
by Contributed | Dec 4, 2020 | Azure, Microsoft, Technology
This article is contributed. See the original author and article here.
Big announcement surrounding the general availability of Azure Synapse Analytics and the public preview release of Azure Purview data catalog is covered this week on AzUpdate. Other news items covered include: Azure AD Application Proxy now natively supports apps that use header-based authentication, and the Microsoft Learn Module of the week.
Azure Synapse now Generally Available
Solutions like data lakes and data warehouses have helped organizations collect and analyze several types of data. The process however, created niches of expertise and specialized technology. Azure Synapse rearchitects operational and analytics data stores to take full advantage of a new, cloud-native architecture. The solution enables organizations to query data using either serverless or dedicated resources at scale while maintaining consistent tools and languages. Think of it as your organization’s one pane of glass to analyze all its captured data. Azure Synapse combines capabilities spanning the needs of data engineering, machine learning, and BI without creating silos in processes and tools.
Further details can be found here: Harnessing the power of Azure Synapse for improved data and analytics
Details have also been shared on how Microsoft’s Modern Workplace team in partnership with CMS Medicare developed an end-to-end Azure Synapse and Power BI tutorial including over 120 million rows of real CMS Medicare Part D Data to help other organizations learn how to harness it.
The entire step-by-step tutorial including the demo public domain Part D data can be viewed here: How to Deploy an End-to-End Azure Synapse Analytics and Power BI Solution
Public Preview of Azure Purview data catalog
Announced alongside Azure Synapse, Azure Purview enters public preview and provides a comprehensive data governance solution enabling organizations to know where all thier data resides. The solution can easily create an up-to-date map of an organization’s data landscape with automated data discovery, sensitive data classification, and end-to-end data lineage wherever it is stored including on-premises, across multi-clouds and multi-edge, in SaaS apps, and in Microsoft Power BI. Azure Purview is integrated with Microsoft Information Protection thus enabling the ability to apply the same sensitivity labels defined in Microsoft 365 Compliance Center.
Further details can be found here: Azure Purview
Azure AD Application Proxy now natively supports apps that use header-based authentication
Public preview of Application Proxy support for applications that use header-based authentication on standard claims that are issued by Azure AD is now available. Some examples of said applications include NetWeaver Portal, Peoplesoft, and WebCenter of which can benefit from all the capabilities of Application Proxy, including single sign-on as well as enforcing pre-authentication and Conditional Access policies like requiring Multi-Factor Authentication (MFA) or using a compliant device before users can access these apps. What’s more, no added software is required as existing Application Proxy connectors can be used.
Steps on how to harness this can be found here: How to enable Azure AD Application Proxy to support apps using header-based authentication
Community Events
- Create: Data – A half day of conversations with experts and community to learn and discuss everything data – from the upcoming trends, to best practices and data for good.
- All Around Azure – A Beginners Guide to IoT – Focus on topics ranging from IoT device connectivity, IoT data communication strategies, use of artificial intelligence at the edge, data processing considerations for IoT data, and IoT solutioning based on the Azure IoT reference architecture
- Festive Tech Calendar – Continuing this month’s content from different Azure communities and people around the globe for the month of December
- Introduction to Cloud Adoption Framework – Sarah Lean investigates Microsoft’s Cloud Adoption Framework offering and what is available for organizations to take advantage of
MS Learn Module of the Week

Realize Integrated Analytical Solutions with Azure Synapse Analytics
This learning path provides details on how Azure Synapse Analytics enables you to perform different types of analytics through its’ components that can be used to build Modern Data Warehouses through to Advanced Analytical solutions.
This learning path can be completed here: Integrated Analytical Solutions via Azure Synapse Analytics
Let us know in the comments below if there are any news items you would like to see covered in next week show. Az Update streams live every Friday so be sure to catch the next episode and join us in the live chat.

by Contributed | Dec 3, 2020 | Technology
This article is contributed. See the original author and article here.

In 2020, developers (along with the rest of the world) were challenged like never before, but the traits of determination and persistence describe practically every dev. I mean, honestly, you can’t code without them – like when you get an error and realize you forgot a “;” somewhere and are scrolling through your IDE for dayyyssss – sigh.
So, to get our first week of #DevDecember off to a running start, we highlighted how resourceful developers proved to be in overcoming unexpected circumstances. Throughout the week we’ve shared various pieces of content that highlight this growth and determination.
