by Scott Muniz | Feb 1, 2021 | Security, Technology
This article is contributed. See the original author and article here.
| rocket.chat — rocket.chat |
Rocket.Chat server before 3.9.0 is vulnerable to a self cross-site scripting (XSS) vulnerability via the drag & drop functionality in message boxes. |
2021-01-26 |
not yet calculated |
CVE-2020-8292
MISC
MISC |
4images — image_gallary_management_system
|
4images Image Gallery Management System 1.7.11 is affected by cross-site scripting (XSS) in the Image URL. This vulnerability can result in an attacker to inject the XSS payload into the IMAGE URL. Each time a user visits that URL, the XSS triggers and the attacker can be able to steal the cookie according to the crafted payload. |
2021-01-26 |
not yet calculated |
CVE-2020-35853
MISC |
abi_stable — abi_stable
|
An issue was discovered in the abi_stable crate before 0.9.1 for Rust. DrainFilter lacks soundness because of a double drop. |
2021-01-26 |
not yet calculated |
CVE-2020-36212
MISC |
abi_stable — abi_stable
|
An issue was discovered in the abi_stable crate before 0.9.1 for Rust. A retain call can create an invalid UTF-8 string, violating soundness. |
2021-01-26 |
not yet calculated |
CVE-2020-36213
MISC |
accfly — wireless_security_ir_camera_720p
|
An issue was discovered on Accfly Wireless Security IR Camera System 720P with software versions v3.10.73 through v4.15.77. There is an unauthenticated heap-based buffer overflow in the function CNetClientTalk::OprMsg during incoming message handling. |
2021-01-28 |
not yet calculated |
CVE-2020-25783
MISC |
accfly — wireless_security_ir_camera_720p
|
An issue was discovered on Accfly Wireless Security IR Camera System 720P with software versions v3.10.73 through v4.15.77. There is an unauthenticated stack-based buffer overflow in the function CFtpProtocol::FtpLogin during the update procedure. |
2021-01-28 |
not yet calculated |
CVE-2020-25785
MISC |
accfly — wireless_security_ir_camera_720p
|
An issue was discovered on Accfly Wireless Security IR Camera 720P System with software versions v3.10.73 through v4.15.77. There is an unauthenticated stack-based buffer overflow in the function CNetClientManage::ServerIP_Proto_Set during incoming message handling. |
2021-01-28 |
not yet calculated |
CVE-2020-25782
MISC |
accfly — wireless_security_ir_camera_720p
|
An issue was discovered on Accfly Wireless Security IR Camera System 720P with software versions v3.10.73 through v4.15.77. There is an unauthenticated stack-based buffer overflow in the function CNetClientGuard::SubOprMsg during incoming message handling. |
2021-01-28 |
not yet calculated |
CVE-2020-25784
MISC |
acdsee — professional_2021
|
PlugInsIDE_ACDStd.apl in ACDSee Professional 2021 14.0 1721 has a User Mode Write Access Violation starting at IDE_ACDStd!JPEGTransW+0x000000000000c7f4 via a crafted BMP image. |
2021-01-26 |
not yet calculated |
CVE-2021-26026
MISC |
acdsee — professional_2021
|
PlugInsIDE_ACDStd.apl in ACDSee Professional 2021 14.0 1721 has a User Mode Write Access Violation starting at IDE_ACDStd!zlibVersion+0x0000000000004e5e via a crafted BMP image. |
2021-01-26 |
not yet calculated |
CVE-2021-26025
MISC |
acronis_true_image — acronis_true_image
|
Acronis True Image for Windows prior to 2021 Update 3 allowed local privilege escalation due to a DLL hijacking vulnerability in multiple components, aka an Untrusted Search Path issue. |
2021-01-29 |
not yet calculated |
CVE-2020-35145
MISC
CONFIRM |
aovec — aovec
|
An issue was discovered in the aovec crate through 2020-12-10 for Rust. Because Aovec<T> does not have bounds on its Send trait or Sync trait, a data race and memory corruption can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36207
MISC |
| apache — activemq_artemis |
The optional ActiveMQ LDAP login module can be configured to use anonymous access to the LDAP server. In this case, for Apache ActiveMQ Artemis prior to version 2.16.0 and Apache ActiveMQ prior to versions 5.16.1 and 5.15.14, the anonymous context is used to verify a valid users password in error, resulting in no check on the password. |
2021-01-27 |
not yet calculated |
CVE-2021-26117
MLIST
MLIST
MISC |
apache — activemq_artemis
|
While investigating ARTEMIS-2964 it was found that the creation of advisory messages in the OpenWire protocol head of Apache ActiveMQ Artemis 2.15.0 bypassed policy based access control for the entire session. Production of advisory messages was not subject to access control in error. |
2021-01-27 |
not yet calculated |
CVE-2021-26118
MLIST
MISC |
apache — druid
|
Apache Druid includes the ability to execute user-provided JavaScript code embedded in various types of requests. This functionality is intended for use in high-trust environments, and is disabled by default. However, in Druid 0.20.0 and earlier, it is possible for an authenticated user to send a specially-crafted request that forces Druid to run user-provided JavaScript code for that request, regardless of server configuration. This can be leveraged to execute code on the target machine with the privileges of the Druid server process. |
2021-01-29 |
not yet calculated |
CVE-2021-25646
MLIST
MLIST
MLIST
MLIST
MISC |
apache — hadoop
|
In Apache Hadoop 3.2.0 to 3.2.1, 3.0.0-alpha1 to 3.1.3, and 2.0.0-alpha to 2.10.0, WebHDFS client might send SPNEGO authorization header to remote URL without proper verification. |
2021-01-26 |
not yet calculated |
CVE-2020-9492
MISC
MLIST |
| archer — archer |
Archer before 6.8 P2 (6.8.0.2) is affected by a path exposure vulnerability. A remote authenticated malicious attacker with access to service files may obtain sensitive information to use it in further attacks. |
2021-01-29 |
not yet calculated |
CVE-2020-29536
CONFIRM
MISC |
| archer — archer |
Archer before 6.8 P2 (6.8.0.2) is affected by an open redirect vulnerability. A remote privileged attacker may potentially redirect legitimate users to arbitrary web sites and conduct phishing attacks. The attacker could then steal the victims’ credentials and silently authenticate them to the Archer application without the victims realizing an attack occurred. |
2021-01-29 |
not yet calculated |
CVE-2020-29537
CONFIRM
MISC |
| archer — archer |
Archer before 6.9 P1 (6.9.0.1) contains an improper access control vulnerability in an API. A remote authenticated malicious administrative user can potentially exploit this vulnerability to gather information about the system, and may use this information in subsequent attacks. |
2021-01-29 |
not yet calculated |
CVE-2020-29538
CONFIRM
MISC |
archer — archer
|
Archer before 6.8 P4 (6.8.0.4) contains a stored XSS vulnerability. A remote authenticated malicious Archer user could potentially exploit this vulnerability to store malicious HTML or JavaScript code in a trusted application data store. When application users access the corrupted data store through their browsers, the malicious code gets executed by the web browser in the context of the vulnerable web application. |
2021-01-29 |
not yet calculated |
CVE-2020-29535
CONFIRM
MISC |
assuweb — assuweb
|
Deserialization of untrusted data in the login page of ASSUWEB 359.3 build 1 subcomponent of ACA ASSUREX RENTES product allows a remote attacker to inject unsecure serialized Java object using a specially crafted HTTP request, resulting in an unauthenticated remote code execution on the server. |
2021-01-28 |
not yet calculated |
CVE-2021-3160
MISC
MISC |
async-h1 — async-h1
|
An issue was discovered in the async-h1 crate before 2.3.0 for Rust. Request smuggling can occur when used behind a reverse proxy. |
2021-01-26 |
not yet calculated |
CVE-2020-36202
MISC |
aterm — wf800hp_firmware
|
Cross-site scripting vulnerability in Aterm WF800HP firmware Ver1.0.9 and earlier allows remote attackers to inject an arbitrary script via unspecified vectors. |
2021-01-28 |
not yet calculated |
CVE-2021-20620
MISC
MISC
MISC |
aterm — wg2600hp_firmware
|
Cross-site request forgery (CSRF) vulnerability in Aterm WG2600HP firmware Ver1.0.2 and earlier, and Aterm WG2600HP2 firmware Ver1.0.2 and earlier allows remote attackers to hijack the authentication of administrators via unspecified vectors. |
2021-01-28 |
not yet calculated |
CVE-2021-20621
MISC
MISC
MISC |
aterm — wg2600hp_firmware
|
Cross-site scripting vulnerability in Aterm WG2600HP firmware Ver1.0.2 and earlier, and Aterm WG2600HP2 firmware Ver1.0.2 and earlier allows remote attackers to inject an arbitrary script via unspecified vectors. |
2021-01-28 |
not yet calculated |
CVE-2021-20622
MISC
MISC
MISC |
atlassian — bamboo
|
Affected versions of Atlassian Bamboo allow an unauthenticated remote attacker to view a stack trace that may reveal the path for the home directory in disk and if certain files exists on the tmp directory, via a Sensitive Data Exposure vulnerability in the /chart endpoint. The affected versions are before version 7.2.2. |
2021-01-28 |
not yet calculated |
CVE-2021-26067
MISC |
atomic-option — atomic-option
|
An issue was discovered in the atomic-option crate through 2020-10-31 for Rust. Because AtomicOption<T> implements Sync unconditionally, a data race can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36219
MISC |
autoand — autoand
|
An issue was discovered in the autorand crate before 0.2.3 for Rust. Because of impl Random on arrays, uninitialized memory can be dropped when a panic occurs, leading to memory corruption. |
2021-01-26 |
not yet calculated |
CVE-2020-36210
MISC |
av-data — av-data
|
An issue was discovered in the av-data crate before 0.3.0 for Rust. A raw pointer is dereferenced, leading to a read of an arbitrary memory address, sometimes causing a segfault. |
2021-01-26 |
not yet calculated |
CVE-2021-25904
MISC |
bakeshop — online_ordering_system
|
Bakeshop Online Ordering System in PHP/MySQLi 1.0 is affected by cross-site scripting (XSS) which allows remote attackers to inject an arbitrary web script or HTML in admin dashboard – “Categories”. |
2021-01-26 |
not yet calculated |
CVE-2020-35309
MISC |
basic_dsp_matrix — basic_dsp_matrix
|
An issue was discovered in the basic_dsp_matrix crate before 0.9.2 for Rust. When a TransformContent panic occurs, a double drop can be performed. |
2021-01-26 |
not yet calculated |
CVE-2021-25906
MISC |
bitcoin — core
|
bitcoind in Bitcoin Core through 0.21.0 can create a new file in an arbitrary directory (e.g., outside the ~/.bitcoin directory) via a dumpwallet RPC call. |
2021-01-26 |
not yet calculated |
CVE-2021-3195
MISC |
bosch — fsm-2500_server_and_fsm-5000_server
|
Use of Hard-coded Credentials in the database of Bosch FSM-2500 server and Bosch FSM-5000 server up to and including version 5.2 allows an unauthenticated remote attacker to log into the database with admin-privileges. This may result in complete compromise of the confidentiality and integrity of the stored data as well as a high availability impact on the database itself. In addition, an attacker may execute arbitrary commands on the underlying operating system. |
2021-01-26 |
not yet calculated |
CVE-2020-6779
MISC |
bosch — fsm-2500_server_and_fsm-5000_server
|
Use of Password Hash With Insufficient Computational Effort in the database of Bosch FSM-2500 server and Bosch FSM-5000 server up to and including version 5.2 allows a remote attacker with admin privileges to dump the credentials of other users and possibly recover their plain-text passwords by brute-forcing the MD5 hash. |
2021-01-26 |
not yet calculated |
CVE-2020-6780
MISC |
bra — bra
|
An issue was discovered in the bra crate before 0.1.1 for Rust. It lacks soundness because it can read uninitialized memory. |
2021-01-26 |
not yet calculated |
CVE-2021-25905
MISC |
buttplug — buttplug
|
An issue was discovered in the buttplug crate before 1.0.4 for Rust. ButtplugFutureStateShared does not properly consider (!Send|!Sync) objects, leading to a data race. |
2021-01-26 |
not yet calculated |
CVE-2020-36218
MISC |
cache — cache
|
An issue was discovered in the cache crate through 2021-01-01 for Rust. A raw pointer is dereferenced. |
2021-01-26 |
not yet calculated |
CVE-2021-25903
MISC |
cakephp — cakephp
|
A vulnerability exists in CakePHP versions 4.0.x through 4.1.3. The CsrfProtectionMiddleware component allows method override parameters to bypass CSRF checks by changing the HTTP request method to an arbitrary string that is not in the list of request methods that CakePHP checks. Additionally, the route middleware does not verify that this overriden method (which can be an arbitrary string) is actually an HTTP method. |
2021-01-26 |
not yet calculated |
CVE-2020-35239
MISC |
cdr-rs — cdr-rs
|
An issue was discovered in Deserializer::read_vec in the cdr crate before 0.2.4 for Rust. A user-provided Read implementation can gain access to the old contents of newly allocated heap memory, violating soundness. |
2021-01-29 |
not yet calculated |
CVE-2021-26305
MISC |
churchrota — churchrota
|
ChurchRota 2.6.4 is vulnerable to authenticated remote code execution. The user does not need to have file upload permission in order to upload and execute an arbitrary file via a POST request to resources.php. |
2021-01-26 |
not yet calculated |
CVE-2021-3164
MISC
MISC |
| ckeditor — ckeditor |
It was possible to execute a ReDoS-type attack inside CKEditor 4 before 4.16 by persuading a victim to paste crafted text into the Styles input of specific dialogs (in the Advanced Tab for Dialogs plugin). |
2021-01-26 |
not yet calculated |
CVE-2021-26271
MISC |
ckeditor — ckeditor
|
It was possible to execute a ReDoS-type attack inside CKEditor 4 before 4.16 by persuading a victim to paste crafted URL-like text into the editor, and then press Enter or Space (in the Autolink plugin). |
2021-01-26 |
not yet calculated |
CVE-2021-26272
MISC |
ckeditor — ckeditor
|
CKEditor 5 is an open source rich text editor framework with a modular architecture. The CKEditor 5 Markdown plugin (@ckeditor/ckeditor5-markdown-gfm) before version 25.0.0 has a regex denial of service (ReDoS) vulnerability. The vulnerability allowed to abuse link recognition regular expression, which could cause a significant performance drop resulting in browser tab freeze. It affects all users using CKEditor 5 Markdown plugin at version <= 24.0.0. The problem has been recognized and patched. The fix will be available in version 25.0.0. |
2021-01-29 |
not yet calculated |
CVE-2021-21254
MISC
CONFIRM
MISC |
codiad — codiad
|
** PRODUCT NOT SUPPORTED WHEN ASSIGNED ** Codiad 2.8.4 /componetns/user/class.user.php:Authenticate() is vulnerable in magic hash authentication bypass. If encrypted or hash value for the passwords form certain formats of magic hash, e.g, 0e123, another hash value 0e234 something can successfully authenticate. |
2021-01-27 |
not yet calculated |
CVE-2020-23355
MISC |
conquer-once — conquer-once
|
An issue was discovered in the conquer-once crate before 0.3.2 for Rust. Thread crossing can occur for a non-Send but Sync type, leading to memory corruption. |
2021-01-26 |
not yet calculated |
CVE-2020-36208
MISC |
containers — containers
|
An issue was discovered in the containers crate before 0.9.11 for Rust. When a panic occurs, a util::{mutate,mutate2} double drop can be performed. |
2021-01-26 |
not yet calculated |
CVE-2021-25907
MISC |
cpanel — cpanel
|
cPanel before 92.0.9 allows a Reseller to bypass the suspension lock (SEC-578). |
2021-01-26 |
not yet calculated |
CVE-2021-26266
MISC |
cpanel — cpanel
|
cPanel before 92.0.9 allows a MySQL user (who has an old-style password hash) to bypass suspension (SEC-579). |
2021-01-26 |
not yet calculated |
CVE-2021-26267
MISC |
d-link — dir_825_r1_devices
|
An issue was discovered on D-Link DIR-825 R1 devices through 3.0.1 before 2020-11-20. A buffer overflow in the web interface allows attackers to achieve pre-authentication remote code execution. |
2021-01-29 |
not yet calculated |
CVE-2020-29557
MISC
MISC |
delta_electronics — ispsoft
|
A use after free issue has been identified in the way ISPSoft(v3.12 and prior) processes project files, allowing an attacker to craft a special project file that may allow arbitrary code execution. |
2021-01-26 |
not yet calculated |
CVE-2020-27280
MISC |
dh2i — dxenterprise_and_dxodyssey
|
A path traversal vulnerability in the DxWebEngine component of DH2i DxEnterprise and DxOdyssey for Windows, version 19.5 through 20.x before 20.0.219.0, allows an attacker to read any file on the host file system via an HTTP request. |
2021-01-29 |
not yet calculated |
CVE-2021-3341
MISC |
duncaen — opendoas
|
In OpenDoas from 6.6 to 6.8 the users PATH variable was incorrectly inherited by authenticated executions if the authenticating rule allowed the user to execute any command. Rules that only allowed to authenticated user to execute specific commands were not affected by this issue. |
2021-01-28 |
not yet calculated |
CVE-2019-25016
MISC
MISC
MISC
MISC |
ecostruxure — operator_terminal_expert_and_pro-face_blue
|
A CWE-20: Improper Input Validation vulnerability exists in EcoStruxure™ Operator Terminal Expert and Pro-face BLUE (version details in the notification) that could cause arbitrary code execution when the Ethernet Download feature is enable on the HMI. |
2021-01-26 |
not yet calculated |
CVE-2020-28221
MISC |
| ecostruxure — power_build |
A CWE-434: Unrestricted Upload of File with Dangerous Type vulnerability exists in the EcoStruxure Power Build – Rapsody software (V2.1.13 and prior) that could allow a stack-based buffer overflow to occur which could result in remote code execution when a malicious SSD file is uploaded and improperly parsed. |
2021-01-26 |
not yet calculated |
CVE-2021-22698
MISC |
ecostruxure — power_build
|
A CWE-434: Unrestricted Upload of File with Dangerous Type vulnerability exists in the EcoStruxure Power Build – Rapsody software (V2.1.13 and prior) that could allow a use-after-free condition which could result in remote code execution when a malicious SSD file is uploaded and improperly parsed. |
2021-01-26 |
not yet calculated |
CVE-2021-22697
MISC |
egavilan — media_crud_operation
|
Stored Cross Site Scripting (XSS) vulnerability in EGavilan Media CRUD Operation with PHP, MySQL, Bootstrap, and Dompdf via First Name or Last Name parameter in the ‘Add New Record Feature’. |
2021-01-28 |
not yet calculated |
CVE-2020-36115
MISC |
egavilanmedia — user_registration_and_login_system
|
EgavilanMedia User Registration & Login System 1.0 is affected by SQL injection to the admin panel, which may allow arbitrary code execution. |
2021-01-26 |
not yet calculated |
CVE-2020-35263
MISC |
electron — electron
|
The Electron framework lets you write cross-platform desktop applications using JavaScript, HTML and CSS. In affected versions of Electron IPC messages sent from the main process to a subframe in the renderer process, through webContents.sendToFrame, event.reply or when using the remote module, can in some cases be delivered to the wrong frame. If your app uses remote, calls webContents.sendToFrame, or calls event.reply in an IPC message handler then it is impacted by this issue. This has been fixed in versions 9.4.0, 10.2.0, 11.1.0, and 12.0.0-beta.9. There are no workarounds for this issue. |
2021-01-28 |
not yet calculated |
CVE-2020-26272
MISC
MISC
MISC
CONFIRM
MISC |
eset — multiple_products
|
A local (authenticated) low-privileged user can exploit a behavior in an ESET installer to achieve arbitrary file overwrite (deletion) of any file via a symlink, due to insecure permissions. The possibility of exploiting this vulnerability is limited and can only take place during the installation phase of ESET products. Furthermore, exploitation can only succeed when Self-Defense is disabled. Affected products are: ESET NOD32 Antivirus, ESET Internet Security, ESET Smart Security, ESET Smart Security Premium versions 13.2 and lower; ESET Endpoint Antivirus, ESET Endpoint Security, ESET NOD32 Antivirus Business Edition, ESET Smart Security Business Edition versions 7.3 and lower; ESET File Security for Microsoft Windows Server, ESET Mail Security for Microsoft Exchange Server, ESET Mail Security for IBM Domino, ESET Security for Kerio, ESET Security for Microsoft SharePoint Server versions 7.2 and lower. |
2021-01-26 |
not yet calculated |
CVE-2020-26941
MISC |
eventio — eventio
|
An issue was discovered in Input<R> in the eventio crate before 0.5.1 for Rust. Because a non-Send type can be sent to a different thread, a data race and memory corruption can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36216
MISC |
fil-ocl — fil-ocl
|
An issue was discovered in the fil-ocl crate through 2021-01-04 for Rust. From<EventList> can lead to a double free. |
2021-01-26 |
not yet calculated |
CVE-2021-25908
MISC |
flarum — flarum
|
Flarum is an open source discussion platform for websites. The “Flarum Sticky” extension versions 0.1.0-beta.14 and 0.1.0-beta.15 has a cross-site scripting vulnerability. A change in release beta 14 of the Sticky extension caused the plain text content of the first post of a pinned discussion to be injected as HTML on the discussion list. The issue was discovered following an internal audit. Any HTML would be injected through the m.trust() helper. This resulted in an HTML injection where <script> tags would not be executed. However it was possible to run javascript from other HTML attributes, enabling a cross-site scripting (XSS) attack to be performed. Since the exploit only happens with the first post of a pinned discussion, an attacker would need the ability to pin their own discussion, or be able to edit a discussion that was previously pinned. On forums where all pinned posts are authored by your staff, you can be relatively certain the vulnerability has not been exploited. Forums where some user-created discussions were pinned can look at the first post edit date to find whether the vulnerability might have been exploited. Because Flarum doesn’t store the post content history, you cannot be certain if a malicious edit was reverted. The fix will be available in version v0.1.0-beta.16 with Flarum beta 16. The fix has already been back-ported to Flarum beta 15 as version v0.1.0-beta.15.1 of the Sticky extension. Forum administrators can disable the Sticky extension until they are able to apply the update. The vulnerability cannot be exploited while the extension is disabled. |
2021-01-26 |
not yet calculated |
CVE-2021-21283
MISC
MISC
MISC
CONFIRM |
foris — foris
|
Foris before 101.1.1, as used in Turris OS, lacks certain HTML escaping in the login template. |
2021-01-29 |
not yet calculated |
CVE-2021-3346
MISC
MISC
MISC |
ftpd — ftpd
|
The ftpd gem 0.2.1 for Ruby allows remote attackers to execute arbitrary OS commands via shell metacharacters in a LIST or NLST command argument within FTP protocol traffic. |
2021-01-26 |
not yet calculated |
CVE-2013-2512
MISC |
geeni — gnc-cw013
|
An issue was discovered on Geeni GNC-CW013 doorbell 1.8.1 devices. A vulnerability exists in the Telnet service that allows a remote attacker to take full control of the device with a high-privileged account. The vulnerability exists because a system account has a default and static password. |
2021-01-26 |
not yet calculated |
CVE-2020-28998
MISC
MISC |
geeni — gnc-cw013
|
An issue was discovered in Apexis Streaming Video Web Application on Geeni GNC-CW013 doorbell 1.8.1 devices. A remote attacker can take full control of the camera with a high-privileged account. The vulnerability exists because a static username and password are compiled into a shared library (libhipcam.so) used to provide the streaming camera service. |
2021-01-26 |
not yet calculated |
CVE-2020-28999
MISC
MISC |
geeni — gnc-cw013
|
An issue was discovered on Geeni GNC-CW013 doorbell 1.8.1 devices. A vulnerability exists in the RTSP service that allows a remote attacker to take full control of the device with a high-privileged account. By sending a crafted message, an attacker is able to remotely deliver a telnet session. Any attacker that has the ability to control DNS can exploit this vulnerability to remotely login to the device and gain access to the camera system. |
2021-01-26 |
not yet calculated |
CVE-2020-29000
MISC
MISC |
geeni — mulitple_products
|
An issue was discovered on Geeni GNC-CW028 Camera 2.7.2, Geeni GNC-CW025 Doorbell 2.9.5, Merkury MI-CW024 Doorbell 2.9.6, and Merkury MI-CW017 Camera 2.9.6 devices. A vulnerability exists in the RESTful Services API that allows a remote attacker to take full control of the camera with a high-privileged account. The vulnerability exists because a static username and password are compiled into the ppsapp RESTful application. |
2021-01-26 |
not yet calculated |
CVE-2020-29001
MISC
MISC |
gfwx — gfwx
|
An issue was discovered in the gfwx crate before 0.3.0 for Rust. Because ImageChunkMut does not have bounds on its Send trait or Sync trait, a data race and memory corruption can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36211
MISC |
glsl-layout — glsl-layout
|
An issue was discovered in the glsl-layout crate before 0.4.0 for Rust. When a panic occurs, map_array can perform a double drop. |
2021-01-26 |
not yet calculated |
CVE-2021-25902
MISC |
gnu — c_library
|
The iconv function in the GNU C Library (aka glibc or libc6) 2.32 and earlier, when processing invalid input sequences in the ISO-2022-JP-3 encoding, fails an assertion in the code path and aborts the program, potentially resulting in a denial of service. |
2021-01-27 |
not yet calculated |
CVE-2021-3326
MLIST
MISC
MISC |
| go — go |
Go before 1.14.14 and 1.15.x before 1.15.7 on Windows is vulnerable to Command Injection and remote code execution when using the “go get” command to fetch modules that make use of cgo (for example, cgo can execute a gcc program from an untrusted download). |
2021-01-26 |
not yet calculated |
CVE-2021-3115
CONFIRM
CONFIRM |
go — go
|
In Go before 1.14.14 and 1.15.x before 1.15.7, crypto/elliptic/p224.go can generate incorrect outputs, related to an underflow of the lowest limb during the final complete reduction in the P-224 field. |
2021-01-26 |
not yet calculated |
CVE-2021-3114
CONFIRM
CONFIRM |
godaddy — godaddy
|
** DISPUTED ** scripts/cli.js in the GoDaddy node-config-shield (aka Config Shield) package before 0.2.2 for Node.js calls eval when processing a set command. NOTE: the vendor reportedly states that this is not a vulnerability. The set command was not intended for use with untrusted data. |
2021-01-27 |
not yet calculated |
CVE-2021-26276
MISC |
google — android
|
In checkGrantUriPermission of UriGrantsManagerService.java, there is a possible way to access contacts due to a permissions bypass. This could lead to local information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11Android ID: A-138791358 |
2021-01-26 |
not yet calculated |
CVE-2020-27098
MISC |
google — android
|
In checkGrantUriPermission of UriGrantsManagerService.java, there is a possible permissions bypass. This could lead to local information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11Android ID: A-140729426 |
2021-01-26 |
not yet calculated |
CVE-2020-27097
MISC |
gstreamer — h264
|
A flaw was found in the gstreamer h264 component of gst-plugins-bad before v1.18.1 where when parsing a h264 header, an attacker could cause the stack to be smashed, memory corruption and possibly code execution. |
2021-01-26 |
not yet calculated |
CVE-2021-3185
MISC |
hackolade — hackolade
|
An elevation of privilege vulnerability exists in Hackolade versions prior 4.2.0 on Windows has an issue in specific deployment scenarios that could allow local users to gain elevated privileges during an uninstall of the application. |
2021-01-26 |
not yet calculated |
CVE-2020-25737
MISC |
hashconsing — hashconsing
|
An issue was discovered in the hashconsing crate before 1.1.0 for Rust. Because HConsed does not have bounds on its Send trait or Sync trait, memory corruption can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36215
MISC |
hedgedoc — hedgedoc
|
