by Contributed | May 5, 2021 | Technology
This article is contributed. See the original author and article here.
The Azure Sentinel: Zero Trust (TIC3.0) Workbook provides an automated visualization of Zero Trust principles cross walked to the Trusted Internet Connections framework. Compliance isn’t just an annual requirement, and organizations must monitor configurations over time like a muscle. This workbook leverages the full breadth of Microsoft security offerings across Azure, Office 365, Teams, Intune, Windows Virtual Desktop, and many more. This workbook enables Implementers, SecOps Analysts, Assessors, Security & Compliance Decision Makers, and MSSPs to gain situational awareness for cloud workloads’ security posture. The workbook features 76+ control cards aligned to the TIC 3.0 security capabilities with selectable GUI buttons for navigation. This workbook is designed to augment staffing through automation, artificial intelligence, machine learning, query/alerting generation, visualizations, tailored recommendations, and respective documentation references.
 Azure Sentinel: Zero Trust (TIC3.0) Workbook
Azure Sentinel: Zero Trust (TIC3.0) Workbook
Mapping technology to Zero Trust frameworks is a challenge in the federal sector. We need to change our thinking in security assessment as the cloud evolves at the speed of innovation and growth, which often challenges our security requirements. We need a method to map Zero Trust approaches to technology while measuring change over time like a muscle.
What Are the Use Cases?
There are numerous use cases for this workbook including role alignment, mappings, visualizations, time-bound measurement, and time-saving features:
Roles
- Implementers: Build/Design
- SecOps: Alert/Automation Building
- Assessors: Audit, Compliance, Assessment
- Security & Compliance Decision Makers: Situational Awareness
- MSSP: Consultants, Managed Service
Mappings
- Framework to Requirement to Microsoft Technology
Visualization
- Hundreds of Visualizations, Recommendations, Queries
Time-Bound
- Measure Posture Over Time for Maturity
Time-Saving
- Aggregation & Analysis
- Capabilities Assessment
- Navigation
- Documentation
- Compliance Mapping
- Query/Alert Generation
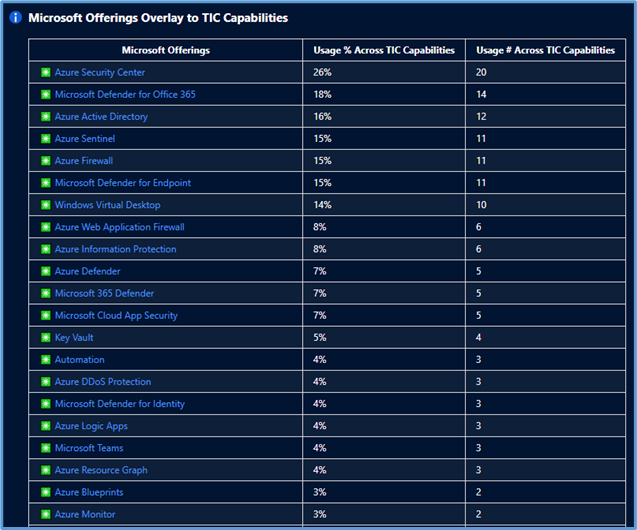 Microsoft Offerings Overlay to TIC Capabilities
Microsoft Offerings Overlay to TIC Capabilities
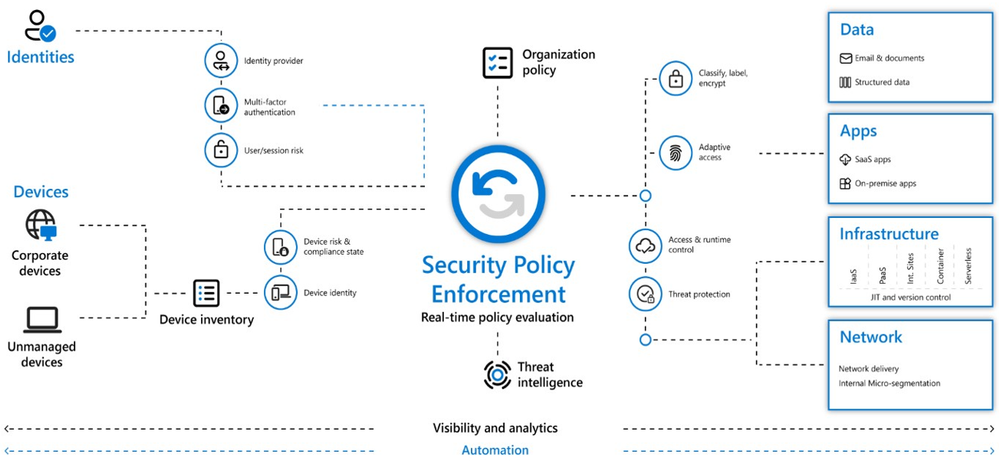
What is Zero Trust?
Zero Trust is a security architecture model that institutes a deny until verified approach to access resources from both inside and outside the network. This approach addresses the challenges associated with a shifting security perimeter in a cloud-centric and mobile workforce era. The core principle of Zero Trust is maintaining strict access control. This concept is critical to prevent attackers from pivoting laterally and elevating access within an environment.
At Microsoft, we define Zero Trust around universal principles.
- Verify Explicitly: Always authenticate and authorize based on all available data points, including user identity, location, device health, service or workload, data classification, and anomalies.
- Use Least Privileged Access: Limit user access with just-in-time and just-enough-access (JIT/JEA), risk-based adaptive policies, and data protection to secure both data and productivity.
- Assume Breach: Minimize blast radius for breaches and prevent lateral movement by segmenting access by the network, user, devices, and app awareness. Verify all sessions are encrypted end to end. Use analytics to get visibility, drive threat detection, and improve defenses.
These principles are technology-agnostic and aligned to six Zero Trust pillars.
 Zero Trust Defined
Zero Trust Defined
- Identity: Whether they represent people, services, or IoT devices—define the Zero Trust control plane. When an identity attempts to access a resource, verify that identity with strong authentication, and ensure access is compliant and typical.
- Endpoints: Once an identity accesses a resource, data can flow to different endpoints—from IoT devices to smartphones, BYOD to partner-managed devices, and on-premises workloads to cloud-hosted servers. This diversity creates a massive attack surface area. Monitor and enforce device health and compliance for secure access.
- Data: Ultimately, security teams are protecting data. Where possible, data should remain safe even if it leaves the devices, apps, infrastructure, and networks the organization controls. Classify, label, and encrypt data, and restrict access based on those attributes.
- Apps: Applications and APIs provide an interface for data consumption. They may be legacy on-premises, lifted-and-shifted to cloud workloads, or modern SaaS applications. Apply controls and technologies to discover shadow IT, ensure appropriate in-app permissions, gate access based on real-time analytics, monitor for abnormal behavior, control user actions, and validate secure configuration options.
- Infrastructure: Infrastructure—whether on-premises servers, cloud-based VMs, containers, or micro-services—represents a critical threat vector. Assess for version, configuration, and JIT access to harden defense. Use telemetry to detect attacks and anomalies, and automatically block and flag risky behavior and take protective actions.
