by Contributed | Mar 4, 2021 | Technology
This article is contributed. See the original author and article here.
By @Sarahzin, @John_Lewis , @DanEdwards
We have some exciting news to share about our Microsoft Cloud App Security documentation updates. Last year, we released the ability to deploy Real Time Controls using any identity provider (IdP). After receiving initial feedback from our customers and the field, the top three most requested IdPs were PingOne, Okta, and AD FS.
The configuration can be tricky. We thought publishing an example for each IdP would be useful for our users. We are happy to announce that all three guides are now LIVE!
They can be found here:
- Configuring your PingOne IdP: Deploy Cloud App Security Conditional Access App Control for any web app using PingOne | Microsoft Docs
- Configuring your AD FS IdP: Deploy Cloud App Security Conditional Access App Control for any web app using AD FS | Microsoft Docs
- Configuring your Okta IdP: Deploy Cloud App Security Conditional Access App Control for any web app using Okta | Microsoft Docs
If you have any feedback or would like to see examples of other identity providers, please leave a comment below!
————————-
Feedback
We welcome your feedback or relevant use cases and requirements for Microsoft Cloud App Security by emailing CASFeedback@microsoft.com and mentioning the core area of concern.
Learn more
For further information on how your organization can benefit from Microsoft Cloud App Security, connect with us at the links below:
To experience the benefits of full-featured CASB, sign up for a free trial—Microsoft Cloud App Security.
Follow us on LinkedIn as #CloudAppSecurity. To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity on Twitter and Microsoft Security on LinkedIn for the latest news and updates on cybersecurity.
by Contributed | Mar 4, 2021 | Technology
This article is contributed. See the original author and article here.
The Azure Sphere 21.02 release includes the following components:
- Updated Azure Sphere OS
- Updated Azure Sphere SDK for Windows and for Linux
If your devices are connected to the internet, they will receive the updated OS from the cloud. We encourage you to install the latest SDK, but the existing 21.01 SDK will continue to work with the updated OS. To install the latest SDK, see the installation Quickstart for Windows or Linux:
New and changed features in the 21.02 release
The 21.02 release includes the promotion of the CLI v2 from Beta to release, and a new tutorial about memory management. The 21.02 OS update includes bug fixes and performance enhancements. The following sections provide details about these changes.
Azure Sphere CLI
The 21.02 Azure Sphere SDK release includes a new version of the Azure Sphere CLI that is easier to use in your shell and in your scripts. The new CLI is available in any shell such as PowerShell, Windows command prompt, or Linux command shell. It is installed alongside the deprecated Azure Sphere classic CLI on both Windows and Linux, so you have access to either interface.
- Azure Sphere CLI v2 now referred to as “Azure Sphere CLI”.
- Earlier Azure Sphere CLI versions (CLI v1 and lower) are now referred to as “Azure Sphere classic CLI”.
- The dedicated Azure Sphere Developer Command Prompt (available from Start > Azure Sphere or a shortcut) will be marked as deprecated and can be used only with the deprecated classic CLI.
The main new features of the new Azure Sphere CLI are summarized below and explained in detail here. The input and output for the new Azure Sphere CLI also have some differences compared to the Azure Sphere classic CLI. We encourage you to familiarize yourself with these differences and plan to migrate your processes and scripts that use the CLI. Although both versions of the CLI can be installed and used side-by-side, the classic CLI is no longer updated or maintained and will be retired in the coming months.
Tab completion
Tab completion is like autocomplete for the command-line interface. Type a few characters of a command and then press TAB to select the desired completion text. If multiple items begin with the text that you initially typed, then continue pressing TAB until the item you want appears.
In Linux, Azure Sphere CLI supports the tab completion feature for commands under the Bash shell.
Additionally, autocompletion helps you discover commands, parameters, and parameter values that are available to use. This is available by using CTRL+Space in Windows PowerShell or press TAB twice in the Linux Bash shell.
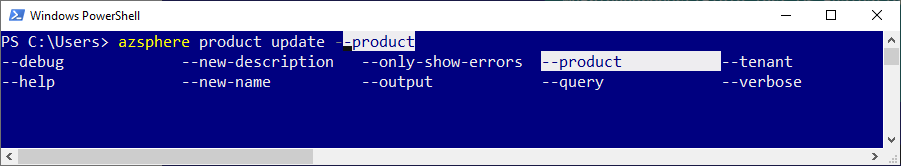
For example, type azsphere product update and use autocompletion to see a list of available parameters.
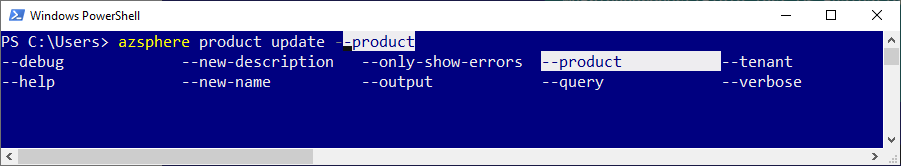
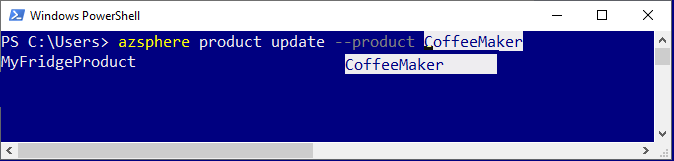
Similarly, type azsphere product update –product and use autocompletion to see a list of available products in your tenant.
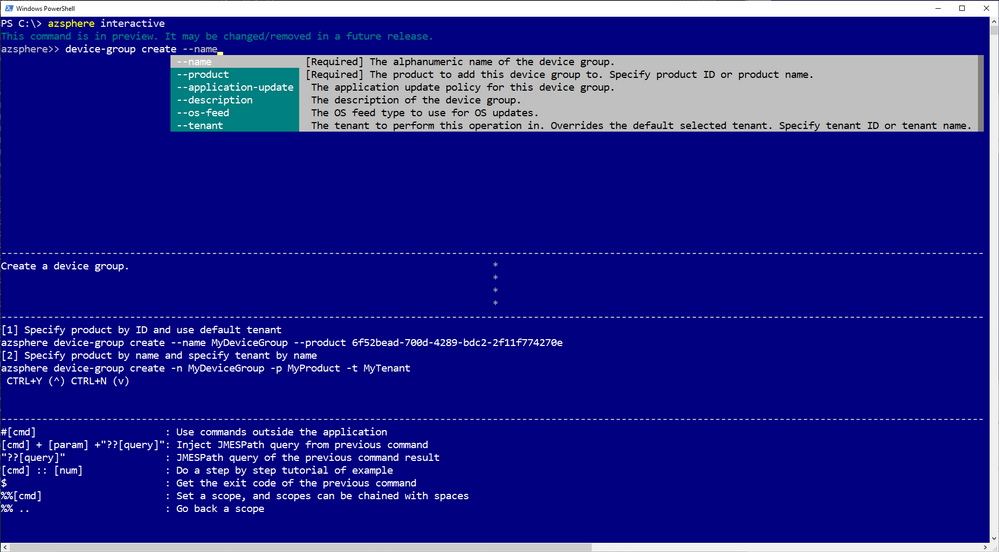
Interactive mode (preview)
Interactive mode automatically displays information and makes it easier to select commands and sub-commands. Enter the interactive mode with the azsphere interactive command. The command prompt changes to azsphere>> to indicate that you are now running commands in the interactive shell.
