workarounds.
by Scott Muniz | Apr 15, 2021 | Security, Technology
This article is contributed. See the original author and article here.
Cybersecurity researchers from Forescout and JSOF have released a report on a set of nine vulnerabilities—referred to as NAME:WRECK—affecting Domain Name System (DNS) implementations. NAME:WRECK affects at least four common TCP/IP stacks—FreeBSD, IPNet, NetX, and Nucleus NET—that are used in Internet of Things (IoT), operational technology (OT), and information technology (IT) devices. A remote attacker could exploit these vulnerabilities to take control of an affected system.
CISA encourages users and administrators to review the Forescout Research Labs and JSOF Research Labs report NAME:WRECK Breaking and Fixing DNS Implementations and Forescout NAME:WRECK web page for more information, including recommended mitigations.
by Contributed | Apr 15, 2021 | Technology
This article is contributed. See the original author and article here.
Initial Update: Thursday, 15 April 2021 10:22 UTC
We are aware of issues within Log Analytics and are actively investigating. Some customers may experience data access, data gaps, data latency and missed or delayed alerts in UAE Central region..
- Work Around: None
- Next Update: Before 04/15 14:30 UTC
We are working hard to resolve this issue and apologize for any inconvenience.
-Deepika
by Contributed | Apr 15, 2021 | Technology
This article is contributed. See the original author and article here.
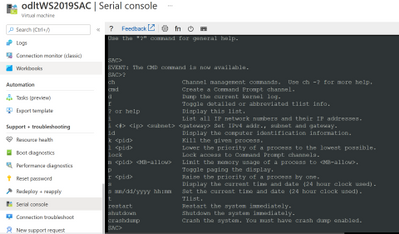
If you make a mistake when configuring operating system firewall rules that block you from accessing the VM, or a service is stopping an IaaS VM from booting, or some other configuration problem such as a newly installed application is stopping you from accessing a Windows Server IaaS VM using RDP or remote PowerShell, you always have the option of interacting with the Special Administration Console (SAC), also known as Emergency Management Services (EMS) if you set it up beforehand.
Enabling EMS can provide you with another “get out of jail” card if something goes wrong with one of your Windows Server IaaS VMs.
Note: Serial Console access is also available for Linux VMs, and you can find out more about it in the following Docs article:
There are several steps that you need to take to enable Serial Console access to Windows Server IaaS VMs. The first is to configure the Windows Server VM operating system to support EMS, something that it isn’t configured for by default. You can do this by opening up an administrative command prompt (not PowerShell) on the VM once it is deployed and running the command:
Bcdedit /ems {current} on
You’ll then need to restart the VM.
When configuring Serial Console for a VM, you also need to ensure that you have an account configured as a member of the local Administrators group on the VM that uses password authentication. This is the account you’ll use to interact with the VM through EMS once you have authenticated.
The next step requires that you configure the VM to support boot diagnostics. It’s important to note that you’ll need to use a custom boot diagnostics account and that you can’t use managed boot diagnostics storage accounts at the time of writing. You can do this from CloudShell by running the command (substituting in the appropriate values for VM name, resource group and storage account that will store boot diagnostics data):
az vm boot-diagnostics enable --name MyVirtualMachine --resource-group MyResourceGroup --storage https://mystor.blob.core.windows.net/
Or by enabling it through the VM’s properties in the Azure portal in the Boot Diagnostics area of the Support + Troubleshooting section.
Once you’ve enabled boot diagnostics, the final step is to enable Serial Console at the subscription level. You can do this in CloudShell by running the following commands:
subscriptionId=$(az account show --output=json | jq -r .id)
az resource invoke-action --action enableConsole --ids "/subscriptions/$subscriptionId/providers/Microsoft.SerialConsole/consoleServices/default" --api-version="2018-05-01"
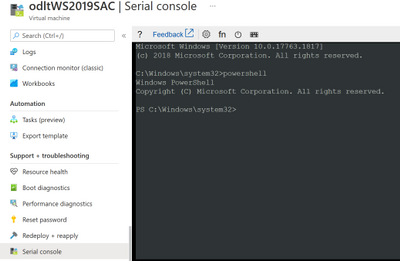
Once you’ve taken these steps you can access the Serial Console for the VM from the Serial Console area of the Support + Troubleshooting section.
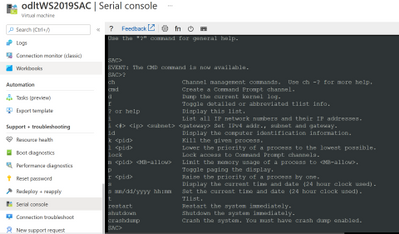
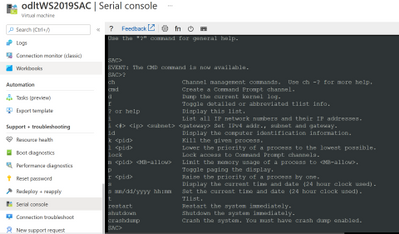
Once you’ve made the connection to SAC, enter the following to create a channel that has the CMD instance
Cmd
You’ll then need to type the following to switch to the cmd channel
Ch -si 1
Press Enter and you’ll be presented with an authentication prompt. Authenticate with the account that has local credentials. Generally you’ll just press Enter when prompted for Domain and if you have to delete characters when authenticating, press <CTRL><H>
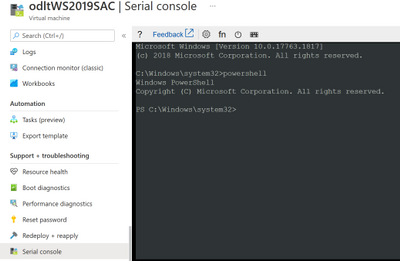
To start a PowerShell session from the command prompt, type PowerShell.exe
You can use PowerShell within a Serial Console to perform the following tasks:
- Edit the registry
- Enable RDP
- Manage services
- Configure service logon accounts
- Configure service startup types
- Configure service dependencies
- Perform network diagnostics
- Manage Windows Firewall settings
- Manage users and groups
- Manage the Windows Event Log
- View or remove installed applications
- Add and remove Windows roles and features
- Restart windows
- Configure network interfaces including setting IP addresses (remember that an Azure IaaS VM should always be configured from within the VM to use DHCP and any adapter address configuration should be performed external to the VM against the network adapter within the Azure console)
For more information on what you can do using cmd.exe and PowerShell within a Serial Console session, consult the following article:
Although you’ll probably not need it, you should enable EMS on all of your Windows Server IaaS VMs as a way of giving yourself a method of troubleshooting a VM you can’t connect to using RDP or Azure PowerShell.
by Contributed | Apr 15, 2021 | Technology
This article is contributed. See the original author and article here.
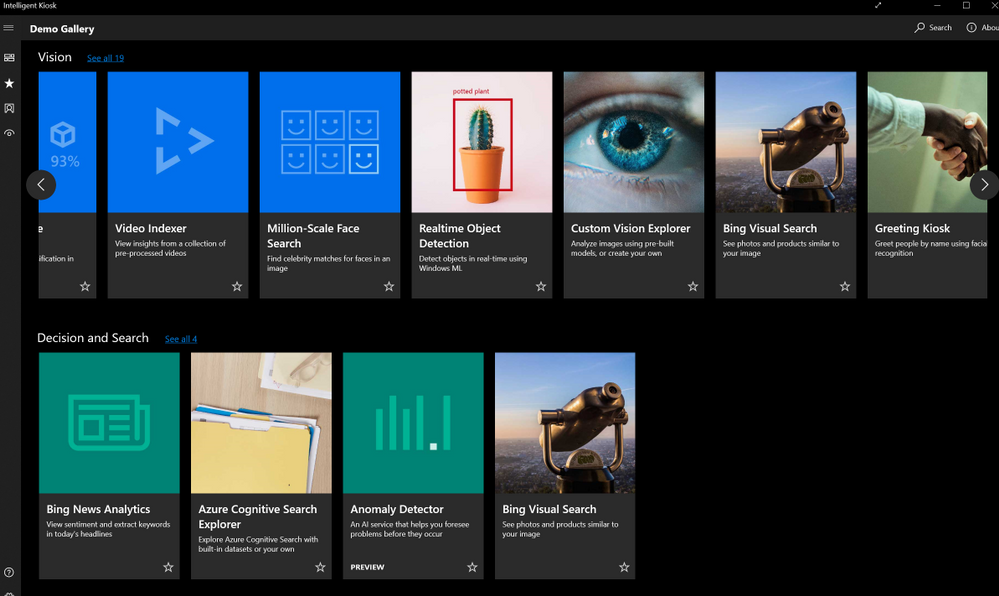
We use AI (Artificial Intelligence) integrated applications daily, from search engines optimized to find the most relevant content, to recommendation engines for streaming or shopping. During AI’s early years rising to popularity, improving applications with AI was only possible for companies with big budgets dedicated to research and experts, preventing companies that cannot effort an AI team to compete. Today AI is readily available for any product, without having to invest in research and development. There are open-source libraries that can help you train Machine Learning models like TensorFlow. With a fraction of the effort and the cost, pre-trained AI services are available to easily integrate into your applications, with APIs and UI based tools to train custom models for your specific use case. In Integrating AI series, I aim to help you decide if and how to integrate AI into your applications, get you started with Azure’s ready to use AI solutions, Cognitive Services and answer your most frequent questions when getting started.
Let’s start with these fundamental questions:
- What are the problems you can solve with AI?
- What do you need to know before starting to build your solution?
- How do you measure the success of your new AI features?
What are the problems you can solve with AI?
AI is a groundbreaking technology but not a magical solution for everything. It is important to know if you are adding value or solving an actual user problem. There are complex products like Wikipedia and Reddit that have a lot of information but use crowdsourcing and simple search to cater to unique needs without the help of AI. To make an informed decision, you need to start with your users’ needs. What are the problems they face? Is there a process that you can automize like filling expense forms that can be automated with Form Recognizer service? Send voice messages to your customers with updates using Speech Services? Do they make complex choices while using your product that could be customized to your users with the use of Personalizer? Do you need to improve the usability of your application with voice interactions and Language Understanding? It is important to solve a real need for your users instead of assuming the solution that will be useful. User research is the best way to figure out the issues and a lot can be surfaced by user analytics. You can use Metrics Advisor AI service to detect anomalies and figure out future AI solutions as well.
