by Contributed | Apr 1, 2021 | Technology
This article is contributed. See the original author and article here.
Doing Microsoft Graph Fundamentals learning path on MS Learn – Part 1
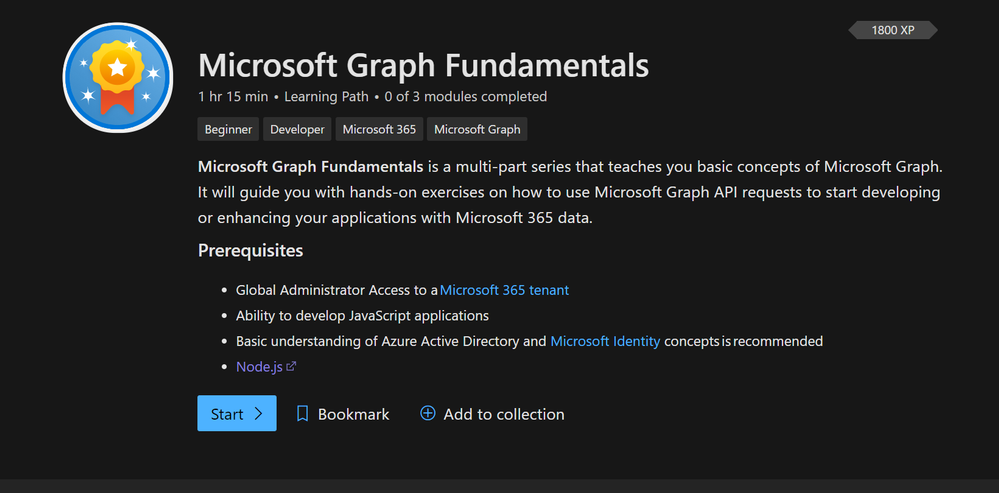
This blog post will summarize how I did the brand new Microsoft Graph Fundamentals Learning path. Microsoft Graph Fundamentals consists of 3 modules:
What is Microsoft Graph – lets you understand the Graph services and shows you how you can access user information from Graph using their learning playground called Graph Explorer. You will do a short exercise on that as well.
Configure a JavaScript application to retrieve Microsoft 365 data using Microsoft Graph – lets you understand how app registration works in Azure AD with permissions for Microsoft Graph powered apps and closes with two exercises using MSAL – making authentication easy.
Access user photo information with Microsoft Graph – in this module, you continue with the application you built-in module 2 and learn how to retrieve a user photo and do an exercise about it.
The whole learning path is estimated to take us ~75 minutes. Let’s see how it goes
To be very honest: I worked with Graph before – see my blog posts here: Microsoft Graph – M365 Princess – but it’s the first time I do this guided learning on Microsoft Learn. I will cover module 1 in this post and continue with module 2 and 3 in the following posts.
What is Microsoft Graph
In super short: Microsoft Graph is a set of APIs that lets you access data in Microsoft 365 and use it for custom coded and low code applications. With this, Microsoft Graph is your key to data. Here are three tremendous advantages of it:
- across all Microsoft services, you can use one endpoint https://graph.microsoft.com – which makes development straightforward as you don’t need to learn all the different APIs for mail and calendar and files and so on
- documentation is fantastic, and there is a ton of learning material – like this learning path or the upcoming Learn Together- Building apps with Microsoft Graph event
- you can try out Graph in Graph Explorer – if you like to read more about that, read my blog post on how to get started with Graph Explorer
- Microsoft Graph Toolkit (you will learn more about it later) makes authentication (my personal kryptonite) easy. It also provides you with ready-to-use components and reduces the time you need to develop.
Intro
For this module, you will need to be a global admin in a Microsoft 365 tenant. The easiest way to have this is to join the Microsoft 365 developer program and get a free E5 subscription. If you are not familiar with this, read Julie Turner’s article about it, at least some basic JavaScript understanding, and you should know what Azure Active Directory does. You will also need to have Node.js installed.
The learning module introduces you to a business scenario so that it is easier for you to imagine which kind of applications we are talking about. In this scenario, we want to bring together messages from chat, emails, attended meetings, notes, key contacts, and relevant files.
Our application could also grow later on and bring in data from more services like Windows 10 services or Enterprise Mobility and Security Services. We will not build this in total in this learning path, but we get a perspective, what we can develop based on our organization’s needs.
Understand Microsoft Graph Services
At the very heart of Graph, we will find users and groups. In our application, we will need to access data from a single user’s personal scope (mail, messages, events) and a group scope (teamwork).
The module introduces you to some Microsoft Graph API calls and shows you how the response will look. All API responses will be in JSON format – in case you want to learn more about it, read this article by Bob German on Introduction to JSON
The even more exciting part is that apart from making direct API calls, Microsoft provides us with the Graph SDK (Software Developer Kit). We can use the client Graph SDK client libraries to even more easily call the Graph API.
Access user information from Microsoft Graph using Graph Explorer
This chapter introduces you to Graph Explorer -easily access it at aka.ms/ge, try out some sample queries! My blog post on how to get started with Graph Explorer explains that in detail.
Exercise – Access user information from Microsoft Graph using Graph Explorer