But, before we get to recapping those, we wanted to highlight a few fun things that we are doing in #DevDecember this year:
Reflect with our fun fill-in-the-blank

So much of getting through the year was about bridging gaps, so we thought a fill-in-the-blank would be the best way to review some of the ways you became more skilled and resilient as a dev. Check out the template, fill it in, tag it as #DevDecember, and share what you got done and how.
#DevWithABev fun on social
 Before we recap, we should also mention #DevWithABev, a growing collection of developer-with-a-beverage selfies. Check out everyone’s favorite winter beverage, and add your own personal flavor by taking a snapshot of yourself with yours and tagging it #DevWithABev. It’s 2020 and we could all use some friendly faces.
Before we recap, we should also mention #DevWithABev, a growing collection of developer-with-a-beverage selfies. Check out everyone’s favorite winter beverage, and add your own personal flavor by taking a snapshot of yourself with yours and tagging it #DevWithABev. It’s 2020 and we could all use some friendly faces.
Now, let’s recap what we highlighted this week:
Beginner’s series to JavaScript
Taking your first steps toward mastering a new programming language is exciting, but it can also feel overwhelming. To help you get started with JavaScript, we’ve created short and easy-to-consume videos that break down the key concepts you need to know.
Start watching the series
Agrotech IoT workshop
Want to grow your professional IoT skills? Your first stop may be the garden. Get your hands dirty with a workshop on how to build an internet-connected device to gather soil moisture data that will tell you (by lighting up an LED) if a plant needs watering.
Start digging in
Bringing browser developer tools to Visual Studio Code
One of our favorite releases in 2020 was the Microsoft Edge Tools for VS Code extension, designed to simplify workflows. Connect to an existing browser instance, start a new one, or use a “headless” browser.
Explore the extension
Building a first “Power Apps” app
@JoeCamp13 built an app to track inventory entirely with Power Apps. His explanation of how he did it, is illustrated with screenshots so you can follow along.
Start the walkthrough
Next week, we’ll talk about some of the ways the dev community came together in 2020. Keep following #DevDecember for daily updates and affirmations of awesomeness.
Not sure what #DevDecember is all about? Check out our homepage for more info!

by Contributed | Dec 3, 2020 | Technology
This article is contributed. See the original author and article here.
We recently had a case escalation and wanted to provide a few more details on a Windows 10 certificate issue. Windows has documented the behavior and resolution. There’s been additional blog posts describing this scenario by several of our MVP’s. In this post, we’ll add on a script we developed to detect whether or not the Intune Mobile Device Management (MDM) enrollment certificate is on a co-managed Windows device and provide a few recommendations for how to resolve.
Let’s start with what devices could be affected:
From the Windows KB article – “System and user certificates might be lost when updating a device from Windows 10, version 1809 or later to a later version of Windows 10. Devices will only be impacted if they have already installed any Latest cumulative update (LCU) released September 16, 2020 or later and then proceed to update to a later version of Windows 10 from media or an installation source which does not have an LCU released October 13, 2020 or later integrated.”
We see impact when managed devices are upgraded using outdated bundles or media through an update management tool such as Windows Server Update Services (WSUS) or Configuration Manager. This might also happen when using outdated physical media or ISO images that do not have the latest updates integrated.
From a device perspective, here’s what you’ll see:
- The MDM enrollment certificate is no longer on the Windows device. Once this certificate is not on the device, it can’t establish the trust needed to get policy from Intune.
- The Windows 10 device may no longer have corporate Wi-Fi, VPN, or other certificate-based authentication policies.
- End users may report they are unable to access sites that they typically had access to (and there’s no other compliance policy or issue affecting their access).
- You may notice a high volume of traffic in the Intune Management Extension logs.
What you can do to determine impact:
The sample script linked below is specifically developed for Intune co-managed devices and can be deployed to find those Windows 10 devices that don’t have the MDM enrollment certificate. We’ve tested this script in our internal environment and also worked with a customer to run the detection portion of the script. Please keep in mind the script is unsupported. If we make any changes to it, we’ll update this post.
You can download the script here – https://aka.ms/mdm_enrollment_cert_script
Again, as shared above this script will only work on Intune co-managed devices – those that have the ConfigMgr client installed and are enrolled into Intune. As described in what devices could be affected, there are a number of other scenarios that could be affected depending on your update path.
How you can mitigate impact:
You have a few different options, depending on your preferred approach:
- If you have already encountered this issue on your device, you can mitigate it within the uninstall window by going back to your previous version of Windows using the instructions here. Windows has documented this as the preferred approach in their KB article.
