by Contributed | Apr 8, 2021 | Technology
This article is contributed. See the original author and article here.
Overview & Use Case
Thanks to Ivan Ovchinnikov, Lead integration developer at Group-IB, Rijuta Kapoor from Microsoft Azure Sentinel Threat Intelligence team, Sreedhar Ande from Microsoft Azure Sentinel PG, the whole Group-IB Threat Intelligence and Azure Sentinel Threat Intelligence Product Group teams for the technical brainstorming, contributing and proof reading!
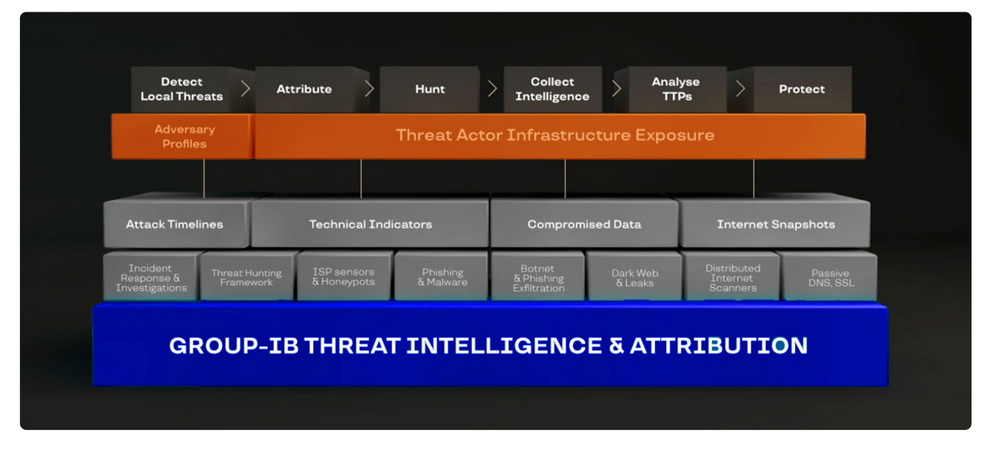
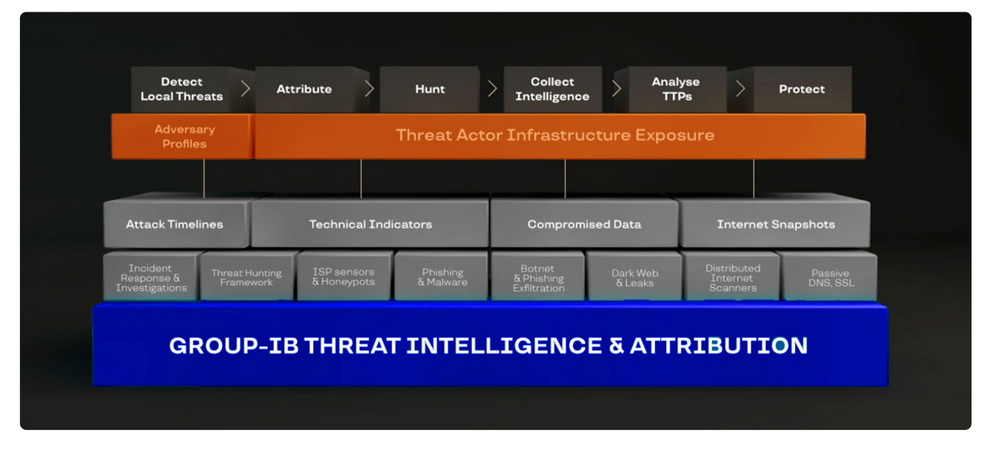
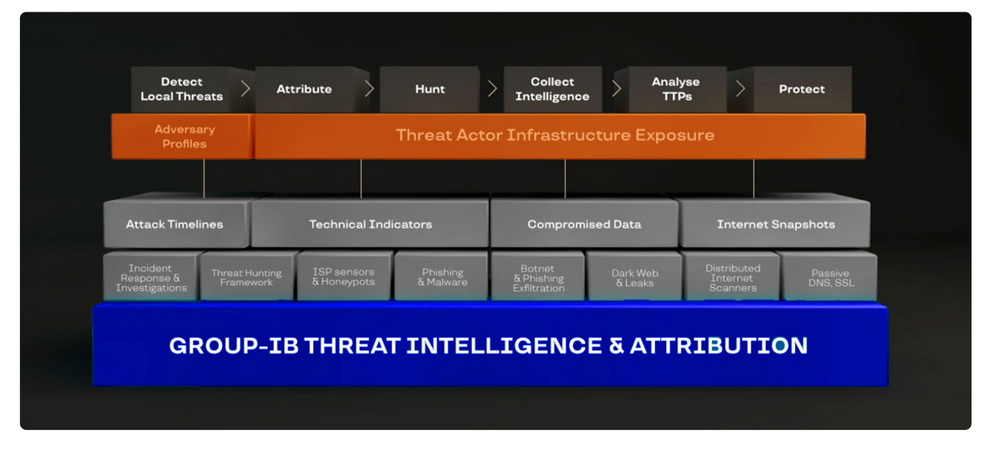
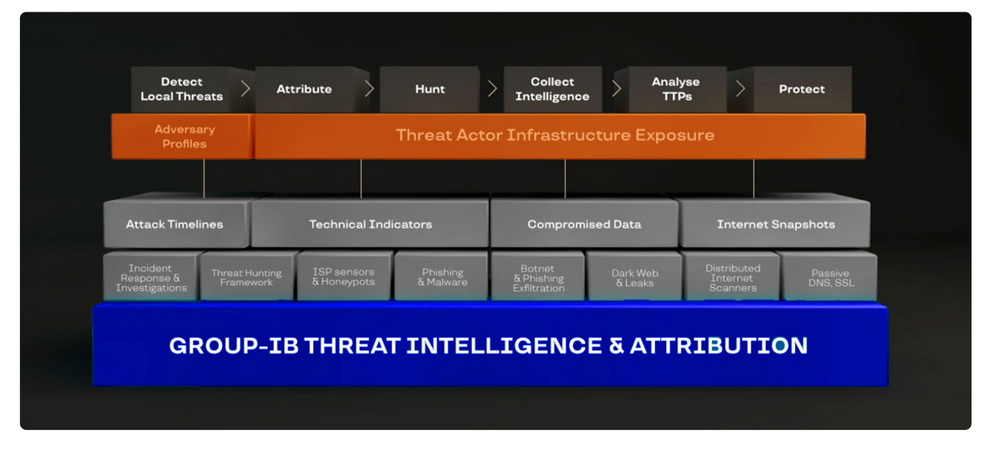
Group-IB Threat Intelligence & Attribution (TI&A) is a system for analyzing and attributing cyberattacks, threat hunting, and protecting network infrastructure based on data relating to adversary tactics, tools and activity. TI&A combines unique data sources and experience in investigating high-tech crimes and responding to complex multi-stage attacks worldwide. The system stores data on threat actors, domains, IPs, and infrastructures collected over the last 15 years, including those that criminals attempted to wipe out. The functionality of the system helps customize it to the threat landscape not only relevant to a particular industry, but also to a specific company in a certain country. Below is the high-level architecture of Group-IB TI&A:
SOC team requirement is to ingest Group-IB TI&A feeds & indicators based on multiple TI collections to Azure Sentinel (and writes them to Microsoft Security Graph API to be listed under Azure Sentinel ThreatIntelligenceIndicators table and custom log tables as well) for automatic scanning and detecting matched TI feeds/indicators across their organizational data sources logs for further investigation and analysis.
Implementation
First let’s understand and get more technical details on the Group-IB TI&A collections to see how we can ingest and map these feeds/indicators to the Azure Sentinel Threat Intelligence data types via TI&A APIs and Azure Sentinel Automation (Playbooks):
gib-tia
|
Collection
|
Has Indicators
|
Indicators Content
|
Description
|
GIBTIA_APT_Threats
|
apt/threat
|
Yes
|
GIB APT Threat Indicator(IPv4)
GIB APT Threat Indicator(domain)
GIB APT Threat Indicator(url)
GIB APT Threat Indicator(md5)
GIB APT Threat Indicator(sha256)
GIB APT Threat Indicator(sha1)
|
Group-IB continuously monitors activities undertaken by hacker groups, investigate, collect, and analyze information about all emerging and ongoing attacks. Based on this information, we provide IOC’s related to APT Groups Attacks
|
GIBTIA_APT_ThreatActor
|
apt/threat_actor
|
No
|
N/A
|
This collection contains APT groups’ info, with detailed descriptions
|
GIBTIA_Attacks_ddos
|
attacks/ddos
|
Yes
|
GIB DDoS
Attack(IPv4)
|
The “DDoS attacks” collection contains a DDoS Attacks targets and C2 indicators
|
GIBTIA_Attacks_deface
|
attacks/deface
|
Yes
|
GIB Attack Deface(url)
|
The “Deface” collection contains information about online resources that have become subject to defacement attacks (the visual content of a website being substituted or modified)
|
GIBTIA_Attacks_phishing
|
attacks/phishing
|
Yes
|
GIB Phishing Domain(domain)
GIB Phishing IP(IPv4)
GIB Phishing URL(url)
|
The “Attacks Phishing” collection provides information about various phishing resources (including URLs, Domains and IPs.)
