by Scott Muniz | Apr 5, 2021 | Security, Technology
This article is contributed. See the original author and article here.
accusoft — imagegear
|
An out-of-bounds write vulnerability exists in the TIFF header count-processing functionality of Accusoft ImageGear 19.8. A specially crafted malformed file can lead to memory corruption. An attacker can provide a malicious file to trigger this vulnerability. |
2021-03-31 |
not yet calculated |
CVE-2021-21773
MISC |
accusoft — imagegear
|
An out-of-bounds write vulnerability exists in the SGI Format Buffer Size Processing functionality of Accusoft ImageGear 19.8. A specially crafted malformed file can lead to memory corruption. An attacker can provide a malicious file to trigger this vulnerability. |
2021-03-31 |
not yet calculated |
CVE-2021-21776
MISC |
adobe — acrobat_reader_dc
|
Acrobat Reader DC versions versions 2020.013.20074 (and earlier), 2020.001.30018 (and earlier) and 2017.011.30188 (and earlier) are missing support for an integrity check. An unauthenticated attacker could leverage this vulnerability to modify content in a certified PDF without invalidating the certification. Exploitation of this issue requires user interaction in that a victim must open the tampered file. |
2021-04-01 |
not yet calculated |
CVE-2021-28546
MISC |
adobe — acrobat_reader_dc
|
Acrobat Reader DC versions versions 2020.013.20074 (and earlier), 2020.001.30018 (and earlier) and 2017.011.30188 (and earlier) are missing support for an integrity check. An unauthenticated attacker could leverage this vulnerability to show arbitrary content in a certified PDF without invalidating the certification. Exploitation of this issue requires user interaction in that a victim must open the tampered file. |
2021-04-01 |
not yet calculated |
CVE-2021-28545
MISC |
apache — cxf
|
CXF supports (via JwtRequestCodeFilter) passing OAuth 2 parameters via a JWT token as opposed to query parameters (see: The OAuth 2.0 Authorization Framework: JWT Secured Authorization Request (JAR)). Instead of sending a JWT token as a “request” parameter, the spec also supports specifying a URI from which to retrieve a JWT token from via the “request_uri” parameter. CXF was not validating the “request_uri” parameter (apart from ensuring it uses “https) and was making a REST request to the parameter in the request to retrieve a token. This means that CXF was vulnerable to DDos attacks on the authorization server, as specified in section 10.4.1 of the spec. This issue affects Apache CXF versions prior to 3.4.3; Apache CXF versions prior to 3.3.10. |
2021-04-02 |
not yet calculated |
CVE-2021-22696
MLIST
CONFIRM
MLIST
MLIST
MLIST
MLIST |
apple — ios_and_ipados
|
A logic issue was addressed with improved state management. This issue is fixed in iOS 14.3 and iPadOS 14.3. An enterprise application installation prompt may display the wrong domain. |
2021-04-02 |
not yet calculated |
CVE-2020-29613
MISC |
apple — ios_and_ipados
|
A lock screen issue allowed access to contacts on a locked device. This issue was addressed with improved state management. This issue is fixed in iOS 14.4 and iPadOS 14.4. An attacker with physical access to a device may be able to see private contact information. |
2021-04-02 |
not yet calculated |
CVE-2021-1756
MISC |
apple — ios_and_ipados
|
A memory initialization issue was addressed with improved memory handling. This issue is fixed in iOS 14.4 and iPadOS 14.4. An attacker in a privileged position may be able to perform a denial of service attack. |
2021-04-02 |
not yet calculated |
CVE-2021-1780
MISC |
apple — ios_and_ipados
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in iOS 14.0 and iPadOS 14.0. Processing a maliciously crafted font may result in the disclosure of process memory. |
2021-04-02 |
not yet calculated |
CVE-2020-29639
MISC |
apple — ios_and_ipados
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in iOS 14.4 and iPadOS 14.4. A remote attacker may be able to cause arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1794
MISC |
apple — ios_and_ipados
|
An out-of-bounds write was addressed with improved input validation. This issue is fixed in iOS 14.4 and iPadOS 14.4. A remote attacker may be able to cause arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1795
MISC |
apple — ios_and_ipados
|
An out-of-bounds write was addressed with improved input validation. This issue is fixed in iOS 14.4 and iPadOS 14.4. A remote attacker may be able to cause arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1796
MISC |
apple — macos
|
KIS for macOS in some use cases was vulnerable to AV bypass that potentially allowed an attacker to disable anti-virus protection. |
2021-04-01 |
not yet calculated |
CVE-2021-26718
MISC |
apple — macos
|
An issue existed in the parsing of URLs. This issue was addressed with improved input validation. This issue is fixed in macOS Server 5.11. Processing a maliciously crafted URL may lead to an open redirect or cross site scripting. |
2021-04-02 |
not yet calculated |
CVE-2020-9995
MISC |
apple — macos
|
OpenVPN Connect installer for macOS version 3.2.6 and older may corrupt system critical files it should not have access via symlinks in /tmp. |
2021-03-30 |
not yet calculated |
CVE-2020-15075
MISC |
| apple — macos_big_sur |
A lock screen issue allowed access to contacts on a locked device. This issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.0.1. A person with physical access to an iOS device may be able to access contacts from the lock screen. |
2021-04-02 |
not yet calculated |
CVE-2021-1755
MISC |
apple — macos_big_sur
|
An issue existed in screen sharing. This issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.0.1. A user with screen sharing access may be able to view another user’s screen. |
2021-04-02 |
not yet calculated |
CVE-2020-27893
MISC |
apple — macos_big_sur
|
An out-of-bounds write issue was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1. An application may be able to execute arbitrary code with kernel privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-27897
MISC
MISC |
apple — macos_big_sur
|
An out-of-bounds write issue was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1. An application may be able to execute arbitrary code with kernel privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-10015
MISC
MISC |
apple — macos_big_sur
|
An input validation issue was addressed with improved memory handling. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. A malicious application may be able to read restricted memory. |
2021-04-02 |
not yet calculated |
CVE-2020-10001
MISC |
apple — macos_big_sur
|
A logic issue was addressed with improved restrictions. This issue is fixed in macOS Big Sur 11.0.1. A malicious application with root privileges may be able to access private information. |
2021-04-02 |
not yet calculated |
CVE-2020-10008
MISC |
| apple — multiple_products |
A use after free issue was addressed with improved memory management. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1, iOS 14.2 and iPadOS 14.2, watchOS 7.1, tvOS 14.2. Processing maliciously crafted web content may lead to code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27920
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
This issue was addressed with improved iframe sandbox enforcement. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Maliciously crafted web content may violate iframe sandboxing policy. |
2021-04-02 |
not yet calculated |
CVE-2021-1801
FEDORA
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds write was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27919
MISC
MISC |
| apple — multiple_products |
A port redirection issue was addressed with additional port validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, tvOS 14.4, watchOS 7.3, iOS 14.4 and iPadOS 14.4, Safari 14.0.3. A malicious website may be able to access restricted ports on arbitrary servers. |
2021-04-02 |
not yet calculated |
CVE-2021-1799
FEDORA
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A memory corruption issue was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1. A malicious application may be able to execute arbitrary code with system privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-27914
MISC
MISC |
| apple — multiple_products |
An out-of-bounds write issue was addressed with improved bounds checking. This issue is fixed in watchOS 7.2, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, tvOS 14.3. Processing a maliciously crafted audio file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27948
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A logic issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A remote attacker may be able to cause unexpected application termination or arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1818
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A logic issue was addressed with improved restrictions. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, iOS 14.4 and iPadOS 14.4. A remote attacker may be able to cause arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited.. |
2021-04-02 |
not yet calculated |
CVE-2021-1871
FEDORA
MISC
MISC |
| apple — multiple_products |
An out-of-bounds write issue was addressed with improved bounds checking. This issue is fixed in tvOS 14.3, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, iCloud for Windows 12.0, watchOS 7.2. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-29611
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
Multiple issues were addressed with improved logic. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. An application may be able to execute arbitrary code with kernel privileges. |
2021-04-02 |
not yet calculated |
CVE-2021-1750
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds write was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1, iOS 14.2 and iPadOS 14.2, watchOS 7.1, tvOS 14.2. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27923
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A logic issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1, iOS 14.2 and iPadOS 14.2, watchOS 7.1, tvOS 14.2. Processing a maliciously crafted font file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27922
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, tvOS 14.3, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, watchOS 7.2. A remote attacker may be able to leak memory. |
2021-04-02 |
not yet calculated |
CVE-2020-29608
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A memory corruption issue existed in the processing of font files. This issue was addressed with improved input validation. This issue is fixed in iOS 14.0 and iPadOS 14.0, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1, watchOS 7.0, tvOS 14.0. Processing a maliciously crafted font file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27931
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. A local user may be able to cause unexpected system termination or read kernel memory. |
2021-04-02 |
not yet calculated |
CVE-2020-27936
MISC |
| apple — multiple_products |
A logic issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, macOS Big Sur 11.0.1. A malicious application may be able to access private information. |
2021-04-02 |
not yet calculated |
CVE-2020-27937
MISC
MISC |
| apple — multiple_products |
Multiple issues were addressed with improved logic. This issue is fixed in iOS 14.2 and iPadOS 14.2, macOS Big Sur 11.0.1, watchOS 7.1, tvOS 14.2. A sandboxed process may be able to circumvent sandbox restrictions. |
2021-04-02 |
not yet calculated |
CVE-2020-27935
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A memory corruption issue existed in the processing of font files. This issue was addressed with improved input validation. This issue is fixed in tvOS 14.3, iOS 14.3 and iPadOS 14.3, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, watchOS 7.2. Processing a maliciously crafted font file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27943
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An integer overflow was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, macOS Big Sur 11.0.1. Processing maliciously crafted web content may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27945
MISC
MISC |
| apple — multiple_products |
This issue was addressed with improved checks. This issue is fixed in watchOS 6.3, iOS 12.5, iOS 14.3 and iPadOS 14.3, watchOS 7.2. Unauthorized code execution may lead to an authentication policy violation. |
