by Contributed | Mar 8, 2021 | Technology
This article is contributed. See the original author and article here.
Last week at Ignite, we made a number of announcements – since the launch of Azure Purview, we have discovered over 14.5 billion data assets in 2000+ Purview accounts. Thank you!
We are debuting a blog series today – “March Ahead with Azure Purview”. This blog series is focused on helping you get the most out of your current Purview implementation. Over the month of March, we will have blogs on best practices, tips and tricks and troubleshooting guidance on topics including Scans, Access, Roles, and Proof-of-Concept planning.
Tell us what other topics you want us to blog about in the comments! The first blog below is intended to help you understand the relationship between Azure Purview and the Apache Atlas Open API ecosystem. Are you planning to use Azure Purview to manage data in Azure Databricks? Read on!
Apache Atlas is a scalable and extensible set of core foundational governance services – enabling enterprises to meet their compliance requirements effectively and efficiently within Hadoop and allows integration with the whole enterprise data ecosystem. The high-level features that Atlas provides are metadata types & instances, classification, lineage, and discovery. Purview provides these capabilities and in most cases, more advanced than what native Atlas provides, while maintaining inter-compatibility with the Atlas API ecosystem. We have added a few APIs like the advanced search capability that enhances functionality over what is available in native Atlas. Let’s dive into this:
The Apache Atlas construct contains 3 fundamental concepts – a type, an entity, and an attribute. A Type in Atlas is a definition of how particular types of metadata objects are stored and accessed. A type represents a collection of attributes that define the properties for that metadata object. An entity in Atlas is a specific value or instance of an Entity Type, and thus represents a specific metadata object in the real world. An attribute represents the properties on an entity. Learn more about the Atlas Type system here.
Setup, Authentication, and using Purview Atlas Endpoints
For an in-depth look at how to set up your development environment for working with Azure Purview’s Atlas REST APIs, review the REST API Tutorial. In short, you will need the following:
- A Service Principal with Data Curator role on your Purview service. Learn about roles here.
- Collect the Purview service’s name.
- Be able to collect an access token from an OAuth2.0 request.
The samples below assume you have completed this setup and have the following environment variables setup.
Get a system Entity’s Metadata with Purview Atlas APIs
A common starting point for using the REST APIs is to get an entity that has already been scanned. By getting an entity through the REST API, you have quick access to the schema, classifications, attributes, and other relationships to the entity.
Start by navigating to the entity you want to get with the API and obtain the GUID from the URL.

You then call the /entity/bulk?guid= endpoint and provide the guid you collected. You could also pass a comma delimited set of guids to retrieve multiple objects.
curl -H “Accept: application/json”
-H “Authorization: Bearer $AUTH_TOKEN”
$ENDPOINT/entity/bulk?guid=e5d12ea7-53a8-4b48-b8a4-61f6f6f60000 | jq .
The response provided contains several key sections including:
- Referred entities: Provides detail about every entity that is referenced. That includes columns in your schema or process entities used in lineage.
- Entities: This provides an array of the entities you asked for in the guid parameter. Each object in this array will have the core properties, attributes, and relationship attributes.
Understanding Type Definitions for system entities
Once you have started exploring the entities you have scanned, you might want to instantiate your own entity based on that type. For example, you scanned an azure sql table but want to be able to programmatically generate your own server, database, schema, tables, and columns. In order to instantiate your own entity for a given type, you must first understand what the required attributes are, and what the other required entities for creation of this entity are.
Part of the response from our GET /entity/bulk?guid call returned a typeName attribute. That type name can be used to retrieve its definition which includes all the attributes we can capture and all the relationship attributes (i.e. the way a database entity relates to a server entity and a column entity relates to a table entity) that are available to the type.
curl -H “Accept: application/json”
-H “Authorization: Bearer $AUTH_TOKEN”
$ENDPOINT/types/entitydef/name/azure_sql_table | jq .
Understanding the Type definition response
The abbreviated response from the azure_sql_table type definition below shows several key features.
- Options.schemaElementsAttribute – The relationship attribute that will be referenced in the schema tab in the Purview UI.
- An array of Attribute Definitions – This defines what attributes we want to collect, the type, whether it is one or many values, the min and max number of values, and whether it’s optional or required.
- superTypes – The type which you are inheriting from, most often it will be DataSet or Process type.
- An array of Relationship Attribute Definitions – These relationships describe how one entity connects to another. A few interesting relationshp attributes for an azure_sql_table include:
- “columns” allows an instance of azure_sql_table to contain reference to an array of azure_sql_columns.
- “dbSchema” points to a single azure_sql_schema. This is a required relationship attribute, you can’t create an azure_sql_table without a database schema.
- “meanings” is available on all entities and it provides the support for adding glossary terms to a given entity.
Here is an example of the response payload:
{
“category”: “ENTITY”,
“guid”: “5f94b8b9-0430-4210-ade2-7b6f7e2d2db4”,
“name”: “azure_sql_table”,
“description”: “azure_sql_table”,
“serviceType”: “Azure SQL Database”,
“options”: {
“schemaElementsAttribute”: “columns”
},
“attributeDefs”: [
{
“name”: “objectType”,
“typeName”: “string”,
“isOptional”: true,
“cardinality”: “SINGLE”,
“valuesMinCount”: 0,
“valuesMaxCount”: 1,
…
},
…
],
“superTypes”: [
“DataSet”
],
“subTypes”: [],
“relationshipAttributeDefs”: [
{
“name”: “dbSchema”,
“typeName”: “azure_sql_schema”,
“isOptional”: false,
“cardinality”: “SINGLE”,
“relationshipTypeName”: “azure_sql_schema_tables”,
…
},
{
“name”: “columns”,
“typeName”: “array<azure_sql_column>”,
“isOptional”: true,
“cardinality”: “SET”,
“relationshipTypeName”: “azure_sql_table_columns”,
…
},
{
“name”: “meanings”,
“typeName”: “array<AtlasGlossaryTerm>”,
“relationshipTypeName”: “AtlasGlossarySemanticAssignment”,
…
},
…
]
}
Creating Your first Custom Type with Purview Atlas APIs
Now that you have learnt about the existing system types in Purview, as a user you might want to create your own type definitions along with creating your own custom lineage. As an example, we are creating our very own Process type to help us represent Lineage between Azure Databricks and existing entities.
Let us start by creating a custom Process entity type for our Databricks notebooks. The JSON below defines a Databricks notebook that has a required “notebook name”, an optional Schedule, and an array of possible parameters for the notebook. Since we are using a super type of Process, we inherit attributes like qualified name and importantly the inputs and outputs attributes, and relationship attributes. Since we are inheriting those attributes, we do not need to specify these attributes in our Type definition.
Here is an example of the request payload:
{“entityDefs”:[{
“category”: “ENTITY”,
“name”: “custom_databricks_notebook_process”,
“superTypes”: [
“Process”
],
“attributeDefs”: [
{
“cardinality”: “SINGLE”,
“includeInNotification”: false,
“isIndexable”: false,
“isOptional”: false,
“isUnique”: false,
“name”: “JobName”,
“typeName”: “string”,
“valuesMaxCount”: 1,
“valuesMinCount”: 0
},
{
“cardinality”: “SINGLE”,
“includeInNotification”: false,
“isIndexable”: false,
“isOptional”: true,
“isUnique”: false,
“name”: “Schedule”,
“typeName”: “string”,
“valuesMaxCount”: 1,
“valuesMinCount”: 0
},
{
“cardinality”: “SET”,
“includeInNotification”: false,
“isIndexable”: false,
“isOptional”: true,
“isUnique”: false,
“name”: “Parameters”,
“typeName”: “array<string>”,
“valuesMaxCount”: 12,
“valuesMinCount”: 0
}
],
“relationshipAttributeDefs”: []
}]
}
Taking that JSON above, we can call the /types/typedefs endpoint and POST this content to our Purview service and create the type.
curl -H “Accept: application/json” -H “Content-type: application/json”
-H “Authorization: Bearer $AUTH_TOKEN”
-X POST –data @path.to.json.file
$ENDPOINT/types/typedefs | jq .
The response will return the completed entity definition.
Using a Custom Type for Custom Lineage and entities
With a custom type for our Databricks Notebook lineage, we need to instantiate our custom entity, and point our input and outputs to existing entities.
The JSON payload below does the following:
- References our custom type.
- We provide a negative number to act as a “dummy guid” that will be translated into a system-assigned guid upon successful upload.
- We provide the required attributes (name, qualifiedName, and our custom JobName).
- Finally, we provide inputs and outputs. In this case, we are demonstrating two ways of referencing existing entities in your Purview data catalog.
- You can pass in a JSON object with key “guid” and the value of the guid itself.
- You can pass in a JSON object with keys type name and unique attributes. Unique attributes is itself a JSON object with qualifiedName as the key.
{“entities”:[{
“typeName”: “custom_databricks_notebook_process”,
“guid”: -2,
“attributes”: {
“name”: “MyNotebook”,
“JobName”: “MyDatabricksJob”,
“qualifiedName”: “custom_dbr://workspace/path/to/notebook”,
“inputs”: [
{
“guid”: “abc-123-456”
}
],
“outputs”: [
{
“typeName”: “azure_sql_table”,
“uniqueAttributes”: {
“qualifiedName”: “mssql://server/database/schema/table”
}
}
]
},
“relationshipAttributes”: {}
}
]}
With that payload body saved, we can POST the JSON to the /entity/bulk endpoint as shown below.
curl -H “Accept: application/json” -H “Content-type: application/json”
-H “Authorization: Bearer $AUTH_TOKEN”
-X POST –data @path.to.json.file
$ENDPOINT/entity/bulk | jq .
The response will tell us if this was a create or an update. In addition, we will get to see the official guid that the entity is assigned to and we can map our “dummy guid” to the official guid using the guidAssignments section of the response.
Here is an example of the request payload:
{
“mutatedEntities”: {
“CREATE”: [
{
“typeName”: “custom_databricks_notebook_process”,
“attributes”: {
“qualifiedName”: “custom_dbr://workspace/path/to/notebook”
},
“lastModifiedTS”: “1”,
“guid”: “3daeee33-0e07-47e0-b877-30225367fc11”
}
]
},
“guidAssignments”: {
“-2”: “3daeee33-0e07-47e0-b877-30225367fc11”
}
}
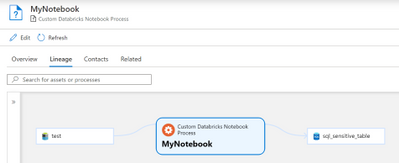
The results of our payload, assuming you had some entities created already, should look like the below Lineage graph when viewing the created custom process entity in the Purview UI.
This works great for existing entities, but if you are uploading new entities at the same time as creating custom entities, you would need to change your input/output “headers” to reference the “dummy guid”.
- Add your desired input / output entities as additional atlas entities to the “entities” array in the above JSON payload.
- Your input / output headers would now have three keys:
- guid: Containing the dummy guid that matches an entity being uploaded.
- typeName: Containing the type of the entity you’re uploading and using as an input/output.
- qualifiedName: Containing the qualified name of the entity you’re uploading and using as an input/output.
Community Driven SDKs
As Purview approaches General Availability, it will provide SDKs and Azure CLI integration. Until then, there are several community driven efforts to make working with the Purview / Atlas APIs easier. One such effort is the PyApacheAtlas project. Let us look at some of these examples above in PyApacheAtlas instead!
Authentication with PyApacheAtlas
Instead of doing the OAuth2.0 dance yourself, you can take advantage of the service principal authentication by passing in your service principal credentials and your purview service account name, and you have a client object that is ready to create types, entities, relationships, and custom lineage.
Here is the sample code to achieve this:
import os
from pyapacheatlas.auth import ServicePrincipalAuthentication
from pyapacheatlas.core.client import PurviewClient
oauth = ServicePrincipalAuthentication(
tenant_id=os.environ.get(“TENANT_ID”, “”),
client_id=os.environ.get(“CLIENT_ID”, “”),
client_secret=os.environ.get(“CLIENT_SECRET”, “”)
)
client = PurviewClient(
account_name=os.environ.get(“PURVIEW_NAME”, “”),
authentication=oauth
)
Getting Types and Entities with PyApacheAtlas
The first thing you will do is get an entity and its type in order to understand how to use that type. In PyApacheAtlas, it’s as simple as calling a couple of methods as shown below
import json
from pyapacheatlas.core.typedef import TypeCategory
# Get the one entity based on its guid
results = client.get_entity(guid=”abc-123-456″)
print(json.dumps(results[“entities”][0], indent=2))
# Get the one type definition
typedefs = client.get_typedef(TypeCategory.ENTITY, name=”azure_sql_table”)
print(json.dumps(typedefs, indent=2))
Creating Types and Entities with PyApacheAtlas
We can quickly create a type and their attributes in PyApacheAtlas. Once the object is created and all the attribute definitions are added, you will call the upload_typdefs method on the client object. Note that the force_update=True parameter will allow us to update the type if it exists already.
Here is the sample code to achieve this:
from pyapacheatlas.core.typedef import EntityTypeDef, AtlasAttributeDef
ed = EntityTypeDef(
name=”custom_databricks_notebook_process”,
superTypes=[“Process”]
)
ed.addAttributeDef(
AtlasAttributeDef(“JobName”, isOptional=False),
AtlasAttributeDef(“Schedule”),
AtlasAttributeDef(“Parameters”, cardinality=”SET”, typeName=”array<string>”, valuesMaxCount=12)
)
type_results = client.upload_typedefs(entityDefs=[ed], force_update=True)
# Now create the custom entity based on this type.
custom_entity = AtlasProcess(
name=”MyNotebook”,
typeName=”custom_databricks_notebook_process”,
qualified_name=”custom_dbr://workspace/path/to/notebook”,
attributs={“JobName”: “MyDatabricksJob”},
# Be sure to change your inputs and outputs before uploading
inputs=[{“guid”: “abc-123-456”}],
outputs=[{
“typeName”: “azure_sql_table”,
“uniqueAttributes”: {
“qualifiedName”: “mssql://server/database/schema/table”
}
}],
)
# Upload the “batch”
entity_results = client.upload_entities(batch=[custom_entity])
Deleting Entities with PyApacheAtlas
Lastly, you can delete entities using the REST API. Use the sample below to clean up your assets from this demonstration, and you have a clean catalog to re-populate!
delete_results = client.delete_entity(guid=”605fb1b1-0ee5-437e-9439-99aea4835127″)
print(json.dumps(delete_results, indent=2))
To learn more about Azure Purview, check out our full documentation today.
by Scott Muniz | Mar 8, 2021 | Security, Technology
This article is contributed. See the original author and article here.