HedgeDoc is open source software which lets you create real-time collaborative markdown notes. In HedgeDoc before version 1.7.2, an attacker can inject arbitrary JavaScript into a HedgeDoc note, which is executed when the note is viewed in slide mode. Depending on the configuration of the instance, the attacker may not need authentication to create or edit notes. The problem is patched in HedgeDoc 1.7.2. ### Workarounds Disallow loading JavaScript from 3rd party sites using the `Content-Security-Policy` header. Note that this will break some embedded content. ### References This issue was discovered by @TobiasHoll and reported to hackmdio/codimd: https://github.com/hackmdio/codimd/issues/1648 ### For more information If you have any questions or comments about this advisory: * Open an topic on our community forum * Join our matrix room |
2021-01-22 |
not yet calculated |
CVE-2021-21259
MISC
MISC
CONFIRM |
hewlett_packard — multiple_products
|
The Baseboard Management Controller(BMC) in HPE Cloudline CL5800 Gen9 Server; HPE Cloudline CL5200 Gen9 Server; HPE Cloudline CL4100 Gen10 Server; HPE Cloudline CL3100 Gen10 Server; HPE Cloudline CL5800 Gen10 Server BMC firmware has a local buffer overlfow in spx_restservice addlicense_func function. |
2021-01-29 |
not yet calculated |
CVE-2021-25123
MISC |
| hitachi — vantara_pentaho |
The New Analysis Report in Hitachi Vantara Pentaho through 7.x – 8.x contains a DOM-based Cross-site scripting vulnerability, which allows an authenticated remote users to execute arbitrary JavaScript code. Specifically, the vulnerability lies in the ‘Analysis Report Description’ field in ‘About this Report’ section. Remediated in >= 8.3.0.9, >= 9.0.0.1, and >= 9.1.0.0 GA. |
2021-01-29 |
not yet calculated |
CVE-2020-24669
MISC
MISC |
| hitachi — vantara_pentaho |
The Dashboard Editor in Hitachi Vantara Pentaho through 7.x – 8.x contains a reflected Cross-site scripting vulnerability, which allows an authenticated remote users to execute arbitrary JavaScript code. Specifically, the vulnerability lies in the ‘type’ attribute of ‘dashboardXml’ parameter. Remediated in >= 7.1.0.25, >= 8.2.0.6, and >= 8.3.0.0 GA. |
2021-01-29 |
not yet calculated |
CVE-2020-24670
MISC
MISC |
hitachi — vantara_pentaho
|
The Dashboard Editor in Hitachi Vantara Pentaho through 7.x – 8.x contains an XML Entity Expansion injection vulnerability, which allows an authenticated remote users to trigger a denial of service (DoS) condition. Specifically, the vulnerability lies in the ‘dashboardXml’ parameter. Remediated in >= 7.1.0.25, >= 8.2.0.6, >= 8.3.0.0 GA |
2021-01-29 |
not yet calculated |
CVE-2020-24665
MISC
MISC |
hitachi — vantara_pentaho
|
The Analysis Report in Hitachi Vantara Pentaho through 7.x – 8.x contains a stored Cross-site scripting vulnerability, which allows an authenticated remote users to execute arbitrary JavaScript code. Specifically, the vulnerability lies in the ‘Display Name’ parameter. Remediated in >= 9.1.0.1 |
2021-01-29 |
not yet calculated |
CVE-2020-24666
MISC
MISC |
hitachi — vantara_pentaho
|
The dashboard Editor in Hitachi Vantara Pentaho through 7.x – 8.x contains a reflected Cross-site scripting vulnerability, which allows an authenticated remote users to execute arbitrary JavaScript code. Specifically, the vulnerability lies in the ‘pho:title’ attribute of ‘dashboardXml’ parameter. Remediated in >= 7.1.0.25, >= 8.2.0.6, and >= 8.3.0.0 GA. |
2021-01-29 |
not yet calculated |
CVE-2020-24664
MISC
MISC |
home_assistant — home_assistant
|
** DISPUTED ** Home Assistant before 2021.1.3 does not have a protection layer that can help to prevent directory-traversal attacks against custom integrations. NOTE: the vendor’s perspective is that the vulnerability itself is in custom integrations written by third parties, not in Home Assistant; however, Home Assistant does have a security update that is worthwhile in addressing this situation. |
2021-01-26 |
not yet calculated |
CVE-2021-3152
CONFIRM
MISC |
htcondor — condor_credd
|
condor_credd in HTCondor before 8.9.11 allows Directory Traversal outside the SEC_CREDENTIAL_DIRECTORY_OAUTH directory, as demonstrated by creating a file under /etc that will later be executed by root. |
2021-01-27 |
not yet calculated |
CVE-2021-25311
MISC |
| htcondor — htcondor |
HTCondor before 8.9.11 allows a user to submit a job as another user on the system, because of a flaw in the IDTOKENS authentication method. |
2021-01-27 |
not yet calculated |
CVE-2021-25312
MISC |
ibm — infosphere_information_server
|
** UNSUPPORTED WHEN ASSIGNED ** IBM InfoSphere Information Server 8.5.0.0 is affected by deserialization of untrusted data which could allow remote unauthenticated attackers to execute arbitrary code. NOTE: This vulnerability only affects products that are no longer supported by the maintainer. |
2021-01-26 |
not yet calculated |
CVE-2020-27583
MISC |
ibm — mq
|
IBM MQ 7.5, 8.0, 9.0, 9.1, 9.2 LTS, and 9.2 CD could allow a remote attacker to execute arbitrary code on the system, caused by an unsafe deserialization of trusted data. An attacker could exploit this vulnerability to execute arbitrary code on the system. IBM X-Force ID: 186509. |
2021-01-28 |
not yet calculated |
CVE-2020-4682
XF
CONFIRM |
| ibm — qradar_siem |
IBM QRadar SIEM 7.4.0 to 7.4.2 Patch 1 and 7.3.0 to 7.3.3 Patch 7 could allow a remote attacker to execute arbitrary commands on the system, caused by insecure deserialization of user-supplied content by the Java deserialization function. By sending a malicious serialized Java object, an attacker could exploit this vulnerability to execute arbitrary commands on the system. IBM X-Force ID: 190912. |
2021-01-28 |
not yet calculated |
CVE-2020-4888
XF
CONFIRM |
ibm — qradar_siem
|
IBM QRadar SIEM 7.4.2 GA to 7.4.2 Patch 1, 7.4.0 to 7.4.1 Patch 1, and 7.3.0 to 7.3.3 Patch 5 is vulnerable to server side request forgery (SSRF). This may allow an authenticated attacker to send unauthorized requests from the system, potentially leading to network enumeration or facilitating other attacks. IBM X-Force ID: 189224. |
2021-01-27 |
not yet calculated |
CVE-2020-4787
XF
CONFIRM |
ibm — qradar_siem
|
IBM QRadar SIEM 7.4.2 GA to 7.4.2 Patch 1, 7.4.0 to 7.4.1 Patch 1, and 7.3.0 to 7.3.3 Patch 5 could allow a remote attacker to traverse directories on the system. An attacker could send a specially-crafted URL request containing “dot dot” sequences (/../) to view arbitrary files on the system. IBM X-Force ID: 189302. |
2021-01-27 |
not yet calculated |
CVE-2020-4789
XF
CONFIRM |
ibm — qradar_siem
|
IBM QRadar SIEM 7.4.2 GA to 7.4.2 Patch 1, 7.4.0 to 7.4.1 Patch 1, and 7.3.0 to 7.3.3 Patch 5 is vulnerable to server side request forgery (SSRF). This may allow an authenticated attacker to send unauthorized requests from the system, potentially leading to network enumeration or facilitating other attacks. IBM X-Force ID: 189221. |
2021-01-27 |
not yet calculated |
CVE-2020-4786
XF
CONFIRM |
ide_atapi_cmd_reply_end — ide_atapi_cmd_reply_end
|
ide_atapi_cmd_reply_end in hw/ide/atapi.c in QEMU 5.1.0 allows out-of-bounds read access because a buffer index is not validated. |
2021-01-26 |
not yet calculated |
CVE-2020-29443
MISC
MISC |
im — im
|
An issue was discovered in the im crate through 2020-11-09 for Rust. Because TreeFocus does not have bounds on its Send trait or Sync trait, a data race can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36204
MISC |
iniparserjs — iniparserjs
|
This affects all versions of package iniparserjs. This vulnerability relates when ini_parser.js is concentrating arrays. Depending on if user input is provided, an attacker can overwrite and pollute the object prototype of a program. |
2021-01-29 |
not yet calculated |
CVE-2021-23328
MISC
MISC |
istio_pilot — istio_pilot
|
A NULL pointer dereference was found in pkg/proxy/envoy/v2/debug.go getResourceVersion in Istio pilot before 1.5.0-alpha.0. If a particular HTTP GET request is made to the pilot API endpoint, it is possible to cause the Go runtime to panic (resulting in a denial of service to the istio-pilot application). |
2021-01-29 |
not yet calculated |
CVE-2019-25014
MISC
MISC |
jenkins — jenkins
|
Jenkins 2.275 and LTS 2.263.2 allows reading arbitrary files using the file browser for workspaces and archived artifacts due to a time-of-check to time-of-use (TOCTOU) race condition. |
2021-01-26 |
not yet calculated |
CVE-2021-21615
MLIST
CONFIRM |
jp2_ decode — jp2_decode
|
jp2_decode in jp2/jp2_dec.c in libjasper in JasPer 2.0.24 has a heap-based buffer over-read when there is an invalid relationship between the number of channels and the number of image components. |
2021-01-27 |
not yet calculated |
CVE-2021-3272
MISC |
jxbrowser — ti_code_composer_studio_ide
|
jxbrowser in TI Code Composer Studio IDE 8.x through 10.x before 10.1.1 does not verify X.509 certificates for HTTPS. |
2021-01-26 |
not yet calculated |
CVE-2021-3285
MISC |
klog — klog_server
|
KLog Server through 2.4.1 allows authenticated command injection. async.php calls shell_exec() on the original value of the source parameter. |
2021-01-26 |
not yet calculated |
CVE-2021-3317
MISC |
late-static — late-static
|
An issue was discovered in the late-static crate before 0.4.0 for Rust. Because Sync is implemented for LateStatic with T: Send, a data race can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36209
MISC |
lazy-init — lazy-init
|
An issue was discovered in the lazy-init crate through 2021-01-17 for Rust. Lazy lacks a Send bound, leading to a data race. |
2021-01-26 |
not yet calculated |
CVE-2021-25901
MISC |
libgcrypt — libgcrypt
|
_gcry_md_block_write in cipher/hash-common.c in Libgcrypt before 1.9.1 has a heap-based buffer overflow when the digest final function sets a large count value. |
2021-01-29 |
not yet calculated |
CVE-2021-3345
MISC
MISC
MISC
MISC
MISC |
linux — linux_kernel
|
A flaw incorrect umask during file or directory modification in the Linux kernel NFS (network file system) functionality was found in the way user create and delete object using NFSv4.2 or newer if both simultaneously accessing the NFS by the other process that is not using new NFSv4.2. A user with access to the NFS could use this flaw to starve the resources causing denial of service. |
2021-01-26 |
not yet calculated |
CVE-2020-35513
MISC
MISC |
linux — linux_kernel
|
An issue was discovered in the Linux kernel through 5.10.11. PI futexes have a kernel stack use-after-free during fault handling, allowing local users to execute code in the kernel, aka CID-34b1a1ce1458. |
2021-01-29 |
not yet calculated |
CVE-2021-3347
MLIST
MLIST
MISC
MISC
MISC
MISC
MISC
MISC
MISC
MISC
MISC
MISC |
local_service — search_engine_management
|
Local Service Search Engine Management System 1.0 has a vulnerability through authentication bypass using SQL injection . Using this vulnerability, an attacker can bypass the login page. |
2021-01-26 |
not yet calculated |
CVE-2021-3278
MISC
MISC |
logstorage — logstorage
|
Logstorage version 8.0.0 and earlier, and ELC Analytics version 3.0.0 and earlier allow remote attackers to execute arbitrary OS commands via a specially crafted log file. |
2021-01-28 |
not yet calculated |
CVE-2020-5626
MISC
MISC |
m&m_software — fdtcontainer_component
|
M&M Software fdtCONTAINER Component in versions below 3.5.20304.x and between 3.6 and 3.6.20304.x is vulnerable to deserialization of untrusted data in its project storage. |
2021-01-22 |
not yet calculated |
CVE-2020-12525
CONFIRM
MISC |
madcodehook — madcodehook
|
A TOCTOU vulnerability exists in madCodeHook before 2020-07-16 that allows local attackers to elevate their privileges to SYSTEM. This occurs because path redirection can occur via vectors involving directory junctions. |
2021-01-30 |
not yet calculated |
CVE-2020-14418
MISC
MISC |
marc_crate — marc_crate
|
An issue was discovered in the marc crate before 2.0.0 for Rust. A user-provided Read implementation can gain access to the old contents of newly allocated memory, violating soundness. |
2021-01-29 |
not yet calculated |
CVE-2021-26308
MISC |
matrikon — opc_ua_tunneller
|
The affected product is vulnerable to a heap-based buffer overflow, which may allow an attacker to manipulate memory with controlled values and remotely execute code on the OPC UA Tunneller (versions prior to 6.3.0.8233). |
2021-01-26 |
not yet calculated |
CVE-2020-27297
MISC |
matrikon — opc_ua_tunneller
|
The affected product is vulnerable to an out-of-bounds read, which may allow an attacker to obtain and disclose sensitive data information or cause the device to crash on the OPC UA Tunneller (versions prior to 6.3.0.8233). |
2021-01-26 |
not yet calculated |
CVE-2020-27299
MISC |
matrikon — opc_ua_tunneller
|
The affected product has uncontrolled resource consumption issues, which may allow an attacker to cause a denial-of-service condition on the OPC UA Tunneller (versions prior to 6.3.0.8233). |
2021-01-26 |
not yet calculated |
CVE-2020-27295
MISC |
matrikon — opc_ua_tunneller
|
Some parsing functions in the affected product do not check the return value of malloc and the thread handling the message is forced to close, which may lead to a denial-of-service condition on the OPC UA Tunneller (versions prior to 6.3.0.8233). |
2021-01-26 |
not yet calculated |
CVE-2020-27274
MISC |
mautic — mautic
|
A cross-site scripting (XSS) vulnerability in the assets component of Mautic before 3.2.4 allows remote attackers to inject executable JavaScript through the Referer header of asset downloads. |
2021-01-28 |
not yet calculated |
CVE-2020-35124
MISC
MISC
MISC
MISC |
may_queue — may_queue
|
An issue was discovered in the may_queue crate through 2020-11-10 for Rust. Because Queue does not have bounds on its Send trait or Sync trait, memory corruption can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36217
MISC |
mediawiki — mediawiki
|
The API in the Push extension for MediaWiki through 1.35 did not require an edit token in ApiPushBase.php and therefore facilitated a CSRF attack. |
2021-01-29 |
not yet calculated |
CVE-2020-29004
MISC
CONFIRM
MISC |
mediawiki — mediawiki
|
The API in the Push extension for MediaWiki through 1.35 used cleartext for ApiPush credentials, allowing for potential information disclosure. |
2021-01-29 |
not yet calculated |
CVE-2020-29005
MISC
MISC |
melfa — fr_series_controllers
|
Resource management errors vulnerability in a robot controller of MELFA FR Series(controller “CR800-*V*D” of RV-*FR***-D-* all versions, controller “CR800-*HD” of RH-*FRH***-D-* all versions, controller “CR800-*HRD” of RH-*FRHR***-D-* all versions, controller “CR800-*V*R with R16RTCPU” of RV-*FR***-R-* all versions, controller “CR800-*HR with R16RTCPU” of RH-*FRH***-R-* all versions, controller “CR800-*HRR with R16RTCPU” of RH-*FRHR***-R-* all versions, controller “CR800-*V*Q with Q172DSRCPU” of RV-*FR***-Q-* all versions, controller “CR800-*HQ with Q172DSRCPU” of RH-*FRH***-Q-* all versions, controller “CR800-*HRQ with Q172DSRCPU” of RH-*FRHR***-Q-* all versions) and a robot controller of MELFA CR Series(controller “CR800-CVD” of RV-8CRL-D-* all versions, controller “CR800-CHD” of RH-*CRH**-D-* all versions) as well as a cooperative robot ASSISTA(controller “CR800-05VD” of RV-5AS-D-* all versions) allows a remote unauthenticated attacker to cause a DoS of the execution of the robot program and the Ethernet communication by sending a large amount of packets in burst over a short period of time. As a result of DoS, an error may occur. A reset is required to recover it if the error occurs. |
2021-01-29 |
not yet calculated |
CVE-2021-20586
MISC |
micrium — uchttp
|
A denial-of-service vulnerability exists in the HTTP Server functionality of Micrium uC-HTTP 3.01.00. A specially crafted HTTP request can lead to denial of service. An attacker can send an HTTP request to trigger this vulnerability. |
2021-01-26 |
not yet calculated |
CVE-2020-13582
MISC |
microsoft — windows
|
Insider Threat Management Windows Agent Local Privilege Escalation Vulnerability The Proofpoint Insider Threat Management (formerly ObserveIT) Agent for Windows before 7.4.3, 7.5.4, 7.6.5, 7.7.5, 7.8.4, 7.9.3, 7.10.2, and 7.11.0.25 as well as versions 7.3 and earlier is missing authentication for a critical function, which allows a local authenticated Windows user to run arbitrary commands with the privileges of the Windows SYSTEM user. Agents for MacOS, Linux, and ITM Cloud are not affected. |
2021-01-26 |
not yet calculated |
CVE-2021-22159
MISC
MISC |
mitel — businesscti_enterprise_client_for_windows
|
The chat window of the Mitel BusinessCTI Enterprise (MBC-E) Client for Windows before 6.4.15 and 7.x before 7.1.2 could allow an attacker to gain access to user information by sending certain code, due to improper input validation of http links. A successful exploit could allow an attacker to view user information and application data. |
2021-01-29 |
not yet calculated |
CVE-2021-3176
MISC
CONFIRM |
mitel — micollab
|
A library index page in NuPoint Messenger in Mitel MiCollab before 9.2 FP1 could allow an unauthenticated attacker to gain access (view and modify) to user data. |
2021-01-29 |
not yet calculated |
CVE-2020-35547
MISC
CONFIRM |
monitorix — monitorix
|
Monitorix 3.13.0 allows remote attackers to bypass Basic Authentication in a default installation (i.e., an installation without a hosts_deny option). This issue occurred because a new access-control feature was introduced without considering that some exiting installations became unsafe, upon an update to 3.13.0, unless the new feature was immediately configured. |
2021-01-27 |
not yet calculated |
CVE-2021-3325
MISC
MISC
MISC
CONFIRM |
| moodle — moodle |
It was found in Moodle before version 3.10.1, 3.9.4 and 3.8.7 that a insufficient capability checks in some grade related web services meant students were able to view other students grades. |
2021-01-28 |
not yet calculated |
CVE-2021-20184
MISC |
| moodle — moodle |
It was found in Moodle before version 3.10.1, 3.9.4, 3.8.7 and 3.5.16 that it was possible for site administrators to execute arbitrary PHP scripts via a PHP include used during Shibboleth authentication. |
2021-01-28 |
not yet calculated |
CVE-2021-20187
MISC |
moodle — moodle
|
It was found in Moodle before version 3.10.1 that some search inputs were vulnerable to reflected XSS due to insufficient escaping of search queries. |
2021-01-28 |
not yet calculated |
CVE-2021-20183
MISC |
moodle — moodle
|
It was found in Moodle before version 3.10.1, 3.9.4, 3.8.7 and 3.5.16 that messaging did not impose a character limit when sending messages, which could result in client-side (browser) denial of service for users receiving very large messages. |
2021-01-28 |
not yet calculated |
CVE-2021-20185
MISC |
moodle — moodle
|
It was found in Moodle before version 3.10.1, 3.9.4, 3.8.7 and 3.5.16 that if the TeX notation filter was enabled, additional sanitizing of TeX content was required to prevent the risk of stored XSS. |
2021-01-28 |
not yet calculated |
CVE-2021-20186
MISC |
multiqueue2 — multiqueue2
|
An issue was discovered in the multiqueue2 crate before 0.1.7 for Rust. Because a non-Send type can be sent to a different thread, a data race can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36214
MISC |
mybb — mybb
|
The Hide-Thread-Content plugin through 2021-01-27 for MyBB allows remote attackers to bypass intended content-reading restrictions by clicking on reply or quote in the postbit. |
2021-01-28 |
not yet calculated |
CVE-2021-3337
MISC
MISC |
nagios — docker_config_wizard
|
Improper access and command validation in the Nagios Docker Config Wizard before 1.1.2, as used in Nagios XI through 5.7, allows an unauthenticated attacker to execute remote code as the apache user. |
2021-01-26 |
not yet calculated |
CVE-2021-3193
MISC |
newbee-mall — newbee-mall
|
newbee-mall all versions are affected by incorrect access control to remotely gain privileges through NewBeeMallIndexConfigServiceImpl.java. Unauthorized changes can be made to any user information through the userID. |
2021-01-26 |
not yet calculated |
CVE-2020-23449
MISC |
newbee-mall — newbee-mall
|
newbee-mall all versions are affected by incorrect access control to remotely gain privileges through AdminLoginInterceptor.java. The authentication logic of the system’s background /admin is in code AdminLoginInterceptor, which can be bypassed. |
2021-01-26 |
not yet calculated |
CVE-2020-23448
MISC |
nextcloud — nextcloud_server
|
A missing input validation in Nextcloud Server before 20.0.2, 19.0.5, 18.0.11 allows users to store unlimited data in workflow rules causing load and potential DDoS on later interactions and usage with those rules. |
2021-01-26 |
not yet calculated |
CVE-2020-8293
MISC
MISC |
nextcloud — nextcloud_server
|
A wrong check in Nextcloud Server 19 and prior allowed to perform a denial of service attack when resetting the password for a user. |
2021-01-26 |
not yet calculated |
CVE-2020-8295
MISC
MISC |
nibbleblog — nibbleblog
|
dmin/kernel/api/login.class.phpin in nibbleblog v3.7.1c allows type juggling for login bypass because == is used instead of === for password hashes, which mishandles hashes that begin with 0e followed by exclusively numerical characters. |
2021-01-27 |
not yet calculated |
CVE-2020-23356
MISC |
nim — nim
|
In Nim before 1.2.6, the standard library asyncftpclient lacks a check for whether a message contains a newline character. |
2021-01-30 |
not yet calculated |
CVE-2020-15690
MISC
CONFIRM |
node-red-contrib-huemagic — node-red-contrib-huemagic
|
node-red-contrib-huemagic 3.0.0 is affected by hue/assets/..%2F Directory Traversal.in the res.sendFile API, used in file hue-magic.js, to fetch an arbitrary file. |
2021-01-26 |
not yet calculated |
CVE-2021-25864
MISC |
nutch — dmozparser
|
An XML external entity (XXE) injection vulnerability was discovered in the Nutch DmozParser and is known to affect Nutch versions < 1.18. XML external entity injection (also known as XXE) is a web security vulnerability that allows an attacker to interfere with an application’s processing of XML data. It often allows an attacker to view files on the application server filesystem, and to interact with any back-end or external systems that the application itself can access. This issue is fixed in Apache Nutch 1.18. |
2021-01-25 |
not yet calculated |
CVE-2021-23901
CONFIRM
CONFIRM
MLIST
MLIST |
nvidia — multiple_products
|
NVIDIA Tegra kernel in Jetson AGX Xavier Series, Jetson Xavier NX, TX1, TX2, Nano and Nano 2GB, all L4T versions prior to r32.5, contains a vulnerability in the INA3221 driver in which improper access control may lead to unauthorized users gaining access to system power usage data, which may lead to information disclosure. |
2021-01-26 |
not yet calculated |
CVE-2021-1071
CONFIRM |
nvidia — multiple_products
|
NVIDIA Jetson AGX Xavier Series, Jetson Xavier NX, TX1, TX2, Nano and Nano 2GB, L4T versions prior to 32.5, contains a vulnerability in the apply_binaries.sh script used to install NVIDIA components into the root file system image, in which improper access control is applied, which may lead to an unprivileged user being able to modify system device tree files, leading to denial of service. |
2021-01-26 |
not yet calculated |
CVE-2021-1070
CONFIRM |
octopusdsc — octopusdsc
|
OctopusDSC is a PowerShell module with DSC resources that can be used to install and configure an Octopus Deploy Server and Tentacle agent. In OctopusDSC version 4.0.977 and earlier a customer API key used to connect to Octopus Server is exposed via logging in plaintext. This vulnerability is patched in version 4.0.1002. |
2021-01-22 |
not yet calculated |
CVE-2021-21270
MISC
MISC
MISC
CONFIRM |
oncommand — unified_manager_core_package
|
OnCommand Unified Manager Core Package versions prior to 5.2.5 may disclose sensitive account information to unauthorized users via the use of PuTTY Link (plink). |
2021-01-28 |
not yet calculated |
CVE-2020-8585
MISC
CONFIRM |
online_news_portal — online_news_portal
|
Online News Portal using PHP/MySQLi 1.0 is affected by cross-site scripting (XSS) which allows remote attackers to inject an arbitrary web script or HTML via the “Title” parameter. |
2021-01-26 |
not yet calculated |
CVE-2020-29241
MISC |
onlyoffice — document_server
|
Directory traversal with remote code execution can occur in /upload in ONLYOFFICE Document Server before 5.6.3, when JWT is used, via a /.. sequence in an image upload parameter. |
2021-01-26 |
not yet calculated |
CVE-2021-3199
MISC
CONFIRM |
open5gs — open5gs
|
Open5GS 2.1.3 listens on 0.0.0.0:3000 and has a default password of 1423 for the admin account. |
2021-01-26 |
not yet calculated |
CVE-2021-25863
MISC |
openemr — openemr
|
A cross-site request forgery vulnerability exists in the GACL functionality of OpenEMR 5.0.2 and development version 6.0.0 (commit babec93f600ff1394f91ccd512bcad85832eb6ce). A specially crafted HTTP request can lead to the execution of arbitrary requests in the context of the victim. An attacker can send an HTTP request to trigger this vulnerability. |
2021-01-28 |
not yet calculated |
CVE-2020-13569
MISC |
openjpeg2 — openjpeg2
|
A heap-buffer overflow was found in the way openjpeg2 handled certain PNG format files. An attacker could use this flaw to cause an application crash or in some cases execute arbitrary code with the permission of the user running such an application. |
2021-01-26 |
not yet calculated |
CVE-2020-27814
MISC
MISC
GENTOO |
openmaint — openmaint
|
openMAINT before 1.1-2.4.2 allows remote authenticated users to run arbitrary JSP code on the underlying web server. |
2021-01-26 |
not yet calculated |
CVE-2020-24549
MISC
MISC |
opensolution — quick
|
OpenSolution Quick.CMS < 6.7 and Quick.Cart < 6.7 allow an authenticated user to perform code injection (and consequently Remote Code Execution) via the input fields of the Language tab. |
2021-01-28 |
not yet calculated |
CVE-2020-35754
MISC
MISC
CONFIRM
MISC |
oras — oras
|
ORAS is open source software which enables a way to push OCI Artifacts to OCI Conformant registries. ORAS is both a CLI for initial testing and a Go Module. In ORAS from version 0.4.0 and before version 0.9.0, there is a “zip-slip” vulnerability. The directory support feature allows the downloaded gzipped tarballs to be automatically extracted to the user-specified directory where the tarball can have symbolic links and hard links. A well-crafted tarball or tarballs allow malicious artifact providers linking, writing, or overwriting specific files on the host filesystem outside of the user-specified directory unexpectedly with the same permissions as the user who runs `oras pull`. Users of the affected versions are impacted if they are `oras` CLI users who runs `oras pull`, or if they are Go programs, which invoke `github.com/deislabs/oras/pkg/content.FileStore`. The problem has been fixed in version 0.9.0. For `oras` CLI users, there is no workarounds other than pulling from a trusted artifact provider. For `oras` package users, the workaround is to not use `github.com/deislabs/oras/pkg/content.FileStore`, and use other content stores instead, or pull from a trusted artifact provider. |
2021-01-25 |
not yet calculated |
CVE-2021-21272
MISC
MISC
CONFIRM
MISC |
oscommerce — oscommerce
|
oscommerce v2.3.4.1 has a functional problem in user registration and password rechecking, where a non-identical password can bypass the checks in /catalog/admin/administrators.php and /catalog/password_reset.php |
2021-01-27 |
not yet calculated |
CVE-2020-23360
MISC |
persis — human_resouce_management_portal
|
The job posting recommendation form in Persis Human Resource Management Portal (Versions 17.2.00 through 17.2.35 and 19.0.00 through 19.0.20), when the “Recommend job posting” function is enabled, allows XSS via the SENDER parameter. |
2021-01-26 |
not yet calculated |
CVE-2020-35753
MISC |
philips — interventional_workspot
|
Philips Interventional Workspot (Release 1.3.2, 1.4.0, 1.4.1, 1.4.3, 1.4.5), Coronary Tools/Dynamic Coronary Roadmap/Stentboost Live (Release 1.0), ViewForum (Release 6.3V1L10). The software constructs all or part of an OS command using externally influenced input from an upstream component but does not neutralize or incorrectly neutralizes special elements that could modify the intended OS command when sent to a downstream component. |