2021-04-02 |
not yet calculated |
CVE-2020-27951
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An information disclosure issue was addressed with improved state management. This issue is fixed in watchOS 7.2, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, tvOS 14.3. Processing a maliciously crafted font may result in the disclosure of process memory. |
2021-04-02 |
not yet calculated |
CVE-2020-27946
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave. Processing a maliciously crafted font may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1790
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A remote attacker may be able to cause arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1792
MISC
MISC
MISC
MISC |
| apple — multiple_products |
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A remote attacker may be able to cause a denial of service. |
2021-04-02 |
not yet calculated |
CVE-2021-1761
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1736
MISC |
| apple — multiple_products |
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27939
MISC |
| apple — multiple_products |
An out-of-bounds write was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1744
MISC
MISC
MISC
MISC |
| apple — multiple_products |
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. A malicious application may be able to bypass Privacy preferences. |
2021-04-02 |
not yet calculated |
CVE-2020-29621
MISC |
| apple — multiple_products |
An out-of-bounds read issue existed in the curl. This issue was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to a denial of service. |
2021-04-02 |
not yet calculated |
CVE-2021-1778
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A buffer overflow was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted USD file may lead to unexpected application termination or arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1763
MISC
MISC |
| apple — multiple_products |
A stack overflow was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted text file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1772
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A local attacker may be able to elevate their privileges. |
2021-04-02 |
not yet calculated |
CVE-2021-1757
MISC
MISC
MISC
MISC |
| apple — multiple_products |
This issue was addressed by removing the vulnerable code. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave. Processing a maliciously crafted font may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1775
MISC |
| apple — multiple_products |
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1746
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A memory corruption issue existed in the processing of font files. This issue was addressed with improved input validation. This issue is fixed in watchOS 7.2, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, tvOS 14.3. Processing a maliciously crafted font file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-29624
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A race condition was addressed with improved locking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A malicious application may be able to elevate privileges. Apple is aware of a report that this issue may have been actively exploited.. |
2021-04-02 |
not yet calculated |
CVE-2021-1782
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved input validation. This issue is fixed in tvOS 14.3, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, iCloud for Windows 12.0, watchOS 7.2. Processing a maliciously crafted image may lead to heap corruption. |
2021-04-02 |
not yet calculated |
CVE-2020-29617
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved input validation. This issue is fixed in watchOS 7.2, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, tvOS 14.3. Processing a maliciously crafted image may lead to a denial of service. |
2021-04-02 |
not yet calculated |
CVE-2020-29615
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1785
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A logic issue was addressed with improved validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A malicious attacker with arbitrary read and write capability may be able to bypass Pointer Authentication. |
2021-04-02 |
not yet calculated |
CVE-2021-1769
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1753
MISC
MISC |
| apple — multiple_products |
This issue was addressed with improved setting propagation. This issue is fixed in macOS Big Sur 11.0.1, tvOS 14.0, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, watchOS 7.0, iOS 14.0 and iPadOS 14.0. An attacker in a privileged network position may be able to unexpectedly alter application state. |
2021-04-02 |
not yet calculated |
CVE-2020-9978
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1742
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds write was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1738
MISC |
| apple — multiple_products |
An out-of-bounds write issue was addressed with improved bounds checking. This issue is fixed in watchOS 7.0, tvOS 14.0, iOS 14.0 and iPadOS 14.0, macOS Big Sur 11.0.1. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-9955
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds write was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing maliciously crafted web content may lead to code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1747
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A memory corruption issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A malicious application could execute arbitrary code leading to compromise of user information. |
2021-04-02 |
not yet calculated |
CVE-2021-1760
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A use after free issue was addressed with improved memory management. This issue is fixed in macOS Big Sur 11.0.1, tvOS 14.0, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, watchOS 7.0, iOS 14.0 and iPadOS 14.0. An application may be able to execute arbitrary code with kernel privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-9975
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
Multiple memory corruption issues were addressed with improved input validation. This issue is fixed in macOS Big Sur 11.0.1, tvOS 14.0, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, watchOS 7.0, iOS 14.0 and iPadOS 14.0. A remote attacker may be able to cause unexpected system termination or corrupt kernel memory. |
2021-04-02 |
not yet calculated |
CVE-2020-9967
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
A buffer overflow was addressed with improved size validation. This issue is fixed in macOS Big Sur 11.0.1, tvOS 14.0, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, watchOS 7.0, iOS 14.0 and iPadOS 14.0. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-9962
MISC
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A remote attacker may be able to cause arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1758
MISC
MISC
MISC
MISC |
| apple — multiple_products |
An out-of-bounds read was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.0.1, tvOS 14.0, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, watchOS 7.0, iOS 14.0 and iPadOS 14.0. Processing a maliciously crafted audio file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-9960
MISC
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A logic issue was addressed with improved restrictions. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1. A sandboxed process may be able to circumvent sandbox restrictions. |
2021-04-02 |
not yet calculated |
CVE-2020-27901
MISC
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1, iOS 14.2 and iPadOS 14.2, watchOS 7.1, tvOS 14.2. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27924
MISC
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A memory corruption issue was addressed with improved memory handling. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1. An application may be able to execute arbitrary code with kernel privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-27907
MISC
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1, iOS 14.2 and iPadOS 14.2, watchOS 7.1, tvOS 14.2. Processing a maliciously crafted audio file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27908
MISC
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A memory corruption issue was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1. A malicious application may be able to execute arbitrary code with system privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-27915
MISC
MISC |
apple — multiple_products
|
A race condition was addressed with improved state handling. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1. An application may be able to execute arbitrary code with kernel privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-27921
MISC
MISC |
apple — multiple_products
|
A memory corruption issue was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. An application may be able to execute arbitrary code with kernel privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-27947
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in tvOS 14.3, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, iCloud for Windows 12.0, watchOS 7.2. Processing a maliciously crafted image may lead to heap corruption. |
2021-04-02 |
not yet calculated |
CVE-2020-29619
MISC
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A memory corruption issue was addressed with improved input validation. This issue is fixed in iOS 13.6 and iPadOS 13.6, iCloud for Windows 7.20, watchOS 6.2.8, tvOS 13.4.8, macOS Catalina 10.15.6, Security Update 2020-004 Mojave, Security Update 2020-004 High Sierra. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27933
MISC
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A memory corruption issue existed in the processing of font files. This issue was addressed with improved input validation. This issue is fixed in watchOS 7.2, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, tvOS 14.3. Processing a maliciously crafted font file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27944
MISC
MISC
MISC
MISC |
apple — multiple_products
|
An out-of-bounds write was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, macOS Big Sur 11.0.1. Processing a maliciously crafted font file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-27952
MISC
MISC |
apple — multiple_products
|
This issue was addressed with improved checks to prevent unauthorized actions. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. A malicious application may cause unexpected changes in memory belonging to processes traced by DTrace. |
2021-04-02 |
not yet calculated |
CVE-2020-27949
MISC |
apple — multiple_products
|
A logic issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave. Mounting a maliciously crafted Samba network share may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1751
MISC |
apple — multiple_products
|
A use after free issue was addressed with improved memory management. This issue is fixed in iOS 14.2 and iPadOS 14.2, macOS Big Sur 11.0.1, watchOS 7.1, tvOS 14.2. A local attacker may be able to elevate their privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-27899
MISC
MISC
MISC
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in macOS Catalina 10.15.6, Security Update 2020-004 Mojave, Security Update 2020-004 High Sierra. A local user may be able to cause unexpected system termination or read kernel memory. |
2021-04-02 |
not yet calculated |
CVE-2020-9930
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in tvOS 14.3, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, iCloud for Windows 12.0, watchOS 7.2. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-29618
MISC
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A validation issue was addressed with improved logic. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. An application may be able to execute arbitrary code with kernel privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-27941
MISC |
apple — multiple_products
|
This issue was addressed with improved entitlements. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. A malicious application may be able to elevate privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-29620
MISC |
apple — multiple_products
|
An out-of-bounds write was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1737
MISC |
apple — multiple_products
|
