Get it now in our marketplace
|
|---|
 |
Acalvio ShadowPlex: ShadowPlex Cyber Deception from Acalvio provides early detection of advanced cybersecurity threats with precision and speed. The AI-driven solution detects deception across on-premises and cloud workloads.
|
 |
Alpine Linux 3.16: Ntegral has packaged Alpine Linux 3.16, a lightweight security-oriented distribution based on musl, libc, BusyBox, and OpenRC, to enable you to enjoy the principles of simple, small, and secure.
|
 |
BizRep SaaS: SETRIO’s BizRep delivers a mobile productivity and CRM solution for sales representatives in the medical and pharmaceutical industries. This Azure-based offering provides a mobile app, a web-based interface for managers, and easy integration with ERP systems.
|
 |
BlackArch Essentials: Ntegral provides this prepackaged virtual machine that includes BlackArch Linux, an Arch-based distribution intended for advanced penetration testing, security auditing, and other information security tasks.
|
 |
Circle Linux 8.6: This prepackaged virtual machine from Ntegral contains Circle Linux 8.6, a CentOS alternative designed for enterprise cloud environments with workloads including Node.js, web apps, and database systems.
|
 |
Cloudanix Security – CSPM, CIEM, and CWPP: Cloudanix gives you a single dashboard to unify cloud infrastructure security by using its cloud security posture management (CSPM), CIEM (cloud infrastructure entitlement management), and CWPP (cloud workload protection platform).
|
 |
CodeIgniter 4 Framework: Get this preconfigured virtual machine (VM) from tunnelbiz Studio for a simple, elegant toolkit for creating full-featured web applications using PHP and CodeIgniter 4. This VM includes Rocky Linux 9 with Nginx and PHP 7.
|
 |
Data Rooms Next-generation Conversational Data Rooms: Dropvault Data Rooms provide secure and encrypted conversation rooms for collaboration and management of sensitive information, backed by custom storage on Microsoft Azure or on-premises
|
 |
DataOps for Snowflake: DataOps.live delivers a single platform to build, test, and deploy apps and products for all your Snowflake DataOps needs. DataOps provides end-to-end orchestration for a heterogenous data environment.
|
 |
Debian 11 Server: Cloud Infrastructure Services has configured this virtual machine with Debian 11, codenamed bullseye. Debian is a popular Linux distribution used as a server for development, cluster systems, storage servers, and more.
|
 |
Demand Forecasting: Co.dx’s Growth Maximizer app uses no-code AutoML powered by Azure machine learning and Azure Databricks to deliver self-service demand forecasting of SKUs at scale while also providing transparency into forecasts.
|
 |
Django Framework: This virtual machine from tunnelbiz Studio provides the Django web framework for Python on Rocky Linux. Django encourages rapid development and clean, pragmatic design while helping developers avoid common security mistakes.
|
 |
Driving License Extractor: Nexus Frontier’s image contains Driving License Extractor to run on Azure Virtual Machine for a convenient, AI-powered solution that extracts data from UK driving licenses in real time.
|
 |
Drupal: Data Science Dojo has configured this virtual machine with Drupal on Ubuntu 20.04 LTS. Drupal is an open-source CMS designed to help you build versatile, structured content and dynamic web experiences.
|
 |
External User Manager: Solutions2Share’s External User Manager helps you better control data and communications in Microsoft Teams through approval workflows and monitoring for guest and external access to your environment.
|
 |
IP Location API – City, Country, Currency, and Maps: Fastah IP Location is a REST API that lets you easily map IP addresses to useful metadata including country, city, approximate geo-location coordinates, currency, and time zone.
|
 |
Juniper Paragon Automation as a Service: Marconi Wireless’s Paragon Automation portfolio of cloud-native software apps integrates with Azure Active Directory and automates your network infrastructure planning, monitoring, provisioning, and optimization.
|
 |
KubeLift Solo: KubeLift Solo from Polverio delivers a development and test environment on a single-node Kubernetes cluster in an Azure-optimized virtual machine (VM). Ready out of the box, the VM lets you take advantage of Azure’s ability to scale.
|
 |
Navy Linux 8.6: Ntegral has configured and certified this Azure virtual machine image containing Navy Linux 8.6. Navy Linux is an open-source alternative to CentOs that is compatible with Red Hat Enterprise Linux.
|
 |
Parrot OS Essentials: Parrot OS Essentials is a virtual machine image (VMI) packaged by Ntegral. This command-line only VMI includes Parrot OS Linux, a Debian-like distribution designed for penetration testing and security auditing.