2021-01-26 |
not yet calculated |
CVE-2020-27298
MISC |
phplist — phplist
|
phpList 3.6.0 allows CSV injection, related to the email parameter, and /lists/admin/ exports. |
2021-01-26 |
not yet calculated |
CVE-2021-3188
MISC |
phplist — phplist
|
phpList 3.5.3 allows type juggling for login bypass because == is used instead of === for password hashes, which mishandles hashes that begin with 0e followed by exclusively numerical characters. |
2021-01-27 |
not yet calculated |
CVE-2020-23361
MISC |
projectsend — projectsend
|
reset-password.php in ProjectSend before r1295 allows remote attackers to reset a password because of incorrect business logic. Errors are not properly considered (an invalid token parameter). |
2021-01-26 |
not yet calculated |
CVE-2020-28874
MISC
CONFIRM
MISC
CONFIRM
MISC |
pyrescom — termod4_time_management_devices
|
Local file inclusion in Pyrescom Termod4 time management devices before 10.04k allows authenticated remote attackers to traverse directories and read sensitive files via the Maintenance > Logs menu and manipulating the file-path in the URL. |
2021-01-26 |
not yet calculated |
CVE-2020-23161
MISC
MISC |
pyrescom — termod4_time_management_devices
|
Sensitive information disclosure and weak encryption in Pyrescom Termod4 time management devices before 10.04k allows remote attackers to read a session-file and obtain plain-text user credentials. |
2021-01-26 |
not yet calculated |
CVE-2020-23162
MISC
MISC |
qdocs — smart_hospital_management_system
|
A cross-site scripting (XSS) issue in Add Patient Form in QDOCS Smart Hospital Management System 3.1 allows a remote attacker to inject arbitrary code via the Name, Guardian Name, Email, Address, Remarks, or Any Known Allergies field. |
2021-01-26 |
not yet calculated |
CVE-2020-36011
MISC
MISC |
qemu — qemu
|
A flaw was found in qemu. A host privilege escalation issue was found in the virtio-fs shared file system daemon where a privileged guest user is able to create a device special file in the shared directory and use it to r/w access host devices. |
2021-01-28 |
not yet calculated |
CVE-2020-35517
MISC
MISC
MISC
MISC |
qemu — sdhci_devices
|
A heap-based buffer overflow was found in QEMU through 5.0.0 in the SDHCI device emulation support. It could occur while doing a multi block SDMA transfer via the sdhci_sdma_transfer_multi_blocks() routine in hw/sd/sdhci.c. A guest user or process could use this flaw to crash the QEMU process on the host, resulting in a denial of service condition, or potentially execute arbitrary code with privileges of the QEMU process on the host. |
2021-01-30 |
not yet calculated |
CVE-2020-17380
CONFIRM
CONFIRM |
raw-cpuid_crate — raw-cpuid_crate
|
An issue was discovered in the raw-cpuid crate before 9.0.0 for Rust. It has unsound transmute calls within as_string() methods. |
2021-01-29 |
not yet calculated |
CVE-2021-26306
MISC |
raw-cpuid_crate — raw-cpuid_crate
|
An issue was discovered in the raw-cpuid crate before 9.0.0 for Rust. It allows __cpuid_count() calls even if the processor does not support the CPUID instruction, which is unsound and causes a deterministic crash. |
2021-01-29 |
not yet calculated |
CVE-2021-26307
MISC |
redhat — keycloak
|
A flaw was found in keycloak before version 13.0.0. In some scenarios a user still has access to a resource after changing the role mappings in Keycloak and after expiration of the previous access token. |
2021-01-28 |
not yet calculated |
CVE-2020-1725
MISC
MISC |
redhat — keycloak
|
The logout endpoint /oauth/logout?redirect=url can be abused to redirect logged in users to arbitrary web pages. This vulnerability could be used in phishing attacks. Versions shipped with Red Hat Mobile Aplication Platform 4 are believed to be vulnerable. |
2021-01-28 |
not yet calculated |
CVE-2020-1723
MISC |
reffers — reffers
|
An issue was discovered in the reffers crate through 2020-12-01 for Rust. ARefss can contain a !Send,!Sync object, leading to a data race and memory corruption. |
2021-01-26 |
not yet calculated |
CVE-2020-36203
MISC |
revive — adserver
|
Revive Adserver before 5.1.0 permits any user with a manager account to store possibly malicious content in the URL website property, which is then displayed unsanitized in the affiliate-preview.php tag generation screen, leading to a persistent cross-site scripting (XSS) vulnerability. |
2021-01-26 |
not yet calculated |
CVE-2021-22871
MISC
FULLDISC
MISC
MISC
MISC
MISC |
revive — adserver
|
Revive Adserver before 5.1.0 is vulnerable to a reflected cross-site scripting (XSS) vulnerability via the publicly accessible afr.php delivery script. While this issue was previously addressed in modern browsers as CVE-2020-8115, some older browsers (e.g., IE10) that do not automatically URL encode parameters were still vulnerable. |
2021-01-26 |
not yet calculated |
CVE-2021-22872
MISC
FULLDISC
MISC
MISC
MISC
MISC |
revive — adserver
|
Revive Adserver before 5.1.0 is vulnerable to open redirects via the `dest`, `oadest`, and/or `ct0` parameters of the lg.php and ck.php delivery scripts. Such open redirects had previously been available by design to allow third party ad servers to track such metrics when delivering ads. However, third party click tracking via redirects is not a viable option anymore, leading to such open redirect functionality being removed and reclassified as a vulnerability. |
2021-01-26 |
not yet calculated |
CVE-2021-22873
MISC
FULLDISC
MISC
MISC
MISC |
riolink — p2p_products
|
The affected Reolink P2P products do not sufficiently protect data transferred between the local device and Reolink servers. This can allow an attacker to access sensitive information, such as camera feeds. |
2021-01-26 |
not yet calculated |
CVE-2020-25169
MISC |
riolink — p2p_products
|
An attacker with local network access can obtain a fixed cryptography key which may allow for further compromise of Reolink P2P cameras outside of local network access |
2021-01-26 |
not yet calculated |
CVE-2020-25173
MISC |
rocket.chat — rocket.chat
|
The `specializedRendering` function in Rocket.Chat server before 3.9.2 allows a cross-site scripting (XSS) vulnerability by way of the `value` parameter. |
2021-01-26 |
not yet calculated |
CVE-2020-8288
MISC
MISC
MISC |
| rostelecom — cs-c2shw |
Denial of Service vulnerability in Rostelecom CS-C2SHW 5.0.082.1. AgentGreen service has a bug in parsing broadcast discovery UDP packet. Sending a packet of too small size will lead to an attempt of allocating buffer of negative size. As the result service AgentGreen will be terminated and started again later. |
2021-01-26 |
not yet calculated |
CVE-2020-27541
MISC |
rostelecom — cs-c2shw
|
Rostelecom CS-C2SHW 5.0.082.1 is affected by: Bash command injection. The camera reads configuration from QR code (including network settings). The static IP configuration from QR code is copied to the file /config/ip-static and after reboot data from this file is inserted into bash command (without any escaping). So bash injection is possible. Camera doesn’t parse QR codes if it’s already successfully configured. Camera is always rebooted after successful configuration via QR code. |
2021-01-26 |
not yet calculated |
CVE-2020-27542
MISC |
rostelecom — cs-c2shw
|
Bash injection vulnerability and bypass of signature verification in Rostelecom CS-C2SHW 5.0.082.1. The camera reads firmware update configuration from SD card file vcversion.json. fw-sign parameter and from this configuration is directly inserted into a bash command. Firmware update is run automatically if there is special file on the inserted SD card. |
2021-01-26 |
not yet calculated |
CVE-2020-27540
MISC |
rostelecom — cs-c2shw
|
Heap overflow with full parsing of HTTP respose in Rostelecom CS-C2SHW 5.0.082.1. AgentUpdater service has a self-written HTTP parser and builder. HTTP parser has a heap buffer overflow (OOB write). In default configuration camera parses responses only from HTTPS URLs from config file, so vulnerable code is unreachable and one more bug required to reach it. |
2021-01-26 |
not yet calculated |
CVE-2020-27539
MISC |
| rsshub — rsshub |
RSSHub is an open source, easy to use, and extensible RSS feed generator. In RSSHub before version 7f1c430 (non-semantic versioning) there is a risk of code injection. Some routes use `eval` or `Function constructor`, which may be injected by the target site with unsafe code, causing server-side security issues The fix in version 7f1c430 is to temporarily remove the problematic route and added a `no-new-func` rule to eslint. |
2021-01-26 |
not yet calculated |
CVE-2021-21278
MISC
CONFIRM
MISC |
rusb — rusb
|
An issue was discovered in the rusb crate before 0.7.0 for Rust. Because of a lack of Send and Sync bounds, a data race and memory corruption can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36206
MISC |
sagemcom — f@st_3686_v2_3.495_devices
|
Sagemcom F@ST 3686 v2 3.495 devices have a buffer overflow via a long sessionKey to the goform/login URI. |
2021-01-26 |
not yet calculated |
CVE-2021-3304
MISC |
sangoma — asterisk
|
An issue was discovered in res_pjsip_diversion.c in Sangoma Asterisk before 13.38.0, 14.x through 16.x before 16.15.0, 17.x before 17.9.0, and 18.x before 18.1.0. A crash can occur when a SIP message is received with a History-Info header that contains a tel-uri, or when a SIP 181 response is received that contains a tel-uri in the Diversion header. |
2021-01-29 |
not yet calculated |
CVE-2020-35652
CONFIRM
CONFIRM
MISC
MISC |
smallvec — smallvec
|
An issue was discovered in the smallvec crate before 0.6.14 and 1.x before 1.6.1 for Rust. There is a heap-based buffer overflow in SmallVec::insert_many. |
2021-01-26 |
not yet calculated |
CVE-2021-25900
MISC |
smartagent — smartagent
|
SmartAgent 3.1.0 allows a ViewOnly attacker to create a SuperUser account via the /#/CampaignManager/users URI. |
2021-01-26 |
not yet calculated |
CVE-2021-3165
MISC
MISC
MISC |
spring_cloud — data_flow
|
In Spring Cloud Data Flow, versions 2.6.x prior to 2.6.5, versions 2.5.x prior 2.5.4, an application is vulnerable to SQL injection when requesting task execution. |
2021-01-27 |
not yet calculated |
CVE-2020-5427
CONFIRM |
spring_cloud — task
|
In applications using Spring Cloud Task 2.2.4.RELEASE and below, may be vulnerable to SQL injection when exercising certain lookup queries in the TaskExplorer. |
2021-01-27 |
not yet calculated |
CVE-2020-5428
CONFIRM |
student_result_management_system — student_result_management_system
|
Student Result Management System In PHP With Source Code is affected by SQL injection. An attacker can able to access of Admin Panel and manage every account of Result. |
2021-01-26 |
not yet calculated |
CVE-2020-35270
MISC
MISC |
sudo — sudo
|
Sudo before 1.9.5p2 has a Heap-based Buffer Overflow, allowing privilege escalation to root via “sudoedit -s” and a command-line argument that ends with a single backslash character. |
2021-01-26 |
not yet calculated |
CVE-2021-3156
MISC
MLIST
MLIST
MLIST
FEDORA
FEDORA
GENTOO
CONFIRM
CONFIRM
CISCO
DEBIAN
MISC
CONFIRM |
tenda — ac5_ac1200
|
A Stored Cross-site scripting (XSS) vulnerability in /main.html Wifi Settings in Tenda AC5 AC1200 version V15.03.06.47_multi allows remote attackers to inject arbitrary web script or HTML via the Wifi Name parameter. |
2021-01-26 |
not yet calculated |
CVE-2021-3186
MISC
MISC |
tendermint — tendermint_core
|
Tendermint Core is an open source Byzantine Fault Tolerant (BFT) middleware that takes a state transition machine – written in any programming language – and securely replicates it on many machines. Tendermint Core v0.34.0 introduced a new way of handling evidence of misbehavior. As part of this, we added a new Timestamp field to Evidence structs. This timestamp would be calculated using the same algorithm that is used when a block is created and proposed. (This algorithm relies on the timestamp of the last commit from this specific block.) In Tendermint Core v0.34.0-v0.34.2, the consensus reactor is responsible for forming DuplicateVoteEvidence whenever double signs are observed. However, the current block is still “in flight” when it is being formed by the consensus reactor. It hasn’t been finalized through network consensus yet. This means that different nodes in the network may observe different “last commits” when assigning a timestamp to DuplicateVoteEvidence. In turn, different nodes could form DuplicateVoteEvidence objects at the same height but with different timestamps. One DuplicateVoteEvidence object (with one timestamp) will then eventually get finalized in the block, but this means that any DuplicateVoteEvidence with a different timestamp is considered invalid. Any node that formed invalid DuplicateVoteEvidence will continue to propose invalid evidence; its peers may see this, and choose to disconnect from this node. This bug means that double signs are DoS vectors in Tendermint Core v0.34.0-v0.34.2. Tendermint Core v0.34.3 is a security release which fixes this bug. As of v0.34.3, DuplicateVoteEvidence is no longer formed by the consensus reactor; rather, the consensus reactor passes the Votes themselves into the EvidencePool, which is now responsible for forming DuplicateVoteEvidence. The EvidencePool has timestamp info that should be consistent across the network, which means that DuplicateVoteEvidence formed in this reactor should have consistent timestamps. This release changes the API between the consensus and evidence reactors. |
2021-01-26 |
not yet calculated |
CVE-2021-21271
MISC
MISC
CONFIRM |
terramaster — terramaster_tos
|
TerraMaster TOS before 4.1.29 has Invalid Parameter Checking that leads to code injection as root. This is a dynamic class method invocation vulnerability in include/exportUser.php, in which an attacker can trigger a call to the exec method with (for example) OS commands in the opt parameter. |
2021-01-30 |
not yet calculated |
CVE-2020-15568
MISC
MISC |
textpattern — textpattern
|
Textpattern 4.8.4 is affected by cross-site scripting (XSS) in the Body parameter. |
2021-01-26 |
not yet calculated |
CVE-2020-35854
MISC
MISC
MISC |
tibco — bpm_enterprise_and_bpm_enterprise_distribution
|
The Application Development Clients component of TIBCO Software Inc.’s TIBCO BPM Enterprise and TIBCO BPM Enterprise Distribution for TIBCO Silver Fabric contains a vulnerability that theoretically allows a low privileged attacker with network access to execute a Cross Site Scripting (XSS) attack on the affected system. Affected releases are TIBCO Software Inc.’s TIBCO BPM Enterprise: versions 4.3.0 and below and TIBCO BPM Enterprise Distribution for TIBCO Silver Fabric: versions 4.3.0 and below. |
2021-01-26 |
not yet calculated |
CVE-2021-23272
CONFIRM |
| tinycheck — tinycheck |
TinyCheck before commits 9fd360d and ea53de8 allowed an authenticated attacker to send an HTTP GET request to the crafted URLs. |
2021-01-26 |
not yet calculated |
CVE-2020-36200
MISC |
tinycheck — tinycheck
|
TinyCheck before commits 9fd360d and ea53de8 was vulnerable to command injection due to insufficient checks of input parameters in several places. |
2021-01-26 |
not yet calculated |
CVE-2020-36199
MISC |
tm_mobile_solutions — testes_de_codigo
|
Mobile application “Testes de Codigo” v11.3 and prior allows stored XSS by injecting a payload in the “feedback” message field causing it to be stored in the remote database and leading to its execution on client devices when loading the “feedback list”, either by accessing the website directly or using the mobile application. |
2021-01-28 |
not yet calculated |
CVE-2021-25647
MISC |
tp-link — tl-wr841N_v13
|
A Command Injection issue in the traceroute feature on TP-Link TL-WR841N V13 (JP) with firmware versions prior to 201216 allows authenticated users to execute arbitrary code as root via shell metacharacters, a different vulnerability than CVE-2018-12577. |
2021-01-26 |
not yet calculated |
CVE-2020-35576
MISC
MISC |
trendmicro — serverprotect
|
A memory exhaustion vulnerability in Trend Micro ServerProtect for Linux 3.0 could allow a local attacker to craft specific files that can cause a denial-of-service on the affected product. The specific flaw exists within a scheduled scan component. An attacker must first obtain the ability to execute low-privileged code on the target system in order to exploit this vulnerability. |
2021-01-27 |
not yet calculated |
CVE-2021-25225
N/A
N/A |
trendmicro — serverprotect
|
A memory exhaustion vulnerability in Trend Micro ServerProtect for Linux 3.0 could allow a local attacker to craft specific files that can cause a denial-of-service on the affected product. The specific flaw exists within a manual scan component. An attacker must first obtain the ability to execute low-privileged code on the target system in order to exploit this vulnerability. |
2021-01-27 |
not yet calculated |
CVE-2021-25224
N/A
N/A |
trendmicro — serverprotect
|
A memory exhaustion vulnerability in Trend Micro ServerProtect for Linux 3.0 could allow a local attacker to craft specific files that can cause a denial-of-service on the affected product. The specific flaw exists within a scan engine component. An attacker must first obtain the ability to execute low-privileged code on the target system in order to exploit this vulnerability. |
2021-01-27 |
not yet calculated |
CVE-2021-25226
N/A
N/A |
trendmirco — housecall_for_home_networks
|
A DLL hijacking vulnerability Trend Micro HouseCall for Home Networks version 5.3.1063 and below could allow an attacker to use a malicious DLL to escalate privileges and perform arbitrary code execution. An attacker must already have user privileges on the machine to exploit this vulnerability. |
2021-01-27 |
not yet calculated |
CVE-2021-25247
N/A |
va-ts — va-ts
|
An issue was discovered in the va-ts crate before 0.0.4 for Rust. Because Demuxer<T> omits a required T: Send bound, a data race and memory corruption can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36220
MISC |
vis-timeline — vis-timeline
|
This affects the package vis-timeline before 7.4.4. An attacker with the ability to control the items of a Timeline element can inject additional script code into the generated application. |
2021-01-22 |
not yet calculated |
CVE-2020-28487
CONFIRM
CONFIRM
CONFIRM
CONFIRM
CONFIRM |
webid — webid
|
WeBid 1.2.2 admin/newuser.php has an issue with password rechecking during registration because it uses a loose comparison to check the identicalness of two passwords. Two non-identical passwords can still bypass the check. |
2021-01-27 |
not yet calculated |
CVE-2020-23359
MISC |
wekan — wekan
|
packages/wekan-ldap/server/ldap.js in Wekan before 4.87 can process connections even though they are not authorized by the Certification Authority trust store, |
2021-01-26 |
not yet calculated |
CVE-2021-3309
MISC
MISC
MISC |
wing_ftp — wing_ftp
|
An XSS issue was discovered in Wing FTP 6.4.4. An arbitrary IFRAME element can be included in the help pages via a crafted link, leading to the execution of (sandboxed) arbitrary HTML and JavaScript in the user’s browser. |
2021-01-26 |
not yet calculated |
CVE-2020-27735
MISC
MISC |
winmail — winmail
|
A SSRF vulnerability exists in Winmail 6.5 in app.php in the key parameter when HTTPS is on. An attacker can use this vulnerability to cause the server to send a request to a specific URL. An attacker can modify the request header ‘HOST’ value to cause the server to send the request. |
2021-01-26 |
not yet calculated |
CVE-2020-23776
MISC |
winmail — winmail
|
A reflected XSS vulnerability exists in tohtml/convert.php of Winmail 6.5, which can cause JavaScript code to be executed. |
2021-01-26 |
not yet calculated |
CVE-2020-23774
MISC |
winscp — winscp
|
WinSCP before 5.17.10 allows remote attackers to execute arbitrary programs when the URL handler encounters a crafted URL that loads session settings. (For example, this is exploitable in a default installation in which WinSCP is the handler for sftp:// URLs.) |
2021-01-27 |
not yet calculated |
CVE-2021-3331
MISC
MISC
MISC
MISC |
wolfssl — tls13.c
|
DoTls13CertificateVerify in tls13.c in wolfSSL through 4.6.0 does not cease processing for certain anomalous peer behavior (sending an ED22519, ED448, ECC, or RSA signature without the corresponding certificate). |
2021-01-29 |
not yet calculated |
CVE-2021-3336
MISC |
xcb — xcb
|
An issue was discovered in the xcb crate through 2020-12-10 for Rust. base::Error does not have soundness. Because of the public ptr field, a use-after-free or double-free can occur. |
2021-01-26 |
not yet calculated |
CVE-2020-36205
MISC |
xen — xen
|
An issue was discovered in Xen 4.12.3 through 4.12.4 and 4.13.1 through 4.14.x. An x86 HVM guest with PCI pass through devices can force the allocation of all IDT vectors on the system by rebooting itself with MSI or MSI-X capabilities enabled and entries setup. Such reboots will leak any vectors used by the MSI(-X) entries that the guest might had enabled, and hence will lead to vector exhaustion on the system, not allowing further PCI pass through devices to work properly. HVM guests with PCI pass through devices can mount a Denial of Service (DoS) attack affecting the pass through of PCI devices to other guests or the hardware domain. In the latter case, this would affect the entire host. |
2021-01-26 |
not yet calculated |
CVE-2021-3308
MLIST
MISC
FEDORA |
xerox — workcentre_products
|
An issue was discovered in certain Xerox WorkCentre products. They do not properly encrypt passwords. This affects 3655, 3655i, 58XX, 58XXi 59XX, 59XXi, 6655, 6655i, 72XX, 72XXi 78XX, 78XXi, 7970, 7970i, EC7836, and EC7856 devices. |
2021-01-26 |
not yet calculated |
CVE-2020-36201
MISC |
yale — wipc-303w_cameras
|
** DISPUTED ** The Yale WIPC-303W 2.21 through 2.31 camera is vulnerable to remote command execution (RCE) through command injection via the HTTP API. NOTE: This may be a duplicate of CVE-2020-10176 . |
2021-01-26 |
not yet calculated |
CVE-2020-23826
MISC |
z-blogphp — valyria
|
Z-BlogPHP 1.6.0 Valyria is affected by incorrect access control. PHP loose comparison and a magic hash can be used to bypass authentication. zb_user/plugin/passwordvisit/include.php:passwordvisit_input_password() uses loose comparison to authenticate, which can be bypassed via magic hash values. |
2021-01-27 |
not yet calculated |
CVE-2020-23352
MISC |
zen — cart
|
Zen Cart 1.5.7b allows admins to execute arbitrary OS commands by inspecting an HTML radio input element (within the modules edit page) and inserting a command. |
2021-01-26 |
not yet calculated |
CVE-2021-3291
MISC |
ziv_automation — 4cct-ea6-334126bf
|
Improper Authentication vulnerability in the cookie parameter of ZIV AUTOMATION 4CCT-EA6-334126BF allows a local attacker to perform modifications in several parameters of the affected device as an authenticated user. |
2021-01-29 |
not yet calculated |
CVE-2021-25910
CONFIRM |
ziv_automation — 4cct-ea6-334126bf
|
ZIV Automation 4CCT-EA6-334126BF firmware version 3.23.80.27.36371, allows an unauthenticated, remote attacker to cause a denial of service condition on the device. An attacker could exploit this vulnerability by sending specific packets to the port 7919. |
2021-01-29 |
not yet calculated |
CVE-2021-25909
CONFIRM |
zte — multiple_products
|
Some ZTE products have a DoS vulnerability. Due to the improper handling of memory release in some specific scenarios, a remote attacker can trigger the vulnerability by performing a series of operations, resulting in memory leak, which may eventually lead to device denial of service. This affects: ZXR10 9904, ZXR10 9908, ZXR10 9916, ZXR10 9904-S, ZXR10 9908-S; all versions up to V1.01.10.B12. |
2021-01-26 |
not yet calculated |
CVE-2021-21723
MISC |
zyxel — nbg2105
|
On Zyxel NBG2105 V1.00(AAGU.2)C0 devices, setting the login cookie to 1 provides administrator access. |
2021-01-26 |
not yet calculated |
CVE-2021-3297
MISC
MISC
MISC |
by Contributed | Feb 1, 2021 | Technology
This article is contributed. See the original author and article here.
Here’s a quick review of the road so far:
CI CD in Azure Synapse Analytics Part 1
- Creating an Azure DevOps project
- Linking our Azure Synapse Analytics environment to that Project via Git
- Validating that our Azure DevOps Repo was populated with our Azure Synapse Analytics environment
CI CD in Azure Synapse Analytics Part 2:
- Create a new branch on our Repo
- Edit our Azure Synapse Analytics environment
- Specifically my SQL scripts have demos all over the place and Buck Woody said I have to clean up my very messy room …. Azure Synapse Analytics environment
- Create a Pull Request in Azure Synapse Analytics to merge our new branch with the main
- Approve the Pull Request in Azure DevOps
- Validate our main branch is updated in our Azure Synapse Analytics Environment
CI CD in Azure Synapse Analytics Part 3
- Create an Artifact pipeline
- This is to create an Artifact we can use to deploy to another environment
This time we will:
- Give our Azure DevOps Service Principal access to our Azure Synapse Workspace
- Validate or Give our Azure DevOps Service Principal Storage Contributor & User Access Administrator (*This is only if your storage account was provisioned before you created your Synapse Workspace or if you connect your Dev, QA, and Prod to the same ADLS G2 storage account. If you create your Synapse Workspace and Storage account from an ARM template deployed from DevOps, then your DevOps Service Principal will have Owner on the Storage Account and that gives the Service Principal User Access Administrator capabilities.)
- Create the release pipeline
- Validate the deployment
- *If you have SQL Provisioned Pools as part of your deployment pause them, because they will be created on deployment
Before we create our release pipeline we need to make sure the Azure Service Principal account has the proper permissions. If we do not, you well get cryptic errors with a GUID and something about “does not have permissions to blah blah blah”. Trust me, it is super annoying.
The two permission we will need are located in two different places, the first is in our Azure Synapse Workspace, specifically using Azure Synapse Studio. The second will be in the Storage Account for our Azure Data Lake Gen 2 that is the default ADLS connection for our Azure Synapse Studio.
First open your Azure Synapse Studio and navigate to the Management Blade.
Now Click on Access Control. The user that created the Azure Synapse Workspace is automatically given the role of Synapse Administrator, the second user with that role will be the Managed Identity for the Azure Synapse Workspace. We need to add our Azure DevOps Service Principal to this role.
*A quick note, I prefer to manage this in an Azure Active Directory Group. In this blog I will show how to add the account directly to the Azure Synapse Workspace. However, the best practice would be to have an AAD group that is granted Synapse Administrator and then add the role to that group.
Click the +Add link.
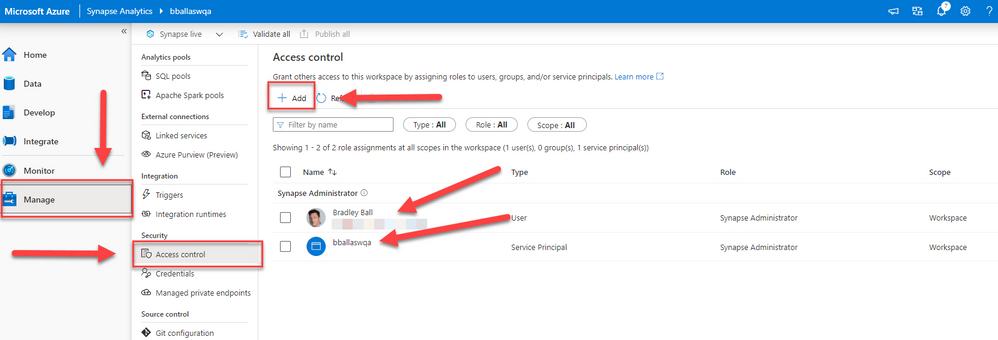
Now we will type in the Azure DevOps Project name. If your project URL was https://bobsburgers.visualstudio.net and your project name was Azure Synapse Studio CI CD you would type in bobsburgers-Azure Synapse Studio CI CD. This would show you the Service Principal GUID following that name.
Click the name as it appears and then click the Apply Button.
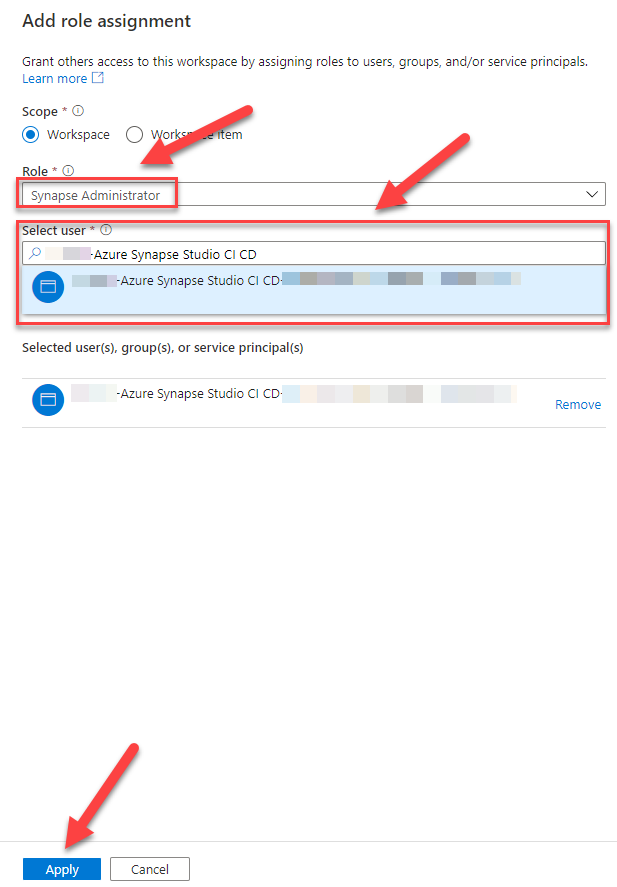
Now open a browser and navigate to the Azure Portal. In the search window at the type Storage Accounts. Select the storage account that you are using as your default ADLS Storage Account for your Azure Synapse Workspace. Click the Access Control (IAM) blade. Click +Add, then click Add role assignment.
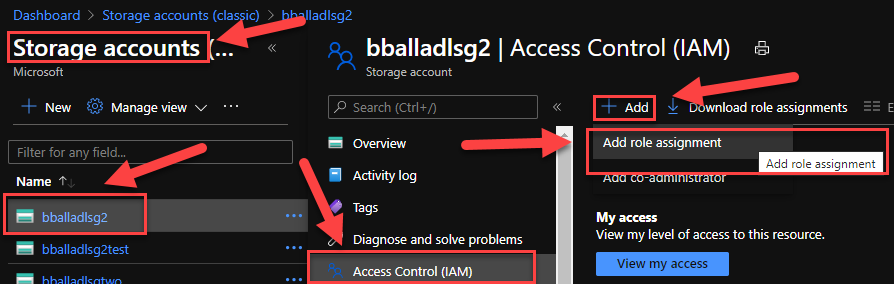
Select Storage Blob Data Contributor for Role. In the Select text box, type in the Azure DevOps Service Principal the same way we did in the for the Synapse Administrator role.