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-29625
MISC |
apple — multiple_products
|
An authentication issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. An attacker in a privileged network position may be able to bypass authentication policy. |
2021-04-02 |
not yet calculated |
CVE-2020-29633
MISC
MISC |
apple — multiple_products
|
“Clear History and Website Data” did not clear the history. The issue was addressed with improved data deletion. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, tvOS 14.3. A user may be unable to fully delete browsing history. |
2021-04-02 |
not yet calculated |
CVE-2020-29623
FEDORA
MISC
MISC
MISC |
apple — multiple_products
|
A validation issue was addressed with improved input sanitization. This issue is fixed in tvOS 14.4, watchOS 7.3, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted URL may lead to arbitrary javascript code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1748
MISC
MISC
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted USD file may lead to unexpected application termination or arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1745
MISC
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1743
MISC
MISC
MISC
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1741
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A use after free issue was addressed with improved memory management. This issue is fixed in iOS 13.6 and iPadOS 13.6, tvOS 13.4.8, watchOS 6.2.8, iCloud for Windows 7.20, macOS Catalina 10.15.6, Security Update 2020-004 Mojave, Security Update 2020-004 High Sierra. Processing maliciously crafted XML may lead to an unexpected application termination or arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-9926
MISC
MISC
MISC
MISC
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.0.1, tvOS 14.0, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, watchOS 7.0, iOS 14.0 and iPadOS 14.0. Processing a maliciously crafted font file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-9956
MISC
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A logic issue was addressed with improved validation. This issue is fixed in watchOS 7.0, tvOS 14.0, iOS 14.0 and iPadOS 14.0, macOS Big Sur 11.0.1. A malicious application may be able to elevate privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-9971
MISC
MISC
MISC
MISC |
apple — multiple_products
|
An out-of-bounds write issue was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. A malicious application may be able to execute arbitrary code with system privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-29612
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in watchOS 7.2, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, tvOS 14.3. Processing a maliciously crafted audio file may disclose restricted memory. |
2021-04-02 |
not yet calculated |
CVE-2020-29610
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A race condition was addressed with additional validation. This issue is fixed in macOS Big Sur 11.2.1, macOS Catalina 10.15.7 Supplemental Update, macOS Mojave 10.14.6 Security Update 2021-002. An application may be able to execute arbitrary code with kernel privileges. |
2021-04-02 |
not yet calculated |
CVE-2021-1806
MISC |
apple — multiple_products
|
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave, iOS 14.3 and iPadOS 14.3, tvOS 14.3. Processing a maliciously crafted file may lead to heap corruption. |
2021-04-02 |
not yet calculated |
CVE-2020-29614
MISC
MISC
MISC
MISC |
apple — multiple_products
|
The issue was addressed with improved permissions logic. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A local user may be able to read arbitrary files. |
2021-04-02 |
not yet calculated |
CVE-2021-1797
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A memory corruption issue was addressed with improved validation. This issue is fixed in iOS 14.4.1 and iPadOS 14.4.1, Safari 14.0.3 (v. 14610.4.3.1.7 and 15610.4.3.1.7), watchOS 7.3.2, macOS Big Sur 11.2.3. Processing maliciously crafted web content may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1844
FEDORA
MISC
MISC
MISC
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1759
MISC
MISC
MISC |
apple — multiple_products
|
A logic issue was addressed with improved restrictions. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, iOS 14.4 and iPadOS 14.4. A remote attacker may be able to cause arbitrary code execution. Apple is aware of a report that this issue may have been actively exploited.. |
2021-04-02 |
not yet calculated |
CVE-2021-1870
FEDORA
MISC
MISC |
apple — multiple_products
|
An out-of-bounds write was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2.1, macOS Catalina 10.15.7 Supplemental Update, macOS Mojave 10.14.6 Security Update 2021-002. An application may be able to execute arbitrary code with kernel privileges. |
2021-04-02 |
not yet calculated |
CVE-2021-1805
MISC |
apple — multiple_products
|
The issue was addressed with improved permissions logic. This issue is fixed in macOS Big Sur 11.0.1. A local application may be able to enumerate the user’s iCloud documents. |
2021-04-02 |
not yet calculated |
CVE-2021-1803
MISC |
apple — multiple_products
|
A logic issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave. A local attacker may be able to elevate their privileges. |
2021-04-02 |
not yet calculated |
CVE-2021-1802
MISC |
apple — multiple_products
|
This issue was addressed by improved management of object lifetimes. This issue is fixed in iOS 12.5.2, iOS 14.4.2 and iPadOS 14.4.2, watchOS 7.3.3. Processing maliciously crafted web content may lead to universal cross site scripting. Apple is aware of a report that this issue may have been actively exploited.. |
2021-04-02 |
not yet calculated |
CVE-2021-1879
MISC
MISC
MISC |
apple — multiple_products
|
A use after free issue was addressed with improved memory management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A remote attacker may be able to cause a denial of service. |
2021-04-02 |
not yet calculated |
CVE-2021-1764
MISC
MISC
MISC
MISC |
apple — multiple_products
|
An access issue was addressed with improved memory management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1783
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A type confusion issue was addressed with improved state handling. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, tvOS 14.4, watchOS 7.3, iOS 14.4 and iPadOS 14.4, Safari 14.0.3. Processing maliciously crafted web content may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1789
FEDORA
MISC
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A privacy issue existed in the handling of Contact cards. This was addressed with improved state management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, iOS 14.4 and iPadOS 14.4. A malicious application may be able to leak sensitive user information. |
2021-04-02 |
not yet calculated |
CVE-2021-1781
MISC
MISC |
apple — multiple_products
|
A memory corruption issue was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2020-29616
MISC |
apple — multiple_products
|
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1793
MISC
MISC
MISC
MISC |
apple — multiple_products
|
This issue was addressed with improved iframe sandbox enforcement. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave. Maliciously crafted web content may violate iframe sandboxing policy. |
2021-04-02 |
not yet calculated |
CVE-2021-1765
FEDORA
MISC |
apple — multiple_products
|
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to a denial of service. |
2021-04-02 |
not yet calculated |
CVE-2021-1766
MISC
MISC
MISC
MISC |
apple — multiple_products
|
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1777
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A logic issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, macOS Big Sur 11.1, Security Update 2020-001 Catalina, Security Update 2020-007 Mojave. A malicious application may be able to elevate privileges. |
2021-04-02 |
not yet calculated |
CVE-2020-27938
MISC
MISC |
apple — multiple_products
|
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1754
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A logic issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A local user may be able to create or modify system files. |
2021-04-02 |
not yet calculated |
CVE-2021-1786
MISC
MISC
MISC
MISC |
apple — multiple_products
|
An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed with improved input validation. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A malicious application may be able to disclose kernel memory. |
2021-04-02 |
not yet calculated |
CVE-2021-1791
MISC
MISC
MISC
MISC |
apple — multiple_products
|
An out-of-bounds write issue was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted font file may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1776
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A use after free issue was addressed with improved memory management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, tvOS 14.4, watchOS 7.3, iOS 14.4 and iPadOS 14.4, Safari 14.0.3. Processing maliciously crafted web content may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1788
FEDORA
MISC
MISC
MISC
MISC
MISC |
apple — multiple_products
|
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1774
MISC
MISC
MISC
MISC |
apple — multiple_products
|
A logic issue was addressed with improved state management. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to a denial of service. |
2021-04-02 |
not yet calculated |
CVE-2021-1773
MISC
MISC
MISC
MISC |
apple — multiple_products
|
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave. A user that is removed from an iMessage group could rejoin the group. |
2021-04-02 |
not yet calculated |
CVE-2021-1771
MISC |
apple — multiple_products
|
An out-of-bounds read was addressed with improved bounds checking. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted USD file may lead to unexpected application termination or arbitrary code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-1768
MISC
MISC |
apple — multiple_products
|
Multiple issues were addressed with improved logic. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, watchOS 7.3, tvOS 14.4, iOS 14.4 and iPadOS 14.4. A local attacker may be able to elevate their privileges. |
2021-04-02 |
not yet calculated |
CVE-2021-1787
MISC
MISC
MISC
MISC |
apple — multiple_products
|
This issue was addressed with improved checks. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave, iOS 14.4 and iPadOS 14.4. Processing a maliciously crafted image may lead to heap corruption. |
2021-04-02 |
not yet calculated |
CVE-2021-1767
MISC
MISC |
apple — multiple_products
|
A logic error in kext loading was addressed with improved state handling. This issue is fixed in macOS Big Sur 11.2, Security Update 2021-001 Catalina, Security Update 2021-001 Mojave. An application may be able to execute arbitrary code with system privileges. |
2021-04-02 |
not yet calculated |
CVE-2021-1779
MISC |
apple — xcode
|
A path handling issue was addressed with improved validation. This issue is fixed in Xcode 12.4. A malicious application may be able to access arbitrary files on the host device while running an app that uses on-demand resources with Xcode. |
2021-04-02 |
not yet calculated |
CVE-2021-1800
MISC |
asus — ux360ca_bios_laptops
|
The UX360CA BIOS through 303 on ASUS laptops allow an attacker (with the ring 0 privilege) to overwrite nearly arbitrary physical memory locations, including SMRAM, and execute arbitrary code in the SMM (issue 3 of 3). |
2021-03-31 |
not yet calculated |
CVE-2021-26943
CONFIRM
MISC |
btcpay — server
|
BTCPay Server before 1.0.7.1 mishandles the policy setting in which users can register (in Server Settings > Policies). This affects Docker use cases in which a mail server is configured. |
2021-04-01 |
not yet calculated |
CVE-2021-29251
MISC |
cms — made_simple
|
CMS Made Simple (CMSMS) 2.2.15 allows authenticated XSS via the /admin/addbookmark.php script through the Site Admin > My Preferences > Title field. |
2021-03-30 |
not yet calculated |
CVE-2021-28935
MISC |
cohesity — dataplatform
|
Undocumented Default Cryptographic Key Vulnerability in Cohesity DataPlatform version 6.3 prior 6.3.1g, 6.4 up to 6.4.1c and 6.5.1 through 6.5.1b. The ssh key can provide an attacker access to the linux system in the affected version. |
2021-04-02 |
not yet calculated |
CVE-2021-28123
CONFIRM |
cohesity — dataplatform
|