Flexible output (preview)
You can more easily automate CLI commands by writing scripts that consume JSON or YAML output. You can separate this “stdout” output from “stderr” related error and informational messages. You can redirect it or paginate it with your favorite tools. And you can filter, modify, and sort it using the new –query option. Only some commands currently support these new output options; let us know via azsphere feedback if we’re missing a command that you need to script.
New and updated samples for 21.02
The 21.02 release includes the following new and updated sample hardware designs and applications:
- New tutorial on memory usage to demonstrate how to detect and fix memory usage problems, such as a memory leak, in your application.
- Updated Readme files include commands for both the new Azure Sphere CLI and deprecated Azure Sphere classic CLI.
Fixed bugs and common vulnerabilities in the 21.02 OS release
The 21.02 OS release includes various bug fixes, a Linux kernel update, and mitigations against the following CVEs:
- CVE-2021-3336
- CVE-2020-8285
- CVE-2020-8286
- CVE-2020-8284
- CVE-2020-8231
For more information on Azure Sphere OS feeds and setting up an evaluation device group, see Azure Sphere OS feeds and Set up devices for OS evaluation.
For self-help technical inquiries, please visit Microsoft Q&A or Stack Overflow. If you require technical support and have a support plan, please submit a support ticket in Microsoft Azure Support or work with your Microsoft Technical Account Manager. If you would like to purchase a support plan, please explore the Azure support plans.
by Contributed | Mar 4, 2021 | Technology
This article is contributed. See the original author and article here.
Follow these step by step guides to help you get started in configuring Teams DLP, Endpoint DLP and Insider Risk in your organization today!
Insider Risk interactive guide
Endpoint DLP interactive guide
Teams DLP interactive guide
by Contributed | Mar 4, 2021 | Technology
This article is contributed. See the original author and article here.
After a customer has connected Microsoft Defender for Identity to Microsoft 365 Defender one of the benefits is the ability to query the Defender for Identity activities. In this blog we showcase two customer use cases that took advantage of the Advanced Hunting functionality available today.
We continue to build functionality into Microsoft 365 Defender and we are encouraging identity focused customers to leverage its available activities in Advanced Hunting. This unified solution provides a platform to conduct advanced hunting, incident correlation and custom detections across the Microsoft 365 security stack. Building on these options, we wanted to supply two queries that have helped solve two customer use cases.
Use Case #1: Enhanced reporting on usage of LDAP Simple Bind
When LDAP Simple Bind is used, the username and password are sent across the network (wire) in cleartext. Imagine if this happens to a user who has elevated privileges in the domain.
In this use case the customer had started a project to eliminate the use of LDAP Simple Bind. Anyone who might be sniffing the network traffic would see this information and could then start impersonating the user.
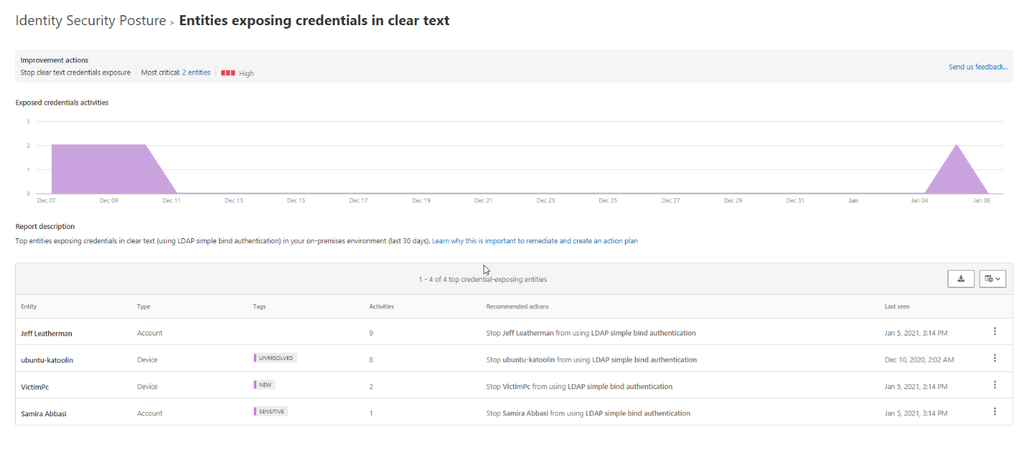
One of the Identity Security Posture assessments part of Defender for Identity is “Entities exposing credentials in clear text”. This assessment shows the top devices that are sending user authentications via LDAP Simple Bind and which users are authenticating from these devices.
For organizations with multiple domains and forests that are monitored by Defender for Identity the assessment shows data across all forests and domains.
For customers that have multiple domains, Microsoft 365 Defender can assist in pinpointing where these accounts fall across their environment. We can create this report by leveraging Microsoft 365 Defender Advanced Hunting , which can be found here.
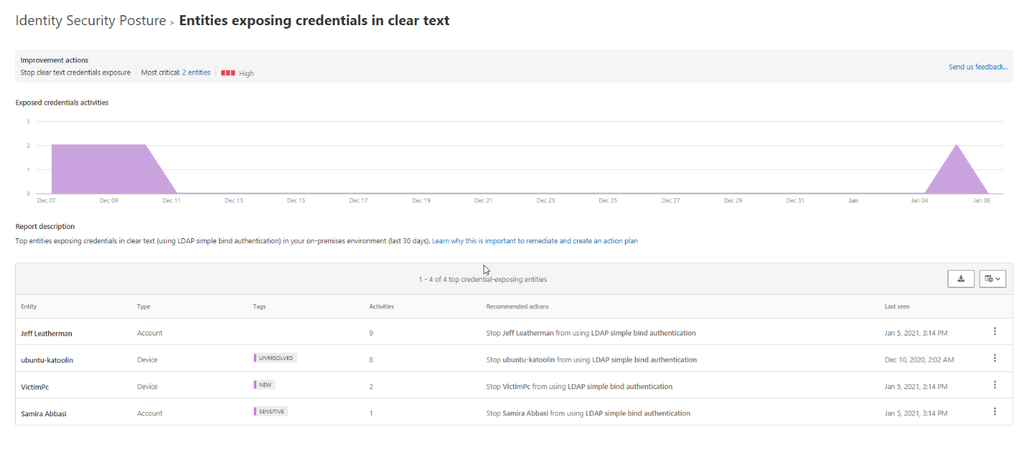
Run the below Kusto Query Language (KQL) query that will return all LDAP logons where the logon types include passwords in clear text.
let firstIndexof = (input:string, lookup: string) {
indexof(input, lookup, 0, -1)
};
IdentityLogonEvents
| where LogonType == "LDAP cleartext" and ActionType == "LogonSuccess"
| extend DomainName = substring(DestinationDeviceName, firstIndexof(DestinationDeviceName, '.') + 1)
| where DomainName == "contoso.azure" // replace contoso.azure with your domain name.
| summarize NumberOfEntries=count()by LogonType, ActionType, AccountDisplayName, DomainName, AccountSid, IPAddress, DeviceName, DC = DestinationDeviceName
| sort by AccountDisplayName
You will see that we have summarized by the number of events and the results you receive will contain data such as users, domain and device, etc.