- Network: All data transits over network infrastructure. Networking controls can provide critical controls to enhance visibility and prevent attackers from moving laterally across the network. Segment networks and deploy real-time threat protection, end-to-end encryption, monitoring, and analytics.
What is Trusted Internet Connections (TIC3.0)?
Trusted Internet Connections (TIC) is a federal cybersecurity initiative to enhance network and perimeter security across the United States federal government. The TIC initiative is a collaborative effort between the Office of Management and Budget (OMB), the Department of Homeland Security (DHS), Cybersecurity and Infrastructure Security Agency (CISA), and the General Services Administration (GSA). The TIC 3.0: Volume 3 Security Capabilities Handbook provides various security controls, applications, and best practices for risk management in federal information systems.
Is Zero Trust Equivalent to TIC 3.0?
No, Zero Trust is a best practice model and TIC 3.0 is a security initiative. Zero Trust is widely defined around core principles whereas TIC 3.0 has specific capabilities and requirements. This workbook demonstrates the overlap of Zero Trust Principles with TIC 3.0 Capabilities. The Azure Sentinel Zero Trust (TIC 3.0) Workbook demonstrates best practice guidance, but Microsoft does not guarantee nor imply compliance. All TIC requirements, validations, and controls are governed by the Cybersecurity & Infrastructure Security Agency. This workbook provides visibility and situational awareness for security capabilities delivered with Microsoft technologies in predominantly cloud-based environments. Customer experience will vary by user and some panels may require additional configurations for operation. Recommendations do not imply coverage of respective controls as they are often one of several courses of action for approaching requirements which is unique to each customer. Recommendations should be considered a starting point for planning full or partial coverage of respective requirements.
Deploying the Workbook
It is recommended that you have the log sources listed above to get the full benefit of the Zero Trust (TIC3.0) Workbook, but the workbook will deploy regardless of your available log sources. Follow the steps below to enable the workbook:
Requirements: Azure Sentinel Workspace and Security Reader rights.
1) From the Azure portal, navigate to Azure Sentinel
2) Select Workbooks > Templates
3) Search Zero Trust and select Save to add to My Workbooks
Navigating the Workbook
The Legend Panel provides a helpful reference for navigating the workbook with respective colors, features, and reference indicators.
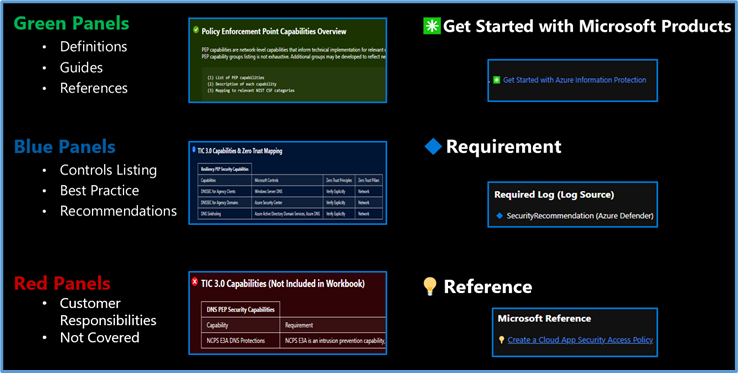 Workbook Navigation
Workbook Navigation
The Guide Toggle is available in the top left of the workbook. This toggle allows you to view panels such as recommendations and guides, which will help you first access the workbook but can be hidden once you’ve grasped respective concepts.
 Guide Toggle
Guide Toggle
The Resource Parameter Options provide configuration options to sort control cards by Subscription, Workspace, and Time Range. The Parameter Options are beneficial for Managed Security Service Providers (MSSP) or large enterprises that leverage Azure Lighthouse for visibility into multiple workspaces. It facilitates assessment from both the aggregate and individual workspace perspectives. Time range parameters allow options for daily, monthly, quarterly, and even custom time range visibility.
 Resource Parameter Options
Resource Parameter Options
The Capabilities Ribbon provides a mechanism for navigating the desired security capabilities sections highlighted in the TIC3.0 framework. Selecting a capability tab will display Control Cards in the respective area. An Overview tab provides more granular detail of the overlaps between the Microsoft Zero Trust model and the TIC3.0 framework.
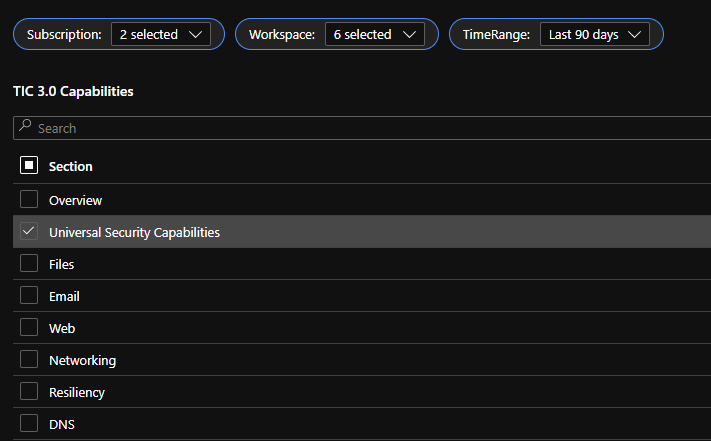 Capabilities Selector
Capabilities Selector
This workbook leverages automation to visualize your Zero Trust security architecture. Is Zero Trust the same as TIC 3.0? No, they’re not the same, but they share numerous common themes which provide a powerful story. The workbook offers detailed crosswalks of Microsoft’s Zero Trust model with the Trusted Internet Connections (TIC3.0) framework to better understand the overlaps.
 TIC 3.0 Overlay to Microsoft Offerings and Zero Trust Principles
TIC 3.0 Overlay to Microsoft Offerings and Zero Trust Principles
The Azure Sentinel Zero Trust (TIC3.0) Workbook displays each control in a Capability Card. The Capability Card provides respective control details to understand requirements, view your data, adjust SIEM queries, export artifacts, onboard Microsoft controls, navigate configuration blades, access reference materials, and view correlated compliance frameworks.
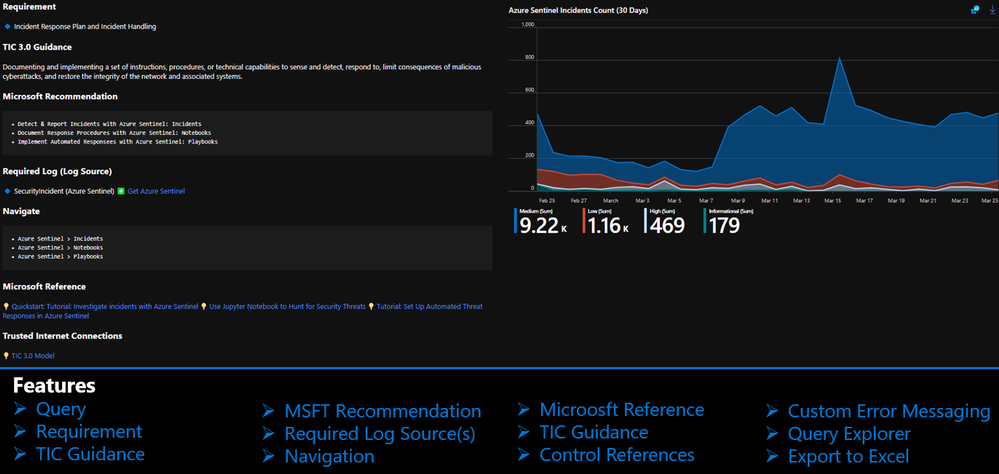 Capability Card
Capability Card
How to Use It?