Once you have a clear definition of the problem and define how to measure success, it is time to explore practical solutions. You can read about the Azure customer stories and learn from their methods and design process. For example, read about BBC’s customer story before you read about the technical story of using Azure’s Speech, Azure Bot Service and Language Understanding Services together to solve the customer needs they identified.
Most AI solutions can fall into two categories. The first major use case for AI is automating the mindless repetitive jobs. If the users of an expense report or a hiring application need to type in information from a form or a receipt to your system, it is easily automated by OCR (Optical Character Recognition). Similar automations are possible for close captioning, translation, classifying images and automizing alert messages.
The second category of AI solutions can be categorized as complex human decisions based on data. You could give your friends recommendations on what to watch next easily, knowing what they like, what they don’t like. For example, a streaming service with thousands of movies to choose from, cannot surface relevant content with simple filtering of the genres or release dates. It would take forever to choose what to watch by browsing unless you know the exact name of the movie. For a decision like recommendation among thousands or millions of results, AI might be better at recommending to your best friend, maybe even better than you over time. Understanding the language and intent of people is another example. A human can understand and classify a review as positive or negative easily. For machines to detect the same emotions, you must do more than detect certain words to get sentiment.
What do you need to know before starting to build your solution?
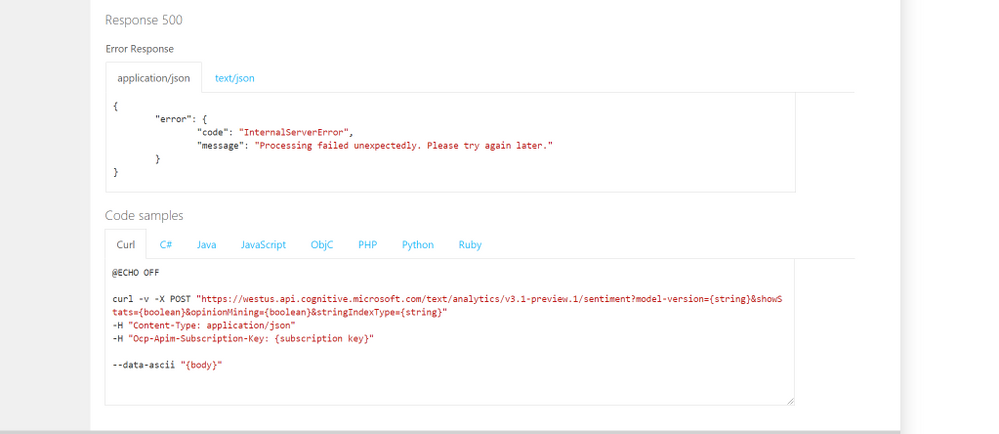
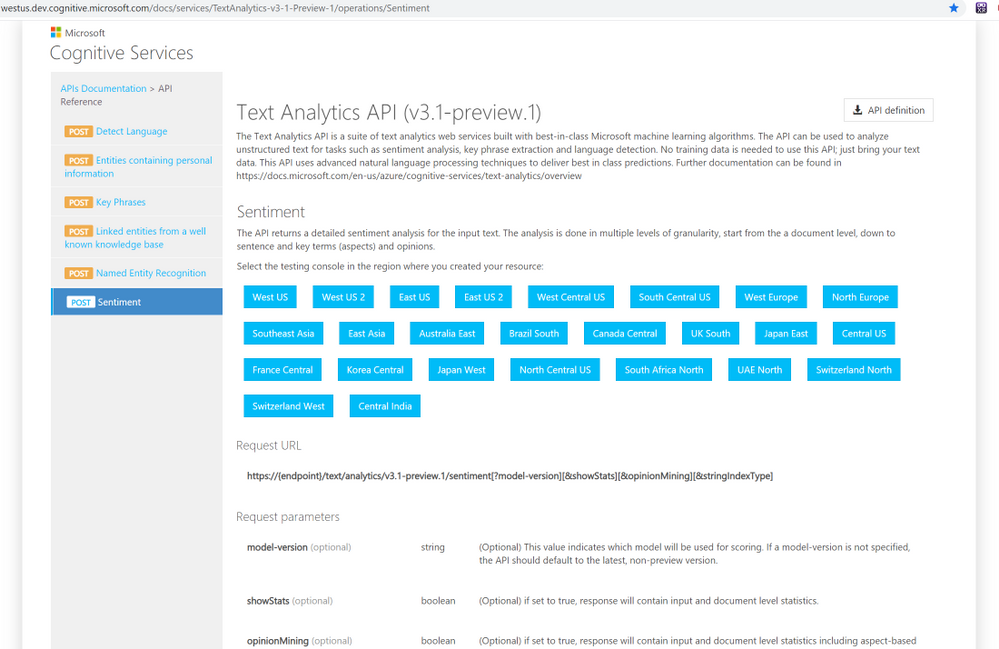
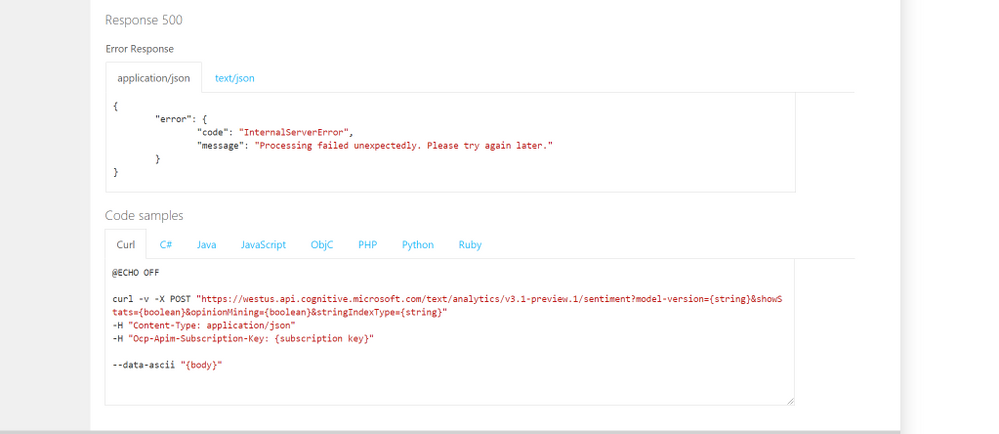
Some problems are easier to solve than others with AI. Experimenting with different tools to confirming your solutions is important. All the Cognitive services are easy to try out and here is how to do that:
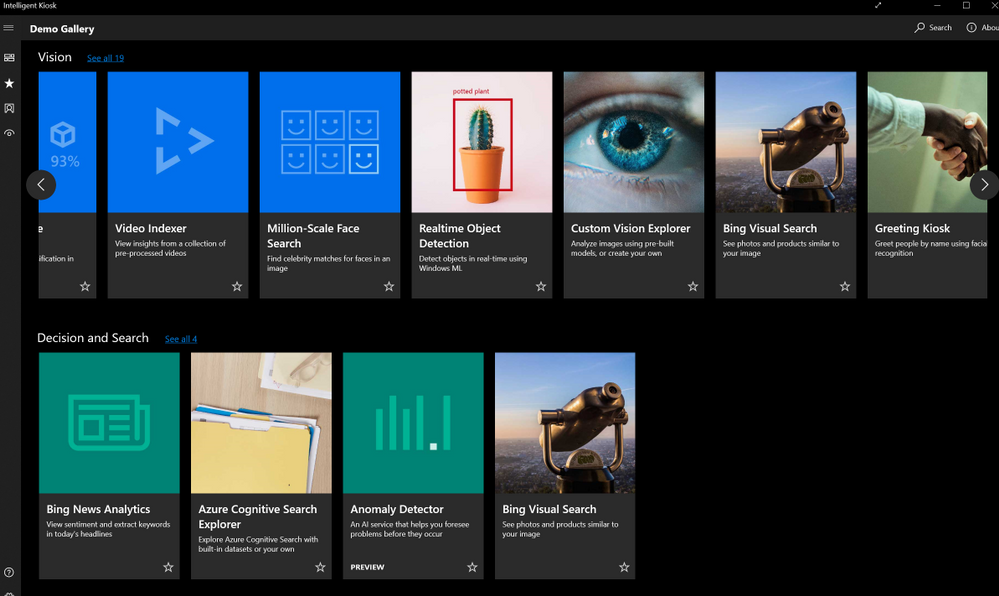
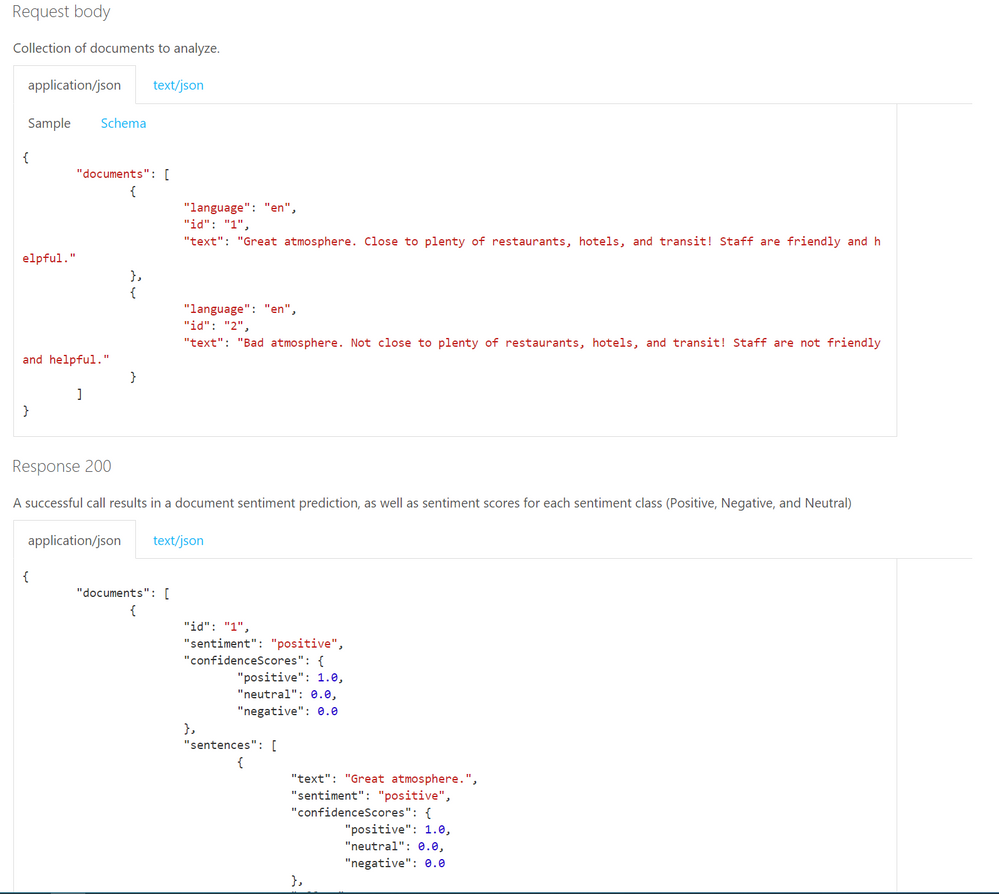
- Once you create an Azure resource, you can see the code samples, API call examples and try out the Rest API end points directly on the Cognitive Services API Reference pages.