activerecord-session_store — activerecord-session_store
|
The activerecord-session_store (aka Active Record Session Store) component through 1.1.3 for Ruby on Rails does not use a constant-time approach when delivering information about whether a guessed session ID is valid. Consequently, remote attackers can leverage timing discrepancies to achieve a correct guess in a relatively short amount of time. This is a related issue to CVE-2019-16782. |
2021-03-05 |
not yet calculated |
CVE-2019-25025
MISC |
adguard — adguard
|
An issue was discovered in AdGuard before 0.105.2. An attacker able to get the user’s cookie is able to bruteforce their password offline, because the hash of the password is stored in the cookie. |
2021-03-03 |
not yet calculated |
CVE-2021-27935
MISC |
advantech — webaccess/scada
|
An exploitable local privilege elevation vulnerability exists in the file system permissions of Advantech WebAccess/SCADA 9.0.1 installation. In webvrpcs Run Key Privilege Escalation in installation folder of WebAccess, an attacker can either replace binary or loaded modules to execute code with NT SYSTEM privilege. |
2021-03-03 |
not yet calculated |
CVE-2020-13554
MISC |
afterlogic — aurora
|
An issue was discovered in AfterLogic Aurora through 8.5.3 and WebMail Pro through 8.5.3, when DAV is enabled. They allow directory traversal to create new files (such as an executable file under the web root). This is related to DAVServer.php in 8.x and DAV/Server.php in 7.x. |
2021-03-04 |
not yet calculated |
CVE-2021-26293
CONFIRM |
ansi — ansi
|
The npm package ansi_up converts ANSI escape codes into HTML. In ansi_up v4, ANSI escape codes can be used to create HTML hyperlinks. Due to insufficient URL sanitization, this feature is affected by a cross-site scripting (XSS) vulnerability. This issue is fixed in v5.0.0. |
2021-03-05 |
not yet calculated |
CVE-2021-3377
MISC
MISC |
anuko — time_tracker
|
Anuko Time Tracker is an open source, web-based time tracking application written in PHP. In TimeTracker before version 1.19.24.5415 tokens used in password reset feature in Time Tracker are based on system time and, therefore, are predictable. This opens a window for brute force attacks to guess user tokens and, once successful, change user passwords, including that of a system administrator. This vulnerability is pathced in version 1.19.24.5415 (started to use more secure tokens) with an additional improvement in 1.19.24.5416 (limited an available window for brute force token guessing). |
2021-03-03 |
not yet calculated |
CVE-2021-21352
MISC
CONFIRM
MISC |
apache — ambari_views
|
A cross-site scripting issue was found in Apache Ambari Views. This was addressed in Apache Ambari 2.7.4. |
2021-03-02 |
not yet calculated |
CVE-2020-1936
MLIST
CONFIRM |
apache — asterixdb
|
When loading a UDF, a specially crafted zip file could allow files to be placed outside of the UDF deployment directory. This issue affected Apache AsterixDB unreleased builds between commits 580b81aa5e8888b8e1b0620521a1c9680e54df73 and 28c0ee84f1387ab5d0659e9e822f4e3923ddc22d. Note: this CVE may be REJECTed as the issue did not affect any released versions of Apache AsterixDB |
2021-03-01 |
not yet calculated |
CVE-2020-9479
MLIST
MISC |
apache — superset
|
Apache Superset up to and including 0.38.0 allowed the creation of a Markdown component on a Dashboard page for describing chart’s related information. Abusing this functionality, a malicious user could inject javascript code executing unwanted action in the context of the user’s browser. The javascript code will be automatically executed (Stored XSS) when a legitimate user surfs on the dashboard page. The vulnerability is exploitable creating a “div” section and embedding in it a “svg” element with javascript code. |
2021-03-05 |
not yet calculated |
CVE-2021-27907
MISC
MLIST |
argopro — argopro
|
The package github.com/argoproj/argo-cd/cmd before 1.7.13, from 1.8.0 and before 1.8.6 are vulnerable to Cross-site Scripting (XSS) the SSO provider connected to Argo CD would have to send back a malicious error message containing JavaScript to the user. |
2021-03-03 |
not yet calculated |
CVE-2021-23347
CONFIRM
CONFIRM |
| aruba — airwave_management_platform |
A remote authenticated authenticated xml external entity (xxe) vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. Due to improper restrictions on XML entities a vulnerability exists in the web-based management interface of AirWave. A successful exploit could allow an authenticated attacker to retrieve files from the local system or cause the application to consume system resources, resulting in a denial of service condition. |
2021-03-05 |
not yet calculated |
CVE-2021-26969
MISC |
| aruba — airwave_management_platform |
A remote authenticated stored cross-site scripting (xss) vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. A vulnerability in the web-based management interface of AirWave could allow an authenticated remote attacker to conduct a stored cross-site scripting (XSS) attack against a user of the interface. A successful exploit could allow an attacker to execute arbitrary script code in a victim’s browser in the context of the affected interface. |
2021-03-05 |
not yet calculated |
CVE-2021-26968
MISC |
| aruba — airwave_management_platform |
A remote reflected cross-site scripting (xss) vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. A vulnerability in the web-based management interface of AirWave could allow a remote attacker to conduct a reflected cross-site scripting (XSS) attack against a user of certain components of the interface. A successful exploit could allow an attacker to execute arbitrary script code in a victim’s browser in the context of the AirWave management interface. |
2021-03-05 |
not yet calculated |
CVE-2021-26967
MISC |
| aruba — airwave_management_platform |
A remote authenticated sql injection vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. Multiple vulnerabilities in the API of AirWave could allow an authenticated remote attacker to conduct SQL injection attacks against the AirWave instance. An attacker could exploit these vulnerabilities to obtain and modify sensitive information in the underlying database. |
2021-03-05 |
not yet calculated |
CVE-2021-26966
MISC |
| aruba — airwave_management_platform |
A remote authenticated sql injection vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. Multiple vulnerabilities in the API of AirWave could allow an authenticated remote attacker to conduct SQL injection attacks against the AirWave instance. An attacker could exploit these vulnerabilities to obtain and modify sensitive information in the underlying database. |
2021-03-05 |
not yet calculated |
CVE-2021-26965
MISC |
| aruba — airwave_management_platform |
A remote authenticated arbitrary command execution vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. Vulnerabilities in the AirWave CLI could allow remote authenticated users to run arbitrary commands on the underlying host. A successful exploit could allow an attacker to execute arbitrary commands as root on the underlying operating system leading to full system compromise. |
2021-03-05 |
not yet calculated |
CVE-2021-26963
MISC |
| aruba — airwave_management_platform |
A remote authenticated arbitrary command execution vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. Vulnerabilities in the AirWave web-base management interface could allow remote authenticated users to run arbitrary commands on the underlying host. A successful exploit could allow an attacker to execute arbitrary commands as a lower privileged user on the underlying operating system leading to partial system compromise. |
2021-03-05 |
not yet calculated |
CVE-2021-26970
MISC |
| aruba — airwave_management_platform |
A remote authenticated arbitrary command execution vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. Vulnerabilities in the AirWave web-base management interface could allow remote authenticated users to run arbitrary commands on the underlying host. A successful exploit could allow an attacker to execute arbitrary commands as a lower privileged user on the underlying operating system leading to partial system compromise. |
2021-03-05 |
not yet calculated |
CVE-2021-26971
MISC |
aruba — airwave_management_platform
|
A remote authentication restriction bypass vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. A vulnerability in the AirWave web-based management interface could allow an authenticated remote attacker to improperly access and modify devices and management user details. A successful exploit would consist of an attacker using a lower privileged account to change management user or device details. This could allow the attacker to escalate privileges and/or change network details that they should not have access to. |
2021-03-05 |
not yet calculated |
CVE-2021-26964
MISC |
aruba — airwave_management_platform
|
A remote unauthenticated cross-site request forgery (csrf) vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. A vulnerability in the AirWave web-based management interface could allow an unauthenticated remote attacker to conduct a CSRF attack against a vulnerable system. A successful exploit would consist of an attacker persuading an authorized user to follow a malicious link, resulting in arbitrary actions being carried out with the privilege level of the targeted user. |
2021-03-05 |
not yet calculated |
CVE-2021-26960
MISC |
aruba — airwave_management_platform
|
A remote unauthenticated cross-site request forgery (csrf) vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. A vulnerability in the AirWave web-based management interface could allow an unauthenticated remote attacker to conduct a CSRF attack against a vulnerable system. A successful exploit would consist of an attacker persuading an authorized user to follow a malicious link, resulting in arbitrary actions being carried out with the privilege level of the targeted user. |
2021-03-05 |
not yet calculated |
CVE-2021-26961
MISC |
aruba — airwave_management_platform
|
A remote authenticated arbitrary command execution vulnerability was discovered in Aruba AirWave Management Platform version(s): Prior to 8.2.12.0. Vulnerabilities in the AirWave CLI could allow remote authenticated users to run arbitrary commands on the underlying host. A successful exploit could allow an attacker to execute arbitrary commands as root on the underlying operating system leading to full system compromise. |
2021-03-05 |
not yet calculated |
CVE-2021-26962
MISC |
bitnami — containers
|
In Bitnami Containers, all Laravel container versions prior to: 6.20.0-debian-10-r107 for Laravel 6, 7.30.1-debian-10-r108 for Laravel 7 and 8.5.11-debian-10-r0 for Laravel 8, the file /tmp/app/.env is generated at the time that the docker image bitnami/laravel was built, and the value of APP_KEY is fixed under certain conditions. This value is crucial for the security of the application and must be randomly generated per Laravel installation. If your application’s encryption key is in the hands of a malicious party, that party could craft cookie values using the encryption key and exploit vulnerabilities inherent to PHP object serialization / unserialization, such as calling arbitrary class methods within your application. |
2021-03-03 |
not yet calculated |
CVE-2021-21979
MISC |
blackboard — collaborate_ultra
|
Blackboard Collaborate Ultra 20.02 is affected by a cross-site scripting (XSS) vulnerability. The XSS payload will execute on the class room, which leads to stealing cookies from users who join the class. |
2021-03-02 |
not yet calculated |
CVE-2020-25902
MISC
MISC |
cgal — libcal
|
A code execution vulnerability exists in the Nef polygon-parsing functionality of CGAL libcgal CGAL-5.1.1. An oob read vulnerability exists in Nef_S2/SNC_io_parser.h SNC_io_parser::read_sface() sfh->volume(). An attacker can provide malicious input to trigger this vulnerability. |
2021-03-04 |
not yet calculated |
CVE-2020-35636
MISC |
cgal — libcal
|
A code execution vulnerability exists in the Nef polygon-parsing functionality of CGAL libcgal CGAL-5.1.1. An oob read vulnerability exists in Nef_S2/SNC_io_parser.h SNC_io_parser::read_sloop() slh->incident_sface. An attacker can provide malicious input to trigger this vulnerability. |
2021-03-04 |
not yet calculated |
CVE-2020-35628
MISC |
cgal — libcgal
|
A code execution vulnerability exists in the Nef polygon-parsing functionality of CGAL libcgal CGAL-5.1.1. An oob read vulnerability exists in Nef_S2/SNC_io_parser.h SNC_io_parser::read_sloop() slh->twin() An attacker can provide malicious input to trigger this vulnerability. |
2021-03-04 |
not yet calculated |
CVE-2020-28636
MISC |
cgal — libcgal
|
A code execution vulnerability exists in the Nef polygon-parsing functionality of CGAL libcgal CGAL-5.1.1. An oob read vulnerability exists in Nef_2/PM_io_parser.h PM_io_parser::read_vertex() Face_of[] OOB read. An attacker can provide malicious input to trigger this vulnerability. |
2021-03-04 |
not yet calculated |
CVE-2020-28601
MISC |
clustered_data — ontap
|
Clustered Data ONTAP versions prior to 9.3P21, 9.5P16, 9.6P12, 9.7P8 and 9.8 are susceptible to a vulnerability which could allow unauthorized tenant users to discover information related to converting a 7-Mode directory to Cluster-mode such as Storage Virtual Machine (SVM) names, volume names, directory paths and Job IDs. |
2021-03-04 |
not yet calculated |
CVE-2021-26988
MISC |
clustered_data — ontap
|
Clustered Data ONTAP versions prior to 9.3P21, 9.5P16, 9.6P12, 9.7P9 and 9.8 are susceptible to a vulnerability which could allow a remote authenticated attacker to cause a Denial of Service (DoS) on clustered Data ONTAP configured for SMB access. |
2021-03-04 |
not yet calculated |
CVE-2021-26989
MISC |
courier — management_system
|
SQL injection vulnerability was discovered in Courier Management System 1.0, which can be exploited via the ref_no (POST) parameter to admin_class.php |
2021-03-04 |
not yet calculated |
CVE-2020-35327
MISC |
datadog — datadog
|
The Java client for the Datadog API before version 1.0.0-beta.9 has a local information disclosure of sensitive information downloaded via the API using the API Client. The Datadog API is executed on a unix-like system with multiple users. The API is used to download a file containing sensitive information. This sensitive information is exposed locally to other users. This vulnerability exists in the API Client for version 1 and 2. The method `prepareDownloadFilecreates` creates a temporary file with the permissions bits of `-rw-r–r–` on unix-like systems. On unix-like systems, the system temporary directory is shared between users. As such, the contents of the file downloaded via the `downloadFileFromResponse` method will be visible to all other users on the local system. Analysis of the finding determined that the affected code was unused, meaning that the exploitation likelihood is low. The unused code has been removed, effectively mitigating this issue. This issue has been patched in version 1.0.0-beta.9. As a workaround one may specify `java.io.tmpdir` when starting the JVM with the flag `-Djava.io.tmpdir`, specifying a path to a directory with `drw——-` permissions owned by `dd-agent`. |
2021-03-03 |
not yet calculated |
CVE-2021-21331
CONFIRM
CONFIRM |
dell — emc_openmanage_server_administrator
|
Dell EMC OpenManage Server Administrator (OMSA) version 9.5 Microsoft Windows installations with Distributed Web Server (DWS) enabled configuration contains an authentication bypass vulnerability. A remote unauthenticated attacker could potentially exploit this vulnerability to gain admin access on the affected system. |
2021-03-02 |
not yet calculated |
CVE-2021-21513
CONFIRM |
dell — emc_openmanage_server_administrator
|
Dell EMC OpenManage Server Administrator (OMSA) versions 9.5 and prior contain a path traversal vulnerability. A remote user with admin privileges could potentially exploit this vulnerability to view arbitrary files on the target system by sending a specially crafted URL request. |
2021-03-02 |
not yet calculated |
CVE-2021-21514
CONFIRM |
dell — emc_sourceone
|
Dell EMC SourceOne, versions 7.2SP10 and prior, contain a Stored Cross-Site Scripting vulnerability. A remote low privileged attacker may potentially exploit this vulnerability, to hijack user sessions or to trick a victim application user to unknowingly send arbitrary requests to the server. |
2021-03-01 |
not yet calculated |
CVE-2021-21515
MISC |
deutsche — post_mailoptimizer
|
Deutsche Post Mailoptimizer 4.3 before 2020-11-09 allows Directory Traversal via a crafted ZIP archive to the Upload feature or the MO Connect component. This can lead to remote code execution. |
2021-03-05 |
not yet calculated |
CVE-2021-28042
MISC
MISC |
docker — dashboard
|
rakibtg Docker Dashboard before 2021-02-28 allows command injection in backend/utilities/terminal.js via shell metacharacters in the command parameter of an API request. NOTE: this is NOT a Docker, Inc. product. |
2021-03-02 |
not yet calculated |
CVE-2021-27886
MISC
MISC
MISC |
| doctor_appointment_system — doctor_appointment_system |
Cross Site Scripting (XSS) vulnerability in contactus.php in Doctor Appointment System 1.0 allows remote attackers to inject arbitrary web script or HTML via the lastname parameter. |
2021-03-01 |
not yet calculated |
CVE-2021-27318
MISC
MISC |
doctor_appointment_system — doctor_appointment_system
|
Cross Site Scripting (XSS) vulnerability in contactus.php in Doctor Appointment System 1.0 allows remote attackers to inject arbitrary web script or HTML via the comment parameter. |
2021-03-01 |
not yet calculated |
CVE-2021-27317
MISC
MISC |
e107 — e107
|
usersettings.php in e107 through 2.3.0 lacks a certain e_TOKEN protection mechanism. |
2021-03-02 |
not yet calculated |
CVE-2021-27885
MISC
MISC
MISC |
epignosis — efontpro
|
A predictable seed vulnerability exists in the password reset functionality of Epignosis EfrontPro 5.2.21. By predicting the seed it is possible to generate the correct password reset 1-time token. An attacker can visit the password reset supplying the password reset token to reset the password of an account of their choice. |
2021-03-03 |
not yet calculated |
CVE-2020-28597
MISC |
| fastify-reply-form — fastify-reply-form |