As the customer, you could also add the following line to specify a domain within your environment
| where DomainName == “domain name”
By using a combination of both products, we have elevated our MDI experience and can continue to generate on demand reports for the last 30 days that will assist in improving your overall security posture.
Use Case #2: What were the commands that were run in the Remote Code Execution alert
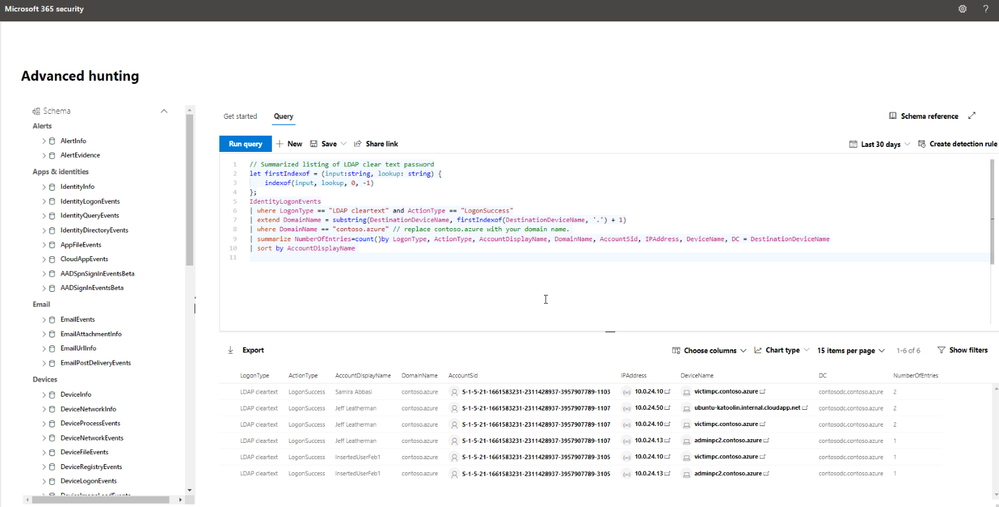
In our second query, we are focusing on using Advanced Hunting to join multiple tables from both Defender for Identity and Microsoft Defender for Endpoint that will better assist us in determining all important details from a single MDI alert.
This alert will trigger when Defender for Identity detects PSexec, Remote WMI, and remote PowerShell connections to a monitored domain controller.
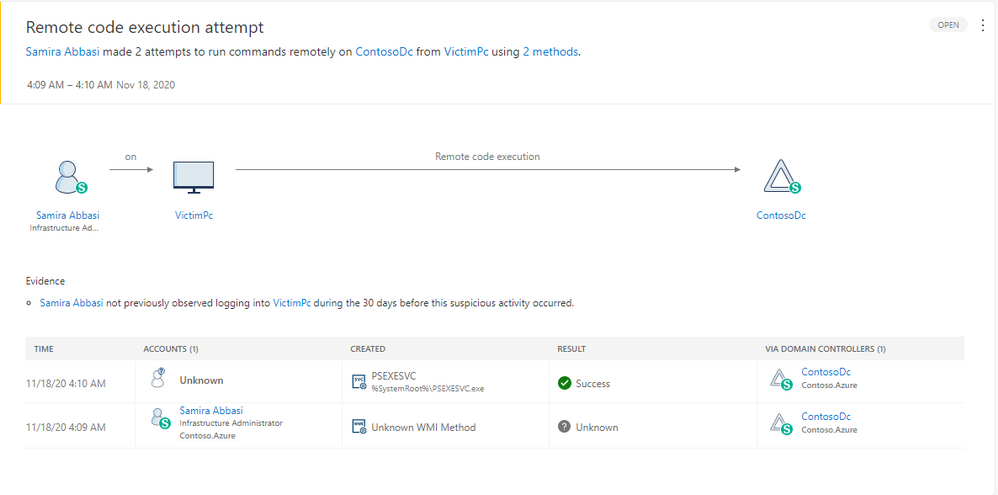
As you can see from the graphic above, Defender for Identity provides critical details that we can use in our query including the timeframe of the suspected attempt, the device name and the user in question. We will take these critical details and join them to data available from Defender for Endpoint.
After receiving the alert, the customer was looking for the WMI command that was run to determine if they would need to further investigate these activities.
In the example above, we also have deployed Defender for Endpoint so local device activity is also available. Via an advanced hunting query we were able to extract the device (VictimPc) from the Defender for Identity alert and then query the endpoint data for the required information. This allows us to extract the commands that triggered the alert.
let duration = totimespan(600m); //update this number of minutes in the future you want to check for WMIC and PSexec commands
AlertInfo
| where Timestamp > ago(7d)
| where ServiceSource == "Microsoft Defender for Identity"
| where Title == "Remote code execution attempt"
| project AlertId, AlertTime = Timestamp, Title
| join (AlertEvidence) on AlertId
| where EvidenceDirection == "Source" and EntityType == "Machine"
| project AlertId, AlertTime, DeviceId, DeviceName, UpdateTime = Timestamp, Title
| join (DeviceProcessEvents
| where FileName == "WMIC.exe" or FileName == "PsExec.exe"
| project ProcessTime = Timestamp, ProcessCommandLine, FileName, FolderPath, DeviceName, DeviceId) on DeviceId
| where ProcessTime - UpdateTime between (-2m .. duration)
// | where ProcessTime >= AlertTime
| project AlertId, AlertTime, ProcessTime, UpdateTime,Title, DeviceName, FolderPath, ProcessCommandLine, FileName
| sort by ProcessTime desc
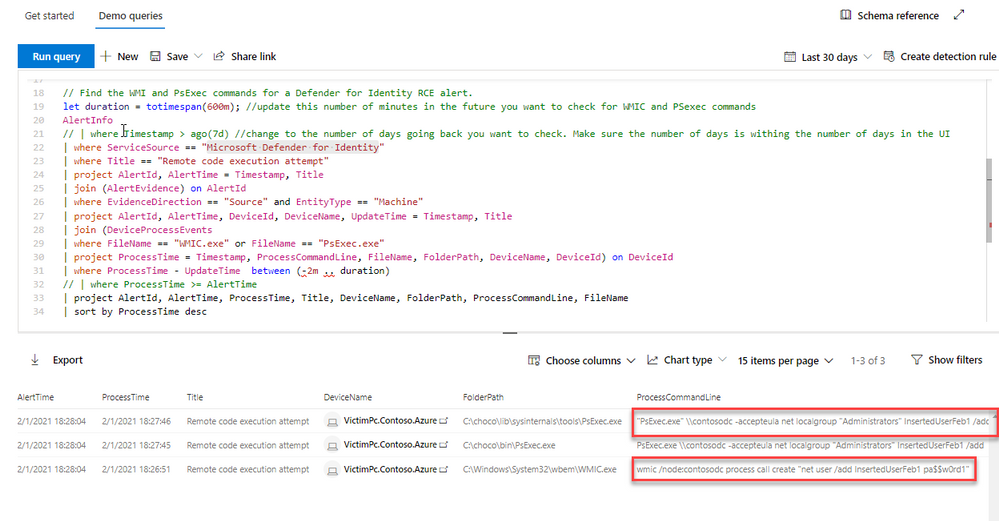
In the above query, you can see the psexec and WMI commands that triggered the alert. Using this information, you can more easily determine if this is anomalous behavior for your environment.