|
GIBTIA_Attacks_phishing_kit
|
attacks/phishing_kit
|
Yes
|
GIB Phishing Kit Email(email)
|
The “Atacks Phishing Kits” collection contains information about the archives of phishing kits. Emails gotten from kits can be obtained as indicators
|
GIBTIA_BP_phishing
|
bp/phishing
|
Yes
|
GIB Phishing Domain(domain)
GIB Phishing IP(IPv4)
GIB Phishing URL(url)
|
The “BP Phishing” collection provides events related to clients company
|
GIBTIA_BP_phishing_kit
|
bp/phishing_kit
|
Yes
|
GIB Phishing Kit Email(email)
|
The “BP Phishing Kit” collection provides phishing kits related to clients company
|
GIBTIA_Compromised_account
|
compromised/account
|
Yes
|
GIB Compromised Account CNC(url)
GIB Compromised Account CNC(domain)
GIB Compromised Account CNC(IPv4)
|
This collection contains credentials collected from various phishing resources, botnets, command-and-control (C&C) servers used by hackers
|
GIBTIA_Compromised_card
|
compromised/card
|
Yes
|
GIB Compromised Card CNC URL(url)
GIB Compromised Card CNC Domain(domain)
GIB Compromised Card CNC IP(IPv4)
|
This collection contains information about compromised bank cards. This includes data collected from card shops, specialized forums, and public sources
|
GIBTIA_Compromised_imei
|
compromised/imei
|
Yes
|
GIB Compromised IMEI CNC Domain(domain)
GIB Compromised IMEI CNC URL(url)
GIB Compromised IMEI CNC IP(IPv4)
|
The section contains data on infected mobile devices, which is obtained by analyzing mobile botnets. It does not contain personal data and is available to all system users
|
GIBTIA_Compromised_mule
|
compromised/mule
|
Yes
|
GIB Compromised Mule CNC Domain(domain)
GIB Compromised Mule CNC URL(url)
GIB Compromised Mule CNC IP(IPv4)
|
This section contains information about bank accounts to which threat actors have transferred or plan to transfer stolen money. Man-in-the-Browser (MITB) attacks, mobile Trojans, and phishing kits allow fraudsters to make money transfers automatically. Playbook provides C2 data related to compromitation
|
GIBTIA_HI_Threats
|
hi/threat
|
Yes
|
GIB HI Threat Indicator(domain)
|
Group-IB continuously monitors activities undertaken by hacker groups, investigate, collect, and analyze information about all emerging and ongoing attacks. Based on this information, we provide IOC’s related to Hackers Attacks
|
GIBTIA_HI_ThreatActor
|
hi/threat_actor
|
No
|
N/A
|
This collection contains non-APT groups’ and Individual hackers info, with detailed descriptions
|
GIBTIA_Malware_cnc
|
malware/cnc
|
Yes
|
GIB Malware CNC Domain(domain)
GIB Malware CNC URL(url)
GIB Malware CNC IP(IPv4)
|
The “Malware” collection contains Malwares C2 detected by group IB
|
GIBTIA_Malware_Targeted_Malware
|
malware/targeted_malware
|
Yes
|
GIB Malware Targeted Malware(md5)
GIB Malware Targeted Malware(sha1)
GIB Malware Targeted Malware(sha256)
GIB Malware Targeted Malware Inject(md5)
|
The “Targeted Trojans” section contains information about malicious programs targeting the client’s infrastructure. Information is collected by examining a multitude of malicious files and investigating various incidents
|
GIBTIA_OSI_GitLeak
|
osi/git_leak
|
No
|
N/A
|
Open-source repositories such as GitHub contain codes that anyone can search for. They are often used by threat actors planning to attack a specific company. The “Git Leaks” section contains the above data in code repositories
|
GIBTIA_OSI_PublicLeak
|
osi/public_leak
|
No
|
N/A
|
The “Public leaks” collection contains the leaked clinets data collected on popular file-sharing resources or text/information exchange websites
|
GIBTIA_OSI_Vulnerability
|
osi/vulnerability
|
No
|
N/A
|
The “Vulnerabilities” collection displays information about vulnerabilities detected in the software by version
|
GIBTIA_Suspicious_ip_open_proxy
|
suspicious_ip/open_proxy
|
Yes
|
GIB Open Proxy Address(IPv4)
|
The “Open proxy” collection proviedes information about lists of proxy servers that are publicly available on various online resources related to anonymity. In addition, proxy servers may be configured as open proxies intentionally or as a result of misconfiguration or breaches
|
GIBTIA_Suspicious_ip_socks_proxy
|
suspicious_ip/socks_proxy
|
Yes
|
GIB Socks Proxy Address(IPv4)
|
The “Socks proxy” collection providess information about addresses where malware that turns infected computers into SOCKS proxies has been installed. Such computers (bots) are rented out and used in various attacks to ensure the attacker as much anonymity as possible
|
GIBTIA_Suspicious_ip_tor_node
|
suspicious_ip/tor_node
|
Yes
|
GIB Tor Node Address(IPv4)
|
The “Tor Node” collection displays information about Tor exit nodes, which are the final Tor relays in the circuit. The nodes act as a medium between a Tor client and public Internet
|
#Deployment Steps
The whole custom connectors code & deployment templates with detailed instructions and considerations already been uploaded at Azure Sentinel github Playbooks repo
Step(1): Azure Sentinel gib-tia Playbooks
- Deploy GIBIndicatorsProcessor playbook first
- Deploy required collections Playbooks and configure the following parameters:
- GIB Username – is a login to access Group-IB TI&A Web Interface
- Save only indicators – set to true if only indicators enrichment is required, otherwise, an additional table in Workspace with full event content will be created
- Some collections provide no indicators, so do not have this parameter configurable and add Group-IB TI&A events only in Log Workspace
- GIB Action – This is an action required to set in a particular indicator type provided through the current collection.(The action to apply if the indicator is matched from within the target Product security tool. Possible values are: unknown, allow, block, alert)
- GIB API URL – is an GIB TI&A API URL
- Configure API Key variable. API Key can be generated in the Profile Section in Group-IB TI&A Web Interface
Step(2): Register an Azure AD App for TI Indicators Graph API Write Access
- Go to Azure Active Directory / App Registrations
- Create +New Registration
- Give it a name. Click Register
- Click API Permissions Blade
- Click Add a Permission
- Click Microsoft Graph
- Click Application Permissions
- Check permissions for ThreatIndicators (ThreatIndicators.ReadWrite.OwnedBy). Click Add permissions
- Click grant admin consent for domain.com
- Click Certificates and Secrets
- Click New Client Secret
- Enter a description, select never. Click Add
- IMPORTANT. Click copy next to the new secret and paste it somewhere temporarily. You cannot come back to get the secret once you leave the blade
- Copy the client ID from the application properties and paste it somewhere as you will need it to be added to the Playbooks
- Also copy the tenant ID from the AAD directory properties blade
Detection & Investigation
A sample Azure Sentinel Analytics rule to identify a match in CommonSecurityLog Event data from any FileHash IOC from gib-tia, we highly recommend you to check out the list of the Azure Sentinel TI Out of the box TI analytics rules:
//gib-tia TI map File Hash to CommonSecurityLog Event data sources in Azure Sentinel, to identify a match in CommonSecurityLog Event data from any FileHash IOC from gib-tia
let dt_lookBack = 1h;
let ioc_lookBack = 14d;
let fileHashIndicators = ThreatIntelligenceIndicator
| where SourceSystem == "SecurityGraph" and ThreatType == "Malware"
| where TimeGenerated >= ago(ioc_lookBack) and ExpirationDateTime > now()
| where Active == true
| where isnotempty(FileHashValue);
// Handle matches against both lower case and uppercase versions of the hash:
( fileHashIndicators | extend FileHashValue = tolower(FileHashValue)
|union (fileHashIndicators | extend FileHashValue = toupper(FileHashValue)))
| join (
CommonSecurityLog | where TimeGenerated >= ago(dt_lookBack)
| where isnotempty(FileHash)
| extend CommonSecurityLog_TimeGenerated = TimeGenerated
)
on $left.FileHashValue == $right.FileHash
| summarize LatestIndicatorTime = arg_max(TimeGenerated, *) by IndicatorId
| project LatestIndicatorTime, Description, ActivityGroupNames, IndicatorId, ThreatType, Url, ExpirationDateTime, ConfidenceScore,
CommonSecurityLog_TimeGenerated, SourceIP, SourcePort, DestinationIP, DestinationPort, SourceUserID, SourceUserName, DeviceName, DeviceAction,
RequestURL, DestinationUserName, DestinationUserID, ApplicationProtocol, Activity
| extend timestamp = CommonSecurityLog_TimeGenerated, IPCustomEntity = SourceIP, HostCustomEntity = DeviceName, AccountCustomEntity = SourceUserName, URLCustomEntity = Url
Get started today!
We encourage you to try it now!
You can also contribute new connectors, workbooks, analytics and more in Azure Sentinel. Get started now by joining the Azure Sentinel Threat Hunters GitHub community.
by Contributed | Apr 7, 2021 | Technology
This article is contributed. See the original author and article here.
By Luke Ramsdale – Service Engineer | Microsoft Endpoint Manager – Intune
This is the fourth blog in our series on using BitLocker with Intune. In the first post, we described occasions when a BitLocker-enabled device enters recovery mode. You can read about the reasons a device enters recovery mode in the documentation under What causes BitLocker recovery. This post walks you through BitLocker recovery options with Windows devices managed with Intune.
BitLocker recovery functionality
Since the inception of the BitLocker configuration service provider (CSP) in Windows 10, version 1703, there’s been an option to configure BitLocker recovery on protected operating system (OS) drives. This option provides a method to back up recovery information to Microsoft Azure Active Directory (Azure AD) or Azure Active Directory Domain Services (Azure AD DS).
