by Contributed | Mar 12, 2021 | Technology
This article is contributed. See the original author and article here.
By: @Caroline_Lee
Welcome to the Real Time Controls blog series! This series will focus on the Real Time Controls pillar in Microsoft Cloud App Security (MCAS) and how to work through some unique use cases, workarounds and pointers when configuring your policies.
For those of you who are unfamiliar with Real Time Controls in Cloud App Security, check out our documentation located here: Deploy Cloud App Security Conditional Access App Control for Azure AD apps | Microsoft Docs. In short, MCAS uses a reverse proxy to monitor user sessions and apply controls in real time (i.e. Block downloads to an unmanaged device). Keep in mind, you can only leverage this feature set for the web versions of applications, not thick clients (one of the most frequently asked questions). If you’re interested in a blog dedicated to how to protect that scenario, please like this post!
For the first blog, I wanted to share a use case that has been popping up over the last couple of months.
Use Case: Block downloads to unmanaged devices for ExchangeOnline.
Current Behavior: When a user accesses the Outlook Web Application (OWA) and tries to preview a PDF attachment, they are blocked by MCAS. This is because in some browsers the PDF needs to be downloaded on the backend in order to preview it.
Technically, MCAS is satisfying the use case as expected. It recognizes a download, so it blocks the action. Some customers have expressed that blocking the preview inhibits users from completing daily tasks. Good news! We have found a workaround for this exact scenario.
There is a PowerShell module specifically for Exchange Online that will allow users to preview PDF but remove the download functionality so data will remain protected even if accessed from an unmanaged device.
Here are the steps:
Note: The “OwaMailboxPolicy-Default” is the default OWA policy in EXO. It is possible customers have deployed additional or created a custom OWA policy with a different name. If customers have multiple OWA policies, they may have those applied to specific users. Therefore, those would also need to be updated to have complete coverage.
- Download the Exchange Online Powershell Module: PowerShell Gallery | ExchangeOnlineManagement 2.0.4
- After this the user will need to connect to the module (depending on the tenant here is the list of commands):
- Connect to Exchange Online PowerShell | Microsoft Docs
- Once the user has established connection to the exchange online Powershell, they will need to update two command lines
- Set-OwaMailboxPolicy (ExchangePowerShell) | Microsoft Docs:
- Set-OwaMailboxPolicy -Identity OwaMailboxPolicy-Default -DirectFileAccessOnPrivateComputersEnabled $false -DirectFileAccessOnPublicComputersEnabled $false
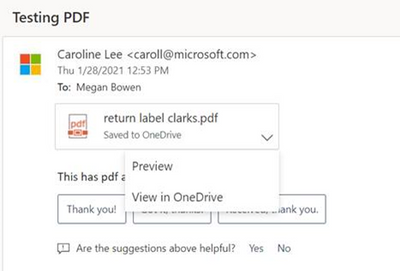
- After these parameters have been set, run a test on OWA with a PDF file & a session policy configured to block downloads. The “Download,” option should be removed from the dropdown and the user can preview the file.
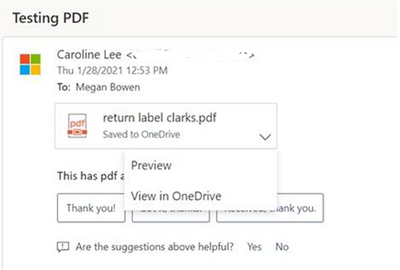
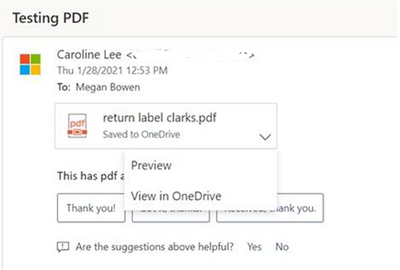
- Before Powershell cmd:
After Powershell cmd:
Thanks for tuning in on the first post on Real Time Controls. Look out for these steps in the Troubleshooting guide (https://docs.microsoft.com/en-us/cloud-app-security/troubleshooting-proxy). If there are any scenarios you’re curious in seeing, please leave a comment below.
——-
Feedback
Let us know if you have any feedback or relevant use cases/requirements for this portion of Microsoft Cloud App Security by emailing CASFeedback@microsoft.com and mentioning the core area of concern.
Learn more
For further information on how your organization can benefit from Microsoft Cloud App Security, connect with us at the links below:
To experience the benefits of full-featured CASB, sign up for a free trial—Microsoft Cloud App Security.
Follow us on LinkedIn as #CloudAppSecurity. To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity on Twitter and Microsoft Security on LinkedIn for the latest news and updates on cybersecurity.
by Contributed | Mar 12, 2021 | Technology
This article is contributed. See the original author and article here.