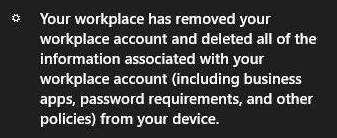
- The sample script we shared above includes optional remediation logic for co-managed devices. One important end-user caveat though, if you use this remediation logic, the following message will appear in the Windows 10 notification center when the device is unenrolled before it is re-enrolled:
This is a standard your device is being unenrolled message which is what the script automates. Once re-enrolled, though, policy will return apps and settings.
Other information:
- The detection logic in the script only returns the devices missing the MDM enrollment certificate.
- You can run the script in detection only mode vs. remediation:
- Running mdmcertcheckandremediate.ps1 without any parameters is detection mode only.
- Running mdmcertcheckandremediate.ps1 -Remediate 1 is detect and remediate.
- If you are a co-managed customer, the remediation process of re-enrolling the device to Intune is done by the Configuration Manager client (ccmexec) based on the co-management policy targeted. The ConfigMgr client uses existing co-management enrollment process if the domain joined device remains in Azure AD-joined state or enrollment is retried as soon as the device re-joins to Azure AD. Co-management enrollment is retried when ccmexec starts up and also during scheduled co-management enrollment process scheduled every day.
Again, keep us posted if you have any feedback by responding on this post or tagging @Intunesuppteam out on Twitter!
by Contributed | Dec 3, 2020 | Technology
This article is contributed. See the original author and article here.
While volume activation is a process that many have utilized over the years, today’s post offers guidance to help you ensure that all your devices have been properly activated regardless of their connection to your organization’s network.
First, a refresher. Volume activation enables a wide range of Windows devices to receive a volume license and be activated automatically and en masse versus tediously entering an activation key on each Windows device manually.
The most common methods of volume activation require that devices to be connected to an organization’s network or connected via virtual private network (VPN) to “check in” from time to time with the organization’s activation service to maintain their licenses. When people work from home and off the corporate or school network; however, their devices’ ability to receive or maintain activation is limited.
Volume activation methods
There are several methods to activate devices via volume licensing. For detailed information, see Plan for volume activation. Here, however, is a summary for easy reference.
Key Management Service
Key Management Service (KMS) activation requires TCP/IP connectivity to, and accessibility from, an organization’s private network so that licenses are not accessible to anyone outside of the organization. By default, KMS hosts and clients use DNS to publish and find the KMS key. Default settings can be used, which require little or no administrative action, or KMS hosts and client computers can be manually configured based on network configuration and security requirements.
KMS activations are valid for 180 days (the activation validity interval). KMS client computers must renew their activation by connecting to the KMS host at least once every 180 days. By default, KMS client computers attempt to renew their activation every 7 days. If KMS activation fails, the client computer retries to reach the host every two hours. After a client computer’s activation is renewed, the activation validity interval begins again.
Multiple Activation Key
A Multiple Activation Key (MAK) is used for one-time activation with Microsoft’s hosted activation services. Each MAK has a predetermined number of activations allowed. This number is based on volume licensing agreements, and it might not match the organization’s exact license count. Each activation that uses a MAK with the Microsoft-hosted activation service counts toward the activation limit.
You can use a MAK for individual computers or with an image that can be duplicated or installed using Microsoft deployment solutions. You can also use a MAK on a computer that was originally configured to use KMS activation, which is useful for moving a computer off the core network to a disconnected environment.
Active Directory-based activation
Active Directory-based activation is similar to KMS activation but uses Active Directory instead of a separate service. Active Directory-based activation is implemented as a role service that relies on Active Directory Domain Services to store activation objects. Active Directory-based activation requires that the forest schema be updated using adprep.exe on a supported server operating system, but after the schema is updated, older domain controllers can still activate clients.
Devices activated via Active Directory maintain their activated state for up to 180 days after the last contact with the domain. Devices periodically attempt to reactivate (every seven days by default) before the end of that period and, again, at the end of the 180 days.
Windows 10 Subscription Activation
Starting with Windows 10, version 1703 Windows 10 Pro supports the Subscription Activation feature, enabling users to “step-up” from Windows 10 Pro to Windows 10 Enterprise automatically if they are subscribed to Windows 10 Enterprise E3 or E5.
With Windows 10, version 1903 the Subscription Activation feature also supports the ability to step-up from Windows 10 Pro Education to the Enterprise grade edition for educational institutions – Windows 10 Education.