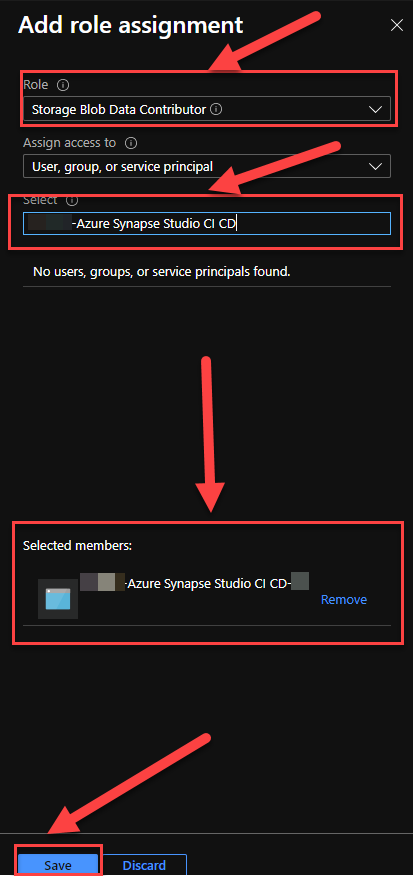
Repeat the previous steps, except this time specify the User Access Administrator Role.
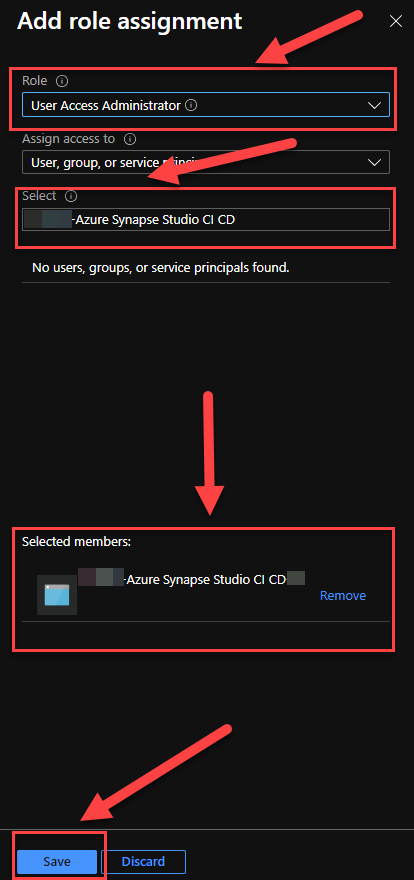
Next we will navigate to our Azure DevOps Project. Select pipelines, Releases, and New Pipeline.
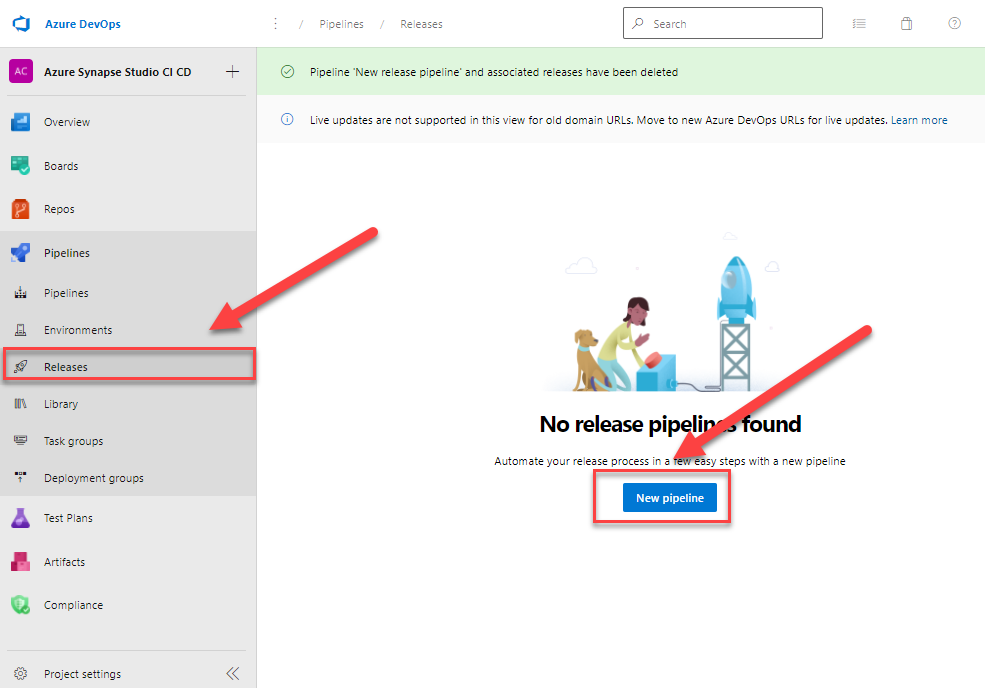
Click on Empty Job. Then click on Add an artifact.
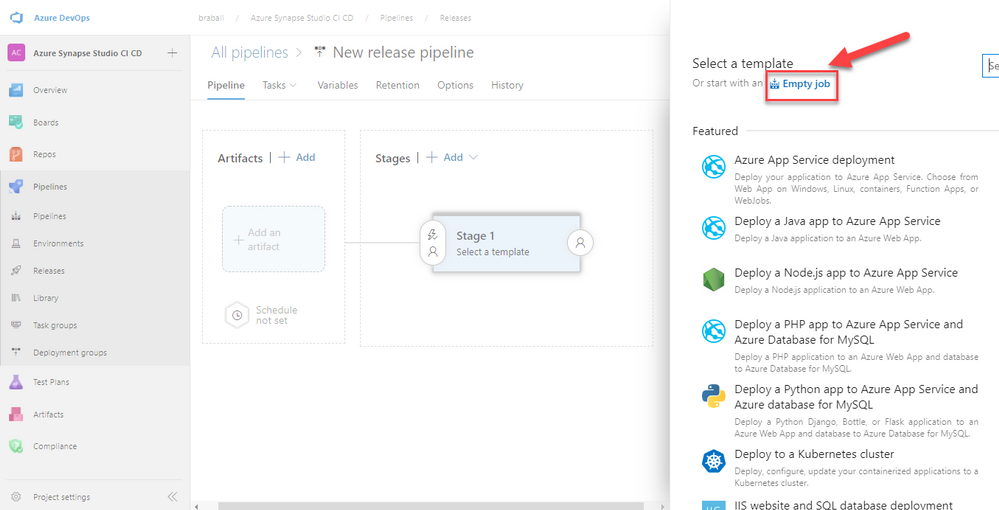
Ensure our project is selected. Select the name of the Build Pipeline that we created in our previous blog (Or whatever YOU wanted to name your Build Pipeline because my naming conventions do not define you!). Select the Latest Build, and click Add.
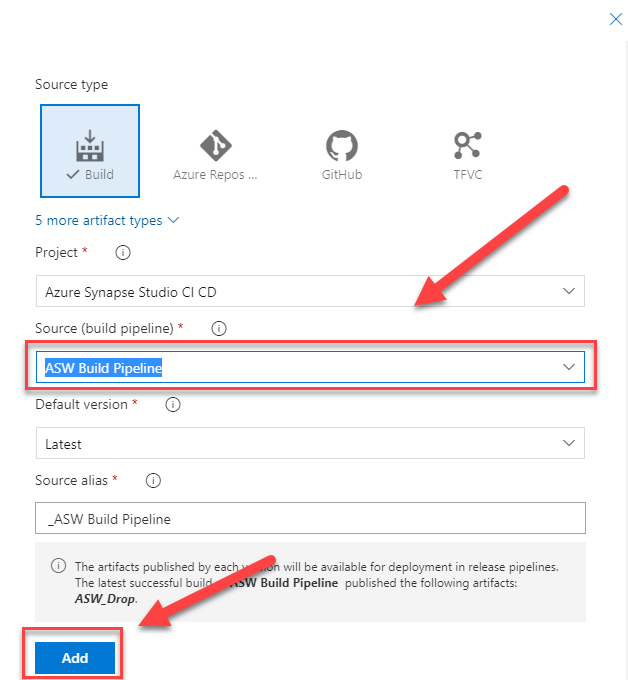
Rename the Release Pipeline to reflect what we are doing. We selected Deploy Dev Release. Clock on the Stage1 link 1 job, 0 task
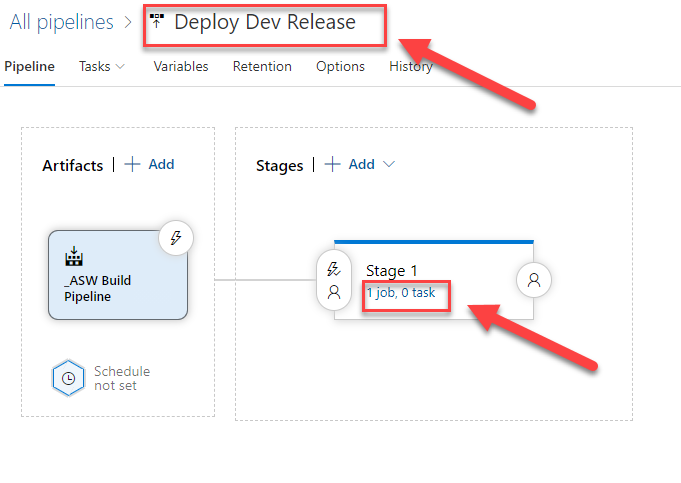
Click the + plus sign on Agent Job. In the search text box type “Synapse”, the Synapse workspace deployment task will appear if you have installed it from the Marketplace. If not, FEAR NOT! You should see a link for it below under the heading Marketplace. Click on it to install the task to your Azure DevOps project.
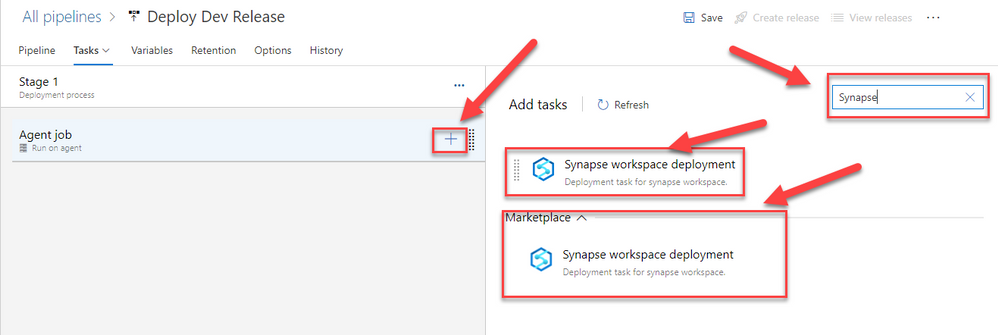
Once you have added the task, click on the task. We will fill out the Template, Template parameters, Synapse Workspace connection type, Synapse Workspace name, and we will get to OverrideArmParameters in a moment. That will a lot more details.
First click on the … ellipses by Template.
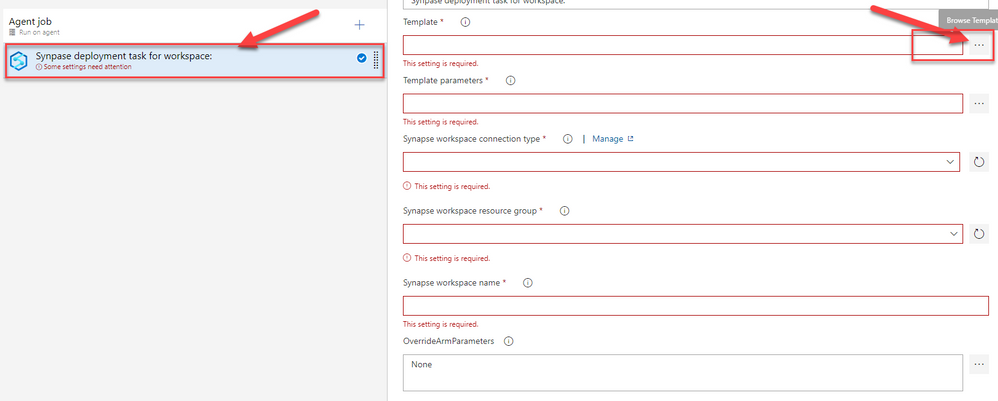
Navigate through the build pipeline, ASW_Drop, ARM, to the TemplateForWorkspace.json. Select the .json file and click OK.
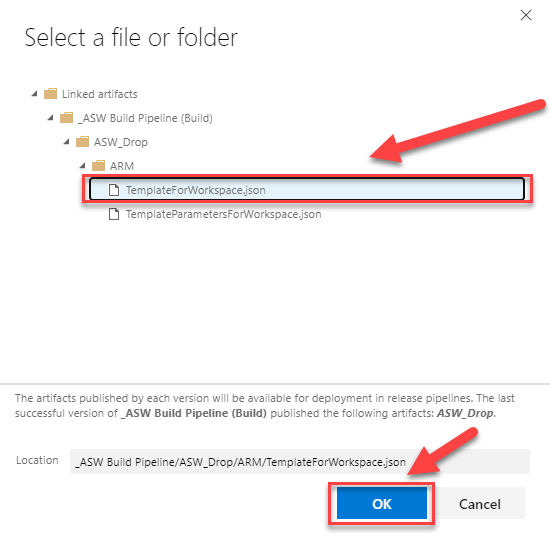
Now repeat the same steps for the Template Parameters text box, this time selecting the TemplateParametersForWorkspace.json file.
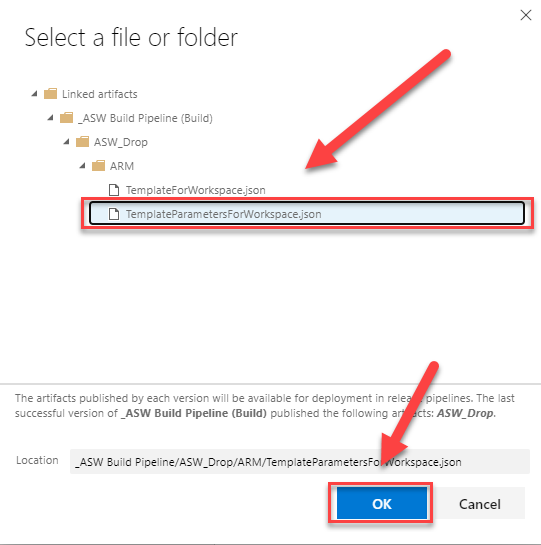
Under Synapse workspace connection type, select the Azure Subscription that contains the environment where we are deploying our release. Specify the Resource Group and the Azure Synapse Workspace name.
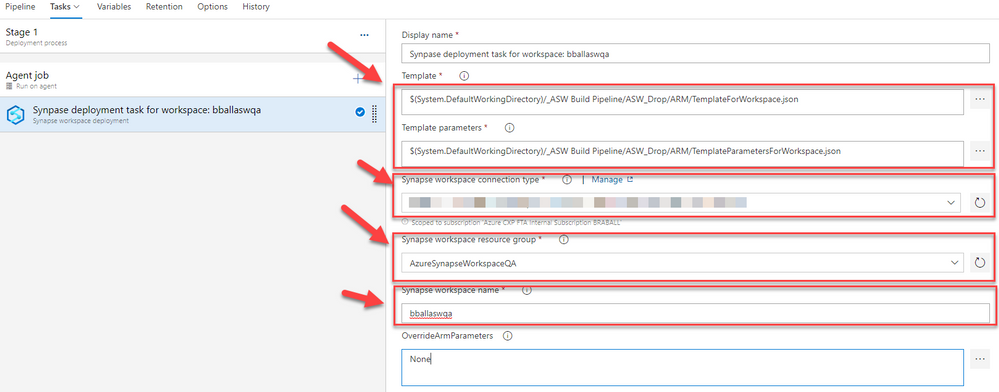
Now we begin to focus on the override parameters. First we will travel back to our Repo and look at the TemplateForWorkspace.json. Any string that has a type “secureString” will need to have an override parameter. Depending on the level of development you have done, you may have many of these strings, in our example we have two. The default workspace connection to the Provisioned SQL Pools and a Linked Service I created to an Azure SQL Database.
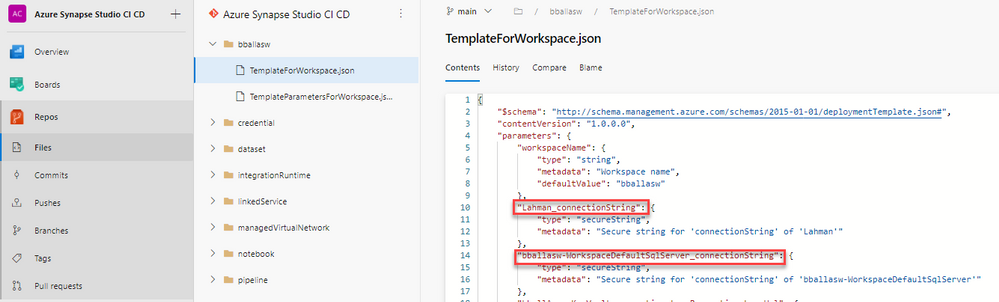
Dear Reader, you are wondering where to find those. You are in luck! Navigate to your Azure Synapse Analytics Workspace, click on the Manage blade, then Linked services. Now click on the { } Code symbol after the name of the linked service that is a type securedString.
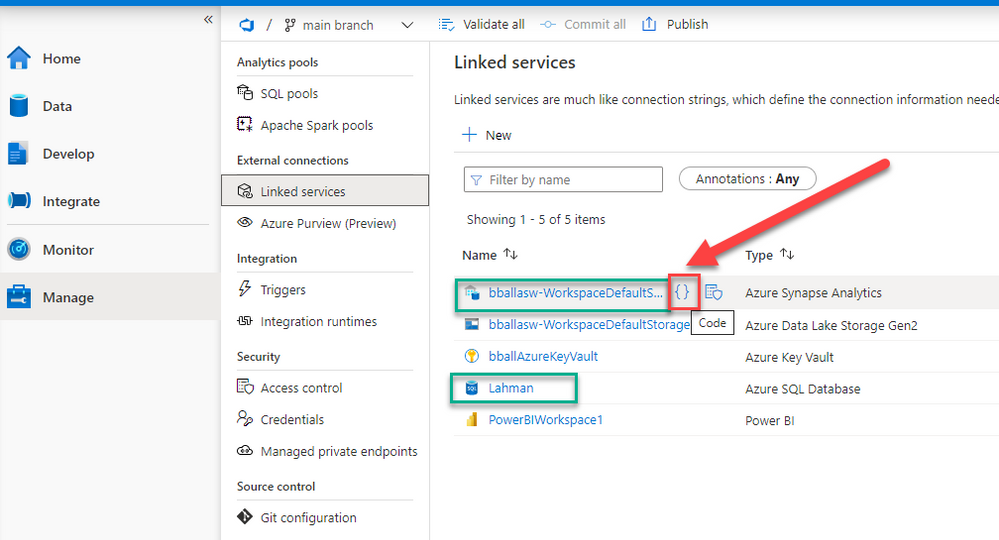
This will open a view of the JSON in that contains the data we need. Copy the text between the double quotes. DO NOT SELECT THE DOUBLE QUOTES!! JUST THE STRING BETWEEN THE DOUBLE QOUTES!
Sorry for yelling, but we will use this string soon and the double quotes “” will cause it to fail.
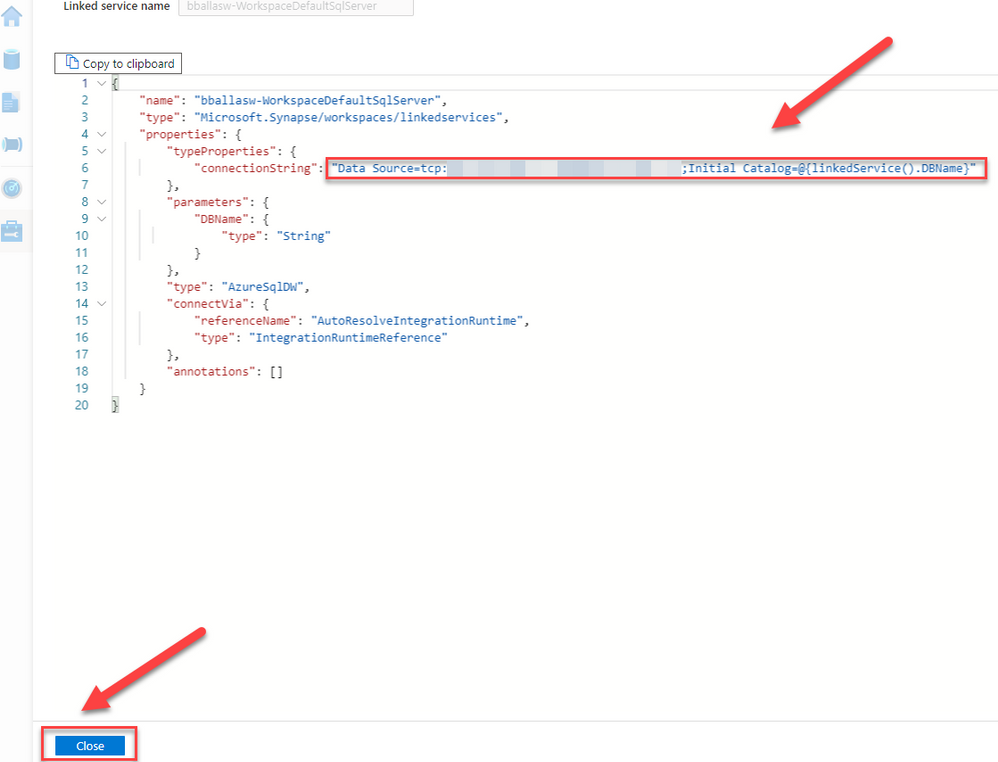
Now let’s do the same thing for the Azure SQL Database.
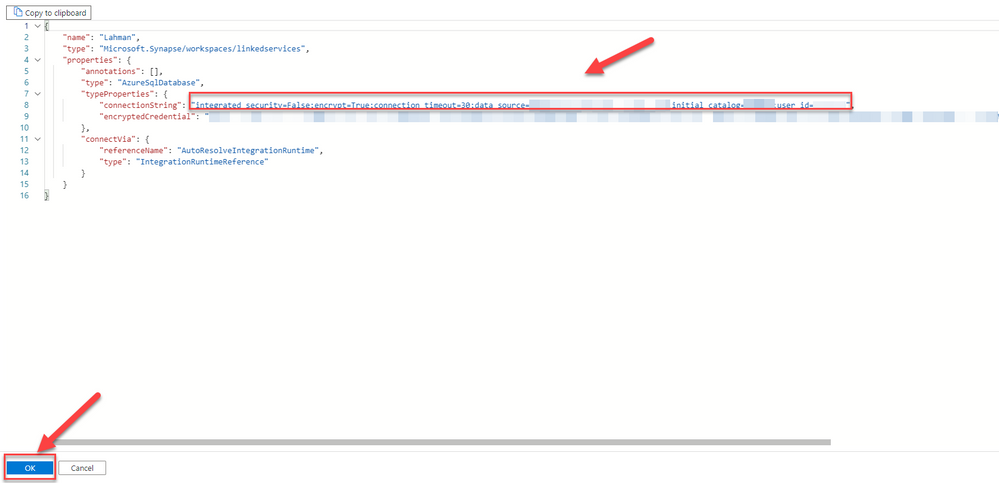
Now navigate back to our Azure DevOps Release pipeline. Click on Variables, then click the + Add button 3 times. We will be creating two variables based on the secureStrings in our JSON file. We will also be creating a system.debug value to give us extra information in our release pipeline, it’s value is True.
After you copy in the secureStrings, click the lock button by the two connection strings, leave system.debug unencrypted.
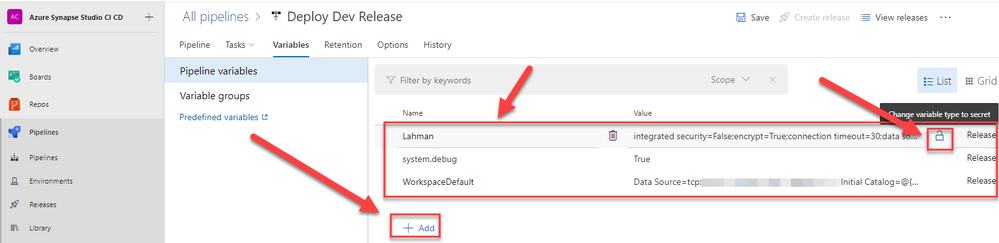
Your pipeline should look similar to this.
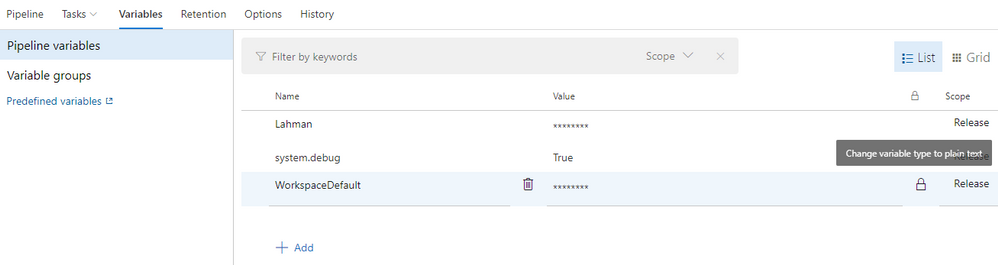
Now we will go to the OverrideArmParameters text area. We will use the following syntax -variableNameFromTheJsonFile $(devOpsPipelineVarriable)
For example:
-bballasw-WorkspaceDefaultSqlServer_connectionString $(WorkspaceDefault) -Lahman_connectionString $(Lahman)
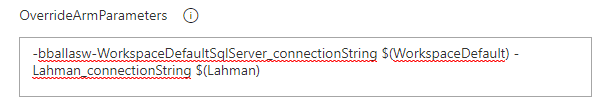
Yours may vary based your number of secureStrings and names. Now let’s click Save on our pipeline.
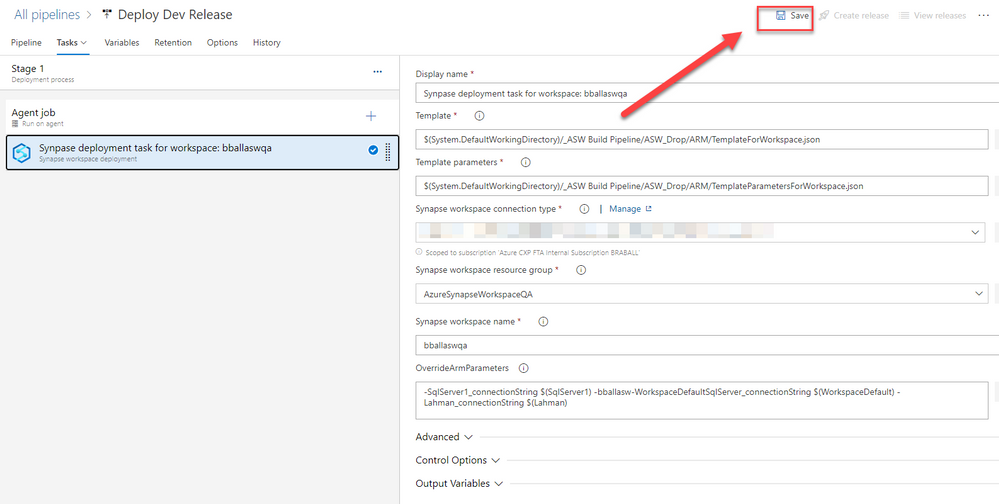
Make a comment and click OK
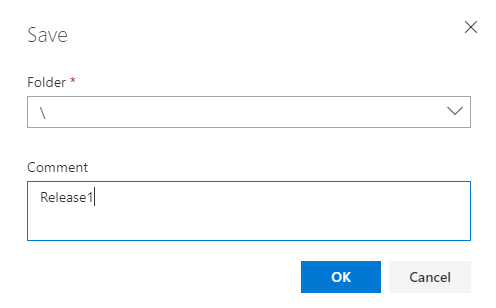
Now click Create release.
