by Contributed | Mar 18, 2021 | Technology
This article is contributed. See the original author and article here.
Introduction
This is John Barbare and I am a Sr Customer Engineer at Microsoft focusing on all things in the Cybersecurity space. In a previous blog back in July, 2020, I walked through a demo of setting up an Attack Surface Reduction (ASR) rule policy in Microsoft Endpoint Manager (MEM) for your Windows Operating Systems and how to view the detections once applied.
Since then, Microsoft has introduced a new “Warn Mode” in addition to the Audit and Block modes previously. With that said, I will give a brief overview of ASR Rules, demo what the differences are in the different modes, show custom security notifications for your organization, and the hunt for ASR rule alerts in the new Microsoft 365 Defender unified portal.
What are Attack Surface Reduction Rules?
Attack surface reduction rules help prevent software behaviors that are often abused to compromise your device or network. For example, an attacker might try to run an unsigned script off a USB drive, or have a macro in an Office document make calls directly to the Win32 API. ASR rules can constrain these kinds of risky behaviors and improve your organization’s defensive posture to decrease your risk considerably from being attacked with Ransomware, various other types of malware, and other attack vectors.
If you are evaluating or executing a proof of concept from a 3rd party HIPS (Host Intrusion Prevention System) over to ASR rules, this article will assist you in the planning, development, and proper configuration in MEM. With the complete end to end protection Microsoft offers, this article will focus on the Attack Surface Reduction component of Windows Defender Exploit Guard. Prevent actions and apps that are commonly used by malware, such as launching executables from email (.exe, .dll, .scr, .ps, .vbs, and .js).
- Scripts or applications that launch child processes
- Most rules can be set to Audit to monitor activity prior to being set to enforce
- All rules support exclusions based on file or folder names
- ASR rules support environmental variables and wildcards
ASR rules may block legitimate applications from making changes, so these features come with both an Audit mode and a Block mode and a newly released Warn mode. I always recommend to my customers when configuring ASR rules for the first time to conduct the changes in Audit mode first so it will allow for testing of the policy before moving any of the rules into Block mode. But now we can audit, then warn, before placing into block mode so our users know that a risky behavior is being detected. This is exactly like using SmartScreen where the user goes to website that is malicious, and is warned but given the choice to bypass or not continue at all. This is great before rolling out a new feature and will provide some great context around the warn mode feature.
Warn mode
With the new warn mode, whenever content is blocked by an ASR rule, users see a dialog box that indicates the content is blocked. The dialog box also offers the user an option to unblock the content. The user can then retry their action, and the operation completes. When a user unblocks content, the content remains unblocked for 24 hours, and then blocking resumes. Warn mode helps your organization have ASR rules in place without preventing users from accessing the content they need to perform their tasks.
Supported OS for Warn Mode and Requirements
Warn mode is supported on devices running the following versions of Windows OS:
Microsoft Defender Antivirus must be running with real-time protection in Active mode.
In addition, make sure Microsoft Defender Antivirus and antimalware updates are installed.
- Minimum platform release requirement: 4.18.2008.9
- Minimum engine release requirement: 1.1.17400.5
Exceptions to Warn Mode
The following three ASR rules are not supported in Warn Mode:
- Block JavaScript or VBScript from launching downloaded executable content (GUID d3e037e1-3eb8-44c8-a917-57927947596d)
- Block persistence through WMI event subscription (GUID e6db77e5-3df2-4cf1-b95a-636979351e5b)
- Use advanced protection against ransomware (GUID c1db55ab-c21a-4637-bb3f-a12568109d35)
In addition, warn mode is not supported on devices running older versions of Windows. In those cases, ASR rules that are configured to run in warn mode will run in block mode.
Setting up Warn Mode Using Microsoft Endpoint Manager
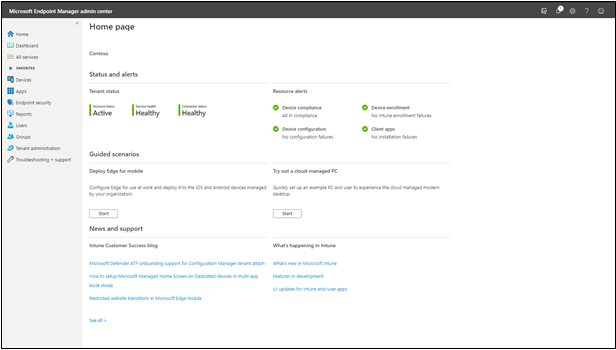
The first item we want to do is make sure that all the devices we want to push the new ASR rule policy are showing up inside MEM admin center. This paper assumes you have enrolled all the devices for your preferred method, and we are checking to make sure the devices are shown before creating or pushing out a new policy. Navigate to the Microsoft Endpoint Manager admin center and login with your credentials. Once logged in you will arrive at the home page.
 MEM Home
MEM Home
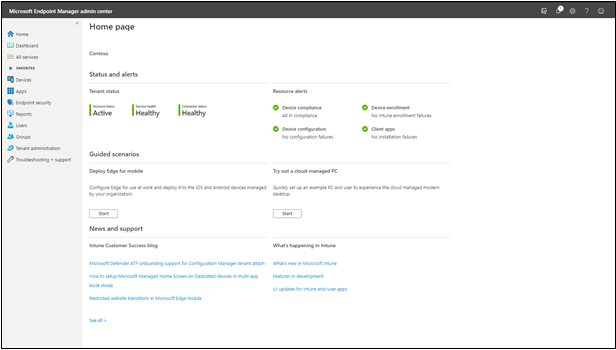
Select “Devices” and then “All devices” to make sure the device you will be applying the new ASR rule Policy has been synchronized.
 All Devices Page
All Devices Page
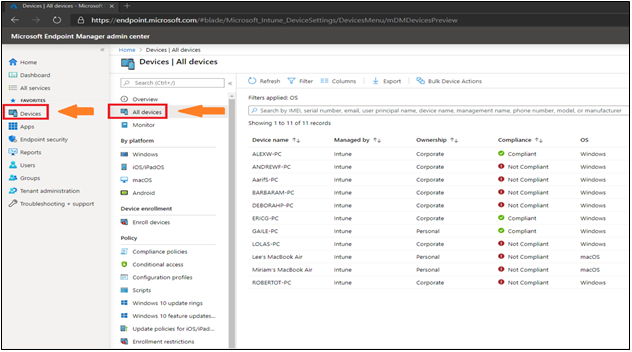
Next, we will select the “Endpoint Security” tab which is under the “Device” tab.
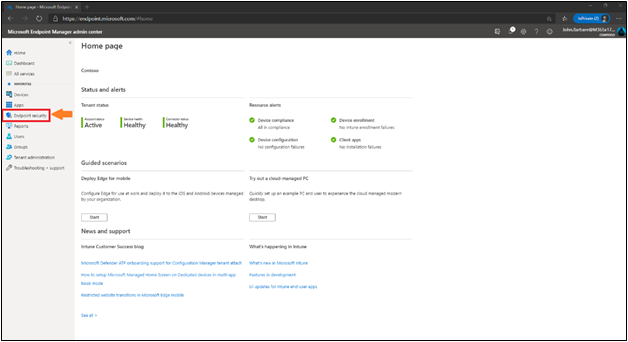 Endpoint Security Home
Endpoint Security Home
This will bring you into the main policy dashboard to create the new ASR Warn rule policy. First you will select “Attack Surface Reduction” under the “Manage” tab. Select “create policy” at the top, and then a window will open to pick the operating system “Platform” and “Profile”. For “Platform”, select Windows 10 and later and for “Profile”, select Attack Surface Reduction Rules and click “Create” at the bottom.