fastify-http-proxy is an npm package which is a fastify plugin for proxying your http requests to another server, with hooks. By crafting a specific URL, it is possible to escape the prefix of the proxied backend service. If the base url of the proxied server is `/pub/`, a user expect that accessing `/priv` on the target service would not be possible. In affected versions, it is possible. This is fixed in version 4.3.1. |
2021-03-02 |
not yet calculated |
CVE-2021-21322
MISC
CONFIRM
MISC |
fastify-reply-form — fastify-reply-form
|
fastify-reply-from is an npm package which is a fastify plugin to forward the current http request to another server. In fastify-reply-from before version 4.0.2, by crafting a specific URL, it is possible to escape the prefix of the proxied backend service. If the base url of the proxied server is “/pub/”, a user expect that accessing “/priv” on the target service would not be possible. In affected versions, it is possible. This is fixed in version 4.0.2. |
2021-03-02 |
not yet calculated |
CVE-2021-21321
MISC
CONFIRM
MISC |
| fatek — fvdesigner |
An uninitialized pointer may be exploited in Fatek FvDesigner Version 1.5.76 and prior while the application is processing project files, allowing an attacker to craft a special project file that may permit arbitrary code execution. |
2021-03-03 |
not yet calculated |
CVE-2021-22670
MISC |
fatek — fvdesigner
|
Fatek FvDesigner Version 1.5.76 and prior is vulnerable to an out-of-bounds write while processing project files, allowing an attacker to craft a special project file that may permit arbitrary code execution. |
2021-03-03 |
not yet calculated |
CVE-2021-22683
MISC |
fatek — fvdesigner
|
A use after free issue has been identified in Fatek FvDesigner Version 1.5.76 and prior in the way the application processes project files, allowing an attacker to craft a special project file that may permit arbitrary code execution. |
2021-03-03 |
not yet calculated |
CVE-2021-22662
MISC |
fatek — fvdesigner
|
Fatek FvDesigner Version 1.5.76 and prior is vulnerable to an out-of-bounds read while processing project files, allowing an attacker to craft a special project file that may permit arbitrary code execution. |
2021-03-03 |
not yet calculated |
CVE-2021-22638
MISC |
fatek — fvdesigner
|
Fatek FvDesigner Version 1.5.76 and prior is vulnerable to a stack-based buffer overflow while project files are being processed, allowing an attacker to craft a special project file that may permit arbitrary code execution. |
2021-03-03 |
not yet calculated |
CVE-2021-22666
MISC |
| fork — forkcms |
PHP object injection in the Ajax endpoint of the backend in ForkCMS below version 5.8.3 allows an authenticated remote user to execute malicious code. |
2021-03-04 |
not yet calculated |
CVE-2020-24036
MISC
MISC
MISC |
fortinet — fortigate
|
When traffic other than HTTP/S (eg: SSH traffic, etc…) traverses the FortiGate in version below 6.2.5 and below 6.4.2 on port 80/443, it is not redirected to the transparent proxy policy for processing, as it doesn’t have a valid HTTP header. |
2021-03-04 |
not yet calculated |
CVE-2020-15938
CONFIRM |
fortinet — fortigate
|
An improper neutralization of input vulnerability in FortiGate version 6.2.x below 6.2.5 and 6.4.x below 6.4.1 may allow a remote attacker to perform a stored cross site scripting attack (XSS) via the IPS and WAF logs dashboard. |
2021-03-03 |
not yet calculated |
CVE-2020-15937
CONFIRM |
fortinet — fortiproxy
|
An improper access control vulnerability in FortiProxy SSL VPN portal 2.0.0, 1.2.9 and below versions may allow an authenticated, remote attacker to access internal service such as the ZebOS Shell on the FortiProxy appliance through the Quick Connection functionality. |
2021-03-04 |
not yet calculated |
CVE-2021-22128
CONFIRM |
| fs-path — fs-path |
fs-path node module before 0.0.25 is vulnerable to command injection by way of user-supplied inputs via the `copy`, `copySync`, `remove`, and `removeSync` methods. |
2021-03-04 |
not yet calculated |
CVE-2020-8298
MISC
MISC
MISC |
| gigaset — dx600a_devices |
The telnet administrator service running on port 650 on Gigaset DX600A v41.00-175 devices does not implement any lockout or throttling functionality. This situation (together with the weak password policy that forces a 4-digit password) allows remote attackers to easily obtain administrative access via brute-force attacks. |
2021-03-02 |
not yet calculated |
CVE-2021-25309
MISC |
gigaset — dx600a_devices
|
A buffer overflow vulnerability in the AT command interface of Gigaset DX600A v41.00-175 devices allows remote attackers to force a device reboot by sending relatively long AT commands. |
2021-03-02 |
not yet calculated |
CVE-2021-25306
MISC |
github — enterprise_server
|
A remote code execution vulnerability was identified in GitHub Enterprise Server that could be exploited when building a GitHub Pages site. User-controlled configuration of the underlying parsers used by GitHub Pages were not sufficiently restricted and made it possible to execute commands on the GitHub Enterprise Server instance. To exploit this vulnerability, an attacker would need permission to create and build a GitHub Pages site on the GitHub Enterprise Server instance. This vulnerability affected all versions of GitHub Enterprise Server prior to 2.22.7 and was fixed in 2.22.7, 2.21.15, and 2.20.24. The underlying issues contributing to this vulnerability were identified through the GitHub Security Bug Bounty program. |
2021-03-03 |
not yet calculated |
CVE-2020-10519
MISC
MISC
MISC |
| github — github |
An improper access control vulnerability was identified in GitHub Enterprise Server that allowed an authenticated user with the ability to fork a repository to disclose Actions secrets for the parent repository of the fork. This vulnerability existed due to a flaw that allowed the base reference of a pull request to be updated to point to an arbitrary SHA or another pull request outside of the fork repository. By establishing this incorrect reference in a PR, the restrictions that limit the Actions secrets sent a workflow from forks could be bypassed. This vulnerability affected GitHub Enterprise Server version 3.0.0, 3.0.0.rc2, and 3.0.0.rc1. This vulnerability was reported via the GitHub Bug Bounty program. |
2021-03-03 |
not yet calculated |
CVE-2021-22862
MISC |
| github — github |
An improper access control vulnerability was identified in the GitHub Enterprise Server GraphQL API that allowed authenticated users of the instance to modify the maintainer collaboration permission of a pull request without proper authorization. By exploiting this vulnerability, an attacker would be able to gain access to head branches of pull requests opened on repositories of which they are a maintainer. Forking is disabled by default for organization owned private repositories and would prevent this vulnerability. Additionally, branch protections such as required pull request reviews or status checks would prevent unauthorized commits from being merged without further review or validation. This vulnerability affected all versions of GitHub Enterprise Server since 2.12.22 and was fixed in versions 2.20.24, 2.21.15, 2.22.7 and 3.0.1. This vulnerability was reported via the GitHub Bug Bounty program. |
2021-03-03 |
not yet calculated |
CVE-2021-22863
MISC
MISC
MISC
MISC |
github — github
|
An improper access control vulnerability was identified in GitHub Enterprise Server that allowed authenticated users of the instance to gain write access to unauthorized repositories via specifically crafted pull requests and REST API requests. An attacker would need to be able to fork the targeted repository, a setting that is disabled by default for organization owned private repositories. Branch protections such as required pull request reviews or status checks would prevent unauthorized commits from being merged without further review or validation. This vulnerability affected all versions of GitHub Enterprise Server since 2.4.21 and was fixed in versions 2.20.24, 2.21.15, 2.22.7 and 3.0.1. This vulnerability was reported via the GitHub Bug Bounty program. |
2021-03-03 |
not yet calculated |
CVE-2021-22861
MISC
MISC
MISC
MISC |
| gitlab — gitlab |
An issue has been discovered in GitLab affecting all versions starting with 13.0. Confidential issue titles in Gitlab were readable by an unauthorised user via branch logs. |
2021-03-03 |
not yet calculated |
CVE-2021-22188
CONFIRM
MISC
MISC |
gitlab — gitlab
|
Starting with version 13.7 the Gitlab CE/EE editions were affected by a security issue related to the validation of the certificates for the Fortinet OTP that could result in authentication issues. |
2021-03-04 |
not yet calculated |
CVE-2021-22189
CONFIRM
MISC |
gitlab — gitlab
|
An issue has been discovered in GitLab affecting all versions starting with 11.8. GitLab was vulnerable to a stored XSS in the epics page, which could be exploited with user interactions. |
2021-03-04 |
not yet calculated |
CVE-2021-22183
CONFIRM
MISC
MISC |
gitlab — gitlab
|
An issue has been discovered in GitLab affecting all versions of Gitlab EE/CE before 12.6.7. A potential resource exhaustion issue that allowed running or pending jobs to continue even after project was deleted. |
2021-03-02 |
not yet calculated |
CVE-2021-22187
CONFIRM
MISC |
| glpi — glpi |
GLPI is an open-source asset and IT management software package that provides ITIL Service Desk features, licenses tracking and software auditing. In GLPI from version 9.5.0 and before version 9.5.4, there is a cross-site scripting injection vulnerability when using ajax/kanban.php. This is fixed in version 9.5.4. |
2021-03-02 |
not yet calculated |
CVE-2021-21258
MISC
CONFIRM |
glpi — glpi
|
GLPI is open source software which stands for Gestionnaire Libre de Parc Informatique and it is a Free Asset and IT Management Software package. In GLPI before verison 9.5.4, there is a vulnerability within the document upload function (Home > Management > Documents > Add, or /front/document.form.php endpoint), indeed one of the form field: “Web Link” is not properly sanitized and a malicious user (who has document upload rights) can use it to deliver JavaScript payload. For example if you use the following payload: ” accesskey=”x” onclick=”alert(1)” x=”, the content will be saved within the database without any control. And then once you return to the summary documents page, by clicking on the “Web Link” of the newly created file it will create a new empty tab, but on the initial tab the pop-up “1” will appear. |
2021-03-03 |
not yet calculated |
CVE-2021-21312
MISC
CONFIRM |
glpi — glpi
|
GLPI is open source software which stands for Gestionnaire Libre de Parc Informatique and it is a Free Asset and IT Management Software package. In GLPI before verison 9.5.4, there is a vulnerability in the /ajax/common.tabs.php endpoint, indeed, at least two parameters _target and id are not properly sanitized. Here are two payloads (due to two different exploitations depending on which parameter you act) to exploit the vulnerability:/ajax/common.tabs.php?_target=javascript:alert(document.cookie)&_itemtype=DisplayPreference&_glpi_tab=DisplayPreference$2&id=258&displaytype=Ticket (Payload triggered if you click on the button). /ajax/common.tabs.php?_target=/front/ticket.form.php&_itemtype=Ticket&_glpi_tab=Ticket$1&id=(){};(function%20(){alert(document.cookie);})();function%20a&#. |
2021-03-03 |
not yet calculated |
CVE-2021-21313
MISC
CONFIRM |
glpi — glpi
|
GLPI is open source software which stands for Gestionnaire Libre de Parc Informatique and it is a Free Asset and IT Management Software package. In GLPI before verison 9.5.4, there is an XSS vulnerability involving a logged in user while updating a ticket. |
2021-03-03 |
not yet calculated |
CVE-2021-21314
MISC
CONFIRM |
glpi — glpi
|
GLPI is an open-source asset and IT management software package that provides ITIL Service Desk features, licenses tracking and software auditing. In GLPI version 9.5.3, it was possible to switch entities with IDOR from a logged in user. This is fixed in version 9.5.4. |
2021-03-02 |
not yet calculated |
CVE-2021-21255
MISC
CONFIRM |
grub2 — grub2
|
A flaw was found in grub2 in versions prior to 2.06. Setparam_prefix() in the menu rendering code performs a length calculation on the assumption that expressing a quoted single quote will require 3 characters, while it actually requires 4 characters which allows an attacker to corrupt memory by one byte for each quote in the input. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability. |
2021-03-03 |
not yet calculated |
CVE-2021-20233
MISC |
grub2 — grub2
|
A flaw was found in grub2 in versions prior to 2.06. The option parser allows an attacker to write past the end of a heap-allocated buffer by calling certain commands with a large number of specific short forms of options. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability. |
2021-03-03 |
not yet calculated |
CVE-2021-20225
MISC |
grub2 — grub2
|
A flaw was found in grub2 in versions prior to 2.06. The rmmod implementation allows the unloading of a module used as a dependency without checking if any other dependent module is still loaded leading to a use-after-free scenario. This could allow arbitrary code to be executed or a bypass of Secure Boot protections. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability. |
2021-03-03 |
not yet calculated |
CVE-2020-25632
MISC |
grub2 — grub2
|
A flaw was found in grub2 in versions prior to 2.06. During USB device initialization, descriptors are read with very little bounds checking and assumes the USB device is providing sane values. If properly exploited, an attacker could trigger memory corruption leading to arbitrary code execution allowing a bypass of the Secure Boot mechanism. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability. |
2021-03-03 |
not yet calculated |
CVE-2020-25647
MISC |
grub2 — grub2
|
A flaw was found in grub2 in versions prior to 2.06. Variable names present are expanded in the supplied command line into their corresponding variable contents, using a 1kB stack buffer for temporary storage, without sufficient bounds checking. If the function is called with a command line that references a variable with a sufficiently large payload, it is possible to overflow the stack buffer, corrupt the stack frame and control execution which could also circumvent Secure Boot protections. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability. |
2021-03-03 |
not yet calculated |
CVE-2020-27749
MISC |
grub2 — grub2
|
A flaw was found in grub2 in versions prior to 2.06. The cutmem command does not honor secure boot locking allowing an privileged attacker to remove address ranges from memory creating an opportunity to circumvent SecureBoot protections after proper triage about grub’s memory layout. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability. |
2021-03-03 |
not yet calculated |
CVE-2020-27779
MISC |
gunua — genugate
|
An issue was discovered in genua genugate before 9.0 Z p19, 9.1.x through 9.6.x before 9.6 p7, and 10.x before 10.1 p4. The Web Interfaces (Admin, Userweb, Sidechannel) can use different methods to perform the authentication of a user. A specific authentication method during login does not check the provided data (when a certain manipulation occurs) and returns OK for any authentication request. This allows an attacker to login to the admin panel as a user of his choice, e.g., the root user (with highest privileges) or even a non-existing user. |
2021-03-03 |
not yet calculated |
CVE-2021-27215
MISC
MISC
MISC |
harmonyos — harmonyos
|
A component API of the HarmonyOS 2.0 has a permission bypass vulnerability. Local attackers may exploit this vulnerability to issue commands repeatedly, exhausting system service resources. |
2021-03-02 |
not yet calculated |
CVE-2021-22294
MISC |
harmonyos — harmonyos
|
A component of HarmonyOS 2.0 has a DoS vulnerability. Local attackers may exploit this vulnerability to mount a file system to the target device, causing DoS of the file system. |
2021-03-02 |
not yet calculated |
CVE-2021-22296
MISC
MISC
MISC |
html-parse-stringify — html-parse-stringify
|
This affects the package html-parse-stringify before 2.0.1; all versions of package html-parse-stringify2. Sending certain input could cause one of the regular expressions that is used for parsing to backtrack, freezing the process. |
2021-03-04 |
not yet calculated |
CVE-2021-23346
CONFIRM
CONFIRM
CONFIRM
CONFIRM
CONFIRM
CONFIRM |
ibm — cloud_apm
|
IBM Monitoring (IBM Cloud APM 8.1.4 ) could allow an authenticated user to modify HTML content by sending a specially crafted HTTP request to the APM UI, which could mislead another user. IBM X-Force ID: 187974. |
2021-03-02 |
not yet calculated |
CVE-2020-4725
XF
CONFIRM |
ibm — cloud_apm
|
The IBM Cloud APM 8.1.4 server will issue a DNS request to resolve any hostname specified in the Cloud Event Management Webhook URL configuration definition. This could enable an authenticated user with admin authorization to create DNS query strings that are not hostnames. IBM X-Force ID: 187861. |
2021-03-02 |
not yet calculated |
CVE-2020-4719
XF
CONFIRM |
ibm — cloud_apm
|
The IBM Application Performance Monitoring UI (IBM Cloud APM 8.1.4) allows web pages to be stored locally which can be read by another user on the system. IBM X-Force ID: 187975. |
2021-03-02 |
not yet calculated |
CVE-2020-4726
XF
CONFIRM |
ibm — multiple_products
|
IBM Engineering products are vulnerable to cross-site scripting. This vulnerability allows users to embed arbitrary JavaScript code in the Web UI thus altering the intended functionality potentially leading to credentials disclosure within a trusted session. IBM X-Force ID: 192435. |
2021-03-04 |
not yet calculated |
CVE-2020-4975
XF
CONFIRM |
ibm — security_verify_bridge
|
IBM Security Verify Bridge uses weaker than expected cryptographic algorithms that could allow an attacker to decrypt highly sensitive information. IBM X-Force ID: 196617. |
2021-03-03 |
not yet calculated |
CVE-2021-20441
XF
CONFIRM |
ibm — security_verify_bridge
|
IBM Security Verify Bridge contains hard-coded credentials, such as a password or cryptographic key, which it uses for its own inbound authentication, outbound communication to external components, or encryption of internal data. IBM X-Force ID: 196618. |
2021-03-03 |
not yet calculated |
CVE-2021-20442
XF
CONFIRM |
identitymodel — identitymodel
|
An issue was discovered in IdentityModel (aka ScottBrady.IdentityModel) before 1.3.0. The Branca implementation allows an attacker to modify and forge authentication tokens. |
2021-03-05 |
not yet calculated |
CVE-2020-36255
MISC
MISC
MISC |
joomla! — joomla!