The Subscription Activation feature eliminates the need to manually deploy Windows 10 Enterprise or Education images on each target device, then later standing up on-prem key management services such as KMS or MAK based activation, entering GVLKs, and subsequently rebooting client devices.
To step a device up to Windows 10 Education via Subscription Activation the device must meet the following requirements:
- Windows 10 Pro Education, version 1903 or later installed on the devices to be upgraded.
- A device with a Windows 10 Pro Education digital license. You can confirm this information in Settings > Update & Security > Activation.
- The Education tenant must have an active subscription to Microsoft 365 with a Windows 10 Enterprise license or a Windows 10 Enterprise or Education subscription.
- Devices must be Azure AD-joined or Hybrid Azure AD joined. Workgroup-joined or Azure AD registered devices are not supported.
Volume activation while working from home
If you activate devices in your organization using MAK, the activation process is straightforward and the devices are permanently activated. If you are using KMS or Active Directory-based Activation, each device must connect to the organization’s local network at least once every 180 days to “check in” with either the KMS host or the Active Directory domain controller. Otherwise, the user will be warned to activate Windows again.
With many users working or taking classes from home, a connection to the organization’s network may not exist, which would ultimately leave their devices in a deactivated state. There are a few options to avoid this:
- Use a VPN. By having the device connect to your organization’s network via a VPN, it will be able to contact a KMS host or Active Directory domain controller and will be able to maintain its activation status. If you manage your devices through a wholly on-premises solution to deploy policies, collect inventory, and deploy updates and other software, there is a good chance you are already using a VPN. Depending on the VPN configuration, some manual configuration of the client device may be required to ensure the KMS service is accessible through the VPN. For more details on these settings, which can be implemented via script, see Slmgr.vbs options for obtaining volume activation information.
- Convert the devices from KMS to MAK activation. By converting from KMS to MAK activation, you replace the license that requires reactivation every 180 days with a permanent one, which requires no additional check-in process. There are some cases—in educational organizations, for example—where each device is re-imaged at the end of the school year to get ready for the next class. In this case, the license must be “reclaimed” by contacting your Microsoft licensing rep or a Microsoft Licensing Activation Center.
One way of converting a device from KMS to MAK activation is to use the Windows Configuration Designer app (available from the Microsoft Store) to create a provisioning package, which includes the MAK, and deploy the package through email or a management solution such as Microsoft Intune.
You can also deploy a MAK directly within Intune without creating a provisioning package by creating a simple PowerShell script with the following commands and deploying the script to a user group:
slmgr.vbs /ipk XXXXX-XXXXX-XXXXX-XXXXX-XXXXX
slmgr.vbs /ato
(In the example above, XXXXX-XXXXX-XXXXX-XXXXX-XXXXX is your MAK key.)
It is important to monitor the success of these activations and remove users from the target group once their devices have been activated so that their other devices do not receive a new license.
- Use Subscription Activation. This requires the devices to be joined to your Azure AD domain, enabling activation in the cloud. This is possible if you have one of the following subscriptions:
- Windows 10 Enterprise E3/E5
- Windows 10 Education A3/A5
- Windows 10 Enterprise with Software Assurance
- Microsoft 365 E3/E5
- Microsoft 365 E3/A5
- Microsoft 365 F1/F3
- Microsoft 365 Business Premium
If you need assistance and have one of the preceding subscriptions with at least 150 licenses, you may be eligible for assistance through FastTrack. Contact your Microsoft representative or request assistance from FastTrack and a Microsoft FastTrack representative will contact you directly.
Conclusion
Windows volume activation has been around for a long time, but the increased number of users working from home may require your organization to re-evaluate how to best keep your devices activated if they cannot reach your on-premises activation service if you are using KMS or Active Directory-based Activation. It is important to consider the options available to you to ensure your devices stay activated. As always, there is no “one-size-fits-all” approach, so consider the pros and cons of each option as you plan on how to best support your remote workers and students.
To learn more about activation, see Activate clients running Windows 10.
by Contributed | Dec 3, 2020 | Technology
This article is contributed. See the original author and article here.
We’re excited to announce the new Universal Print Partner Integrations page, offering details about partner solutions and how they integrate with Universal Print.
Microsoft partners have been instrumental in delivering solutions to satisfy diverse requirements, including industry-specific solutions that integrate valuable printing and print management functionality. This new page will be especially helpful for IT administrators who want to get a better view of the availability of these solutions, and how they can make them work for their organizations. In addition to technical solution briefs, you’ll also find demos, videos, and quick links to blog posts and partner websites.