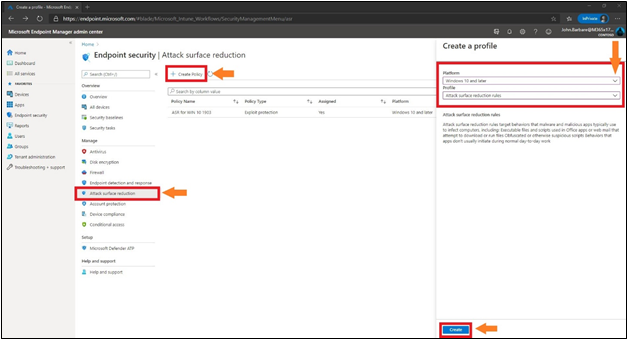 Creating the Profile/Policy
Creating the Profile/Policy
This will bring you to the creation of the profile for ASR. Name the profile in the “basics” tab and then provide a brief description and click next.
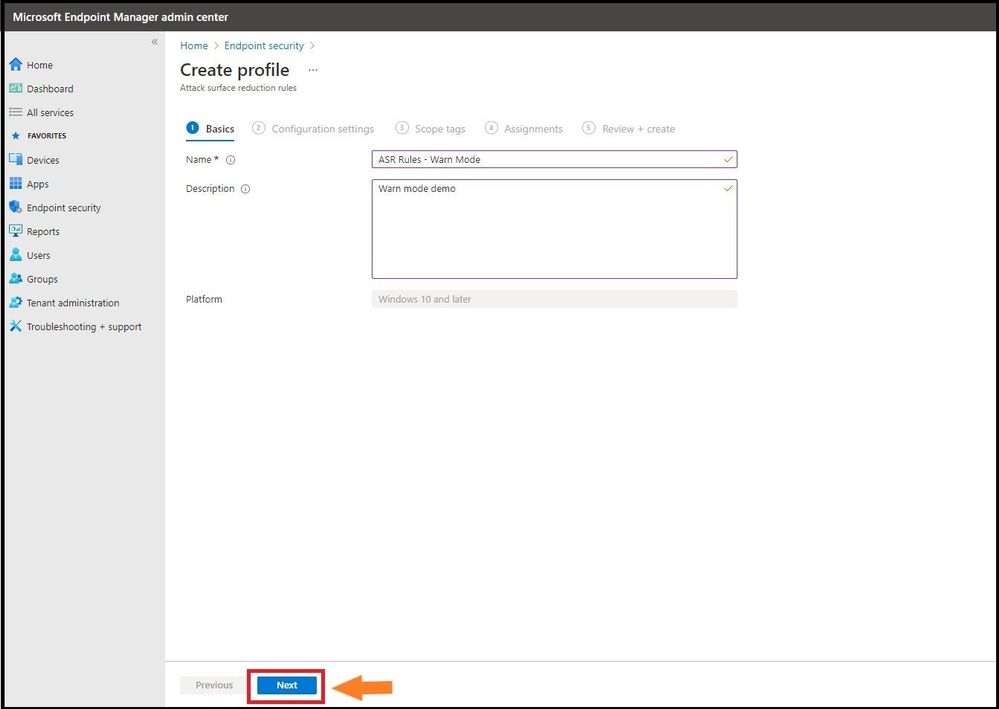 Name the Profile
Name the Profile
Configuration Settings
The next tab, “Configuration settings” is where you will configure the ASR rules. Here we have placed all the ASR rules in warn except the ones that are not allowed. From selecting the third ASR rule, one can see all the settings for the rule including the new Warn mode. You can also search for a setting in the top box underneath the settings and before the ASR rules. After placing them in the correct mode, select next.
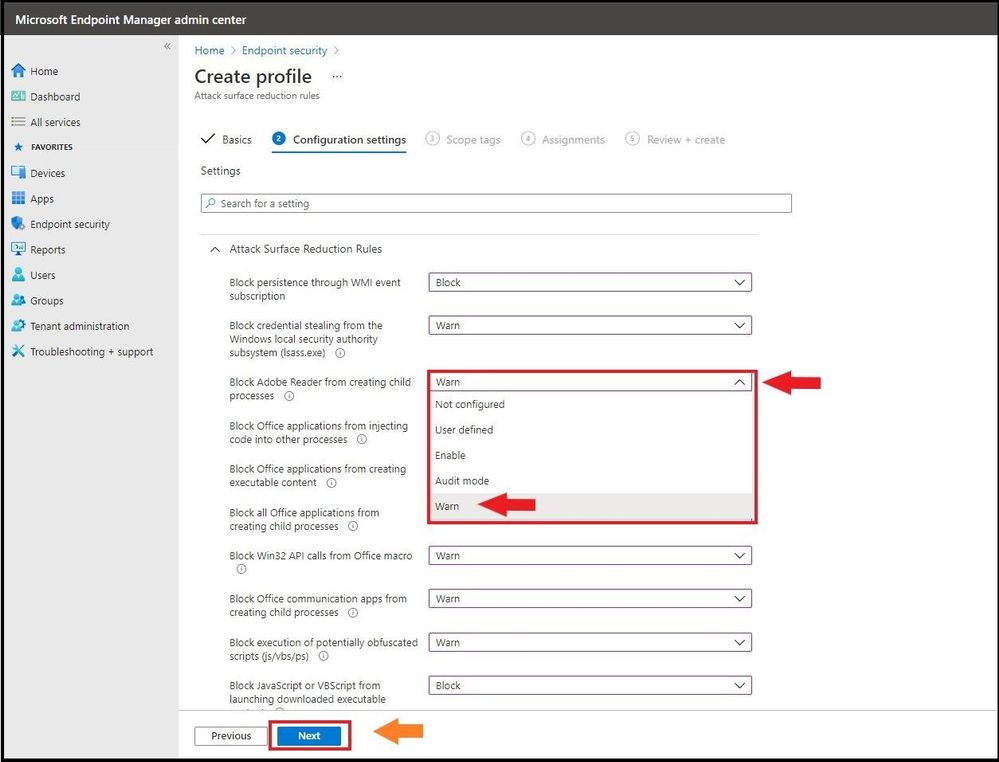 Selecting Warn Mode for the ASR Rule Policy
Selecting Warn Mode for the ASR Rule Policy
Assignments
Next, we will have the option to assign the policy to select groups, all users, all devices, or all users and devices. Here we are targeting just a select group and will pick the IT Group for this new policy. Selecting the groups to include and IT Group will target the devices inside the group and then click select and then click next. This is the equivalent to applying a policy to an organizational unit in Group Policy Objects.
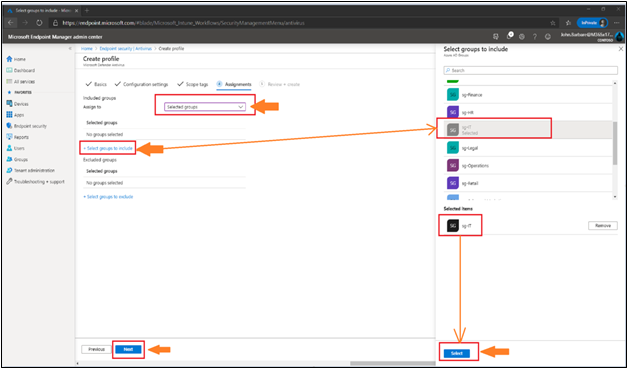 Adding Assignments
Adding Assignments
Many users ask when to use user groups and when to use device groups. The answer depends on your goal. Use device groups when you do not care who is signed in on the device, or if anyone is signed in. You want your settings to always be on the device. Use user groups when you want your settings and rules to always go with the user, whatever device they use.