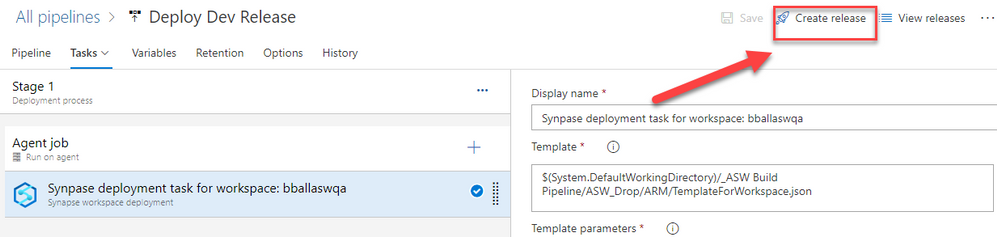
Click Create
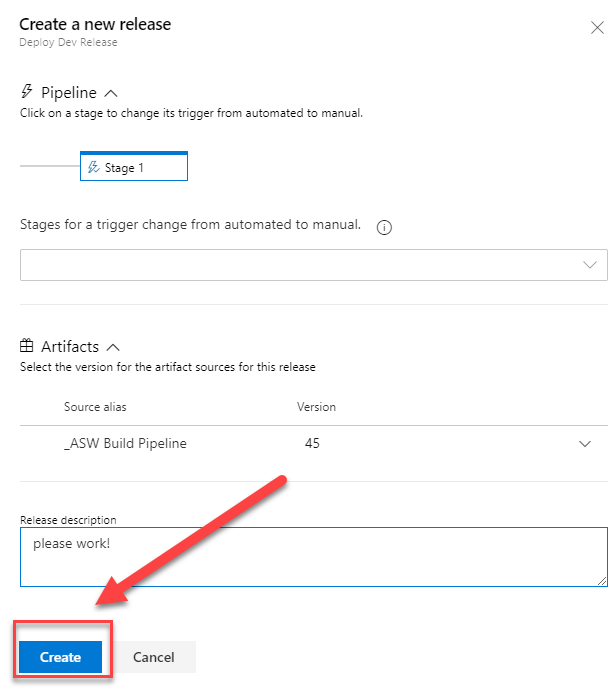
Click Release-1 (or whatever your release number is).
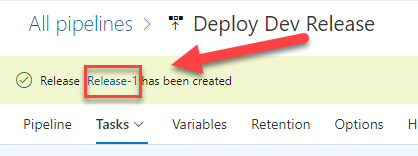
After your Agent begins to process click on Logs and watch it run!
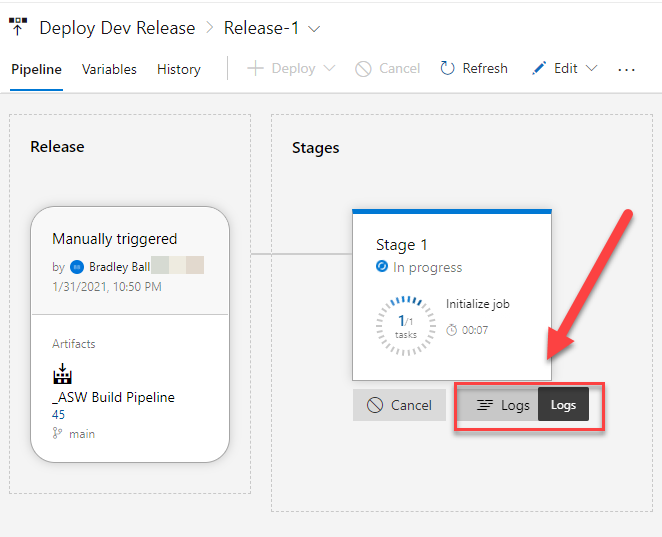
AND NOW!!!!! ……it failed.
A few times. But hey, it’s not developing if there isn’t a failure. So it’s almost 1 am, and I *believe* I have it running so let me take this time to walk you through what I’ve found.
Spark Pools and Self Hosted Integration Runtimes are not created in a pipeline. If you have a Linked Service that uses a Self Hosted Integration Runtime you will need to manually create that in your QA or Prod environment prior to deployment.
If you are developing Notebooks and have them connected to a Spark Pool, you will need to recreate that Spark Pool in QA or Production. Notebooks that are linked to a Spark Pool that does not exist in an environment will fail to deploy.
Name them the same thing. Do not change names. Trust me.
If you are doing a deployment and your Provisioned SQL Pools are Paused then the deployment will fail. *More to come on database migrations, a database project build, and release is still needed.
Here’s a quick image.
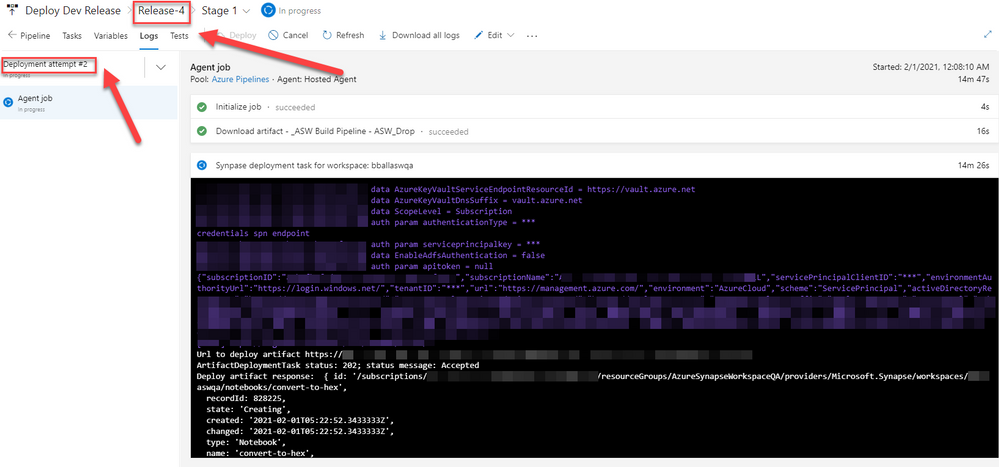
I’m on release 4, attempt 2. This appears to be running just fine for me.
VICTORY!!
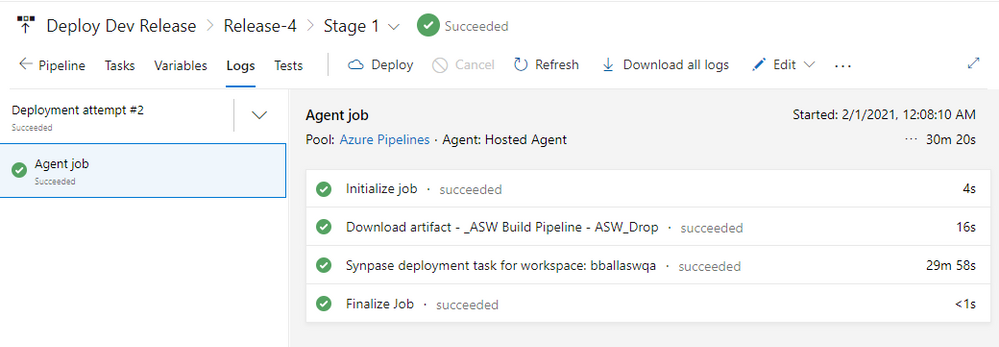
Now let us go and check our QA Workspace! First up Scripts and Notebooks.
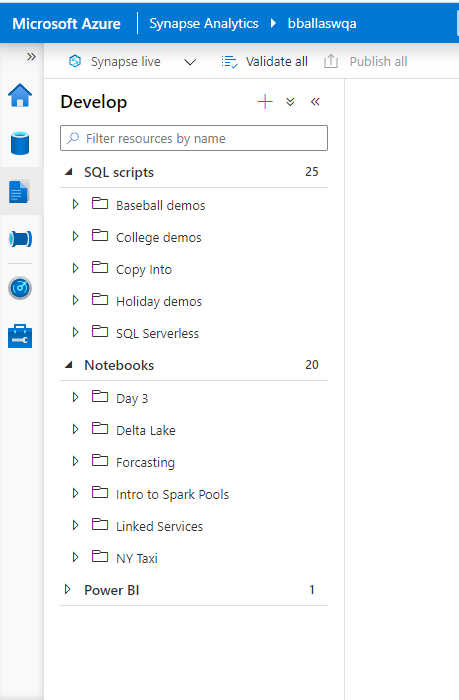
Excellent! Everything is there. Next let us look at our Provisioned SQL Pools.
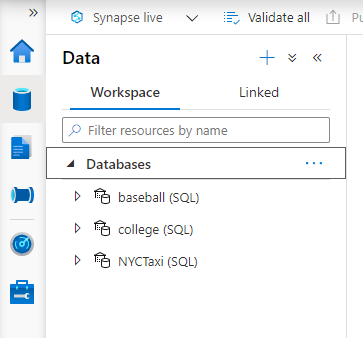
Looks great! As a quick side note the databases will be brought over at DW100c, so you can auto scale them as needed. Also if you are in a demo environment like me, be sure to pause them after the deployment completes. Next up Pipelines.
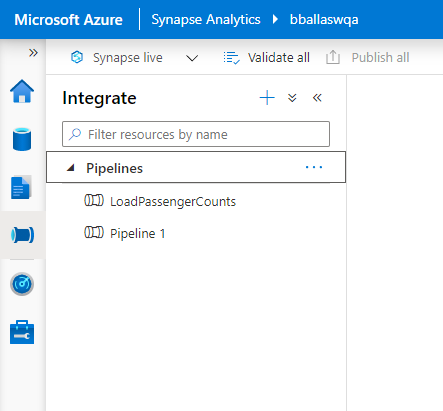
I like this! Now let’s check out linked services.
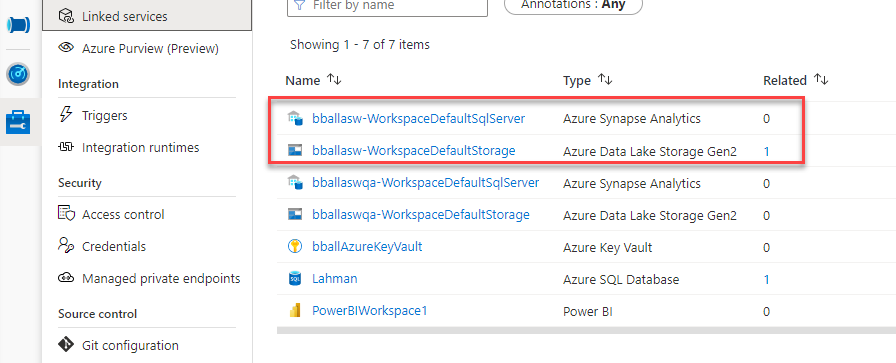
I don’t like this. Here are my Dev links for my default workspace in my QA environment. Right now the only way I’ve found to clean this up is to use the Az.Synapse PowerShell Module. Navigate back to your release pipeline. Edit it, add an Azure PowerShell task. We will then use this script:
##Required for azure devops initial deployment
Install-Module Az.Synapse -RequiredVersion 0.2.0 -Scope CurrentUser -Force
#get rid of dev linked service in QA
Remove-AzSynapseLinkedService -WorkspaceName yourworkspaceName -Name linkedservicetoRemove
Remove-AzSynapseLinkedService -WorkspaceName yourworkspaceName -Name linkedservicetoRemove
Under Azure PowerShell version options select Specify other version, set Preferred Azure PowerShell Version 3.1.0.
The next time you run your deployment, this should clean up those links.
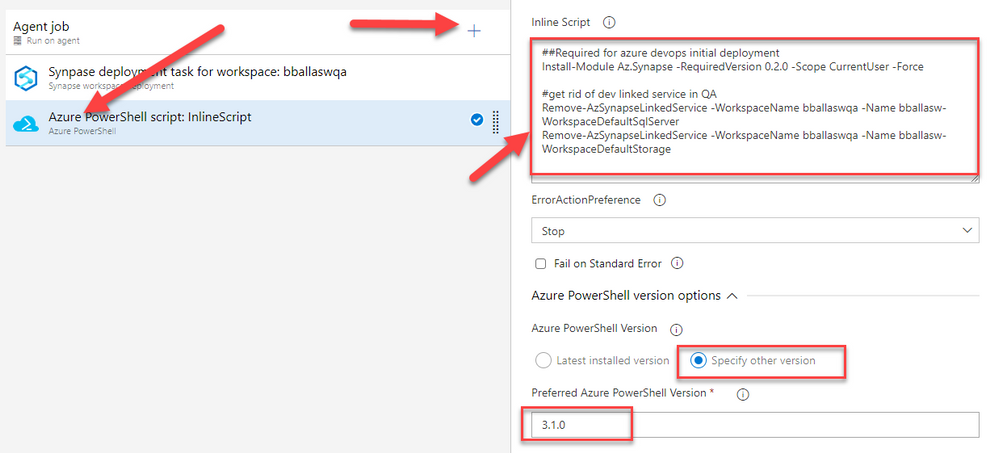
All right Dear Reader, I’m off to sleep. Happy Monday and as always, thank you for stopping by.
Thanks,
Brad
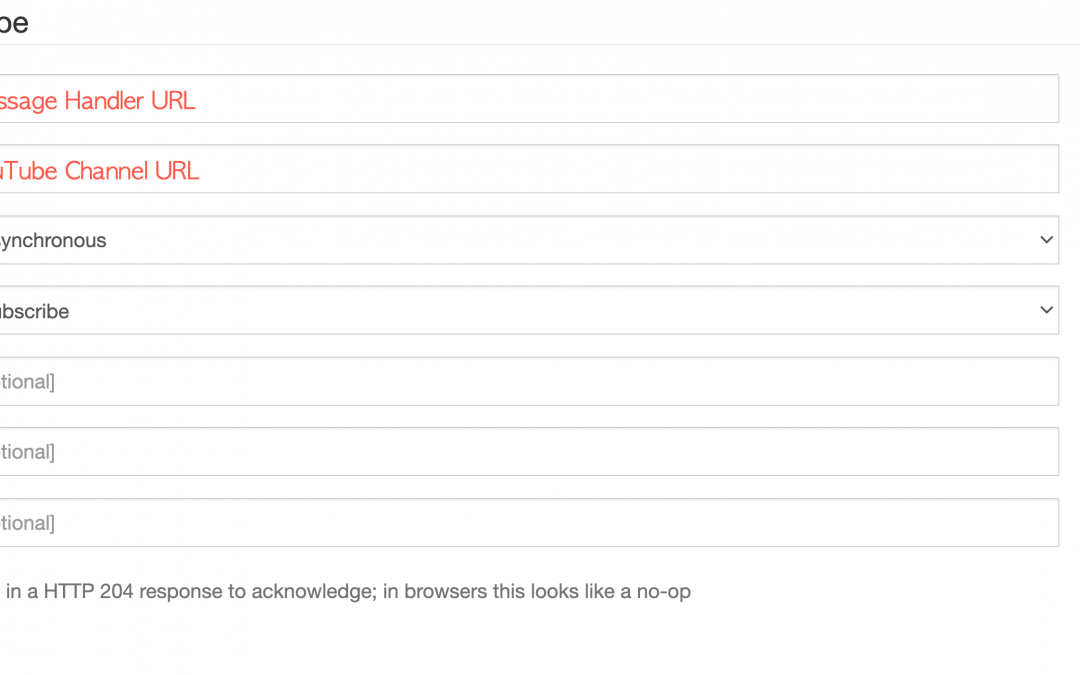
by Contributed | Jan 31, 2021 | Technology
This article is contributed. See the original author and article here.
Let’s say you’ve got a YouTube channel uploading videos in a regular cadence. When a new video is published, you want to cross-post it to other social media channels that you’re running. What could be the best way to do so? There are hundreds of commercial tools on the market for online content marketing. There are hundreds of companies to help you, and those companies have their proprietary solutions for it. It could make sense to utilise those tools or companies. However, with various reasons or circumstances, what if you need to build your own one? What if the existing tools don’t fulfil your requirements? Then, it’s a good time to build the solution by yourself, isn’t it?
This post will discuss an end-to-end workflow story, from YouTube video update to other social media exposure. For the workflow, let’s use Azure serverless services like Azure EventGrid, Azure Functions and Azure Logic Apps.
If you like to see the source codes of the solution, find this GitHub repository. It’s completely open-source, and you can use it under your discretion with care.
Subscribing YouTube Notification Feed
YouTube uses a protocol called PubSubHubbub for its notification mechanism. It’s now become a web standard called WebSub since 2018, after the first working draft in 2016.
Google registers all YouTube channels to their WebSub Hub. Therefore, if you want to get the update notification from a specific channel, you can simply send a subscription request to the Hub. To subscribe, enter the message handler URL and YouTUbe channel URL and click the Do It! button. Too easy!
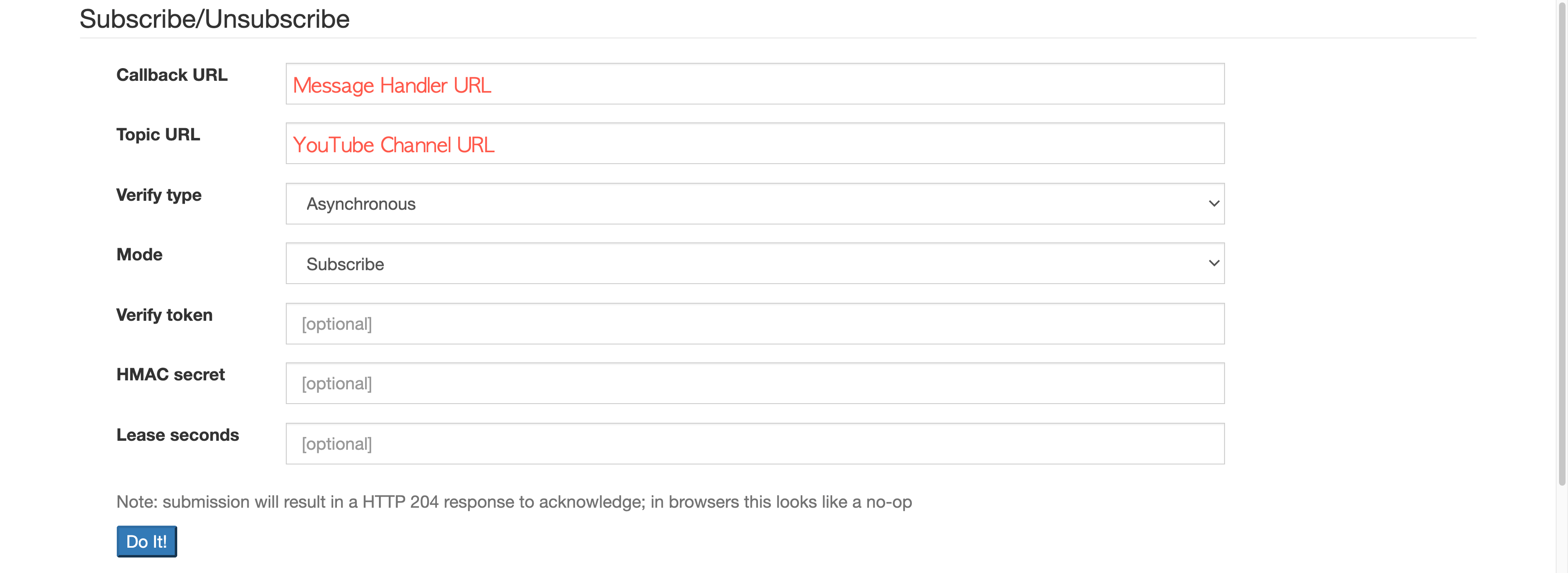
Please ensure that the subscription process is completed only after passing the message handler verification request.
Verifying WebSub Subscription Request
To verify the WebSub subscription request, the WebSub Hub sends an API call to the message handler. When it arrives, the handler MUST deal with the following.
- The verification request sends a
GET request with the following query parameters:
hub.mode: The subscribe string.
hub.topic: The YouTube channel URL.
hub.challenge: A random string generated by the WebSub Hub, used for the verification.
hub.lease_seconds: The validation period in seconds from the time of the request. The request will be void unless the request is not verified within this period.
- The response of the verification request MUST include the
hub.challenge value to the response body, with the HTTP status code of 200:
- If the response body includes anything other than the
hub.challenge value, the WebSub Hub won’t accept it as the valid response.
Here’s the verification request handling logic in the Azure Function method:
[FunctionName(“CallbackAsync”)]
public async Task CallbackAsync(
[HttpTrigger(AuthorizationLevel.Function, “GET”, “POST”, Route = “callback”)] HttpRequest req,
ILogger log)
{
if (HttpMethods.IsGet(req.Method))
{
string challenge = req.Query[“hub.challenge”];
var result = new ObjectResult(challenge) { StatusCode = 200 };
return result;
}
Once the message handler is verified, the WebSub Hub keeps sending the notification message to the handler whenever a new video update is made, from the subscribed channel.
Converting WebSub Notification Feed
As the mechanism of WebSub follows the same Publisher/Subscriber (Pub/Sub) pattern, it’s not that new. The only difference of WebSub is the event data that makes use of the existing ATOM feed format. Therefore, as long as any subscriber understands the feed format, it should be OK. In other words, the subscriber has a strong dependency on the event data format the publisher sends. In the modern application environments, we recommend decoupling between the publisher and subscriber as much as we can, so that each can organically grow independently. In other words, the subscriber don’t have to know the ATOM feed format. How can we make them decoupled, then? The event data format or message format needs to be canonicalised. Then, converting the canonical data into the subscriber-specific format should be done by the subscriber’s end.
Therefore, we are going to use CloudEvents as the canonical data format. There are two steps for the conversion–1) canonicalisation and 2) domain-specific conversion. Let’s have a look.
1. Canonicalisation: WebSub Feed :right_arrow: CloudEvents
The purpose of this step is to decouple between WebSub Hub and your application. The XML data delivered from the WebSub Hub is just wrapped with the CloudEvents format. When a new video is updated onto YouTube, it sends a notification to the WebSub Hub, which looks like the following:
<feed xmlns:yt=”http://www.youtube.com/xml/schemas/2015″ xmlns=”http://www.w3.org/2005/Atom”>
<link rel=”hub” href=”https://pubsubhubbub.appspot.com”/>
<link rel=”self” href=”https://www.youtube.com/xml/feeds/videos.xml?channel_id=[channel_id]”/>
<title>YouTube video feed</title>
<updated>2021-01-27T07:00:00.123456789+00:00</updated>
<entry>
<id>yt:video:[video_id]</id>
<yt:videoId>[video_id]</yt:videoId>
<yt:channelId>[channel_id]</yt:channelId>
<title>hello world</title>
<link rel=”alternate” href=”http://www.youtube.com/watch?v=<video_id>”/>
<author>
<name>My Channel</name>
<uri>http://www.youtube.com/channel/[channel_id]</uri>
</author>
<published>2021-01-27T07:00:00+00:00</published>
<updated>2021-01-27T07:00:00.123456789+00:00</updated>
</entry>
</feed>
As the message handler takes this request through POST, it is stringified like this:
var payload = default(string);
using (var reader = new StreamReader(req.Body))
{
payload = await reader.ReadToEndAsync().ConfigureAwait(false);
}
The request header also contains the following Link information:
Link: <https://pubsubhubbub.appspot.com>; rel=hub, <https://www.youtube.com/xml/feeds/videos.xml?channel_id=[channel_id]>; rel=self
As it includes the YouTube channel URL as the message source, you need to extract it.
var headers = req.Headers.ToDictionary(p => p.Key, p => string.Join(“|”, p.Value));
var links = headers[“Link”]
.Split(new[] { “,” }, StringSplitOptions.RemoveEmptyEntries)
.Select(p => p.Trim().Split(new[] { “;” }, StringSplitOptions.RemoveEmptyEntries))
.ToDictionary(p => p.Last().Trim(), p => p.First().Trim().Replace(“<“, string.Empty).Replace(“>”, string.Empty));
var source = links[“rel=self”];
Then, set the event type and content type like the following.
var type = “com.youtube.video.published”;
var contentType = “application/cloudevents+json”;
As I mentioned in my previous post, at the time of this writing, the Azure EventGrid Binding for Azure Function currently has a limitation to support the CloudEvents format. Therefore, you should handle it manually:
var @event = new CloudEvent(source, type, payload, contentType);
var events = new List<CloudEvent>() { @event };
var topicEndpoint = new Uri(“https://<eventgrid_name>.<location>-<random_number>.eventgrid.azure.net/api/events”);
var credential = new AzureKeyCredential(“eventgrid_topic_access_key”);
var publisher = new EventGridPublisherClient(topicEndpoint, credential);
var response = await publisher.SendEventsAsync(events).ConfigureAwait(false);
return new StatusCodeResult(response.Status);
}
So far, the WebSub data is canonicalised with the CloudEvents format and sent to EventGrid. The canonicalised information looks like this:
{
“id”: “c2e9b2d1-802c-429d-b772-046230a9261e”,
“source”: “https://www.youtube.com/xml/feeds/videos.xml?channel_id=<channel_id>”,
“data”: “<websub_xml_data>”,
“type”: “com.youtube.video.published”,
“time”: “2021-01-27T07:00:00.123456Z”,
“specversion”: “1.0”,
“datacontenttype”: “application/cloudevents+json”,
“traceparent”: “00-37d33dfa0d909047b8215349776d7268-809f0432fbdfd94b-00”
}
Now, you have cut the dependency on the WebSub Hub.
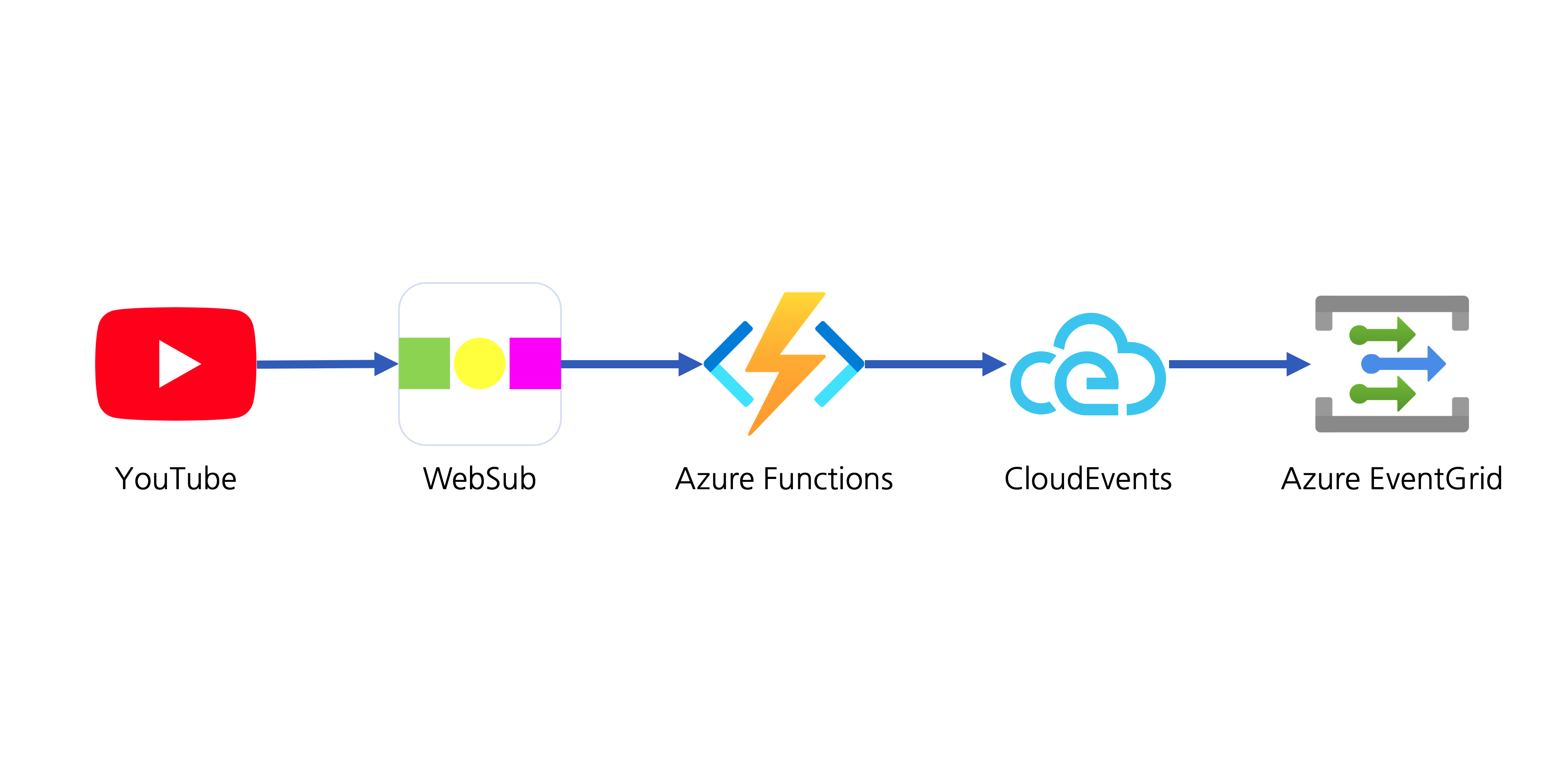
Let’s move onto the next step.
2. Domain-Specific Conversion: WebSub XML Data Manipulation
At this step, the XML data is actually converted into the format we’re going to use for social media amplification.
The WebSub XML data only contains bare minimum information like the video ID and channel ID. Therefore, you need to call a YouTube API to get more details for social media amplification. An event handler should be registered to handle the published event data on Azure EventGrid. Like the WebSub subscription process, it also requires delivery authentication. One of the good things using Azure Logic Apps as the event handler is that it automatically does all the verification process internally. Therefore, you just use the Logic App to handle the event data.
The Logic App handler’s first action is to verify whether the event data is what you are looking for–it should meet your channel ID and event type of com.youtube.video.published. If either channel ID or the event type is different, this handler stops processing.