We hope you find this page useful and visit it often. We will add new resources and partners monthly and regularly update the page as our Universal Print partners make progress with their solution and integration development. For quick access, bookmark https://aka.ms/UPintegrations.
![[Guest Blog] Mixed Reality and the Human Component of Innovation](https://www.drware.com/wp-content/uploads/2020/12/medium-20)
by Contributed | Dec 3, 2020 | Assistive Technologies, Microsoft, Technology
This article is contributed. See the original author and article here.
This article was written by community member Alexandra Petty, a Mixed Reality Evangelist and Change Management Consultant in the Netherlands as part of our new #HumansofMixedReality guest blogger series, which seeks to humanize the world of mixed reality. In this series, we’ll spotlight the wonderful people working in the mixed reality space globally. Read on to hear her story about why she believes this technology can truly transform lives.
Meet Alexandra – this is her story:

Meet Alexandra Petty, Mixed Reality Evangelist and Change Management Consultant in the Netherlands
Let me start off by saying that I am a CODA, i.e child of deaf adult(s). I love discovering how we can make innovative technology work for all of us and our loved ones, and to make this world and our lives a more meaningful one. I’ve personally seen how technology has empowered my mother to make meaningful connections through the use of her smartphone. It opened up a world of possibilities for her, and now she can now leverage all forms of content – from video calling, to speech and text. I cannot wait to see how we continue to push boundaries of technology in helping empower people with various accessibility needs.
New technologies are very exciting – and not just from a technical perspective. I think it’s exciting from a human perspective. How can it work for us? How can we use it to improve someone’s quality of life? How can we use this to improve the quality of our work?
Now focusing back on a topic much closer to our hearts here in the Mixed Reality Community – what can Mixed Reality really do? I think, anything. With near limitless possibilities, driving Mixed Reality to its boundaries is exciting. Sometimes so exciting that we lose sight of the human component. Many end-users out there aren’t even aware that this technology exists, let alone understand how it works. We need to help bridge that knowledge gap so others can also learn and benefit from this technology.
Next to that, as with any technology innovation, there is a strong need for the human perspective as well. Privacy concerns and ethics matter. Just because we can do it, doesn’t mean we should do it. Especially now where we’re discovering more about artificial intelligence and contextualizing data within our environment and visualizing it.
I invite you to join me in a thought experiment:
Imagine you’re an engineer tasked with correctly positioning side mirrors on a car. Every shift you make needs to be recalculated to see if it fits within the norm of so many different countries. Now imagine you can just do that with the help of Mixed Reality, Edge Computing and AI. No more having to always go back to the drawing board, but immediately perfecting what you can do in real-time. It’s a very clear value-add to a business process and someone’s day to day work. Better yet, the various scenarios in which this can be applied is endless.
Sounds revolutionary? This scenario is actually not new, and has actually already been shown at Microsoft Ignite three years ago. With a little bit more context and accuracy, of course.
Let’s continue our thought experiment:
Now imagine working as a healthcare professional and you could just see the patient information at a glance, right in your field of view, when you’re talking to your patient. No more rifling through documents to look up the file, spending time at a desk instead of spending critical face-to-face time with your patient. All the information of your patient, you can easily just review and pull up whilst sitting face-to-face with your patient.
The technology is there- it can already do it using Mixed Reality, Edge computing, AI and Azure Services. The ethics, privacy laws and, most importantly, global awareness is where the challenges lie, and is something that all of us as Mixed Reality professionals continue to work on daily. So few people are actually aware of what Mixed Reality truly is. How can we, as pioneers and early adopters, the driving force behind this technology, help our fellow human beings understand how this can work for them?
Here’s where the strong human perspective at the conception of any innovation becomes critical.
Let’s say, as a business you understand the need for innovation. You have:
- Your scenarios well thought out and clearly identified
- The means to research and fund this innovation
- Finally come to the conclusion that this would benefit your employees and ultimately your business
What next? How do you make this change successful within your organization? How do you ensure that your employees will have room to process this change, to adapt, learn and truly embrace this technology? The answer is simple: You need to have a human-centered lens, understand how humans perceive innovation and change, and then help facilitate them through the tech adoption process.
Involve the change management team, your early adopters and identify ambassadors right from the start. When implementing Mixed Reality solutions, there is also a strong behavioral change involved. Unlike typical desktop/ line of business applications, you’re not simply replacing one application with another. You’re moving into an entirely new space, often with a new form factor that people are not familiar with, and may find intimidating. Think about how ubiquitous mobile phones are today, and how almost everyone is glued to one wherever they go – that was not always the case. We all have to start somewhere with new technology and build familiarity as we go. This is why we need to demystify Mixed Reality, and open the floodgates of knowledge so everyone can learn.