Time to access your own data! I strongly recommend not playing in your production tenant- especially if you do not only want to read data with GET requests but also want to write, update, or delete data with POST, PATCH, UPDATE, or DELETE requests. Get yourself a Microsoft 365 developer tenant and use this.
This chapter teaches you how to modify permissions in Graph explorer and how tips help you.
You will learn how to send a message to Teams via Graph – this is not a test; it will really appear in Teams.
Let us 1’up this already fantastic experience. Besides using this beautiful UI, Graph Explorer provides you with:
- Access tokens used for authentication (recognizing who a user is) and authorization (looking up the correct privileges)
- Code snippets for three different languages so that you can copy-paste them into your applications
- Microsoft Graph Toolkit components – most fabulous thing ever! If you are not familiar with MGT, go check it out
- Adaptive cards snippets so you can quickly build UI components for your apps
You see, this is the ‘absolutely carefree package’ provided by the Microsoft Graph team.
Conclusion on Module 1:
Microsoft Graph is not only THE door opener to access all kinds of information and data across Microsoft 365 for developers and makers. They also provide us with this fantastic learning playground, aka Graph Explorer, in which we can try out, learn, explore and get snippets for all kinds of development scenarios.
After introducing you to some basic concepts on Microsoft Graph, you have learned on a real-world example how to use Microsoft Graph before continuing to access data via Graph in a JavaScript application. This learning module is fantastic! If you never heard about Graph, you’ll get everything you need to start right away with it!
by Contributed | Apr 1, 2021 | Technology
This article is contributed. See the original author and article here.
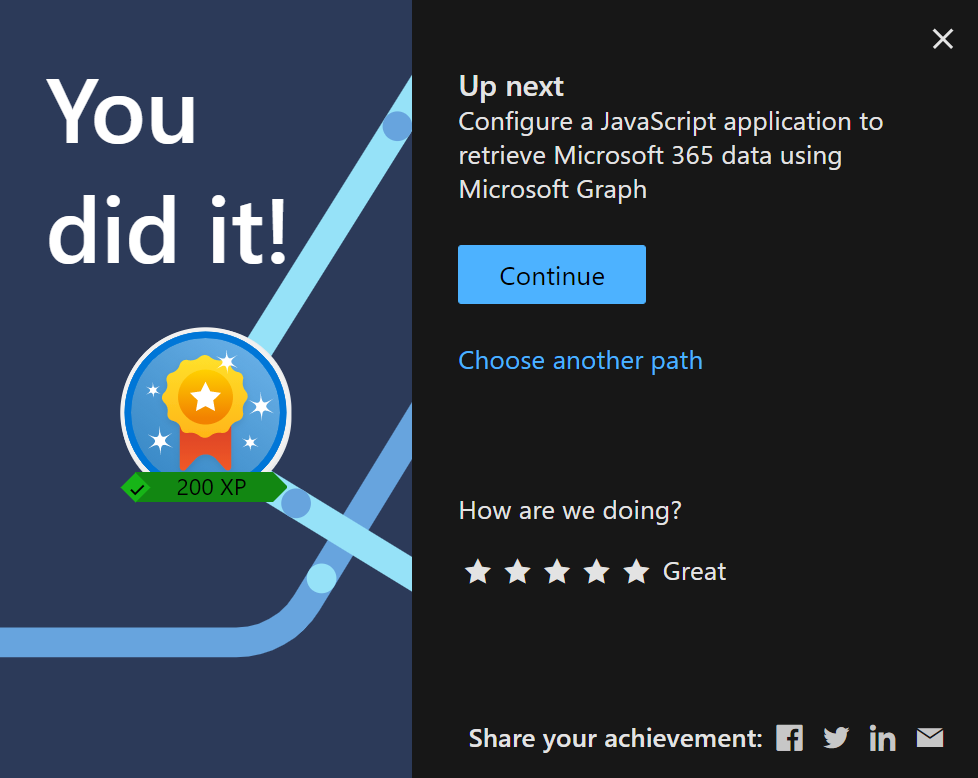
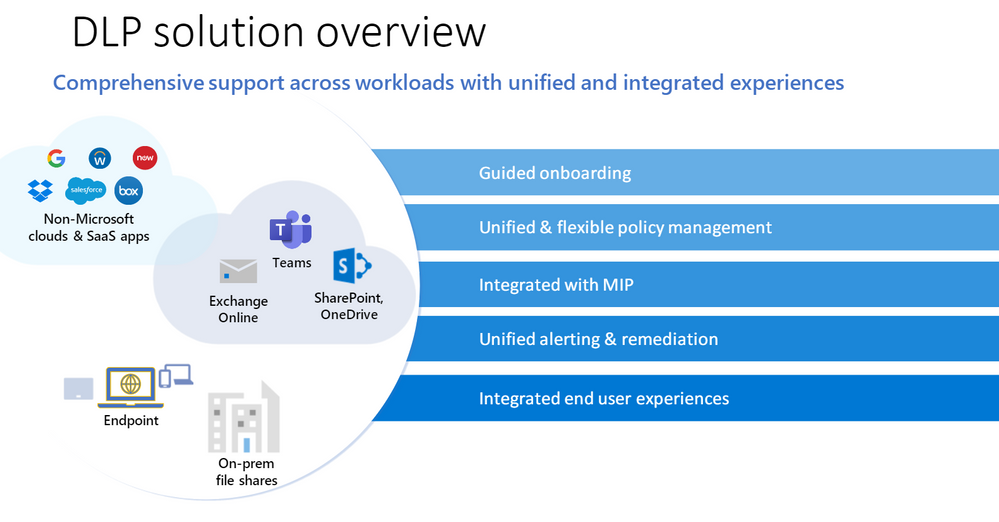
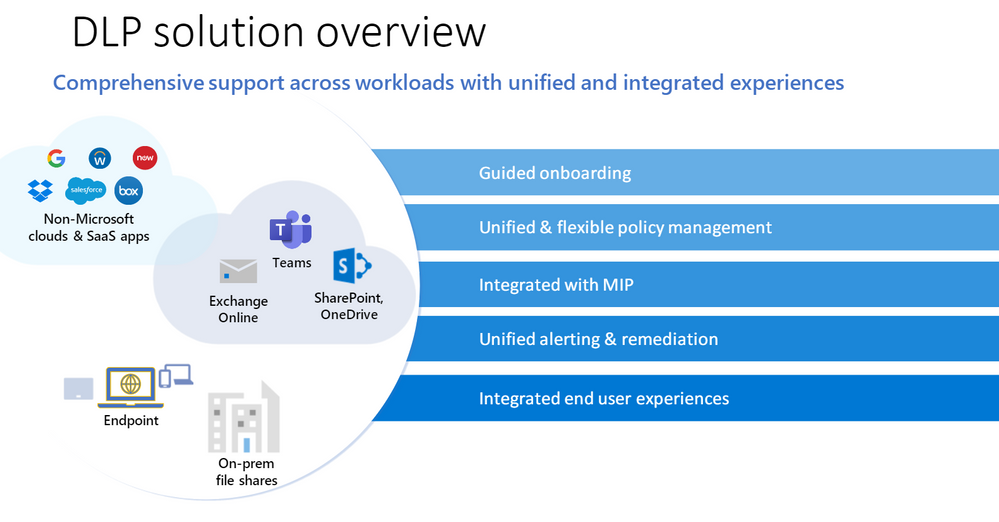
This webinar provides an overview of Microsoft’s unified DLP solution and covers the new features that have been released to help better protect your data.
Resources:
WATCH the on-demand webinar
Overview of data loss prevention – Microsoft 365 Compliance | Microsoft Docs
Microsoft Information Protection SDK documentation | Microsoft Docs
This webinar was presented on March 17, 2021, and the recording can be found here.
Attached to this post are:
- The FAQ document that summarizes the questions and answers that came up over the course of both Webinars.
- A PDF copy of the presentation.
Thanks to those of you who participated during the two sessions and if you haven’t already, don’t forget to check out our resources available on the Tech Community.
Thanks!
@Robin_Baldwin on behalf of the MIP and Compliance CXE team
by Contributed | Apr 1, 2021 | Technology
This article is contributed. See the original author and article here.
This survey captures the top asks we captured from our customers via the various engagements, discussions, and feedback channels.
Hello Microsoft Information governance community,
The survey is available at: https://aka.ms/MIPC/MIG21H2-FeatureSurvey and it will be opened for the next 3 weeks till April 21, 2021.
If you want to influence the platform with features and capabilities that you want, need and like, this is the time to make it happen and share your feedback.
Thanks,
Randall Galloway on behalf of the MIG product group
by Contributed | Apr 1, 2021 | Technology
This article is contributed. See the original author and article here.
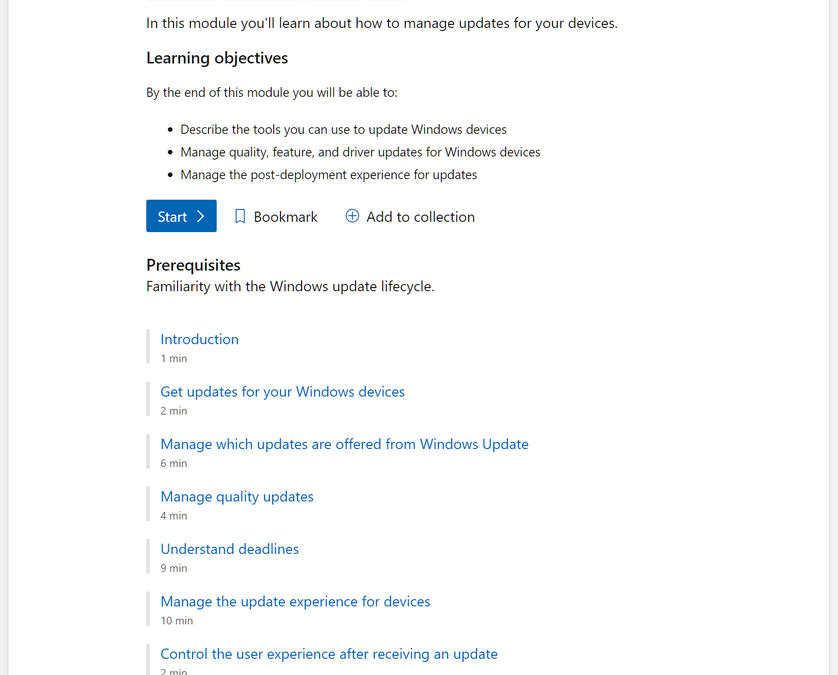
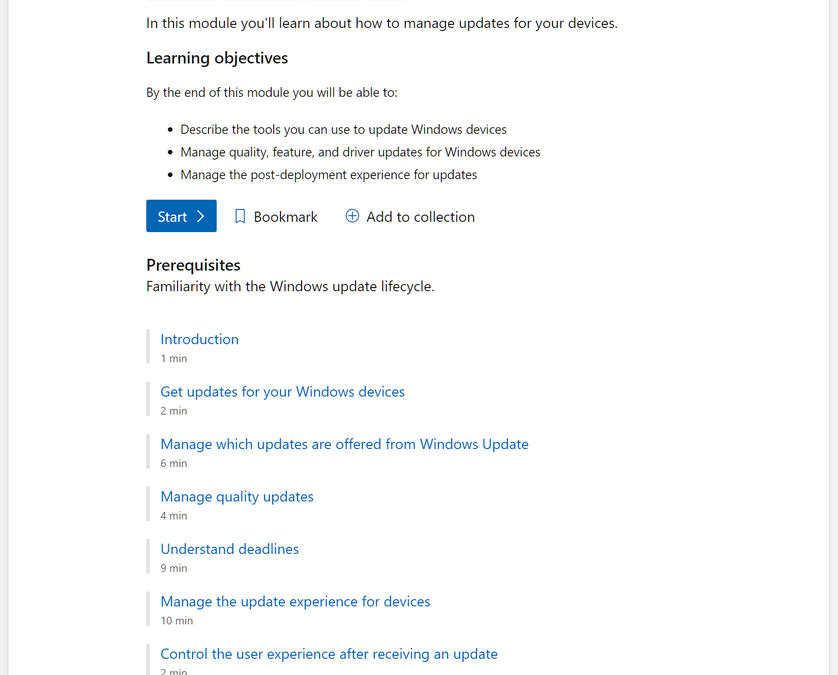
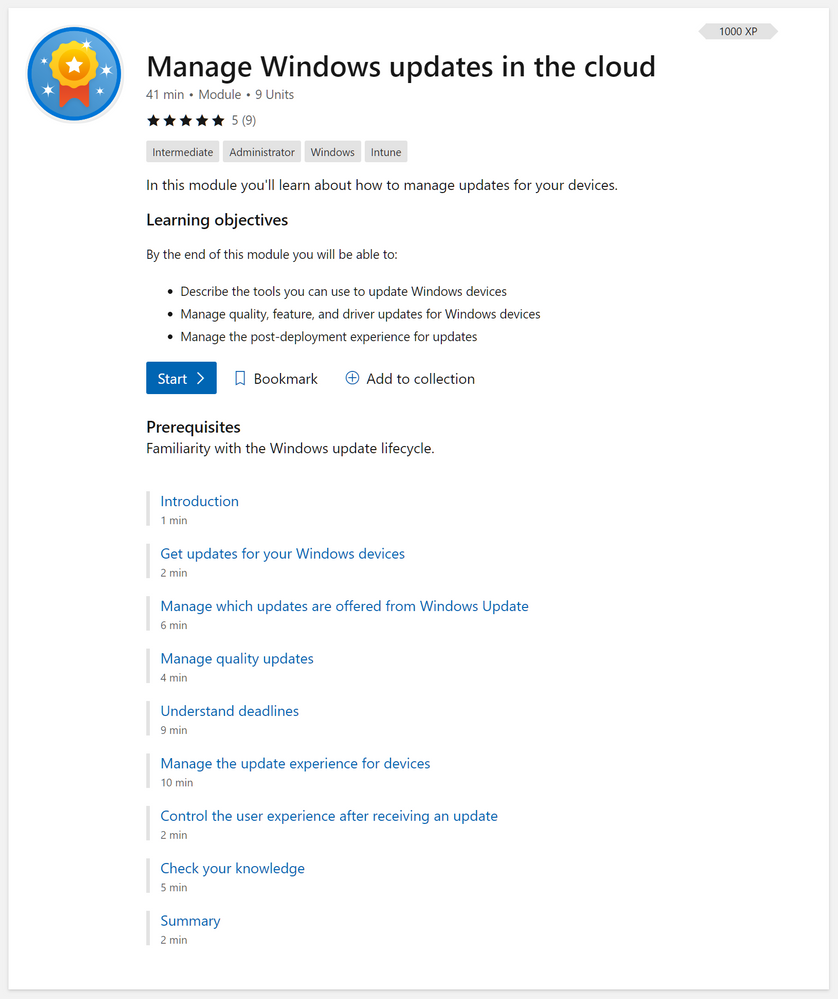
If you want to understand how to best configure Windows updates and optimize the user experience, this is the learning path you’ve been waiting for. Building on the fundamentals we outlined in Stay current with Windows 10 and Microsoft 365 Apps, our new learning module is designed to help you Manage Windows updates in the cloud—in 41 minutes or less! :smiling_face_with_smiling_eyes:
What will I learn?
- The tools you can use to update Windows devices
- How to manage quality (i.e. monthly), feature, and driver updates for Windows devices
- How to create a positive update experience for your end users
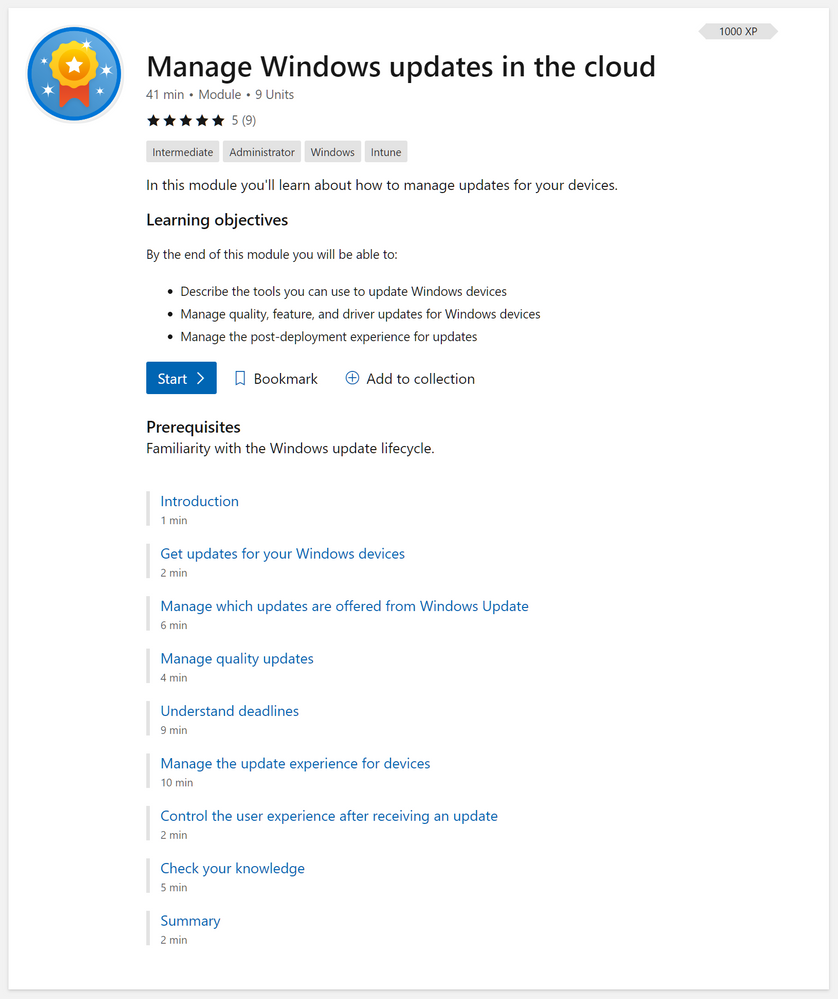 Screenshot of the full “Manage Windows updates in the cloud” learning module