Additionally, new password rotation functionality added in Windows 10, version 1909, allows the recovery key to refresh automatically after it is used to recover a BitLocker enabled device. Only the key used for recovery is refreshed.
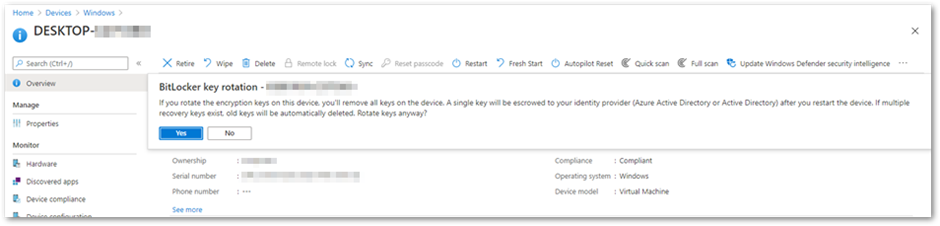
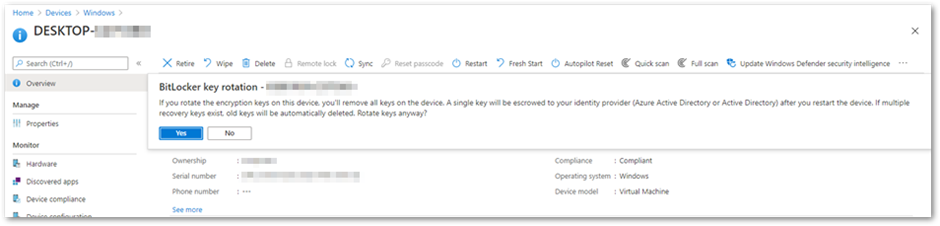
 BitLocker key rotation remote action in the Microsoft Endpoint Manager admin center
BitLocker key rotation remote action in the Microsoft Endpoint Manager admin center
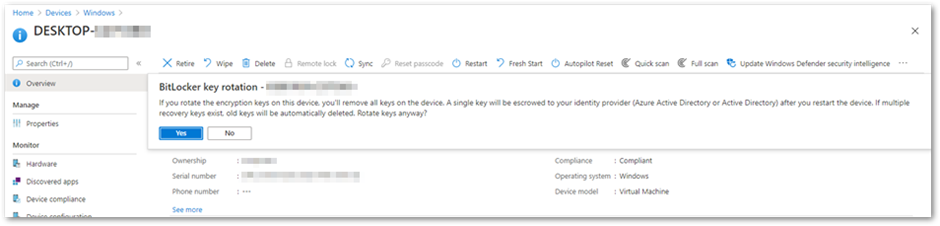
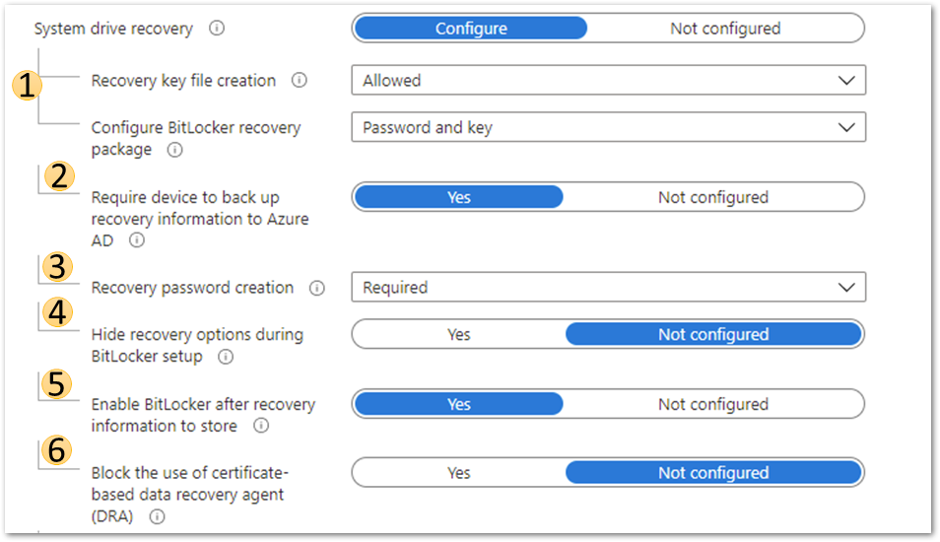
 Azure AD joined device system drive recovery settings
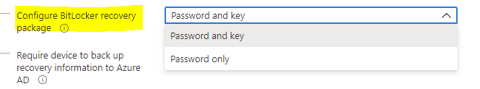
Azure AD joined device system drive recovery settings
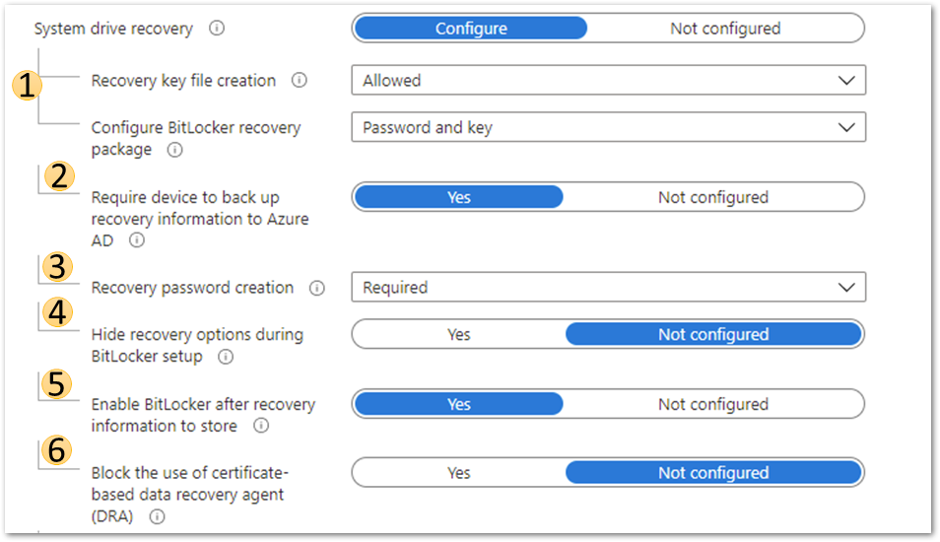
This setting will configure whether the device will back up the password and key or just the key in Azure AD DS.
- The recovery password is a 48-digit recovery password that is used to unlock a volume when the device enters recovery mode.
- The key package and password will help decrypt the encrypted volume if the disk becomes corrupted or damaged.
For more information on BitLocker recovery, review this article, especially the Recovery password retrieval, BitLocker key package, and Retrieving the BitLocker key package sections.
 Configure BitLocker recovery package settings
Configure BitLocker recovery package settings
Setting this to Allowed or Required will generate a 48-digit recovery password during BitLocker initialization and send it to Azure AD if the policy Require device to back up recovery information to Azure Active Directory is set to Yes. Administrative users will be allowed to create new recovery passwords manually on the device.
Setting this option to Deny prevents BitLocker encryption from creating a recovery password and sending it to Azure AD. It will disallow users from generating new recovery passwords manually.
Note
For BitLocker silent encryption to succeed, this setting should be configured to Allowed or Required.
4. Hide recovery options during BitLocker setup
Setting this option to Yes will prevent the end user from accessing recovery options such as saving the key to file or printing it out during the BitLocker setup process. This setting does not apply to silent encryption.
5. Enable BitLocker after recovery information to store
When this option is set to Yes, the recovery key will be backed up to Azure AD DS. This setting is only required in an Azure hybrid services joined scenario.
6. Block the use of certificate-based data recovery agent (DRA)
Setting this option to Yes blocks the ability to use a data recovery agent (DRA) to recover BitLocker enabled drives. Selecting Not Configured will allow the DRA to be set up.
Note
Setting up a DRA requires an enterprise PKI infrastructure to deploy the DRA agent and certificates. A DRA agent gives administrators another method to recover encrypted drives if the recovery key is not available. However, configuring DRA using Intune is not currently supported.
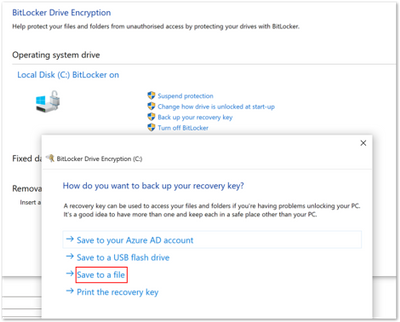
Creating a recovery key text file on the device
After configuring the recovery options in the BitLocker policy, it’s important that the end user can easily access the recovery key on their device. Using the following BitLocker drive encryption settings, you can create a recovery key file manually (as an administrative user) and save the BitLocker recovery key to a local drive as a text file.
- Navigate to Control Panel > System and Security > BitLocker Encryption.
- Select Save to a file if the drive has been encrypted silently.
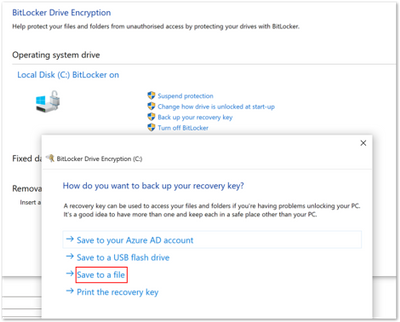 BitLocker Drive Encryption window
BitLocker Drive Encryption window
Note
We don’t recommend printing recovery keys or saving them to a file. Instead, use Active Directory backup or a cloud-based backup. Cloud-based backup includes Azure AD and a Microsoft Account.