There are several use cases for the Azure Sentinel Zero Trust (TIC 3.0) Workbook depending on user roles and requirements. The graphic below shows how a SecOps analyst can leverage the workbook to review requirements, explore queries, configure alerts, and implement automation. There are also several additional use cases where this workbook will be helpful:
- Security Architect: Build/design a cloud security architecture to compliance requirements.
- Managed Security Services Provider: Leverage the workbook for Zero Trust (TIC3.0) Assessments.
- SecOps Analyst: Review activity in query, configure alerts, deploy SOAR automation.
- IT Pro: Identify performance issues, investigate issues, set alerts for remediation monitoring.
- Security Engineer: Assess security controls, review alerting thresholds, adjust configurations.
- Security Manager: Review requirements, analyze reporting, evaluate capabilities, adjust accordingly.
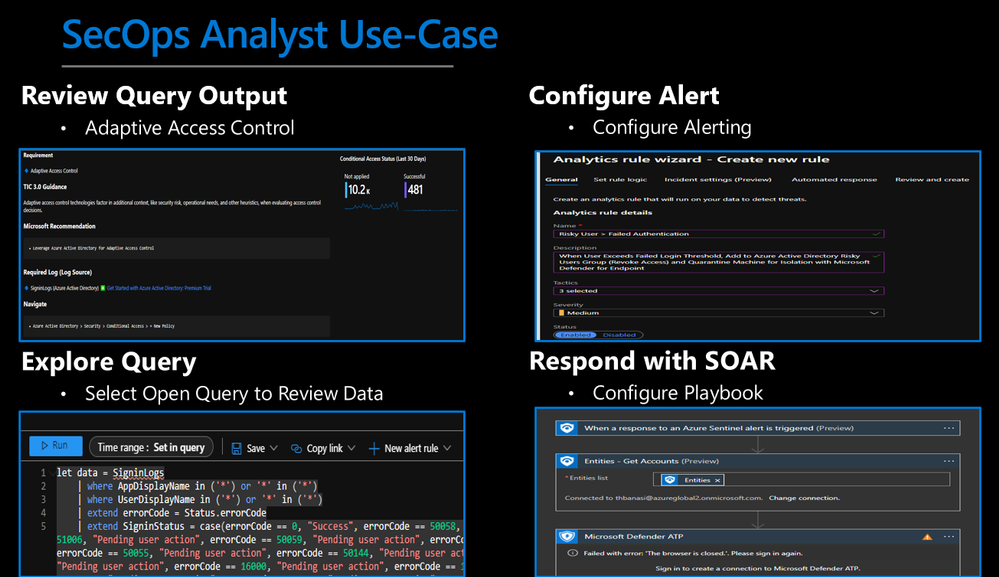 SecOps Analyst Use-Case
SecOps Analyst Use-Case
Configurations & Troubleshooting
It’s important to note that this workbook provides visibility and situational awareness for control requirements delivered with Microsoft technologies in predominantly cloud-based environments. Customer experience will vary by user, and some panels may require additional configurations and query modification for operation. It’s unlikely that all 76+ panels will populate data, but this is expected as panels without data highlight respective areas for evaluation in maturing cybersecurity capabilities. Capability Cards without data will display the custom error message below. Most issues are resolved by confirming the log source’s licensing/availability/health, ensuring the log source is connected to the Sentinel workspace, and adjusting time thresholds for larger data sets. Ultimately this workbook is customer-controlled content, so panels are configurable per customer requirements. You can edit/adjust Control Card queries as follows:
- Zero Trust (TIC3.0) Workbook > Edit > Edit Panel > Adjust Panel KQL Query > Save
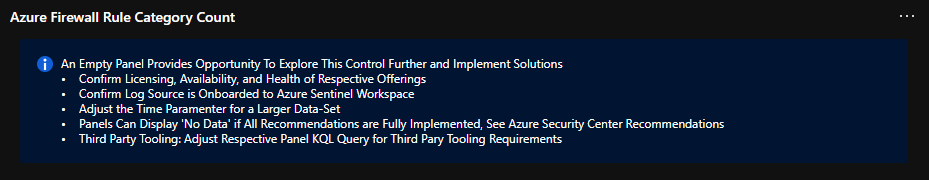 Custom Error Messaging
Custom Error Messaging
While using Microsoft offerings for the Zero Trust (TIC3.0) Workbook is recommended, it’s not a set requirement as customers often rely on many security providers and solutions. Below is a use-case example for adjusting a Control Card to include third-party tooling. The default KQL query provides a framework for target data, and it is readily adjusted with the desired customer controls/solutions.
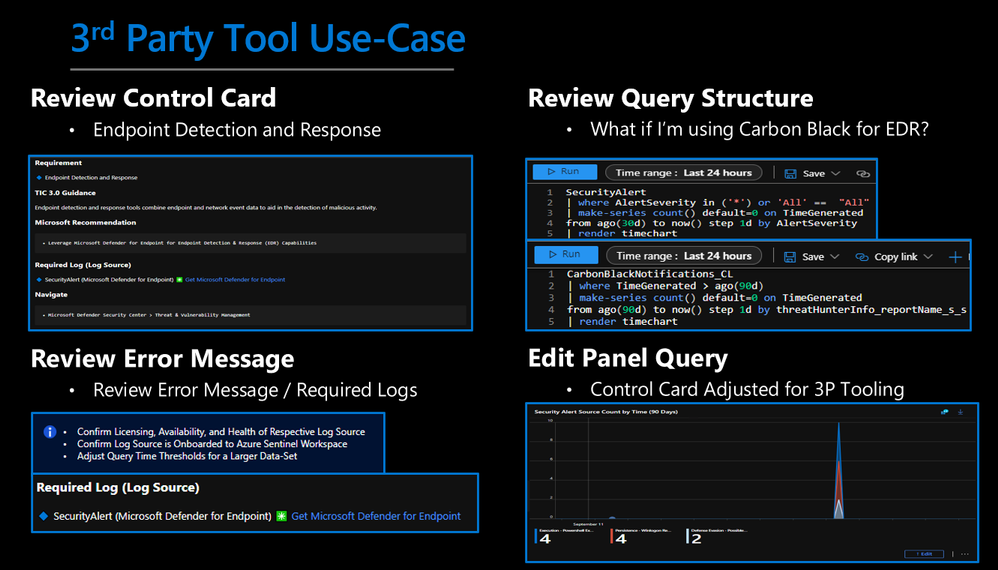 3rd Party Tool Use-Case
3rd Party Tool Use-Case
Get Started with Azure Sentinel and Learn More About Zero Trust with Microsoft
Below are additional resources for learning more about Zero Trust (TIC3.0) with Microsoft. Bookmark the Security blog to keep up with our expert coverage on security matters and follow us at @MSFTSecurity or visit our website for the latest news and cybersecurity updates.