-
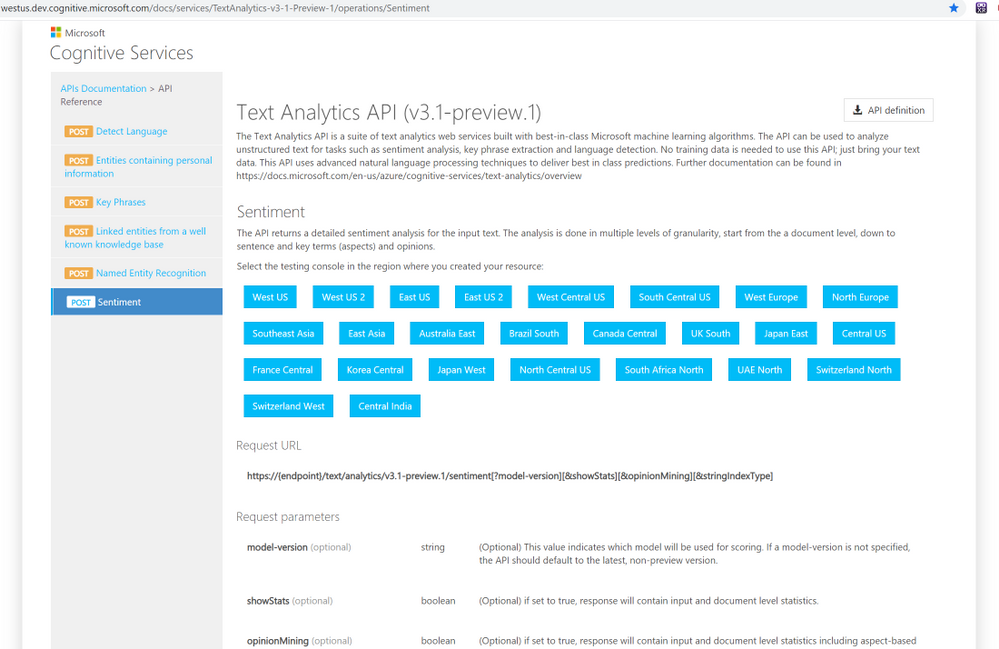 API descriptions
API descriptions
 Code Samples
Code Samples
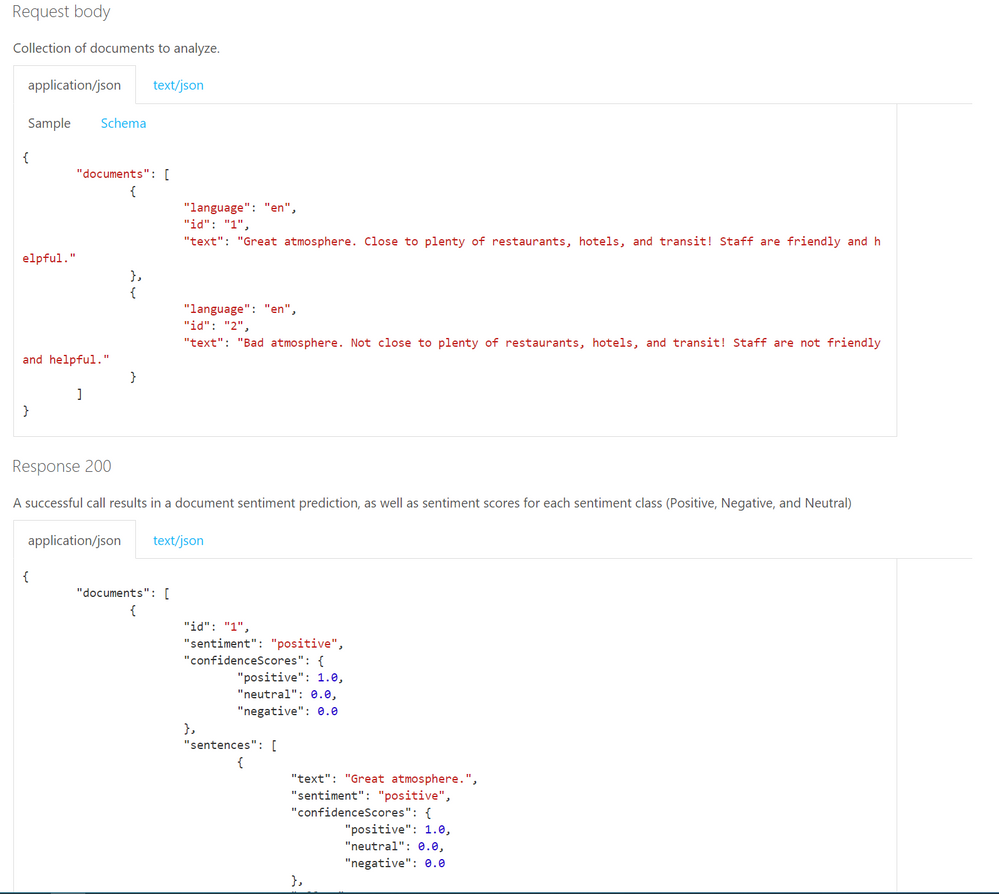 Request
Request
Will your users love your solution?
Scaling an application and polishing the user experience takes most of the development time. It is better to try out features fast and adjust before making the investment in perfecting the wrong experience. You might assume an application flow that users are going to interact, but users can surprise you in their own creative ways of using your tools. Prototype your applications quickly and get user feedback early on.
Power platform is one of the tools that allows you to create mobile apps that integrates important AI capabilities without writing any code. With power platform, you can easily deploy and share your prototypes, without leaving the platform’s UI. After the free trial period, both training and using your AI models will cost but not as much as the development time of an actual app with AI and having to make major changes after the release. Check out some of the capabilities and use cases of AI Builder on Power Platform and how to train a custom vision model and creating a mobile app on Power Platform in this article.
There are other fast and easy options to add AI to your applications, without a big development investment, especially if you are adding the capabilities to an existing application. You can use a logic app to design an application on Azure platform to find twitter mentions of your brand and analyze the sentiment of the tweets. You can visualize the data on Power BI or your choice of visualization platform or tools.
Once you integrate your AI solution, you can make the new AI features to a limited group of users and compare the effectiveness of your solution with your non-AI features.
 AI Show Live every Friday on LearnTV
AI Show Live every Friday on LearnTV
- Let us know the problems you are trying to solve and your specific use cases on the comments below.
Thanks!
by Contributed | Apr 14, 2021 | Technology
This article is contributed. See the original author and article here.
API connections resources work as the bridges for Logic App to communicate with other services. While most of them are used to connect to cloud resources, a few of them leverage On-premises Data Gateways to connect local data sources to Azure. However, we may find that it is not easy to check which On-premises Data Gateway (OPDG) is used by which API connection resource.
Objective:
Find out which On-premises Data Gateways are used by which API connection resources.
Workaround:
The most known way to check OPDG used by a connector is by inspecting the Logic App designer.
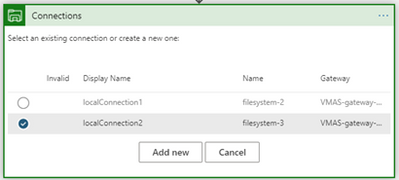
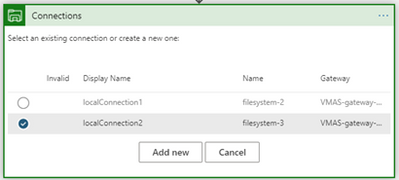
- When creating API connections with OPDG, we can find the OPDG used from the connection list in the Logic App designer.
However, this method seems unhandy as we need to go every Logic App’s designer mode and may cause unwanted change. My preferred way is to check the sourced OPDG from the JSON definition of an API connection resource.
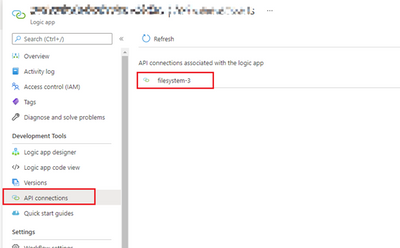
- From a Logic App, open the API connection blade, and choose the API connection which is using the OPDG.
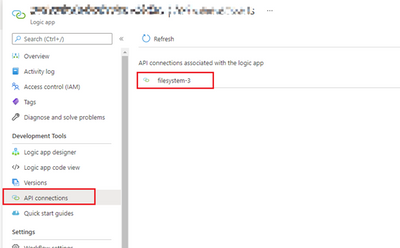
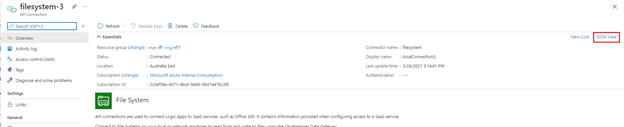
- From the API connection resource main page, click on “JSON View” on the far right.
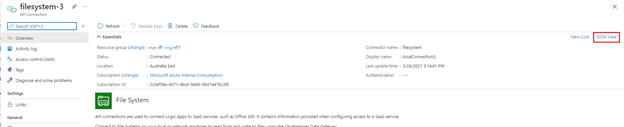
- In the JSON definition of the API connection, you will find the OPDG’s name, resource ID in the “properties” > “parameterValues” > “gateway”.

One more step:
As we have found out that OPDG information can be extracted from the JSON definition of an API connection resource. We can use a PowerShell script to find out all API connections which is using an OPDG.
Prerequisites:
Run the script:
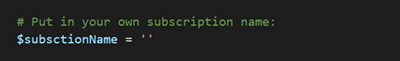
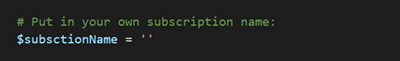
- After downloading the script into your machine, put in the name of your Azure subscription for the subscriptionName variable.