Review and Create
Now let’s head over to finalizing up the newly created profile on the review and create profile page. You will see all the settings for our new Warn ASR policy, and you can confirm before selecting create. Go ahead and click on create to save the new ASR policy.
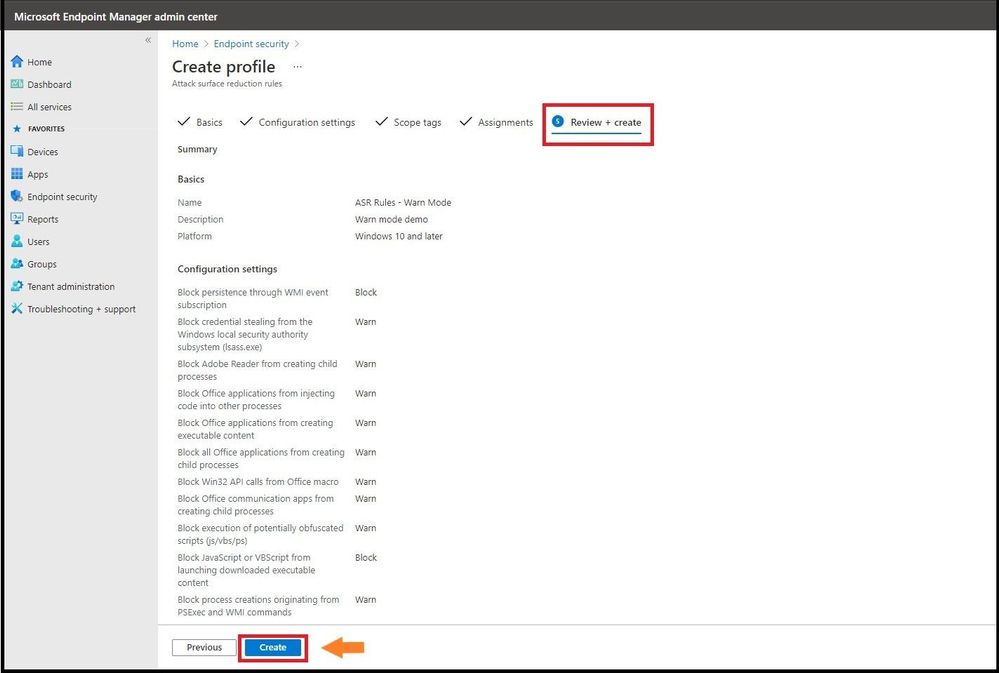 Creating the Profile
Creating the Profile
The next page will bring you to the summary page where you can view the new ASR rule policy you just created. When you select the policy name that you have created, you will be redirected to the overview page which will display more detailed information.
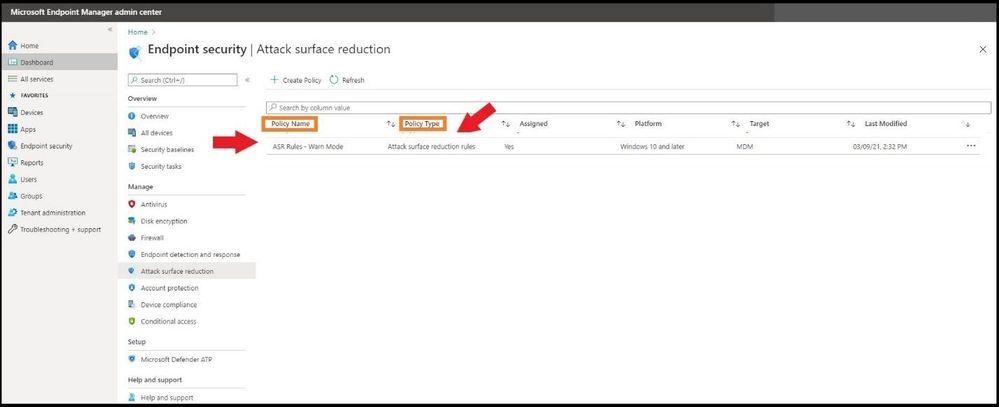 Viewing the new Profile
Viewing the new Profile
When you select a tile from this view, MEM displays additional details for that profile if they are available. In this case, it applied my new ASR Rule Warn Mode policy to my lab test machine that I targeted successfully.
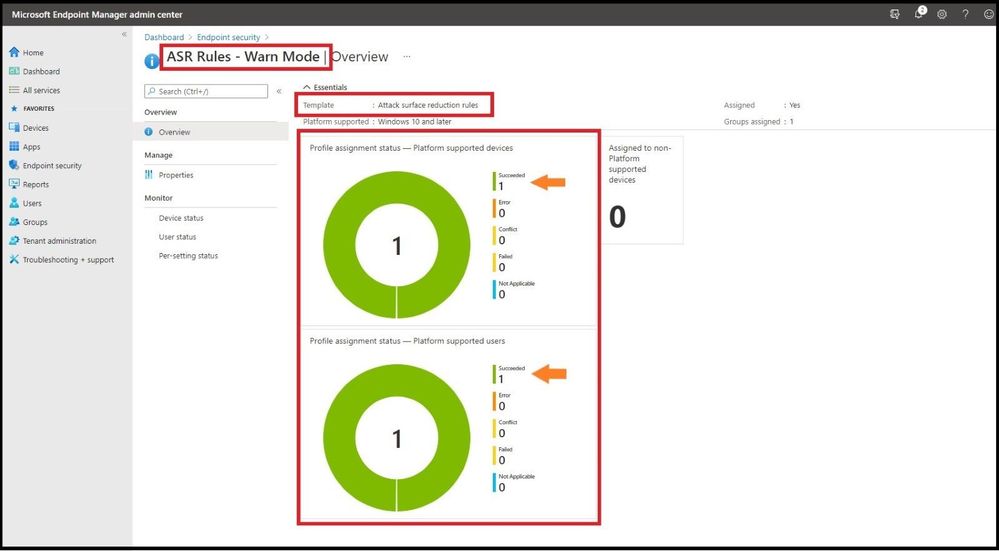 Profile Synced to Targeted Machine
Profile Synced to Targeted Machine
Testing Out the New Warn Mode
In my lab, I will test out one of the rules to show you what Warn mode looks like when triggering an ASR Rule with my newly applied ASR Warn mode policy. In the first instance I have a malicious Microsoft Word Document that will create multiple child processes. As seen below, I open the document and then bypass the security warning and click on Enable Content.