|
 |
PostgreSQL 14 on Alpine Linux 3.16: Ntegral has configured this virtual machine image containing PostgreSQL 14 on Alpine Linux 3.16. PostgreSQL is a free, open-source relational database system built for enterprise-class workloads.
|
 |
QuestDB: Data Science Dojo has packaged this virtual machine image containing QuestDB on Ubuntu 20.04 LTS. Built specifically for time-series data, QuestDB is an open-source, SQL database that supports parallelized vectorized execution.
|
 |
Redis 7.0.5 on Alpine Linux 3.16: Ntegral has configured this virtual machine image containing Redis 7.05 on Alpine Linux 3.16. A NoSQL database, Redis provides a flexible, in-memory data structure store that facilitates the storage of large amounts of data.
|
 |
SecureBox: EcoLink Technology’s SecureBox app for Microsoft Teams lets you quickly secure plaintext information by using AES encryption, decrypting the information only when opened.
|
 |
SFTP – OpenSSH FTP on SUSE Linux Enterprise Server 12 Minimal: Art Group has configured this image containing OpenSSH FTP on SUSE Linux Enterprise Server 12. OpenSSH FTP is a secure FTP server that provides high levels of access control and encrypted file transmission.
|
 |
SFTP – OpenSSH FTP on SUSE Linux Enterprise Server 15 Minimal: Art Group has configured this image containing OpenSSH FTP on SUSE Linux Enterprise Server 15. OpenSSH FTP is a secure FTP server that provides high levels of access control and encrypted file transmission.
|
 |
SFTP – OpenSSH FTP Server on CentOS Linux 7.9 Minimal: Art Group has configured this image containing OpenSSH FTP on CentOS 7.9 Linux. OpenSSH FTP is a secure FTP server that provides high levels of access control and encrypted file transmission.
|
 |
SFTP – OpenSSH FTP Server on CentOS Stream Linux 8 Minimal: Art Group has configured this image containing OpenSSH FTP on CentOS Stream 8 Linux. OpenSSH FTP is a secure FTP server that provides high levels of access control and encrypted file transmission.
|
 |
SFTP – OpenSSH FTP Server on Debian 10 Minimal: Art Group has configured this image containing OpenSSH FTP on Debian 10 Linux. OpenSSH FTP is a secure FTP server that provides high levels of access control and encrypted file transmission.
|
 |
SFTP – OpenSSH FTP Server on Red Hat Enterprise Linux 8.6 Minimal: Art Group has configured this image containing OpenSSH FTP on Red Hat Enterprise Linux 8.6. OpenSSH FTP is a secure FTP server that provides high levels of access control and encrypted file transmission.
|
 |
SFTP – OpenSSH FTP Server on Ubuntu 18.04 LTS Minimal: Art Group has configured this image containing OpenSSH FTP on Ubuntu 18.04 LTS. OpenSSH FTP is a secure FTP server that provides high levels of access control and encrypted file transmission.
|
 |
SFTP – OpenSSH FTP Server on Ubuntu 20.04 LTS Minimal: Art Group has configured this image containing OpenSSH FTP on Ubuntu 20.04 LTS. OpenSSH FTP is a secure FTP server that provides high levels of access control and encrypted file transmission.
|
 |
SFTP – OpenSSH FTP Server on Ubuntu 22.04 LTS Minimal: Art Group has configured this image containing OpenSSH FTP on Ubuntu 22.04 LTS. OpenSSH FTP is a secure FTP server that provides high levels of access control and encrypted file transmission.
|
 |
SFTPGo – SFTP, HTTP/S, FTP/S to Azure Blob Storage: Built by the SFTPGo project, this virtual machine includes SFTPGo configured to use SQLite. SFTPGo supports SFTP and FTP/S services, including web file browsing and file sharing, backed by Azure Blob Storage.
|
 |
TPP Validation & Confirmation (PSD2): Mobilitas Sweden AB offers an Azure-based service to help account servicing payment service providers manage their PSD2 regulatory processes in an automated, safe, and cost-effective manner.
|
 |
Ubuntu 22.04 LTS – CIS Benchmark Level 1: Center for Internet Security (CIS) has configured this image of Ubuntu 22.04 LTS to meet CIS’s Level 1 benchmark, a vendor-agnostic, consensus-based configuration designed to comply with numerous cybersecurity frameworks.