Screenshot of the full “Manage Windows updates in the cloud” learning module
Share your thoughts
We hope you will find this new learning module valuable! We will continue to invest in Microsoft Learn experiences around deploying and managing Windows so if you have a suggest on something we should cover in an official module or learning path, leave a comment below!
by Contributed | Apr 1, 2021 | Technology
This article is contributed. See the original author and article here.
Reimagine Project Management with Microsoft
You’ve missed our live keynote, but there’s still lots of time to check out the Reimagine Project Management with Microsoft conference! Registration is free.
This conference includes our recorded keynote as well as 6+ hours of on-demand demos and product walkthroughs to help you discover and leverage new features and learn best practices to keep your projects on track. Our engineering team is hosting live roundtables and boardrooms now through June, so you still have a chance to connect with engineers and find out more about Project.
You can sign up for free to check out the entire conference here.
Microsoft Project Trivia
Last Month :
Thanks to everyone who put their guesses in our comments last month!
Question: What year was Microsoft Project first released?
Answer: 1984
Bonus: How many Windows applications did Microsoft release before Project?
Bonus Answer: Project was the third Windows-based application released by Microsoft.
This Month :
Question: Which type of resource is NOT supported by Project for the web?
A:
- Equipment
- Placeholder
- Crew
- Generic
Leave your answer in the comments and check back next month to see if you were right! If you want to learn more about resources & calendars in Project for the web, check out our blog post here.
New Features
- Export Timeline to PDF ~ All users can print their timeline information to a PDF file. You can do this by going to the Timeline view and clicking the ‘…’ menu in the top-right of the screen.
- Email Assignment Notifications ~ Rolling out now, your teammates will get an email whenever they are assigned a task in Project. Edit your notification settings by clicking on the gear icon in the top Office ribbon and clicking on the “Notification settings” under the Project heading.
- Project Accelerator ~ The Project Accelerator allows users to leverage Power Apps to manage the entire lifecycle of their projects, including demand management, financial goals, and more! For more information, check out our blog post on it here.
- Effort in the Project details pane ~ See overall effort on your project directly in the Project details pane, including the total effort, completed effort for your project, and remaining effort on your whole project.
Upcoming Features
- Import from Project Desktop ~ Import your .mpp files into Project for the web.
- Assign tasks to non-group members ~ Assign a task to someone without automatically adding them to your project group.
- Actions on Project Home ~ Copy, rename, export, or delete your project directly from Project Home, without needing to open it in the browser.
FAQ:
This section includes questions we see frequently, either through the in-app Feedback button or from comments on last month’s blog.
Q: Why can’t I change my working days on a project?
A: You actually can change your working days, using work hour templates in Power Apps. Check out our blog post here for more detailed information on how to change your working days.
Q: How can I change the group on a project in Project for the web?
A: You can’t change the group assigned to a project in Project for the web. To get around this, we suggest that you make a copy of the project. Copied projects aren’t shared to any groups, so you can assign your copy to the correct group.
We want to hear from you! If you have feedback, submit it by using the “Feedback” button in Project for the web. Make sure to include your email address so we can contact you directly with any follow up questions or comments. Your comments on our blog posts are also monitored, so let us know what you think about this or other articles.
![[Upcoming Webinar] Enabling customers in their CMMC journey](https://www.drware.com/wp-content/uploads/2021/04/fb_image-4.jpeg)
by Contributed | Apr 1, 2021 | Technology
This article is contributed. See the original author and article here.