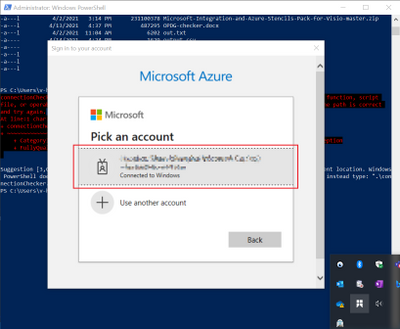
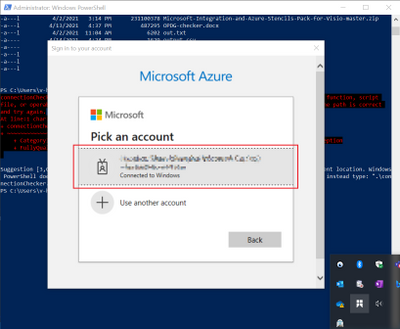
- Then run the script and log into your Azure account in the pop-up window.
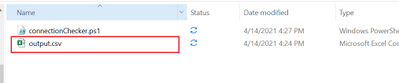
- A CSV file named “output.csv” will be created in the same folder where the script resides.
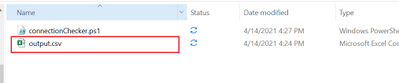
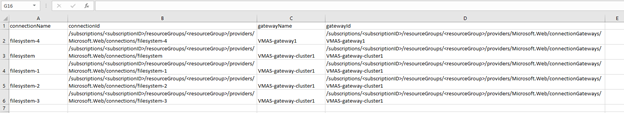
- The CSV file will contain all API connection resources along with the OPDGs they are using.
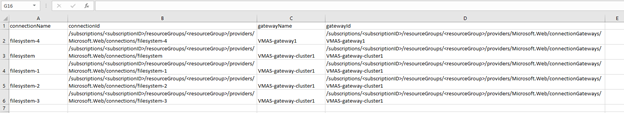
Columns:
connectionName: name of the API connection resource
connectionId: resource ID of the API connection
gatewayName: name of the On-premises Data Gateway resource
gatewatyId: resource ID of the On-premises Data Gateway
Notes:
- Alternative to run the script locally, you may choose to run this through Azure cloud shell. However, please remember the first command “Connect-AzAccount” as it will no longer be required.
Raw script:
# If you encountered "script is not signed error", please use below comand in the PowerShell first.
# Set-ExecutionPolicy -Scope Process -ExecutionPolicy Bypass
# Login to your Azure Account:
Connect-AzAccount
# Put in your own subscription name:
$subsctionName = ''
Set-AzContext -SubscriptionName $subsctionName
# Get all API connection resources
$connectionList = Get-AzResource -ResourceType 'Microsoft.Web/connections'
# Loop through connection list
Write-Host '---------------------------------------'
Write-Host ' Start loop connections - Processing'
Write-Host '---------------------------------------'
$result = @()
foreach ($connection in $connectionList){
$currentConnectionObj = Get-AzResource -ResourceId $connection.ResourceId
$connectionName = $currentConnectionObj.Name
$connectionId = $connection.ResourceId
Write-Host 'Processing connection:' $connectionName
# Extract gateway information
$opdgName = $currentConnectionObj.Properties.parameterValues.gateway.name
$opdgId = $currentConnectionObj.Properties.parameterValues.gateway.id
if (!($opdgId -eq $null)){
Write-Host '------------------------------------------------'
Write-Host 'OPDG found:'
Write-Host 'Connection' $connectionName 'is using gateway' $opdgName
Write-Host '------------------------------------------------'
$new = [PSCustomObject]@{
connectionName = $connectionName
connectionId = $connectionId
gatewayName = $opdgName
gatewayId = $opdgId
}
$result += $new
}
}
# Write collected information to output.csv file
$result | Export-Csv -Path .output.csv -NoTypeInformation
by Contributed | Apr 14, 2021 | Technology
This article is contributed. See the original author and article here.
Note: Please take extreme caution before making any changes in Production. Make sure you test the changes in a test environment first.
Recently due to a spate of updates to various endpoints in SharePoint, Azure, and the AAD auth login endpoints, we are seeing projects compiled with version of .NET before 4.6 cause TLS errors which don’t always show as TLS errors in the PHA.
The error messages The underlying connection was closed” or “System.Net.Sockets.SocketException: An existing connection was forcibly closed by the remote host” you are seeing is mainly due to deprecation of TLS1 1.0 & 1.1. Please see:
Preparing for TLS 1.2 in Office 365 and Office 365 GCC – Microsoft 365 Compliance | Microsoft Docs
Enable TLS 1.2 on servers – Configuration Manager | Microsoft Docs
TLS 1.0 and 1.1 deprecation – Microsoft Tech Community
The updates were communicated in the Office 365 message center.
- MC218794 – July 17, 2020 | TLS 1.0 and 1.1 retirement date in Office 365 to be October 15, 2020
- MC240160 – Feb 16, 2021 | Reminder: Disabling TLS 1.0 and TLS 1.1 in Microsoft 365
If the PHA app web is hosted on a remote physical server, then.
3 ways you can resolve the error:
1] You can either update applications web.config file and update httpRuntime to 4.7 example:
<httpRuntime targetFramework=”4.7″/>
Or
2] You can add the following registry key settings on your remote app web server(s):
[HKEY_LOCAL_MACHINESOFTWAREMicrosoft.NETFrameworkv4.0.30319]
“SystemDefaultTlsVersions” = dword:00000001
“SchUseStrongCrypto” = dword:00000001
Note: You may need to restart your server(s)
Or
3] Add this one line of code above each instantiation of the ClientContext in your code:
System.Net.ServicePointManager.SecurityProtocol = System.Net.SecurityProtocolType.Tls12;
Note: Extensive code updates will be needed.
If the App web is hosted on Azure, then.
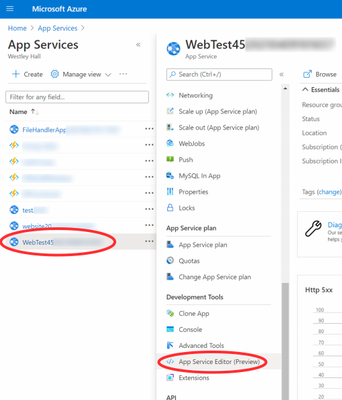
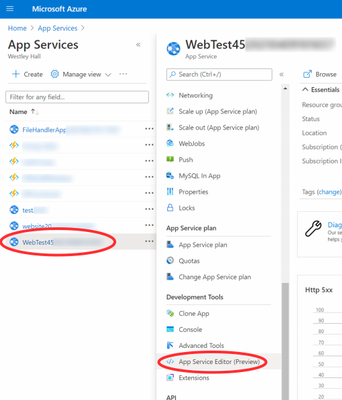
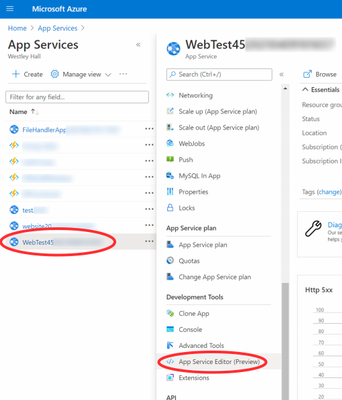
Log into the Azure portal (portal.azure.com) with an account with admin rights on the web app in question.
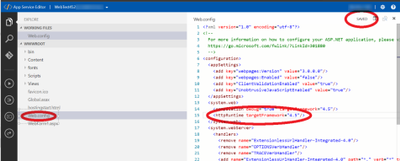
Once you open the App Services and select the web app hosting the PHA site, click on the App Service Editor (Preview).
This will open the editor, then select the web.config file and change the circled targetFramework attribute to 4.7 preferably (any setting higher than 4.6 will work too). Note the status in the upper right will say ‘DIRTY’ for a bit, then it should auto-save and change back to ‘SAVED’-
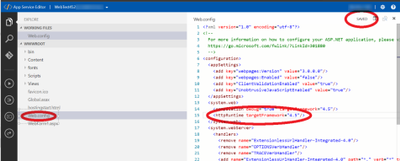
At this point you should be set, refresh the page with the PHA and all should be good.
if the application is a Azure WebJob, then.
You will have to re-target/re-compile the app to 4.6+ (recommend 4.7) and re-upload it to fix it.
You can’t use the config file for the exe to re-target the same way we can for a web application.
by Contributed | Apr 14, 2021 | Technology
This article is contributed. See the original author and article here.
The Windows Recovery Environment (WinRE) is a companion operating system installed alongside Windows 10, typically in a separate partition, that can help with troubleshooting, recovery, or booting from external media, such as a USB stick. WinRE is also used during the Windows update process to apply updates in specific paths or phases. (This process is sometimes referred to as SafeOS.)
In this post, we’re going to walk you through the tools in WinRE, offer tips and tricks for using it effectively, and, while we’re at it, clear up common misconceptions around WinRE. We’ll also show how WinRE can enable a Windows 10 device that might have issues starting or applying the latest updates, get back to a good state.
An overview of WinRE
When talking to IT pros, enthusiasts, and other Microsoft employees, I like to refer to WinRE as the “blue screen of life.” Some agree with me out of politeness, but I believe the phrase resonates with many people because, at the end of the day, WinRE is typically used to fix something.
WinRE is almost always located in a separate partition that immediately follows the main Windows partition. (For more details on the default partition layout for UEFI-based PCs, see our partition layout documentation.)
If you are familiar with Windows PE (WinPE), this may sound similar. Think of WinPE as the base OS and WinRE as the user interface with some recovery tools added.
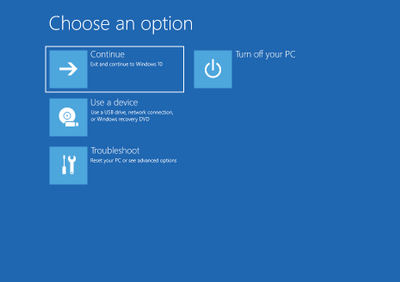
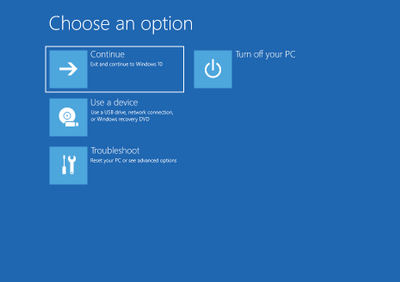
When you launch WinRE, you may see these options: Continue (exit WinRE and continue to Windows 10), Use a device (use a USB drive, network connection, or Windows recovery DVD), Troubleshoot (reset your PC or use advanced options), and Turn off your PC.