As a change management consultant, one of the challenges I’ve seen with implementing innovative technologies is that the excitement gets too overwhelming and distracts from the key focus area. People get excited by shiny new things, and can sometimes overlook the importance of getting the brass tacks of implementation and adoption of these new technologies right. Don’t get me wrong – excitement and enthusiasm is good. However, losing sight of who will be impacted by this change and failing to have a comprehensive change management plan to support your employees in this process, not so much.
Want to drive mixed reality adoption in your organization?
- Your change management team should be working together with your project team as soon as possible. There is a lot of work to be done. Everyone driving this change will also have to learn to use this new technology. They will go through their own personal change management process as they learn to adapt themselves, before considering the bigger picture of how it impacts the organization and most importantly, who.
- Focus on your people – the humans who will be using this technology. Best practices gathered over the years have shown that the human aspect of change is extremely important and will make or break your project. It is the difference between how slow or fast the change will take to be fully rolled through your organization for it to start generating more revenue and begin netting a true return on investment (ROI).
Where am I in my personal Mixed Reality journey? I’m fortunate to have joined an exciting new startup in the Netherlands that shares my vision. I am excited to explore this new frontier where innovation and people come together, powered by the wonders of mixed reality. I cannot wait to share my findings and my journey with everyone. Today, I work on a lot of Dynamics 365 Remote Assist customer projects to help them infuse MR into their business, and there will be more mixed reality goodness to come!
I hope you enjoyed my story and that my blog left you with some food for thought.
#HumansofMixedReality #CareerJourney #ChangeManagement
by Scott Muniz | Dec 3, 2020 | Security, Technology
This article is contributed. See the original author and article here.
Original release date: December 3, 2020
VMware has released security updates to address a vulnerability—CVE-2020-4006—in VMware Workspace One Access, Access Connector, Identity Manager, and Identity Manager Connector. An attacker could exploit this vulnerability to take control of an affected system.
The Cybersecurity and Infrastructure Security Agency (CISA) encourages users and administrators to review VMware Security Advisory VMSA-2020-0027.2 and apply the necessary updates.
This product is provided subject to this Notification and this Privacy & Use policy.

by Contributed | Dec 3, 2020 | Azure, Microsoft, Technology
This article is contributed. See the original author and article here.
As part of our recent Azure Security Center (ASC) Blog Series, we are diving into the different controls within ASC’s Secure Score. In this post we will be discussing the control of “Apply Adaptive Application control”.
This security control contains up to 7 recommendations, depending on the resources you have deployed within your environment, and it is worth maximum of 1 point (2%) that counts towards your overall Secure Score. To understand about Azure Security Center’s secure score make sure you read this article. These recommendations are meant to keep your resources safe and improve your security hygiene.
Apply adaptive application control contains the following 7 recommendations, depending on your environment:
- Log Analytics agent should be installed on your virtual machine
- Monitoring agent should be installed on your machines
- Log Analytics agent should be installed on your Windows-based Azure Arc machines
- Log Analytics agent should be installed on your Linux-based Azure Arc machines
- Log Analytics agent health issues should be resolved on your machines
- Adaptive application controls for defining safe applications should be enabled on your machines
- Allowlist rules in your adaptive application control policy should be updated
The example screenshot below shows an environment in which only 6 of those 7 recommendations are within the scope of Apply adaptive application control security control, because the recommendations which do not apply to any resource within your environment do not appear.
 Image 1 – Recommendations within the Apply adaptive application control
Image 1 – Recommendations within the Apply adaptive application control
Like the rest of the Secure Score controls, all these recommendations must be considered in order to get the full points and drive up your Secure Score (you can review all of the recommendations here). Also, some might have a “Quick Fix!” button as well! No excuses not to enable those, it simplifies remediation and enables you to quickly increase your secure score, improving your environment’s security. To understand how Quick Fix works, please make sure to visit here
Category #1: Log Analytics agent should be installed on your virtual machine
To monitor for security vulnerabilities and threats, Azure Security Center depends on the Log Analytics Agent. The agent collects various security-related configuration details and event logs from connected machines, and then copies the data to your Log Analytics workspace for further analysis. Without the agent, Security Center will not be able to collect security data from the VM and some security
recommendations and alerts will be unavailable and within 24hrs, Security Center will determine that the VM is missing the extension and recommends you to install it via this security control. You could manually install the agent with the help of this recommendation or If you have auto-provisioning turned on, when Security Center identifies missing agent, it installs the extension automatically which in-turn reduces management overhead. Refer to this article to understand deployment options. Several questions arise at this point for scenarios like, how auto provisioning works in cases where there is already an agent installed and to understand that please read this information.