With the capabilities discussed above, you can see there is a lot of data available to query and assist customers in deep diving into their environment after receiving an alert. As our products and analytics grow, we will continue to find more ways to elevate the customer experience across the Microsoft 365 security stack.
by Scott Muniz | Mar 4, 2021 | Security, Technology
This article is contributed. See the original author and article here.
The National Security Agency (NSA) and CISA have released a Joint Cybersecurity Information (CSI) sheet with guidance on selecting a protective Domain Name System (PDNS) service as a key defense against malicious cyber activity. Protective DNS can greatly reduce the effectiveness of ransomware, phishing, botnet, and malware campaigns by blocking known-malicious domains. Additionally organizations can use DNS query logs for incident response and threat hunting activities.
CISA encourages users and administrators to consider the benefits of using a protective DNS service and review NSA and CISA’s CSI sheet on Selecting a Protective DNS Service for more information.

by Contributed | Mar 4, 2021 | Technology
This article is contributed. See the original author and article here.

Mixed reality enables immersive capabilities that merge the digital and the physical worlds. With Azure mixed reality services, developers can create experiences that understand people, places, and things in their environment. These services consist of Azure Spatial Anchors, Azure Remote Rendering, and Azure Object Anchors. Azure Spatial Anchors is generally available and enables multi-user, multi-device, spatially aware mixed reality experiences. At Ignite 2021, we announced the general availability of Azure Remote Rendering and preview of Azure Object Anchors.
Azure Remote Rendering is now generally available
Mixed reality use cases require users to view and interact with 3D models. Models are decimated and simplified to enable visualizations through target devices – mixed reality headsets or mobile devices. The result is the loss of important detail which is necessary in design reviews and for making business decisions. Azure Remote Rendering enables developers to render high-quality, interactive 3D content and stream it to a HoloLens 2 device in real time. Remote Rendering leverages the power of the Azure cloud to enable visualizations without decimation for the most complex models. Developers can render models up to 20 million polygons with Standard Remote Rendering and over a billion or more polygons with Premium Remote Rendering.
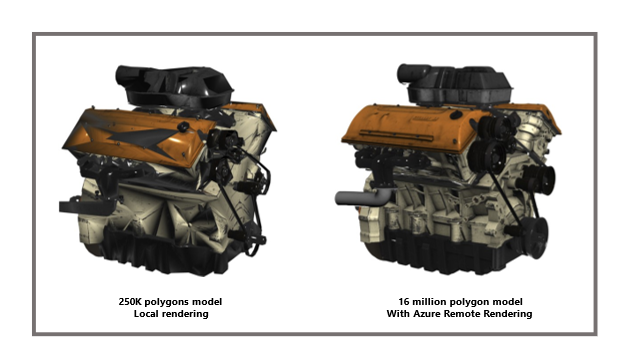
How does the service work?
Azure Remote Rendering moves the workload to high-end GPUs in the cloud. A cloud-hosted graphics engine renders the image, encodes it as a video stream, and streams that to the target mixed reality device. In addition, Remote Rendering supports hybrid rendering where local content like menus are automatically combined with remote objects for an immersive experience.
Get started today with this learning module. For more information, review our documentation.
Customer adoption
It has been great to see how customers and partners are leveraging Remote Rendering to enable 3D visualizations with high fidelity. Bentley Systems has reimagined the bridge inspection process using HoloLens and Remote Rendering. Every detail matters when performing structural inspections. Dan Vogen summarizes it well:
“We need to display, and interact with, hundreds of millions of polygons in reality meshes.
Azure Remote Rendering helps us do this and more – it’s like sci-fi interaction with infrastructure assets. The resolution, detail, and accuracy “teleport” users to an asset. This cuts time spent, lowers costs, improves safety, and reduces traffic disruptions thanks to our HoloLens-based immersive inspection processes.”
Dan Vogen, Vice President, Transportation Asset Management, Bentley Systems
HoloLab is building an application to enable visualization of architectural layouts at scale and with precision using Azure Remote Rendering.
“We’re excited about the innovation and efficiency of Azure Remote Rendering. We work with enterprises in manufacturing, architecture, engineering, and construction. They use Remote Rendering for visualization, and sharing, of high polygon, 3D CAD data. The BIM construction data used to be so large that you could only display one floor at a time. Now, thanks to Remote Rendering, HoloLens shows an entire building at once.”
Kaoru Nakamura, Co-Founder & CEO, HoloLab Inc.
To provide our global partners and customers a choice of regions for their Remote Rendering solutions we’ve expanded the availability of Remote Rendering to 10 regions including Australia East, East US 2, Japan East, North Europe, South Central US, and UK South, East US, West US 2, West Europe, and Southeast Asia.
Azure Object Anchors is now in public preview
Azure Object Anchors is innovation based on customer and partner feedback. Adoption of mixed reality technologies has accelerated and customers want to easily align holograms to physical objects. Enter Azure Object Anchors. Object Anchors enables developers to automatically align and anchor 3D content to objects in the physical world. This eliminates the need for markers and manual holographic alignment.
During the private preview, we worked closely with Toyota. Toyota is leveraging Object Anchors so that its technicians can easily align holographic wiring content with car engine wiring. As soon as the technicians align objects, they can walk up, scan, and begin work. This saves time and reduces errors.
“Azure Object Anchors enables our technicians to service vehicles more quickly and accurately thanks to markerless and dynamic 3D model alignment. It has removed our need for QR codes, and eliminated the risk of error from manual model alignment, thus making our maintenance procedures more efficient.“
Koichi Kayano, Project Manager Technical Service Division at Toyota
We’re working with other partners as well as internal teams including D365 Guides. It has integrated Object Anchors in private preview and is hearing positive feedback from customers. Whether you’re building a custom mixed reality application or an industry specific solution, developers can use Object Anchors in scenarios such as task guidance, step-by-step training, and virtual inspections.
The early feedback from our customers has led to many improvements in our latest SDK, documentation, and samples. We’re excited to expand this broadly with Azure Object Anchors entering public preview.
How does this service work?
The Azure Object Anchors workflow encompasses two main steps: training and runtime.
Training
The Object Anchors service converts 3D assets into AI models that enable object-aware mixed reality experiences. For the physical object to which you’d like to align content, you need a 3D model of it in one of our supported formats (gltf, glb, obj, fbx, ply). The service ingests the model and runs it through our training pipeline. Once completed, it outputs the information you need to leverage detection and alignment in our runtime.