A man-in-the-middle vulnerability in Cohesity DataPlatform support channel in version 6.3 up to 6.3.1g, 6.4 up to 6.4.1c and 6.5.1 through 6.5.1b. Missing server authentication in impacted versions can allow an attacker to Man-in-the-middle (MITM) support channel UI session to Cohesity DataPlatform cluster. |
2021-04-02 |
not yet calculated |
CVE-2021-28124
CONFIRM |
confluence — server_and_data_center
|
The WidgetConnector plugin in Confluence Server and Confluence Data Center before version 5.8.6 allowed remote attackers to manipulate the content of internal network resources via a blind Server-Side Request Forgery (SSRF) vulnerability. |
2021-04-01 |
not yet calculated |
CVE-2021-26072
MISC |
conquest — dicom_server
|
CONQUEST DICOM SERVER before 1.5.0 has a code execution vulnerability which can be exploited by attackers to execute malicious code. |
2021-03-31 |
not yet calculated |
CVE-2020-35308
MISC |
core — ltp_le
|
Buffer overflow in Core FTP LE v2.2 allows local attackers to cause a denial or service (crash) via a long string in the Setup->Users->Username editbox. |
2021-04-02 |
not yet calculated |
CVE-2020-21588
MISC
MISC |
coursems — coursems
|
CourseMS (aka Course Registration Management System) 2.1 is affected by cross-site scripting (XSS). When an attacker with access to an Admin account creates a Job Title in the Site area (aka the admin/add_jobs.php name parameter), they can insert an XSS payload. This payload will execute whenever anyone visits the registration page. |
2021-03-31 |
not yet calculated |
CVE-2021-29663
MISC
MISC |
curl — curl
|
curl 7.63.0 to and including 7.75.0 includes vulnerability that allows a malicious HTTPS proxy to MITM a connection due to bad handling of TLS 1.3 session tickets. When using a HTTPS proxy and TLS 1.3, libcurl can confuse session tickets arriving from the HTTPS proxy but work as if they arrived from the remote server and then wrongly “short-cut” the host handshake. When confusing the tickets, a HTTPS proxy can trick libcurl to use the wrong session ticket resume for the host and thereby circumvent the server TLS certificate check and make a MITM attack to be possible to perform unnoticed. Note that such a malicious HTTPS proxy needs to provide a certificate that curl will accept for the MITMed server for an attack to work – unless curl has been told to ignore the server certificate check. |
2021-04-01 |
not yet calculated |
CVE-2021-22890
MISC
MISC
FEDORA |
curl — curl
|
curl 7.1.1 to and including 7.75.0 is vulnerable to an “Exposure of Private Personal Information to an Unauthorized Actor” by leaking credentials in the HTTP Referer: header. libcurl does not strip off user credentials from the URL when automatically populating the Referer: HTTP request header field in outgoing HTTP requests, and therefore risks leaking sensitive data to the server that is the target of the second HTTP request. |
2021-04-01 |
not yet calculated |
CVE-2021-22876
MISC
MISC
FEDORA |
d-link — dir-816_devices
|
D-link DIR-816 A2 v1.10 is affected by a remote code injection vulnerability. An HTTP request parameter can be used in command string construction in the handler function of the /goform/dir_setWanWifi, which can lead to command injection via shell metacharacters in the statuscheckpppoeuser parameter. |
2021-03-30 |
not yet calculated |
CVE-2021-26810
MISC
MISC |
d-link — dir-846_routers
|
HNAP1/control/SetMasterWLanSettings.php in D-Link D-Link Router DIR-846 DIR-846 A1_100.26 allows remote attackers to execute arbitrary commands via shell metacharacters in the ssid0 or ssid1 parameter. |
2021-04-02 |
not yet calculated |
CVE-2020-27600
MISC
MISC
MISC |
d-link — dir-878_devices
|
An issue was discovered in prog.cgi on D-Link DIR-878 1.30B08 devices. Because strcat is misused, there is a stack-based buffer overflow that does not require authentication. |
2021-04-02 |
not yet calculated |
CVE-2021-30072
MISC
MISC |
dell — system_update
|
Dell System Update (DSU) 1.9 and earlier versions contain a denial of service vulnerability. A local authenticated malicious user with low privileges may potentially exploit this vulnerability to cause the system to run out of memory by running multiple instances of the vulnerable application. |
2021-04-02 |
not yet calculated |
CVE-2021-21529
MISC |
dell — wyse_management_suite
|
Wyse Management Suite versions up to 3.2 contains a vulnerability wherein a malicious authenticated user can cause a denial of service in the job status retrieval page, also affecting other users that would have normally access to the same subset of job details |
2021-04-02 |
not yet calculated |
CVE-2021-21533
MISC |
dell — wyse_thinos
|
Dell Wyse ThinOS 8.6 MR9 contains remediation for an improper management server validation vulnerability that could be potentially exploited to redirect a client to an attacker-controlled management server, thus allowing the attacker to change the device configuration or certificate file. |
2021-04-02 |
not yet calculated |
CVE-2021-21532
MISC |
| devolutions — remote_desktop_manager |
An issue was discovered in Devolutions Remote Desktop Manager before 2020.2.12. There is a cross-site scripting (XSS) vulnerability in webviews. |
2021-04-01 |
not yet calculated |
CVE-2021-23922
CONFIRM |
devolutions — remote_desktop_manager
|
Cross-Site Scripting (XSS) in Administrative Reports in Devolutions Remote Desktop Manager before 2021.1 allows remote authenticated users to inject arbitrary web script or HTML via multiple input fields. |
2021-04-01 |
not yet calculated |
CVE-2021-28047
CONFIRM |
devolutions — server
|
An issue was discovered in Devolutions Server before 2020.3. There is broken access control on Password List entry elements. |
2021-04-01 |
not yet calculated |
CVE-2021-23921
CONFIRM |
devolutions — server
|
An issue was discovered in Devolutions Server before 2020.3. There is an exposure of sensitive information in diagnostic files. |
2021-04-01 |
not yet calculated |
CVE-2021-23924
CONFIRM |
devolutions — server
|
An issue was discovered in Devolutions Server before 2020.3. There is Broken Authentication with Windows domain users. |
2021-04-01 |
not yet calculated |
CVE-2021-23923
CONFIRM |
devolutions — server
|
An issue was discovered in Devolutions Server before 2020.3. There is a cross-site scripting (XSS) vulnerability in entries of type Document. |
2021-04-01 |
not yet calculated |
CVE-2021-23925
CONFIRM |
django — django-registration
|
django-registration is a user registration package for Django. The django-registration package provides tools for implementing user-account registration flows in the Django web framework. In django-registration prior to 3.1.2, the base user-account registration view did not properly apply filters to sensitive data, with the result that sensitive data could be included in error reports rather than removed automatically by Django. Triggering this requires: A site is using django-registration < 3.1.2, The site has detailed error reports (such as Django’s emailed error reports to site staff/developers) enabled and a server-side error (HTTP 5xx) occurs during an attempt by a user to register an account. Under these conditions, recipients of the detailed error report will see all submitted data from the account-registration attempt, which may include the user’s proposed credentials (such as a password). |
2021-04-01 |
not yet calculated |
CVE-2021-21416
CONFIRM |
dma — softlab_radius_manager
|
DMA Softlab Radius Manager 4.4.0 is affected by Cross Site Scripting (XSS) via the description, name, or address field (under admin.php). |
2021-04-02 |
not yet calculated |
CVE-2021-29011
MISC
MISC |
dma — softlab_radius_manager
|
DMA Softlab Radius Manager 4.4.0 assigns the same session cookie to every admin session. The cookie is valid when the admin is logged in, but is invalid (temporarily) during times when the admin is logged out. In other words, the cookie is functionally equivalent to a static password, and thus provides permanent access if stolen. |
2021-04-02 |
not yet calculated |
CVE-2021-29012
MISC
MISC |
docsify — docsify
|
docsify 4.12.1 is affected by Cross Site Scripting (XSS) because the search component does not appropriately encode Code Blocks and mishandles the ” character. |
2021-04-02 |
not yet calculated |
CVE-2021-30074
MISC |
| eclipse — jetty |
In Eclipse Jetty 7.2.2 to 9.4.38, 10.0.0.alpha0 to 10.0.1, and 11.0.0.alpha0 to 11.0.1, CPU usage can reach 100% upon receiving a large invalid TLS frame. |
2021-04-01 |
not yet calculated |
CVE-2021-28165
CONFIRM |
eclipse — jetty
|
In Eclipse Jetty 9.4.37.v20210219 to 9.4.38.v20210224, the default compliance mode allows requests with URIs that contain %2e or %2e%2e segments to access protected resources within the WEB-INF directory. For example a request to /context/%2e/WEB-INF/web.xml can retrieve the web.xml file. This can reveal sensitive information regarding the implementation of a web application. |
2021-04-01 |
not yet calculated |
CVE-2021-28164
CONFIRM |
eclipse — jetty
|
In Eclipse Jetty 9.4.32 to 9.4.38, 10.0.0.beta2 to 10.0.1, and 11.0.0.beta2 to 11.0.1, if a user uses a webapps directory that is a symlink, the contents of the webapps directory is deployed as a static webapp, inadvertently serving the webapps themselves and anything else that might be in that directory. |
2021-04-01 |
not yet calculated |
CVE-2021-28163
CONFIRM |
emlog — emlog
|
Vulnerability in emlog v6.0.0 allows user to upload webshells via zip plugin module. |
2021-04-02 |
not yet calculated |
CVE-2020-21585
MISC
MISC |
episerver –find
|
An Open Redirect vulnerability in EpiServer Find before 13.2.7 allows an attacker to redirect users to untrusted websites via the _t_redirect parameter in a crafted URL, such as a /find_v2/_click URL. |
2021-03-31 |
not yet calculated |
CVE-2020-24550
MISC |
etsy — rest_api_client
|
node-etsy-client is a NodeJs Etsy ReST API Client. Applications that are using node-etsy-client and reporting client error to the end user will offer api key value too This is fixed in node-etsy-client v0.3.0 and later. |
2021-04-01 |
not yet calculated |
CVE-2021-21421
MISC
CONFIRM |
| f5 — big-ip |
On versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, 12.1.x before 12.1.5.3, and 11.6.x before 11.6.5.3, the upload functionality in BIG-IP Advanced WAF and BIG-IP ASM allows an authenticated user to upload files to the BIG-IP system using a call to an undisclosed iControl REST endpoint. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-23001
MISC |
| f5 — big-ip |
On BIG-IP versions 13.1.3.4-13.1.3.6 and 12.1.5.2, if the tmm.http.rfc.enforcement BigDB key is enabled in a BIG-IP system, or the Bad host header value is checked in the AFM HTTP security profile associated with a virtual server, in rare instances, a specific sequence of malicious requests may cause TMM to restart. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-23000
MISC |
| f5 — big-ip |
On BIG-IP Advanced WAF and BIG-IP ASM versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2, 14.1.x before 14.1.3.1, 13.1.x before 13.1.3.6, and 12.1.x before 12.1.5.3, DOM-based XSS on DoS Profile properties page. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22993
MISC |
| f5 — big-ip |
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2, 14.1.x before 14.1.3.1, 13.1.x before 13.1.3.6, 12.1.x before 12.1.5.3, and 11.6.x before 11.6.5.3, the Traffic Management Microkernel (TMM) process may produce a core file when undisclosed MPTCP traffic passes through a standard virtual server. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-23003
MISC |
| f5 — big-ip |
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, 12.1.x before 12.1.5.3, and 11.6.x before 11.6.5.3, SYN flood protection thresholds are not enforced in secure network address translation (SNAT) listeners. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22998
MISC |
| f5 — big-ip |
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2, 14.1.x before 14.1.3.1, 13.1.x before 13.1.3.6, 12.1.x before 12.1.5.3, and 11.6.x before 11.6.5.3, Multipath TCP (MPTCP) forwarding flows may be created on standard virtual servers without MPTCP enabled in the applied TCP profile. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-23004
MISC |
f5 — big-ip
|
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, 12.1.x before 12.1.5.3, and 11.6.x before 11.6.5.3, TMUI, also referred to as the Configuration utility, has an authenticated remote command execution vulnerability in undisclosed pages. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22988