Scenario—Troubleshooting an Azure AD joined device
Step 1. Examining recovery settings in mobile device management (MDM) logs
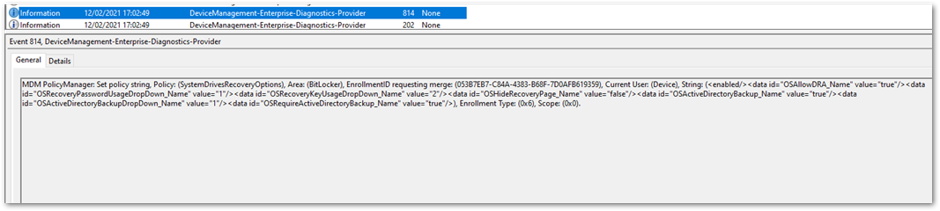
As we discussed in the blog post, Troubleshooting BitLocker from the Microsoft Endpoint Manager admin center, the first step in troubleshooting is examining the encryption report in the Microsoft Endpoint Manager admin center. If that doesn’t help, your next step is to examine the MDM logs on the device to see if the policy has applied successfully. There are many ways to collect event logs from a Windows device. You can read this article to learn about the procedures for collecting logs.
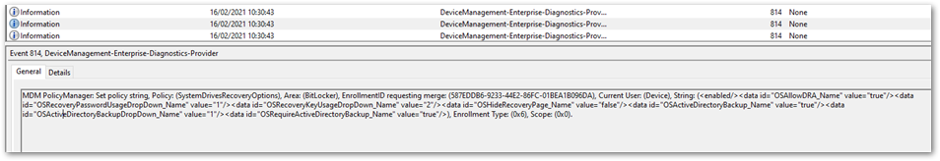
When you enroll a device or change policy settings, you should see similar information for recovery settings in the DeviceManagement-Enterprise-Diagnostic-Provider event log. If there are problems applying the policy from an MDM agent perspective, errors will show up in this log.
The following example shows troubleshooting an Azure AD joined device viewing this event log and the MDMDiagnostics report. The deployment is successful, and you can see that there are two ways to view the same settings.
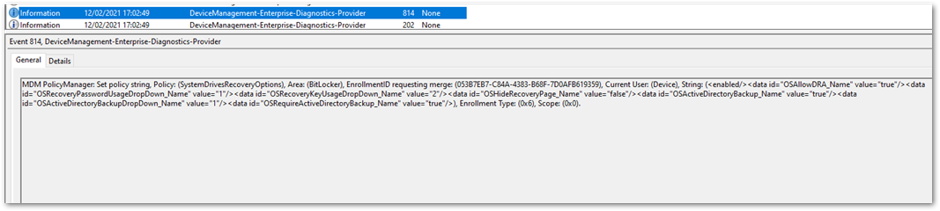 DeviceManagement-Enterprise-Diagnostic-Provider event log
DeviceManagement-Enterprise-Diagnostic-Provider event log
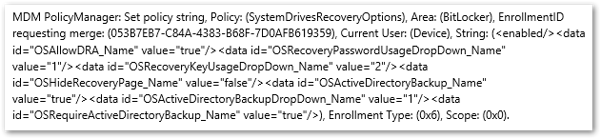
 DeviceManagement-Enterprise-Diagnostic-Provider output from the general tab
DeviceManagement-Enterprise-Diagnostic-Provider output from the general tab
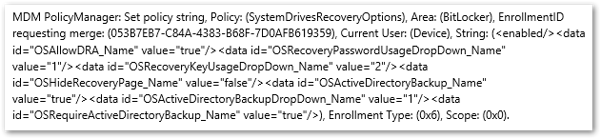
 MDMDiagnostics report entry
MDMDiagnostics report entry
<data id="OSAllowDRA_Name" value="true"/>
<data id="OSRecoveryPasswordUsageDropDown_Name" value="1"/>
<data id="OSRecoveryKeyUsageDropDown_Name" value="2"/>
<data id="OSHideRecoveryPage_Name" value="false"/>
<data id="OSActiveDirectoryBackup_Name" value="true"/>
<data id="OSActiveDirectoryBackupDropDown_Name" value="1"/>
<data id="OSRequireActiveDirectoryBackup_Name" value="true"/>
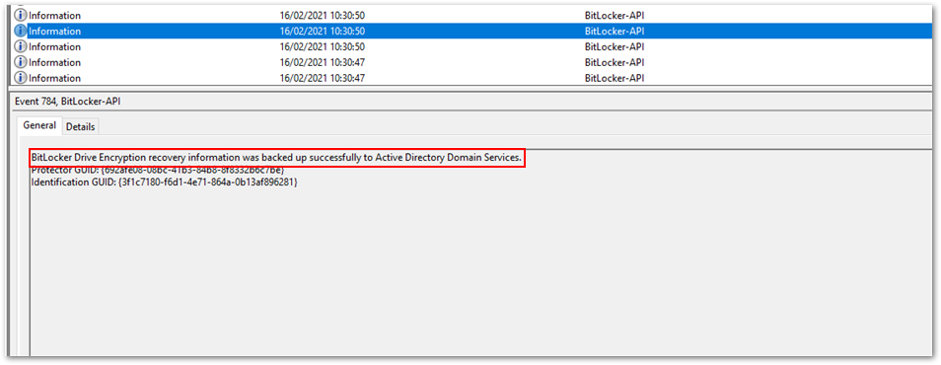
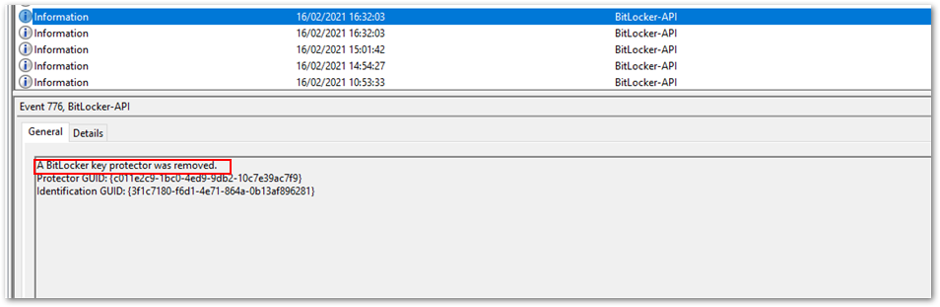
Step 2. Checking the BitLocker-API event log
If the report confirms that there were no errors applying the policy in the DeviceManagement-Enterprise-Diagnostic-Provider event log, the next step is to check event logs in the BitLocker-API folder to see how the recovery information was processed. (The Management log, Operational log and other logs are generated in this folder.) To review the event log, right-click on Start > Event Viewer > Applications and Services Logs > Microsoft > Windows > BitLocker–API.
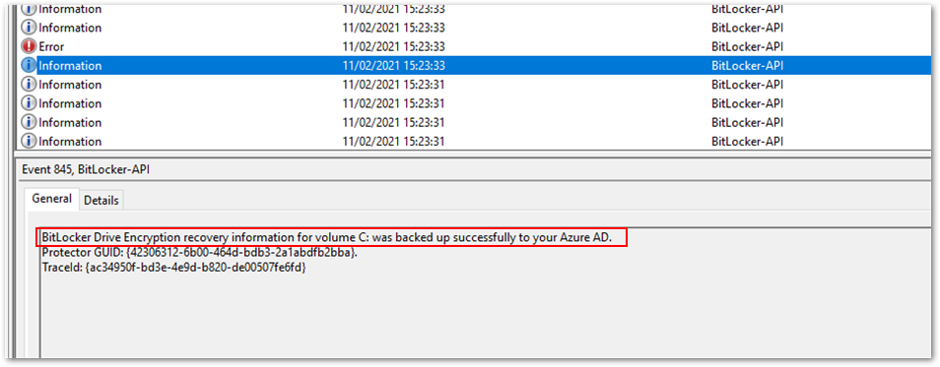
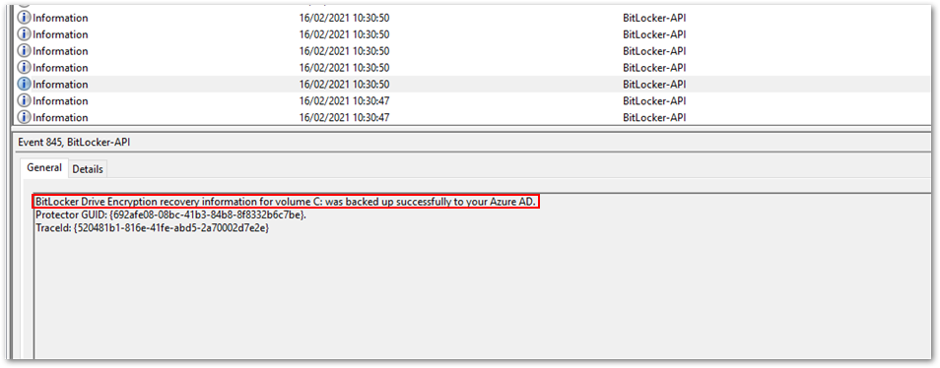
This example displays the Management log and shows that the key was successfully backed up to Azure AD.