Please join Microsoft, CORTAC Group and industry partners to hear about the current state of CMMC adoption and to learn about right-sized and cost-optimized solutions you can leverage in your Cybersecurity Maturity Model Certification (CMMC) journey.
The webinar begins with delivery of the current status of adoption of CMMC including updates and ideas to assist suppliers in their implementation of CMMC presented by Katie Arrington, CISO, Acquisition and Sustainment, United States Department of Defense. Joining us are several national industry experts discussing supply-chain challenges and risks.
We shift to how the DoD supply-chain can leverage industry leading solutions that are right-sized and cost-optimized. This enables small, medium, and large suppliers to achieve and stay CMMC compliant and keep existing business and grow future opportunities as an early CMMC adopter.
In closing, we’ll discuss industry resources available to suppliers empowering them through their journey. Impact Washington and the Pacific Northwest Defense Coalition (PNDC) will discuss how a public/private partnership has been successful in supporting many small and medium suppliers on their CMMC journey across the Pacific Northwest.
Register here today!
Speakers info found below :

Katie Arrington
CISO A&S
United States Department of Defense
Twitter: https://twitter.com/karringtonsc
LinkedIn: https://www.linkedin.com/in/katie-arrington-a6949425/

Ryan Bonner
@rybo3000
Compliance Consultant
DefCERT
LinkedIn: https://www.linkedin.com/in/rybonner/

Richard Wakeman
@RichardWakeman
Sr. Director of Aerospace & Defense, Microsoft Azure Global
Microsoft
LinkedIn: https://www.linkedin.com/in/wakeman/

Scott Edwards
CEO
Summit 7
LinkedIn: https://www.linkedin.com/in/mscottedwards/

Kate Kanapeaux
VP, Marketing & Strategic Partnerships
Pacific Northwest Defense Coalition
LinkedIn: https://www.linkedin.com/in/kate-kanapeaux/

Geoff Lawrence
Account Executive
Impact Washington
LinkedIn: https://www.linkedin.com/in/lawrencegeoff/

Jerry Leishman
@jerryleishman
Executive VP & National Security and Compliance Director
CORTAC
LinkedIn: https://www.linkedin.com/in/jerryleishman/

Saif Rahman
Leader: Cloud Security, Architecture and Application Risk
Quzara
LinkedIn: https://www.linkedin.com/in/saif-rahman-aa19814/

Kris Carter
VP, Technology & Compliance
Verify Inc.
LinkedIn: https://www.linkedin.com/in/kriscarter/
by Contributed | Apr 1, 2021 | Technology
This article is contributed. See the original author and article here.
In this episode of Data Exposed with David Trigano, learn how you can leverage new capabilities in Dynamic Data Masking, help your organization prevent unauthorized access to sensitive data, and gain control by masking it to a non-privileged user at different levels of your database.
Watch on Data Exposed
Resources:
Dynamic data masking
View/share our latest episodes on Channel 9 and YouTube!

by Contributed | Apr 1, 2021 | Technology
This article is contributed. See the original author and article here.
The Problem
Have you ever heard this from a client or colleague?
“I have a list of data on this one site that I need to move to another site.”