Runtime
To create a runtime detection experience:
- Start a session
- Load object model (output from training)
- Set search area
- Detect physical object and align content
- Lock alignment
- Render 3D content
It’s easy to get started with Object Anchors sample applications leveraging Unity and MRTK. You can also write custom code using our runtime SDK.
Learn more about Object Anchors here. To get started with existing 3D models see this.
Azure mixed reality services have momentum. In only two years, our customers and partners have built immersive mixed reality solutions to enable technicians, educators, students, and professionals to achieve more. We can’t wait to see what you build next. Get started today with Azure mixed reality services.
Credits: Archana Iyer, Jonathan Lyons, Armin Rezaiean-Asel
by Contributed | Mar 4, 2021 | Technology
This article is contributed. See the original author and article here.
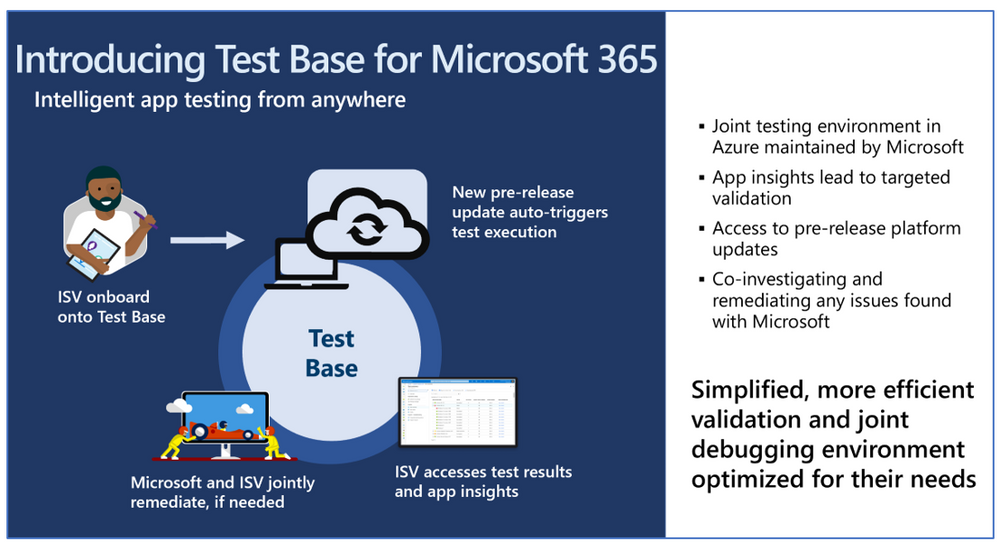
We are excited to update you on the latest Test Base for Microsoft 365 features and how you and your organization can take advantage of this service.
A little more than a year ago, we announced the availability of a new testing service targeted at desktop applications called Test Base for Microsoft 365. Over the last several months, the Test Base for Microsoft 365 team met with several enterprise customers to learn more about their testing operations and challenges. They shared some valuable insights into enterprise behaviors and key pain points, including:
- More than three-quarters are pursuing a cloud-based virtualization strategy.
- About half are doing pre-deployment testing on monthly Windows updates.
- Most are neutral to dissatisfied with pre-deployment testing of Windows feature updates.
- Test needs span across third-party, line-of-business (LOB), and in-house built applications.
Subtle changes have happened in the application testing space since the launch of Windows 10. It has ushered in an era of superior application compatibility, with newer processes such as ring-based testing and flighting strategies helping IT pros pilot devices against upcoming builds of Windows and Office, while limiting exposure to many end users. Despite these positive changes, there is still a need to test business critical apps such as antivirus, VPN or internally-developed LOB applications.
What is Test Base for Microsoft 365?
Test Base for Microsoft 365 is an Azure service that facilitates data-driven testing of applications. Backed by the power of data and the cloud, it enables IT professionals to take advantage of intelligent testing from anywhere in the world. If you are a developer or a tester, Test Base strengthens your application’s ability to continue working even as platform dependencies such as the latest Windows updates change. It will help you test your applications without the hassle, time commitment, and expenditure of setting up and maintaining complex test environments. Most importantly, it will give you access to pre-release Windows Updates on secure virtual machines (VMs) and world-class intelligence for your applications.
The IT pro and Test Base
As an IT professional, you’re no doubt evaluating modernization technologies that will simplify the application and device management across your user base. Technologies such as Windows Virtual Desktop and MSIX, in tandem with early adoption via the Windows Insider Program, help reduce the application compatibility concerns associated with Windows and Office updates. Based on your feedback, the testing workflow usually takes you outside of the core device management tools that you use today. In addition, the install base or the business-critical nature of some applications can make it painful when encountering a failure. The subsequent coordination of failure analysis with software vendors or internal developers can be time consuming and can delay remediation. You have asked that testing and validation be part of the seamless workflow – assess, remediate, deploy at scale.
Test Base aspires to help our customers focus their test efforts and get to the confidence they seek faster. Our initial offering focused on critical third-party software vendors whose applications (anti-virus, VPN, disk encryption etc.) we all depend on. As we expand the value to our enterprise customers, we want to invite you to onboard your internal LOB applications on Test Base. Not only will you get test coverage against Windows security and feature updates, but also data insights and support on application failures, allowing you to quickly remediate fixes prior to broad release across your organization.
While we further build out this seamless workflow, here is what you can do now as an IT professional – nominate the software vendors or onboard your internal standalone apps. Once onboarded, you will benefit by having the confidence signals for the applications that you care about.
What’s new since Microsoft Ignite: September 2020?
We are constantly innovating and adding capabilities based on customer feedback. Here’s a quick summary of new features that you can look forward to:
- Intelligent CPU regression analysis – Test Base now provides software developers with insights into CPU performance regressions when their application is running on a pre-release version of an upcoming Windows update.
- Support for Server application testing – A top ask from software vendors, your apps will be validated against pre-release monthly security updates for Windows Server 2019 and/or Windows Server 2016, including the Server Core edition.
- Test Base Champions – We established a program where our most active customers can meet with us to share feedback as well as learn what’s next for Test Base. This is a great forum for customers to collaborate on their favorite features and drive prioritization.
- Test Base how-to videos – Our how-to video series will help you ramp up quickly. Learn how to onboard your applications and analyze the results on Test Base:
What’s next on the roadmap for Test Base for Microsoft 365?
We are continuously gathering and collaborating on feedback to improve upon and prioritize the future for the Test Base service. Examples of capabilities that you can expect to light up in the next few months include asynchronous alerts & notifications, support for API-based onboarding and support for Office 365 testing.
Join the Test Base community
We are actively engaging with enterprise customers now to understand their needs and design a solution that addresses their use cases. If you would like to participate in this discussion, please join in! I would also like invite you to come join us on the new Test Base for Microsoft 365 community on Tech Community so you can share your experiences and connect with other customers using the service.
If you are software vendor who is interested in onboarding your applications to Test Base, or if you are an IT professional whose organization is interested in nominating a software vendor to participate, please complete the preview sign-up form.
by Contributed | Mar 4, 2021 | Technology
This article is contributed. See the original author and article here.