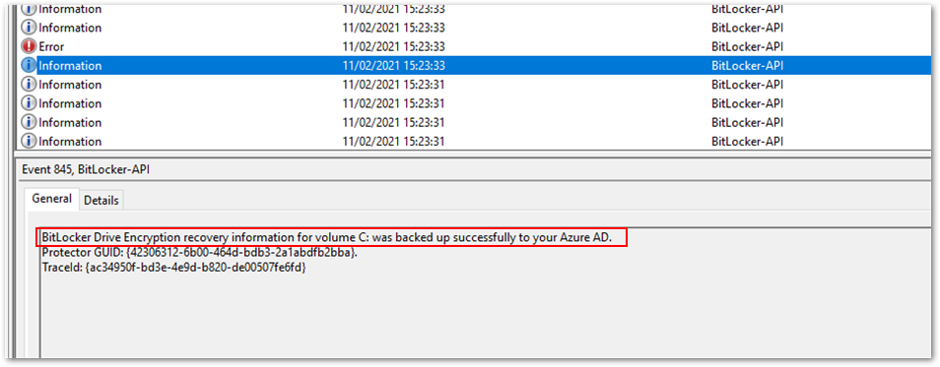 Successful back-up to Azure AD
Successful back-up to Azure AD
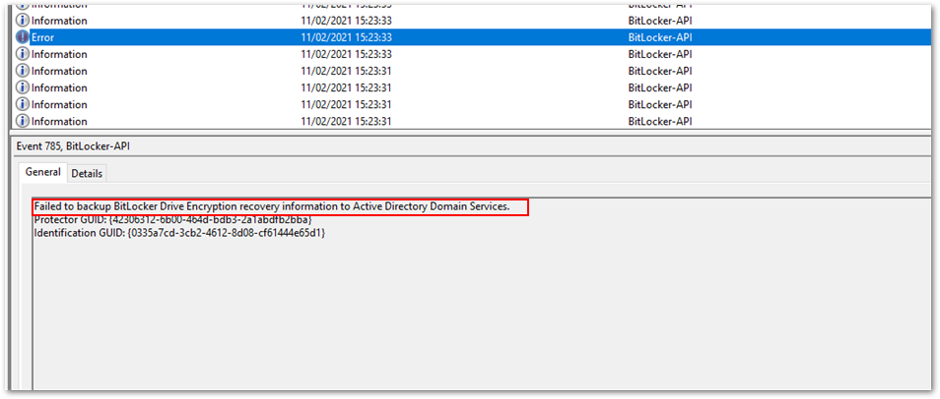
In the following example, backing up the key failed because the device was Azure AD joined but the policy specified backing up to Azure AD DS.
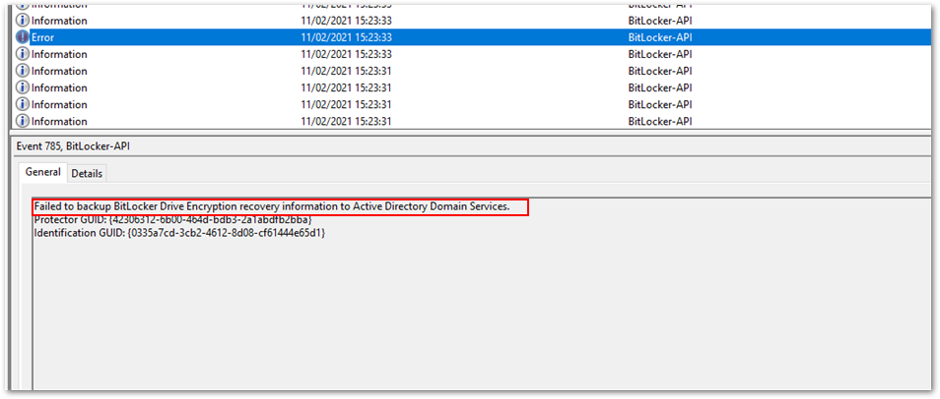 Policy causes back-up error
Policy causes back-up error
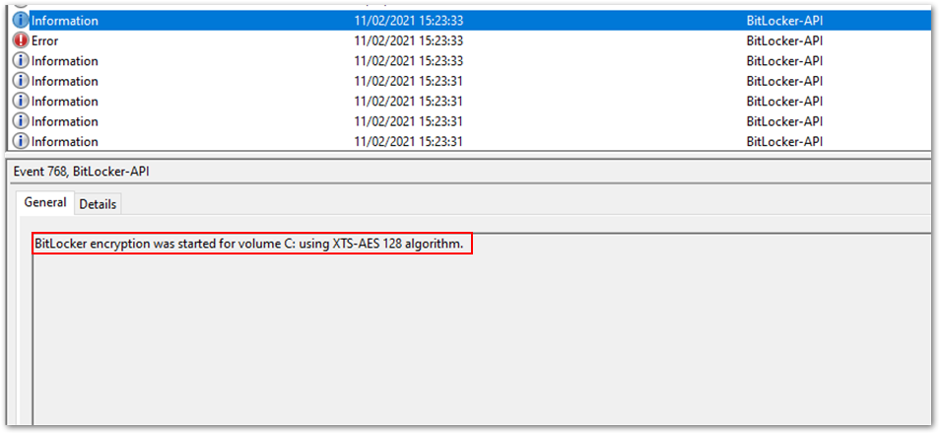
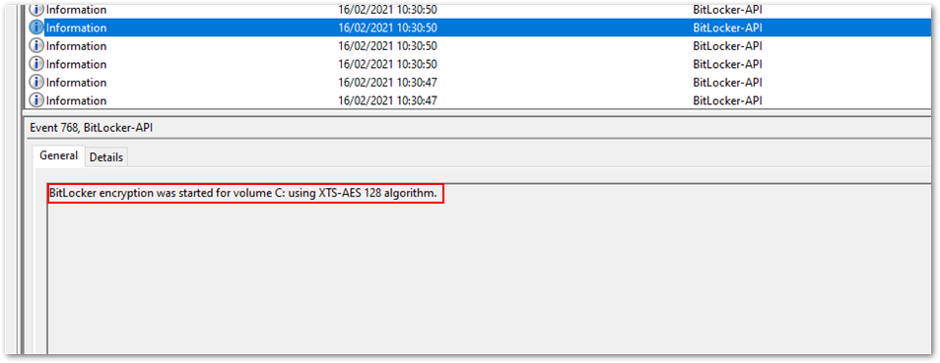
After the key is backed up, BitLocker encryption will start immediately.
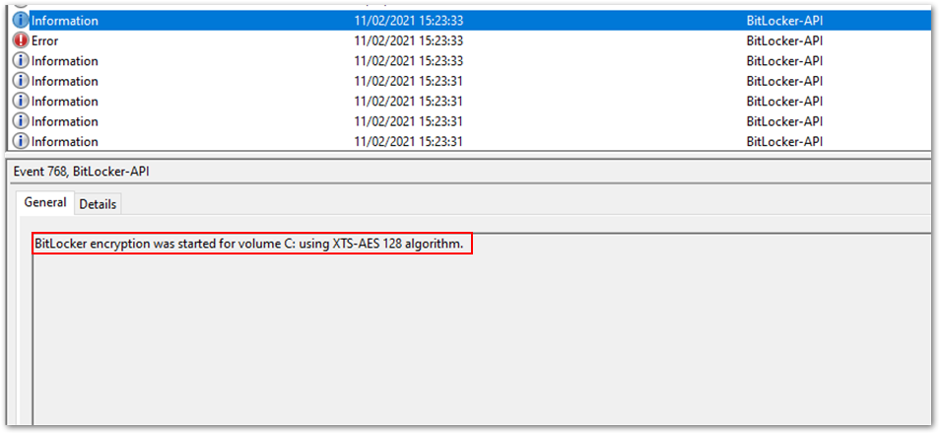 Encryption begins after back-up
Encryption begins after back-up
Important
In this scenario, the same policy and settings are used to silently encrypt an Azure hybrid services joined Windows 10 device. (See the above scenario for the event text and settings).
Step 1. Examining the event log
The policy settings are picked up in the DeviceManagement-Enterprise-Diagnostic-Provider event log:
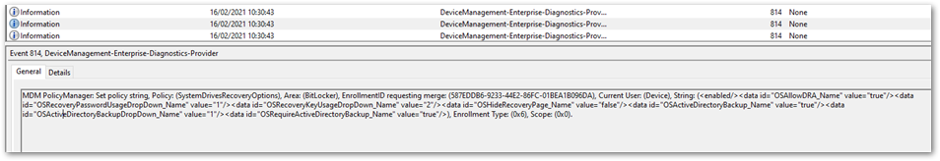 Policy settings in the DeviceManagement-Enterprise-Diagnostic-Provider event log
Policy settings in the DeviceManagement-Enterprise-Diagnostic-Provider event log
Step 2. Checking the BitLocker-API event log
In the BitLocker-API event log, you see the following events:
- First, recovery information is backed up to Azure AD.