MISC |
f5 — big-ip
|
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, and 12.1.x before 12.1.5.3, undisclosed requests to a virtual server may be incorrectly handled by the Traffic Management Microkernel (TMM) URI normalization, which may trigger a buffer overflow, resulting in a DoS attack. In certain situations, it may theoretically allow bypass of URL based access control or remote code execution (RCE). Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22991
MISC |
f5 — big-ip
|
On BIG-IP versions 14.1.4 and 16.0.1.1, when the Traffic Management Microkernel (TMM) process handles certain undisclosed traffic, it may start dropping all fragmented IP traffic. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-23007
MISC |
f5 — big-ip
|
When using BIG-IP APM 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, or all 12.1.x and 11.6.x versions or Edge Client versions 7.2.1.x before 7.2.1.1, 7.1.9.x before 7.1.9.8, or 7.1.8.x before 7.1.8.5, the session ID is visible in the arguments of the f5vpn.exe command when VPN is launched from the browser on a Windows system. Addressing this issue requires both the client and server fixes. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-23002
MISC |
f5 — big-ip
|
On versions 15.0.x before 15.1.0 and 14.1.x before 14.1.4, the BIG-IP system provides an option to connect HTTP/2 clients to HTTP/1.x servers. When a client is slow to accept responses and it closes a connection prematurely, the BIG-IP system may indefinitely retain some streams unclosed. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22999
MISC |
f5 — big-ip
|
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, 12.1.x before 12.1.5.3, and 11.6.x before 11.6.5.3 when running in Appliance mode, the Traffic Management User Interface (TMUI), also referred to as the Configuration utility, has an authenticated remote command execution vulnerability in undisclosed pages. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22987
MISC |
f5 — big-ip
|
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, 12.1.x before 12.1.5.3, and 11.6.x before 11.6.5.3, when running in Appliance mode with Advanced WAF or BIG-IP ASM provisioned, the TMUI, also referred to as the Configuration utility, has an authenticated remote command execution vulnerability in undisclosed pages. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22989
MISC |
f5 — big-ip
|
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, 12.1.x before 12.1.5.3, and 11.6.x before 11.6.5.3, undisclosed endpoints in iControl REST allow for a reflected XSS attack, which could lead to a complete compromise of the BIG-IP system if the victim user is granted the admin role. This vulnerability is due to an incomplete fix for CVE-2020-5948. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22994
MISC |
f5 — big-ip
|
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, 12.1.x before 12.1.5.3, and 11.6.x before 11.6.5.3, a malicious HTTP response to an Advanced WAF/BIG-IP ASM virtual server with Login Page configured in its policy may trigger a buffer overflow, resulting in a DoS attack. In certain situations, it may allow remote code execution (RCE), leading to complete system compromise. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22992
MISC |
f5 — big-ip
|
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, 12.1.x before 12.1.5.3, and 11.6.x before 11.6.5.3, on systems with Advanced WAF or BIG-IP ASM provisioned, the Traffic Management User Interface (TMUI), also referred to as the Configuration utility, has an authenticated remote command execution vulnerability in undisclosed pages. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22990
MISC |
f5 — big-ip
|
On BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, and 12.1.x before 12.1.5.3 amd BIG-IQ 7.1.0.x before 7.1.0.3 and 7.0.0.x before 7.0.0.2, the iControl REST interface has an unauthenticated remote command execution vulnerability. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22986
MISC
MISC
MISC |
| f5 — big-iq |
On all 7.x and 6.x versions (fixed in 8.0.0), when using a Quorum device for BIG-IQ high availability (HA) for automatic failover, BIG-IQ does not make use of Transport Layer Security (TLS) with the Corosync protocol. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-23005
MISC |
| f5 — big-iq |
On all 7.x and 6.x versions (fixed in 8.0.0), BIG-IQ high availability (HA) when using a Quorum device for automatic failover does not implement any form of authentication with the Corosync daemon. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22995
MISC |
f5 — big-iq
|
On all 7.x and 6.x versions (fixed in 8.0.0), undisclosed BIG-IQ pages have a reflected cross-site scripting vulnerability. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-23006
MISC |
f5 — big-iq_data_collection_device
|
On all 7.x versions (fixed in 8.0.0), when set up for auto failover, a BIG-IQ Data Collection Device (DCD) cluster member that receives an undisclosed message may cause the corosync process to abort. This behavior may lead to a denial-of-service (DoS) and impact the stability of a BIG-IQ high availability (HA) cluster. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22996
MISC |
| f5 — big-iq_ha_elasticsearch |
On all 7.x and 6.x versions (fixed in 8.0.0), BIG-IQ HA ElasticSearch service does not implement any form of authentication for the clustering transport services, and all data used by ElasticSearch for transport is unencrypted. Note: Software versions which have reached End of Software Development (EoSD) are not evaluated. |
2021-03-31 |
not yet calculated |
CVE-2021-22997
MISC |
fireeye — ex_3500_devices
|
eMPS 9.0.1.923211 on FireEye EX 3500 devices allows remote authenticated users to conduct SQL injection attacks via the sort_by parameter to the email search feature. According to the vendor, the issue is fixed in 9.0.3. NOTE: this is different from CVE-2020-25034 and affects newer versions of the software. |
2021-04-01 |
not yet calculated |
CVE-2021-28969
MISC |
fireeye — ex_3500_devices
|
eMPS 9.0.1.923211 on the Central Management of FireEye EX 3500 devices allows remote authenticated users to conduct SQL injection attacks via the job_id parameter to the email search feature. According to the vendor, the issue is fixed in 9.0.3. |
2021-04-01 |
not yet calculated |
CVE-2021-28970
MISC |
flycms — flycms
|
Server Side Request Forgery (SSRF) vulnerability in saveUrlAs function in ImagesService.java in sunkaifei FlyCMS version 20190503. |
2021-04-01 |
not yet calculated |
CVE-2020-19613
MISC |
github — enterprise_server
|
An improper access control vulnerability was identified in GitHub Enterprise Server that allowed access tokens generated from a GitHub App’s web authentication flow to read private repository metadata via the REST API without having been granted the appropriate permissions. To exploit this vulnerability, an attacker would need to create a GitHub App on the instance and have a user authorize the application through the web authentication flow. The private repository metadata returned would be limited to repositories owned by the user the token identifies. This vulnerability affected all versions of GitHub Enterprise Server prior to 3.0.4 and was fixed in versions 3.0.4, 2.22.10, 2.21.18. This vulnerability was reported via the GitHub Bug Bounty program. |
2021-04-02 |
not yet calculated |
CVE-2021-22865
MISC
MISC
MISC |
github — gitbuh
|
A deadlock vulnerability was found in ‘github.com/containers/storage’ in versions before 1.28.1. When a container image is processed, each layer is unpacked using `tar`. If one of those layers is not a valid `tar` archive this causes an error leading to an unexpected situation where the code indefinitely waits for the tar unpacked stream, which never finishes. An attacker could use this vulnerability to craft a malicious image, which when downloaded and stored by an application using containers/storage, would then cause a deadlock leading to a Denial of Service (DoS). |
2021-04-01 |
not yet calculated |
CVE-2021-20291
MISC |
| gitlab — ce/ee |
An issue has been discovered in GitLab CE/EE affecting all versions starting from 13.9. A specially crafted import file could read files on the server. |
2021-04-02 |
not yet calculated |
CVE-2021-22201
CONFIRM
MISC
MISC |
gitlab — ce/ee
|
An issue has been discovered in GitLab CE/EE affecting all previous versions. If the victim is an admin, it was possible to issue a CSRF in System hooks through the API. |
2021-04-02 |
not yet calculated |
CVE-2021-22202
CONFIRM
MISC
MISC |
gitlab — ce/ee
|
An issue has been discovered in GitLab CE/EE affecting all versions starting with 12.6. Under a special condition it was possible to access data of an internal repository through a public project fork as an anonymous user. |
2021-04-02 |
not yet calculated |
CVE-2021-22200
CONFIRM
MISC |
gitlab — ce/ee
|
An issue has been discovered in GitLab CE/EE affecting all versions from 13.8 and above allowing an authenticated user to delete incident metric images of public projects. |
2021-04-02 |
not yet calculated |
CVE-2021-22198
CONFIRM
MISC
MISC |
gitlab — ce/ee
|
An issue has been discovered in GitLab CE/EE affecting all versions starting from 10.6 where an infinite loop exist when an authenticated user with specific rights access a MR having source and target branch pointing to each other |
2021-04-02 |
not yet calculated |
CVE-2021-22197
CONFIRM
MISC |
gitlab — ce/ee
|
An issue has been discovered in GitLab CE/EE affecting all versions starting from 13.4. It was possible to exploit a stored cross-site-scripting in merge request via a specifically crafted branch name. |
2021-04-02 |
not yet calculated |
CVE-2021-22196
CONFIRM
MISC
MISC |
gitlab — ce/ee
|
Client side code execution in gitlab-vscode-extension v3.15.0 and earlier allows attacker to execute code on user system |
2021-04-01 |
not yet calculated |
CVE-2021-22195
CONFIRM
MISC |
gitlab — ce/ee
|
Potential DoS was identified in gitlab-shell in GitLab CE/EE version 12.6.0 or above, which allows an attacker to spike the server resource utilization via gitlab-shell command. |
2021-04-01 |
not yet calculated |
CVE-2021-22177
CONFIRM
MISC
MISC |
gitlab — ce/ee
|
An issue has been discovered in GitLab CE/EE affecting all versions starting with 13.7.9. A specially crafted Wiki page allowed attackers to read arbitrary files on the server. |
2021-04-02 |
not yet calculated |
CVE-2021-22203
CONFIRM
MISC
MISC |
gocd — gocd
|
In GoCD, versions 19.6.0 to 21.1.0 are vulnerable to Cross-Site Request Forgery due to missing CSRF protection at the `/go/api/config/backup` endpoint. An attacker can trick a victim to click on a malicious link which could change backup configurations or execute system commands in the post_backup_script field. |
2021-04-01 |
not yet calculated |
CVE-2021-25924
MISC
MISC |
google — exposure_notification_verification_server
|
A privilege escalation vulnerability impacting the Google Exposure Notification Verification Server (versions prior to 0.23.1), allows an attacker who (1) has UserWrite permissions and (2) is using a carefully crafted request or malicious proxy, to create another user with higher privileges than their own. This occurs due to insufficient checks on the allowed set of permissions. The new user creation event would be captured in the Event Log. |
2021-03-31 |
not yet calculated |
CVE-2021-22538
CONFIRM
CONFIRM
CONFIRM
CONFIRM |
hewlett_packard_enterprises — ilo_amplified_pack
|
A potential security vulnerability has been identified in HPE iLO Amplifier Pack. The vulnerability could be remotely exploited to allow Cross-Site Scripting (XSS). HPE has provided the following software update to resolve the vulnerability in HPE iLO Amplifier Pack: HPE iLO Amplifier Pack 1.80 or later. |
2021-04-01 |
not yet calculated |
CVE-2021-26580
MISC |
hewlett_packard_enterprises — superdome_flex_server
|
A potential security vulnerability has been identified in HPE Superdome Flex server. A denial of service attack can be remotely exploited leaving hung connections to the BMC web interface. The monarch BMC must be rebooted to recover from this situation. Other BMC management is not impacted. HPE has made the following software update to resolve the vulnerability in HPE Superdome Flex Server: Superdome Flex Server Firmware 3.30.142 or later. |
2021-04-01 |
not yet calculated |
CVE-2021-26581
MISC |
| huawei — smartphone |
An application bypass mechanism vulnerability exists in a component interface of Huawei Smartphone. Local attackers can exploit this vulnerability to delete user SMS messages. |