Just a simple list of data that they want moved from Site A to Site B. For such a simple request, the solution has, historically, always been anything but simple.
Until now! Thanks to PnP PowerShell, we can handle this request in 5 lines of PowerShell!
The Setup
Aside from the obvious set of SharePoint sites and a list, the only real prerequisite is to make sure you have PnP PowerShell installed.
This blog is running the newer PnP.PowerShell module, which I highly recommend you jump over to.
You can use the link from the introduction for the full instructions, or you can open up PowerShell and…
Install-Module -Name PnP.PowerShell
The Solution
In a previous blog post, we walked through the process of creating custom view formats to create a pretty nifty dashboard full of cards about members of the Fellowship of the Ring.
For the sake of this example, let’s pretend I made a mistake (which never happens IRL), and I put that list on the wrong site.
The solution is pretty straightforward. We’re basically going to create a PnP site template, add our list data to it, and then apply that template to our target site.
Step 1 – Connect to the Source Site
The first thing we’ll do is connect to the source site.
Connect-PnPOnline -Url https://constoso.sharepoint.com/sites/star-wars -Interactive
Step 2 – Create the Template
We actaully have two lists we need to copy. Fellowship Members is the list we care about but, since it contains a lookup column, we need to grab the Middle Earth Locales lookup list as well.
Get-PnPSiteTemplate -Out Lists.xml -ListsToExtract “Middle Earth Locales”, “Fellowship Members” -Handlers Lists
Step 3 – Get the List Data
We’ll use the Add-PnPDataRowToSiteTemplate cmdlet to populate our list instances with actual list item. Because we have two lists, we need to run the cmdlet twice. (So, technically, I guess we’re doing 6 lines of PowerShell. Shh!)
Add-PnPDataRowsToSiteTemplate -Path Lists.xml -List “Middle Earth Locales”
Add-PnPDataRowsToSiteTemplate -Path Lists.xml -List “Fellowship Members”
Step 4 – Connect to Target Site
Now we connect to the target site…
Connect-PnPOnline -Url https://constoso.sharepoint.com/sites/lotr -Interactive
Step 5 – Apply the Template
…and we apply our template using the Invoke-PnPSiteTemplate cmdlet.
Invoke-PnPSiteTemplate -Path Lists.xml
Game Over
Now you’ve got your list(s), complete with data, copied over to another site. All that’s left to do is get rid of the old one, if necessary.

by Contributed | Apr 1, 2021 | Technology
This article is contributed. See the original author and article here.