|
An issue was discovered in Joomla! 1.6.0 through 3.9.24. Inadequate filtering of form contents could allow to overwrite the author field. |
2021-03-04 |
not yet calculated |
CVE-2021-26029
MISC |
joomla! — joomla!
|
An issue was discovered in Joomla! 3.0.0 through 3.9.24. Extracting an specifilcy crafted zip package could write files outside of the intended path. |
2021-03-04 |
not yet calculated |
CVE-2021-26028
MISC |
joomla! — joomla!
|
An issue was discovered in Joomla! 3.0.0 through 3.9.24. Incorrect ACL checks could allow unauthorized change of the category for an article. |
2021-03-04 |
not yet calculated |
CVE-2021-26027
MISC |
kentico — the_blog
|
The Blog module in Kentico CMS 5.5 R2 build 5.5.3996 allows SQL injection via the tagname parameter. |
2021-03-05 |
not yet calculated |
CVE-2021-27581
MISC
MISC |
lg — mobile_devices
|
An issue was discovered on LG mobile devices with Android OS 11 software. They mishandle fingerprint recognition because local high beam mode (LHBM) does not function properly during bright illumination. The LG ID is LVE-SMP-210001 (March 2021). |
2021-03-02 |
not yet calculated |
CVE-2021-27901
MISC |
linux — linux_kernel
|
An issue was discovered in the Linux kernel 5.9.x through 5.11.3, as used with Xen. In some less-common configurations, an x86 PV guest OS user can crash a Dom0 or driver domain via a large amount of I/O activity. The issue relates to misuse of guest physical addresses when a configuration has CONFIG_XEN_UNPOPULATED_ALLOC but not CONFIG_XEN_BALLOON_MEMORY_HOTPLUG. |
2021-03-05 |
not yet calculated |
CVE-2021-28039
MLIST
MISC |
linux — linux_kernel
|
An issue was discovered in the Linux kernel through 5.11.3, as used with Xen PV. A certain part of the netback driver lacks necessary treatment of errors such as failed memory allocations (as a result of changes to the handling of grant mapping errors). A host OS denial of service may occur during misbehavior of a networking frontend driver. NOTE: this issue exists because of an incomplete fix for CVE-2021-26931. |
2021-03-05 |
not yet calculated |
CVE-2021-28038
MLIST
MISC |
linux — linux_kernel
|
A NULL pointer dereference flaw was found in the Linux kernel’s GPU Nouveau driver functionality in versions prior to 5.12-rc1 in the way the user calls ioctl DRM_IOCTL_NOUVEAU_CHANNEL_ALLOC. This flaw allows a local user to crash the system. |
2021-03-04 |
not yet calculated |
CVE-2020-25639
MISC |
lumisxp — lumisxp
|
LumisXP (aka Lumis Experience Platform) before 10.0.0 allows unauthenticated blind XXE via an API request to PageControllerXml.jsp. One can send a request crafted with an XXE payload and achieve outcomes such as reading local server files or denial of service. |
2021-03-03 |
not yet calculated |
CVE-2021-27931
MISC |
markdown — markdown
|
markdown2 >=1.0.1.18, fixed in 2.4.0, is affected by a regular expression denial of service vulnerability. If an attacker provides a malicious string, it can make markdown2 processing difficult or delayed for an extended period of time. |
2021-03-03 |
not yet calculated |
CVE-2021-26813
MISC |
matrix-react-sdk — matrix-react-sdk
|
matrix-react-sdk is an npm package which is a Matrix SDK for React Javascript. In matrix-react-sdk before version 3.15.0, the user content sandbox can be abused to trick users into opening unexpected documents. The content is opened with a `blob` origin that cannot access Matrix user data, so messages and secrets are not at risk. This has been fixed in version 3.15.0. |
2021-03-02 |
not yet calculated |
CVE-2021-21320
MISC
MISC
CONFIRM
MISC |
| microsoft — exchange_server |
Microsoft Exchange Server Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-26412, CVE-2021-26854, CVE-2021-26855, CVE-2021-26857, CVE-2021-27065, CVE-2021-27078. |
2021-03-03 |
not yet calculated |
CVE-2021-26858
MISC |
| microsoft — exchange_server |
Microsoft Exchange Server Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-26412, CVE-2021-26854, CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065. |
2021-03-03 |
not yet calculated |
CVE-2021-27078
MISC |
| microsoft — exchange_server |
Microsoft Exchange Server Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-26412, CVE-2021-26854, CVE-2021-26855, CVE-2021-26858, CVE-2021-27065, CVE-2021-27078. |
2021-03-03 |
not yet calculated |
CVE-2021-26857
MISC |
microsoft — exchange_server
|
Microsoft Exchange Server Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-26412, CVE-2021-26854, CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27078. |
2021-03-03 |
not yet calculated |
CVE-2021-27065
MISC |
microsoft — exchange_server
|
Microsoft Exchange Server Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-26854, CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065, CVE-2021-27078. |
2021-03-03 |
not yet calculated |
CVE-2021-26412
MISC |
microsoft — exchange_server
|
Microsoft Exchange Server Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-26412, CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065, CVE-2021-27078. |
2021-03-03 |
not yet calculated |
CVE-2021-26854
MISC |
microsoft — exchange_server
|
Microsoft Exchange Server Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-26412, CVE-2021-26854, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065, CVE-2021-27078. |
2021-03-03 |
not yet calculated |
CVE-2021-26855
MISC |
misp — misp
|
An issue was discovered in app/Model/SharingGroupServer.php in MISP 2.4.139. In the implementation of Sharing Groups, the “all org” flag sometimes provided view access to unintended actors. |
2021-03-02 |
not yet calculated |
CVE-2021-27904
MISC |
mobilewips — mobilewips
|
Calling of non-existent provider in MobileWips application prior to SMR Feb-2021 Release 1 allows unauthorized actions including denial of service attack by hijacking the provider. |
2021-03-02 |
not yet calculated |
CVE-2021-25330
MISC |
mongodb — mongodb_server
|
A user authorized to performing a specific type of query may trigger a denial of service by issuing a generic explain command on a find query. This issue affects: MongoDB Inc. MongoDB Server v4.0 versions prior to 4.0.6; MongoDB Server v3.6 versions prior to 3.6.11. |
2021-03-01 |
not yet calculated |
CVE-2018-25004
MISC |
mongodb — mongodb_server
|
A user authorized to perform database queries may trigger denial of service by issuing specially crafted query contain a type of regex. This issue affects: MongoDB Inc. MongoDB Server v3.6 versions prior to 3.6.21 and MongoDB Server v4.0 versions prior to 4.0.20. |
2021-03-01 |
not yet calculated |
CVE-2020-7929
CONFIRM |
| movable — multiple_products |
Cross-site scripting vulnerability in in Add asset screen of Contents field of Movable Type 7 r.4705 and earlier (Movable Type 7 Series), Movable Type Advanced 7 r.4705 and earlier (Movable Type Advanced 7 Series), Movable Type Premium 1.39 and earlier, and Movable Type Premium Advanced 1.39 and earlier allows remote attackers to inject an arbitrary script via unspecified vectors. |
2021-03-05 |
not yet calculated |
CVE-2021-20665
MISC
MISC |
movable — multiple_products
|
Cross-site scripting vulnerability in in Role authority setting screen of Movable Type 7 r.4705 and earlier (Movable Type 7 Series), Movable Type Advanced 7 r.4705 and earlier (Movable Type Advanced 7 Series), Movable Type 6.7.5 and earlier (Movable Type 6.7 Series), Movable Type Premium 1.39 and earlier, and Movable Type Premium Advanced 1.39 and earlier allows remote attackers to inject an arbitrary script via unspecified vectors. |
2021-03-05 |
not yet calculated |
CVE-2021-20663
MISC
MISC |
movable — multiple_products
|
Cross-site scripting vulnerability in in Asset registration screen of Movable Type 7 r.4705 and earlier (Movable Type 7 Series), Movable Type Advanced 7 r.4705 and earlier (Movable Type Advanced 7 Series), Movable Type 6.7.5 and earlier (Movable Type 6.7 Series), Movable Type Premium 1.39 and earlier, and Movable Type Premium Advanced 1.39 and earlier allows remote attackers to inject an arbitrary script via unspecified vectors. |
2021-03-05 |
not yet calculated |
CVE-2021-20664
MISC
MISC |
msi — dragon_center
|
The MsIo64.sys driver before 1.1.19.1016 in MSI Dragon Center before 2.0.98.0 has a buffer overflow that allows privilege escalation via a crafted 0x80102040, 0x80102044, 0x80102050, or 0x80102054 IOCTL request. |
2021-03-05 |
not yet calculated |
CVE-2021-27965
MISC
MISC |
mymvconnect24 — mymvconnect24
|
An issue was discovered in MB connect line mymbCONNECT24 and mbCONNECT24 software in all versions through V2.6.2. There is an XSS issue in the redirect.php allowing an attacker to inject code via a get parameter. |
2021-03-02 |
not yet calculated |
CVE-2020-12530
CONFIRM |
mymvconnect24 — mymvconnect24
|
An issue was discovered in MB connect line mymbCONNECT24 and mbCONNECT24 software in all versions through V2.6.2 There is a SSRF in the LDAP access check, allowing an attacker to scan for open ports. |
2021-03-02 |
not yet calculated |
CVE-2020-12529
CONFIRM |
mymvconnect24 — mymvconnect24
|
An issue was discovered in MB connect line mymbCONNECT24 and mbCONNECT24 software in all versions through V2.6.2. Improper use of access validation allows a logged in user to kill web2go sessions in the account he should not have access to. |
2021-03-02 |
not yet calculated |
CVE-2020-12528
CONFIRM |
mymvconnect24 — mymvconnect24
|
An issue was discovered in MB connect line mymbCONNECT24 and mbCONNECT24 software in all versions through V2.6.2. Improper use of access validation allows a logged in user to interact with devices in the account he should not have access to. |
2021-03-02 |
not yet calculated |
CVE-2020-12527
CONFIRM |
| netgear — r7800_devices |
This vulnerability allows network-adjacent attackers to execute arbitrary code on affected installations of NETGEAR R7800 firmware version 1.0.2.76. Although authentication is required to exploit this vulnerability, the existing authentication mechanism can be bypassed. The specific flaw exists within the handling of the rc_service parameter provided to apply_save.cgi. The issue results from the lack of proper validation of a user-supplied string before using it to execute a system call. An attacker can leverage this vulnerability to execute code in the context of root. Was ZDI-CAN-12355. |
2021-03-05 |
not yet calculated |
CVE-2021-27256
N/A
N/A |
| netgear — r7800_devices |
This vulnerability allows remote attackers to execute arbitrary code on affected installations of NETGEAR R7800 firmware version 1.0.2.76. Authentication is not required to exploit this vulnerability. The specific flaw exists within the refresh_status.aspx endpoint. The issue results from a lack of authentication required to start a service on the server. An attacker can leverage this vulnerability to execute code in the context of root. Was ZDI-CAN-12360. |
2021-03-05 |
not yet calculated |
CVE-2021-27255
N/A
N/A |
netgear — r7800_devices
|
This vulnerability allows network-adjacent attackers to bypass authentication on affected installations of NETGEAR R7800. Authentication is not required to exploit this vulnerability. The specific flaw exists within the apply_save.cgi endpoint. This issue results from the use of hard-coded encryption key. An attacker can leverage this vulnerability to execute arbitrary code in the context of root. Was ZDI-CAN-12287. |
2021-03-05 |
not yet calculated |
CVE-2021-27254
N/A
N/A |
netgear — r7800_devices
|
This vulnerability allows network-adjacent attackers to compromise the integrity of downloaded information on affected installations of NETGEAR R7800 firmware version 1.0.2.76. Authentication is not required to exploit this vulnerability. The specific flaw exists within the downloading of files via FTP. The issue results from the lack of proper validation of the certificate presented by the server. An attacker can leverage this in conjunction with other vulnerabilities to execute arbitrary code in the context of root. Was ZDI-CAN-12362. |
2021-03-05 |
not yet calculated |
CVE-2021-27257
N/A
N/A |
newlib — newlib
|
A flaw was found in newlib in versions prior to 4.0.0. Improper overflow validation in the memory allocation functions mEMALIGn, pvALLOc, nano_memalign, nano_valloc, nano_pvalloc could case an integer overflow, leading to an allocation of a small buffer and then to a heap-based buffer overflow. |
2021-03-05 |
not yet calculated |
CVE-2021-3420
MISC |
nextcloud — nexcloud_server
|
Nextcloud Server prior to 20.0.6 is vulnerable to reflected cross-site scripting (XSS) due to lack of sanitization in `OC.Notification.show`. |
2021-03-03 |
not yet calculated |
CVE-2021-22878
MISC
MISC
MISC |
nextcloud — nexcloud_server
|
A missing user check in Nextcloud prior to 20.0.6 inadvertently populates a user’s own credentials for other users external storage configuration when not already configured yet. |
2021-03-03 |
not yet calculated |
CVE-2021-22877
MISC
MISC
MISC
MISC |
nextcloud — nextcloud_server
|
Nextcloud Server prior to 20.0.0 stores passwords in a recoverable format even when external storage is not configured. |
2021-03-03 |
not yet calculated |
CVE-2020-8296
MISC
MISC
MISC
MISC |
node.js — node.js
|
Node.js before 10.24.0, 12.21.0, 14.16.0, and 15.10.0 is vulnerable to DNS rebinding attacks as the whitelist includes “localhost6”. When “localhost6” is not present in /etc/hosts, it is just an ordinary domain that is resolved via DNS, i.e., over network. If the attacker controls the victim’s DNS server or can spoof its responses, the DNS rebinding protection can be bypassed by using the “localhost6” domain. As long as the attacker uses the “localhost6” domain, they can still apply the attack described in CVE-2018-7160. |
2021-03-03 |
not yet calculated |
CVE-2021-22884
MISC
MISC
MISC |
node.js — node.js
|
Node.js before 10.24.0, 12.21.0, 14.16.0, and 15.10.0 is vulnerable to a denial of service attack when too many connection attempts with an ‘unknownProtocol’ are established. This leads to a leak of file descriptors. If a file descriptor limit is configured on the system, then the server is unable to accept new connections and prevent the process also from opening, e.g. a file. If no file descriptor limit is configured, then this lead to an excessive memory usage and cause the system to run out of memory. |
2021-03-03 |
not yet calculated |
CVE-2021-22883
MISC
MISC |
online_invoicing_system — online_invoicing_system
|
A CSV injection vulnerability found in Online Invoicing System (OIS) 4.3 and below can be exploited by users to perform malicious actions such as redirecting admins to unknown or harmful websites, or disclosing other clients’ details that the user did not have access to. |
2021-03-03 |
not yet calculated |
CVE-2021-27839
MISC
MISC |
openark — orchestrator
|
resources/public/js/orchestrator.js in openark orchestrator before 3.2.4 allows XSS via the orchestrator-msg parameter. |
2021-03-03 |
not yet calculated |
CVE-2021-27940
MISC
MISC
MISC |
openssh — openssh
|