Disclaimer
The Azure Sentinel Zero Trust (TIC 3.0) Workbook demonstrates best practice guidance, but Microsoft does not guarantee nor imply compliance. All TIC requirements, validations, and controls are governed by the Cybersecurity & Infrastructure Security Agency. This workbook provides visibility and situational awareness for control requirements delivered with Microsoft technologies in predominantly cloud-based environments. Customer experience will vary by user, and some panels may require additional configurations and query modification for operation. Recommendations do not imply coverage of respective controls as they are often one of several courses of action for approaching requirements which is unique to each customer. Recommendations should be considered a starting point for planning full or partial coverage of respective control requirements.
by Contributed | May 5, 2021 | Technology
This article is contributed. See the original author and article here.
This week we are announcing the preview support of Microsoft Azure SQL Edge on Red Hat Enterprise Linux (RHEL). Developers can now easily extend their existing SQL Server 2019 offerings for RHEL and Red Hat Openshift to IoT edge gateways and devices for consistent edge to cloud data management.
Azure SQL Edge is a small-footprint, edge-optimized database delivered as an Open Containers Initiative (OCI) compatible container for connected, disconnected or hybrid environments and supports the latest generation of the Podman container management tools on RHEL 8. Features include built-in data streaming and time series, with in-database machine learning and graph features for low-latency analytics as well as capabilities for machine learning at the edge to optimize bandwidth, reaction time, and cost. The availability of Azure SQL Edge on RHEL expands the existing ecosystem of tools, applications, frameworks, and libraries for building and running containers on the edge.
Because Azure SQL Edge is packaged as a container, it is easy to deploy and update on RHEL. You can pull the latest image down from an internal repository directly to your edge devices, from the official Microsoft container repository, or manage everything directly from Azure. A basic installation for an Azure SQL Edge developer edition on RHEL is as simple as running:
$ podman run –cap-add SYS_PTRACE -e ‘ACCEPT_EULA=1’ -e ‘MSSQL_SA_PASSWORD=StrongPassword’ -p 1433:1433 –name azuresqledge -d mcr.microsoft.com/azure-sql-edge
That’s it! The Azure SQL Edge database is up and running and you are ready to start developing your RHEL-based project on the edge.
It needs to be noted that in the connected deployment scenario, Azure SQL Edge is deployed as a module of Azure IoT Edge. Azure IoT Edge’s platform support documentation states RHEL as Tier 2 systems. This means RHEL is compatible with Azure IoT Edge but is not actively tested or maintained by Microsoft.
To learn more about Azure SQL Edge visit the product page or watch the latest customer evidence stories
by Contributed | May 5, 2021 | Technology
This article is contributed. See the original author and article here.
Microsoft Defender for Identity is removing non-secure cipher suites to provide best-in-class encryption, and to ensure our service is more secure by default. As of version 2.149 (expected to be deployed on the week commencing 23rd May) Microsoft Defender for Identity will no longer support the following cipher suites. From this date forward, any connection using these protocols will no longer work as expected, and no support will be provided.
Non-secure cipher suites:
- TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA
- TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA
- TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
Support will continue for the following suites:
- TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384
- TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256
- TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256
What do I need to do to prepare for this change?
Nothing – this change will be automatic and we don’t anticipate it affecting customer environments.
For additional inquiries please contact support.
– Microsoft Defender for Identity team.

by Contributed | May 5, 2021 | Technology
This article is contributed. See the original author and article here.
As schools begin to reopen across the world, concern about student wellbeing is at the forefront of many discussions. Educators want to help students recognize and navigate their emotions by providing regular opportunities to share and be heard.
This need inspired us to develop Reflect in Microsoft Teams for Education.
Reflect can help broaden learners’ emotional vocabulary and deepen empathy for their peers while also providing valuable feedback to educators for a healthy classroom community.
Whatever your role in the educational community (educator, school leader, or part of the wellbeing team), this blog post will show you how to support student wellbeing by encouraging reflective conversations in your school and making emotional check-ins a part of your routine.
Decades of research on the science of learning, and the important role emotions play in how we humans learn and process information, has finally caught up with what most educators have always known – students need more than academics to successfully navigate their way through this complex world they have inherited. Social Emotional Learning (SEL) is about treating a student as a whole person, emotions and all, and cultivating the skills we all need to become engaged citizens leading happy, healthy, successful lives.
CASEL (Collaborative for Academic, Social, and Emotional Learning) defines SEL as:
The process through which children and adults acquire and effectively apply the knowledge, attitudes, and skills necessary to understand and manage emotions, set and achieve positive goals, feel and show empathy for others, establish and maintain positive relationships, and make responsible decisions.
Once we understand SEL, we can implement it throughout the school community. One tool that can help you is the new Reflect app in Microsoft Teams, and here are some tips on how to start.
 Student journal in Reflect
Student journal in Reflect
What is Reflect, and why it’s used
We want to build a school community that recognizes the whole student. It is important that we support them emotionally, understand when they are going through a rough time, and ensure that the classroom environment stays positive and conducive to learning.
Reflect is an emotional check-in app that helps educators support their students and the class as a whole. Reflect helps students recognize and navigate their emotions by providing regular opportunities to share and be heard. Reflect can help broaden a student’s emotional vocabulary and deepen empathy for their peers while also providing valuable feedback to educators for a healthy classroom community.
This check-in app uses emojis and research-backed emotional granularity to support educators in adding social and emotional learning and support into their routine.
Schools are reopening, Reflect is as valuable as ever
The future is unpredictable. Preparing youth for the challenges of tomorrow in the ambiguity of today is a hurdle that educators have taken in their stride. Social-emotional skills help us better navigate complexity and uncertainty while minimizing the adverse effects of disruption and sustaining the relationships that support the students. The past year’s changes have highlighted the importance of personal connection, accelerated the integration of technology in the classroom, and amplified the role of teachers. Adjusting back to in-person learning is a disruption in itself. Students will need support in re-establishing their bonds, noticing social cues, and communicating their needs to their peers and educators. A regular SEL routine like Reflect can provide an entry point for educators to host classroom conversations and a safe space for students to voice their concerns.
Privacy and Security
Reflect follows the same privacy and security standards as Education Insights to protect students’ sensitive information.
The information collected and shown through Reflect meets more than 90 regulatory and industry standards, including GDPR and the Family Education Rights and Privacy Act (FERPA) for students and children’s security and other, similar, privacy-oriented regulations.
Students never see the names of other students, only how they responded. While they can see the distribution of responses, they cannot see the student names associated with each reflection.
Steps to successful Reflect adoption
1. Enable Reflect
You can locate the Reflect app through the Teams apps gallery or using this link: https://aka.ms/getReflect.
If you don’t find the Reflect app in the gallery or if the link is not accessible, it may be that your IT Admin has limited the app in your tenant. In such a case, please refer your IT Admin to the following document: IT Admin Guide to Reflect in Microsoft Teams.