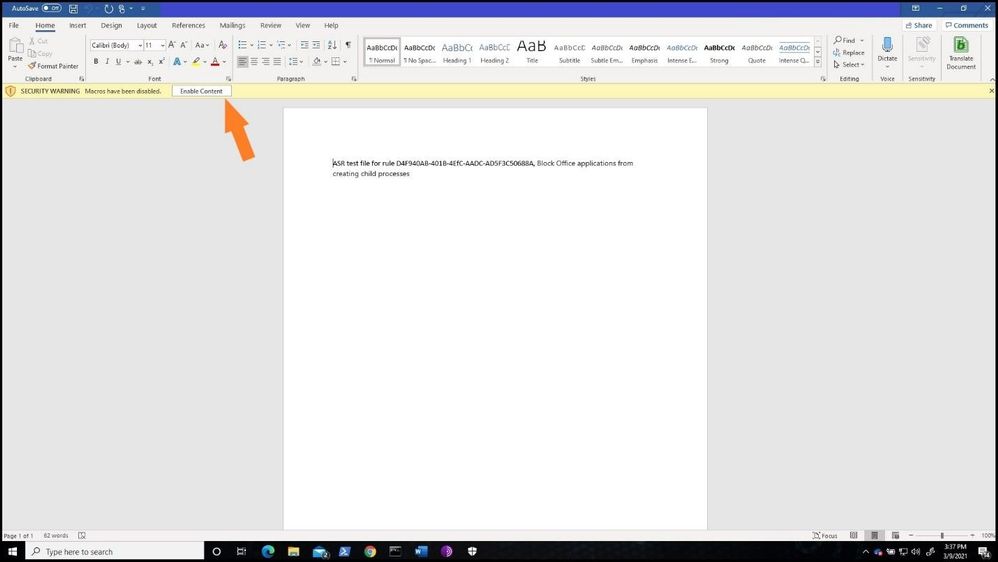 Bypassing Security Warning
Bypassing Security Warning
After bypassing the alert, a Windows Security notification is presented with a dialog box that indicates the content is blocked. The dialog box also offers me the new option to unblock the content. The dialog box below has been increased in size to show you the full warning.
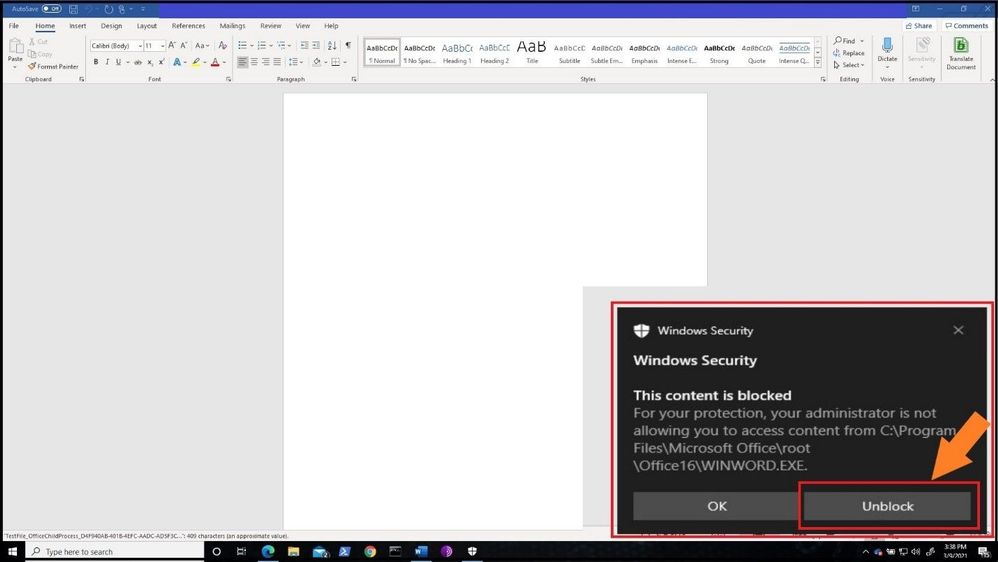 Warn Mode Notification
Warn Mode Notification
If the ASR Policy would have been in Block mode, the below dialog box would have been presented to the user.
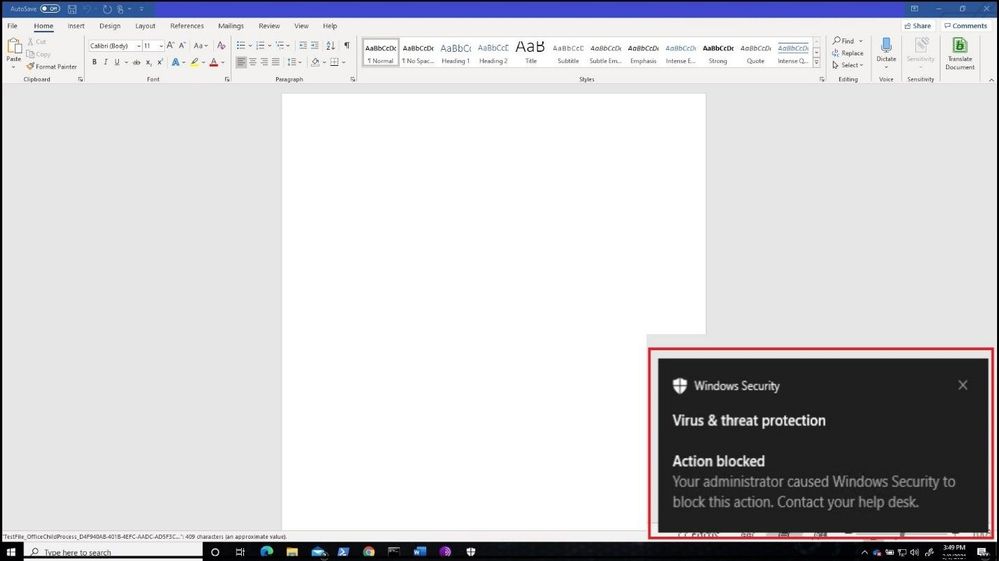 Block Mode Notification
Block Mode Notification
As one can see during testing or implementation of ASR Rules, you can see the real value of using Warn mode versus going strait to Audit and then full Block mode. This way you can let your users know you will be implementing a new security policy and they will be warned before full implementation.
Customizing the Dialog Box
If your organization wants to display a customized notification from Windows Security to display options to call, email, or redirect the user to a help portal, the instructions can be found here. I will not walk through the steps, but the screenshot below depicts what a customized notification would look like when an ASR Rule or any other Windows Security notification is displayed.