2021-04-01 |
not yet calculated |
CVE-2020-9148
MISC |
huawei — smartphone
|
A memory buffer error vulnerability exists in a component interface of Huawei Smartphone. Local attackers can exploit this vulnerability to cause memory leakage and doS attacks by carefully constructing attack scenarios. |
2021-04-01 |
not yet calculated |
CVE-2020-9146
MISC |
huawei — smartphone
|
An application error verification vulnerability exists in a component interface of Huawei Smartphone. Local attackers can exploit this vulnerability to modify and delete user SMS messages. |
2021-04-01 |
not yet calculated |
CVE-2020-9149
MISC |
huawei — smartphone
|
A memory buffer error vulnerability exists in a component interface of Huawei Smartphone. Local attackers may exploit this vulnerability by carefully constructing attack scenarios to cause out-of-bounds read. |
2021-04-01 |
not yet calculated |
CVE-2020-9147
MISC |
isolated-vm — isolated-vm
|
isolated-vm is a library for nodejs which gives you access to v8’s Isolate interface. Versions of isolated-vm before v4.0.0 have API pitfalls which may make it easy for implementers to expose supposed secure isolates to the permissions of the main nodejs isolate. Reference objects allow access to the underlying reference’s full prototype chain. In an environment where the implementer has exposed a Reference instance to an attacker they would be able to use it to acquire a Reference to the nodejs context’s Function object. Similar application-specific attacks could be possible by modifying the local prototype of other API objects. Access to NativeModule objects could allow an attacker to load and run native code from anywhere on the filesystem. If combined with, for example, a file upload API this would allow for arbitrary code execution. This is addressed in v4.0.0 through a series of related changes. |
2021-03-30 |
not yet calculated |
CVE-2021-21413
MISC
MISC
MISC
CONFIRM |
jamf — pro
|
Jamf Pro before 10.28.0 allows XSS related to inventory history, aka PI-009376. |
2021-04-02 |
not yet calculated |
CVE-2021-30125
MISC |
jenkins — rest_list_parameter_plugin
|
Jenkins REST List Parameter Plugin 1.3.0 and earlier does not escape a parameter name reference in embedded JavaScript, resulting in a stored cross-site scripting (XSS) vulnerability exploitable by attackers with Job/Configure permission. |
2021-03-30 |
not yet calculated |
CVE-2021-21635
MLIST
CONFIRM |
jenkins — team_foundation_server_plugin
|
A missing permission check in Jenkins Team Foundation Server Plugin 5.157.1 and earlier allows attackers with Overall/Read permission to enumerate credentials ID of credentials stored in Jenkins. |
2021-03-30 |
not yet calculated |
CVE-2021-21636
MLIST
CONFIRM |
jenkins — team_foundation_server_plugin
|
A missing permission check in Jenkins Team Foundation Server Plugin 5.157.1 and earlier allows attackers with Overall/Read permission to connect to an attacker-specified URL using attacker-specified credentials IDs obtained through another method, capturing credentials stored in Jenkins. |
2021-03-30 |
not yet calculated |
CVE-2021-21637
MLIST
CONFIRM |
jira — server_and_data_center
|
The SetFeatureEnabled.jspa resource in Jira Server and Data Center before version 8.5.13, from version 8.6.0 before version 8.13.5, and from version 8.14.0 before version 8.15.1 allows remote anonymous attackers to enable and disable Jira Software configuration via a cross-site request forgery (CSRF) vulnerability. |
2021-04-01 |
not yet calculated |
CVE-2021-26071
MISC |
jira — server_and_data_center
|
The membersOf JQL search function in Jira Server and Data Center before version 8.5.13, from version 8.6.0 before version 8.13.5, and from version 8.14.0 before version 8.15.1 allows remote anonymous attackers to determine if a group exists & members of groups if they are assigned to publicly visible issue field. |
2021-04-01 |
not yet calculated |
CVE-2020-36286
N/A |
jira — server_and_data_center
|
The /rest/api/1.0/render resource in Jira Server and Data Center before version 8.5.13, from version 8.6.0 before version 8.13.5, and from version 8.14.0 before version 8.15.1 allows remote anonymous attackers to determine if a username is valid or not via a missing permissions check. |
2021-04-01 |
not yet calculated |
CVE-2020-36238
MISC |
kopano — groupware_core
|
kopano-ical (formerly zarafa-ical) in Kopano Groupware Core through 8.7.16, 9.x through 9.1.0, 10.x through 10.0.7, and 11.x through 11.0.1 and Zarafa 6.30.x through 7.2.x allows memory exhaustion via long HTTP headers. |
2021-03-31 |
not yet calculated |
CVE-2021-28994
MLIST
MISC |
latrix — latrix
|
An issue was discovered in LATRIX 0.6.0. SQL injection in the txtaccesscode parameter of inandout.php leads to information disclosure and code execution. |
2021-04-02 |
not yet calculated |
CVE-2021-30000
MISC
MISC |
lightmeter — controlcenter
|
Lightmeter ControlCenter 1.1.0 through 1.5.x before 1.5.1 allows anyone who knows the URL of a publicly available Lightmeter instance to access application settings, possibly including an SMTP password and a Slack access token, via a settings HTTP query. |
2021-04-02 |
not yet calculated |
CVE-2021-30126
MISC |
| linux — linux_kernel |
An issue was discovered in the Linux kernel before 5.11.11. The BPF subsystem does not properly consider that resolved_ids and resolved_sizes are intentionally uninitialized in the vmlinux BPF Type Format (BTF), which can cause a system crash upon an unexpected access attempt (in map_create in kernel/bpf/syscall.c or check_btf_info in kernel/bpf/verifier.c), aka CID-350a5c4dd245. |
2021-03-30 |
not yet calculated |
CVE-2021-29648
MISC
MISC
FEDORA
FEDORA
FEDORA |
linux — linux_kernel
|
An issue was discovered in the Linux kernel before 5.11.11. qrtr_recvmsg in net/qrtr/qrtr.c allows attackers to obtain sensitive information from kernel memory because of a partially uninitialized data structure, aka CID-50535249f624. |
2021-03-30 |
not yet calculated |
CVE-2021-29647
MISC
MISC
FEDORA
FEDORA
FEDORA |
linux — linux_kernel
|
An issue was discovered in the Linux kernel before 5.11.11. tipc_nl_retrieve_key in net/tipc/node.c does not properly validate certain data sizes, aka CID-0217ed2848e8. |
2021-03-30 |
not yet calculated |
CVE-2021-29646
MISC
MISC
FEDORA
FEDORA
FEDORA |
linux — linux_kernel
|
An issue was discovered in the Linux kernel before 5.11.11. The netfilter subsystem allows attackers to cause a denial of service (panic) because net/netfilter/x_tables.c and include/linux/netfilter/x_tables.h lack a full memory barrier upon the assignment of a new table value, aka CID-175e476b8cdf. |
2021-03-30 |
not yet calculated |
CVE-2021-29650
MISC
MISC
FEDORA
FEDORA
FEDORA |
linux — linux_kernel
|
An issue was discovered in the Linux kernel before 5.11.11. The user mode driver (UMD) has a copy_process() memory leak, related to a lack of cleanup steps in kernel/usermode_driver.c and kernel/bpf/preload/bpf_preload_kern.c, aka CID-f60a85cad677. |
2021-03-30 |
not yet calculated |
CVE-2021-29649
MISC
MISC
FEDORA
FEDORA
FEDORA |
linux — linux_kernel
|
An issue was discovered in the Linux kernel before 5.11.3 when a webcam device exists. video_usercopy in drivers/media/v4l2-core/v4l2-ioctl.c has a memory leak for large arguments, aka CID-fb18802a338b. |
2021-04-02 |
not yet calculated |
CVE-2021-30002
MISC
MISC
MISC |
luvion — grand_elite_3
|
An issue was discovered in Luvion Grand Elite 3 Connect through 2020-02-25. Authentication to the device is based on a username and password. The root credentials are the same across all devices of this model. |
2021-04-02 |
not yet calculated |
CVE-2020-11925
MISC |
magnolia — cms
|
Magnolia CMS From 6.1.3 to 6.2.3 contains a stored cross-site scripting (XSS) vulnerability in the setText parameter of /magnoliaAuthor/.magnolia/. |
2021-04-02 |
not yet calculated |
CVE-2021-25893
MISC
MISC
MISC |
magnolia — cms
|
Magnolia CMS contains a stored cross-site scripting (XSS) vulnerability in the /magnoliaPublic/travel/members/login.html mgnlUserId parameter. |
2021-04-02 |
not yet calculated |
CVE-2021-25894
MISC
MISC
MISC |
magpierss — magpierss
|
Because of a incorrect escaped exec command in MagpieRSS in 0.72 in the /extlib/Snoopy.class.inc file, it is possible to add a extra command to the curl binary. This creates an issue on the /scripts/magpie_debug.php and /scripts/magpie_simple.php page that if you send a specific https url in the RSS URL field, you are able to execute arbitrary commands. |
2021-04-02 |
not yet calculated |
CVE-2021-28940
MISC
MISC |
magpierss — magpierss
|
Because of no validation on a curl command in MagpieRSS 0.72 in the /extlib/Snoopy.class.inc file, when you send a request to the /scripts/magpie_debug.php or /scripts/magpie_simple.php page, it’s possible to request any internal page if you use a https request. |
2021-04-02 |
not yet calculated |
CVE-2021-28941
MISC
MISC |
mahara — mahara
|
Mahara 20.10 is affected by Cross Site Request Forgery (CSRF) that allows a remote attacker to remove inbox-mail on the server. The application fails to validate the CSRF token for a POST request. An attacker can craft a module/multirecipientnotification/inbox.php pieform_delete_all_notifications request, which leads to removing all messages from a mailbox. |
2021-03-31 |
not yet calculated |
CVE-2021-29349
MISC |
mobileiron — mobile@work
|
MobileIron Mobile@Work through 2021-03-22 allows attackers to distinguish among valid, disabled, and nonexistent user accounts by observing the number of failed login attempts needed to produce a Lockout error message |
2021-03-29 |
not yet calculated |
CVE-2021-3391
MISC
MISC
MISC |
mozilla — firefox
|
Mozilla developers reported memory safety bugs present in Firefox 86. Some of these bugs showed evidence of memory corruption and we presume that with enough effort some of these could have been exploited to run arbitrary code. This vulnerability affects Firefox < 87. |
2021-03-31 |
not yet calculated |
CVE-2021-23988
MISC
MISC |
mozilla — firefox
|
By causing a transition on a parent node by removing a CSS rule, an invalid property for a marker could have been applied, resulting in memory corruption and a potentially exploitable crash. This vulnerability affects Firefox < 87. |
2021-03-31 |
not yet calculated |
CVE-2021-23983
MISC
MISC |
mozilla — firefox
|
A malicious extension with the ‘search’ permission could have installed a new search engine whose favicon referenced a cross-origin URL. The response to this cross-origin request could have been read by the extension, allowing a same-origin policy bypass by the extension, which should not have cross-origin permissions. This cross-origin request was made without cookies, so the sensitive information disclosed by the violation was limited to local-network resources or resources that perform IP-based authentication. This vulnerability affects Firefox < 87. |
2021-03-31 |
not yet calculated |
CVE-2021-23986
MISC
MISC |
mozilla — firefox
|
If an attacker is able to alter specific about:config values (for example malware running on the user’s computer), the Devtools remote debugging feature could have been enabled in a way that was unnoticable to the user. This would have allowed a remote attacker (able to make a direct network connection to the victim) to monitor the user’s browsing activity and (plaintext) network traffic. This was addressed by providing a visual cue when Devtools has an open network socket. This vulnerability affects Firefox < 87. |
2021-03-31 |
not yet calculated |
CVE-2021-23985
MISC
MISC |
| mozilla — multiple_products |
Using techniques that built on the slipstream research, a malicious webpage could have scanned both an internal network’s hosts as well as services running on the user’s local machine utilizing WebRTC connections. This vulnerability affects Firefox ESR < 78.9, Thunderbird < 78.9, and Firefox < 87. |
2021-03-31 |
not yet calculated |
CVE-2021-23982
MISC
MISC
MISC
MISC |
mozilla — multiple_products
|
A malicious extension could have opened a popup window lacking an address bar. The title of the popup lacking an address bar should not be fully controllable, but in this situation was. This could have been used to spoof a website and attempt to trick the user into providing credentials. This vulnerability affects Firefox ESR < 78.9, Thunderbird < 78.9, and Firefox < 87. |
2021-03-31 |
not yet calculated |
CVE-2021-23984
MISC
MISC
MISC
MISC |
mozilla — multiple_products
|