Only when Reflect is allowed can educators see and use the app in their classes.
Guest users (students or educators) cannot use Reflect.
2. Work with educators, so they understand the importance of regular check-ins and emotional granularity
Reflect helps educators easily check how their students feel in general or about a specific topic, such as learning from home, an assignment, current events, or a change within their community.
Emotional granularity is the ability to differentiate between emotions and articulate the specific emotion experienced. Developing language to talk about feelings is foundational to social and emotional learning. Accurately defining our emotions can help identify the source of the feeling and plan to meet our needs.
Introduce your educators to the app and show them how it can support a positive emotional climate in the classroom. Reflect provides an emotional safe space to grow student-teacher connections and help students develop their emotional vocabulary. We worked with SEL experts to select 50 emotion words that students can identify with as they reflect.
3. Ask educators to try Reflect and share their feedback
The first step is always the hardest. Reflect provides a variety of questions educators can ask their class for some common scenarios. The questions are a closed list, developed with the help of experts, and designed to provide Insights when associated with other data. One way to customize a Reflect check-in is to publish it and then “reply” to the message with specific guidelines.
Ask the educators to share their experiences using Reflect so that you can support them and their specific needs.
 Choose a check-in question in Reflect
Choose a check-in question in Reflect
We have created a resource page for educators that includes instructions, short videos, and a free course on getting started.
Listen to their feedback, and work with them to find what works best for their classes.
* The capacity to schedule repeat check-ins and access detailed data for Reflect in Insights will be available summer of 2021
4. Ask educators to use Reflect as part of their routine
Encouraging communication about emotions and supporting students in voicing their needs can go a long way toward preventing feelings of isolation, frustration, and disengagement. Once educators understand how Reflect supports them, suggest to them that they use it as part of their routine.
Here are some suggestions for using Reflect in the classroom.
- Implement a daily check-in to provide students with opportunities to practice evaluating and naming their emotions and ensure educators have a touchpoint with every student every day.
- Jumpstart conversations with students after a difficult day by asking What does the mood in our classroom feel like? This can be an excellent opportunity to model self-reflection and set goals together as a class.
- To support learning, assess student confidence about a concept or assignment, and plan accordingly.
- Celebrate wins with a Reflect check-in after a successful activity. Remember, mistakes can be framed as successes too!
- Identify dynamics between students by asking How do your friendships feel today? This can be paired with conversations or stories about sharing, bullying, and healthy relationships.
5. Empower the educator
The educator has complete control of when (or even if) to use Reflect. Only they should decide whether to post a new Reflect check-in, when and what type. If an educator feels it is not suitable for their classroom or they cannot support the students that way, they will not publish a new check-in, and you need to support them in that decision.
6. Don’t set goals for students
There is no right or wrong answer when dealing with emotions. All feelings are valid, and we want students to provide an honest assessment from their perspective and feel safe when describing their emotions. The goal is to develop a deeper understanding of student needs and work together to create a more positive climate and foster greater well-being in class.
We want to make the classroom a place where student emotions are valued, and everyone feels safe and heard.
7. Use Insights reports
Through Education Insights, educators can see how students respond to check-ins over time, making it easier to identify and address student needs.
The digital activity report now includes Reflect check-in data, with additional Reflect insights coming soon.
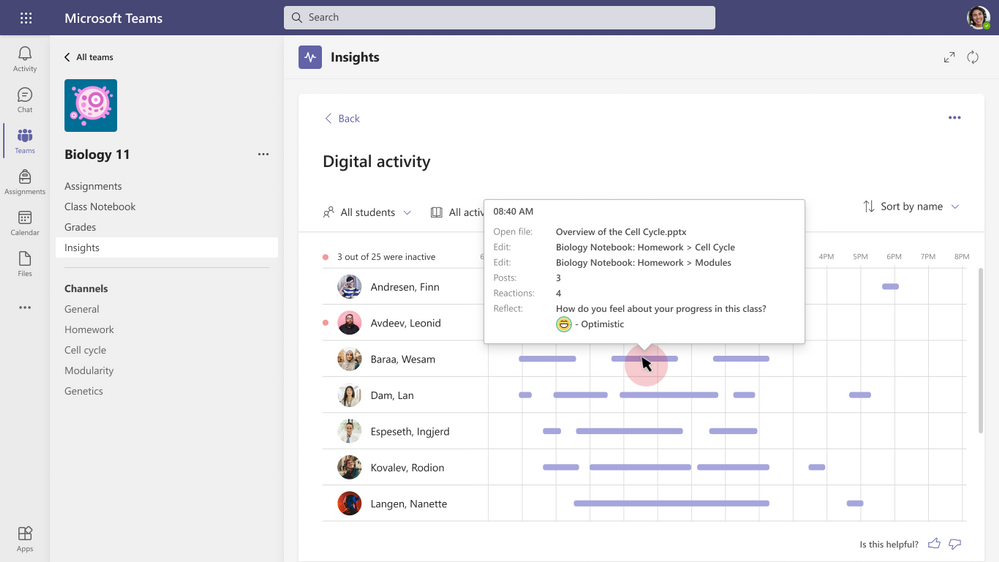 Education Insights – Reflect check-ins in the digital activity report
Education Insights – Reflect check-ins in the digital activity report
Educators can also track the adoption of the tool amongst their students to make sure they feel comfortable sharing their emotions. If there is low adoption, you may want to provide a framework to help establish the classroom as a safe space to share and support them in developing the emotional vocabulary needed to feel confident in sharing.
If you have Education Insights Premium (currently in preview), you can also see adoption across classes, grade level, school, etc., in your organizational view, and provide support and assistance for those who either don’t use Reflect at all or stopped using it after the initial adoption.
We’re always looking for ways to make Education Insights and Reflect better. Have questions, comments, or ideas? Let me know! Add your idea here, share your comment below, and find me on Twitter (@grelad).
Elad Graiver
Senior Program Manager, Education Insights and Reflect
by Contributed | May 5, 2021 | Technology
This article is contributed. See the original author and article here.