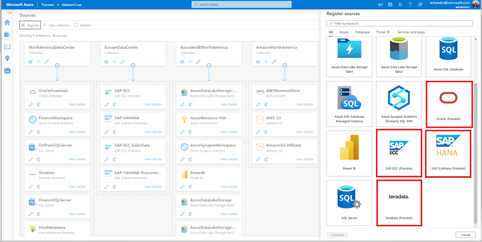
Azure Purview expands on the Non-Microsoft Connectors supportability. In addition to the numerous Azure sources supported today, customers can now register and scan from various databases like Teradata and Oracle. Azure purview also supports ERP sources like SAP S/4HANA and SAP ECC.
Functionalities Supported
1. Register and Scan: Once the sources are registered, customers can now run a full scan on all these sources. For Teradata and Oracle sources, customers can either scan their entire database or scope scans based on schema names.
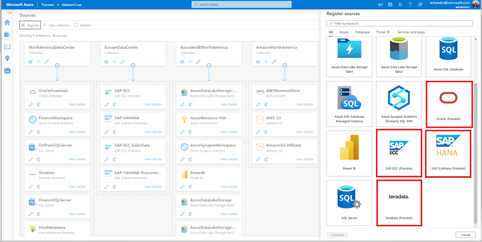
2. Classify: Customers can manually classify the data assets in these sources
3. Lineage: In addition to the lineage obtained from ETL tools like Azure Data factory, Azure Purview can now fetch lineage between the data assets for these sources. As shown below, the SAP View has two tables as upstream sources. The view query used to fetch from these two tables will also be represented in the lineage view.
Permissions and access
- Purview Data Source Administrator can register and trigger scans on these sources.
- In addition, the Data Source Administrator should be a Data Reader or a Data Curator as well.
What’s coming next
Stay tuned for the ability to automatically classify the data from these on-premises sources as we will have more information to share soon!
Get started today!
For detailed information on how to register and setup a scan, please refer to the below how-to-guides:
- Teradata: Register and scan Teradata source
- Oracle: Register and scan Oracle source
- SAP S/4HANA: Register and scan SAP S/4HANA source
- SAP ECC: Register and scan SAP ECC source
by Contributed | Mar 4, 2021 | Technology
This article is contributed. See the original author and article here.
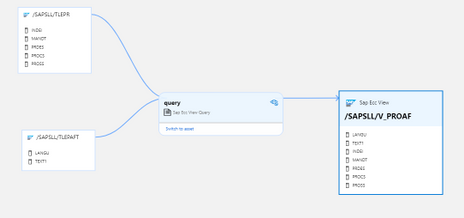
We announce a new feature called Azure Active Directory only authentication for Azure SQL (hereafter “AAD-only auth”). This feature is in public preview and is supported for all Azure SQL SKUs such as Azure SQL Database, Azure Synapse Analytics, Managed Instance (MI) and Hyperscale.
Following the SQL on-premises feature that allows the disabling of SQL authentication and enables only Windows authentication, we developed a similar feature for Azure SQL that allows only Azure AD authentication and disables SQL authentication in the Azure SQL environment.
Behavior in detail
When “AAD-only auth” is active (enabled), it disables SQL authentication, including SQL server admin as well as SQL logins and users, and allows only Azure AD authentication for the Azure SQL server and MI. SQL authentication is disabled at the server level (including all databases) and prevents any authentication (connection to the Azure SQL server and MI) based on any SQL credentials.
Although SQL authentication is disabled, the creation of new SQL logins and users is not blocked. Neither the pre-existing nor newly created SQL accounts will not be allowed to connect to the server. In addition, enabling the AAD-only auth does not remove existing SQL login and user accounts, but it disallows these accounts to connect to Azure SQL server and any database created for this server.
Tooling-support
We support PowerShell, CLI commands, Rest APIs, ARM templates, as well as the Azure portal for SQL Database to enable or disable the AAD-only auth feature. The Azure portal for MI is currently not supported. For more on details on this feature and available interfaces, see the AAD-only-authentication.
Permissions required to enable/disable this feature
To enable or disable the AAD-only auth feature, one of the following built-in roles are required for the AAD users executing these operations: subscription owner, contributor or co-administrator. The required permissions can also be customized by creating custom roles. For more information on Azure built-in roles, see https://docs.microsoft.com/en-us/azure/role-based-access-control/built-in-roles. To allow Azure AD users with lower privileges to set/unset the AAD-only auth feature, the existing built-in role SQL Security Manager was modified to allow these operations for SQL DB and MI. The two Azure SQL built-in roles, SQL Server Contributor (used for SQL DB) and SQL Managed Instance Contributor (used for MI), do not have that permission. This role-separation helps in implementing Separation of Duties, where users who can create an Azure SQL server or create an Azure AD admin, such as SQL Server contributor or SQL Managed Instance Contributor, cannot enable nor disable security features such as AAD-only auth.
Enabling/disabling the AAD-only auth feature using the Azure portal
After assigning an Azure AD user a role discussed above such as SQL Security Manager, the AAD-only auth feature can be enabled using the Azure portal by checking the feature box and saving its action (see below). The AAD-only auth feature using the Azure Portal is currently supported only for SQL DB, and not for MI.
Note that the Azure AD admin must be set for this server to check the feature box.
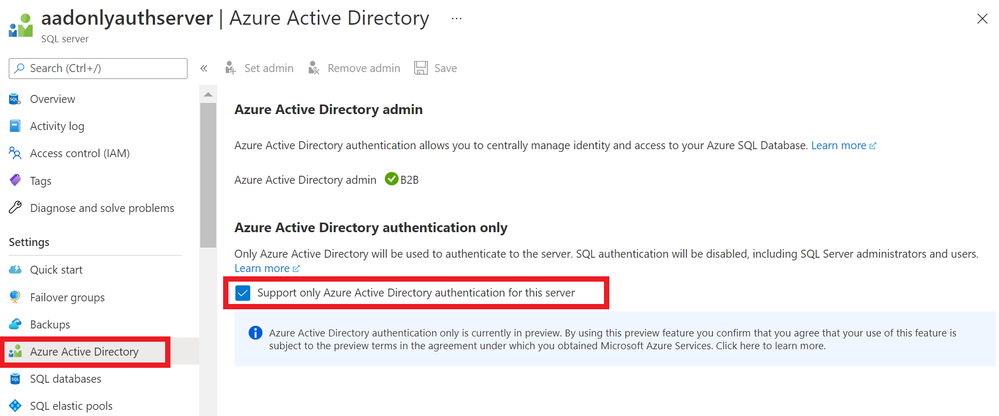
Once the feature is enabled, any attempt to login to this server using SQL authentication fails with an error message indicating the cause of the failure (see below).