A texture upload of a Pixel Buffer Object could have confused the WebGL code to skip binding the buffer used to unpack it, resulting in memory corruption and a potentially exploitable information leak or crash. This vulnerability affects Firefox ESR < 78.9, Thunderbird < 78.9, and Firefox < 87. |
2021-03-31 |
not yet calculated |
CVE-2021-23981
MISC
MISC
MISC
MISC |
mozilla — multiple_products
|
Mozilla developers and community members reported memory safety bugs present in Firefox 86 and Firefox ESR 78.8. Some of these bugs showed evidence of memory corruption and we presume that with enough effort some of these could have been exploited to run arbitrary code. This vulnerability affects Firefox ESR < 78.9, Thunderbird < 78.9, and Firefox < 87. |
2021-03-31 |
not yet calculated |
CVE-2021-23987
MISC
MISC
MISC
MISC |
netmask — npm_package
|
Improper input validation of octal strings in netmask npm package v1.0.6 and below allows unauthenticated remote attackers to perform indeterminate SSRF, RFI, and LFI attacks on many of the dependent packages. A remote unauthenticated attacker can bypass packages relying on netmask to filter IPs and reach critical VPN or LAN hosts. |
2021-04-01 |
not yet calculated |
CVE-2021-28918
MISC
MISC
MISC
MISC
MISC |
netty — netty
|
Netty is an open-source, asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers & clients. In Netty (io.netty:netty-codec-http2) before version 4.1.61.Final there is a vulnerability that enables request smuggling. The content-length header is not correctly validated if the request only uses a single Http2HeaderFrame with the endStream set to to true. This could lead to request smuggling if the request is proxied to a remote peer and translated to HTTP/1.1. This is a followup of GHSA-wm47-8v5p-wjpj/CVE-2021-21295 which did miss to fix this one case. This was fixed as part of 4.1.61.Final. |
2021-03-30 |
not yet calculated |
CVE-2021-21409
MISC
MISC
CONFIRM
MISC |
nokia — g-120w-f-3fe46606agab91_devices
|
An issue was discovered on Nokia G-120W-F 3FE46606AGAB91 devices. There is Stored XSS in the administrative interface via urlfilter.cgi?add url_address. |
2021-04-02 |
not yet calculated |
CVE-2021-30003
MISC |
okta — access_gateway
|
A command injection vulnerability in the cookieDomain and relayDomain parameters of Okta Access Gateway before 2020.9.3 allows attackers (with admin access to the Okta Access Gateway UI) to execute OS commands as a privileged system account. |
2021-04-02 |
not yet calculated |
CVE-2021-28113
CONFIRM |
olivier_poitrey — node_demask
|
The netmask package before 2.0.1 for Node.js mishandles certain unexpected characters in an IP address string, such as an octal digit of 9. This (in some situations) allows attackers to bypass access control that is based on IP addresses. NOTE: this issue exists because of an incomplete fix for CVE-2021-28918. |
2021-03-30 |
not yet calculated |
CVE-2021-29418
MISC
MISC |
| openexr — openexr |
There’s a flaw in OpenEXR’s scanline input file functionality in versions before 3.0.0-beta. An attacker able to submit a crafted file to be processed by OpenEXR could consume excessive system memory. The greatest impact of this flaw is to system availability. |
2021-03-31 |
not yet calculated |
CVE-2021-3478
MISC
MISC |
openexr — openexr
|
There’s a flaw in OpenEXR’s Scanline API functionality in versions before 3.0.0-beta. An attacker who is able to submit a crafted file to be processed by OpenEXR could trigger excessive consumption of memory, resulting in an impact to system availability. |
2021-03-31 |
not yet calculated |
CVE-2021-3479
MISC
MISC |
openexr — openexr
|
A flaw was found in OpenEXR in versions before 3.0.0-beta. A crafted input file supplied by an attacker, that is processed by the Dwa decompression functionality of OpenEXR’s IlmImf library, could cause a NULL pointer dereference. The highest threat from this vulnerability is to system availability. |
2021-04-01 |
not yet calculated |
CVE-2021-20296
MISC
MISC |
openexr — openexr
|
A flaw was found in OpenEXR’s B44 uncompression functionality in versions before 3.0.0-beta. An attacker who is able to submit a crafted file to OpenEXR could trigger shift overflows, potentially affecting application availability. |
2021-03-30 |
not yet calculated |
CVE-2021-3476
MISC
MISC |
openexr — openexr
|
There’s a flaw in OpenEXR in versions before 3.0.0-beta. A crafted input file that is processed by OpenEXR could cause a shift overflow in the FastHufDecoder, potentially leading to problems with application availability. |
2021-03-30 |
not yet calculated |
CVE-2021-3474
MISC
MISC |
openexr — openexr
|
There is a flaw in OpenEXR in versions before 3.0.0-beta. An attacker who can submit a crafted file to be processed by OpenEXR could cause an integer overflow, potentially leading to problems with application availability. |
2021-03-30 |
not yet calculated |
CVE-2021-3475
MISC
MISC |
openexr — openexr
|
There’s a flaw in OpenEXR’s deep tile sample size calculations in versions before 3.0.0-beta. An attacker who is able to submit a crafted file to be processed by OpenEXR could trigger an integer overflow, subsequently leading to an out-of-bounds read. The greatest risk of this flaw is to application availability. |
2021-03-31 |
not yet calculated |
CVE-2021-3477
MISC
MISC |
ovidentia — cms
|
Ovidentia CMS 6.x contains a SQL injection vulnerability in the “id” parameter of index.php. The “checkbox” property into “text” data can be extracted and displayed in the text region or in source code. |
2021-03-30 |
not yet calculated |
CVE-2021-29343
MISC
MISC |
pbootcms — pbotcms
|
PbootCMS 3.0.4 contains a SQL injection vulnerability through index.php via the search parameter that can reveal sensitive information through adding an admin account. |
2021-03-31 |
not yet calculated |
CVE-2021-28245
MISC |
pega — chat_access_group
|
Misconfiguration of the Pega Chat Access Group portal in Pega platform 7.4.0 – 8.5.x could lead to unintended data exposure. |
2021-04-01 |
not yet calculated |
CVE-2021-27653
MISC |
perl — perl
|
The Data::Validate::IP module through 0.29 for Perl does not properly consider extraneous zero characters at the beginning of an IP address string, which (in some situations) allows attackers to bypass access control that is based on IP addresses. |
2021-03-31 |
not yet calculated |
CVE-2021-29662
MISC |
piwigo — piwigo
|
SQL injection exists in Piwigo before 11.4.0 via the language parameter to admin.php?page=languages. |
2021-04-02 |
not yet calculated |
CVE-2021-27973
MISC |
pomerium — pomerium
|
Pomerium from version 0.10.0-0.13.3 has an Open Redirect in the user sign-in/out process |
2021-04-02 |
not yet calculated |
CVE-2021-29652
CONFIRM |
pomerium — pomerium
|
Pomerium before 0.13.4 has an Open Redirect (issue 1 of 2). |
2021-04-02 |
not yet calculated |
CVE-2021-29651
CONFIRM |
portswigger — burp_suite
|
An issue was discovered in PortSwigger Burp Suite before 2021.2. During viewing of a malicious request, it can be manipulated into issuing a request that does not respect its upstream proxy configuration. This could leak NetNTLM hashes on Windows systems that fail to block outbound SMB. |
2021-03-29 |
not yet calculated |
CVE-2021-29416
MISC
MISC |
postgresql — postgresql
|
An information leak was discovered in postgresql in versions before 13.2, before 12.6 and before 11.11. A user having UPDATE permission but not SELECT permission to a particular column could craft queries which, under some circumstances, might disclose values from that column in error messages. An attacker could use this flaw to obtain information stored in a column they are allowed to write but not read. |
2021-04-01 |
not yet calculated |
CVE-2021-3393
MISC |
pretashop — ps_emailsubscription
|
ps_emailsubscription is a newsletter subscription module for the PrestaShop platform. An employee can inject javascript in the newsletter condition field that will then be executed on the front office The issue has been fixed in 2.6.1 |
2021-03-31 |
not yet calculated |
CVE-2021-21418
MISC
MISC
CONFIRM
MISC |
prtg — network_monitor
|
An issue was discovered in PRTG Network Monitor before 21.1.66.1623. By invoking the screenshot functionality with prepared context paths, an attacker is able to verify the existence of certain files on the filesystem of the PRTG’s Web server. |
2021-03-31 |
not yet calculated |
CVE-2021-27220
CONFIRM |
| python — python |
models/metadata.py in the pikepdf package 1.3.0 through 2.9.2 for Python allows XXE when parsing XMP metadata entries. |
2021-04-01 |
not yet calculated |
CVE-2021-29421
CONFIRM |
red_hat — red_hat
|
A flaw was found in several ansible modules, where parameters containing credentials, such as secrets, were being logged in plain-text on managed nodes, as well as being made visible on the controller node when run in verbose mode. These parameters were not protected by the no_log feature. An attacker can take advantage of this information to steal those credentials, provided when they have access to the log files containing them. The highest threat from this vulnerability is to data confidentiality. This flaw affects Red Hat Ansible Automation Platform in versions before 1.2.2 and Ansible Tower in versions before 3.8.2. |
2021-04-01 |
not yet calculated |
CVE-2021-3447
MISC |
redis — redis
|
A heap overflow issue was found in Redis in versions before 5.0.10, before 6.0.9 and before 6.2.0 when using a heap allocator other than jemalloc or glibc’s malloc, leading to potential out of bound write or process crash. Effectively this flaw does not affect the vast majority of users, who use jemalloc or glibc malloc. |
2021-03-31 |
not yet calculated |
CVE-2021-3470
MISC |
rstudio — shiny_server
|
Directory traversal in RStudio Shiny Server before 1.5.16 allows attackers to read the application source code, involving an encoded slash. |
2021-04-02 |
not yet calculated |
CVE-2021-3374
MISC
MISC |
| rust — rust |
An issue was discovered in the arenavec crate through 2021-01-12 for Rust. A double drop can sometimes occur upon a panic in T::drop(). |
2021-04-01 |
not yet calculated |
CVE-2021-29931
MISC |
| rust — rust |
An issue was discovered in the telemetry crate through 2021-02-17 for Rust. There is a drop of uninitialized memory if a value.clone() call panics within misc::vec_with_size(). |
2021-04-01 |
not yet calculated |
CVE-2021-29937
MISC |
rust — rust
|
An issue was discovered in the insert_many crate through 2021-01-26 for Rust. Elements may be dropped twice if a .next() method panics. |
2021-04-01 |
not yet calculated |
CVE-2021-29933
MISC |
rust — rust
|
An issue was discovered in the through crate through 2021-02-18 for Rust. There is a double free (in through and through_and) upon a panic of the map function. |
2021-04-01 |
not yet calculated |
CVE-2021-29940
MISC |
rust — rust
|
An issue was discovered in the reorder crate through 2021-02-24 for Rust. swap_index has an out-of-bounds write if an iterator returns a len() that is too small. |
2021-04-01 |
not yet calculated |
CVE-2021-29941
MISC |
rust — rust
|
An issue was discovered in the arenavec crate through 2021-01-12 for Rust. A drop of uninitialized memory can sometimes occur upon a panic in T::default(). |
2021-04-01 |
not yet calculated |
CVE-2021-29930
MISC |
rust — rust
|
An issue was discovered in the parse_duration crate through 2021-03-18 for Rust. It allows attackers to cause a denial of service (CPU and memory consumption) via a duration string with a large exponent. |
2021-04-01 |
not yet calculated |
CVE-2021-29932
MISC |
rust — rust
|
An issue was discovered in the adtensor crate through 2021-01-11 for Rust. There is a drop of uninitialized memory via the FromIterator implementation for Vector and Matrix. |
2021-04-01 |
not yet calculated |
CVE-2021-29936
MISC |
rust — rust
|
An issue was discovered in the rocket crate before 0.4.7 for Rust. uri::Formatter can have a use-after-free if a user-provided function panics. |
2021-04-01 |
not yet calculated |
CVE-2021-29935
MISC |
rust — rust
|
An issue was discovered in the stackvector crate through 2021-02-19 for Rust. There is an out-of-bounds write in StackVec::extend if size_hint provides certain anomalous data. |
2021-04-01 |
not yet calculated |
CVE-2021-29939
MISC |
rust — rust
|
An issue was discovered in the slice-deque crate through 2021-02-19 for Rust. A double drop can occur in SliceDeque::drain_filter upon a panic in a predicate function. |
2021-04-01 |
not yet calculated |
CVE-2021-29938
MISC |
rust — rust
|