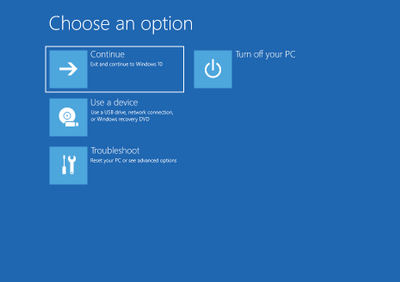
Figure 1. Initial WinRE menu options
Accessing WinRE
You can access WinRE via multiple entry points:
- From the Start menu, select Power then select and hold down the Shift key while selecting Restart.
- In Windows 10, select Start > Settings > Update & Security > Recovery. Under Advanced startup, select Restart now.
- By booting to recovery media.
- A hardware recovery button (or button combination) configured by the OEM.
Here are two lesser-known ways to access WinRE:
- Use REAgentC. From Windows 10, run a command prompt as an administrator, then type reagentc /boottore. Restart the device and it will load WinRE instead of Windows 10.
- The shutdown command also has an entry point for WinRE. Run command prompt as an administrator and type shutdown /r /o.
Okay, so now that you’re in WinRE, what can you do?
Depending on how you started WinRE, the options may differ. For example, if you boot from a USB stick, the Reset this PC option does not appear. You can continue to Windows 10 or turn off your PC.
If the options presented are not desired, select Continue to start Windows 10. Likewise, the Turn off your PC option will shut down the device. If you have multiple operating systems installed, this would also be where you could select which OS to boot.
Use a device
This option helps you boot from another source such as USB, DVD, or even a network connection. This can be helpful as it is simpler than some BIOS/Unified Extensible Firmware Interface (UEFI) menus and provides a consistent experience.
Troubleshoot
WinRE has many troubleshooting tools to help you get devices back to a good state quickly and easily. For more information, see Use WinRE to troubleshoot common startup issues.
Now, let’s explore the options available in the Troubleshoot category.
Reset this PC
Resetting a PC reinstalls Windows 10, but lets you choose whether to keep your files or remove them before reinstalling Windows. Reset this PC is the most popular option and offers a few options. (You can also access Reset this PC from the Settings menu if you can successfully start Windows 10.) For more information on Reset this PC, see Recovery options in Windows 10. I’ll also dive deeper into Reset this PC in future posts, so stay tuned!
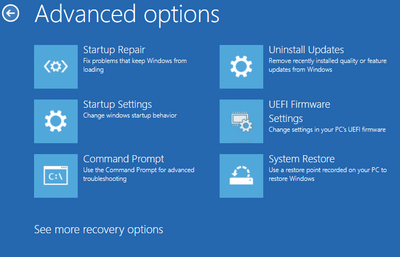
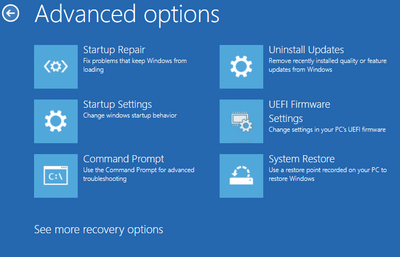
Figure 2. The Advanced options menu
Startup Repair
If Windows fails to start twice, the third attempt will run Startup Repair automatically. This is also available as an option on the advanced options page of troubleshooting. Startup Repair can help fix a corrupt master boot record (MBR), partition table, or boot sector. Beginning with Windows 10, version 1809, automatic Startup Repair also removes the most recently installed update if that installation immediately preceded the startup failure.
Startup Settings
Another troubleshooting step is to change how Windows starts up. Enabling debugging or boot logging can help identify a specific issue. This is also where you can enable Safe Mode. Check out the support page on Startup Settings for more information.
Command Prompt
While not the most approachable tool for unfamiliar users, the command prompt is the most powerful and dynamic tool in WinRE. It can do everything from registry edits to copying files to running Deployment Image Servicing and Management (DISM) commands. Next, we’ll cover a few notable examples. (Note that while using Command Prompt in WinRE, it automatically runs with elevated administrator permissions.)
Copying files
If you need to copy a few files from your device before reinstalling Windows, using a USB drive or network share can be a quick way to do this using the command prompt within WinRE.
There is also a popular Notepad trick that makes it easier to copy files. I love it and wish I could take credit as it a big timesaver for visual people like me. !
Chkdsk
Running chkdsk is a common first step to help resolve issues. This process checks the file system and file system metadata of a volume for logical and physical errors. (While in WinRE, drive letters may be assigned differently than in Windows 10. You can run BCDEdit to get the correct drive letters.)
SFC
SFC scans and verifies the integrity of all protected system files and replaces incorrect versions with correct versions. If this command discovers that a protected file has been overwritten, it retrieves the correct version of the file, and then replaces the incorrect file.
Repair corrupt components using DISM
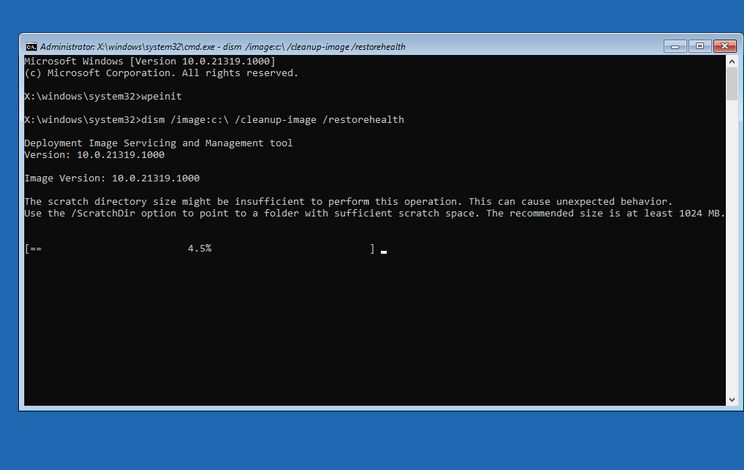
Windows system components may become corrupt from hard drive malfunctions or update issues. If you have a wired ethernet connection, you can turn on networking to then scan and repair corrupted content using Windows Update and the /Cleanup-Image switch in DISM.
From the command prompt, type wpeinit and Enter to turn on the networking stack then type the following command:
dism /image:c: /cleanup-image /restorehealth
Figure 3. Using DISM within the command prompt in WinRE
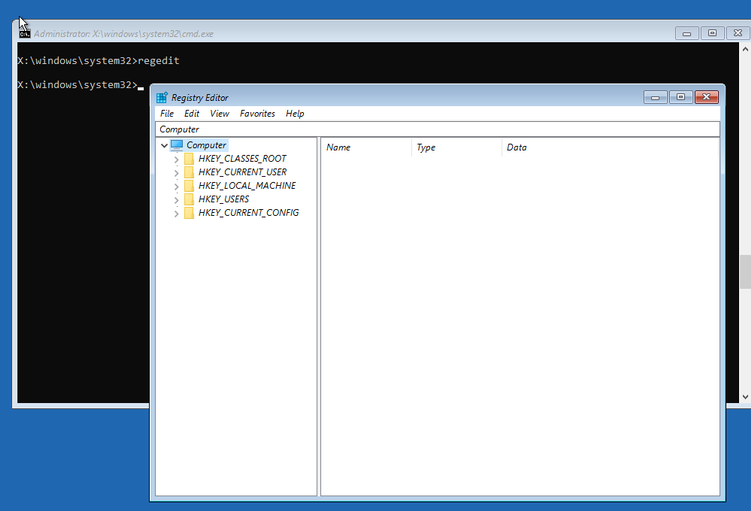
Registry Editor
Yes, you can use regedit within Windows RE, but warning: this is a powerful tool that can really mess things up if not used correctly! Keep in mind the X: drive is the WinRE OS and has its own registry. C: is likely where the Windows 10 registry is.
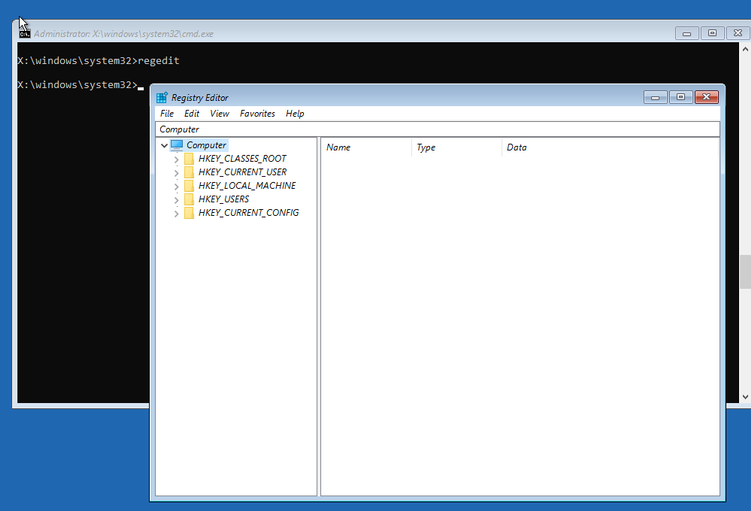
Figure 4. Launching the Registry Editor from the command prompt in WinRE
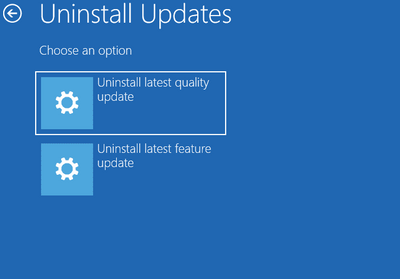
Uninstall Updates
Removing the latest updates recently installed to Windows 10 can be a good troubleshooting step if you are having trouble starting your PC or if you are having trouble uninstalling something within Windows 10. Simply select Uninstall latest quality update or Uninstall latest feature update to uninstall the desired update from WinRE with just a couple of steps. Please note; however, that you should reapply the latest updates as soon as possible to help keep your devices protected and productive.