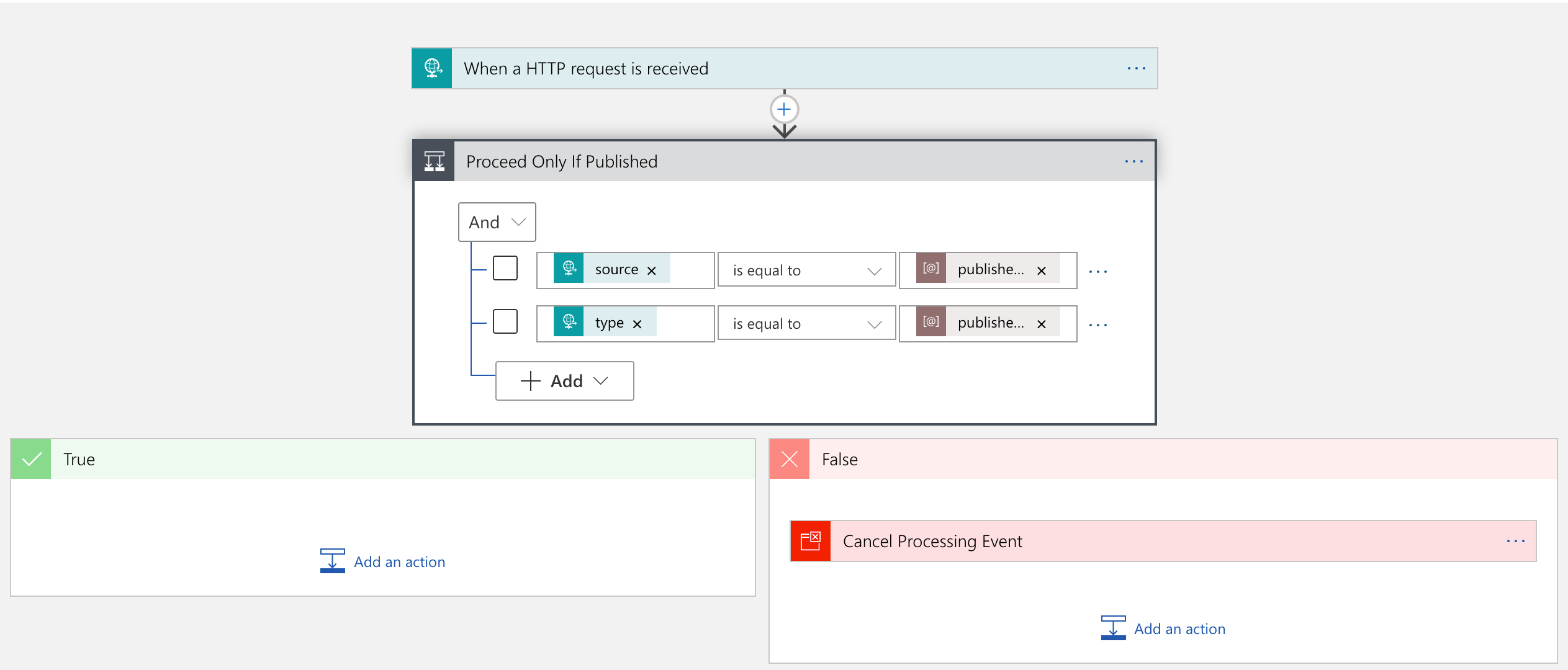
If the event data is what you are looking for, the handler passes it to Azure Functions for further manipulation.
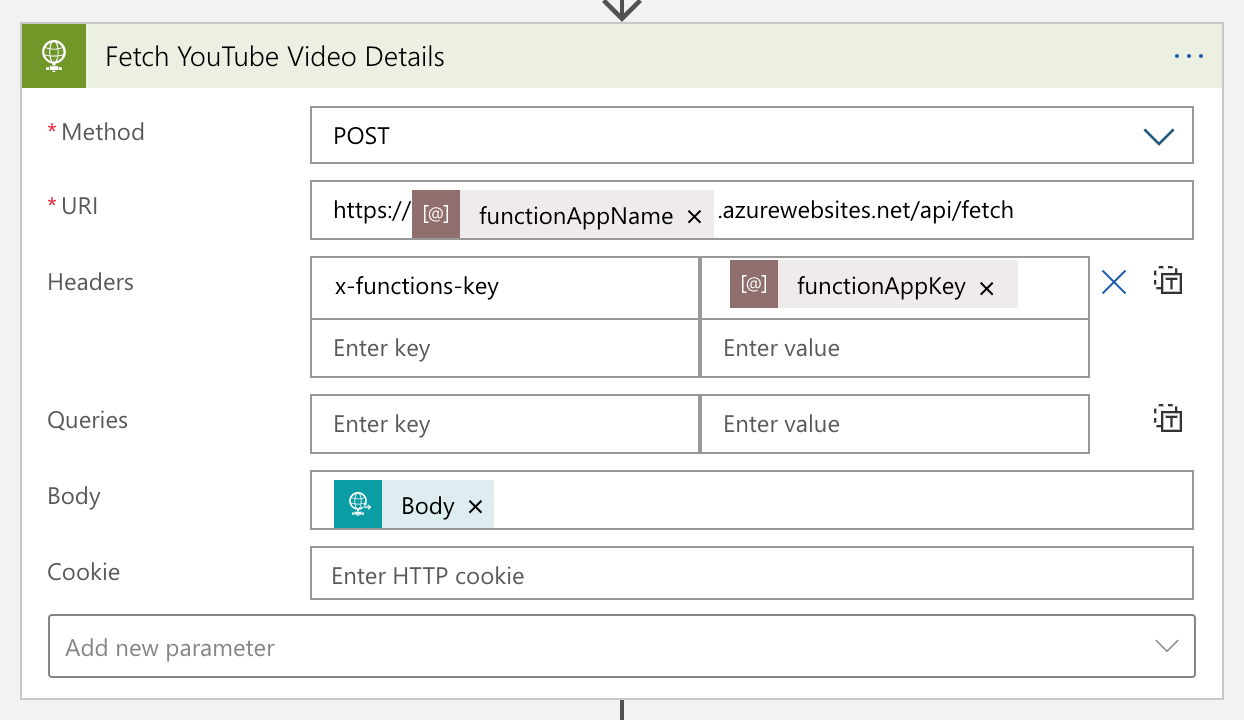
The Azure Functions app calls the YouTube API to get more details of the video, manipulates them, and turns it back to Logic App. The converted data looks like:
{
“channelId”: “<channel_id>”,
“videoId”: “<video_id>”,
“title”: “hello world”,
“description”: “Lorem ipsum dolor sit amet, consectetur adipiscing elit. Duis malesuada.”,
“link”: “https://www.youtube.com/watch?v=<video_id>”,
“thumbnailLink”: “https://i.ytimg.com/vi/<video_id>/maxresdefault.jpg”,
“datePublished”: “2021-01-27T07:00:00+00:00”,
“dateUpdated”: “2021-01-27T07:00:00+00:00”
}
YouTube data has been massaged for our purpose.
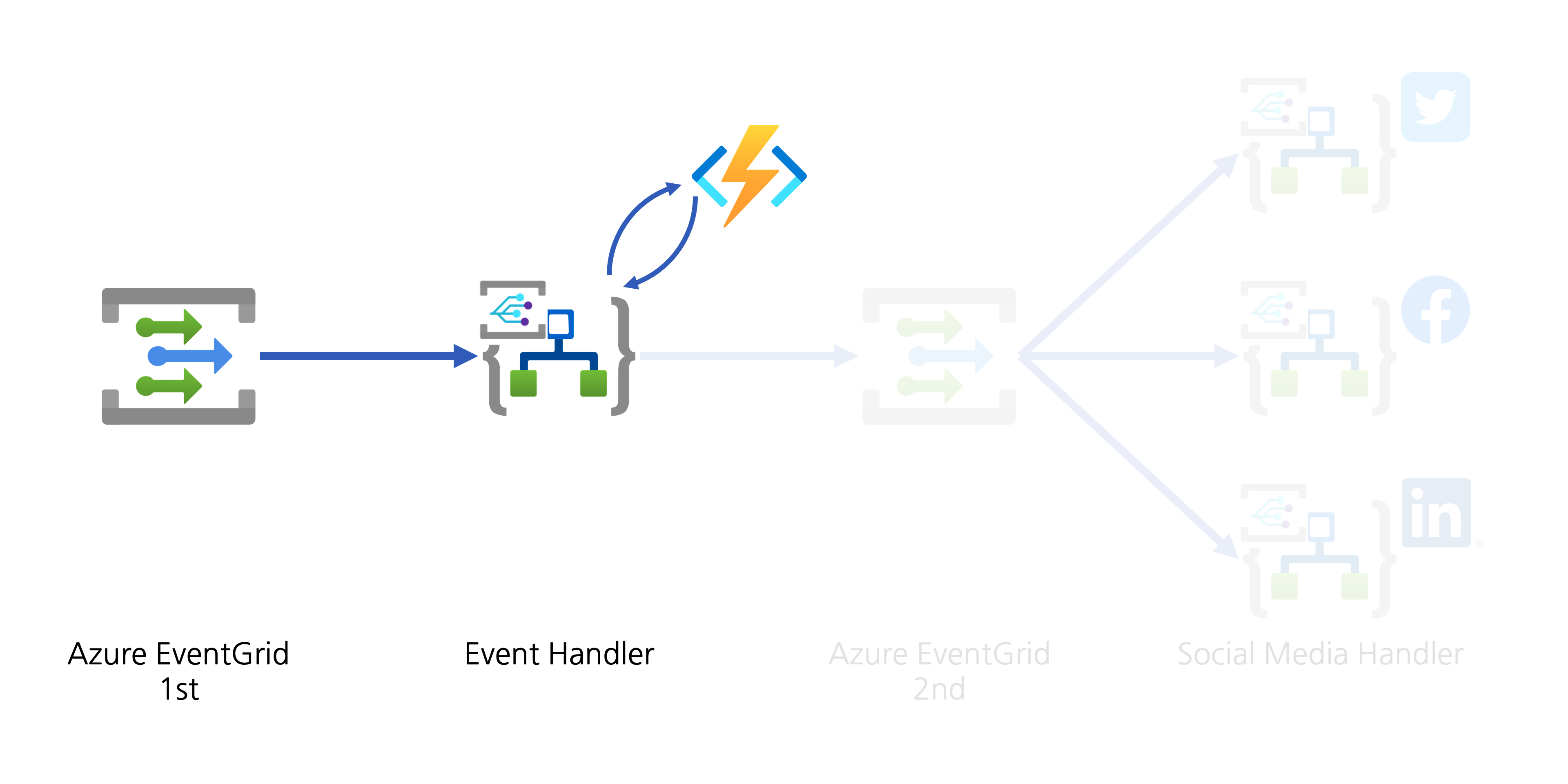
Social Media Exposure
The event handler now needs to help spread the YouTube video update to the world through designated social media. There are two approaches:
- The event handler directly connects to APIs of individual social media, or
- The event handler publishes another event to Azure EventGrid for other event handlers takes care of social media amplification.
Although both approaches are valid, the first one has strong coupling between the handler and amplifiers. If you need to add a new amplifier or remove an existing one, the Logic App handler must be updated, which is less desirable, from the maintenance perspective. On the other hand, The second approach publishes another event containing the converted data. All social media amplifiers act as event handlers, and they are all decoupled. I chose the second one.
1. Event Publish: Converted YouTube Video Details
In order to publish the converted YouTube video details to Azure EventGrid, the data needs to be wrapped with the CloudEvents format. The screenshot shows the action on how to wrap the video details data with CloudEvents. This time, the event type will be com.youtube.video.converted.
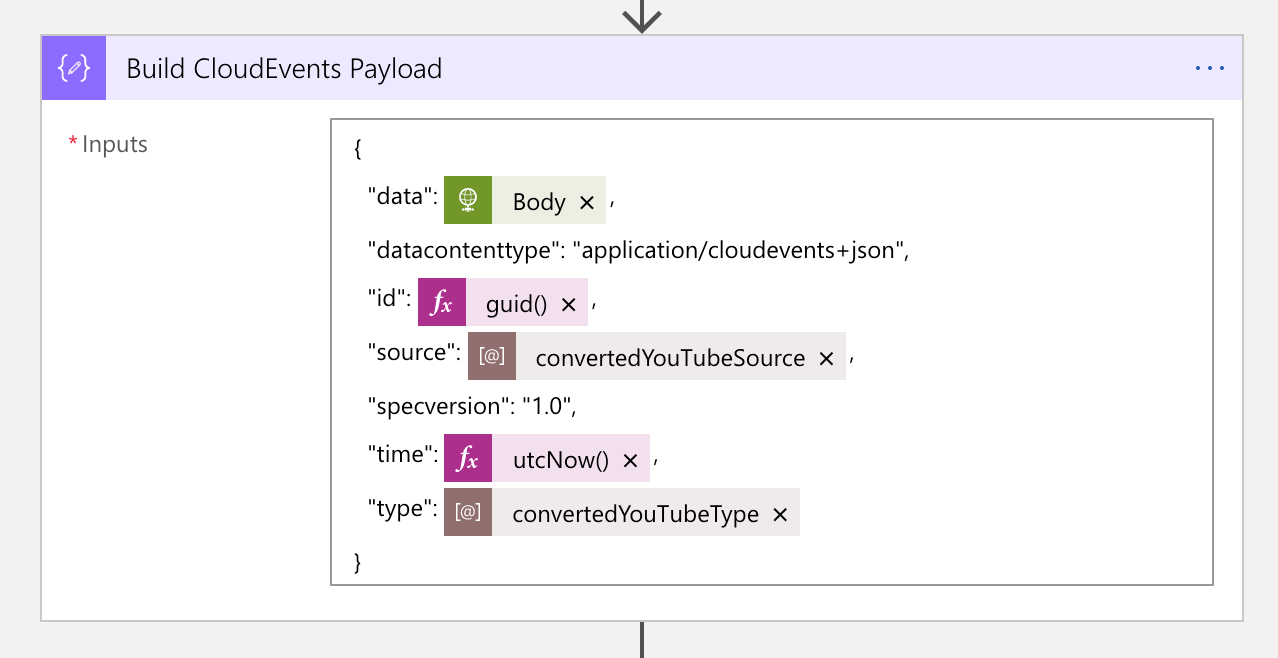
The next action is to send an HTTP request to Azure EventGrid, with the CloudEvents payload. You can notice that many metadata headers are starting with ce-, defined in the cross reference check spec over HTTP.
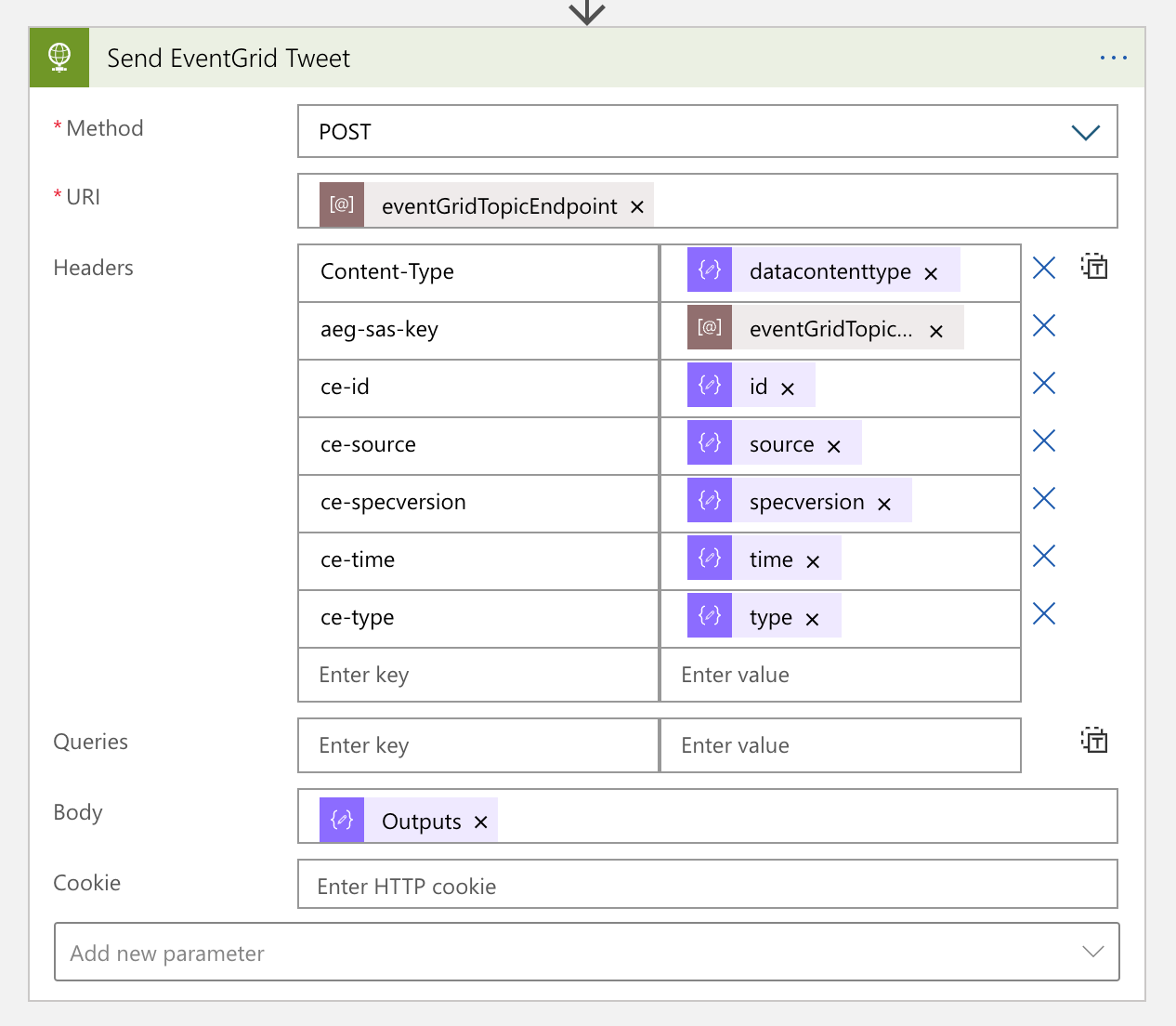
The message handler now completes its workflow. From now on, each social media handler takes care of the new event data.
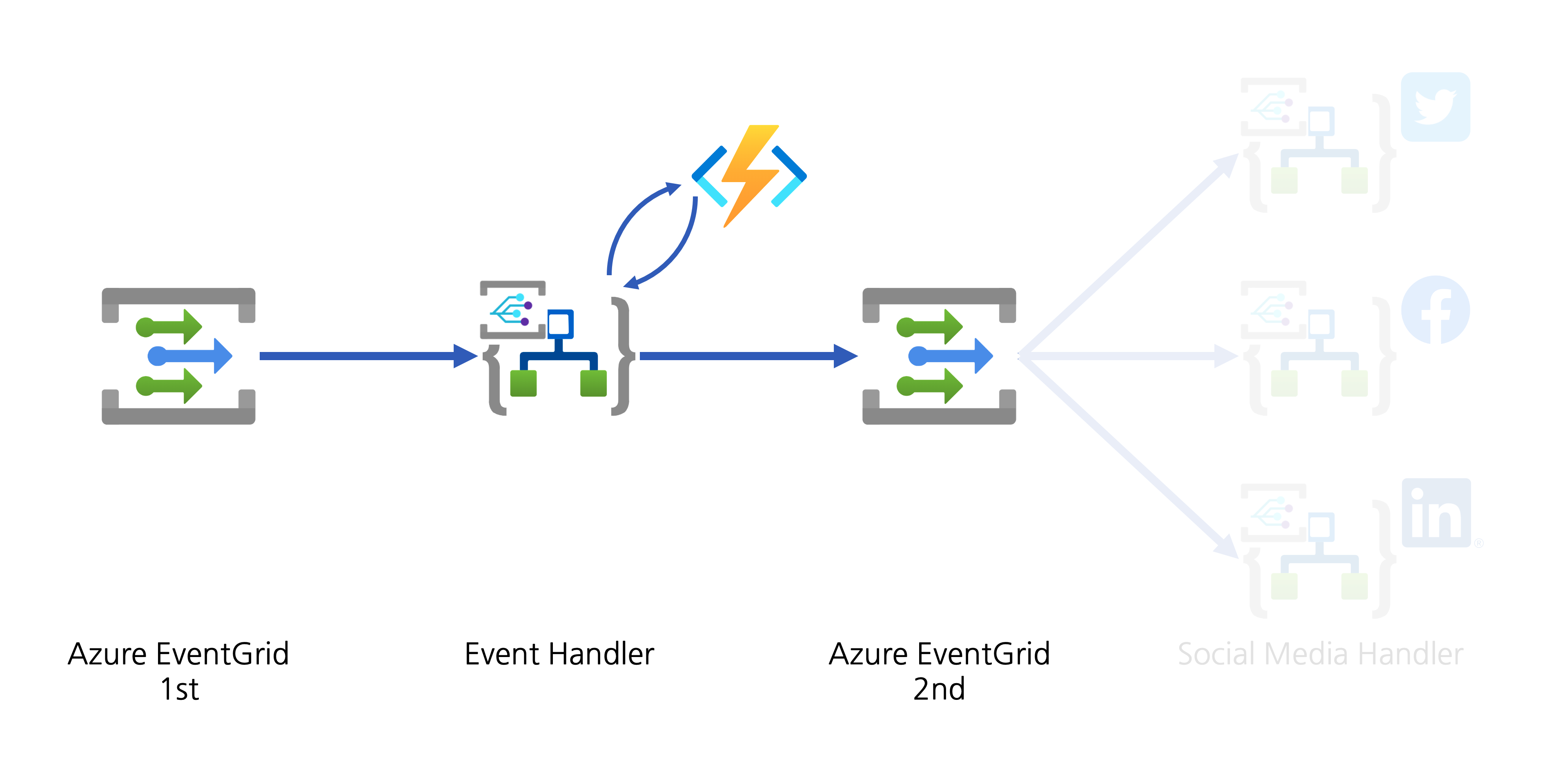
2. Event Handlers: Social Media Amplification
YouTube video details are now ready for amplification! Each social media handler takes care of the event data by adapting their circumstances. The event data received from EventGrid looks like this:
{
“id”: “4cee6312-6584-462f-a8c0-c3d5d0cbfcb1”,
“specversion”: “1.0”,
“source”: “https://www.youtube.com/xml/feeds/videos.xml?channel_id=<channel_id>”,
“type”: “com.youtube.video.converted”,
“time”: “2021-01-16T05:21:23.9068402Z”,
“datacontenttype”: “application/cloudevents+json”,
“data”: {
“channelId”: “<channel_id>”,
“videoId”: “<video_id>”,
“title”: “hello world”,
“description”: “Lorem ipsum dolor sit amet, consectetur adipiscing elit. Duis malesuada.”,
“link”: “https://www.youtube.com/watch?v=<video_id>”,
“thumbnailLink”: “https://i.ytimg.com/vi/<video_id>/maxresdefault.jpg”,
“datePublished”: “2021-01-27T07:00:00+00:00”,
“dateUpdated”: “2021-01-27T07:00:00+00:00”
}
}
Twitter Amplification
As Logic Apps provides the Twitter connector out-of-the-box, you don’t need to use the API by yourselves. Therefore, simply use the actions like below:
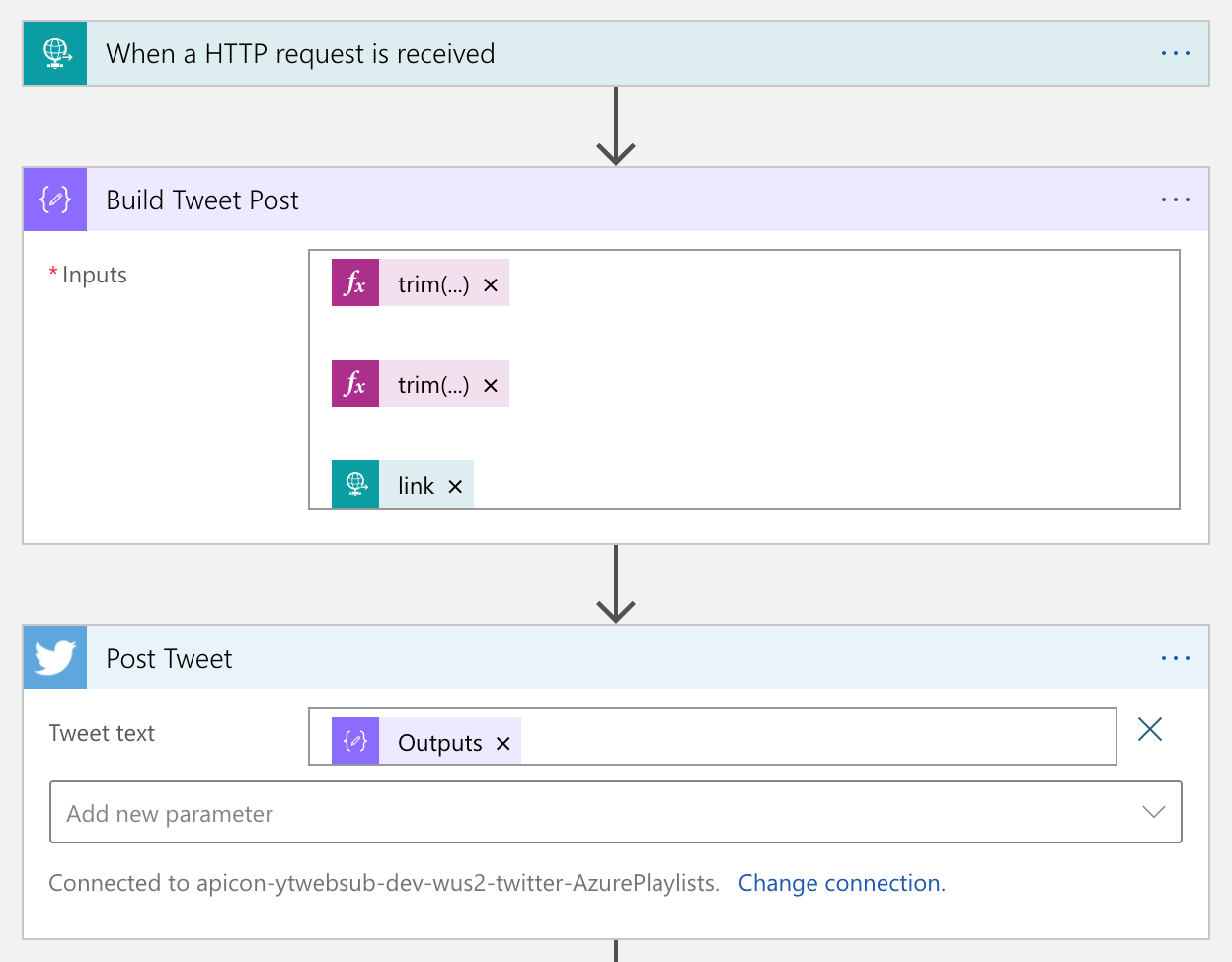
LinkedIn
Logic Apps also provides a built-in LinkedIn connector. So, simply you use it.
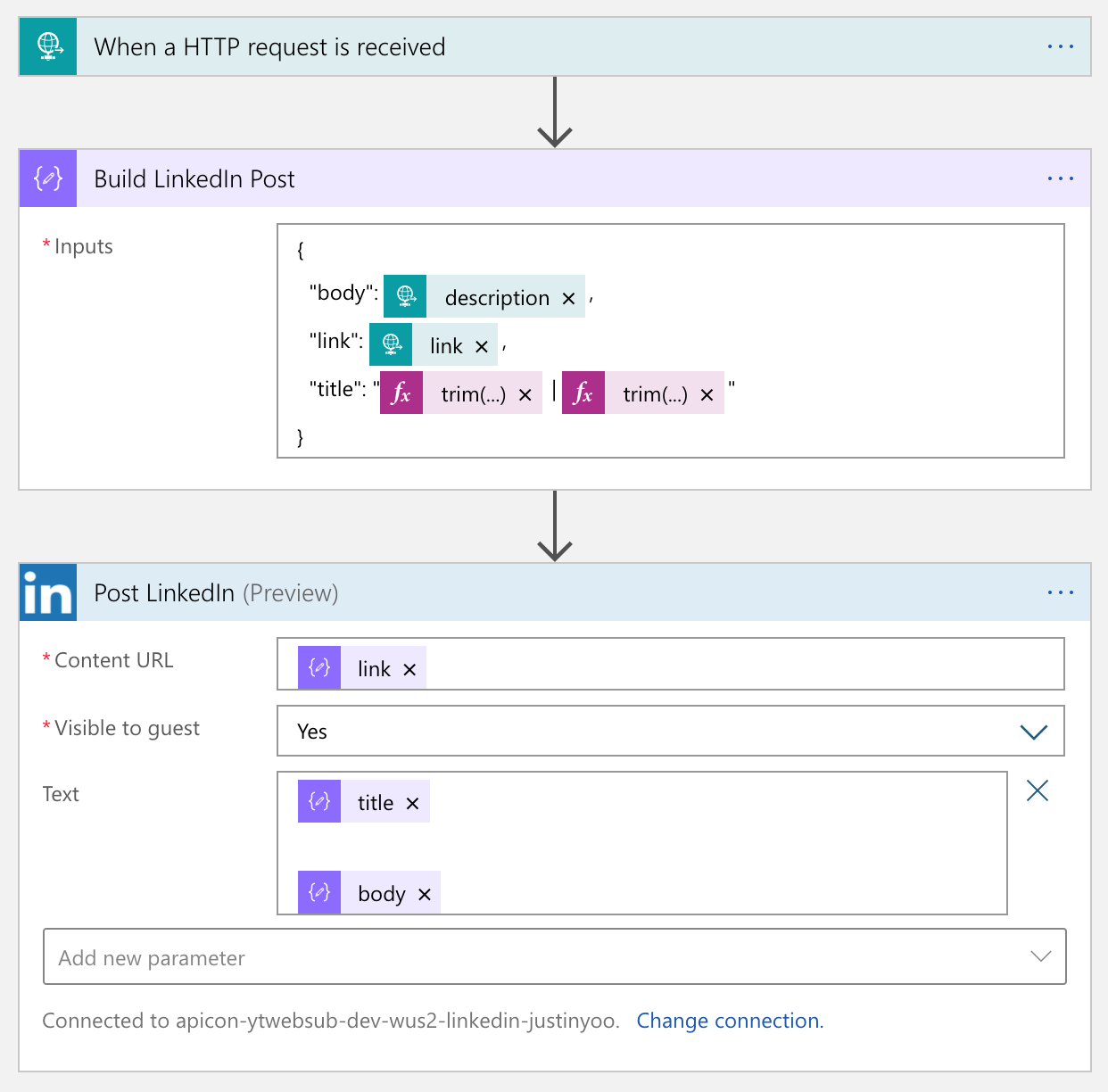
Facebook
Unlike the other two connectors, the Facebook connector has been deprecated. Instead, it’s now become an open-source project. So, you should use this open-sourced custom connector or something else. Fortunately IFTTT provides the Facebook Page connector, so you just use it.