An issue was discovered in PartialReader in the uu_od crate before 0.0.4 for Rust. Attackers can read the contents of uninitialized memory locations via a user-provided Read operation. |
2021-04-01 |
not yet calculated |
CVE-2021-29934
MISC |
rust — rust
|
An issue was discovered in the reorder crate through 2021-02-24 for Rust. swap_index can return uninitialized values if an iterator returns a len() that is too large. |
2021-04-01 |
not yet calculated |
CVE-2021-29942
MISC |
sannce — smart_hd_wifi_security_camera
|
An issue was discovered on Sannce Smart HD Wifi Security Camera EAN 2 950004 595317 devices. By default, a mobile application is used to stream over UDP. However, the device offers many more services that also enable streaming. Although the service used by the mobile application requires a password, the other streaming services do not. By initiating communication on the RTSP port, an attacker can obtain access to the video feed without authenticating. |
2021-04-02 |
not yet calculated |
CVE-2019-20464
MISC |
sannce — smart_hd_wifi_security_camera
|
An issue was discovered on Sannce Smart HD Wifi Security Camera EAN 2 950004 595317 devices. A local attacker with the “default” account is capable of reading the /etc/passwd file, which contains a weakly hashed root password. By taking this hash and cracking it, the attacker can obtain root rights on the device. |
2021-04-02 |
not yet calculated |
CVE-2019-20466
MISC |
sannce — smart_hd_wifi_security_camera
|
An issue was discovered on Sannce Smart HD Wifi Security Camera EAN 2 950004 595317 devices. It is possible (using TELNET without a password) to control the camera’s pan/zoom/tilt functionality. |
2021-04-02 |
not yet calculated |
CVE-2019-20465
MISC |
sannce — smart_hd_wifi_security_camera
|
An issue was discovered on Sannce Smart HD Wifi Security Camera EAN 2 950004 595317 devices. A crash and reboot can be triggered by crafted IP traffic, as demonstrated by the Nikto vulnerability scanner. For example, sending the 111111 string to UDP port 20188 causes a reboot. To deny service for a long time period, the crafted IP traffic may be sent periodically. |
2021-04-02 |
not yet calculated |
CVE-2019-20463
MISC |
softing — ag_opc_toolbox
|
Softing AG OPC Toolbox through 4.10.1.13035 allows /en/diag_values.html Stored XSS via the ITEMLISTVALUES##ITEMID parameter, resulting in JavaScript payload injection into the trace file. This payload will then be triggered every time an authenticated user browses the page containing it. |
2021-04-02 |
not yet calculated |
CVE-2021-29661
MISC |
softing — ag_opc_toolbox
|
A Cross-Site Request Forgery (CSRF) vulnerability in en/cfg_setpwd.html in Softing AG OPC Toolbox through 4.10.1.13035 allows attackers to reset the administrative password by inducing the Administrator user to browse a URL controlled by an attacker. |
2021-04-02 |
not yet calculated |
CVE-2021-29660
MISC |
synology — diskstation_manager
|
Improper neutralization of special elements used in an OS command in SYNO.Core.Network.PPPoE in Synology DiskStation Manager (DSM) before 6.2.3-25426-3 allows remote authenticated users to execute arbitrary code via realname parameter. |
2021-04-01 |
not yet calculated |
CVE-2021-29083
CONFIRM |
terramaster — f2-210_devices
|
TerraMaster F2-210 devices through 2021-04-03 use UPnP to make the admin web server accessible over the Internet on TCP port 8181, which is arguably inconsistent with the “It is only available on the local network” documentation. NOTE: manually editing /etc/upnp.json provides a partial but undocumented workaround. |
2021-04-03 |
not yet calculated |
CVE-2021-30127
MISC
MISC |
visual_code_stuido — visual_code_studio
|
The unofficial vscode-rufo extension before 0.0.4 for Visual Studio Code allows attackers to execute arbitrary binaries if the user opens a crafted workspace folder. |
2021-03-31 |
not yet calculated |
CVE-2021-29658
MISC
MISC
MISC |
visual_studio_code — stripe
|
vscode-stripe is an extension for Visual Studio Code. A vulnerability in Stripe for Visual Studio Code extension exists when it loads an untrusted source-code repository containing malicious settings. An attacker who successfully exploited the vulnerability could run arbitrary code in the context of the current user. The update addresses the vulnerability by modifying the way the extension validates its settings. |
2021-04-01 |
not yet calculated |
CVE-2021-21420
CONFIRM |
vrealize — operations_manager_api
|
Server Side Request Forgery in vRealize Operations Manager API (CVE-2021-21975) prior to 8.4 may allow a malicious actor with network access to the vRealize Operations Manager API can perform a Server Side Request Forgery attack to steal administrative credentials. |
2021-03-31 |
not yet calculated |
CVE-2021-21975
MISC |
vrealize — operations_manager_api
|
Arbitrary file write vulnerability in vRealize Operations Manager API (CVE-2021-21983) prior to 8.4 may allow an authenticated malicious actor with network access to the vRealize Operations Manager API can write files to arbitrary locations on the underlying photon operating system. |
2021-03-31 |
not yet calculated |
CVE-2021-21983
MISC |
vwmware — carbon_black_cloud_workload_appliance
|
VMware Carbon Black Cloud Workload appliance 1.0.0 and 1.01 has an authentication bypass vulnerability that may allow a malicious actor with network access to the administrative interface of the VMware Carbon Black Cloud Workload appliance to obtain a valid authentication token. Successful exploitation of this issue would result in the attacker being able to view and alter administrative configuration settings. |
2021-04-01 |
not yet calculated |
CVE-2021-21982
MISC |
wire-webapp — wire-webapp
|
wire-webapp is an open-source front end for Wire, a secure collaboration platform. In wire-webapp before version 2021-03-15-production.0, when being prompted to enter the app-lock passphrase, the typed passphrase will be sent into the most recently used chat when the user does not actively give focus to the input field. Input element focus is enforced programatically in version 2021-03-15-production.0. |
2021-04-02 |
not yet calculated |
CVE-2021-21400
MISC
MISC
MISC
CONFIRM |
wiz — colors_a60_lightbulb
|
An issue was discovered in WiZ Colors A60 1.14.0. Wi-Fi credentials are stored in cleartext in flash memory, which presents an information-disclosure risk for a discarded or resold device. |
2021-04-02 |
not yet calculated |
CVE-2020-11924
MISC |
wiz — colors_a60_lightbulb
|
An issue was discovered in WiZ Colors A60 1.14.0. The device sends unnecessary information to the cloud controller server. Although this information is sent encrypted and has low risk in isolation, it decreases the privacy of the end user. The information sent includes the local IP address being used and the SSID of the Wi-Fi network the device is connected to. (Various resources such as wigle.net can be use for mapping of SSIDs to physical locations.) |
2021-04-02 |
not yet calculated |
CVE-2020-11922
MISC |
wiz — colors_a60_lightbulb
|
An issue was discovered in WiZ Colors A60 1.14.0. API credentials are locally logged. |
2021-04-02 |
not yet calculated |
CVE-2020-11923
MISC |
wpa_supplicant — hostapd
|
In wpa_supplicant and hostapd 2.9, forging attacks may occur because AlgorithmIdentifier parameters are mishandled in tls/pkcs1.c and tls/x509v3.c. |
2021-04-02 |
not yet calculated |
CVE-2021-30004
MISC |
wuzhi — cms_4.1.0
|
Directory traversal in coreframe/app/template/admin/index.php in WUZHI CMS 4.1.0 allows attackers to list files in arbitrary directories via the dir parameter. |
2021-04-02 |
not yet calculated |
CVE-2020-21590
MISC
MISC |
xerox — multiple_products
|
Xerox Phaser 6510 before 64.65.51 and 64.59.11 (Bridge), WorkCentre 6515 before 65.65.51 and 65.59.11 (Bridge), VersaLink B400 before 37.65.51 and 37.59.01 (Bridge), B405 before 38.65.51 and 38.59.01 (Bridge), B600/B610 before 32.65.51 and 32.59.01 (Bridge), B605/B615 before 33.65.51 and 33.59.01 (Bridge), B7025/30/35 before 58.65.51 and 58.59.11 (Bridge), C400 before 67.65.51 and 67.59.01 (Bridge), C405 before 68.65.51 and 68.59.01 (Bridge), C500/C600 before 61.65.51 and 61.59.01 (Bridge), C505/C605 before 62.65.51 and 62.59.01 (Bridge), C7000 before 56.65.51 and 56.59.01 (Bridge), C7020/25/30 before 57.65.51 and 57.59.01 (Bridge), C8000/C9000 before 70.65.51 and 70.59.01 (Bridge), C8000W before 72.65.51 have a remote Command Execution vulnerability in the Web User Interface that allows remote attackers with “a weaponized clone file” to execute arbitrary commands. |
2021-03-29 |
not yet calculated |
CVE-2021-28671
CONFIRM |
xerox — multiple_products
|
Xerox Phaser 6510 before 64.65.51 and 64.59.11 (Bridge), WorkCentre 6515 before 65.65.51 and 65.59.11 (Bridge), VersaLink B400 before 37.65.51 and 37.59.01 (Bridge), B405 before 38.65.51 and 38.59.01 (Bridge), B600/B610 before 32.65.51 and 32.59.01 (Bridge), B605/B615 before 33.65.51 and 33.59.01 (Bridge), B7025/30/35 before 58.65.51 and 58.59.11 (Bridge), C400 before 67.65.51 and 67.59.01 (Bridge), C405 before 68.65.51 and 68.59.01 (Bridge), C500/C600 before 61.65.51 and 61.59.01 (Bridge), C505/C605 before 62.65.51 and 62.59.01 (Bridge), C7000 before 56.65.51 and 56.59.01 (Bridge), C7020/25/30 before 57.65.51 and 57.59.01 (Bridge), C8000/C9000 before 70.65.51 and 70.59.01 (Bridge), C8000W before 72.65.51 allows remote attackers to execute arbitrary code through a buffer overflow in Web page parameter handling. |
2021-03-29 |
not yet calculated |
CVE-2021-28672
CONFIRM |
xerox — multiple_products
|
Xerox Phaser 6510 before 64.61.23 and 64.59.11 (Bridge), WorkCentre 6515 before 65.61.23 and 65.59.11 (Bridge), VersaLink B400 before 37.61.23 and 37.59.01 (Bridge), B405 before 38.61.23 and 38.59.01 (Bridge), B600/B610 before 32.61.23 and 32.59.01 (Bridge), B605/B615 before 33.61.23 and 33.59.01 (Bridge), B7025/30/35 before 58.61.23 and 58.59.11 (Bridge), C400 before 67.61.23 and 67.59.01 (Bridge), C405 before 68.61.23 and 68.59.01 (Bridge), C500/C600 before 61.61.23 and 61.59.01 (Bridge), C505/C605 before 62.61.23 and 62.59.11 (Bridge), C7000 before 56.61.23 and 56.59.01 (Bridge), C7020/25/30 before 57.61.23 and 57.59.01 (Bridge), C8000/C9000 before 70.61.23 and 70.59.01 (Bridge), allows remote attackers with “a weaponized clone file” to execute arbitrary commands in the Web User Interface. |
2021-03-29 |
not yet calculated |
CVE-2021-28673
CONFIRM |
| zeromq — zeromq |
There’s a flaw in the zeromq server in versions before 4.3.3 in src/decoder_allocators.hpp. The decoder static allocator could have its sized changed, but the buffer would remain the same as it is a static buffer. A remote, unauthenticated attacker who sends a crafted request to the zeromq server could trigger a buffer overflow WRITE of arbitrary data if CURVE/ZAP authentication is not enabled. The greatest impact of this flaw is to application availability, data integrity, and confidentiality. |
2021-04-01 |
not yet calculated |
CVE-2021-20235
MISC
MISC |
zeromq — zeromq
|
An uncontrolled resource consumption (memory leak) flaw was found in the ZeroMQ client in versions before 4.3.3 in src/pipe.cpp. This issue causes a client that connects to multiple malicious or compromised servers to crash. The highest threat from this vulnerability is to system availability. |
2021-04-01 |
not yet calculated |
CVE-2021-20234
MISC
MISC |
zohocorp — manageengine_opmanager
|
Manage Engine OpManager builds below 125346 are vulnerable to a remote denial of service vulnerability due to a path traversal issue in spark gateway component. This allows a remote attacker to remotely delete any directory or directories on the OS. |
2021-04-01 |
not yet calculated |
CVE-2021-20078
MISC |


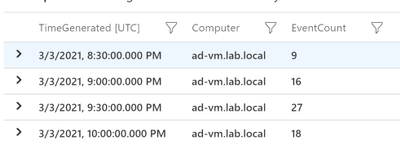
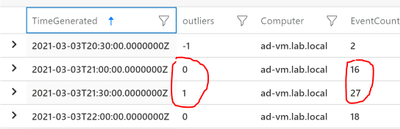
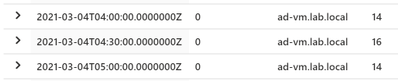
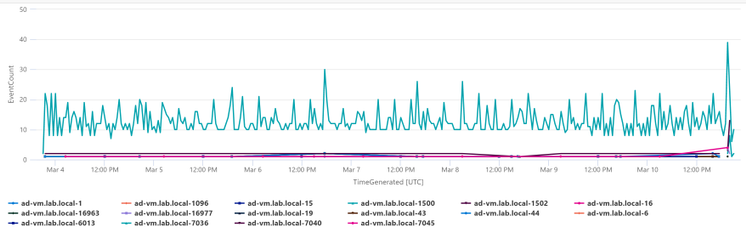

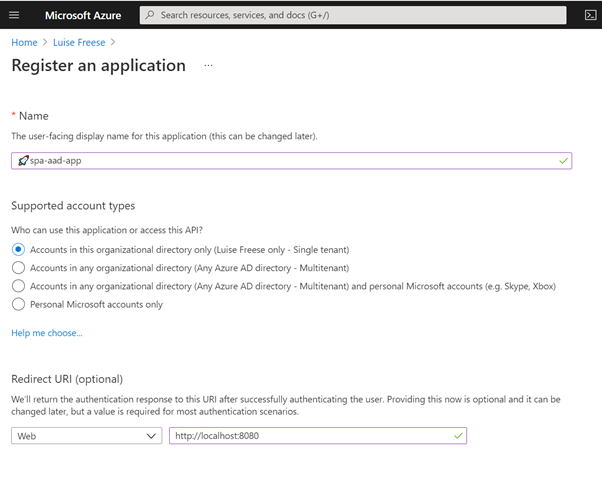
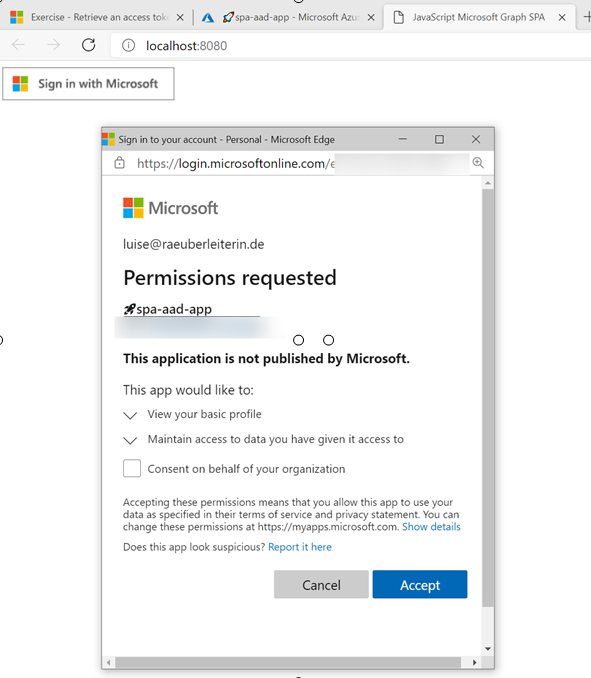
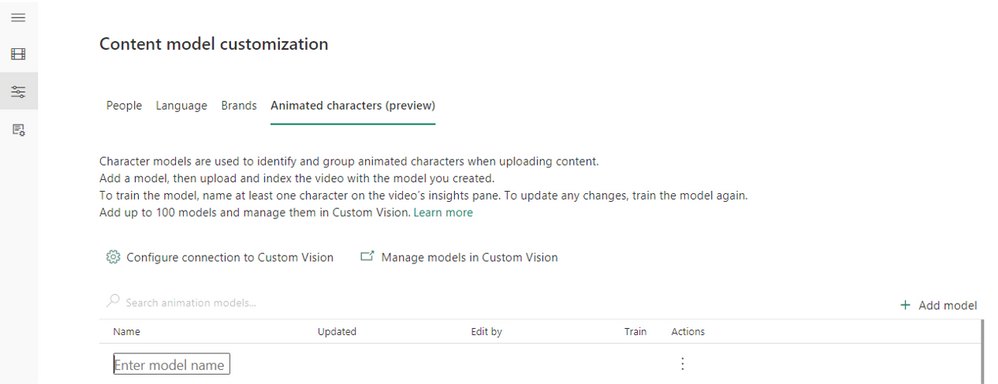


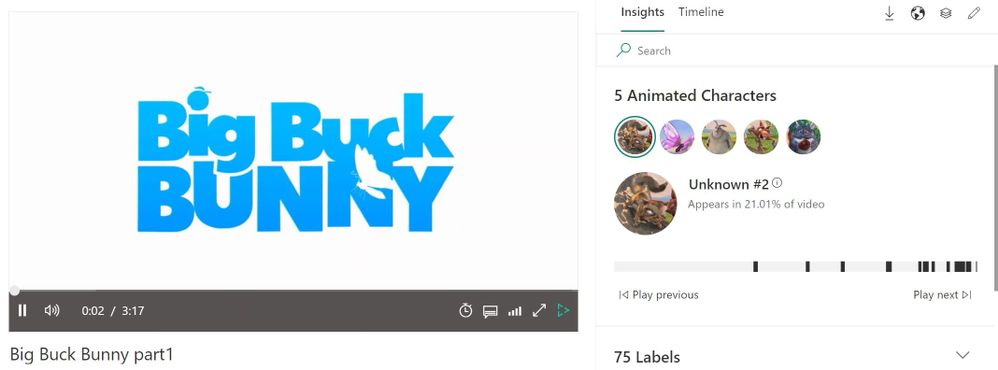

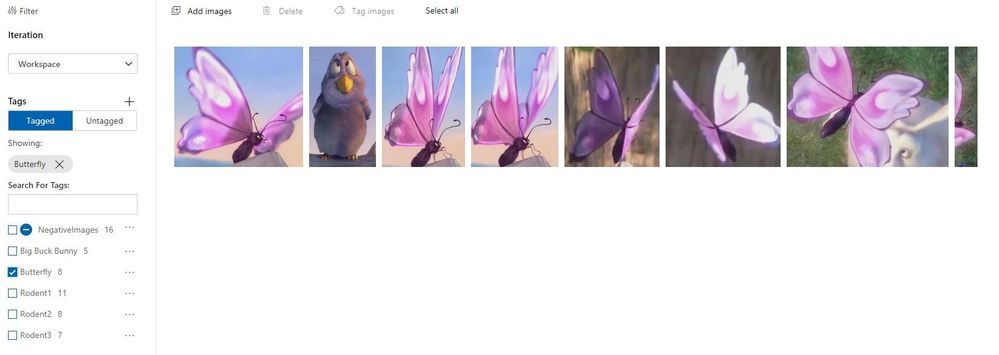
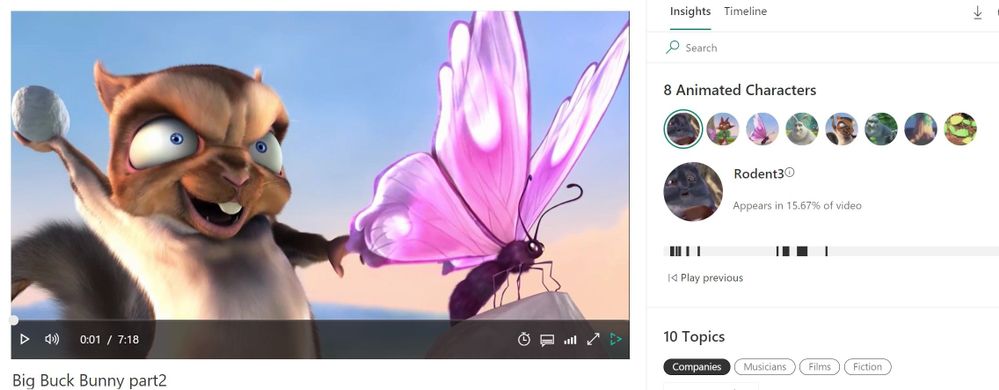

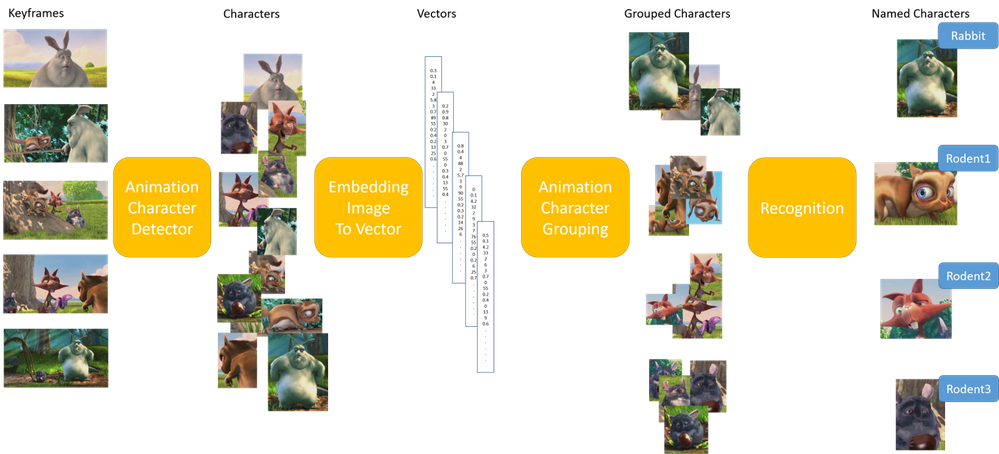
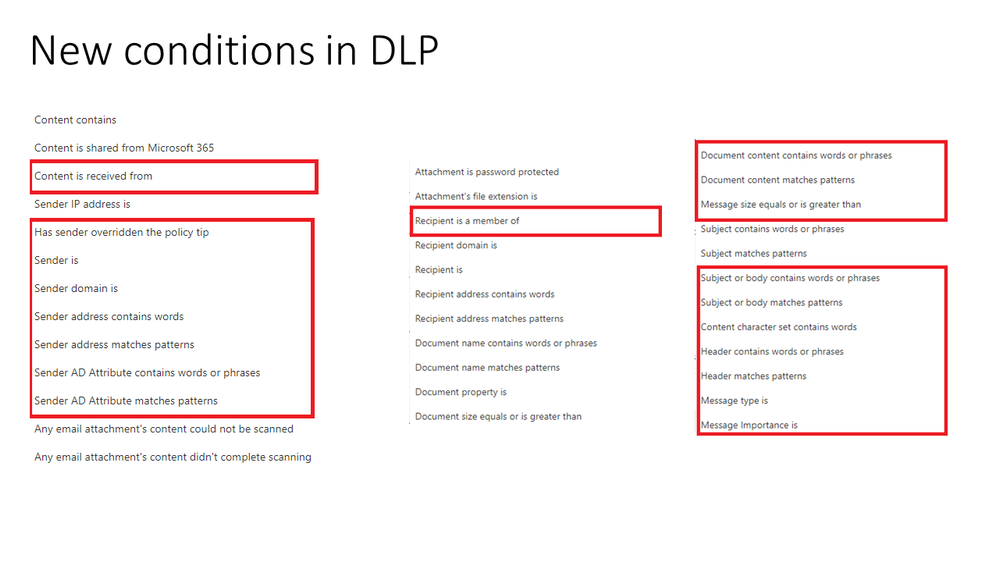
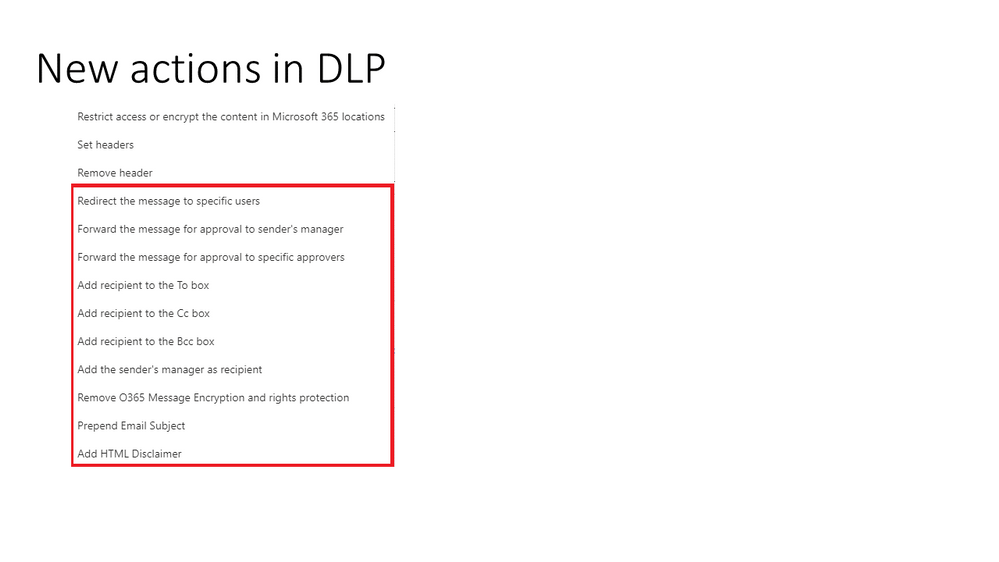

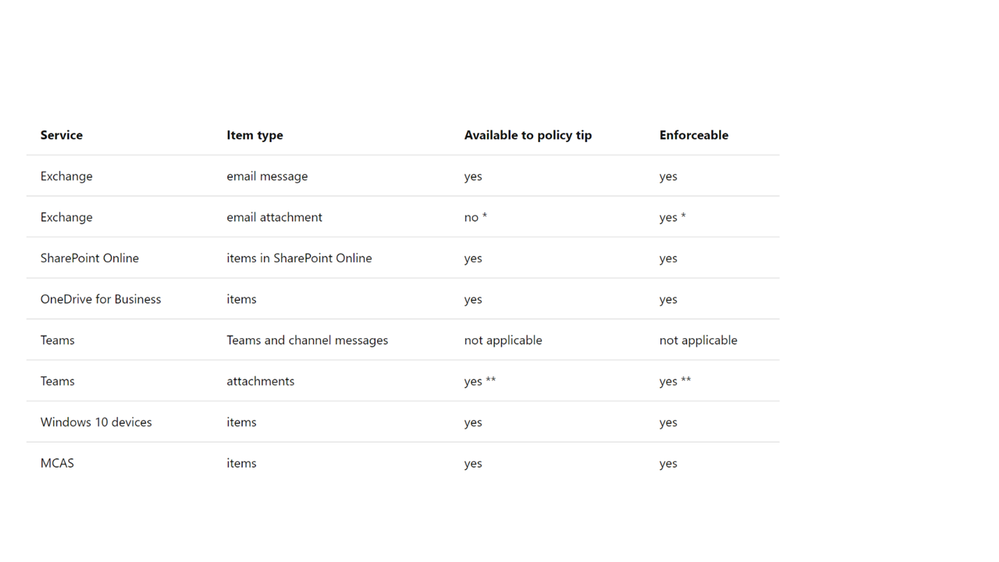
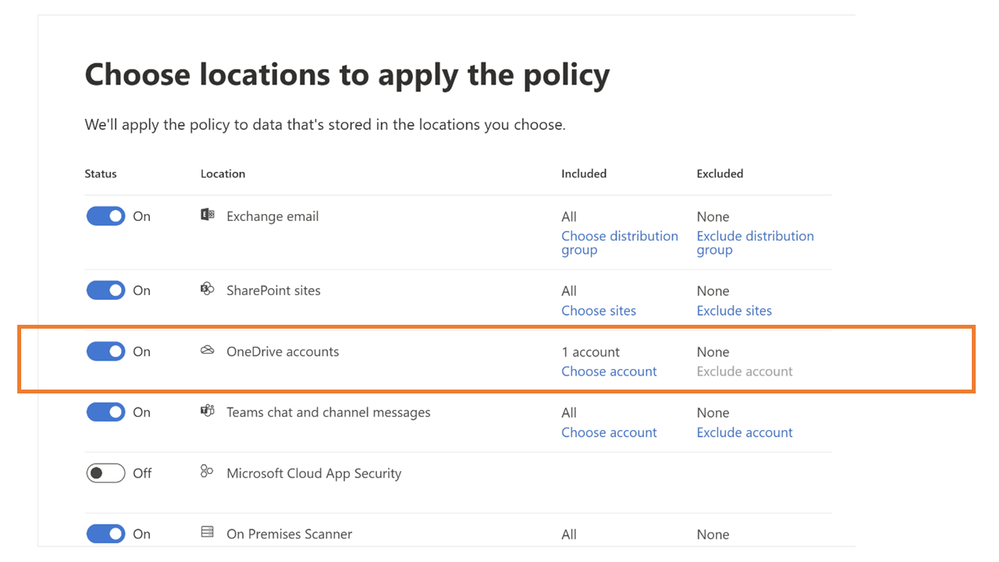
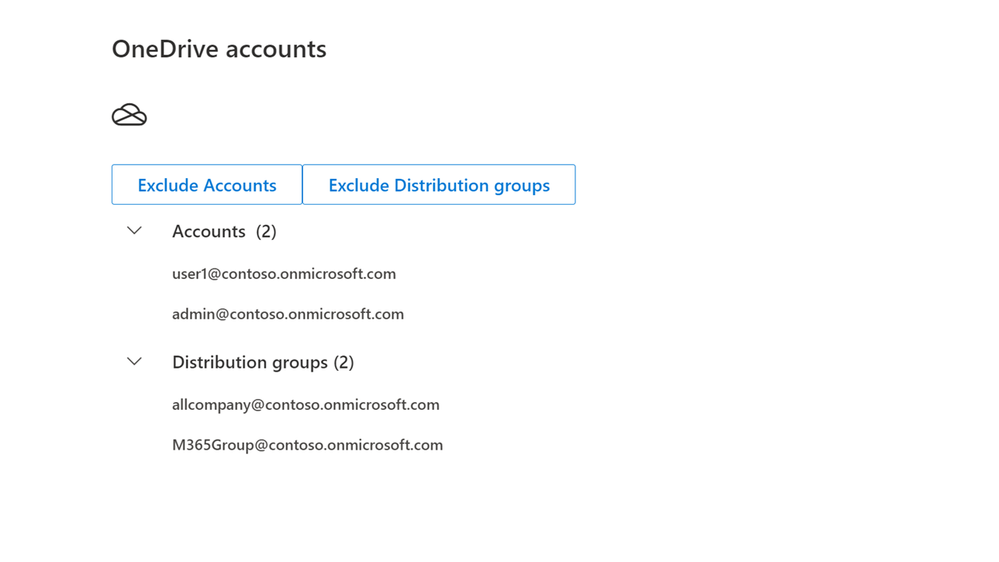
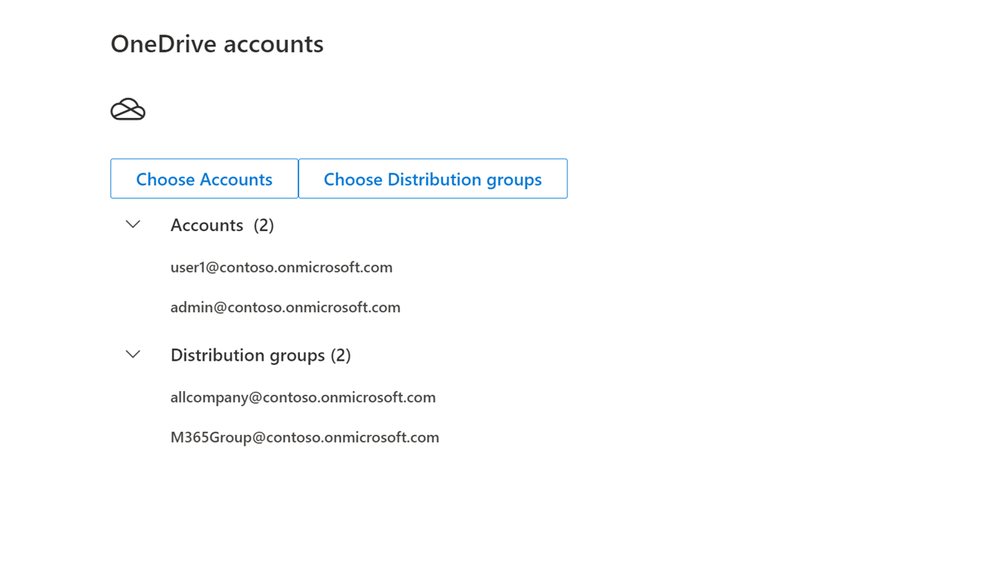
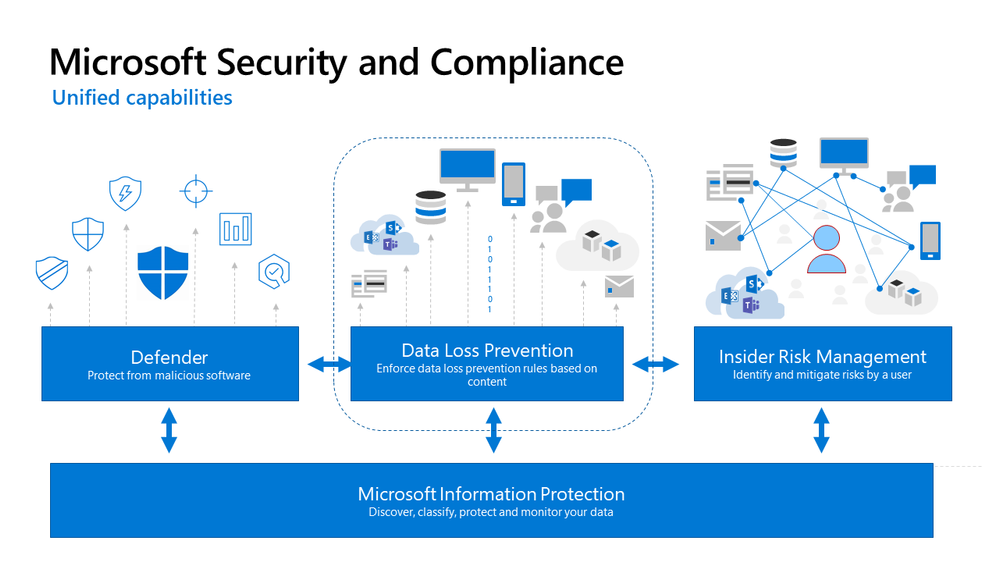



































































































Recent Comments