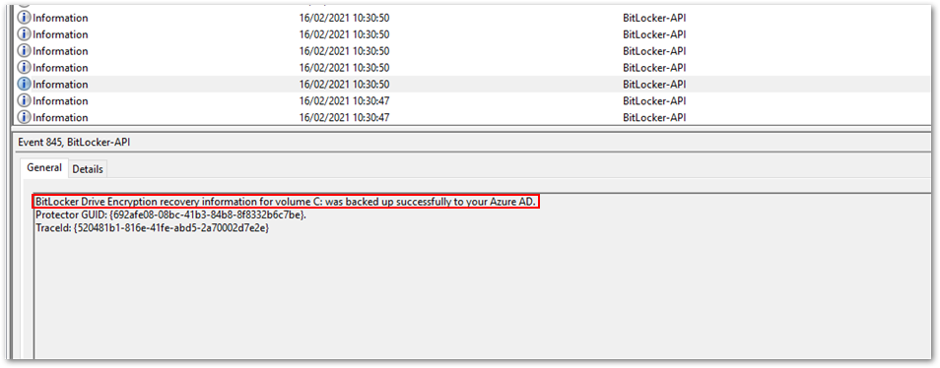 Recovery information is backed up to Azure AD
Recovery information is backed up to Azure AD
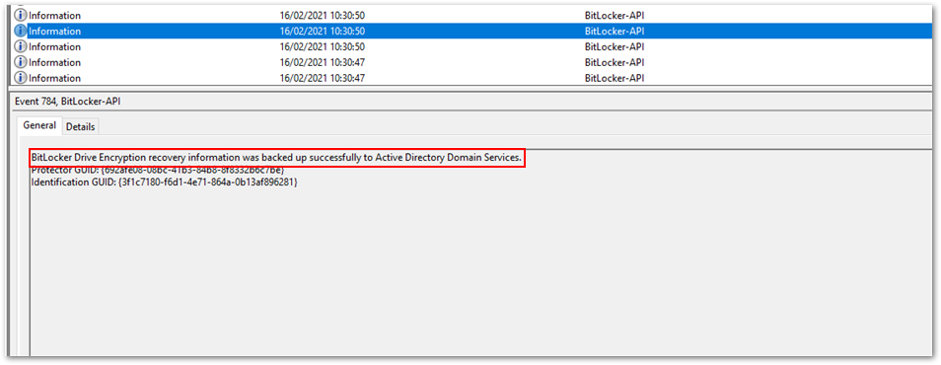
- Then recovery information is backed up to Active Directory Domain Services.
 Backup to Azure AD DS
Backup to Azure AD DS
- As soon as the keys have been backed up to both Azure AD and Azure AD DS, encryption begins:
 Encryption begins after the backup process is complete.
Encryption begins after the backup process is complete.
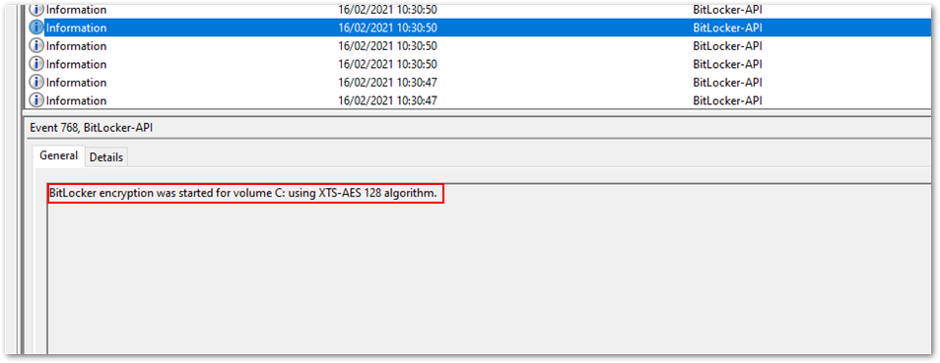
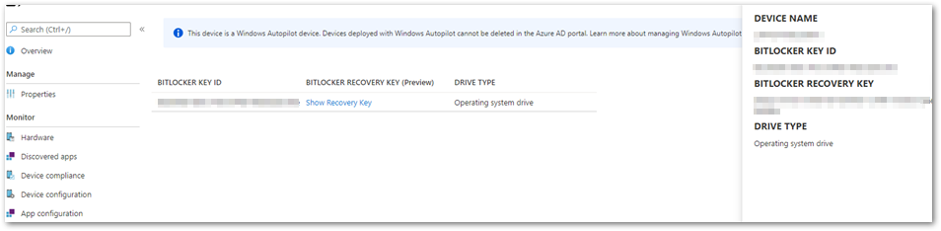
- The recovery key is now visible in the Microsoft Endpoint Manager admin center. To view the recovery key:
Open the Microsoft Endpoint Manager admin center.
Select Devices > All devices.
Select your device from the list and then select Monitor > Recovery keys.
 Recovery key in the MEM admin center
Recovery key in the MEM admin center
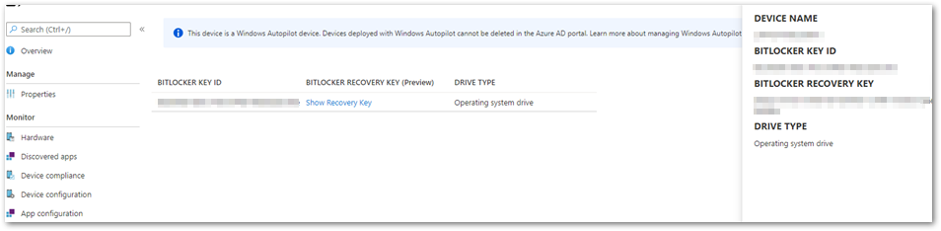
Additional viewing and troubleshooting tools
BitLocker Recovery Password Viewer tool
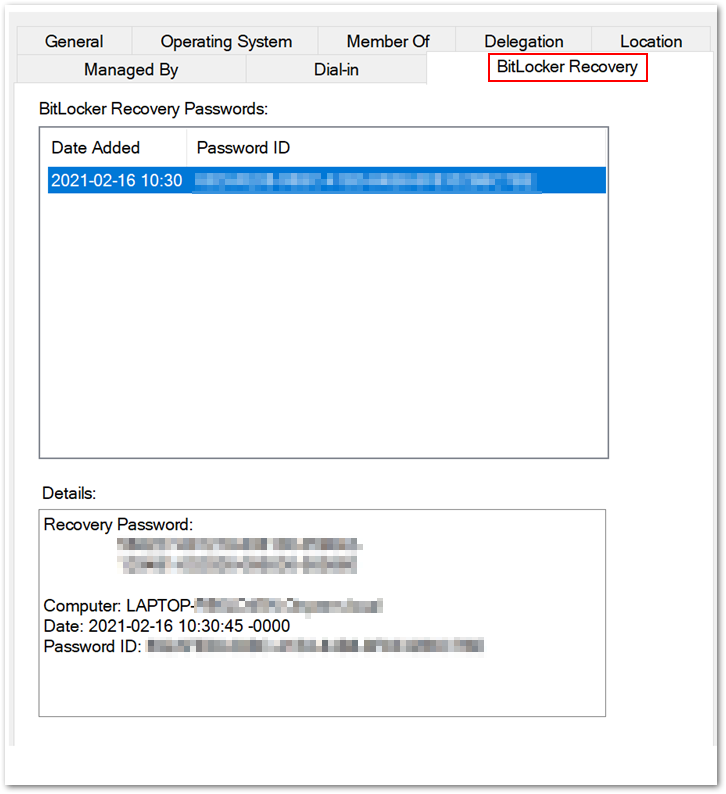