ssh-agent in OpenSSH before 8.5 has a double free that may be relevant in a few less-common scenarios, such as unconstrained agent-socket access on a legacy operating system, or the forwarding of an agent to an attacker-controlled host. |
2021-03-05 |
not yet calculated |
CVE-2021-28041
MISC
MISC
MISC
MISC |
oracle — cloud_infrastructure_data_science_notebook
|
Vulnerability in the Oracle Cloud Infrastructure Data Science Notebook Sessions. Easily exploitable vulnerability allows low privileged attacker with access to the physical communication segment attached to the hardware where the Oracle Cloud Infrastructure Data Science Notebook Sessions executes to compromise Oracle Cloud Infrastructure Data Science Notebook Sessions. Successful attacks of this vulnerability can result in unauthorized update, insert or delete access to some of Oracle Cloud Infrastructure Data Science Notebook Sessions accessible data as well as unauthorized read access to a subset of Oracle Cloud Infrastructure Data Science Notebook Sessions accessible data. All affected customers were notified of CVE-2021-2138 by Oracle. CVSS 3.1 Base Score 4.6 (Confidentiality and Integrity impacts). CVSS Vector: (CVSS:3.1/AV:A/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:N) |
2021-03-03 |
not yet calculated |
CVE-2021-2138
MISC |
ossec — ossec
|
An issue was discovered in OSSEC 3.6.0. An uncontrolled recursion vulnerability in os_xml.c occurs when a large number of opening and closing XML tags is used. Because recursion is used in _ReadElem without restriction, an attacker can trigger a segmentation fault once unmapped memory is reached. |
2021-03-05 |
not yet calculated |
CVE-2021-28040
MISC |
| pillow — pillow |
Pillow before 8.1.1 allows attackers to cause a denial of service (memory consumption) because the reported size of a contained image is not properly checked for an ICNS container, and thus an attempted memory allocation can be very large. |
2021-03-03 |
not yet calculated |
CVE-2021-27922
MISC |
| pillow — pillow |
Pillow before 8.1.1 allows attackers to cause a denial of service (memory consumption) because the reported size of a contained image is not properly checked for an ICO container, and thus an attempted memory allocation can be very large. |
2021-03-03 |
not yet calculated |
CVE-2021-27923
MISC |
pillow — pillow
|
Pillow before 8.1.1 allows attackers to cause a denial of service (memory consumption) because the reported size of a contained image is not properly checked for a BLP container, and thus an attempted memory allocation can be very large. |
2021-03-03 |
not yet calculated |
CVE-2021-27921
MISC |
pug — pug
|
Pug is an npm package which is a high-performance template engine. In pug before version 3.0.1, if a remote attacker was able to control the `pretty` option of the pug compiler, e.g. if you spread a user provided object such as the query parameters of a request into the pug template inputs, it was possible for them to achieve remote code execution on the node.js backend. This is fixed in version 3.0.1. This advisory applies to multiple pug packages including “pug”, “pug-code-gen”. pug-code-gen has a backported fix at version 2.0.3. This advisory is not exploitable if there is no way for un-trusted input to be passed to pug as the `pretty` option, e.g. if you compile templates in advance before applying user input to them, you do not need to upgrade. |
2021-03-03 |
not yet calculated |
CVE-2021-21353
MISC
MISC
MISC
MISC
CONFIRM
MISC
MISC |
| qcubed — qcubed |
A PHP object injection bug in profile.php in qcubed (all versions including 3.1.1) unserializes the untrusted data of the POST-variable “strProfileData” and allows an unauthenticated attacker to execute code via a crafted POST request. |
2021-03-04 |
not yet calculated |
CVE-2020-24914
MISC
MISC
MISC |
qcubed — qcubed
|
A reflected cross-site scripting (XSS) vulnerability in qcubed (all versions including 3.1.1) in profile.php via the stQuery-parameter allows unauthenticated attackers to steal sessions of authenticated users. |
2021-03-04 |
not yet calculated |
CVE-2020-24912
MISC
MISC
MISC |
readpermutation — readpermutation
|
jpeg-xl v0.3.2 is affected by a heap buffer overflow in /lib/jxl/coeff_order.cc ReadPermutation. When decoding a malicous jxl file using djxl, an attacker can trigger arbitrary code execution or a denial of service. |
2021-03-05 |
not yet calculated |
CVE-2021-28026
MISC |
red_hat — red_hat
|
A flaw was found in grub2 in versions prior to 2.06, where it incorrectly enables the usage of the ACPI command when Secure Boot is enabled. This flaw allows an attacker with privileged access to craft a Secondary System Description Table (SSDT) containing code to overwrite the Linux kernel lockdown variable content directly into memory. The table is further loaded and executed by the kernel, defeating its Secure Boot lockdown and allowing the attacker to load unsigned code. The highest threat from this vulnerability is to data confidentiality and integrity, as well as system availability. |
2021-03-03 |
not yet calculated |
CVE-2020-14372
MISC
MISC |
redis — redis
|
Redis is an open-source, in-memory database that persists on disk. In affected versions of Redis an integer overflow bug in 32-bit Redis version 4.0 or newer could be exploited to corrupt the heap and potentially result with remote code execution. Redis 4.0 or newer uses a configurable limit for the maximum supported bulk input size. By default, it is 512MB which is a safe value for all platforms. If the limit is significantly increased, receiving a large request from a client may trigger several integer overflow scenarios, which would result with buffer overflow and heap corruption. We believe this could in certain conditions be exploited for remote code execution. By default, authenticated Redis users have access to all configuration parameters and can therefore use the “CONFIG SET proto-max-bulk-len” to change the safe default, making the system vulnerable. **This problem only affects 32-bit Redis (on a 32-bit system, or as a 32-bit executable running on a 64-bit system).** The problem is fixed in version 6.2, and the fix is back ported to 6.0.11 and 5.0.11. Make sure you use one of these versions if you are running 32-bit Redis. An additional workaround to mitigate the problem without patching the redis-server executable is to prevent clients from directly executing `CONFIG SET`: Using Redis 6.0 or newer, ACL configuration can be used to block the command. Using older versions, the `rename-command` configuration directive can be used to rename the command to a random string unknown to users, rendering it inaccessible. Please note that this workaround may have an additional impact on users or operational systems that expect `CONFIG SET` to behave in certain ways. |
2021-02-26 |
not yet calculated |
CVE-2021-21309
MISC
MISC
CONFIRM |
rockwell_automation — studio_5000_logix_designer_and_rslogic_5000
|
Rockwell Automation Studio 5000 Logix Designer Versions 21 and later, and RSLogix 5000 Versions 16 through 20 use a key to verify Logix controllers are communicating with Rockwell Automation CompactLogix 1768, 1769, 5370, 5380, 5480: ControlLogix 5550, 5560, 5570, 5580; DriveLogix 5560, 5730, 1794-L34; Compact GuardLogix 5370, 5380; GuardLogix 5570, 5580; SoftLogix 5800. Rockwell Automation Studio 5000 Logix Designer Versions 21 and later and RSLogix 5000: Versions 16 through 20 are vulnerable because an unauthenticated attacker could bypass this verification mechanism and authenticate with Rockwell Automation CompactLogix 1768, 1769, 5370, 5380, 5480: ControlLogix 5550, 5560, 5570, 5580; DriveLogix 5560, 5730, 1794-L34; Compact GuardLogix 5370, 5380; GuardLogix 5570, 5580; SoftLogix 5800. |
2021-03-03 |
not yet calculated |
CVE-2021-22681
MISC |
rust — rust
|
An issue was discovered in the nano_arena crate before 0.5.2 for Rust. There is an aliasing violation in split_at because two mutable references can exist for the same element, if Borrow<Idx> behaves in certain ways. This can have a resultant out-of-bounds write or use-after-free. |
2021-03-05 |
not yet calculated |
CVE-2021-28032
MISC |
samsung — keyboard
|
Improper access control vulnerability in Samsung keyboard version prior to SMR Feb-2021 Release 1 allows physically proximate attackers to change in arbitrary settings during Initialization State. |
2021-03-04 |
not yet calculated |
CVE-2021-25340
MISC
CONFIRM |
samsung — mobile_devices
|
Improper memory access control in RKP in Samsung mobile devices prior to SMR Mar-2021 Release 1 allows an attacker, given a compromised kernel, to write certain part of RKP EL2 memory region. |
2021-03-04 |
not yet calculated |
CVE-2021-25338
MISC
CONFIRM |
samsung — mobile_devices
|
Improper access control in clipboard service in Samsung mobile devices prior to SMR Mar-2021 Release 1 allows untrusted applications to read or write certain local files. |
2021-03-04 |
not yet calculated |
CVE-2021-25337
MISC
CONFIRM |
samsung — mobile_devices
|
Improper address validation in HArx in Samsung mobile devices prior to SMR Mar-2021 Release 1 allows an attacker, given a compromised kernel, to corrupt EL2 memory. |
2021-03-04 |
not yet calculated |
CVE-2021-25339
MISC
CONFIRM |
samsung — mobile_devices
|
Improper input check in wallpaper service in Samsung mobile devices prior to SMR Feb-2021 Release 1 allows untrusted application to cause permanent denial of service. |
2021-03-04 |
not yet calculated |
CVE-2021-25334
MISC
CONFIRM |
samsung — mobile_devices
|
Improper lockscreen status check in cocktailbar service in Samsung mobile devices prior to SMR Mar-2021 Release 1 allows unauthenticated users to access hidden notification contents over the lockscreen in specific condition. |
2021-03-04 |
not yet calculated |
CVE-2021-25335
MISC
CONFIRM |
samsung — mobile_devices
|
Improper access control in NotificationManagerService in Samsung mobile devices prior to SMR Mar-2021 Release 1 allows untrusted applications to acquire notification access via sending a crafted malicious intent. |
2021-03-04 |
not yet calculated |
CVE-2021-25336
MISC
CONFIRM |
| samsung — pay |
Improper access control in Samsung Pay mini application prior to v4.0.14 allows unauthorized access to balance information over the lockscreen via scanning specific QR code. |
2021-03-04 |
not yet calculated |
CVE-2021-25333
MISC
CONFIRM |
| samsung — pay |
Improper access control in Samsung Pay mini application prior to v4.0.14 allows unauthorized access to contacts information over the lockscreen in specific condition. |
2021-03-04 |
not yet calculated |
CVE-2021-25332
MISC
CONFIRM |
samsung — pay
|
Improper access control in Samsung Pay mini application prior to v4.0.14 allows unauthorized access to balance information over the lockscreen in specific condition. |
2021-03-04 |
not yet calculated |
CVE-2021-25331
MISC
CONFIRM |
| samsung — samsung |
Hijacking vulnerability in Samsung Email application version prior to SMR Feb-2021 Release 1 allows attackers to intercept when the provider is executed. |
2021-03-04 |
not yet calculated |
CVE-2021-25347
MISC
CONFIRM |
| samsung — samsung |
A possible arbitrary memory overwrite vulnerabilities in quram library version prior to SMR Jan-2021 Release 1 allow arbitrary code execution. |
2021-03-04 |
not yet calculated |
CVE-2021-25346
MISC
CONFIRM |
samsung — samsung
|
Graphic format mismatch while converting video format in hwcomposer prior to SMR Mar-2021 Release 1 results in kernel panic due to unsupported format. |
2021-03-04 |
not yet calculated |
CVE-2021-25345
MISC
CONFIRM |
samsung — samsung
|
Calling of non-existent provider in Samsung Members prior to version 2.4.81.13 (in Android O(8.1) and below) and 3.8.00.13 (in Android P(9.0) and above) allows unauthorized actions including denial of service attack by hijacking the provider. |
2021-03-04 |
not yet calculated |
CVE-2021-25343
MISC
CONFIRM |
samsung — samsung
|
Missing permission check in knox_custom service prior to SMR Mar-2021 Release 1 allows attackers to gain access to device’s serial number without permission. |
2021-03-04 |
not yet calculated |
CVE-2021-25344
MISC
CONFIRM |
sangoma — asterisk
|
An issue was discovered in channels/chan_sip.c in Sangoma Asterisk through 13.29.1, through 16.6.1, and through 17.0.0; and Certified Asterisk through 13.21-cert4. A SIP request can be sent to Asterisk that can change a SIP peer’s IP address. A REGISTER does not need to occur, and calls can be hijacked as a result. The only thing that needs to be known is the peer’s name; authentication details such as passwords do not need to be known. This vulnerability is only exploitable when the nat option is set to the default, or auto_force_rport. |
2021-03-05 |
not yet calculated |
CVE-2019-18351
MISC
MISC |
| secomea — sitemanager |
Cross-Site Request Forgery (CSRF) vulnerability in web GUI of Secomea GateManager allows an attacker to execute malicious code. This issue affects: Secomea GateManager All versions prior to 9.4. |
2021-03-05 |
not yet calculated |
CVE-2020-29030
MISC |
secomea — sitemanager
|
Cross-site Scripting (XSS) vulnerability in web GUI of Secomea GateManager allows an attacker to inject arbitrary javascript code. This issue affects: Secomea GateManager all versions prior to 9.4. |
2021-03-05 |
not yet calculated |
CVE-2020-29028
MISC |
secomea — sitemanager
|
Improper Input Validation, Cross-site Scripting (XSS) vulnerability in Web GUI of Secomea GateManager allows an attacker to execute arbitrary javascript code. This issue affects: Secomea GateManager all versions prior to 9.4. |
2021-03-05 |
not yet calculated |
CVE-2020-29029
MISC |
secomea — sitemanager
|
Upload of Code Without Integrity Check vulnerability in firmware archive of Secomea GateManager allows authenticated attacker to execute malicious code on server. This issue affects: Secomea GateManager all versions prior to 9.4.621054022 |
2021-03-05 |
not yet calculated |
CVE-2020-29032
MISC |
secomea — sitemanager
|
Improper Access Control vulnerability in web service of Secomea SiteManager allows remote attacker to access the web UI from the internet using the configured credentials. This issue affects: Secomea SiteManager All versions prior to 9.4.620527004 on Hardware. |
2021-03-05 |
not yet calculated |
CVE-2020-29020
MISC |
slic3r — slic3r
|
An out-of-bounds read vulnerability exists in the AMF File AMFParserContext::endElement() functionality of Slic3r libslic3r 1.3.0 and Master Commit 92abbc42. A specially crafted AMF file can lead to information disclosure. An attacker can provide a malicious file to trigger this vulnerability. |
2021-03-03 |
not yet calculated |
CVE-2020-28591
MISC |
smp — smp
|
Calling of non-existent provider in SMP sdk prior to version 3.0.9 allows unauthorized actions including denial of service attack by hijacking the provider. |
2021-03-04 |
not yet calculated |
CVE-2021-25342
MISC
CONFIRM |
sonicwall — sonicwall
|
SonicWall SSO-agent default configuration uses NetAPI to probe the associated IP’s in the network, this client probing method allows a potential attacker to capture the password hash of the privileged user and potentially forces the SSO Agent to authenticate allowing an attacker to bypass firewall access controls. |