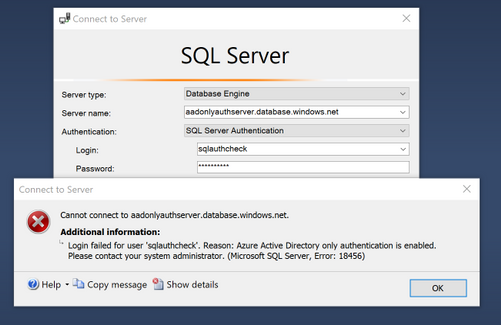
Similarly, the feature box can be unchecked allowing both Azure AD and SQL authentication. In this case, repeating the SQL login using the SSMS example above will succeed.
Limitations
- AAD-only auth is supported at the Azure SQL server level
- This means that when this mode is enabled, all databases that belong to this server can only be accessed using Azure AD authentication
- Enabling AAD-only auth does not remove existing SQL logins or SQL users based on these logins. They continue being stored in SQL metadata, but cannot be used for SQL authentication
- Even though the AAD-only auth is enabled, with proper SQL permissions for Azure AD users, SQL logins and SQL users can be created. However, the authentication process to connect to Azure SQL using such logins/users will fail
- Azure AD users with proper permissions can impersonate existing SQL users
- Impersonation continues working between SQL authentication users even though the AAD-only auth feature is enabled. This is consistent to the way impersonation works today where even disabled users can be impersonated
by Scott Muniz | Mar 4, 2021 | Security
This article was originally posted by the FTC. See the original article here.
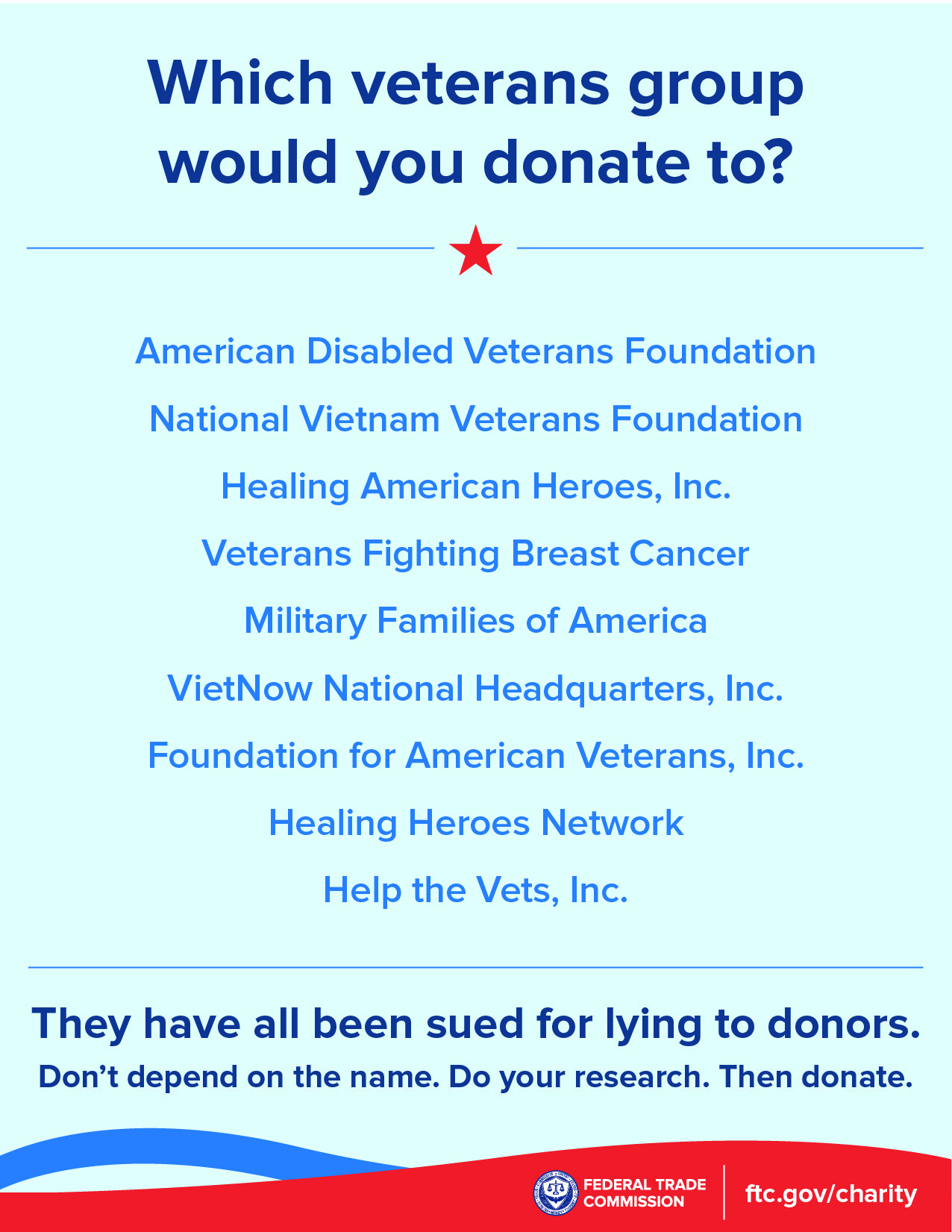
In 2015, the FTC and state partners
sued and shut down four sham charities that harassed millions of people with more than 1.3 billion illegal robocalls about donating to charity. The FTC and 46 charity state regulators from 38 states and the District of Columbia are holding the fundraisers that made those illegal calls accountable in a
lawsuit announced today.
According to the FTC, Associated Community Services (and some related companies and individuals) called more than 67 million people using illegal pre-recorded messages. Those messages falsely claimed the money would go to support breast cancer patients, the families of children with cancer, homeless veterans, and other people in need. In reality, the FTC says that almost none of the more than $110 million donated between 2016 and 2018 went to help those causes.