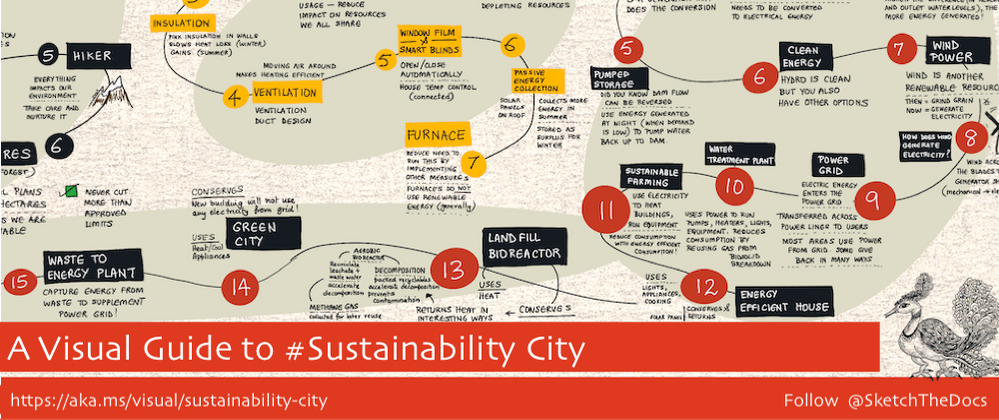
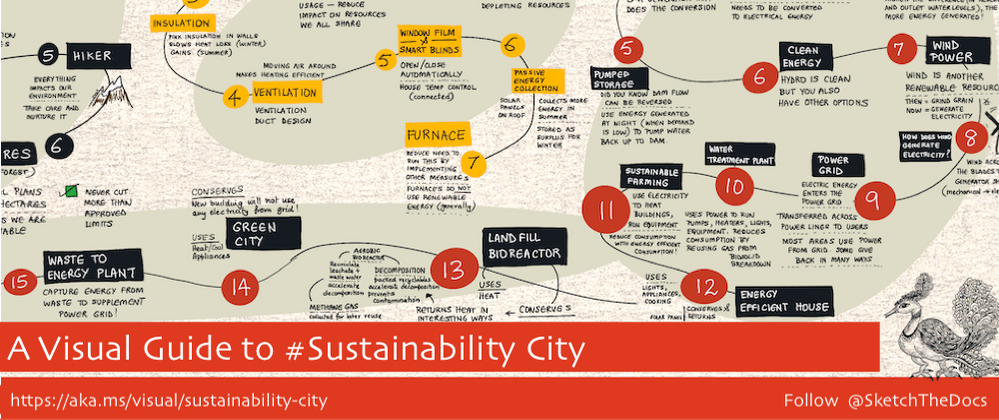
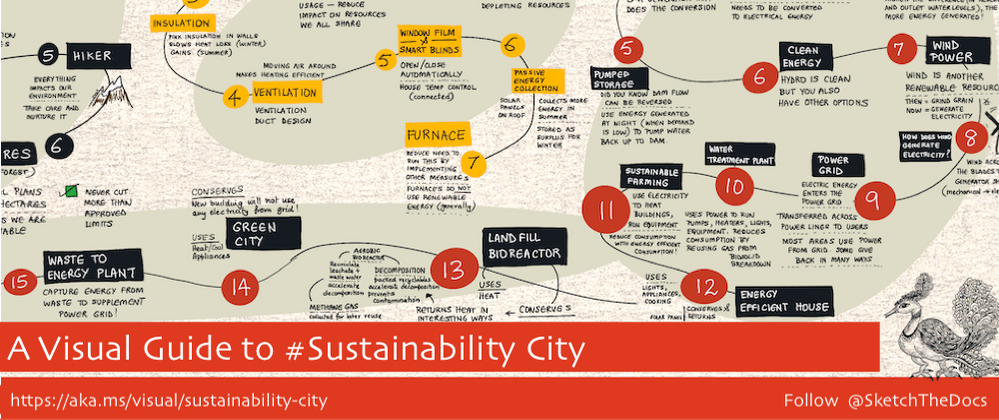
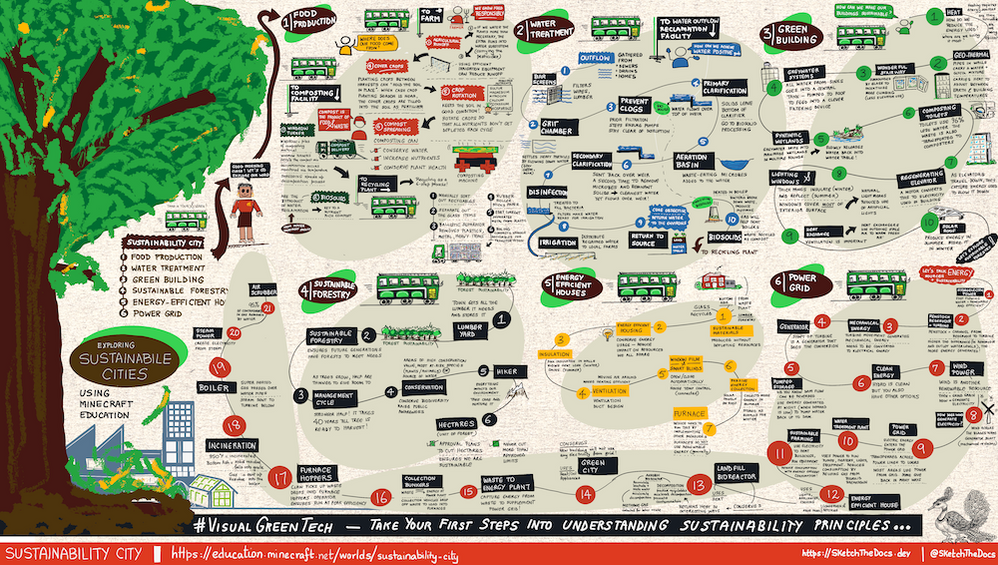
A Visual Guide To #Sustainability City
Welcome to the second in my series of visual guides focused on the topic of Sustainability and Green Tech. The first one focused on a Visual Guide To Sustainable Software Engineering, visualizing the core philosophies and eight principles of sustainable software engineering, as defined by this fantastic Microsoft Learn Module.
Putting Philosophy Into Practice
In fact, it was that first philosophy (“Everyone has a part to play in the climate solution”) that inspired me to work with the Microsoft Green Cloud Advocacy team on the #VisualGreenTech challenge for EarthDay and co-host a special Earth Day themed episode of #HelloWorld featuring Green Tech experts from Microsoft.
The challenge itself featured 24 prompts, three of which explored Sustainability interactively using Minecraft Education Edition resources for Earth Day. The first of these prompts focused on Sustainability City – a Minecraft world where you can take green buses around a bustling city, visiting various facilities to learn about sustainable practices targeting water treatment, food production, sustainable forestry, green buildings, energy-efficient homes, and the power grid. This community-created video does a great job of navigating the world in under eight minutes.
It was there that my personal journey into putting that philosophy to practice began!
Using Minecraft To Motivate Sustainability Education
Minecraft is an amazing resource for educating K-12 students on sustainability in actionable ways. The Minecraft Education Edition provides downloadable words that students can navigate and it has detailed lesson plans with activities and discussion guides to help students go from awareness to engagement, and action.
In my case, I took advantage of our Microsoft employee access to the Minecraft Edu Edition to begin a sustainability city journey with my 12-year-old. We took every bus, talked to every character, and had interesting follow-up conversations like: where does our water come from? how can we be more sustainable at home during the pandemic? and my favorite: should we create our own vegetable garden so we know where our food comes from?
If you are a parent, I strongly advocate for doing this exploration with kids and using the visual guide below to have a conversation once you leave the world. If you are an educator with access to this edition of Minecraft, I hope you find this visual guide a good resource for classroom conversations or continued awareness of what they learned, once they have completed that lesson.