2021-03-05 |
not yet calculated |
CVE-2020-5148
CONFIRM |
| sonlogger — sonlogger |
SonLogger before 6.4.1 is affected by Unauthenticated Arbitrary File Upload. An attacker can send a POST request to /Config/SaveUploadedHotspotLogoFile without any authentication or session header. There is no check for the file extension or content of the uploaded file. |
2021-03-05 |
not yet calculated |
CVE-2021-27964
MISC
MISC |
sonlogger — sonlogger
|
SonLogger before 6.4.1 is affected by user creation with any user permissions profile (e.g., SuperAdmin). An anonymous user can send a POST request to /User/saveUser without any authentication or session header. |
2021-03-05 |
not yet calculated |
CVE-2021-27963
MISC
MISC |
| spire — spire |
In SPIRE before versions 0.8.5, 0.9.4, 0.10.2, 0.11.3 and 0.12.1, the “aws_iid” Node Attestor improperly normalizes the path provided through the agent ID templating feature, which may allow the issuance of an arbitrary SPIFFE ID within the same trust domain, if the attacker controls the value of an EC2 tag prior to attestation, and the attestor is configured for agent ID templating where the tag value is the last element in the path. This issue has been fixed in SPIRE versions 0.11.3 and 0.12.1 |
2021-03-05 |
not yet calculated |
CVE-2021-27099
MISC |
spire — spire
|
In SPIRE 0.8.1 through 0.8.4 and before versions 0.9.4, 0.10.2, 0.11.3 and 0.12.1, specially crafted requests to the FetchX509SVID RPC of SPIRE Server’s Legacy Node API can result in the possible issuance of an X.509 certificate with a URI SAN for a SPIFFE ID that the agent is not authorized to distribute. Proper controls are in place to require that the caller presents a valid agent certificate that is already authorized to issue at least one SPIFFE ID, and the requested SPIFFE ID belongs to the same trust domain, prior to being able to trigger this vulnerability. This issue has been fixed in SPIRE versions 0.8.5, 0.9.4, 0.10.2, 0.11.3 and 0.12.1. |
2021-03-05 |
not yet calculated |
CVE-2021-27098
MISC |
spring-integration-zip — spring-integration-zip
|
Addresses partial fix in CVE-2018-1263. Spring-integration-zip, versions prior to 1.0.4, exposes an arbitrary file write vulnerability, that can be achieved using a specially crafted zip archive (affects other archives as well, bzip2, tar, xz, war, cpio, 7z), that holds path traversal filenames. So when the filename gets concatenated to the target extraction directory, the final path ends up outside of the target folder. |
2021-03-01 |
not yet calculated |
CVE-2021-22114
MISC |
squarebox — catdv_server
|
An issue was discovered in SquareBox CatDV Server through 9.2. An attacker can invoke sensitive RMI methods such as getConnections without authentication, the results of which can be used to generate valid authentication tokens. These tokens can then be used to invoke administrative tasks within the application, such as disclosing password hashes. |
2021-03-05 |
not yet calculated |
CVE-2021-26705
MISC |
srs — policy_manager
|
SRS Policy Manager 6.X is affected by an XML External Entity Injection (XXE) vulnerability due to a misconfigured XML parser that processes user-supplied DTD input without sufficient validation. A remote unauthenticated attacker can potentially exploit this vulnerability to read system files as a non-root user and may be able to temporarily disrupt the ESRS service. |
2021-03-01 |
not yet calculated |
CVE-2021-21517
MISC |
stormshield — network_security
|
A vulnerability in Stormshield Network Security could allow an attacker to trigger a protection related to ARP/NDP tables management, which would temporarily prevent the system to contact new hosts via IPv4 or IPv6. This affects versions 2.0.0 to 2.7.7, 2.8.0 to 2.16.0, 3.0.0 to 3.7.16, 3.8.0 to 3.11.4, and 4.0.0 to 4.1.5. Fixed in versions 2.7.8, 3.7.17, 3.11.5, and 4.2.0. |
2021-03-02 |
not yet calculated |
CVE-2021-3384
CONFIRM |
suse — linux_enterprise_server
|
A Incorrect Implementation of Authentication Algorithm vulnerability in of SUSE SUSE Linux Enterprise Server 15 SP 3; openSUSE Tumbleweed allows local attackers to execute arbitrary code via salt without the need to specify valid credentials. This issue affects: SUSE SUSE Linux Enterprise Server 15 SP 3 salt versions prior to 3002.2-3. openSUSE Tumbleweed salt version 3002.2-2.1 and prior versions. |
2021-03-03 |
not yet calculated |
CVE-2021-25315
CONFIRM |
suse — rancher
|
A Improper Neutralization of Input During Web Page Generation (‘Cross-site Scripting’) vulnerability in Rancher allows remote attackers to execute JavaScript via malicious links. This issue affects: SUSE Rancher Rancher versions prior to 2.5.6. |
2021-03-05 |
not yet calculated |
CVE-2021-25313
CONFIRM
CONFIRM
CONFIRM |
tenable.sc — core
|
Tenable.sc and Tenable.sc Core versions 5.13.0 through 5.17.0 were found to contain a vulnerability that could allow an authenticated, unprivileged user to perform Remote Code Execution (RCE) on the Tenable.sc server via Hypertext Preprocessor unserialization. |
2021-03-03 |
not yet calculated |
CVE-2021-20076
MISC |
thinkadmin — thinkadmin
|
ThinkAdmin v6 has default administrator credentials, which allows attackers to gain unrestricted administratior dashboard access. |
2021-03-03 |
not yet calculated |
CVE-2020-35296
MISC
MISC
MISC |
totvs — fluig_luke
|
TOTVS Fluig Luke 1.7.0 allows directory traversal via a base64 encoded file=../ to a volume/stream/ URI. This affects: Fluig Lake 1.7.0-210217, Fluig Lake 1.7.0-210112, Fluig Lake 1.7.0-201215, Fluig Lake 1.7.0-201124 and Fluig Lake 1.7.0-200915. |
2021-03-05 |
not yet calculated |
CVE-2020-29134
MISC
MISC |
trend_micro — virus_scan_api_and_advanced_threat_scan_engine
|
Trend Micro’s Virus Scan API (VSAPI) and Advanced Threat Scan Engine (ATSE) – are vulnerable to a memory exhaustion vulnerability that may lead to denial-of-service or system freeze if exploited by an attacker using a specially crafted file. |
2021-03-03 |
not yet calculated |
CVE-2021-25252
MISC |
ultimatekode — neo_billing
|
Cross Site Scripting (XSS) vulnerability in UltimateKode Neo Billing – Accounting, Invoicing And CRM Software up to version 3.5 which allows remote attackers to inject arbitrary web script or HTML. |
2021-03-02 |
not yet calculated |
CVE-2020-23518
MISC |
veritas — backup_exec
|
An issue was discovered in Veritas Backup Exec before 21.2. The communication between a client and an Agent requires successful authentication, which is typically completed over a secure TLS communication. However, due to a vulnerability in the SHA Authentication scheme, an attacker is able to gain unauthorized access and complete the authentication process. Subsequently, the client can execute data management protocol commands on the authenticated connection. The attacker could use one of these commands to execute an arbitrary command on the system using system privileges. |
2021-03-01 |
not yet calculated |
CVE-2021-27878
MISC |
veritas — backup_exec
|
An issue was discovered in Veritas Backup Exec before 21.2. It supports multiple authentication schemes: SHA authentication is one of these. This authentication scheme is no longer used in current versions of the product, but hadn’t yet been disabled. An attacker could remotely exploit this scheme to gain unauthorized access to an Agent and execute privileged commands. |
2021-03-01 |
not yet calculated |
CVE-2021-27877
MISC |
veritas — backup_exec
|
An issue was discovered in Veritas Backup Exec before 21.2. The communication between a client and an Agent requires successful authentication, which is typically completed over a secure TLS communication. However, due to a vulnerability in the SHA Authentication scheme, an attacker is able to gain unauthorized access and complete the authentication process. Subsequently, the client can execute data management protocol commands on the authenticated connection. By using crafted input parameters in one of these commands, an attacker can access an arbitrary file on the system using System privileges. |
2021-03-01 |
not yet calculated |
CVE-2021-27876
MISC |
vmware — view_planner
|
VMware View Planner 4.x prior to 4.6 Security Patch 1 contains a remote code execution vulnerability. Improper input validation and lack of authorization leading to arbitrary file upload in logupload web application. An unauthorized attacker with network access to View Planner Harness could upload and execute a specially crafted file leading to remote code execution within the logupload container. |
2021-03-03 |
not yet calculated |
CVE-2021-21978
MISC |
wazuh — wazuh
|
Wazuh API in Wazuh from 4.0.0 to 4.0.3 allows authenticated users to execute arbitrary code with administrative privileges via /manager/files URI. An authenticated user to the service may exploit incomplete input validation on the /manager/files API to inject arbitrary code within the API service script. |
2021-03-06 |
not yet calculated |
CVE-2021-26814
MISC
MISC |
webkit — webkitgtk
|
A code execution vulnerability exists in the AudioSourceProviderGStreamer functionality of Webkit WebKitGTK 2.30.1. A specially crafted web page can lead to a use after free. |
2021-03-03 |
not yet calculated |
CVE-2020-13558
MISC |
wordpress — wordpress
|
The wp-hotel-booking plugin through 1.10.2 for WordPress allows remote attackers to execute arbitrary code because of an unserialize operation on the thimpress_hotel_booking_1 cookie in load in includes/class-wphb-sessions.php. |
2021-03-03 |
not yet calculated |
CVE-2020-29047
MISC
MISC |
wps_hide_login — wps_hide_login
|
WPS Hide Login 1.6.1 allows remote attackers to bypass a protection mechanism via post_password. |
2021-03-01 |
not yet calculated |
CVE-2021-3332
MISC |
xerox — altalink
|
Xerox AltaLink B8045/B8055/B8065/B8075/B8090 and C8030/C8035/C8045/C8055/C8070 multifunction printers with software releases before 101.00x.099.28200 allow an attacker to execute an unwanted binary during a exploited clone install. This requires creating a clone file and signing that file with a compromised private key. |
2021-03-04 |
not yet calculated |
CVE-2019-18629
MISC
CONFIRM |
xerox — altalink
|
On Xerox AltaLink B8045/B8055/B8065/B8075/B8090 and C8030/C8035/C8045/C8055/C8070 multifunction printers with software releases before 101.00x.099.28200, portions of the drive containing executable code were not encrypted thus leaving it open to potential cryptographic information disclosure. |
2021-03-04 |
not yet calculated |
CVE-2019-18630
MISC |
xmlhttprequest — xmlhttprequest
|
This affects the package xmlhttprequest before 1.7.0; all versions of package xmlhttprequest-ssl. Provided requests are sent synchronously (async=False on xhr.open), malicious user input flowing into xhr.send could result in arbitrary code being injected and run. |
2021-03-05 |
not yet calculated |
CVE-2020-28502
MISC
MISC
MISC
MISC
MISC |
| ymfe — yapi |
Weak JSON Web Token (JWT) signing secret generation in YMFE YApi through 1.9.2 allows recreation of other users’ JWT tokens. This occurs because Math.random in Node.js is used. |
2021-03-01 |
not yet calculated |
CVE-2021-27884
MISC
MISC |
ytnef — ytnef
|
In ytnef 1.9.3, the SwapWord function in lib/ytnef.c allows remote attackers to cause a denial-of-service (and potentially code execution) due to a heap buffer overflow which can be triggered via a crafted file. |
2021-03-04 |
not yet calculated |
CVE-2021-3404
MISC
MISC |
ytnef — ytnef
|
In ytnef 1.9.3, the TNEFSubjectHandler function in lib/ytnef.c allows remote attackers to cause a denial-of-service (and potentially code execution) due to a double free which can be triggered via a crafted file. |
2021-03-04 |
not yet calculated |
CVE-2021-3403
MISC
MISC |
yubico — yubihsm-shell
|
An issue was discovered in the _send_secure_msg() function of Yubico yubihsm-shell through 2.0.3. The function does not correctly validate the embedded length field of an authenticated message received from the device. Out-of-bounds reads performed by aes_remove_padding() can crash the running process, depending on the memory layout. This could be used by an attacker to cause a client-side denial of service. The yubihsm-shell project is included in the YubiHSM 2 SDK product. |
2021-03-04 |
not yet calculated |
CVE-2021-27217
MISC
CONFIRM |
zabbix — zabbix
|
In Zabbix before 4.0.28rc1, 5.x before 5.0.8rc1, 5.1.x and 5.2.x before 5.2.4rc1, and 5.3.x and 5.4.x before 5.4.0alpha1, the CControllerAuthenticationUpdate controller lacks a CSRF protection mechanism. The code inside this controller calls diableSIDValidation inside the init() method. |
2021-03-03 |
not yet calculated |
CVE-2021-27927
MISC |
zendto — zendto
|
ZendTo before 6.06-4 Beta allows XSS during the display of a drop-off in which a filename has unexpected characters. |
2021-03-02 |
not yet calculated |
CVE-2021-27888
MISC |
zint — barcode_generator
|
ean_leading_zeroes in backend/upcean.c in Zint Barcode Generator 2.9.1 has a stack-based buffer overflow that is reachable from the C API through an application that includes the Zint Barcode Generator library code. |
2021-02-26 |
not yet calculated |
CVE-2021-27799
MISC
MISC
MISC
MISC
MISC |
zoho — manageengine_admanager_plus
|
Zoho ManageEngine ADManager Plus before 7066 allows XSS. |
2021-03-05 |
not yet calculated |
CVE-2020-35594
MISC |
zoho — manageengine_application_control_plus
|
Zoho ManageEngine Application Control Plus before 100523 has an insecure SSL configuration setting for Nginx, leading to Privilege Escalation. |
2021-03-05 |
not yet calculated |
CVE-2020-29658
MISC |
zoho — manageengine_desktop_central
|
Zoho ManageEngine Desktop Central before build 10.0.647 allows a single authentication secret from multiple agents to communicate with the server. |
2021-03-05 |
not yet calculated |
CVE-2020-28050
CONFIRM
CONFIRM |
zstd — zstd
|
In the Zstandard command-line utility prior to v1.4.1, output files were created with default permissions. Correct file permissions (matching the input) would only be set at completion time. Output files could therefore be readable or writable to unintended parties. |
2021-03-04 |
not yet calculated |
CVE-2021-24031
MISC
MISC
MISC |
zstd — zstd
|
Beginning in v1.4.1 and prior to v1.4.9, due to an incomplete fix for CVE-2021-24031, the Zstandard command-line utility created output files with default permissions and restricted those permissions immediately afterwards. Output files could therefore momentarily be readable or writable to unintended parties. |
2021-03-04 |
not yet calculated |
CVE-2021-24032
MISC
MISC
MISC |
zte — zte
|
A ZTE product has an information leak vulnerability. An attacker with higher authority can go beyond their authority to access files in other directories by performing specific operations, resulting in information leak. This affects: ZXHN H196Q V9.1.0C2. |
2021-03-05 |
not yet calculated |
CVE-2021-21725
MISC |

by Contributed | Mar 8, 2021 | Technology
This article is contributed. See the original author and article here.