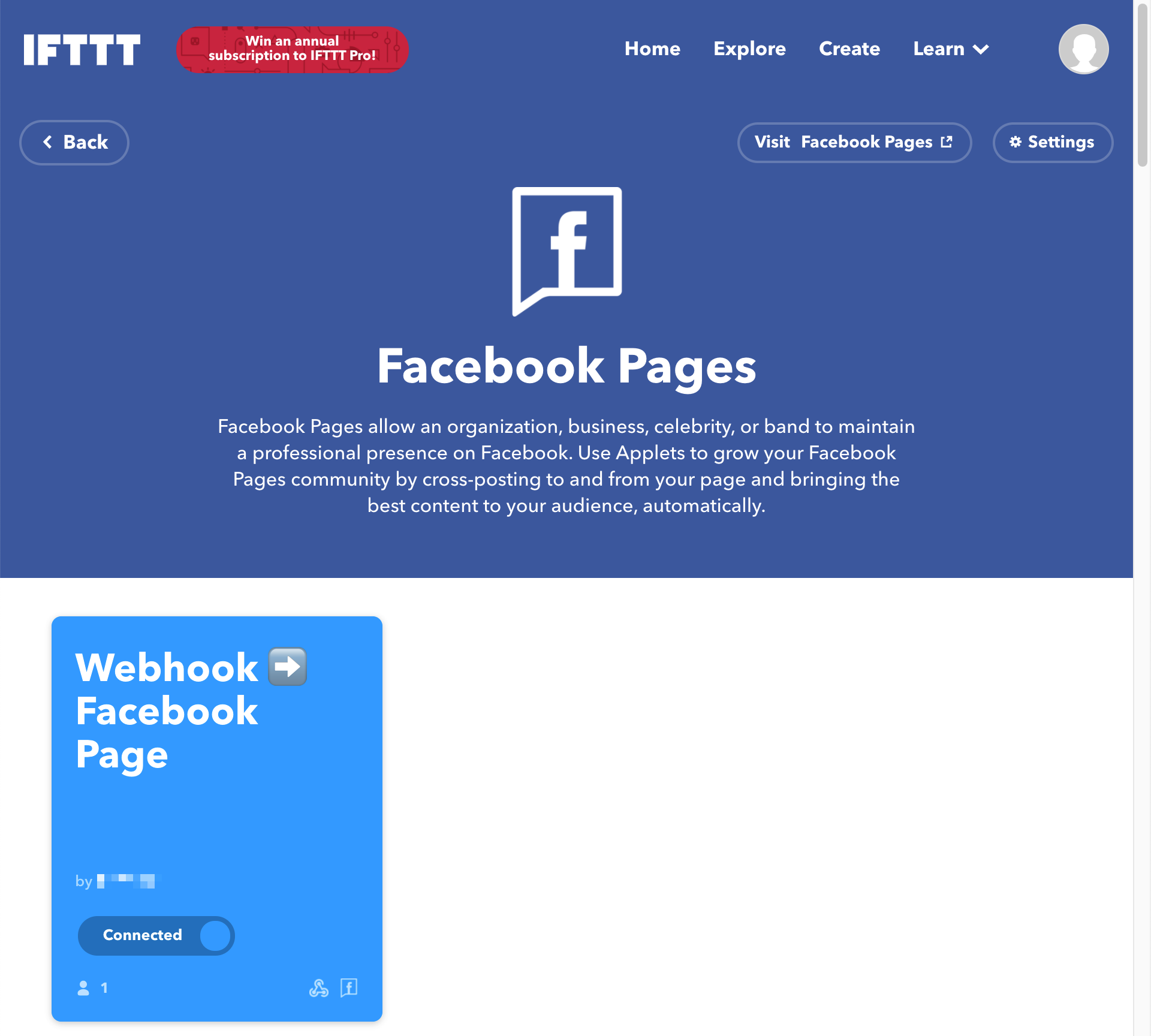
From the Logic App point of view, calling IFTTT is just another HTTP call. So it’s not that tricky. The only thing to remember is that the request payload can only include no more than value, value2 and value3.
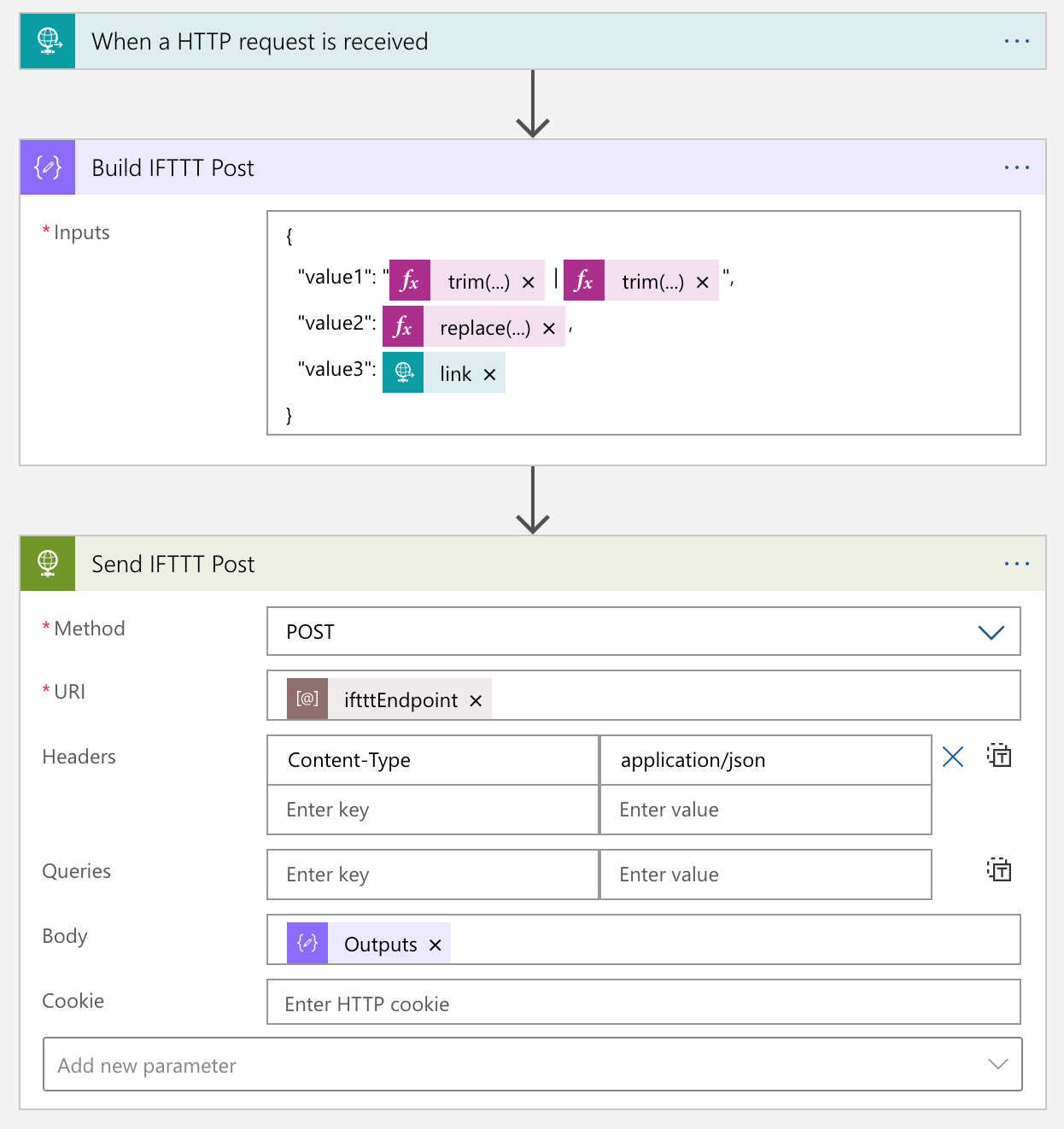
The actual process result in the IFTTT end looks like this:

We’ve amplified to social media of Twitter, LinkedIn and Facebook.
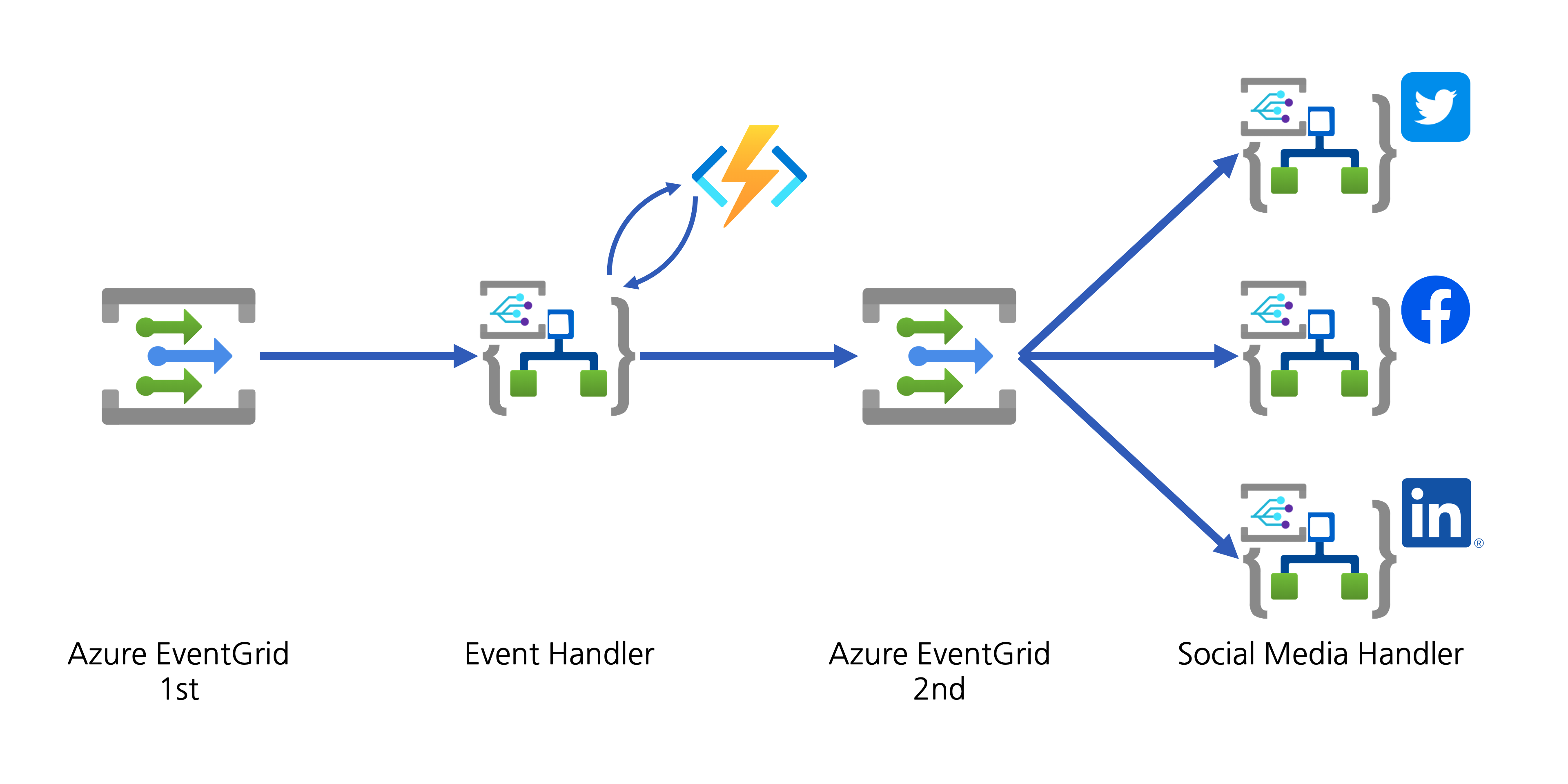
If you want to add another social media, you can simply add another Logic App as the event handler.
So far, we’ve implemented a workflow solution that posts to designated social media platform when a new YouTube video update is notified through WebSub, by using CloudEvents, Azure EventGrid, Azure Functions and Azure Logic Apps. As steps are all decoupled, we don’t need to worry about the dependencies during the maintenance phase. In addition to that, although a new social media platform is planned to add, it wouldn’t impact on the existing solution architecture.