Visual Guide & Navigation
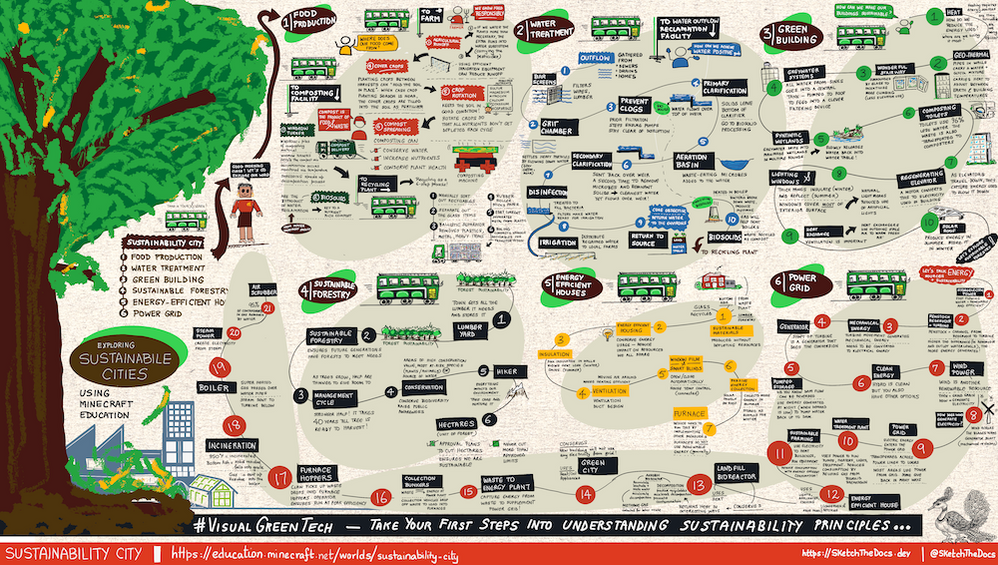
Here is the visual guide to Sustainability City. You can find a hi-res downloadable version of this visual guide here – warning: this is a large file (13MB) so make sure you have the data/bandwidth to download it. See this tweet for a behind-the-scenes time-lapse replay of how it was created.
The visual guide has six sections, each mapping to one of the regions of Sustainability City. Start from the top left and work your way clockwise to the last one. Here is what you’ll learn. Start with Food Production to explore sustainable farming practices including water reclamation and composting. Next, travel to the Water Outflow Reclamation Facility to learn how water from sewers and drains is “cleaned” and used for irrigation or returned to source (water positive) – the removed biosolids become fodder for composting.
Then, explore sustainable practices in the construction of large buildings (make them self-sustaining in energy needs) and explore sustainable forestry practices required to support our lumber needs. Finally, we look at energy-efficient housing and explore the power grid in some detail. As we know, electricity is a proxy for carbon, and understanding the various ways we generate, transport, and use, energy is critical to sustainability education.