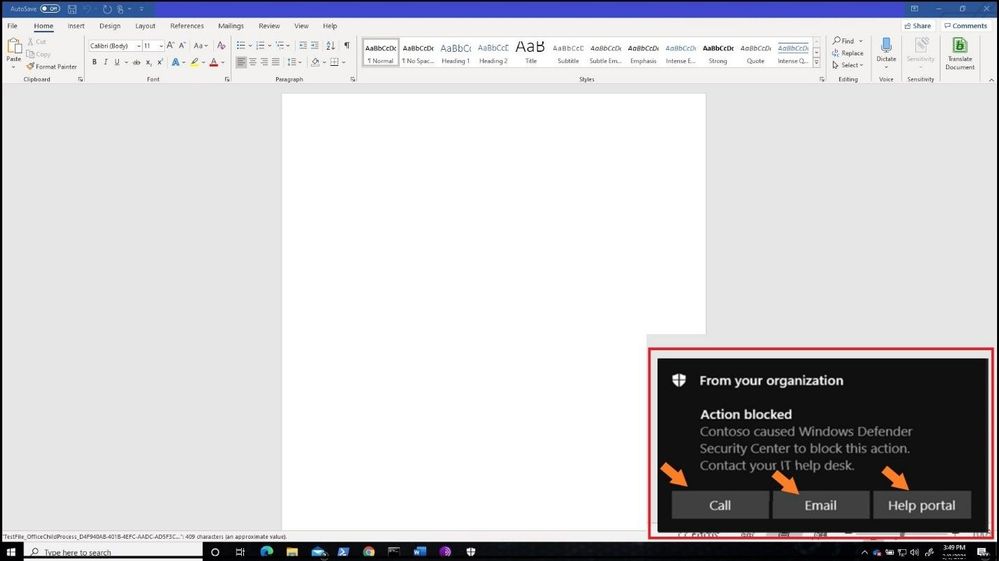 Customized Dialog Box from Defender
Customized Dialog Box from Defender
Advanced Hunting with ASR Rules in Microsoft 365 Defender
Microsoft Defender 365 provides detailed reporting for events as part of its alert investigation scenarios. You can query Microsoft Defender 365 data by using advanced hunting using KQL (Kusto Query Language). Login into Microsoft 365 Defender and select Hunting and then Advanced Hunting blade at the top. The query we will run is the following:
DeviceEvents
| where ActionType startswith ‘Asr’
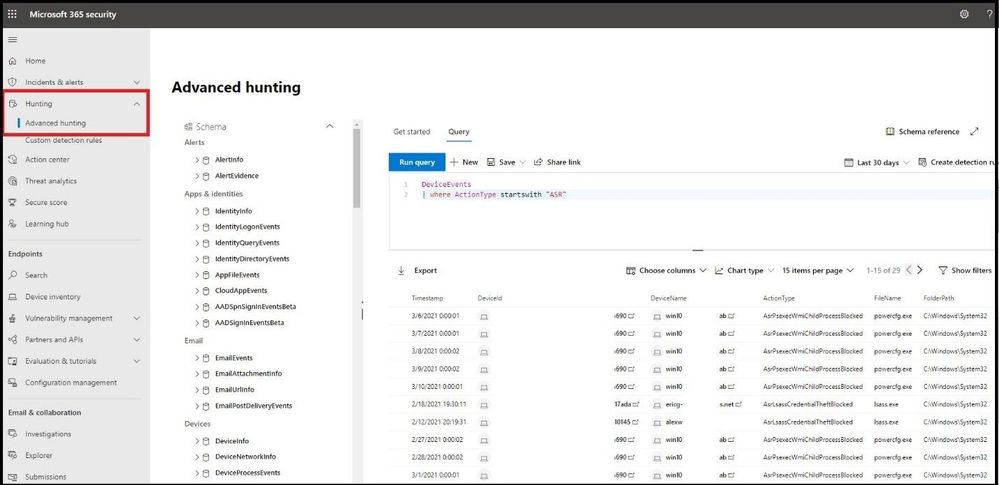 Advanced Hunting for ASR Triggers
Advanced Hunting for ASR Triggers
Monitoring the ASR Rules in Microsoft 365 Defender
In the same window, select Configuration Management blade under Endpoints and then select Go to Attack Surface Management. Select the detections tab to see a more fine-grained ASR rule detection graph in Audit and Block mode over a period time and what has been detected.
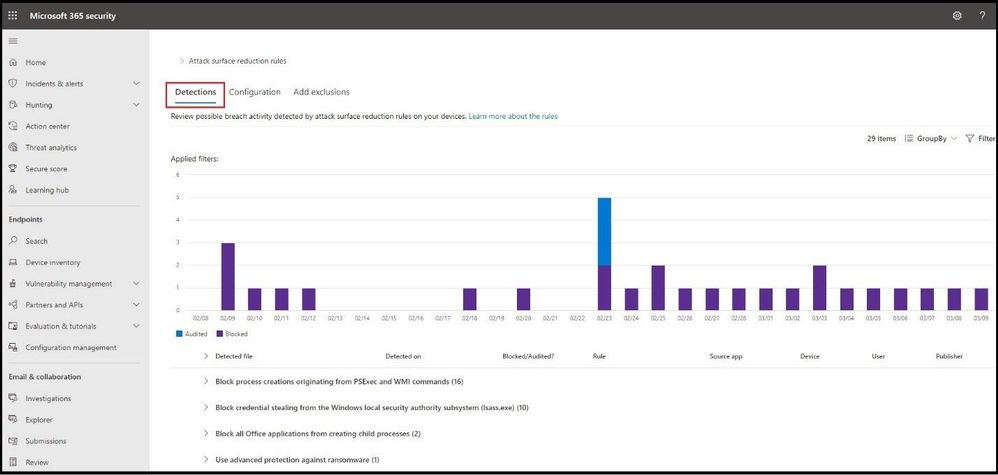 Microsoft 365 Defender ASR Rule Line Chart Triggers
Microsoft 365 Defender ASR Rule Line Chart Triggers
Conclusion
Thanks for taking the time to read this article and I hope you understand the new Warn mode for ASR rules and how you can use it in your organization during testing and pre-implementation. Using the new unified portal – Microsoft Defender 365 – to hunt for ASR detections and see a graph of what is getting triggered will further show the value for any IT Manager the value of the Microsoft 365 security stack. Hope to see you in the next blog and always protect your endpoints!
Thanks for reading and have a great Cybersecurity day!
Follow my Microsoft Security Blogs: http://aka.ms/JohnBarbare and also on LinkedIn.
by Contributed | Mar 17, 2021 | Technology
This article is contributed. See the original author and article here.
こんにちは。SQL Server サポート チームです。
今回は1つの OS 上に SQL Server x64 版 と x86 版が両方インストールされており、x64 版でフェールオーバークラスターインスタンス(以下、FCI)を構成している環境に対して、x86 版の更新プログラムを適用した場合に発生する問題について説明します。
本現象が発生すると、FCI 構成の SQL Server の役割を移動(フェールオーバー)する際に失敗しますので、発生した場合は後述する回避策を実施ください。
■概要
任意のバージョンの SQL Server x64 版と、x86 版を両方インストールしている環境に、x86 版の更新プログラムを適用した場合、FCI で使用する x64 版用の DLL ファイルが、意図せず x86 版用の DLL ファイルで置き換えられてしまう事があります。
具体的には、x86 版の更新プログラムの動作により、本来 x86 版用の「C:WindowsSysWOW64SQSRVRES.DLL」を置き換えるべきところが、誤って x64 版用の「C:WindowsSystem32sqsrvres.dll」を置き換えてしまうことによって発生します。
なお、「C:WindowsSystem32sqsrvres.dll」や「C:WindowsSysWOW64SQSRVRES.DLL」は、FCI 構成において、役割の移動時などリソースの操作や管理に使用されるライブラリです。
■影響
x64 版の SQL Server にて FCI を構成している環境において本現象が発生すると、「C:WindowsSystem32sqsrvres.dll」がx86 版用のファイルで置き換えられたノードに SQL Server の役割を移動(フェールオーバー)させようとすると、エラーとなり役割の移動(フェールオーバー)や起動が行えません。
■発生条件
以下の条件を全て満たす場合に発生します。
・SQL Server(x64)の任意のバージョンで FCI 構成をしているインスタンスが存在する。
・SQL Server(x86)のインスタンスが存在する。
※ SQL Server 2016 以降 64ビット OS で 32ビットで稼働する WOW64 のサポートが終了しているため、SQL Server 2014 以前が対象となります。
・C:WindowsSysWOW64 フォルダーに SQSRVRES.DLL が存在する。
■問題が発生する手順
・SQL Server(x86) のインスタンスに更新プログラムを適用します。
■発生状況の確認方法
「C:WindowsSystem32sqsrvres.dll」が、下記例のようなパスに格納される x86 版のファイルと同じであれば、本現象が発生していると判断できます。
同じか否かは、ファイルのプロパティを開き、[詳細] タブから [製品バージョン] を比較することが可能です。
(x86 版の sqsrvres.dll の格納先例)
C:Program Files (x86)Microsoft SQL ServerMSSQL12.SQLEXPRESSMSSQLBinnSQSRVRES.DLL
※ バージョン(12)やインスタンス ID(SQLEXPRESS)により上記パスは異なります。適宜読み替えてください。
■回避策
上記条件に該当する環境にて、x86 版 SQL Server の更新プログラムを適用する際、適用前に「C:WindowsSysWOW64」に「SQSRVRES.DLL」がある場合には、削除を行ってください。
また、更新プログラムを続けて複数インストールする場合には、インストールした更新プログラムで「C:WindowsSysWOW64SQSRVRES.DLL」にファイルを配置する可能性があるため、各インストールごとに上記ファイルの削除の手順を実施ください。
※ SQL Server の更新プログラムはサービスパックごとに累積型となっており、適用予定の更新プログラムのうち最新の更新プログラムを適用するのみで、対処可能ですので、併せてご検討ください。
既に「C:WindowsSystem32sqsrvres.dll」が置き換わってしまっている場合や、更新プログラムが多くあり上記回避策が難しい場合には、x64 版 SQL Sever のインストール フォルダーの「Binn」フォルダーより「SQSRVRES.DLL」を、「C:Windowssystem32」へ、コピーすることで対処できます。
例)
コピー元: C:Program FilesMicrosoft SQL ServerMSSQL15.MSSQLSERVERMSSQLBinn
コピー先: C:Windowssystem32
※ バージョン(15)やインスタンスID(MSSQLSERVER)により上記パスは異なります。適宜読み替えて下さい。
※ファイルが使用中で置き換えられない場合、クラスター サービスを停止する必要があります。まずは、パッシブノードから実施することをご検討ください。
以上となります。
by Contributed | Mar 17, 2021 | Technology
This article is contributed. See the original author and article here.