|
 |
WireGuard Server on CentOS Stream Linux 8 Minimal: Configured by Art Group, this virtual machine image contains WireGuard on CentOS Stream 8 Linux. WireGuard is a compact, easy-to-configure, fast, and secure VPN server.
|
 |
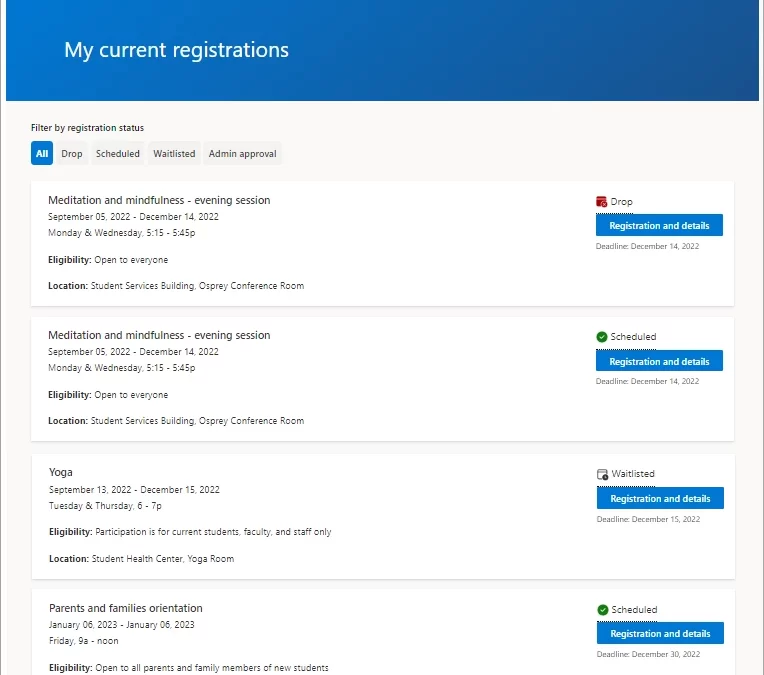
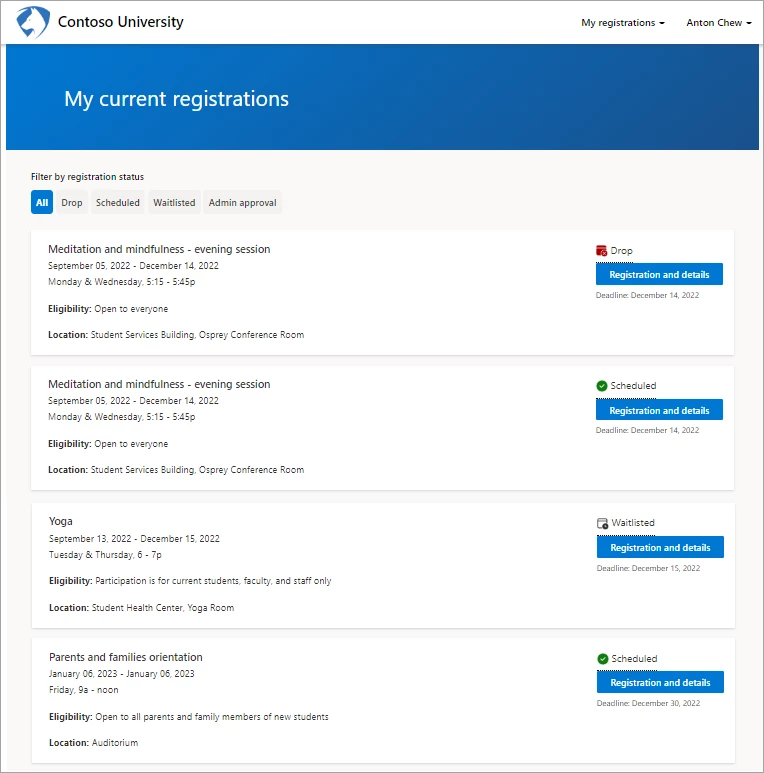
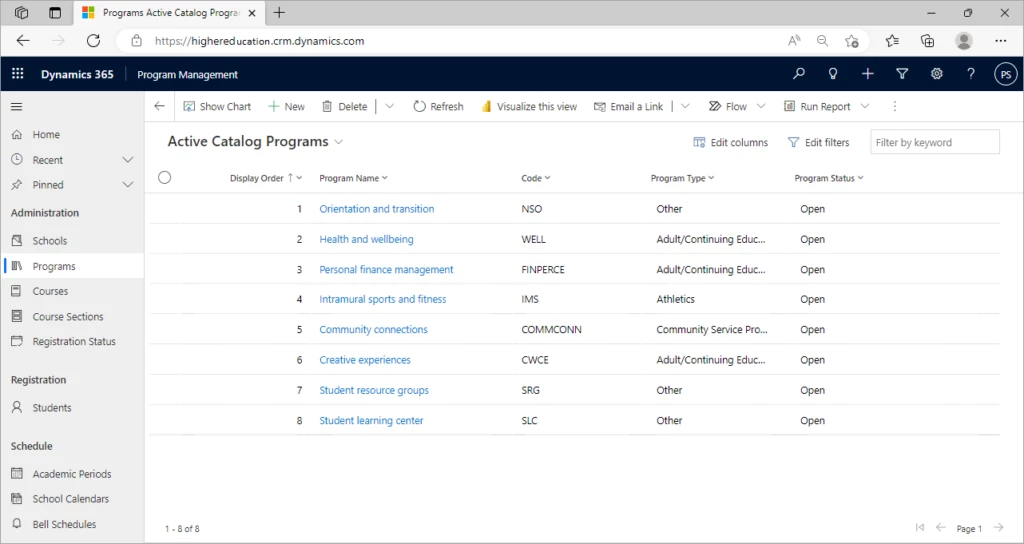
ZenCRM Business Line – Sales Edition: InterZen’s ZenCRM Sales Edition provides an Azure-based, sales-focused CRM solution that uses the lead-to-cash process. ZenCRM Sales Edition lets you manage contents, generate business proposals from templates, and more.
|
Go further with workshops, proofs of concept, and implementations
|
|---|
 |
.NET App Service: 8-Week Implementation: Groove Technology will identify your .NET development challenges, create a functional specification document for integration of Azure services, and develop the solution to meet your desired outcomes.
|
 |
AI Workshop: 3-Day Proof of Concept: Coppei Partners will work with your functional and technical leaders to understand and define high-impact AI use cases specific to your business, then build a targeted proof of concept by using Azure Cognitive Services and Azure ML Studio.
|
 |
App and Database Modernization: 3-Day Workshop: In this workshop, Plain Concepts will help you identify the resources required to migrate and modernize your different workloads to Microsoft Azure. This workshop aligns to the Microsoft Cloud Adoption Framework for Azure.
|
 |
App Modernization Kick-Start and Proof of Concept: Innofactor Finland will review your current processes and identify the value of modernizing your business apps by using low-code development and Microsoft Azure services. This offer includes a cost estimate for Azure consumption.
|
 |