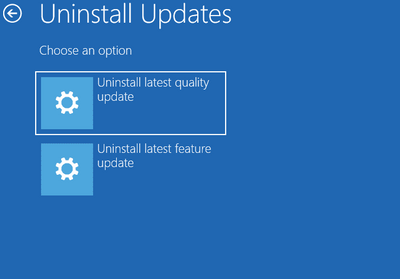
Figure 5. The Uninstall Updates menu
UEFI Firmware Settings
This option makes it easy to boot into the UEFI menu to change firmware settings, especially as the many different devices offered by OEMs use different keyboard or button combinations to access UEFI. For example, some use volume buttons, function keys, the delete key, or a combination therein. WinRE provides a consistent method for accessing UEFI firmware settings across all devices.
System Restore and System Image Recovery
These two options can be useful if you are using legacy system restore features or image-based recovery. The System Restore option can restore your PC to a previous restore point which, for example, could undo the latest win32 application installation if you captured a restore point prior to the installation.
Recovery Drive
Creating a recovery drive is a built-in Windows ability that can easily create a USB drive with WinRE. Optionally, it can also “back up system files to the recovery drive,” a process that takes a while but will fully reinstall Windows onto that same system even if the hard drive is blank. This is often referred to as Bare Metal Recovery (BMR). When starting your system from a Recovery Drive, you will notice that is uses WinRE to perform the recovery. You will need to pick your language first and there will then be an option on the first screen to “Recover from a drive.”
Managing WinRE
WinRE can help devices recover back to Windows, but, if needed, it can be disabled by opening an elevated command prompt and using the reagentc /disable command. By disabling WinRE, however, some Windows 10 features may not work, including many outlined in this blog post. Additionally, WinRE will be re-enabled after a feature update is installed as it is a critical part of the update process.
Permission and authentication
If you are a Windows Insider taking flights, you may have seen a behavior change on Windows 10 Insider Preview Build 19536 and later, where the default authentication requirements for WinRE are different. Previously, most tools and actions required local admin credentials but were not able to use modern credentials like Windows Hello (face, PIN, fingerprint). This became a big problem with passwordless accounts and Azure Active Directory accounts that weren’t backed up with a local admin account. To address this, we changed the default behavior to no longer require local administrator authentication to access WinRE tools.
If you manage devices using mobile device management (MDM) solutions such as Microsoft Endpoint Manager, you can configure the Security/RecoveryEnvironmentAuthentication policy if you would like to require local administrator authentication to use WinRE components.
Other interesting things
Booting into RAM
WinRE can be installed in the same partition as Windows, but it is usually installed in the Recovery or WinRE tools partition. Regardless of where it is installed, it always runs in the RAM (or RAM disk boot) and is assigned the X: drive. This is important to note because any changes you make to X: will not be saved after a reboot.
BitLocker
Depending on the combination of your entry points to WinRE, how BitLocker is configured (auto-unlock), and what WinRE option you select, you may be prompted for the BitLocker recovery key to unlock your Windows partition. As an example, when launching a command prompt, you will be prompted to unlock BitLocker. If you skip the unlock process, the Windows installation drive will remain locked, but you will have access to the X: drive, where WinRE runs in RAM.
BootIM.exe
One potentially confusing thing about WinRE is the implementation of BootIM.exe. Most won’t see a difference, but I want to explain how this works. When using the entry point from the lock/login screen and holding the Shift key or Settings > Advanced Startup, Windows 10 is not rebooting into WinRE. Instead, it is entering pre-shutdown and showing the BootIM screen which looks exactly like WinRE. If you select an option that needs to change the boot flag like Use a device, it saves you one restart because you don’t have to start WinRE to then restart the system again using a device.
You can see this functionality by running BootIM.exe from an elevated command prompt, but a quick tip is to open Task Manager beforehand so you can easily use the Alt + Tab combination and end the task when you are done. If you are a Windows Insider taking flights, you will see a behavior change beginning with Windows 10 Insider Preview Build 19577 to enable greater accessibility within this experience. As the pre-shutdown behavior doesn’t support Narrator or other accessibility features, BootIM will only be used if WinRE isn’t available. Otherwise, the system will restart directly to WinRE and skip BootIM.
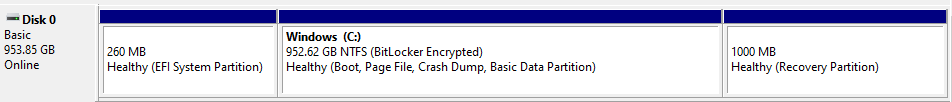
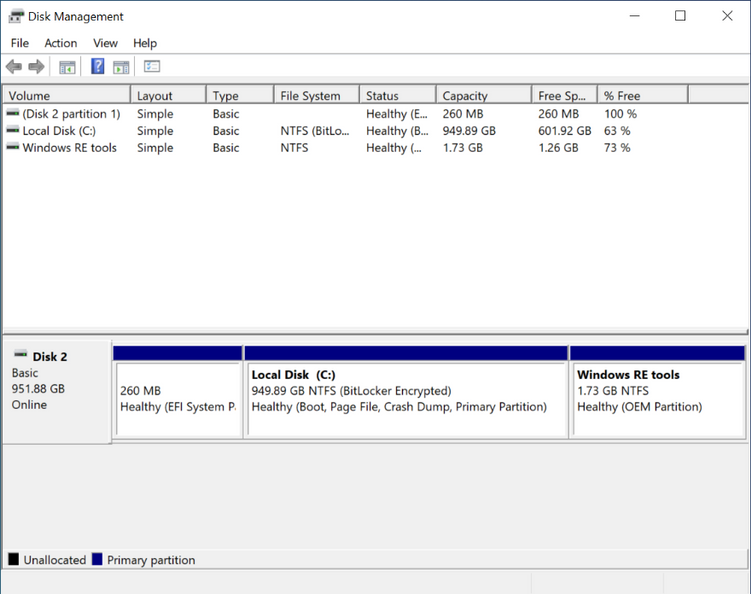
Partition layout
Prior to Windows 10, the recommended partition layout was to place the recovery partition before the OS partition. Unfortunately, this made it difficult to update WinRE. For Windows 10, we updated the recommendation to always list WinRE immediately after the OS partition. Depending on how Windows was originally installed, your partitions may not have this layout.
Even with the updated recommendation, OEMs have the flexibility to choose a different partition layout for specific solutions. When installing from USB, the legacy layout was still being used by some partners until it was formally updated in Windows 10, version 20H1. For example, in this screenshot from a newer laptop, the OEM put an Recovery Partition where it needs to go, last in line.
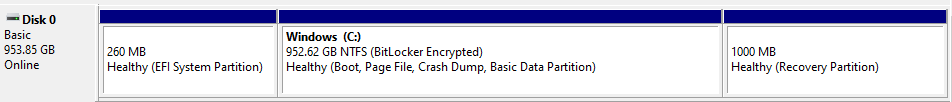
Figure 6. A Disk Management partition layout example
Recovery partition labeling
The WinRE partition can have any volume label or no label, but the most common labels are WinRE tools, WinRE, or Recovery. The label is subject to change upon update. The status could also say OEM Partition or Recovery Partition.
The WinRE partition shouldn’t have a drive letter assigned and any folders or files should not be available for editing. A common misunderstanding is that the recovery partition contains a compressed copy of Windows and that this copy is what is restored during the reset process. This is not the case. This partition only contains WinRE and drivers. The size can vary depending on how it was configured by the OEM (e.g., what languages and drivers were included).
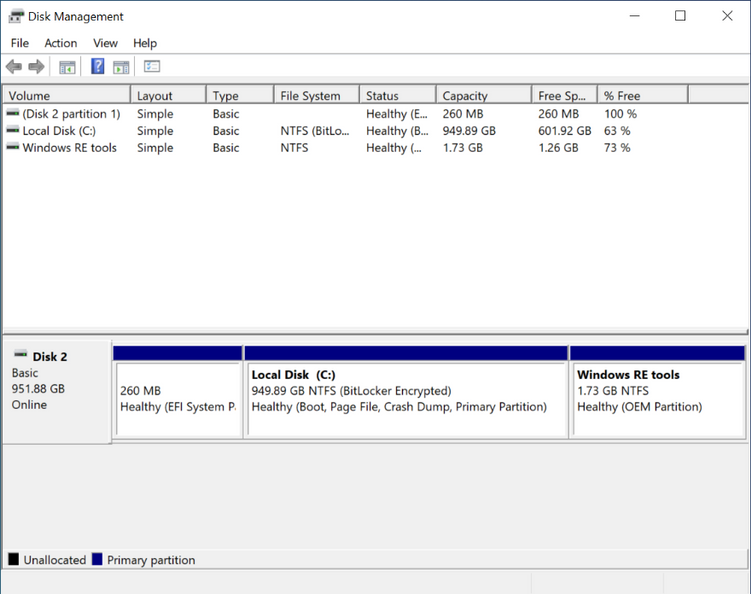
Figure 7. An example of labels within the Disk Management partition
Conclusion
In closing, I hope this information has been helpful and helps provide greater understanding about WinRE. As we continue to improve, we are always interested in your ideas and feedback, and ask that you please share them in Feedback Hub (<– this is direct link to the Advanced startup category that includes WinRE).
If you have ideas or requests on other aspects of recovery you’d like us to share, please let us know in the comments section below.
by Contributed | Apr 14, 2021 | Technology
This article is contributed. See the original author and article here.
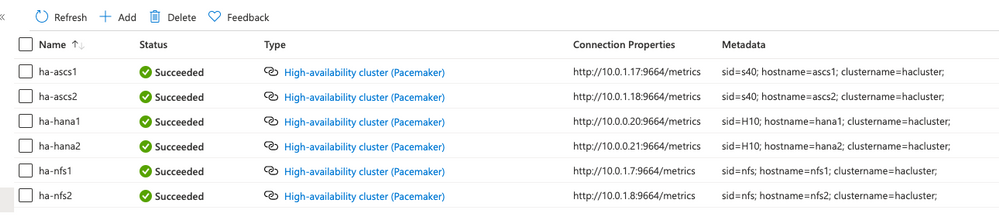
Introduction
The Azure Monitor for SAP solutions (AMS) team has announced new capabilities for AMS, including monitoring SAP NetWeaver metrics, OS metrics and enhanced High Availability cluster visualization. This blog post is an overview of the recent changes for the High Availability cluster provider for AMS and associated cluster workbook views.
The most important changes for the HA provider are in the workbook visualizations. You can now see:
- Location constraints that are left by “crm resource move” and “crm resource migrate” commands. These will change the operation of the cluster, and it’s useful to be reminded if they have been left in the cluster configuration.
- Historical node view. You can now see whether a cluster node is up, and is the “designated coordinator” for the cluster, for configurable time periods.