I hope you found the guide useful. Making visual guides takes time but is infinitely rewarding. Have comments or feedback? Do leave them below.
 Azure Sentinel: Zero Trust (TIC3.0) Workbook
Azure Sentinel: Zero Trust (TIC3.0) Workbook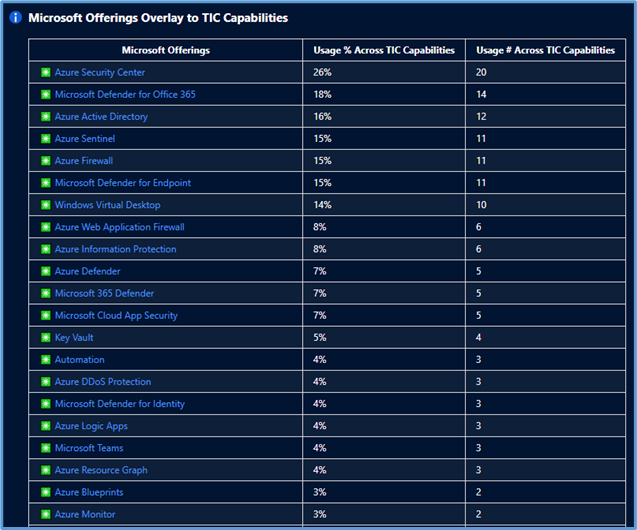 Microsoft Offerings Overlay to TIC Capabilities
Microsoft Offerings Overlay to TIC Capabilities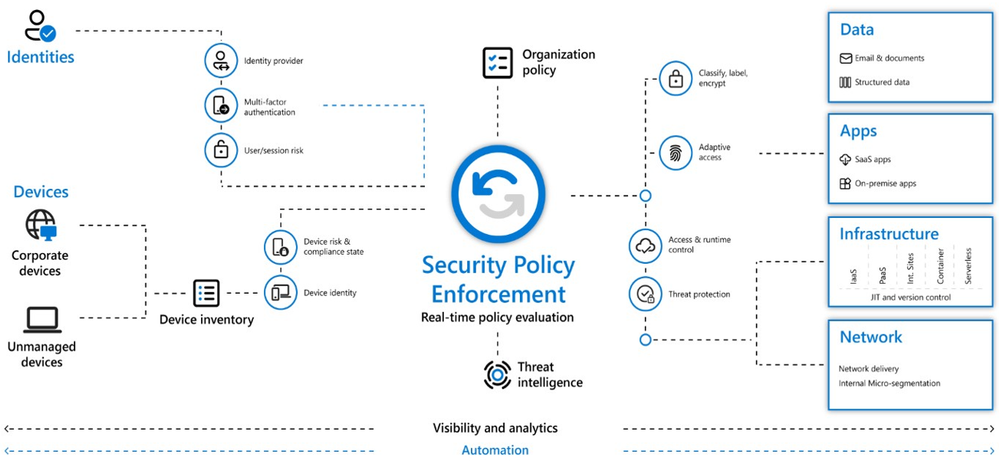 Zero Trust Defined
Zero Trust Defined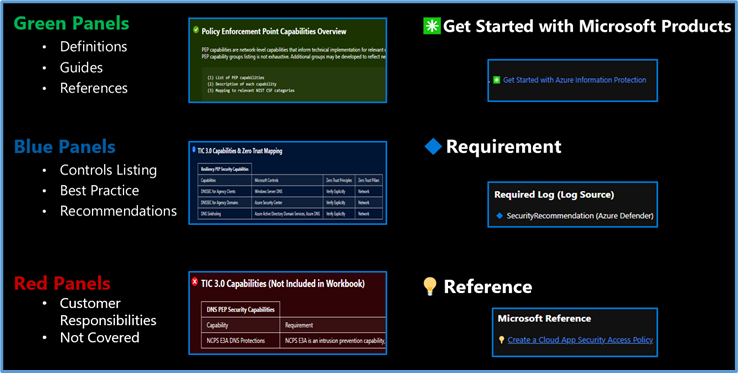 Workbook Navigation
Workbook Navigation Guide Toggle
Guide Toggle Resource Parameter Options
Resource Parameter Options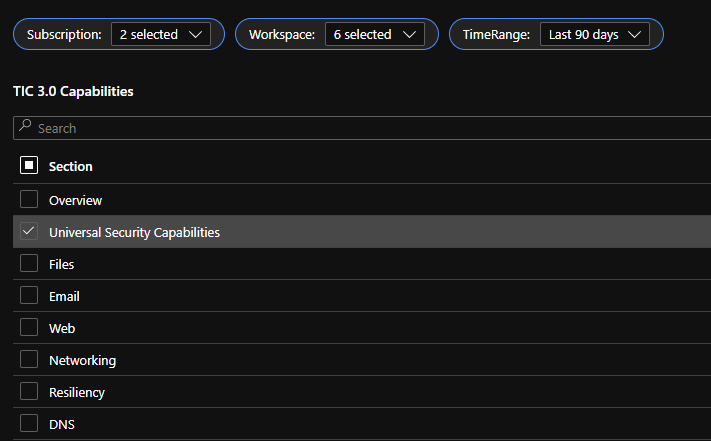 Capabilities Selector
Capabilities Selector TIC 3.0 Overlay to Microsoft Offerings and Zero Trust Principles
TIC 3.0 Overlay to Microsoft Offerings and Zero Trust Principles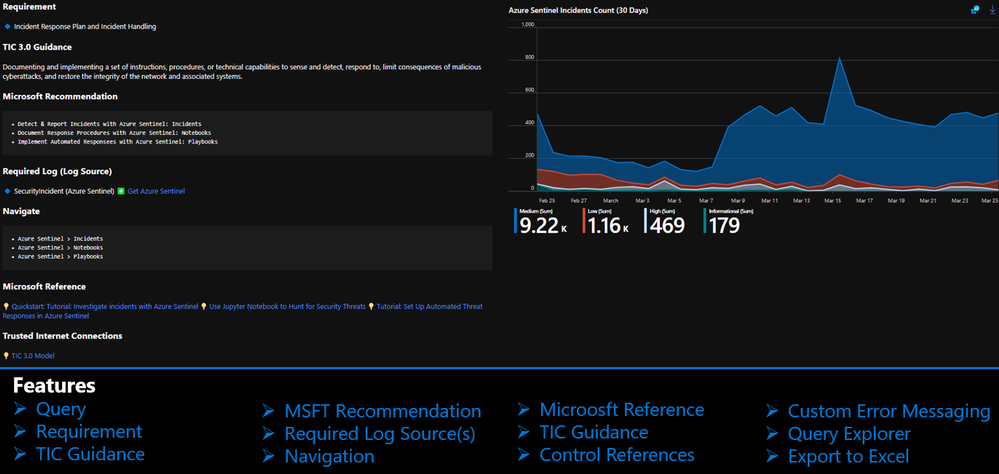 Capability Card
Capability Card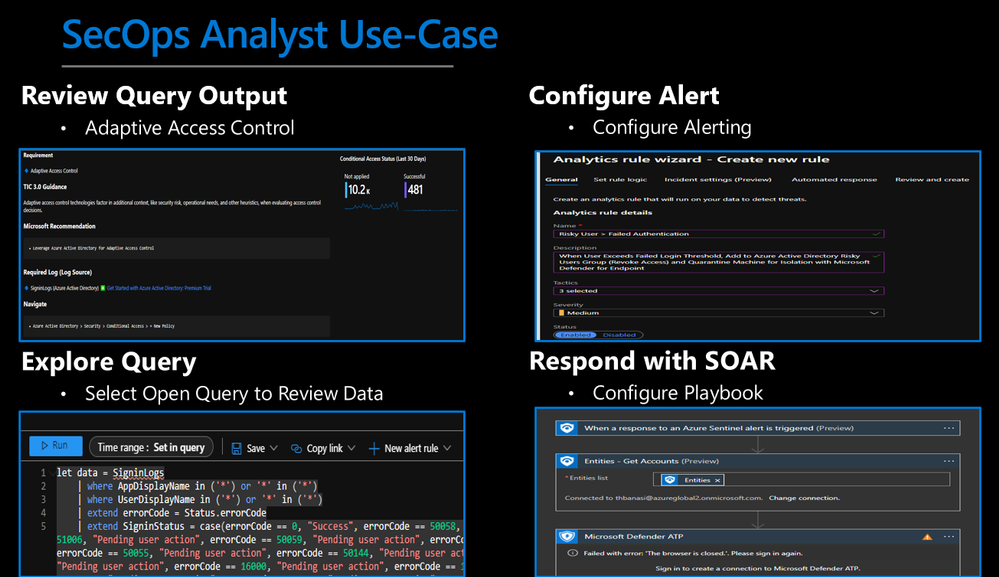 SecOps Analyst Use-Case
SecOps Analyst Use-Case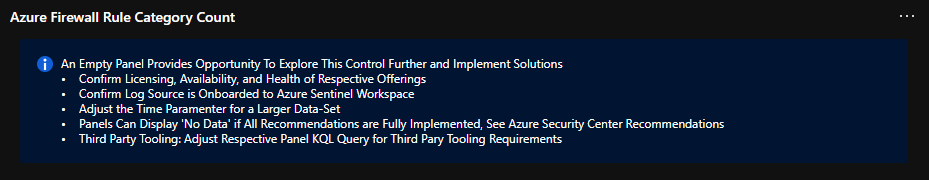 Custom Error Messaging
Custom Error Messaging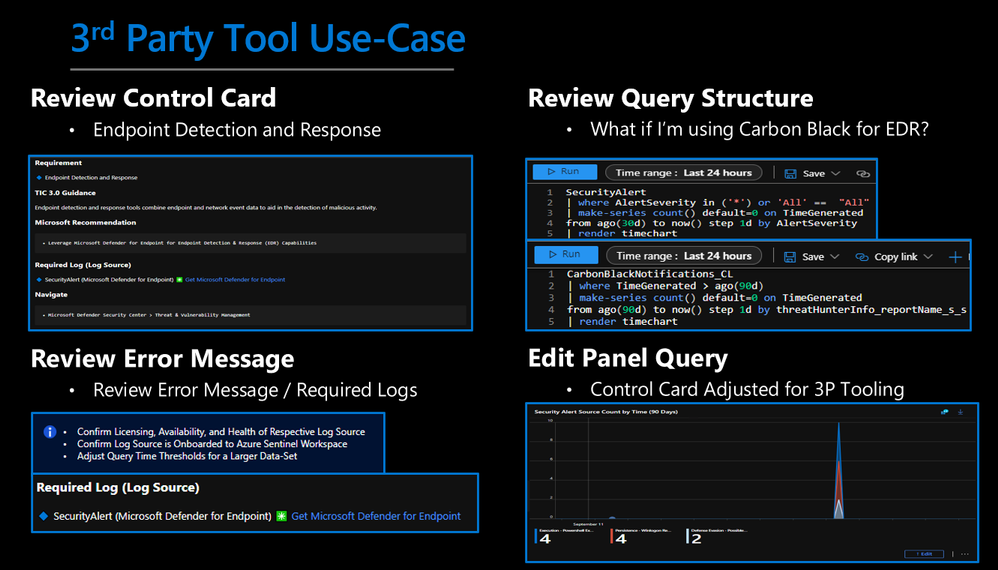 3rd Party Tool Use-Case
3rd Party Tool Use-Case




Recent Comments