The following recommendations belong to this category:
- Monitoring agent should be installed on your machines.
- Log Analytics agent should be installed on your Windows-based Azure Arc machines. This recommendation applies to Windows-based Azure Arc machines
- Log Analytics agent should be installed on your Linux-based Azure Arc machines. This recommendation applies to Linux-based Azure Arc machines
Alternatively, to fix this recommendation, you can visit our Github Repository and leverage the automations we have published there.
Category #2: Log Analytics agent health issues should be resolved on your machines
You’ll notice this recommendation when Azure Security Center finds Log Analytics agent unhealthy which means, a VM is unmonitored by Security Center since the VM does not have healthy Log Analytics agent extension. This could be due to several reasons, one of it could be the agents are not able to connect to and register with Security Center due to no access to the network resources. Read more about this scenario here. To fully benefit from all of Security Center’s capabilities, the Log Analytics agent extension is required.
For more information about the reasons Security Center is unable to successfully monitor VMs and computers initialized for automatic provisioning, see Monitoring agent health issues.
NOTE: The above recommendations (Category #1 and #2) to install the agent and recommendation about agent health issues are pre-requisites. You might observe these recommendations also show up in a different security control, and if they were remediated there, it will not appear here in this Security control.
Category #3: Adaptive application controls for defining safe applications should be enabled on your machines
Application allowlist is not necessarily a new concept. One of the biggest challenges of dealing with the application allowlist is how to maintain that list. The traditional approach of using AppLocker in Windows is a good solution, but still has the overhead of keeping up with the applications and making the initial baseline work properly for our needs.
Adaptive application controls is one of the advanced protection features you can benefit from, when you upgrade to Azure Defender ON, this falls under the cloud Workload Platform Protection (CWPP).
Adaptive application controls help to harden your VMs against malware by making it easier to control which applications can run on your Azure VMs. Azure Defender has built-in intelligence that allows you to apply allowlist rules based on machine learning. This intelligence analyzes the processes that are running in your VMs, creates a baseline of applications, and groups the virtual machines. From here, recommendations are provided that allow you to automatically apply the appropriate allowlist rules. The use of machine learning intelligence makes it super simple to configure and maintain application the allowlist.
With this feature, you’re able to alert on or audit . These can even be malicious applications that might otherwise be missed by endpoint protection solutions, or applications with known vulnerabilities. By default, Azure Defender enables application control in Audit mode. No enforcement options are available at this time of writing.
Adaptive Application Control do not support Windows machines for which AppLocker policy is already enabled by either group policy objects (GPOs) or Local Security policy.
Hope this helps you understand why it is super important for you to enable them. Learning about Adaptive Application Control is essential for anyone looking to gain more granular control and security within their environment, so make sure to read our documentation.
Category #4: Allowlist rules in your adaptive application control policy should be updated
This recommendation will be displayed when Azure Defender’s machine learning identifies potentially legitimate behavior that hasn’t previously been allowed. This recommendation suggests you to add new rules to the existing policy to reduce the number of false positives in adaptive application controls violation alerts. To edit the application control policy please refer to this for more information.
Next Steps
As with all security controls, you need to make sure to remediate all recommendations within the control that apply to a particular resource in order to gain credit towards your secure score.
I hope you enjoyed reading this blog post as much as I enjoyed writing it and learned how this specific control can assist you to strengthen your Azure security posture.
- The main blog post to this series (found here)
- The DOCs article about Secure Score (this one)
Reviewer
Special Thanks to @Yuri Diogenes, Principal Program Manager in the CxE ASC Team for reviewing this article.
by Scott Muniz | Dec 3, 2020 | Security, Technology
This article is contributed. See the original author and article here.
Original release date: December 3, 2020
Iranian cyber threat actors have been continuously improving their offensive cyber capabilities. They continue to engage in more conventional offensive cyber activities ranging from website defacement, distributed denial of service (DDoS) attacks, and theft of personally identifiable information (PII), to more advanced activities—including social media-driven influence operations, destructive malware, and, potentially, cyber-enabled kinetic attacks.