Aztek App and DB: 4-Week Migration: Aztek, part of R-Net D B LTD., will enable you to enjoy faster processing, simpler management, and flexible configurations for your apps and database migrations to Microsoft Azure. You’ll also get post-migration training and optimization.
|
 |
Azure Landing Zone: 1-Week Implementation: Click2Cloud will implement a Microsoft Azure landing zone aligned with the Microsoft Azure Cloud Adoption Framework. The solution will utilize the latest Microsoft best practices to align with your business requirements.
|
 |
Azure MLOps Prepackaged Pipeline: 4-Week Implementation: Orange Business Services will deliver a solution to retrain and deploy your machine learning models while guaranteeing test coverage, continuous integration, and model monitoring by using Azure machine learning operations (MLOps).
|
 |
Azure Red Hat OpenShift App Dev Sprint: 1-Week Implementation: Red Hat will help you accelerate your app migration and modernization to Microsoft Azure Red Hat OpenShift, a turnkey Kubernetes solution that provides high availability container platform as a service to improve your DevOps experience.
|
 |
Backup as a Service with Microsoft Azure and Cohesity: 5-Day Workshop: eGroup will focus on hybrid cloud governance and security, including a design for data protection built on Microsoft Azure Backup and Cohesity. You’ll also receive a technical analysis and a total cost of ownership report.
|
 |
Cloud Database Management Services: 3-Week Implementation: NCS will implement its Cloud Database as a Service portfolio to support your organization through monitoring, maintenance, performance management, backups, and more for databases hosted on Microsoft Azure.
|
 |
CloudRiches EDA on Azure: 1-Month Proof of Concept: Available only in Chinese, this proof of concept from CloudRiches will show you how migrating EDA tools to Microsoft Azure will benefit your IC businesses by providing the flexibility to scale resources up or down.