- Historical resource view. You can now see the failcount over time for individual cluster resources.
Prerequisites
To use AMS monitoring for your HA clusters, there are some requirements for your environment:
- One or more clusters of monitored Azure VMs or Azure Large instances.
- The OS for the cluster nodes currently should be SLES 12 or 15. Other OS options are in development.
- The Pacemaker cluster installation should be completed – there are instructions for this in Setting up Pacemaker on SLES in Azure – Azure Virtual Machines
- The monitored instances must be reachable over the network that AMS is deployed to. Also, the HA provider uses HTTP requests to the monitored instances to retrieve monitoring data, so this must be enabled.
The AMS team has tested monitoring several different types of cluster managed applications with the AMS HA provider, including
- SUSE Linux Network File System (NFS)
- SAP HANA
- IBM DB/2
- SAP Netweaver Central Services
Other managed applications and services should work with the AMS HA provider, but are not officially supported.
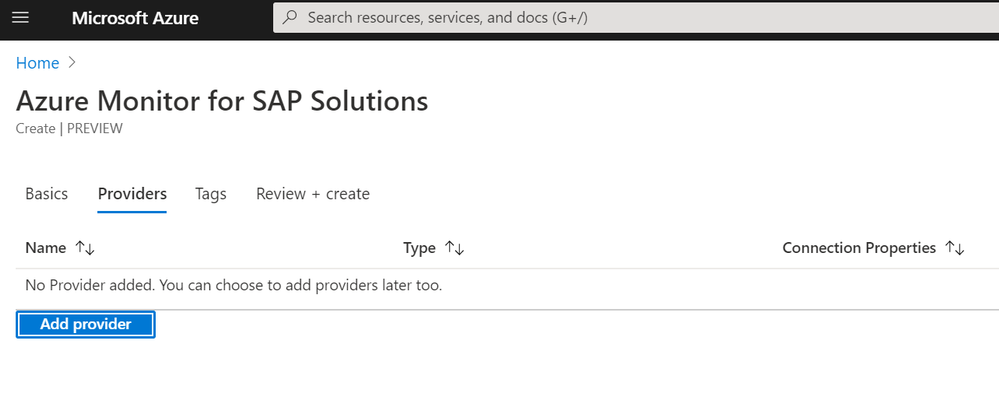
Setting up the HA Provider
The process for setting up the HA provider hasn’t changed, but here is a walkthrough of the process for setting up your cluster, AMS, and the HA cluster providers:
- Create your HA cluster in Azure, using the instructions linked above.
- Install the Prometheus ha_cluster_exporter in each of the cluster nodes, following the instructions here. For each instance, log onto the machine as root and install using the zypper package manager:
zypper install prometheus-ha_cluster_exporter
After the exporter is installed you can enable it (so it is automatically started on future reboots of the instance):
systemctl –now enable prometheus-ha_cluster_exporter
After this is done, it is useful to test that the cluster exporter is actually working. From another machine on the same network, you can test this using the Linux “curl” command (using the proper machine name). For example:
testuser@linuxjumpbox:~> curl http://hana1:9664/metrics
# HELP ha_cluster_corosync_member_votes How many votes each member node has contributed with to the current quorum
# TYPE ha_cluster_corosync_member_votes gauge
ha_cluster_corosync_member_votes{local=”false”,node=”hana2″,node_id=”2″} 1
ha_cluster_corosync_member_votes{local=”true”,node=”hana1″,node_id=”1″} 1
# HELP ha_cluster_corosync_quorate Whether or not the cluster is quorate
# TYPE ha_cluster_corosync_quorate gauge
ha_cluster_corosync_quorate 1
…
You should configure a HA cluster provider for each node of the cluster using the following information:
- Type – High-availability cluster(Pacemaker)
- Name – a unique name you give the cluster provider. I use a pattern of “ha-nodename” for this.
- Prometheus Endpoint – this is the same as the URL you used to test the cluster exporter above, and usually will be
http://nodeipaddr:9664/metrics
- SID – this is three-character abbreviation to identify the cluster – if this is an SAP instance, you should make this the same as the SAP SID
- Hostname – this is the hostname for the monitored node
- Cluster – this is the name of the monitored cluster – you can find this out by doing the following on a cluster instance:
hana1:~ # crm config show | grep cluster-name
cluster-name=hacluster
- When finished, select Add provider
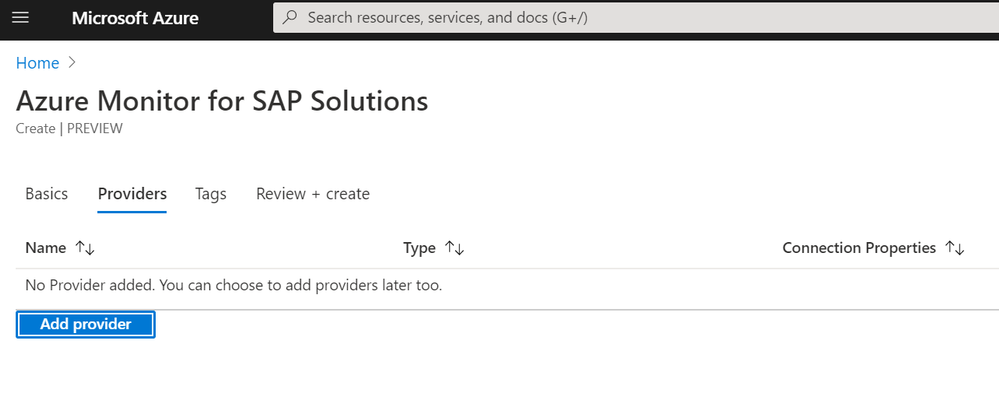
As an example, here is a subscription with three clusters – one for NFS, one for SAP HANA, and one for SAP central services. The provider view looks like this:
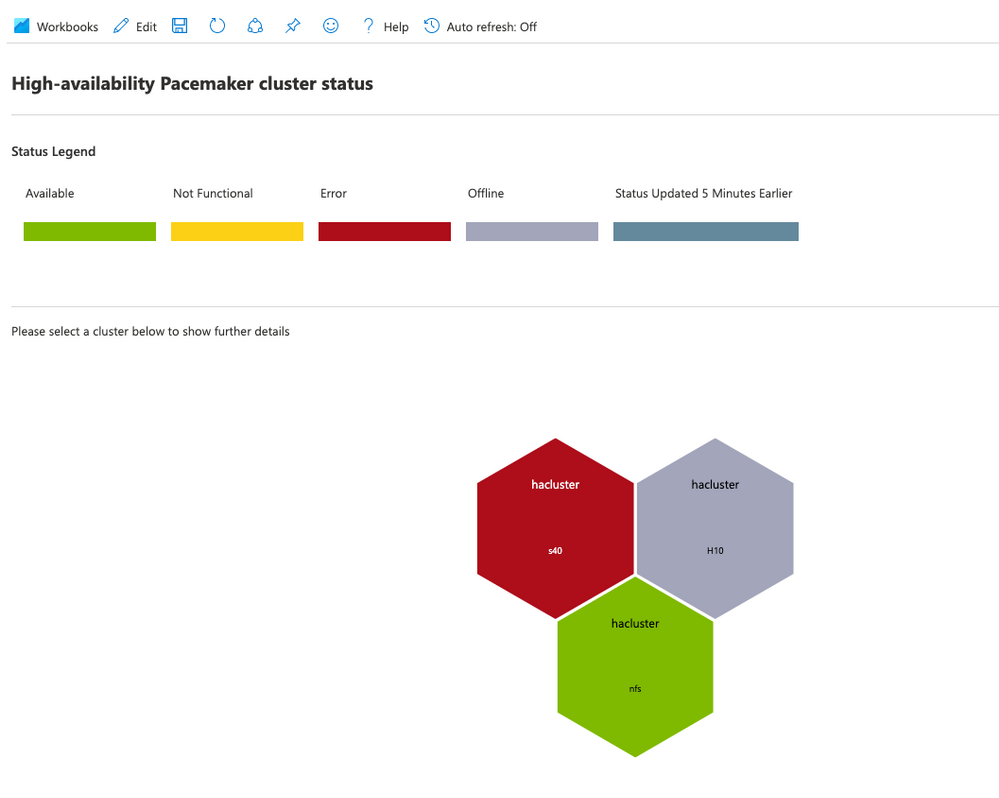
Overview of the new views
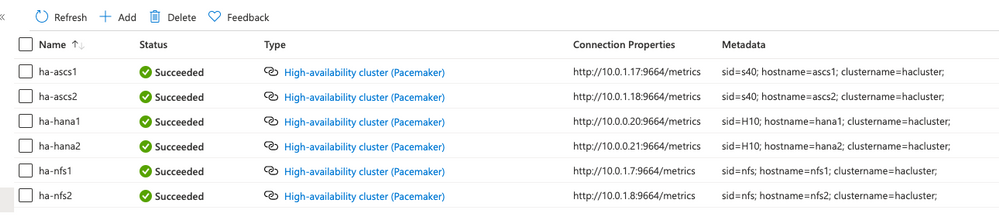
Continuing with the example of the resource group with three clusters, here is the overall HA cluster status:
Here, you can tell that there are three clusters, but only one of them (the NFS cluster) is in a healthy state. The H10 cluster is in maintenance mode, which means the cluster is not managing cluster resources. The s40 cluster has had errors in the resource state.
Cli location constraints
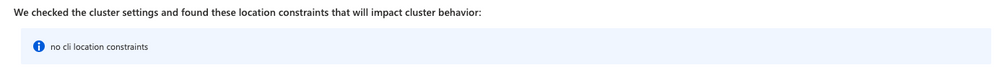
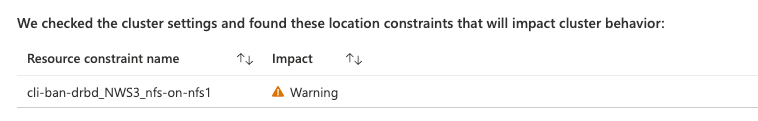
When you select one of the cluster hexagons, you will see more information on that specific cluster. First, there is information on cli-ban or cli-prefer location constraints in the cluster configuration. These constraints are created by commands such as crm resource move or crm resource migrate. This is what you will see in the HA workbook if there are no such constraints:
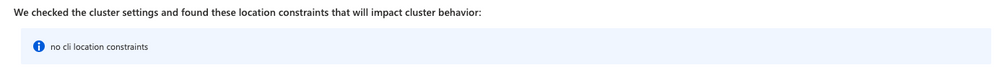
If there are any of these constraints, you will see the constraint names:
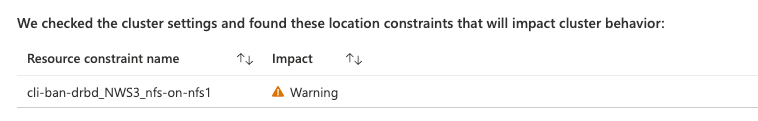
You should remove these constraints after the resource movement has been completed using the “crm configure delete <constraint name>” command. If you do not, they will impact the expected operation of the cluster.