The 21.03 Azure Sphere OS quality update is now available for evaluation in the Retail Eval feed. The retail evaluation period provides 14 days for backwards compatibility testing. During this time, please verify that your applications and devices operate properly with this release before it is deployed broadly via the Retail feed. The Retail feed will continue to deliver OS version 21.02 until we publish 21.03 in two weeks.
This evaluation release of 21.03 includes updates to mitigate against the following CVEs. It does not include an updated SDK.
For more information on Azure Sphere OS feeds and setting up an evaluation device group, see Azure Sphere OS feeds and Set up devices for OS evaluation.
For self-help technical inquiries, please visit Microsoft Q&A or Stack Overflow. If you require technical support and have a support plan, please submit a support ticket in Microsoft Azure Support or work with your Microsoft Technical Account Manager. If you would like to purchase a support plan, please explore the Azure support plans.
![[Guest Blog] Human Touch with Microsoft Teams](https://www.drware.com/wp-content/uploads/2021/03/large-1155)
by Contributed | Mar 17, 2021 | Technology
This article is contributed. See the original author and article here.
This blog is written by Mario Trentim as a part of our Humans of IT guest blogger series. Mario has a passion for creativity, problem solving, continuous improvement and technology. He shares his best practices to adding a human touch to your remote experience on Microsoft Teams.
I delivered a webinar about team building and teamwork. To my surprise, I got a lot of comments mentioning that it is challenging to engage with colleagues virtually. People even mentioned that we are losing touch with our human side because of technology. What are your thoughts on this, especially as we’ve shifted to remote work?
As we’ve all experience remote work now and picked up a tip or two, we know virtual meetings do not have to be boring, inflexible, impersonal neither meetings have to be always “straight to the point.” It is important to know that if you feel disconnected from your coworkers, you can make a change in the way you’re conducting or participating in meetings, and ultimate, it’s on you. The technology is “just” a tool.
In this article, I bring some tricks and tricks to engage and motivate coworkers using Microsoft Teams. Please read on if this is relevant to you.
By working in a physical space, you have the chance to approach your colleagues in various ways. You meet informally at the cafeteria, you have lunch together. You can walk across the office and ask for help or chat about personal topics.
Working from home and moving to virtual-only meetings, are we sentenced to behave like machines? The answer is no.
It is on you and your team to build productive habits. To be a valuable team member, it is essential that you:
- Participate actively in the discussions;
- Provide feedback;
- Be empathetic.
As we reflect on the principles above, we can come up with simple behaviors for our daily virtual meetings and teamwork collaboration. Let’s start with virtual meetings:
1) Turn on your camera;
2) Take a few minutes to talk about personal topics;
3) Pay attention to people’s reactions and ask questions;
4) Take notes, paraphrase, and summarize.
I discovered that by changing my Microsoft Teams’ background can spark interesting warm-up conversations. I use photos from the places I visited, sometimes cartoons or movie scenes.
Warming-up questions are a cornerstone of every meeting. Ask direct questions about hobbies, family, or other appropriate topics. For example, “How is Ana doing with homeschooling?”, “Is your dog okay?”, “Did you had a chance to go for a run yesterday?”. Well, use your imagination.
It is not a chore. You have to be genuinely interested in the other person. Start doing that, and you will feel better.
Multi-tasking and half-hearted attention are obstacles to productivity and team morale. Avoid them at all costs. To get people focused, ask questions, engage people, summarize.
By using Microsoft Teams, I take full advantage of collaboration with Microsoft Whiteboard. It is an engaging and fun process.
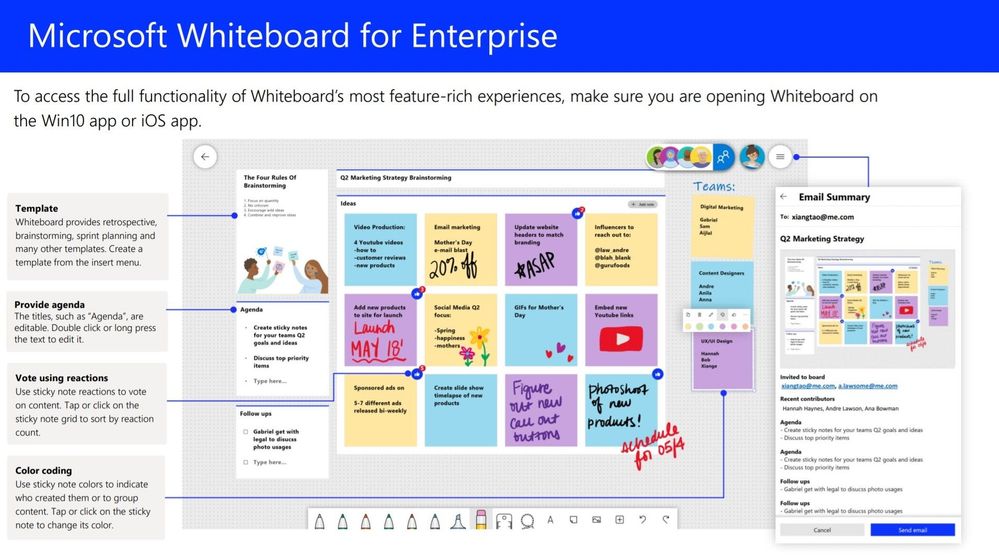
Finally, don’t forget to define action plans and owners. Assigning responsibility and following up on decisions is a final touch on team motivation. In the physical office, we could have those Post-It notes.