|
 |
DevOps: U-BTech offers consulting and adoption advice for DevOps processes on Microsoft Azure, including expert advice to manage, optimize, and secure your deployments for improved go-to market capabilities.
|
 |
DevSecOps Accelerator: 2-Week Implementation: Architech will implement its DevSecOps Accelerator to help you go to market faster with end-to-end capabilities on Microsoft Azure and GitHub, including CI/CD pipelines, security as code, integration pipelines, and more.
|
 |
Integrated Security Monitoring Service for Microsoft 365 E3 / E5: Available only in Japanese, this monitoring service from PSC Security uses Microsoft Sentinel and Microsoft 365 E3 or E5 for security information and event management. This offer is available as an initial proof of concept.
|
 |
Landing Zone Accelerator: 2-Week Implementation: Architech Solutions will implement its Landing Zone Accelerator on Microsoft Azure to enable your business to scale infrastructure quickly with SOC2 compliance for demanding markets.
|
 |
Nutanix Clusters (NC2) on Azure: 1-Month Proof of Concept: eGroup will simplify your adoption of Nutanix Clusters (NC2) on Microsoft Azure, speeding your migration to hybrid, multi-cloud environments on the public cloud and enhancing your business resilience.
|
 |
QuickBooks to Azure Migration: 5-Day Implementation: EFC Data will enable your business to grow faster by migrating your QuickBooks implementation to a well-architected solution built on Microsoft Azure for increased reliability, security, and backup protection.
|
 |
SOC as a Service: Implementation and Operation: Available in Polish from Chmura Krajowa, this security operations center (SOC) as a service is based on Microsoft Azure Sentinel and includes around-the-clock monitoring and support.
|
 |
Sustainability: 3-Week Proof of Concept: Available in Spanish, Rico’s Sustainability Dashboard highlights sustainability scores for your company. This proof of concept also includes a Sustainability Roadmap, breaking down how to achieve outcomes by utilizing Microsoft Azure.
|
 |
Windows 365: 2-Day Proof of Concept: ProServeIT will guide you through configuring and integrating Windows 365 into your Microsoft Azure environment, including deployment and management by using Microsoft Endpoint Manager.
|
Contact our partners
|
|---|
AMG – Adoption 365
|
ARVI – Aviation Weather Service
|
Ataccama ONE Data Quality
|
Ataccama ONE Master Data Management (MDM)
|
Azure Cloud: 2-Week Assessment + Migration
|
Azure Full-Stack Delivery for Business Innovation: Migration
|
Azure IoT Migration: Assessment
|
Azure Migration & Modernization: Briefing
|
Bank Integration
|
Bodhee Dynamic Production Scheduler
|
Candor Protect – Artificial Intelligence (AI) Penetration Testing as a Service
|
ClearVisibility
|
Cloud Managed Backup of Microsoft 365
|
CRAG NaaS
|
Cyber Defense Center (CDC) Security Operations Center
|
Data Platform in 30 Days
|
DeviceOn ePaper
|
Digital Customer Lifecycle Manager
|
ERP for Manufacturing
|
FranklyAI
|
Global Buyer/Supplier List API
|
Global Buyer/Supplier Profile API
|
Hybrid Cloud Observability
|
Identity Management Solution
|
Infor SunSystems Connector for Microsoft Power BI
|
Integrate ADP with Active Directory: 1-Week Implementation
|
Landed Cost Calculator API
|
LSP Services
|
Managed XDR Service
|
Microsoft Cloud for Financial Services: 1-Week Briefing
|
NetDocuments Connector for DocuSign SaaS Solution
|
Networking for Azure: 1-Day Assessment
|
Payara Cloud
|
PKI as a Service
|
Portfolio Carbon Navigator
|
Postgres Pro Standard Database 15 (Container)
|
SCIM and HR Onboarding Bridge for Azure Active Directory
|
SIOS DataKeeper
|
SIOS LifeKeeper
|
SUSE Linux Enterprise Server 15 SP4 for SAP – Hardened BYOS
|
Taxi Activity Automation
|
Tetrate Service Bridge (TSB)
|
The Omni-Channel Consumer Skincare Insight Solution
|
Transportame
|
Trend Micro Deep Security for Microsoft Sentinel
|
Trend Micro TippingPoint for Microsoft Sentinel
|
Trend Micro Vision One for Microsoft Sentinel
|
Volo Azure Landing Zone
|
Well-Architected Cloud Environment: 2-Week Trial
|
Zelly Web Hosting
|



Recent Comments