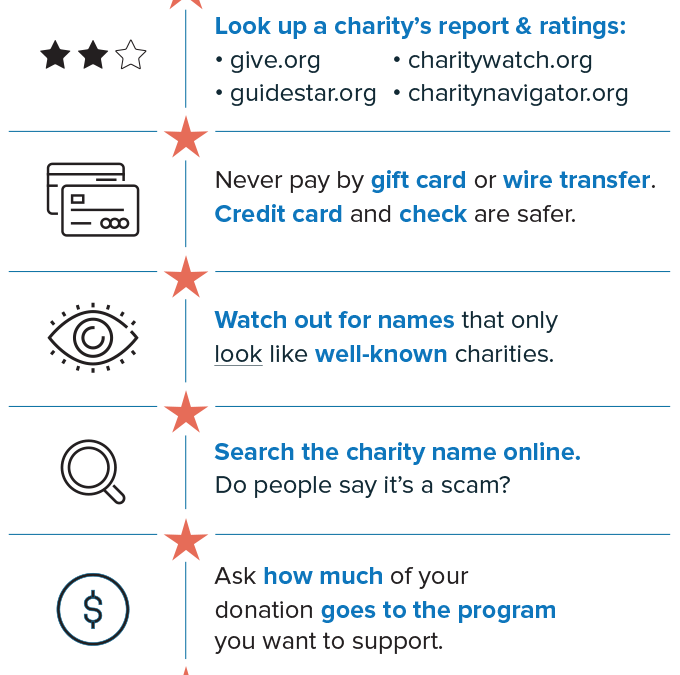
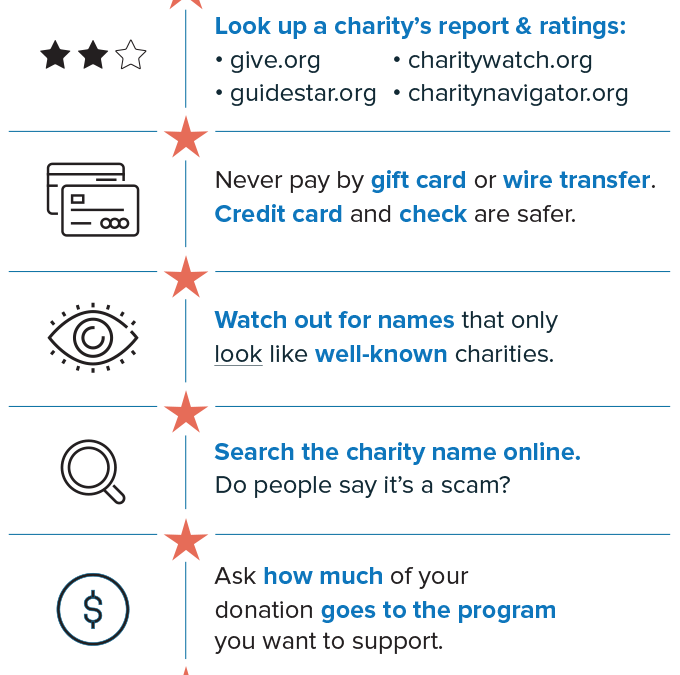
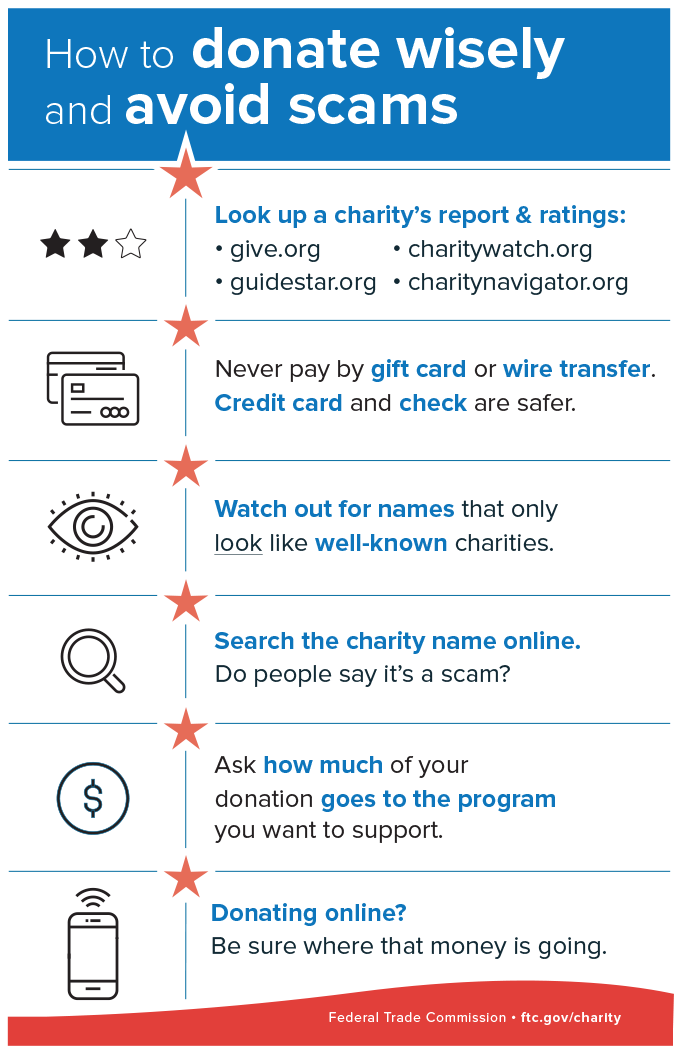
The next time you get a call with a pre-recorded message from charity fundraisers, remember these tips:
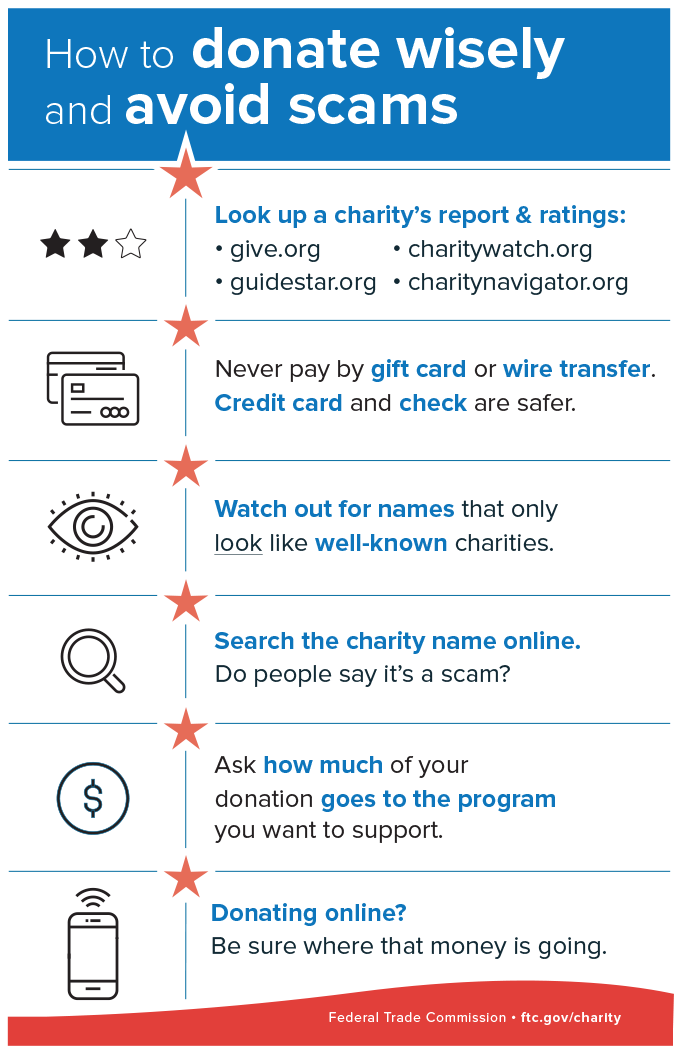
- Don’t trust your caller ID. Dishonest fundraisers can make calls look like they’re from your local area code to get you to answer.
- Hang up if you get a robocall with a pre-recorded message from a charity you don’t know. It’s illegal for a charity to call you with pre-recorded messages, unless you’ve donated to them before. In that case, the caller must tell you that you can opt out of future calls and give you a way to do that.
- Don’t be rushed. A legitimate charity won’t pressure you and will take your donation at any time.
- Ask questions. Ask the fundraiser for the charity’s exact name, web address, and mailing address, so you can confirm it later. And ask exactly how much of your donated dollars will be spent on the charitable cause.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.


Recent Comments