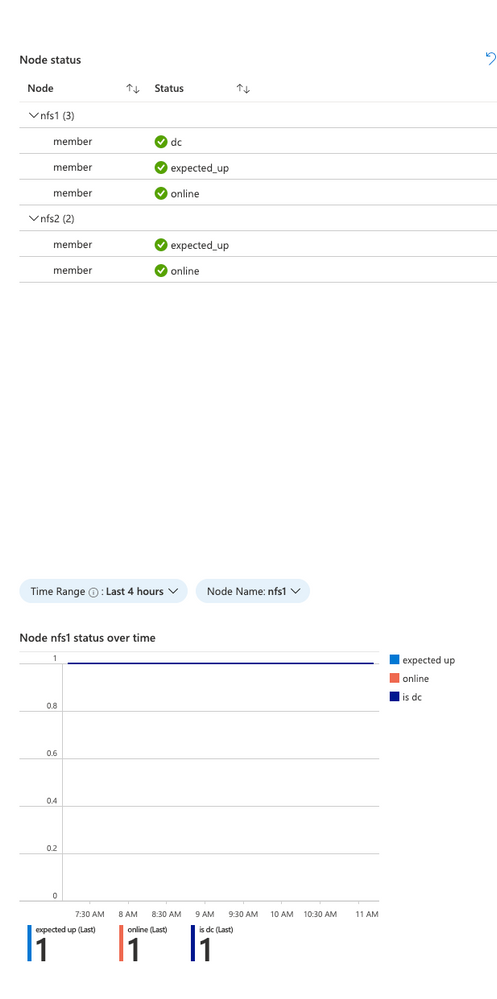
Node status over time
In the cluster view, you will see the current node status for each node in the cluster, and you will now also see the historical status of a particular node at the bottom:
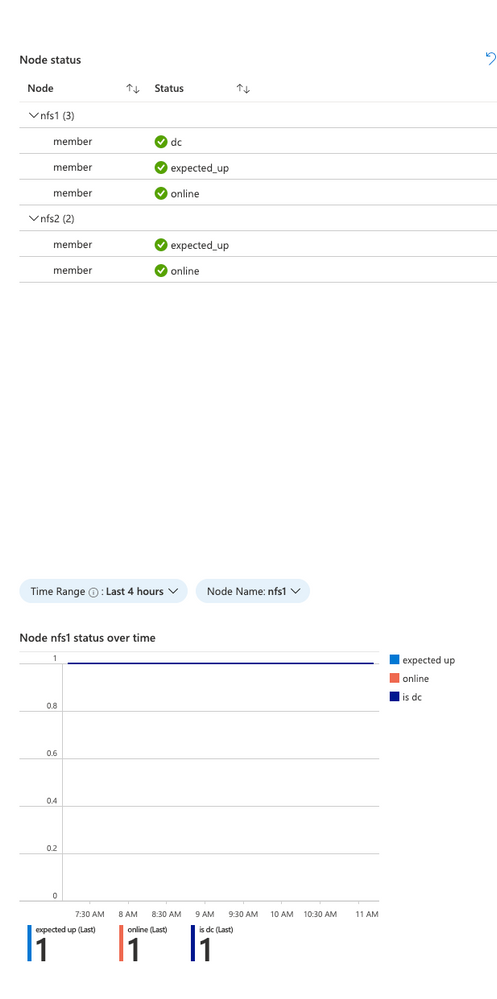
The Time range and node are selectable in this view. This is useful to see when a particular node went offline from the standpoint of the cluster. It will also indicate which of the nodes is the clusters “designated coordinator”.
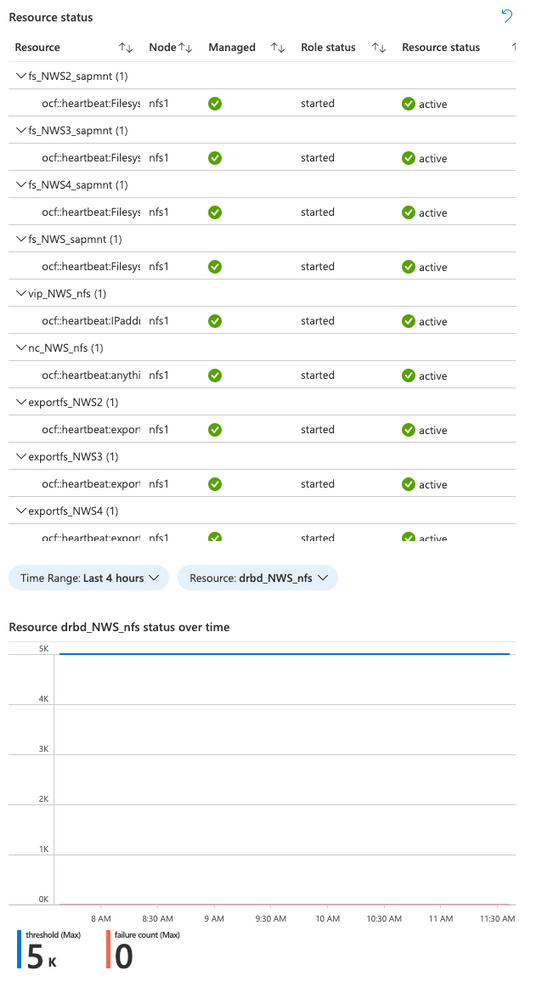
Resource status over time
The cluster view will show the current resource status for the cluster managed resources, and there is now a historical view of the failure counts for a selected resource:
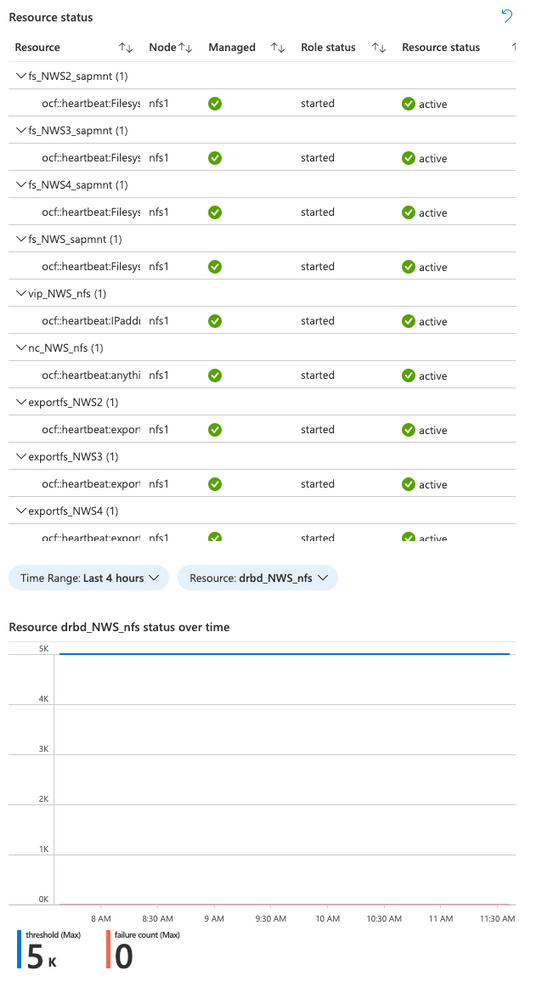
Again, the time range and resource are selectable in this view. It shows the failure count and failure threshold for the selected resource – If the failure count reaches the threshold, the resource will be moved to another node. Any errors should be investigated and resolved if possible.
Resources
Here are some additional resource links for learning about Azure Monitor for SAP Solutions and providers for other monitoring information:
Feedback form:
Summary
We hope you will find the new visualizations helpful, and please let us know if you have ideas for any new features for Azure Monitor for SAP solutions.
by Contributed | Apr 14, 2021 | Technology
This article is contributed. See the original author and article here.
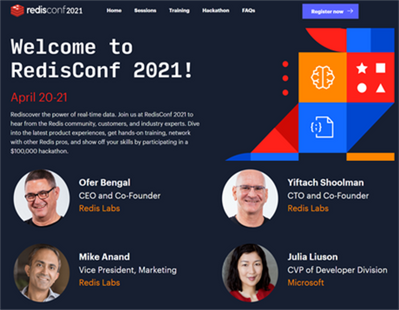
Spring has arrived, which means that RedisConf—the annual celebration of all things Redis—is almost here! Attending RedisConf is one of the best ways to sharpen your Redis skills by exploring best practices, learning about new features, and hearing from industry experts. You’ll also be able to virtually hang out with and learn from thousands of other developers passionate about Redis.
We love Redis here at Microsoft, so we’re excited to be showing up at RedisConf in a big way this year. We’ll not only be talking more about our new Azure Cache for Redis Enterprise offering, but we’ll also be hosting sessions and panels that dive deeper into the best ways to use Redis on Azure. Want to learn more? Here are seven reasons to attend RedisConf 2021:
- Explore live and on-demand training on how to use Redis with popular frameworks like Spring and .NET Core.
- Hear Microsoft CVP Julia Liuson present a keynote status update about the ongoing collaboration between Microsoft and Redis Labs, including the Enterprise tiers of Azure Cache for Redis.
- Listen to customers like Genesys, Adobe, and SitePro who are using Redis Enterprise on Azure for use-cases as diverse as IoT data ingestion and mobile push notification deduplication.
- Tune in for a roundtable discussion between the Microsoft and Redis Labs teams that touches on what the collaboration between the companies looks like and the benefits it brings to customers.
- Learn how to harness the power of Redis and Apache Kafka to crunch high-velocity time series data through the power of RedisTimeSeries.
- Hear from experts from our product team on the best way to run Redis on Azure, including tips-and-tricks for maximizing performance, ensuring network security, limiting costs, and building enterprise-scale deployments.
RedisConf kicks off on April 20th, and registration is free! Sign-up now to attend. We’ll see you there.




Recent Comments