We are back to announce the release of Update Rollup 3(UR3) for System Center Operations Management 2019! UR3 comes fully loaded with extended auditing capabilities, performance improvements, Linux monitoring enhancements and web console improvements. Let’s dig into each of these aspects below.
Extended auditing capabilities
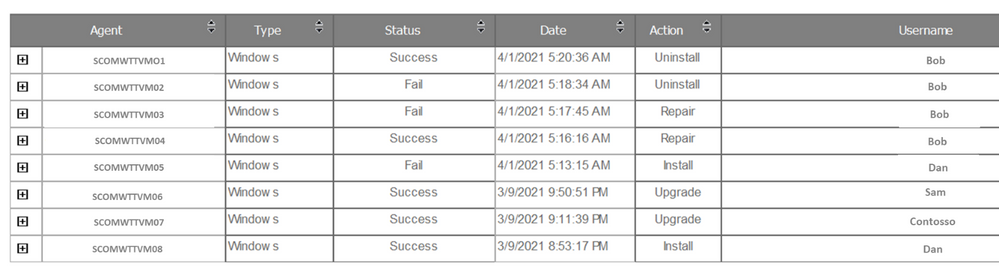
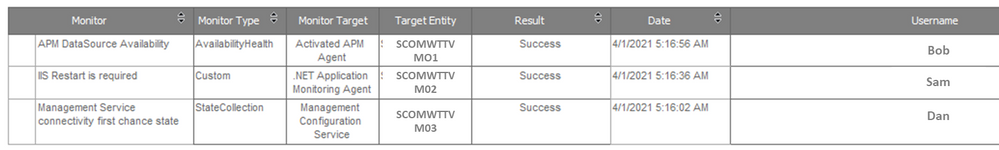
Operations Manager 2019 UR3 includes updates to the change tracking feature for management packs that was well received by our customers in UR2.For SCOM customers with large scale environments it is critical to be able to quickly identify root causes for issues caused due to changes done by any user in SCOM .The change tracking feature provides auditing capabilities for management packs that allows customers to track WHAT changes are done by WHOM and WHEN? This feature has been further rounded off to now support tracing of agents (windows or Linux agents) and the ability to track monitor health reset related actions. There are 2 new reports created in SCOM that show these changes.
- The Agent tracking report gives details on the actions such as install/uninstall/repair/upgrade carried out on Windows or Linux agents. A sample report can be seen below:
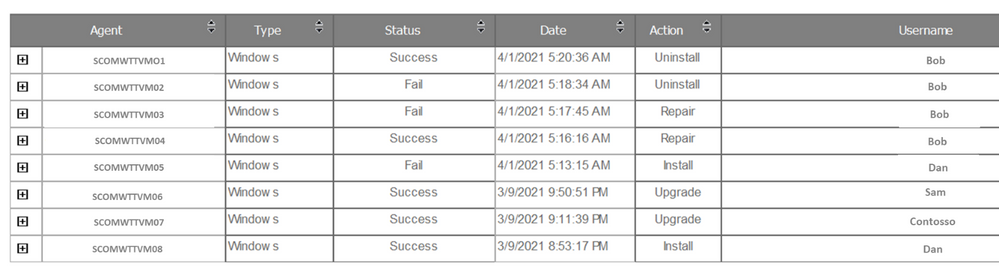
- Monitor Health Reset Tracking Report: Change tracking for monitor health reset is the next addition made in UR3. You can see health reset actions on the monitors as a consolidated view under Reports via the Monitor Health Reset Tracking report.
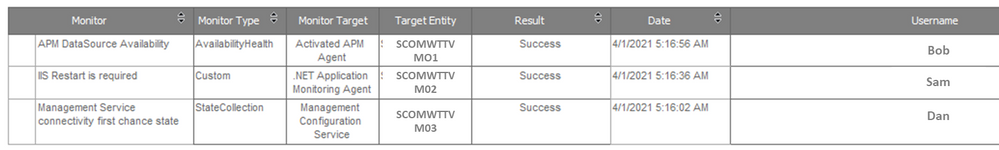
Users can export both the new reports as an Excel, PDF, Notepad and edit the exported content if needed. The reports can also be filtered by date/time, username, and monitor name.
Other enhancements to the change tracking feature include the ability to customize when and how the change tracking data from the Operations Manager DB is synced to the Data Warehouse, this helps in ensuring the DB performance is optimized and data is being stored for the appropriate periods of time based on legal requirements and Data Warehouse sizing . Customers can override the default values for synchronization of change tracking data in Data Warehouse and also customize the parameters of the groom change tracking data workflow through the Data Warehouse Job Status Information Grooming rule based on their specific needs.
Performance Improvements in SCOM
Operations Manager 2019 UR3 also comprises many performance improvements which has been one of the key focus areas for SCOM. Load time of the windows computer view in the operations console and load time of views when any changes are made to a user’s role privileges have been vastly improved by optimizing the relevant SQL queries.
In the past lack of grooming of maintenance mode staging table in Data Warehouse was leading to the increase in utilization of the database that was found to cause decrease in performance of the operations manager’s console. With the Operations Manager 2019 UR3, an index has been added to the maintenance mode staging table that facilitates the efficient grooming of this table leading to performance improvements of the operations console.