 BitLocker Recovery tab in the Properties dialog box
BitLocker Recovery tab in the Properties dialog box
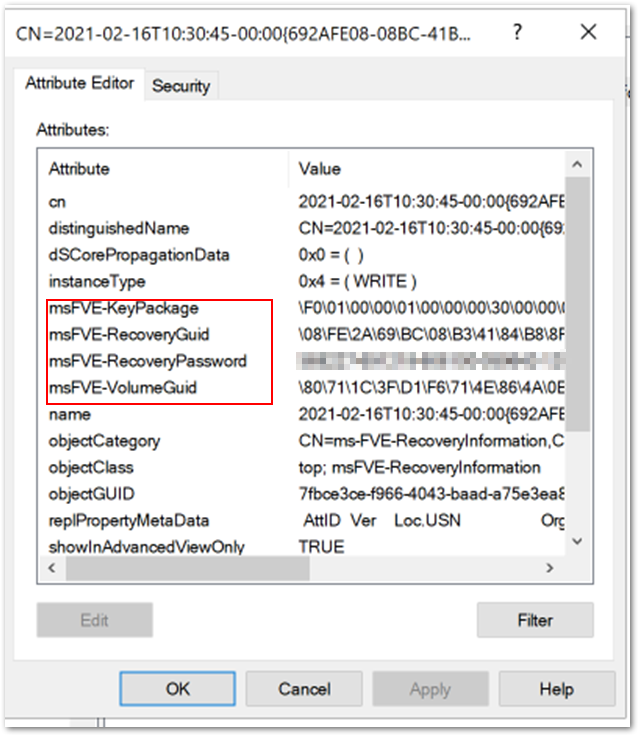
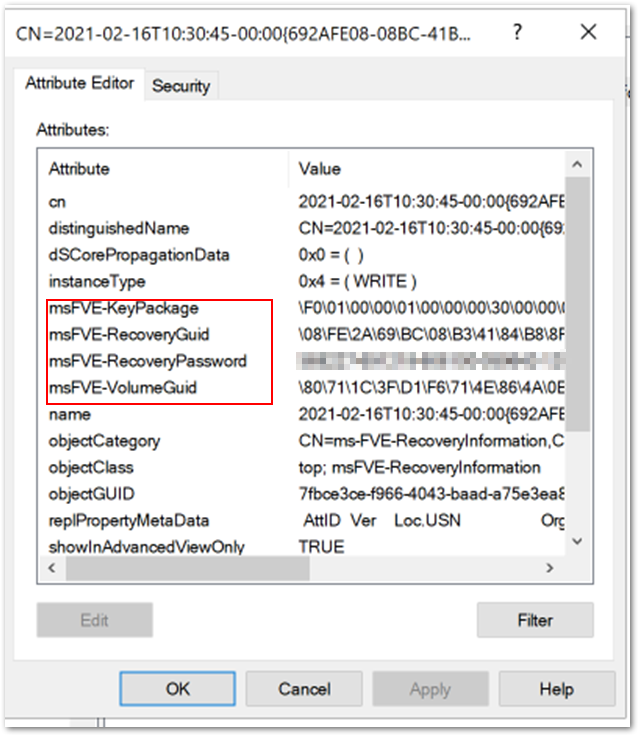 Additional FVE attributes stored in Azure AD DS
Additional FVE attributes stored in Azure AD DS
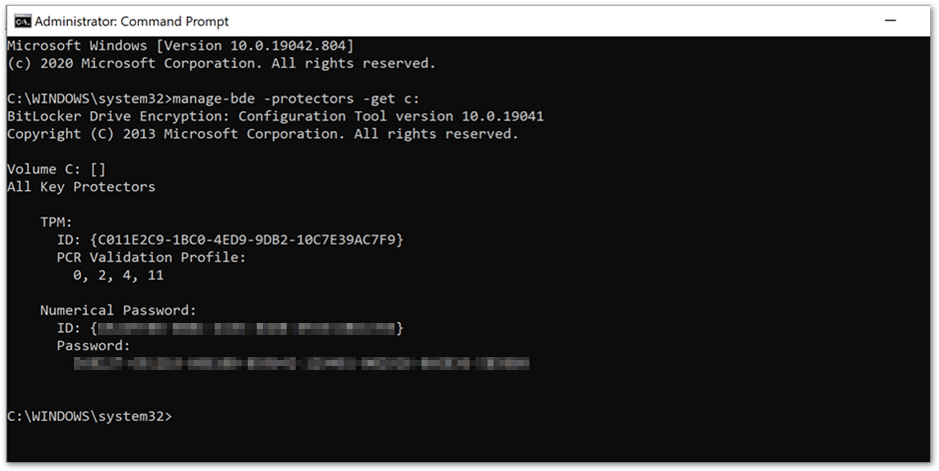
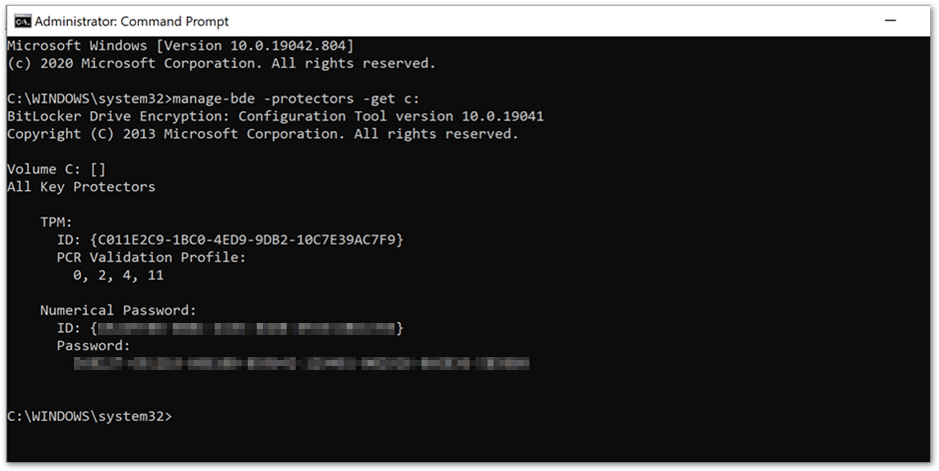 Manage-bde command prompt showing key protectors
Manage-bde command prompt showing key protectors
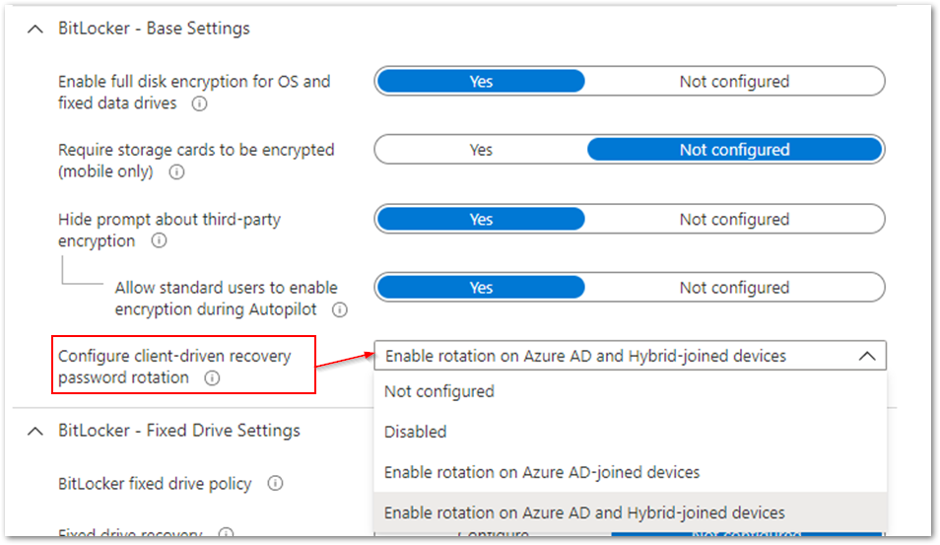
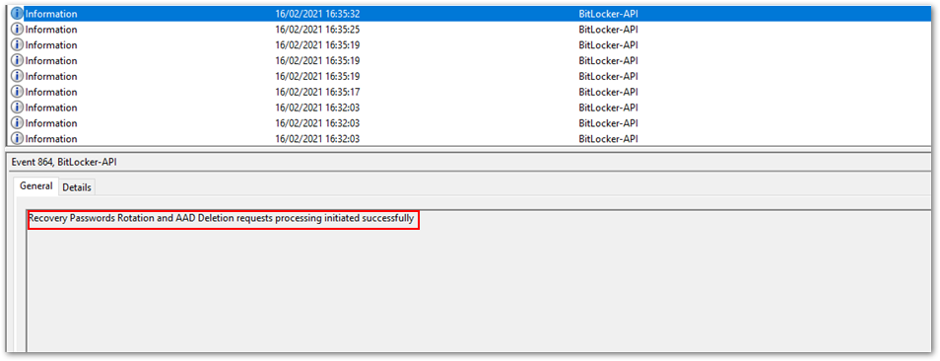
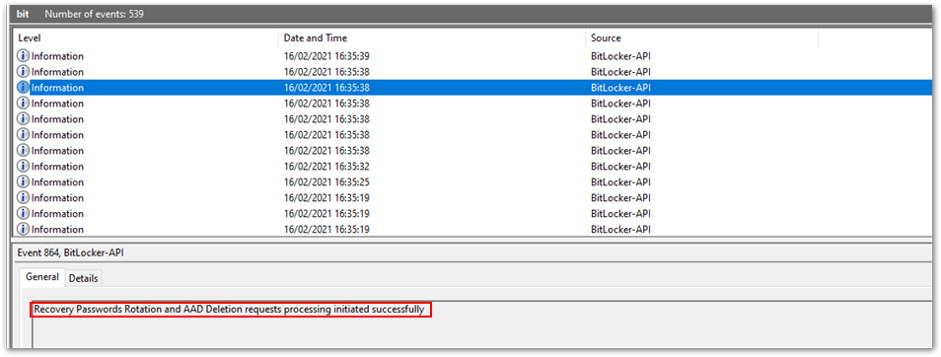
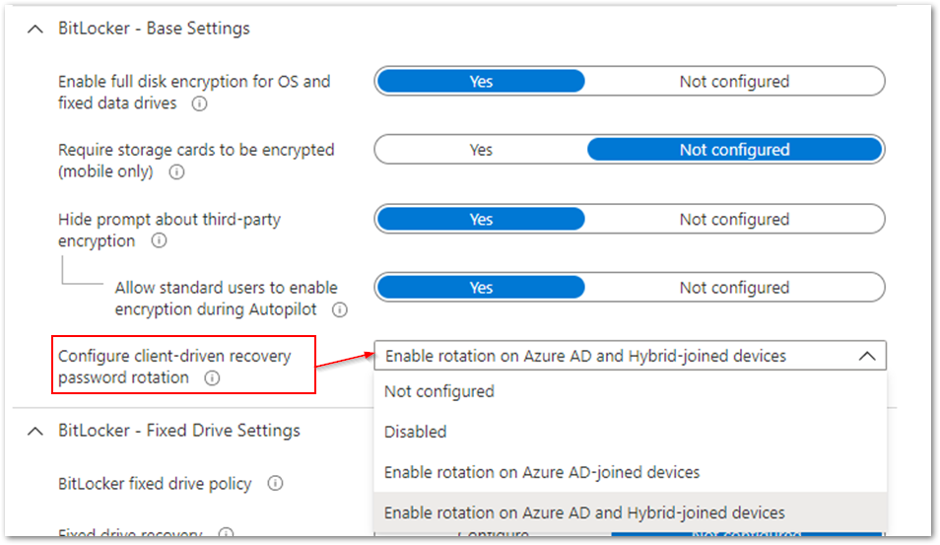 Client-driven password rotation options
Client-driven password rotation options
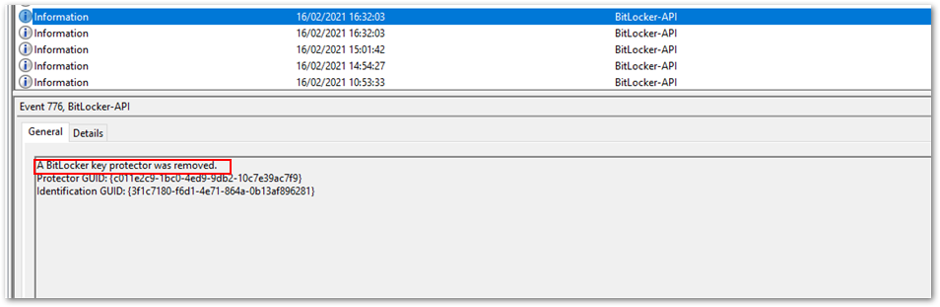 BitLocker-API event log
BitLocker-API event log
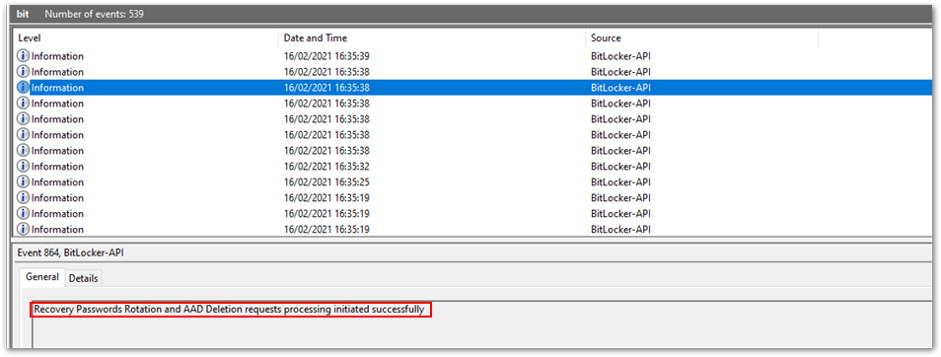 Successful recovery password rotation and Azure AD deletion request
Successful recovery password rotation and Azure AD deletion request
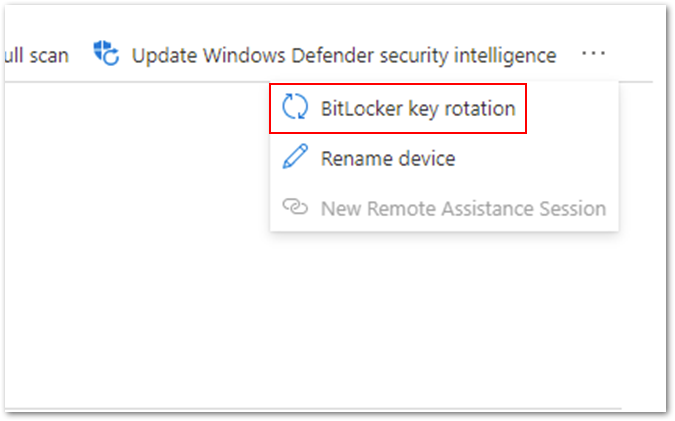
It’s also possible to initiate the rotation of recovery passwords for individual devices remotely.