The Cybersecurity and Infrastructure Security Agency (CISA) encourages users and administrators to review Joint Cybersecurity Advisory AA20-259A: Iran-Based Threat Actor Exploits VPN Vulnerabilities and Activity Alert AA20-133A: Top 10 Routinely Exploited Vulnerabilities for information on known Iranian advanced persistent threat (APT) actor tactics, techniques, and procedures (TTPs).
For more information on Iranian cyber threats, review the following products.
This product is provided subject to this Notification and this Privacy & Use policy.
by Contributed | Dec 3, 2020 | Technology
This article is contributed. See the original author and article here.
Both Microsoft Teams Administrators AND all End Users should review this article in order to understand how to enable and use Virtual Breakout Rooms in your Microsoft Teams Desktop Client.
Note: Teams Virtual Breakout Rooms will begin rolling out to all GCC tenants starting in early December with completion happening by mid-December.
Administrators – What to do to Prepare Your Organization:
- As an admin, ensure users can schedule private meetings with the following settings:
- Allow scheduling private meeting = on
- Allow Meet now in private meeting = on
- Allow channel meeting scheduling = on
- Allow meet now in channels = on
All Users in the Organization Should do the Following in their Teams Desktop Client:
- To see the breakout rooms option within your meetings, you must turn on the new Teams meeting experience by
- Clicking on your profile image within Teams
- Selecting Settings
- Checking the “Turn on new meeting experience” option within General settings.
- Restart your Teams client.
- You can double check that the setting is setup correctly by starting a meeting and verifying that the meeting opens in its own window.
- Make sure all participants, including the meeting organizer are using the latest version of Teams. If joining on Android or iOS mobile or tablet, make sure participants go to their App Store and download the latest update.
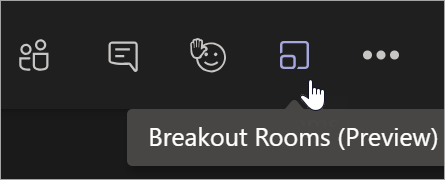
- As a meeting organizer, join a channel / private scheduled meeting, or channel / private meet now meeting. Once you are in the meeting you should see the breakout room option next to the raise hand control.
- You must be a meeting organizer to see the option. Meeting attendees and presenters will not see the breakout rooms option.
Features available for Organizers:
- Breakout room setup on Teams desktop client
- Create breakout rooms in scheduled private meetings (including recurring) and private meet now meetings
- Meeting organizers can manage rooms and hop between rooms freely
- Setup breakout rooms during an active meeting
- Create up to 50 breakout rooms in a single meeting
- Add, remove, delete breakout rooms
- Rename rooms to the title of your choice
- Reassign room participants from one room to another before as well as while the rooms are open
- Room transition: as an organizer, you can decide if participants get moved to the room automatically when you open the room, or, if they need to click to confirm the move. The “auto-accept” setting is available per meeting.
- Send an announcement that will show up as a meeting chat message in each room.
- Chats, files, and recordings: only the organizer will always have access to all rooms meeting artifacts
Features available for the participants::
- Join breakout rooms from web, desktop, iOS, iPads, Android mobiles and tablets. Note that organizers cannot move participants who joined via Desk phones or Teams devices join to a breakout room, they can stay in main meeting as their breakout room.
- Participants join the room as presenters, so they can present, share Whiteboard, etc. freely.
- Participants cannot add others to meeting chat, copy meeting details, nudge others to the meeting, or use “call me back”
- Hoping between rooms: Meeting participants cannot hop back to main meeting or between rooms on their own. They must wait for the meeting organizer to pull them back to the main meeting.
- Chat during the breakout session. Chat and artifacts shared during meeting are viewable for room participants.
- Chats, files, and recordings: Participants have access to artifacts, but only organizer has access to the links – if link is shared by meeting organizer, then participants will have access
- Multi-device join: breakout room is not supported when the participant joins the same meeting and same account from multiple devices
Where and when can I set up breakout rooms?
- You can set up breakout rooms after you join the meeting as the organizer. You can bulk create rooms at the start, or manually add or remove rooms.
- You can set up breakout rooms from desktop client, but not in mobile and web.
- We plan to enable the ability for you to set up breakout rooms before the meeting very soon.
When can I assign participants to breakout room?
- You can assign participant when you are setting up the rooms. You can do so manually before the rooms open or reassign participants to a different room while the room is open.
- You can also auto-assign the participants to rooms when you first set up the rooms in the meeting.



Recent Comments