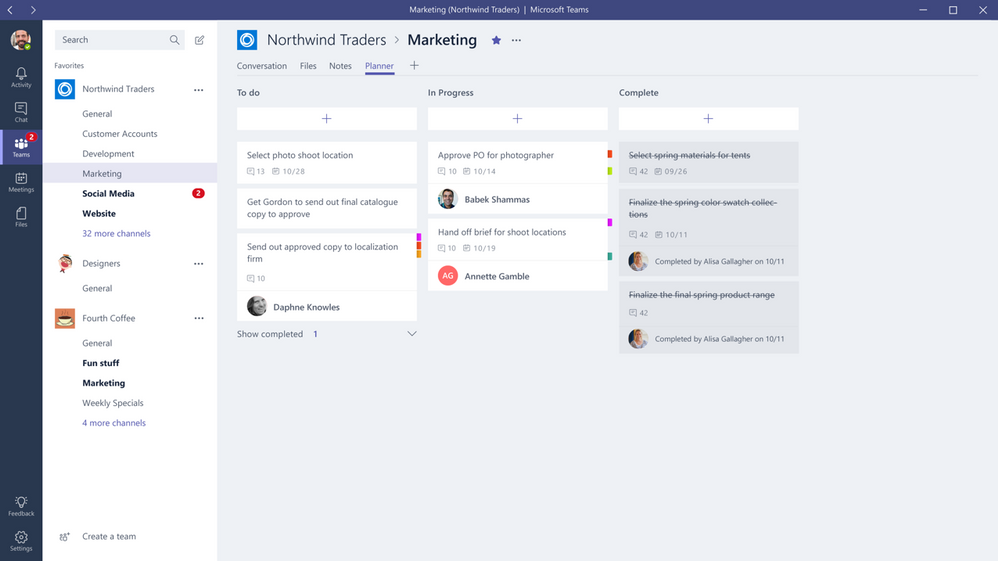
You can do the same with Microsoft Teams by using Lists or Planner. Visually tracking goals and activities is another tool for engagement and motivation.
Hope that this article was a reminder of the human touch we’re are all capable of having from our homes. As we are all now well-versed in remote work, what other suggestions do you have? Share in the comments below!
by Contributed | Mar 17, 2021 | Technology
This article is contributed. See the original author and article here.
Final Update: Wednesday, 17 March 2021 22:01 UTC
We’ve confirmed that all systems are back to normal as of 03/17 21:21 UTC. Our logs show the incident started on 03/17 20:07 UTC and that during the timeline that it took to resolve the issue 10% of active customers in the East US region experienced data access issues and missed alerts.
- Root Cause: The failure was due to stability issues in one of our backend systems.
- Incident Timeline: 03/17 20:07 UTC through 03/17 21:21 UTC
We understand that customers rely on Application Insights as a critical service and apologize for any impact this incident caused.
-chandar
by Contributed | Mar 17, 2021 | Technology
This article is contributed. See the original author and article here.
March is Women’s History Month and what a more fitting time for our team, Microsoft Azure Engineering, to have our first post go up here on the Tech Community Blog.
As a woman working in tech, I’m proud to work for a company like Microsoft, where diversity and inclusion is celebrated. This mindset also shapes the way we build our products and services. That’s where a program like Microsoft Customer Co-creation comes into play. If you haven’t heard about it, I’d like to take this opportunity to tell you more.
Microsoft Customer co-creation connects you directly with engineers within the Cloud Engineering (C+ AI) organization so you can talk to them about the products you care about. Sometimes this could mean playing an early role in product and service development before a single line of code is even written. Ultimately, our hope is your feedback will result in the creation of something you’ll really love using.
You can start by filling out your profile and telling us about yourself and what you’re interested in.
When the right opportunity comes up, our team will contact you, let you know the topic, and ask your availability to participate in a feedback session.
Your voice matters and I hope you’ll consider joining the Microsoft Customer Co-creation program and help influence the services and products you use.
by Contributed | Mar 17, 2021 | Technology
This article is contributed. See the original author and article here.
Final Update: Wednesday, 17 March 2021 20:18 UTC
We’ve confirmed that all systems are back to normal as of 03/17, 19:54 UTC. Our logs show the incident started on 03/17, 19:14 UTC and that during this timeline subset of customers in East US experienced data access issues and possible missed alerts.
- Root Cause: The failure was due to backend component that needed to be restarted.
- Incident Timeline: 40 minutes – 03/17, 19:14 UTC through 03/17, 19:54 UTC
We understand that customers rely on Application Insights as a critical service and apologize for any impact this incident caused.
-Chandar
by Contributed | Mar 17, 2021 | Technology
This article is contributed. See the original author and article here.
Hi Teams Community,
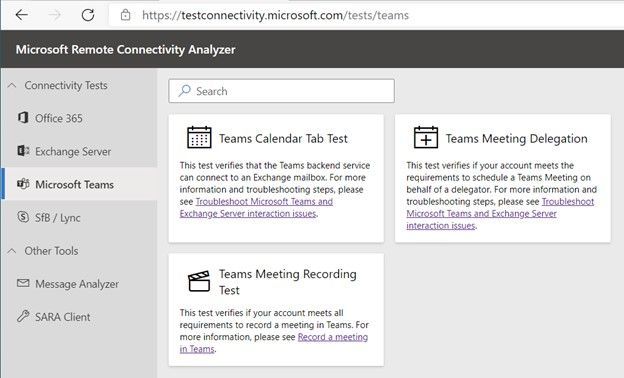
We’re back with another addition to Support Diagnostics for Microsoft Teams. @João Loureiro has written our third offering in the Microsoft Remote Connectivity Analyzer, the Meeting Recording test.
This new Diagnostic will help you troubleshoot and test if you meet requirements to record a Teams meeting. If you recently attempted to record a Teams meeting or group call and you were unable to, for example the Recording button was greyed out, you should use this diagnostic to help you troubleshoot.
To access the new diagnostic, navigate to Microsoft Remote Connectivity Analyzer, select Microsoft Teams, then click on the Teams Meeting Recording Test.
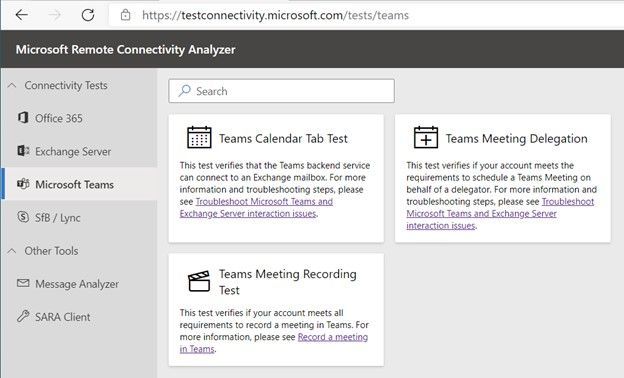
You’ll need to enter valid credentials of an affected account. Optionally you can specify the Teams Meeting URL you are planning to record. Keep in mind your end users can also perform these tests, you do not need to be an Administrator of your tenant. In some scenarios you’ll want to work with your impacted end user to run the tests and collect additional data for Microsoft Support.
At a high level the test checks a couple things:
- The user is licensed and fully provisioned for Teams
- The user is enabled for cloud meeting recording
- Recordings saved to OneDrive for Business and SharePoint or Microsoft Stream
- If recordings configured to use Stream will check if user is within valid region for streaming
- The user as permissions to record provided Teams Meeting URL
You’ll also want to go over the following documents carefully when configuring Teams cloud meeting recording
Teams cloud meeting recording
Use OneDrive for Business and SharePoint or Stream for meeting recordings
Record a meeting in Teams
Please give the new diagnostic a try if you’re having trouble with Teams Meetings Recording and let us know if it helped?
Thanks!
Microsoft Teams Support
by Contributed | Mar 17, 2021 | Technology
This article is contributed. See the original author and article here.
We have a guest post today from @thibaudcolas from our Services Team.