Dear IT Pros,
Today we discuss about MBAM’s Bitlocker data migration to MEM
Microsoft provides a range of flexible BitLocker management alternatives to meet organization’s needs, as follows:
- Cloud-based BitLocker management using Microsoft Endpoint Manager.
- On-premises BitLocker management using System Center Configuration Manager
- Microsoft BitLocker Administration and Monitoring (MBAM) ended support on 7/9/2019, extended support 4/14/2026.
To future proof the Bitlocker Management and simplify the administration, some corporates have planned to migrate MBAM data directly from MBAM servers to Microsoft Endpoint Manager. The key point of the migration is that, making sure the amount number of recovery keys listed by MBAM Server are the same as the ones listed by Azure AD before the cut-off point of time in the migration process.
Migration steps:
- Generate a list of Bitlocker recovery keys in MBAM SQL Server
- Setup MEM Policy to escrow Bitlocker recovery passwords to Azure AD Device Accounts.
- Generate a list of Bitlocker recovery keys by Graph API in Azure AD, also generate a list of devices failed to escrow their keys
- Compare list and make manually escrow of recovery keys to Azure AD
- Shutdown MBAM Server and decommission them.
Now we would look into the detail steps.
- Generate a list of Bitlocker recovery keys in MBAM SQL Server:
- To backup the recovery keys by SQL:
Open the SQL Management Studio, and Expand the MBAM_Recovery_and_Hardware database.
- Under Tables, Select RecoveryAndHardwareCore.Keys.
- Right-Click RecoveryAndHardwareCore.Keys, and Select Top 1000 Rows.
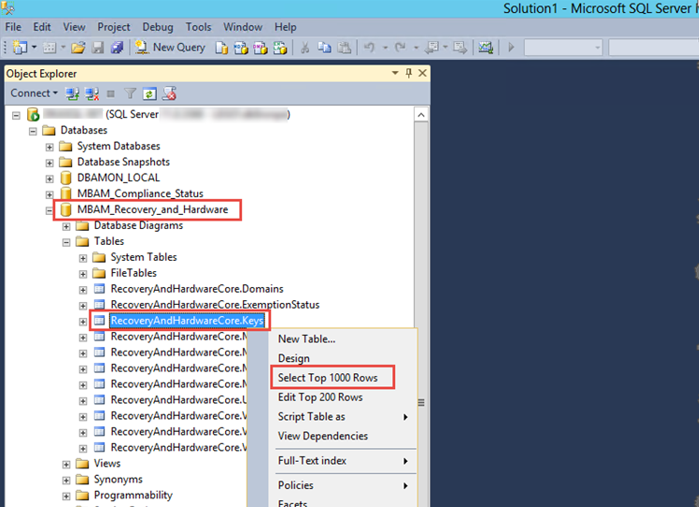
- This should create a query that will give you a list of all RevoveryKeyID’s and RecoveryKey’s in the Database.
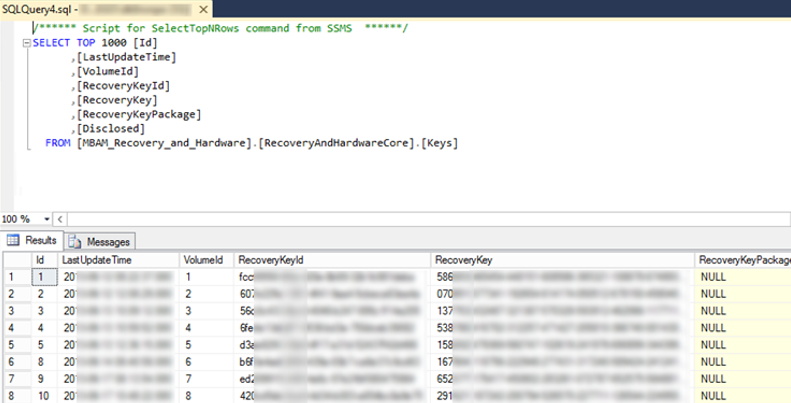
You could modify the above query for more rows with SELECT TOP nnnnn instead of 1000 (rows)
2 Setup MEM Policy to escrow Bitlocker recovery passwords to Azure AD Device Accounts.
2.1 Make 2 device groups: Bitlocker GPO devices and Bitlocker MEM devices
During the transition period, you will migrating batch by batch the devices from the “Bitlocker GPO devices group” to the “Bitlocker MEM devices group”.
2.2 Manage BitLocker using Microsoft Endpoint Manager – Intune
In Microsoft Endpoint Manager admin center.
- Select Endpoint security > Disk encryption, and then
- Create policy. Enter in the Platform and Profile indicated in the screen capture below, and then select Create.
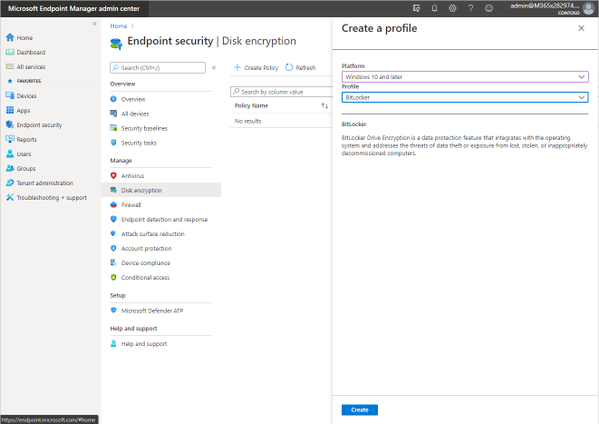
creating a new Microsoft BitLocker policy in Microsoft Endpoint Manager
- Next, enter the basics, such as the name of the policy and an optional description, then move on to Configuration settings. Notice you can search for a specific setting, like “fixed drive policy,” or you can scroll through the settings. Also notice the options offered for key rotation. This setting, which requires Windows 10, version 1909 or later, will change the recovery key when the recovery key is used to unlock a drive.
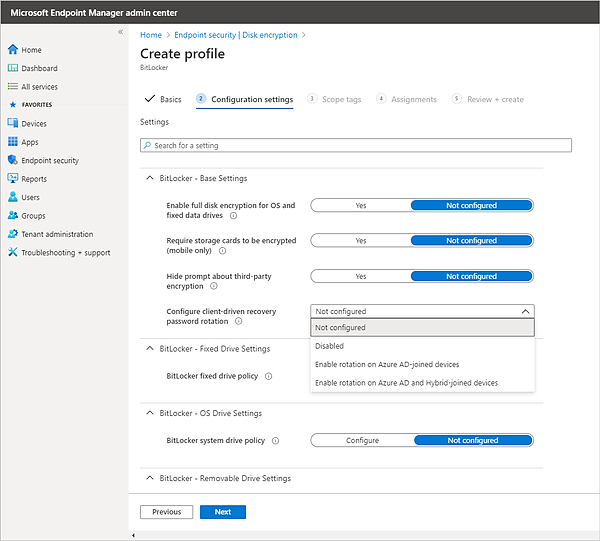
Create an Endpoint Security profile in Microsoft Endpoint Manager
- As you enable settings, additional settings may appear. For example, Enabling Fixed drive encryption expands more options: Recovery key file creation and Configure BitLocker recovery key package.
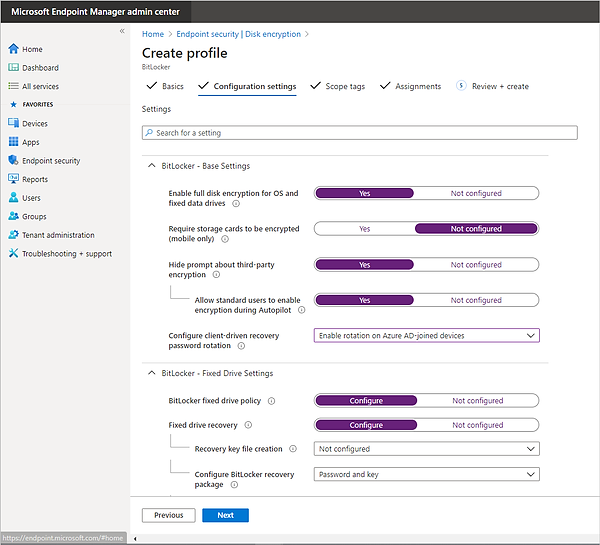
Configuring BitLocker settings in Microsoft Endpoint Manager
- Finally, add Scope tags, assign the new policy to the “Bitlocker MEM devices” group, and select Create.
The settings that can be configured here include:
- BitLocker – Base Settings
- Enable full disk encryption for OS and fixed data drives
- Require storage cards to be encrypted (mobile only)
- Hide Prompt about third-party encryption
- Configure client-driven recovery password rotation
- BitLocker – Fixed Drive Settings
- BitLocker fixed drive policy
- BitLocker – OS Drive Settings
- BitLocker system drive policy
- BitLocker – Removable Drive Settings
- BitLocker removable drive settings
2.2 For End Users To get the Bitlocker Recovery Key
Option 1, Using the Azure Management Portal
- Open the Azure AD resource object in the Management Portal
https://portal.sazure.com
- Go to the All Users object and search for the account associated to the device.
- Click the user object name to view the profile properties.
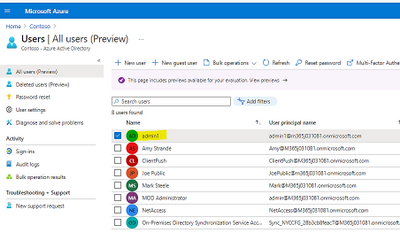
Go to the Devices object under the Manage heading.
- Select the appropriate listed device.
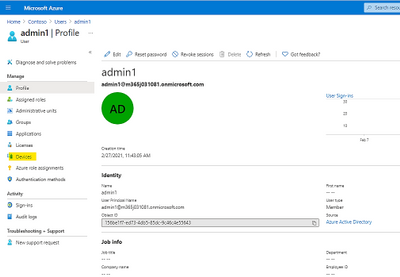
If the device is registered with Bitlocker encryption, then the Bitlocker Key ID and Recovery Key will be visible.
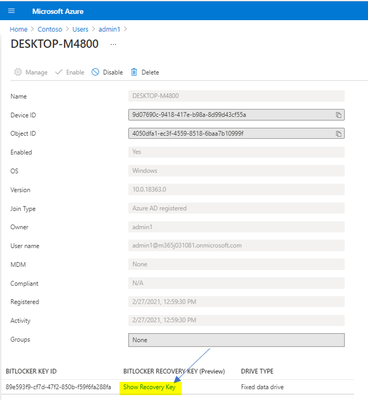
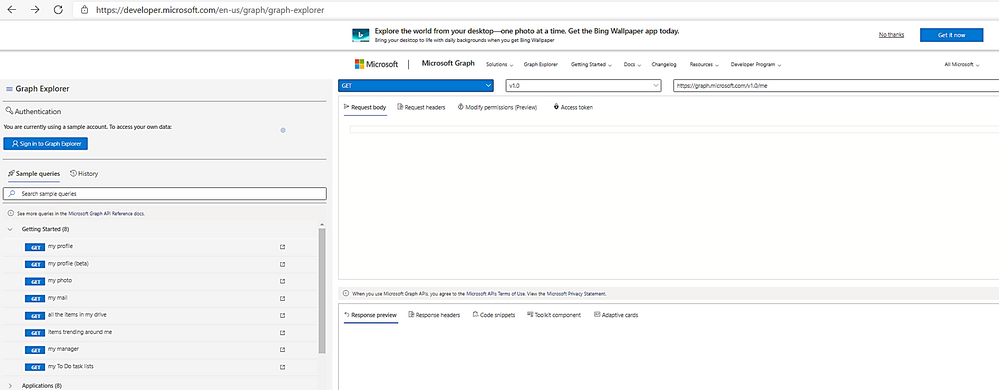
- Click the Copy to Clipboard button and paste the data to view the entire string.
Option 2, Using the Microsoft Endpoint Manager Admin Center Portal
- Open the admin center https://endpoint.microsoft.com
- Go the Devices blade
- Search for the appropriate target device
- In the “Monitor” section, find and click on “Recovery keys”
Click the Copy to Clipboard button and paste the data to view the entire string.
Option 3, Using the Company Portal website to get MacOS Recovery Key:
- Sign into the Intune Company Portal website from any device.
- In the portal, go to Devices and select the macOS device that is encrypted with FileVault.
- Select Get recovery key. The current recovery key is displayed.
On an iPhone, you must select the three dots before the Get recovery key option appears.