Linux Monitoring enhancements
We also continue to invest in enhancing the cross-platform monitoring capabilities of SCOM to cater to the rapidly increasing diverse environments of customers. Cross-platform related enhancements include support for RHEL 6 via the RHEL6 management pack and TLS 1.2 support for Solaris 10 SPARC in UR3. Reliability and performance improvements have correspondingly been added to the Linux agent, for example in earlier releases changes to log-level settings of OMI processes required an agent restart, in UR3 log-level settings can now be changed without the need for restarting the agent .In addition filters have been introduced in the Linux management pack to help users customize the discovery and monitoring scope of the entities of interest.
Last but not the least additional view options in web console widgets have been added and you can now sort the results columns in the Alert widget and State widget, along with being able to group the columns.
Additionally, fixes for critical defects continue to be a part of UR3. Find more details at the following link:
KB Article- Update Rollup 3 (UR3) for System Center 2019 Operations Manager. For the details of features that are released in Update Rollup 3, see the following Microsoft Docs article: What’s New in System Center Operations Manager 2019 Update Rollup 3. We sincerely hope you enjoy the SCOM 2019 Update Roll up 3. Upgrade Now!
by Contributed | Apr 1, 2021 | Technology
This article is contributed. See the original author and article here.
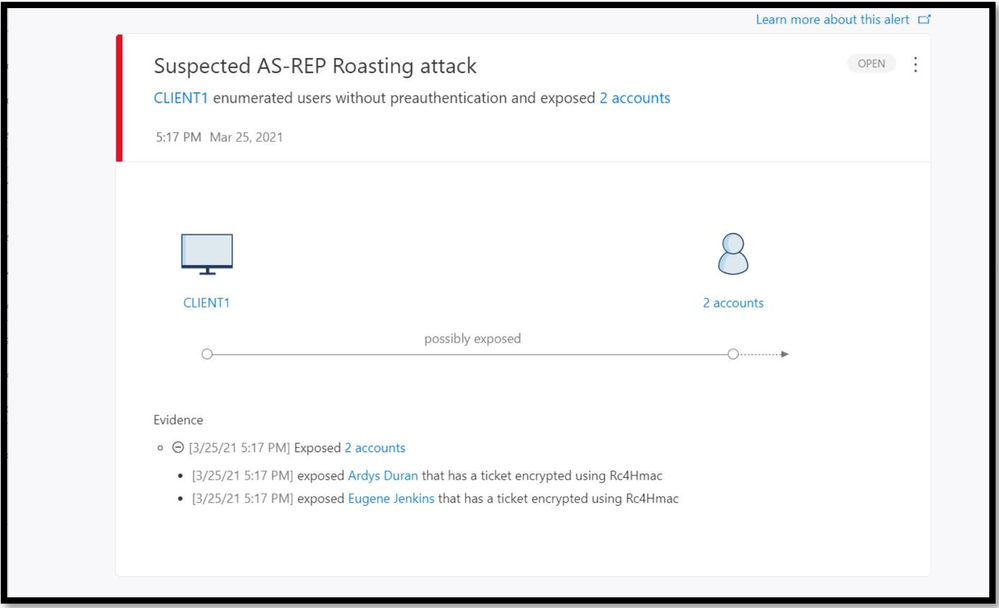
One of the huge advantages of using Microsoft Defender for Identity to help protect your on-premises identities from advanced attacks, is that new detections, features and improvements are being added all the time. After some recent updates, we thought that we’d take some time to properly introduce one of these new detections and give it the attention it deserves!
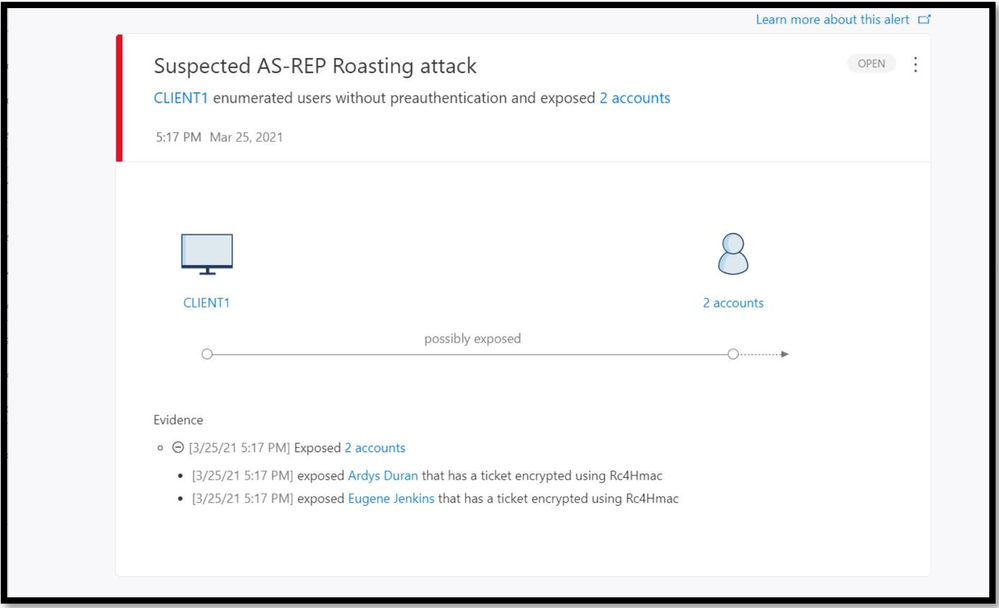
The alert in today’s update covers a notorious attack method that was requested by many of our customers and security partners. It addresses an attack technique that we’ve seen become more and more popular – AS-REP Roasting.
What is AS-REP Roasting?
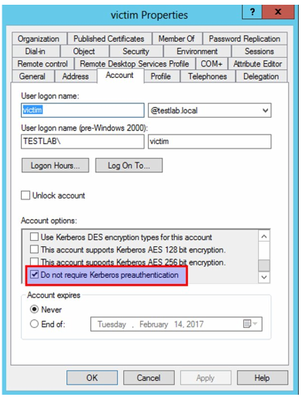
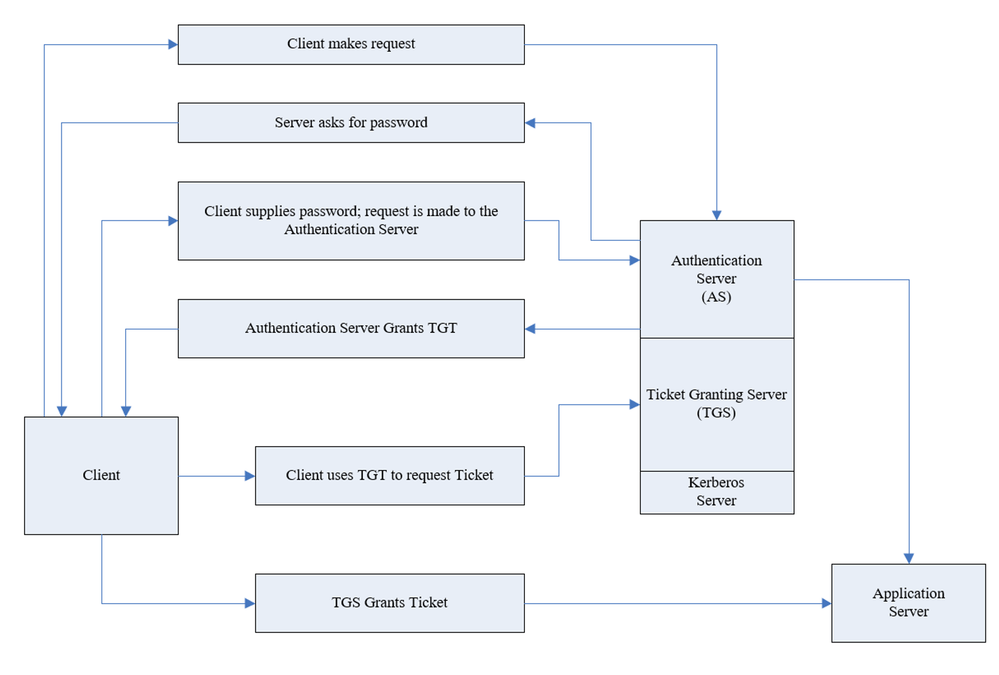
In short, AS-REP Roasting is an attack against Kerberos that targets users that do not require Kerberos pre-authentication.
To understand what AS-REP Roasting is, we need to start with simple explanation about what Kerberos is and how it works.
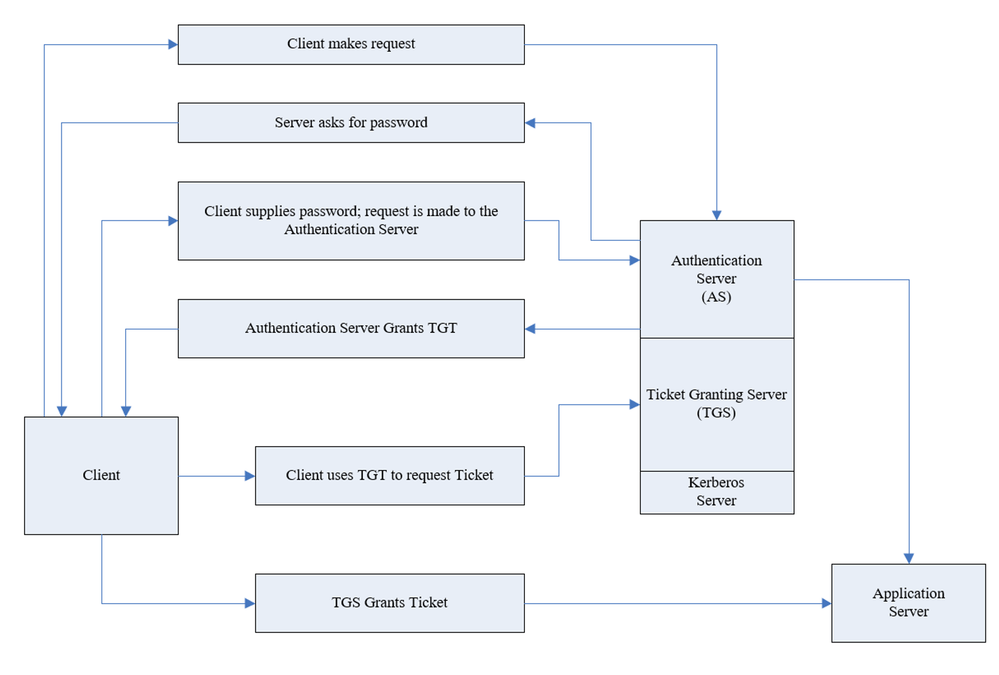
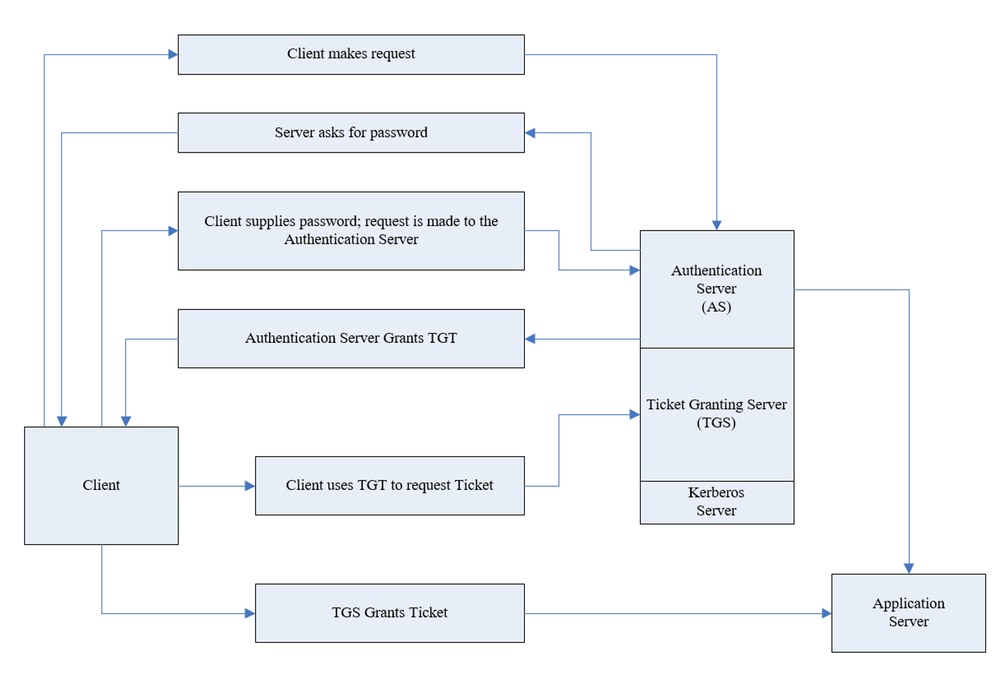
Kerberos is authentication protocol that works based on tickets and this is its basic flow:
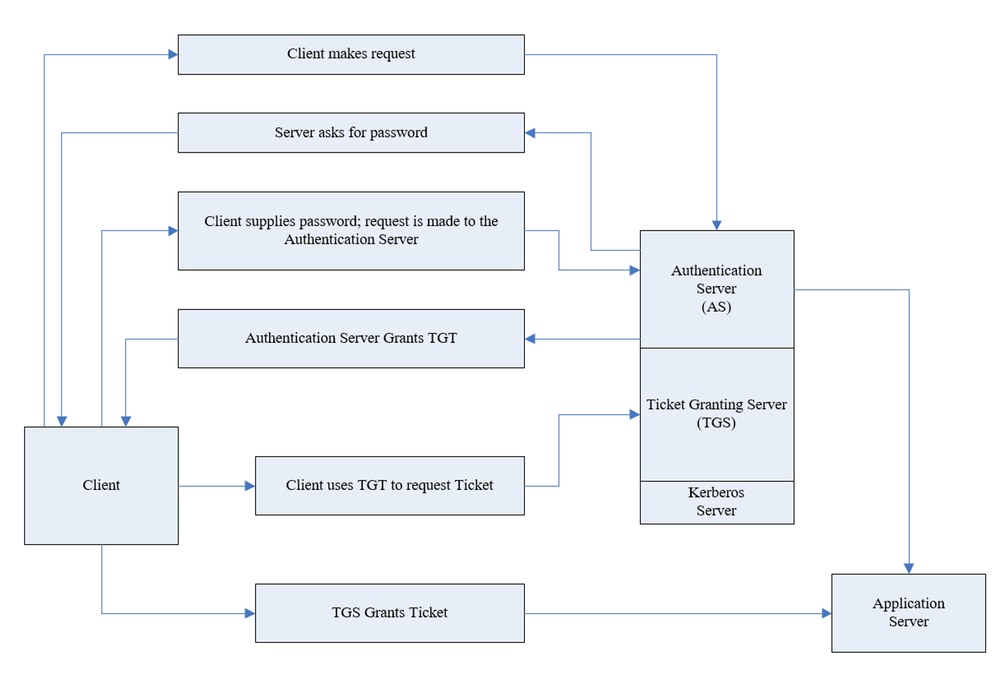