Disclaimer: With the introduction of cross platform co-auth support announced recently at Ignite (Announcing co-authoring on Microsoft Information Protection-encrypted documents and labeling updates), this capability will change in the future as the metadata location used to store the sensitivity label will change and not be readable by this approach, once co-auth support is enabled in your tenant (which is not the case by default).
The purpose of this process is to allow the re-classification of existing documents classified with a deprecated sensitivity label to a new one. This process mainly aims to reclassify files which have been manually classified and which are not reachable by the AIP scanner. Files not matching these criteria can also be addressed, but other solutions exist (e.g. MCAS).
A deprecated label is a label which cannot be used anymore for technical reasons. An example could be when a label used to classify documents becomes a top label (sub-labels have been introduced). Then, as documents cannot be classified with a top label, these legacy items may fail some mechanisms (e.g. attachment’s inheritance to mail or sensitivity labels as a condition with M365 DLP).
Notes:
- When possible, renaming the display name of a label should be preferred as it does not imply any significant configuration changes while still allowing changing the user interface.
- Keep in mind, Microsoft recommends implementing in production a classification taxonomy the most tailored to organizations’ needs from Day 1, avoiding having to deal with such situations.
Context:
Contoso had the following classification taxonomy:
General
|
Confidential
|
Highly Confidential
|
Contoso used to have a label “Confidential” which was set as a default label for all new documents. Therefore, a significant amount of newly created and edited documents has been classified as “Confidential”.
Then, the classification has been updated by the introduction of two sub-labels:
General
|
Confidential
|
Highly Confidential
|
All Employees
|
All Employees
|
User-Defined permissions
|
User-Defined permissions
|
To ensure “Confidential” documents can still be protected by M365 DLP or benefit the attachment’s inheritance to mail, they must be reclassified to “Confidential – All Employees”.
Requirements:
- Compliance admin role
- PowerShell module to access SCC
- Access to Microsoft Compliance portal
- Information in the matrix below
- AIP UL client
- This process is not supported with Office built-in labeling feature (Windows, Mac, Mobile devices, and Web).
“Confidential” label custom property*
|
MSIP_Label_<Confidential_ImmutableID>_Name
|
“Confidential” label custom property value*
|
Confidential
|
“Confidential-new” ImmutableID**
|
<Confidential-new_ImmutableID>
|
Sub-label 1 to migrate
|
All Employees
|
Sub-label 2 to migrate
|
User-Defined permissions
|
* : Open a “Confidential” document > click File > Info > Properties > Advanced Properties > Custom
** : Use “Get-Label -Identity “Confidential-new” | fl”
Note: This process relies on the utilization of the advanced setting “LabelByCustomProperties”. This one only works with properties it “does not know”, which includes metadata applied by the client. As long as the deprecated label will exist in the tenant, the advanced setting will not work as it “knows” its associated custom properties. For this reason, the deprecated label must be deleted.
Solution:
We will recreate the “Confidential” label and sub-labels structure with a new label which will looks identical for end-users.
Note: This process should be transparent for end-users if no one opens a new Office app during the process. However if it happens, the user will receive the policy as it is at this moment. Once the process completed, sensitivity labels will look identical for end-users.
- In SCC portal, change the display name of label “Confidential” to “Confidential.”
- This is to make the display name “Confidential” available again and minimizing impact on user experience.
- In SCC portal, create a new label “Confidential-new” with “Confidential” as Display name.
- All future mentions of labels in this process refers to Name and not DisplayName.
- In SCC portal, adjust the order of “Confidential-new” label to be located between “General” and “Confidential” labels.
- Click of the “…” button of the label “Confidential-new” and “move up or down”).
- In SCC portal, select the appropriate label policy(ies) and add the new label “Confidential” for publication.
- This is required to migrate sub-labels which are already published.
- Change the parent label of sub-labels “All Employees” and “User-Defined Permissions” from “Confidential” to “Confidential-new”.
- In a PowerShell session, connect to SCC and run below commands:
- Set-Label -Identity “All Employees” -ParentId $null
- Set-Label -Identity “All Employees” -ParentId <Confidential-new_ImmutableID>
- Set-Label -Identity “User-Defined Permissions” -ParentId $null
- Set-Label -Identity “User-Defined Permissions” -ParentId <Confidential-new_ImmutableID>
- In SCC portal, unpublish label “Confidential” from all policies.
- In SCC portal, delete the label “Confidential”.
- Before moving forward, ensure with below PowerShell cmd the label has correctly been deleted. It can take few minutes for a label to disappear
- Set the advanced setting “LabelByCustomProperties” to automatically reclassified “Confidential” documents as “Confidential-new / All Employees” when opened.
- Set-Label -Identity “All Employees” -AdvancedSettings @{LabelByCustomProperties=“reclassificationrule,MSIP_Label_<Confidential_ImmutableID>_Name,Confidential”}
- Verify the advanced setting has correctly been set
- (Get-Label -Identity “All Employees”).Settings
- The setting “labelbycustomproperties” should be listed.
- Try to consume a “Confidential” document in new Word session
- The label should be automatically updated to “Confidential-new / All Employees”, and it will work the same way for any documents classified “Confidential” and which be consumed with AIP UL client in future.
- If ever it does not work, it may be the client did not download the last policy version. In that case, try following options:
- Restart Word.
- Reset AIP UL client settings (Sensitivity > Help and Feedback > Reset Settings).
Note: This process should be transparent for end-users if no one opens a new Office app during the process. However if it happens, the user will receive the policy as it is at this moment. Once the process completed, sensitivity labels will look identical for end-users.
Thanks for reading and we hope you find this useful! If you haven’t already, don’t forget to check out our resources available on the Tech Community.
Thanks!
@Robin_Baldwin on behalf of the MIP and Compliance CXE team
by Contributed | Mar 17, 2021 | Technology
This article is contributed. See the original author and article here.
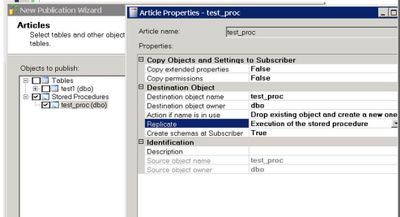
With Transactional Replication you can replicate execution of the Stored Procedure like this:
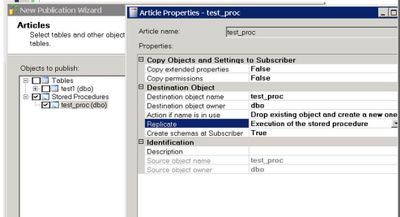
This has several advantages as discussed in this article:
https://docs.microsoft.com/en-us/sql/relational-databases/replication/transactional/publishing-stored-procedure-execution-in-transactional-replication?view=sql-server-ver15
When you enable CDC at the Database level, replication of the stored procedure execution will NOT work. This is By Design. CDC does not support tracking at stored procedure execution level, which means individual rows logged by stored proc execution need to be flagged with REPLICATE bit, which makes it impossible for transactional replication to replicate stored proc execution. As a result, ‘stored proc execution’ will work only when transactional replication is enabled and CDC is disabled.
MEM Home
All Devices Page
Endpoint Security Home
Creating the Profile/Policy
Name the Profile
Selecting Warn Mode for the ASR Rule Policy
Adding Assignments
Creating the Profile
Viewing the new Profile
Profile Synced to Targeted Machine
Bypassing Security Warning
Warn Mode Notification
Block Mode Notification
Customized Dialog Box from Defender
Advanced Hunting for ASR Triggers
Microsoft 365 Defender ASR Rule Line Chart Triggers


Recent Comments