If you or your organisation is planning online content marketing, it’s worth building this sort of system by yourself. And it would be an excellent opportunity to make a well-decoupled and event-driven cloud solution architecture.
This article was originally published on Dev Kimchi.


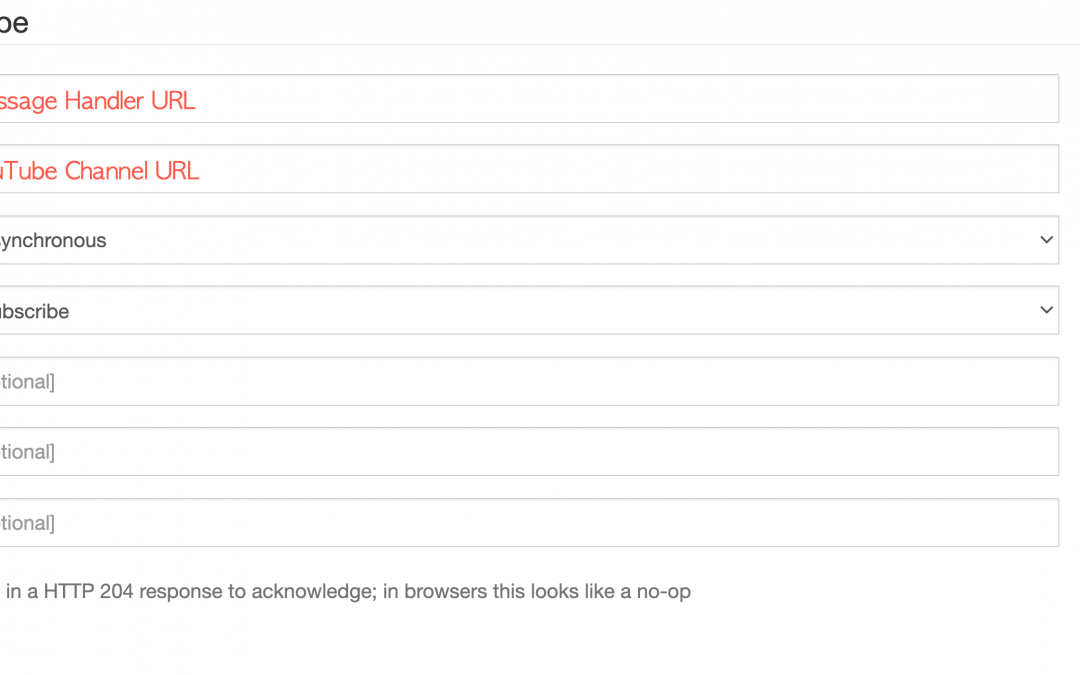
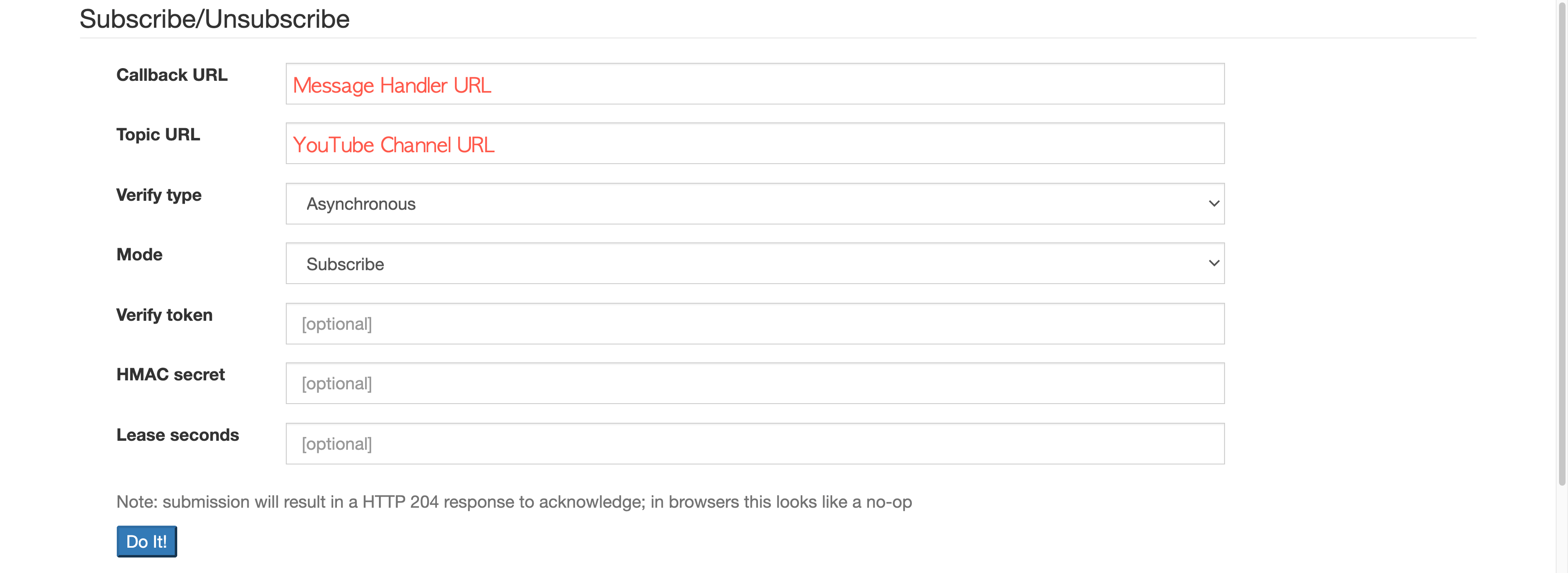
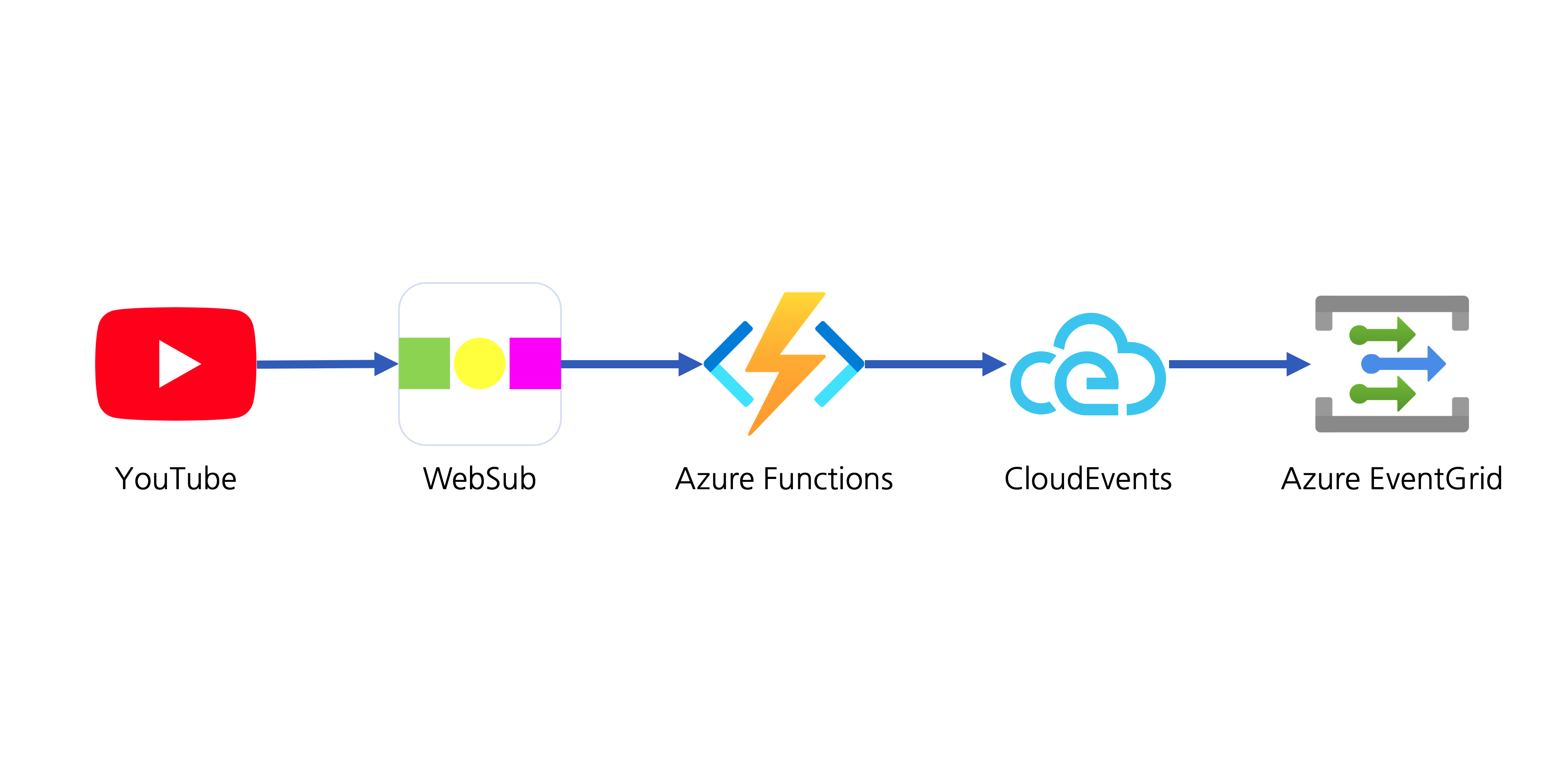
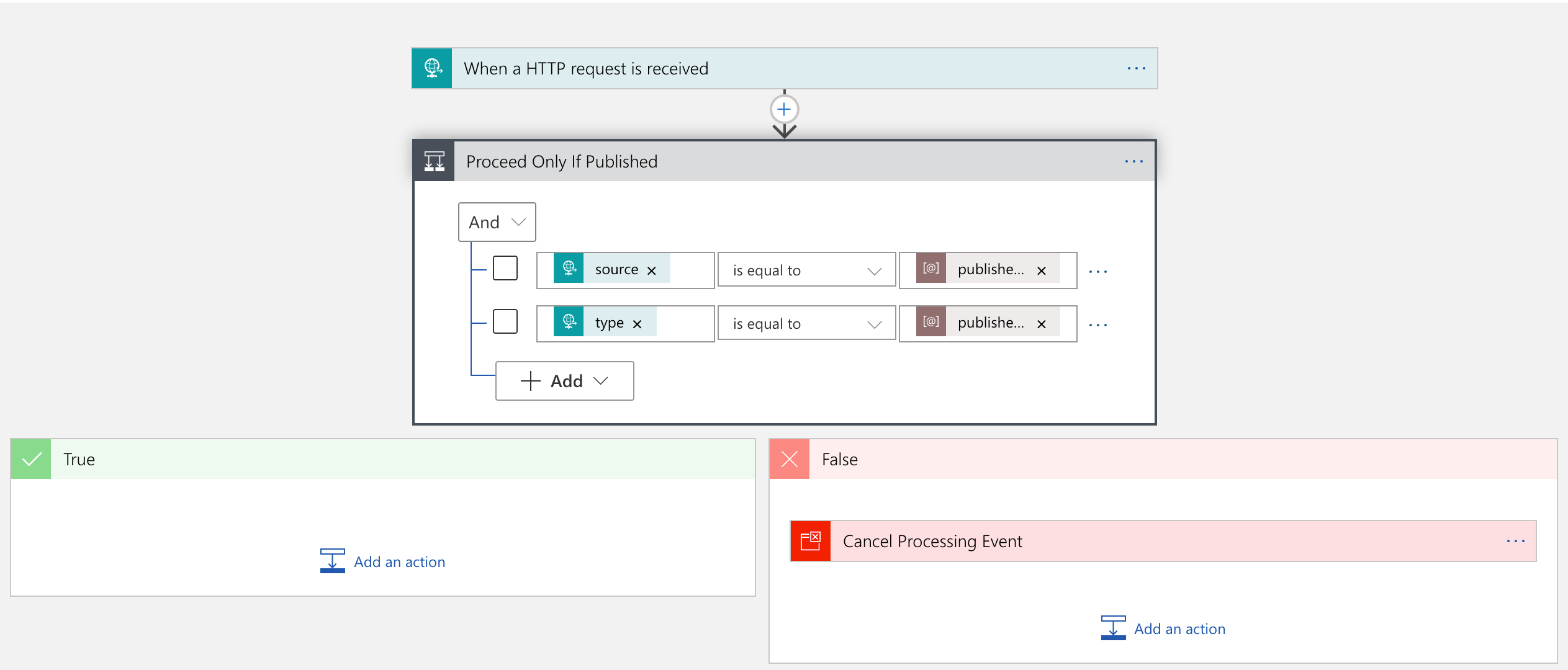
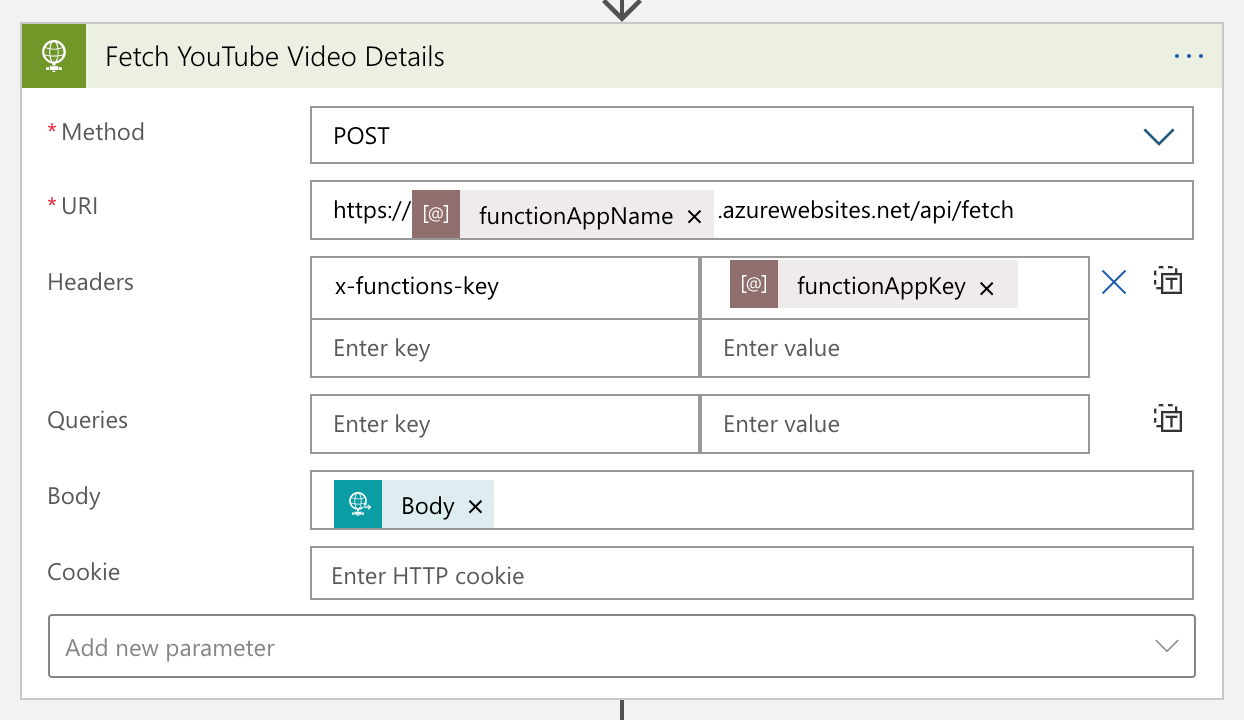
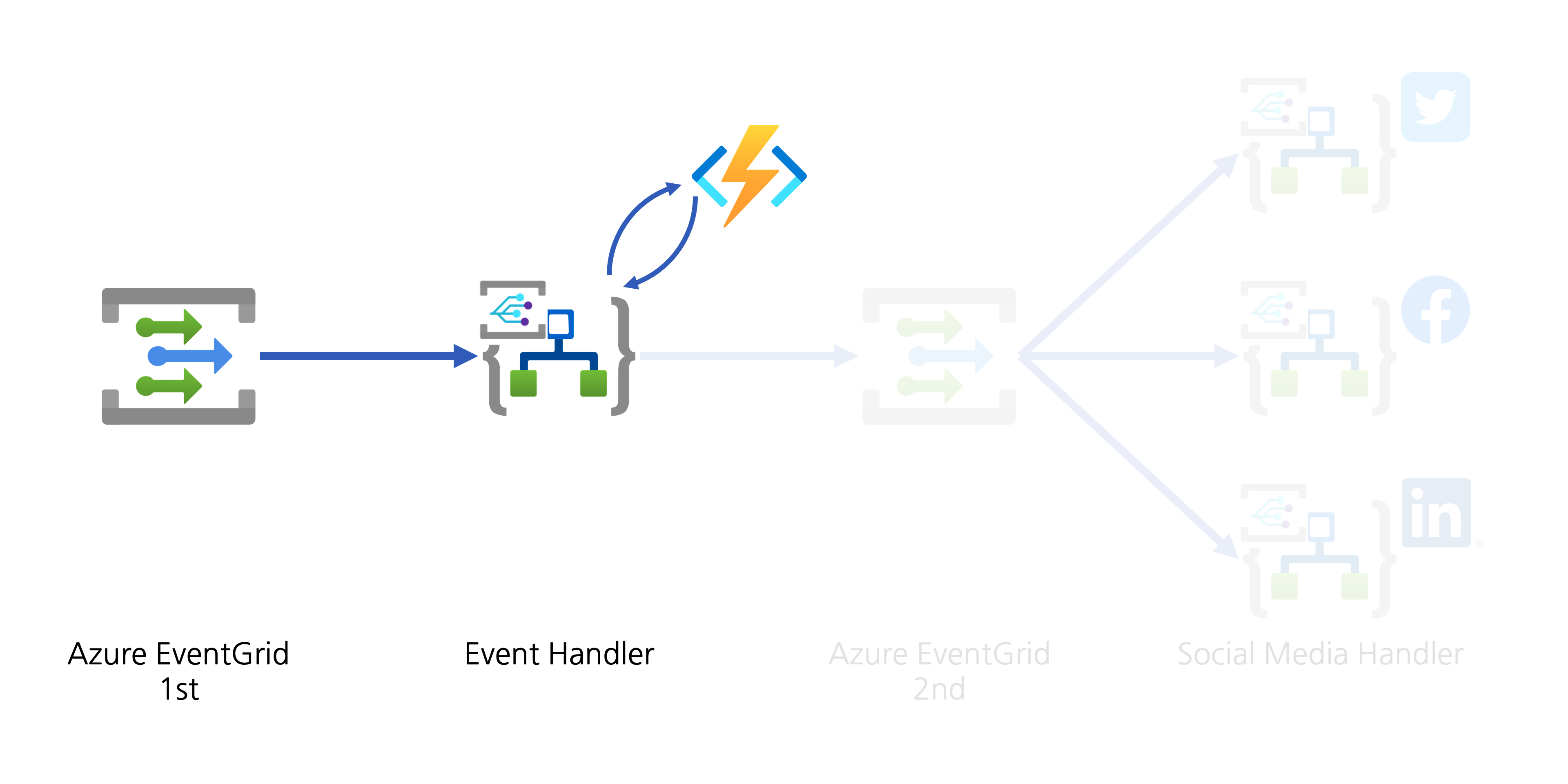
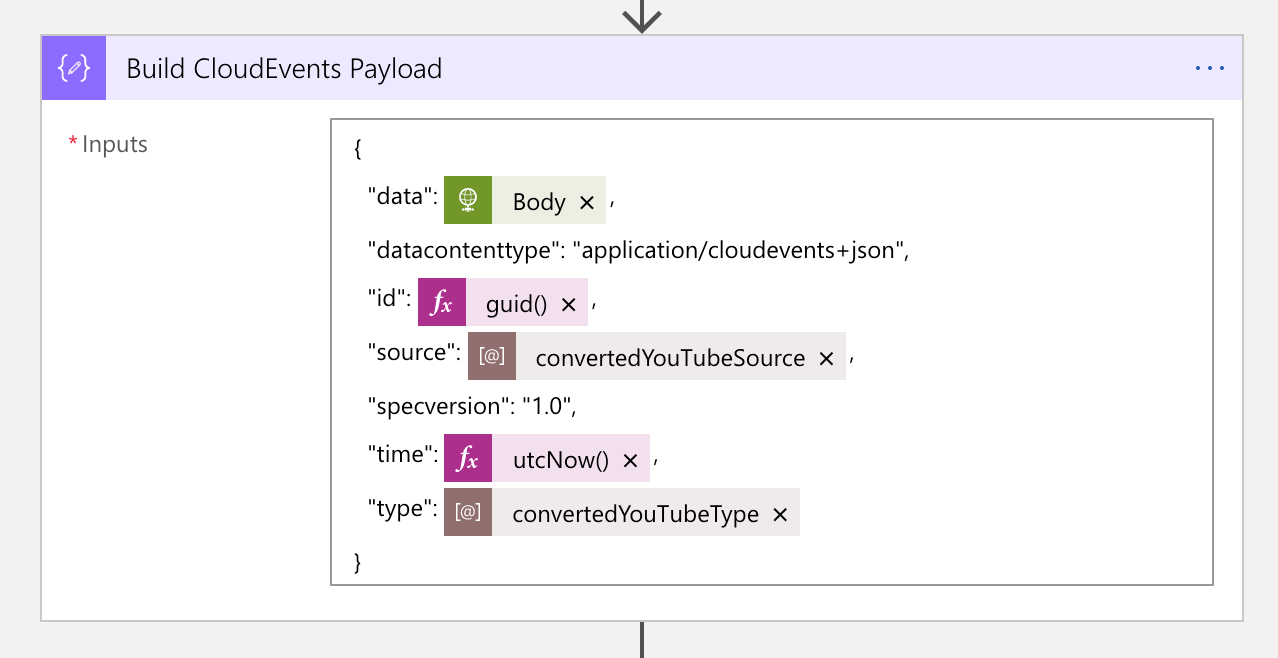
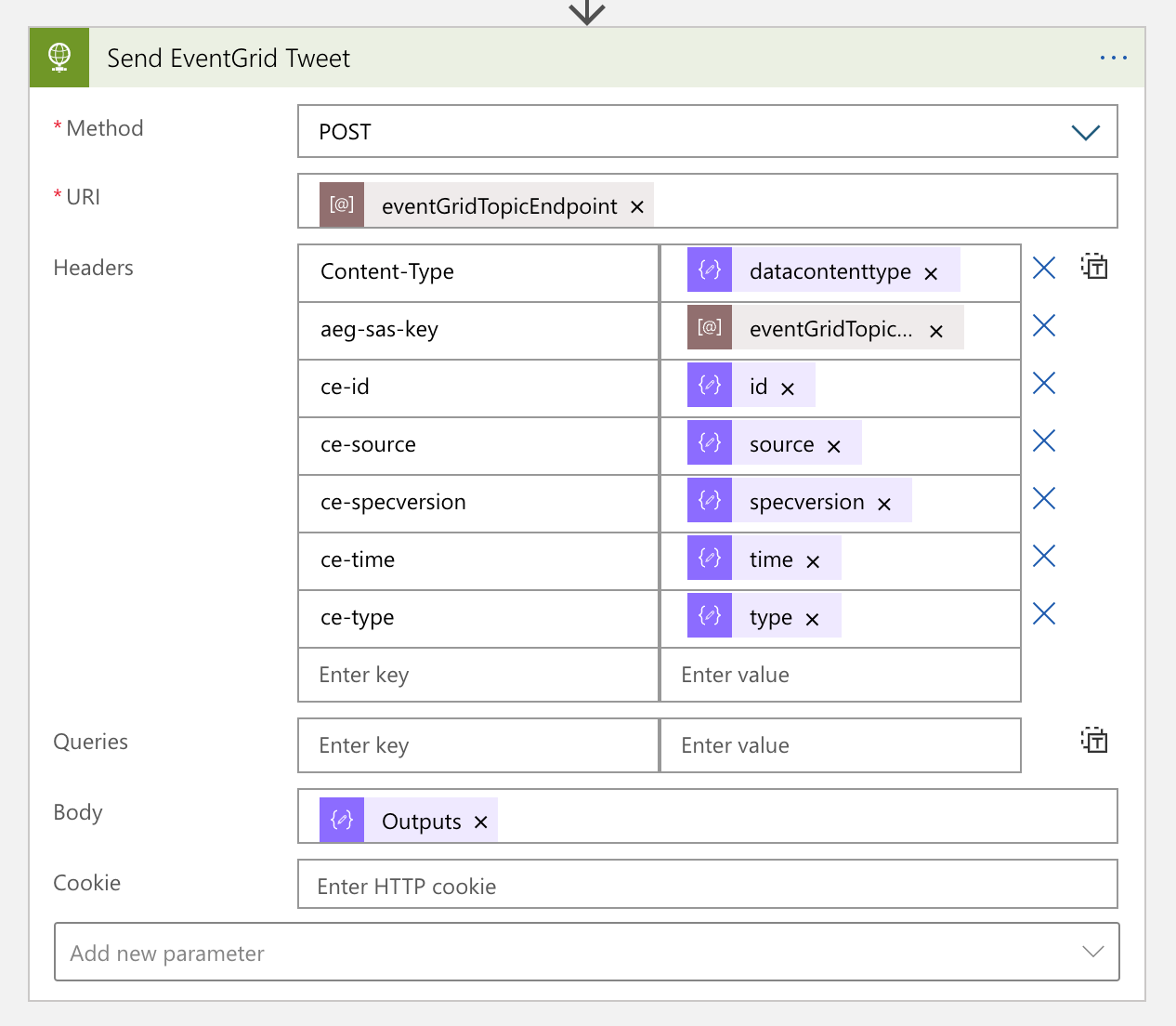
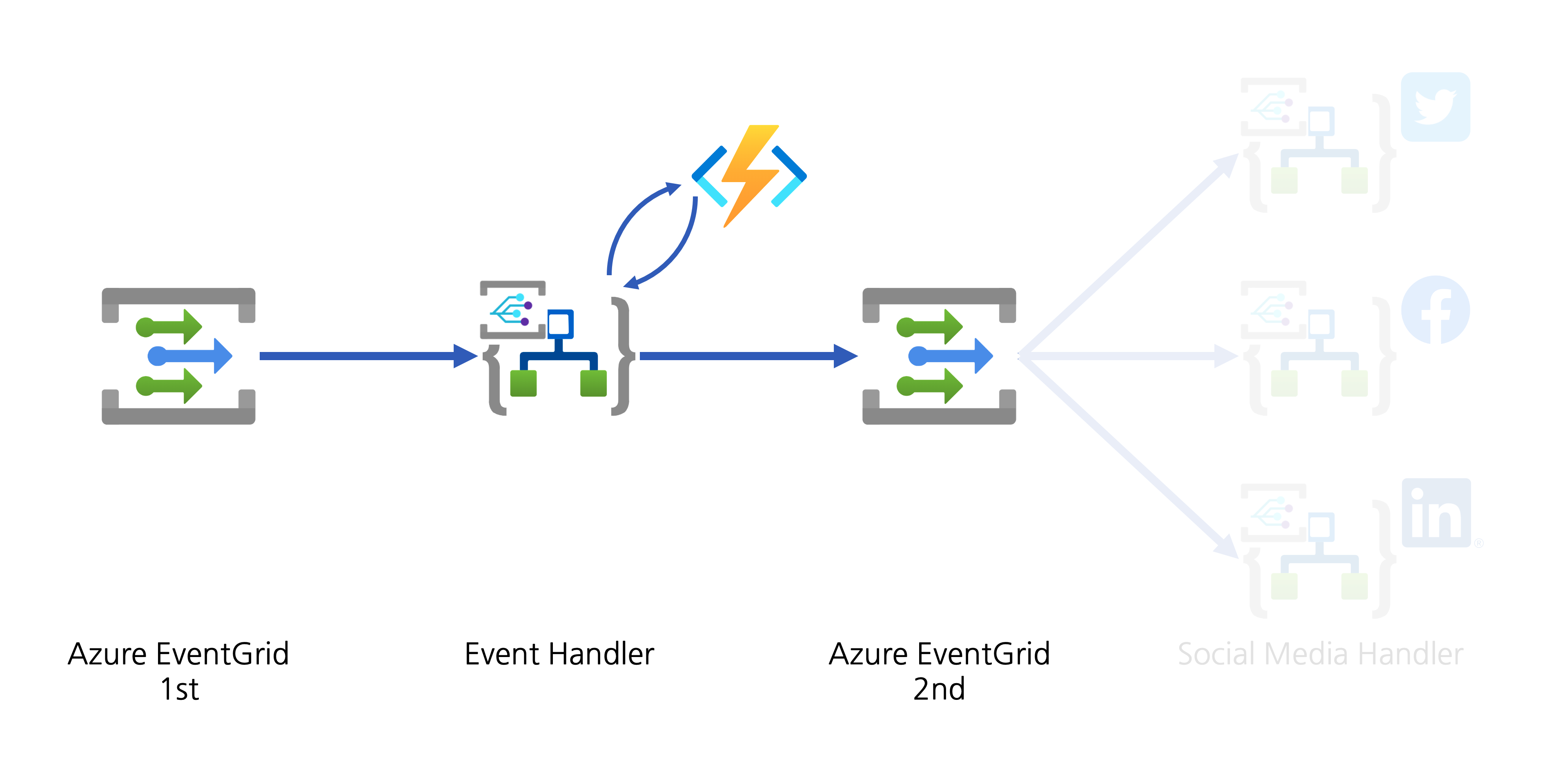
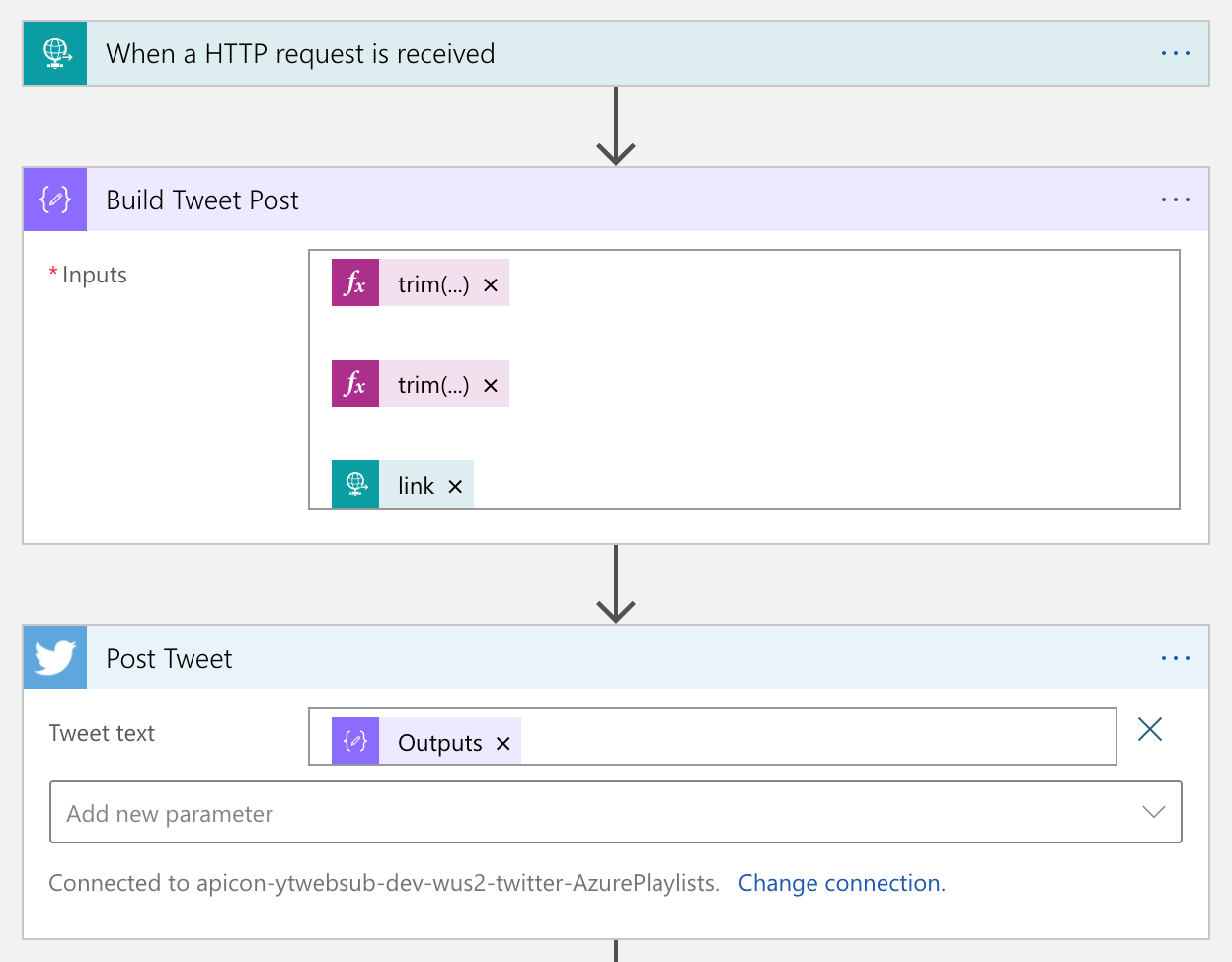
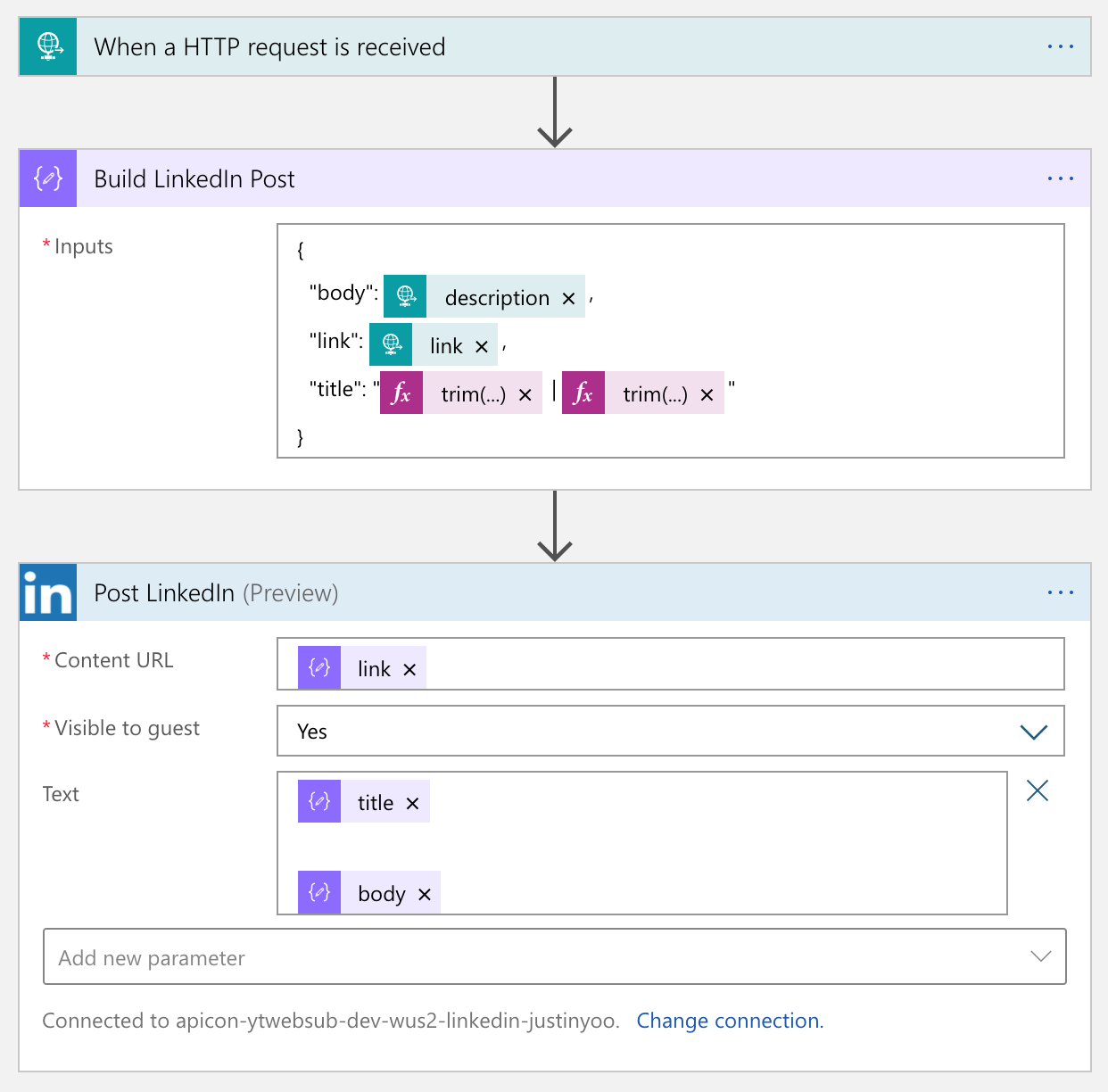
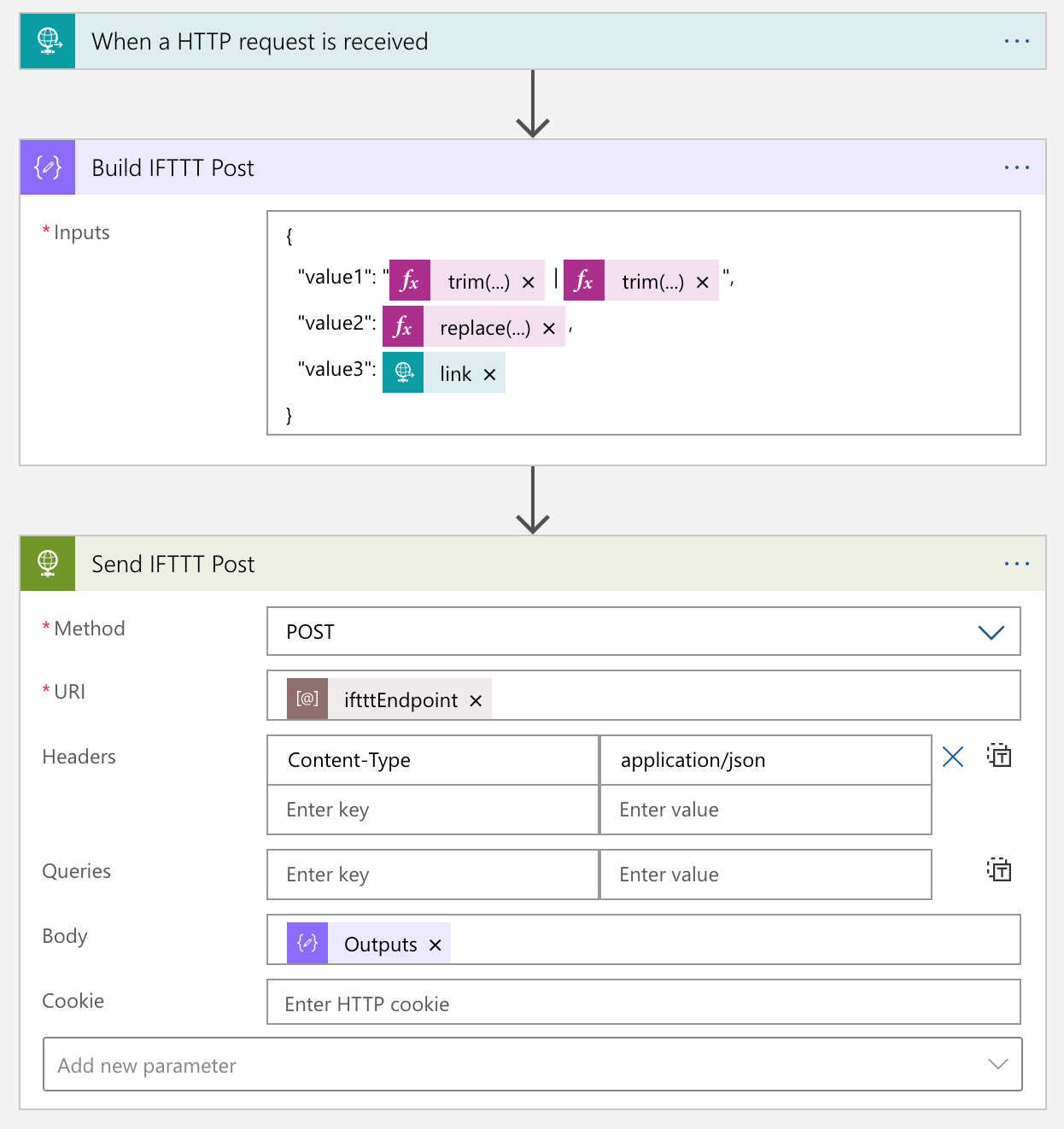

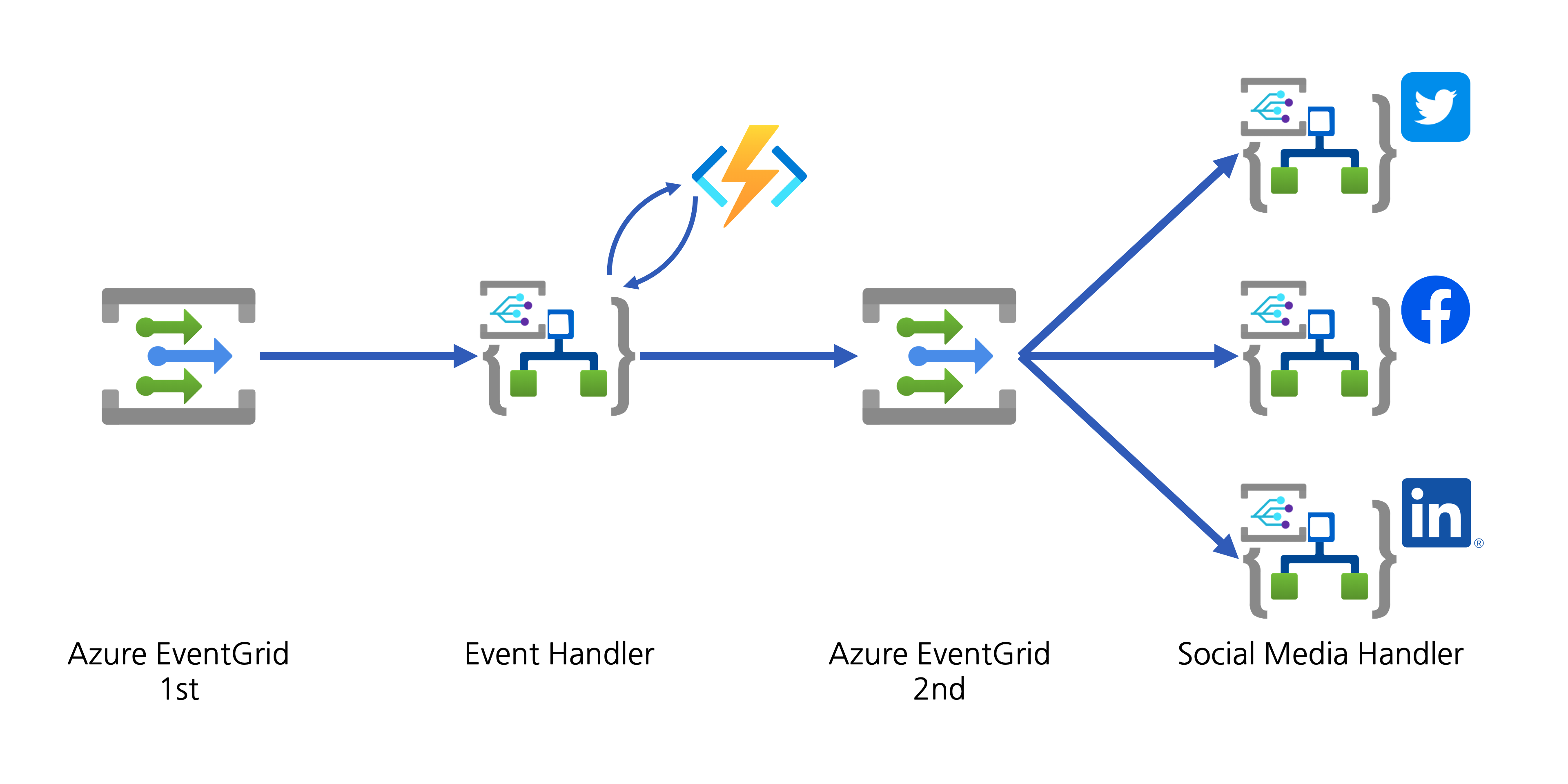

Recent Comments