- Generate a list of Bitlocker recovery keys by Graph API in Azure AD
3.1 Export list of recovery keys from Azure AD
- The BitLocker Recovery Keys are stored in Azure AD, and there is Graph API (beta) to export the whole recovery keys by Graph Explorer
3.2 Steps to get Bitlocker Recovery Password List
- Sign into Graph Explorer as Global Admin or Intune Admin,
Graph Explorer – Microsoft Graph
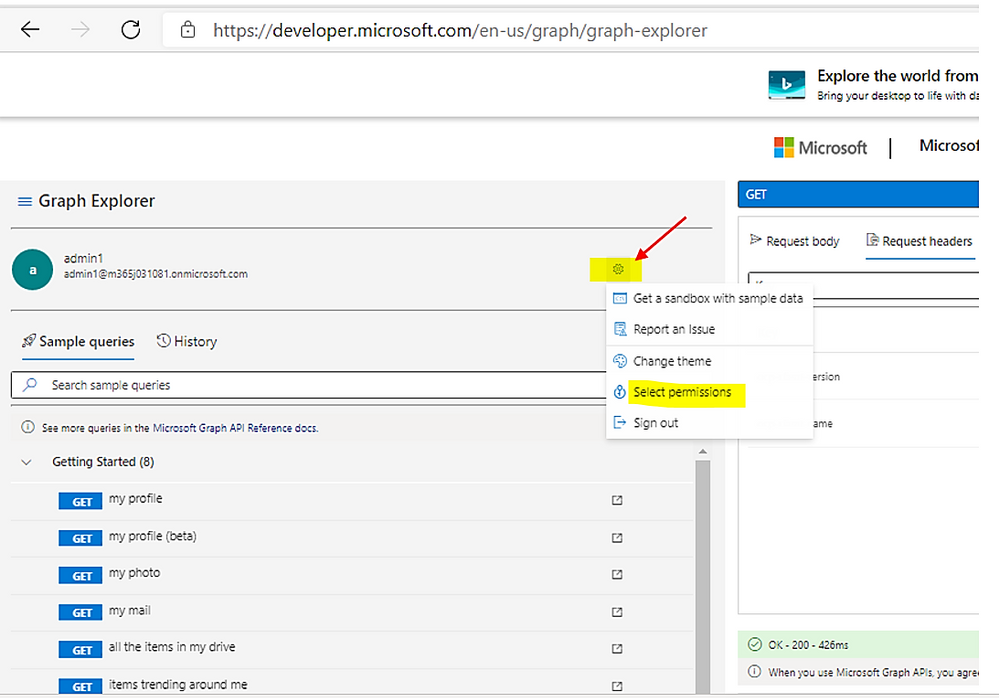
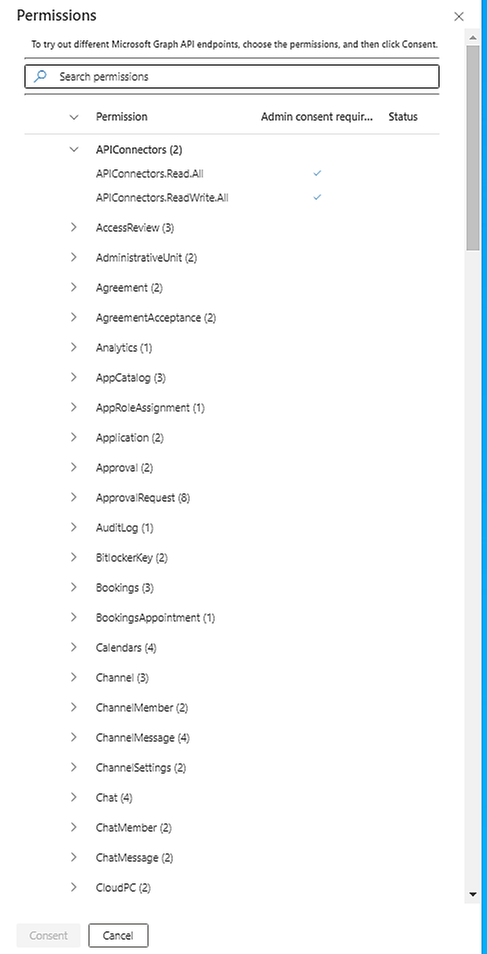
- Choose the permission to read Bitlocker ‘s properties as shown here:
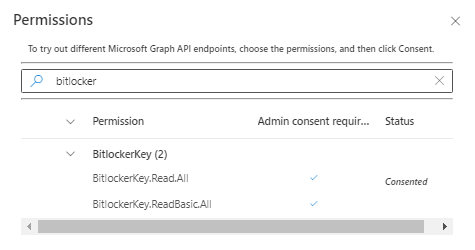
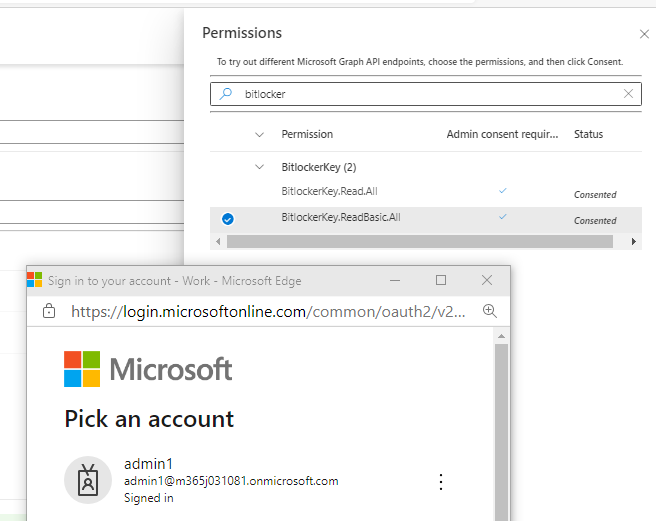
- In the search box: typing bitlocker to search for bitlocker permissions
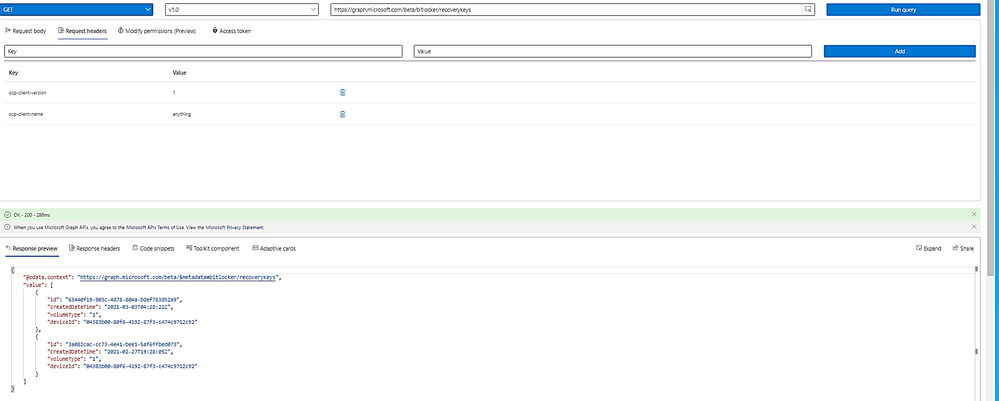
- Choose the Bitlocker permission Read Basic or Read All:
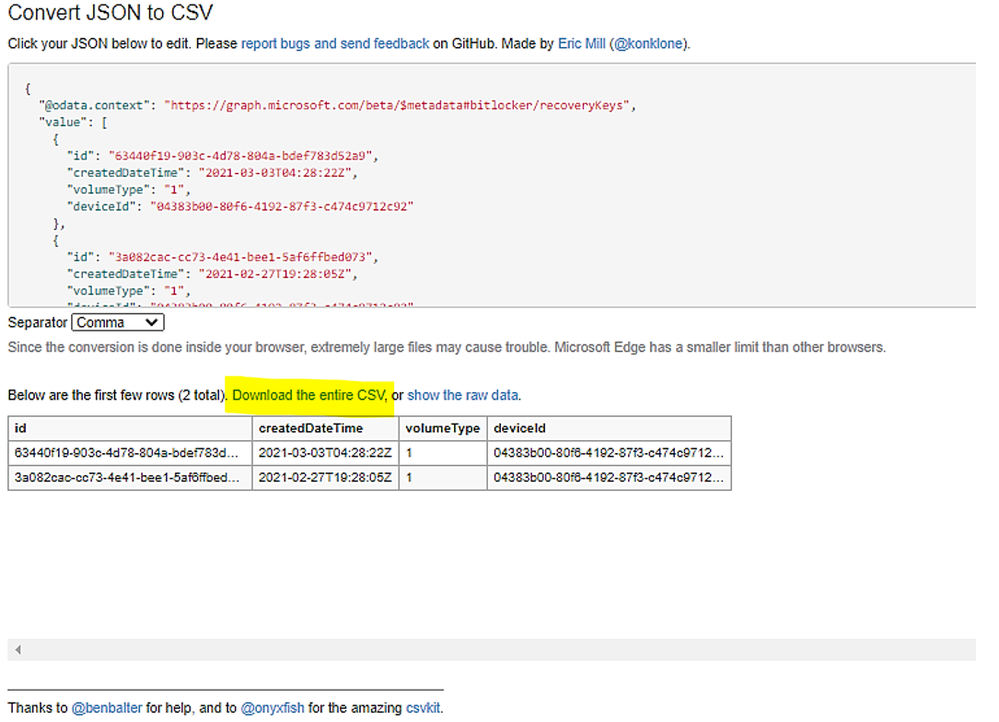
- Choose Consent and Sign-in,
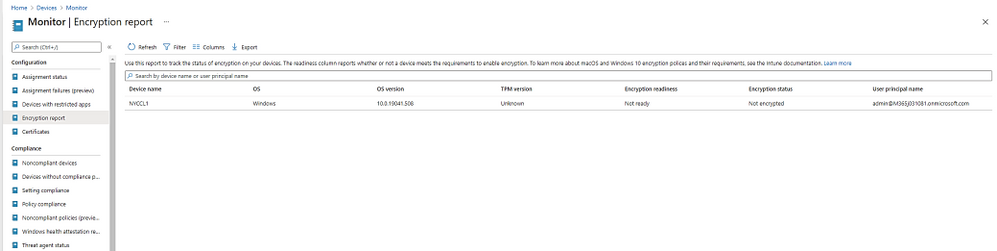
- Check the box “Consent on behalf of your Organization”
- Make Query with the HTTP Graph beta and Header as shown here:
Ocp-client-name: anything (you could use your application API name registered in Azure AD
Ocp-client-version: 1
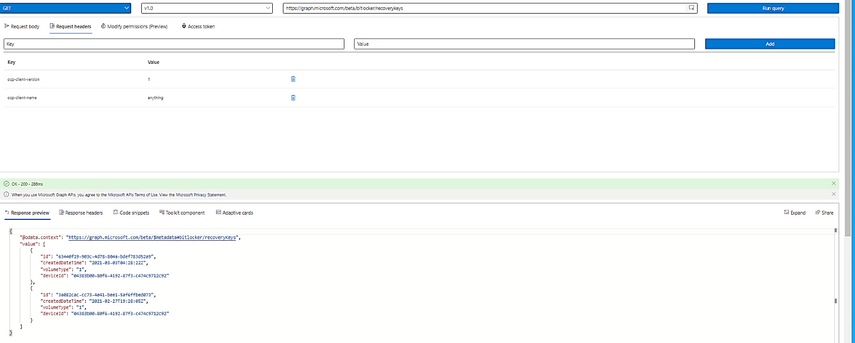
- The current list of JSON is limited to 999 items.
- Copy the JSON list and make a csv file from the query result by convert tool, the tool could be powershell converter or your trusted online, converting JSON to csv Website.
Example of converting JSON to CSV file:
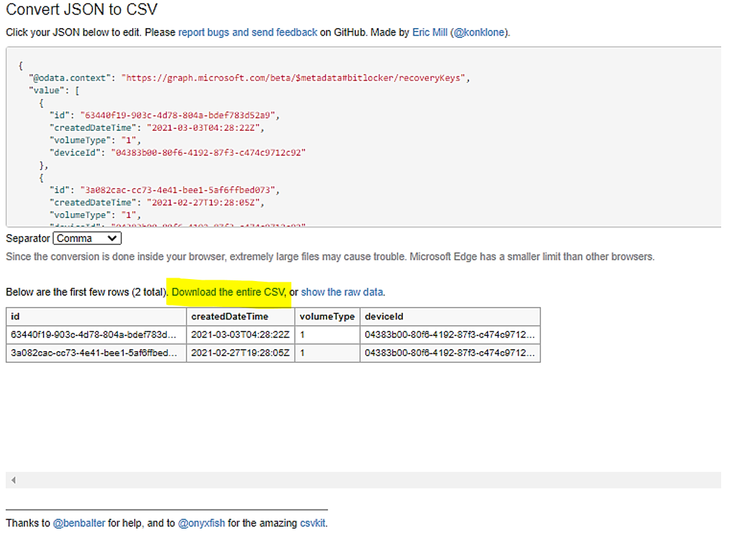
3.3 To monitor the status of Bitlocker device:
The Microsoft Intune encryption report is a centralized location to view details about a device’s encryption status and find options to manage device recovery keys. The recovery key options that are available depend on the type of device you’re viewing.
> Select Devices
>Monitor, and then
> under Configuration, select Encryption report.
- To View encryption details
The encryption report shows common details across the supported devices you manage. The following sections provide more details about the information that MEM presents in the report.
Encryption readiness
|
Ready: The device can be encrypted by using MDM policy, which requires MacOS10.13 or later, Windows with TPM and Enterprise version 1709 or Pro 1809
|
Not ready
|
The device doesn’t have full encryption capabilities, but may still support encryption.
|
Not applicable
|
There isn’t enough information to classify this device.
|
Encryption status
|
Whether the OS drive is encrypted
|
…
|
…
|
When you select a device from the Encryption report, MEM displays the Device encryption status pane with the following detail:
A list of the Device configuration profiles that apply to this device·
- macOS: Profile type = Endpoint protectiono Settings > FileVault > FileVault = Enable·
- Windows 10: Profile type = Endpoint protectiono Settings > Windows Encryption > Encrypt devices = Require
Encryption readiness
|
TPM status is ready for bitlocker encryption or not
(the device can still be manually encrypted. or through a MDM/Group Policy setting that can be set to allow encrypting without a TPM.)
|
Encryption status
|
Whether the OS drive is encrypted. It can take up to 24 hours for MEM to report
For Windows devices, this field does not look at whether other drives, such as fixed drives, are encrypted
|
Profiles
|
Status details
|
This field displays information for each applicable error that can be detected. You can use this information to understand why a device might not be encryption ready:
MacOS:
· The recovery key hasn’t been retrieved and stored yet,
· The user is deferring encryption or is currently in the process of encryption.
· The device is already encrypted. Device user must decrypt the device to continue.
· FileVault needs the user to approve their management profile in macOS Catalina and higher.
· Unknown
Windows:
· The BitLocker policy requires user consent to launch the BitLocker Drive Encryption Wizard on the OS volume.
· The encryption method of the OS volume doesn’t match the BitLocker policy.
· The policy BitLocker requires a TPM protector, or PIN, or Startup Key.
· Recovery key backup failed.
· A fixed drive is unprotected.
· The encryption method of the fixed drive doesn’t match the BitLocker policy.
· To encrypt drives, the BitLocker policy requires either the user to sign in as an Administrator or, if the device is joined to Azure AD, the AllowStandardUserEncryption policy must be set to 1.
· Windows Recovery Environment (WinRE) isn’t configured.
· The TPM isn’t ready for BitLocker.
· The network isn’t available.
|
3.4 To view list of Unencrypted device:
We need to know if the Devices ever backup the recovery keys to Azure AD. Jos Lieben provided the script to generate a report about the devices who have not been escrowed the bitlocker recovery key to Azure AD.
Download the Get-bitlockerEscrowStatusForAzureADDevices.ps1script from Github
4. Compare list and make manually escrow of recovery keys to Azure AD
Use the Excel spreadsheet’s comparing feature to make sure no discrepancy between the 2 files.
5. Shutdown MBAM Server and decommission them.
- Correct any problem with the devices who are missing recovery passwords in Azure AD or MEM
- Power off the MBAM Server for 2 months (optional),
- Backup and Remove the MBAM Database.
- Decommission the MBAM Servers.
I hope the information is useful for your migration plan and deployment.
Thanks for viewing and discussing this topic.
Reference
Disclaimer
The sample scripts are not supported under any Microsoft standard support program or service.
The sample scripts are provided AS IS without warranty of any kind. Microsoft further disclaims all
implied warranties including, without limitation, any implied warranties of merchantability or of
fitness for a particular purpose. The entire risk arising out of the use or performance of the
sample scripts and documentation remains with you. In no event shall Microsoft, its authors, or
anyone else involved in the creation, production, or delivery of the scripts be liable for any
damages whatsoever (including, without limitation, damages for loss of business profits,
business interruption, loss of business information, or other pecuniary loss) arising out of
the use of or inability to use the sample scripts or documentation, even if Microsoft has been
advised of the possibility of such damages.


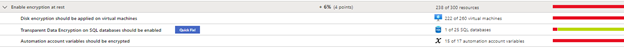



Recent Comments