As part of the authentication request sent (AS-REQ), the user will provide their password that encrypts the timestamp. The domain controller will attempt to decrypt it and validate that the right password was used. If the request is granted, the user will be issued with a ticket-granting ticket (TGT) that will be used for future authentication. However, there is an attribute in Active Directory that facilitates disabling pre-authentication for users in the organization. Although this attribute is required by default in Active directory, this can be changed freely.
The typical attack vector in this scenario is to enumerate users that have the attribute turned off and then ask for TGT for these users. The TGT allows a potential attack to crack the password offline.
Covering all of the bases…
Microsoft Defender for Identity can help protect against these kinds of threats in different ways. Let’s dive in to each of these approaches:
Prevention
Defender for Identity allows you to pre-emptively protect against this kind of method using our Security Assessments. If you are not familiar with our security assessments, check out our docs pages for a summary of how you can help prevent threats before they happen.
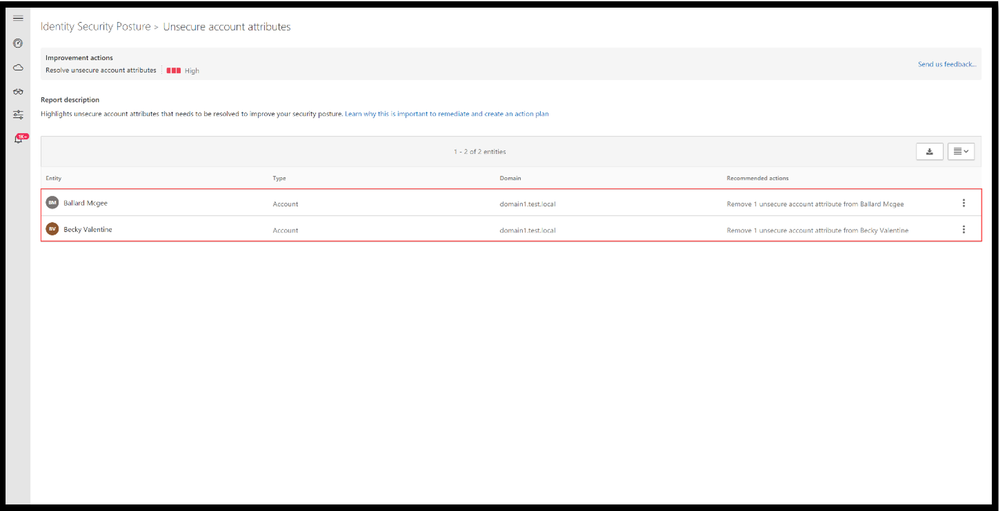
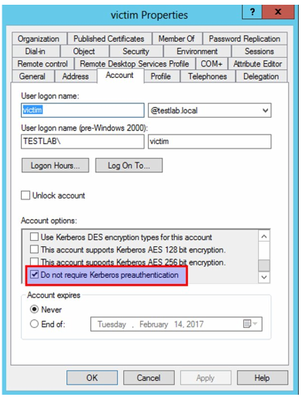
In short, Defender for Identity offers proactive identity security posture assessments to detect misconfigurations or legacy settings that may not have been reviewed in a long time. Suggested improvement actions are then given to bolster your identity posture across your on-premises Active Directory. One of these assessments is “Unsecure account attributes”. This assessment continuously monitors your environment to identify accounts with attribute values that expose a security risk – including Kerberos pre-authentication. Click here to learn more about this assessment
Detections
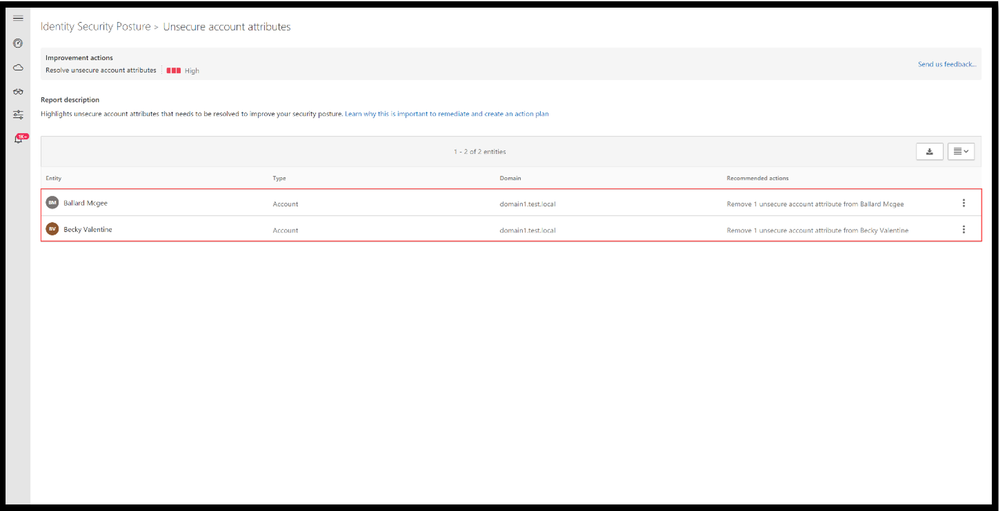
Aside from the preventative nature of the assessments that have been covered above, we offer two detections to help identify this type of attack – 1) the reconnaissance phase and 2) the actual ticket granting ask for future brute force usage.
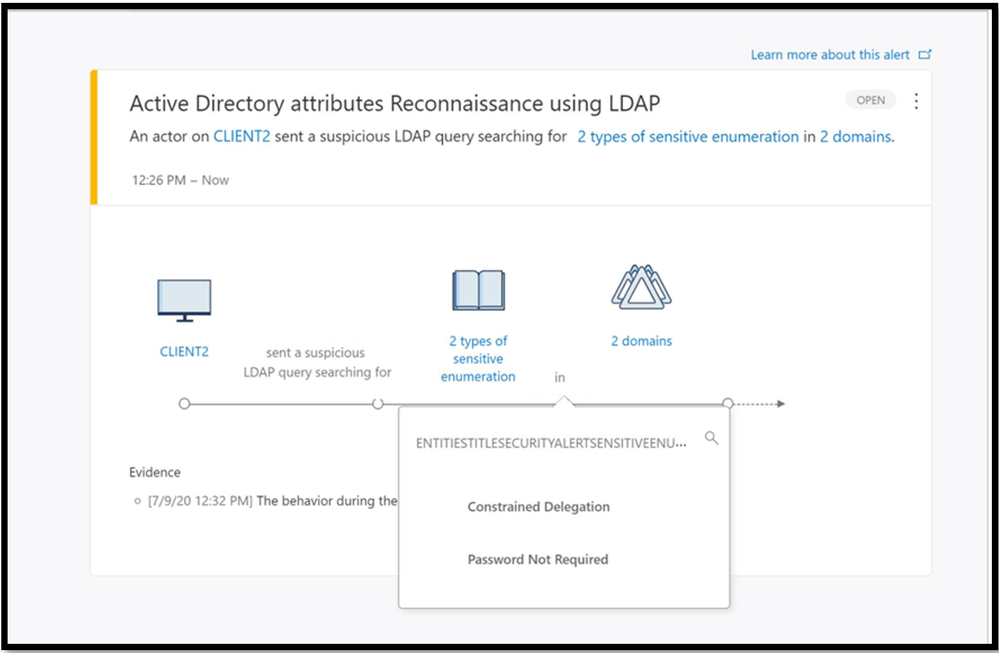
The reconnaissance portion often involves the attacker preforming enumeration techniques to find users that have the pre-authentication attribute turned off. If the reconnaissance was performed with LDAP it will result in triggering Active Directory attributes reconnaissance (LDAP) alert. This alert triggers when certain attributes are enumerated.
The new detection we are announcing today, Suspected AS-REP Roasting attack helps identify AS-REQ messages without encrypted timestamps and AS-REP messages with TGT data.
This comprehensive protection against AS-REP roasting style attacks will be available in Defender for Identity starting from version 2.141. Try it out for yourselves, and as always, we’d love to hear your feedback on this new feature.

![[Upcoming Webinar] Enabling customers in their CMMC journey](https://www.drware.com/wp-content/uploads/2021/04/fb_image-4.jpeg)













Recent Comments