Navigate to the Microsoft Endpoint Manager admin center.
Select Devices > Windows.
Select a device from the list of devices, select Overview > ellipses (…), and then select BitLocker key rotation.
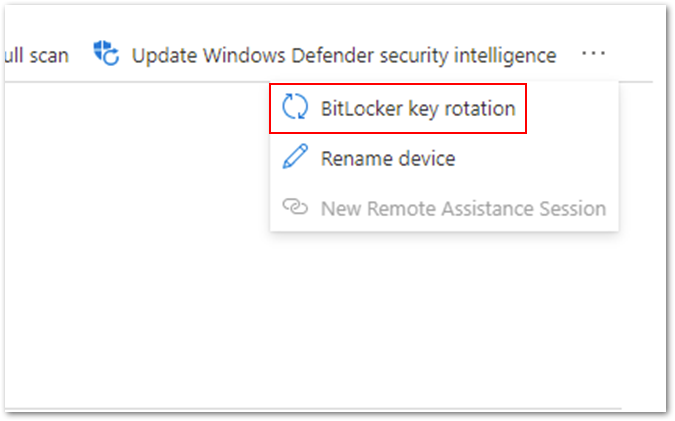 Option for remote BitLocker key rotation
Option for remote BitLocker key rotation
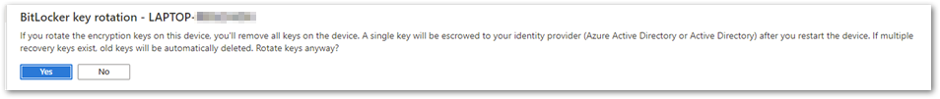
After selecting this option, you will receive an additional prompt to make sure you understand the implications:
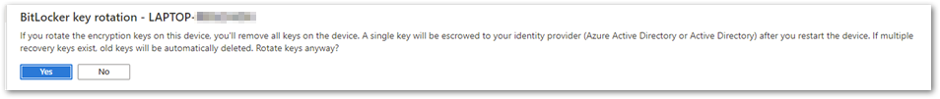 BitLocker key rotation confirmation screen
BitLocker key rotation confirmation screen
All the existing keys will be removed from the device and the new recovery key will be stored in Azure AD or Azure AD DS . The key that was deleted from the device and stored in Azure AD will be removed.
Summary of BitLocker recovery options with Intune managed devices
- You can store recovery keys in Azure AD before initiating the encryption of a device if the device is Azure AD joined.
- Recovery keys can also be stored in Azure AD and on-premises Active directory (if required) for Azure hybrid services joined devices.
- For increased security you can rotate a device’s recovery keys automatically or manually through the Microsoft Endpoint Manager admin center.
- For troubleshooting recovery key policy processing, examine the DeviceManagement-Enterprise-Diagnostic-Provider event log and MDMDiagnostic report.
- For troubleshooting recovery key implementation, examine the BitLocker-API event log and use the manage-bde -protectors command.
Note
DRA is not currently supported for Intune managed devices.
Frequently asked questions (FAQs)
- What happens if a device is removed from Intune? Will I still have access to the recovery keys?
Answer: If the device is backed up to Microsoft Azure Active Directory (Azure AD) or on-premises Active Directory and the device object is not removed from those directories, then the key will still accessible.
- Does Intune store recovery keys for removable storage devices?
Answer: Currently there is no way to store the recovery key for removable storage devices in Azure AD or on-premises Active Directory.
- What are the minimum role-based access control (RBAC) rights required to access the recovery key in the Intune console?
Answer: To be able to access the recovery keys, an administrator must be granted Helpdesk Administrator permissions. Find out more about Azure AD roles in this article.
- If my device is already encrypted before enrolling into Intune, how do I back up the recovery key?
Answer: Use the BackupToAAD-BitLockerKeyProtector PowerShell Cmdlet or rotate the key from the Microsoft Endpoint Manager admin center.
More info and feedback
For further resources on this subject, please see the links below.
BitLocker recovery guide (Windows 10)
BitLocker CSP documentation
Setting the BitLocker encryption algorithm for Autopilot devices
Encrypt Windows 10 devices with BitLocker in Intune – Microsoft Intune
Guidelines for troubleshooting BitLocker
The last post in this series will cover recommended settings for configuring BitLocker encryption with Endpoint security. Stay tuned! Check out other blogs in this series:
- Enabling BitLocker with Microsoft Endpoint Manager – Microsoft Intune – Microsoft Tech Community
- Troubleshooting BitLocker from the Microsoft Endpoint Manager admin center – Microsoft Tech Community
- Troubleshooting BitLocker policies from the client side – Microsoft Tech Community
Let us know if you have any additional questions by replying to this post or reaching out to @IntuneSuppTeam on Twitter.
by Contributed | Apr 7, 2021 | Technology
This article is contributed. See the original author and article here.
Workbooks in Application Insights are a powerful tool for guided investigations, data analysis, & rich visualizations.
We’ve updated the Application Insights Workbooks resource type to match the resource type used by all other Azure Workbooks so our users can take full advantage of all the functionality provided by Workbooks. The new Workbook resources can be queried via Azure Resource Graph, support ARM templates, saved in the region of your choice, & more!
To take advantage of these new features & preserve your favorite reports please convert your existing workbooks by June 30, 2021.
Conversion steps to take:
- Open the desired workbook
- Select the ‘Edit’ option
- Then click ‘Save as’
- Enter the workbook’s name
- Select a subscription, resource group, & region where you have write access
- Delete the legacy workbook
(Optional)
- Update links in other workbooks to use your new version
See this documentation for in-depth conversion guidance and more information about the upcoming change!
by Contributed | Apr 7, 2021 | Technology
This article is contributed. See the original author and article here.
SQL Server 2019 on Ubuntu 20.04
We are happy to announce the official production support and availability of SQL Server 2019 package native to Ubuntu 20.04 distribution starting with CU 10. You can read more about the SQL Server 2019 CU 10 release here.
You can follow the below link to get started with SQL Server 2019 on Ubuntu 20.04:
https://docs.microsoft.com/en-us/sql/linux/quickstart-install-connect-ubuntu?view=sql-server-ver15#install
SQL Server 2019 on Ubuntu 20.04 based containers
We are glad to announce the availability of SQL Server 2019 CU 10 container image built on ubuntu 20.04. It is fully supported for production use. The tag for the container image is : ‘2019-CU10-ubuntu-20.04’ and you can pull the image using the command below:
docker pull mcr.microsoft.com/mssql/server:2019-CU10-ubuntu-20.04
No more python 2 dependency across all supported distributions, starting from SQL Server 2019 CU 10.
As we all are aware that python 2 is no longer supported and has reached end of life, starting SQL Server 2019 CU 10 we have also moved away from python 2 dependency to python 3 for all supported SQL Server 2019 distributions.
Thanks!
Mike Habben (Principal Software Engineering Manager)
Pat Schaefer (Senior Software Engineer)
Pranav Raj (Software Engineer)
Tejas Shah (Principal Program Manager)
Amit Khandelwal (Senior Program Manager)



Recent Comments