The accelerated networking update for the HPC SKUs on Azure has caused problems for older OS distributions or any MPI versions that do not use the latest UCX. This is due to inconsistent naming for the IB devices. My recent patch to rdma-core can be used to provide consistent naming with udev rules. This following script can be used when building an image:
yum install -y cmake libnl3-devel
git clone https://github.com/linux-rdma/rdma-core.git
cd rdma-core
bash build.sh
cp build/bin/rdma_rename /usr/lib/udev/
cat <<EOF >/etc/udev/rules.d/60-ib.rules
# Accelnet board
ACTION==”add”, ATTR{board_id}==”MSF0010110035″, SUBSYSTEM==”infiniband”, PROGRAM=”rdma_rename %k NAME_FIXED mlx5_an0″
# HBv2 board
ACTION==”add”, ATTR{board_id}==”MT_0000000223″, SUBSYSTEM==”infiniband”, PROGRAM=”rdma_rename %k NAME_FIXED mlx5_ib0″
# HC board
ACTION==”add”, ATTR{board_id}==”MT_0000000010″, SUBSYSTEM==”infiniband”, PROGRAM=”rdma_rename %k NAME_FIXED mlx5_ib0″
EOF
This will name the accelerated networking mlx5_an0 and the infiniband to mlx5_ib0. Now, you can use the older MPI/UCX versions by setting:
export UCX_NET_DEVICES=mlx5_ib0:1
The script includes rules that will work for HB, HC, HBv2 and NDv2.
by Contributed | Mar 12, 2021 | Technology
This article is contributed. See the original author and article here.
Authored with Itamar Falcon, Product Manager, Microsoft Cloud App Security
Attacks don’t respect domain boundaries. They move fast across cloud applications, endpoints, user identities and data domains. They establish a foothold and move laterally across platforms. The integration of Microsoft Cloud App Security and Microsoft 365 Defender is designed to reduce the surface area for potential attack by accomplishing these three key objectives (and that’s just the start):
- Protecting against attacks and coordinating defensive responses in multi-cloud, multi-app environments and other Microsoft 365 Defender workloads through signal sharing and automated actions.
- Delivering complete narration of the attack across products for security teams by joining data on alerts, suspicious events by comparing UEBA analytics and impacted assets to incidents.
- Enabling security teams to perform detailed, effective threat hunting across all security domains.
Threat protection from your CASB should help automate your responses to incidents and alert you to risky activities in your cloud environment. Check out this brief two-minute video, which demonstrates the value of integrated threat protection in Microsoft Cloud App Security:
As organizations move increasingly to the cloud, protecting the cloud attack vector is critical. In some cases, attackers perform malicious activities on the organization’s cloud infrastructure with a limited footprint on other domains. In other cases, the cloud attack is only part of a much bigger campaign. To fully understand the connections between different alerts and signals, Microsoft 365 Defender, together with Cloud App Security, has developed unique correlations to lend SOC teams insight on the full story with less effort.
In the video below, Itamar leads a discussion on threat protection in Microsoft Cloud App Security, demonstrating:
- The flow of correlation of signals into an incident between Microsoft 365 Defender and Microsoft Cloud App Security.
- The scope of breach as coordinated by Microsoft 365 Defender advanced hunting by combining signals across workloads: classification of an alert in Microsoft Cloud App Security from the Microsoft 365 Defender portal.
These simple examples illustrate the power of integration of Microsoft Cloud App Security and Microsoft 365 Defender. This integration delivers a set of full capabilities to save time, strengthen security and quickly resolve incidents in your environment. In upcoming development cycles, you will have new threat capabilities around advanced hunting and correlations with Cloud App Security alerts.
For additional deeper information on this topic, read Sebastien Molendijk’s recent blog: Microsoft Cloud App Security: The Hunt in a multi-stage incident.
Feedback
We welcome your feedback or relevant use cases and requirements for these capabilities in Cloud App Security by emailing CASFeedback@microsoft.com and mention “Threat Protection”.
Learn more
For further information on how your organization can benefit from Microsoft Cloud App Security, connect with us at the links below:
To experience the benefits of full-featured CASB, sign up for a free trial—Microsoft Cloud App Security.
Follow us on LinkedIn as #CloudAppSecurity. To learn more about Microsoft Security solutions visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity on Twitter, and Microsoft Security on LinkedIn for the latest news and updates on cybersecurity.

by Contributed | Mar 12, 2021 | Technology
This article is contributed. See the original author and article here.
I am very excited to announce to you the monthly M365 Government Community Call – a live(ish) call occurring the second Tuesday of every month led by and for the Government Community.
This monthly call will be based here, in the Microsoft PubSec Tech Community, will include six panelists covering the latest announcements for O365 GCC, GCC-H, and DOD tenants. While each month two slots will change based on topic and availability, it will be led by the following four community leaders:
- Jeremy Wood (@geekwithin), Director of Policy & Planning at the Millennium Challenge Corporation, Organizer of Microsoft 365 for Government DC Users Group
- Rima Reyes (@rimazima), Principal Program Manager for Government at Microsoft Teams Engineering
- Sarah Gilbert (@singingtech), Community Technical Manager Public Sector at Microsoft
- Jay Leask (@jayleask), Lead Modern Workplace Strategist at AvePoint Public Sector, Organizer at NOVA365 and Azure User Group
*Special thanks to the AvePoint Public Sector team who is managing our broadcast and providing all the wonderful graphics!!!
M365 Gov Community Call Notes

YOUTUBEVIDEO: https://www.youtube.com/watch?v=AQTnHYTc_xw&list=PLyJFOtpJV3wNOExhHa6Uo5XLieb0RC_EW
https://www.youtube-nocookie.com/embed/AQTnHYTc_xw
This month brought special guests Amie Seisay (LinkedIn), DC-area O365 and SharePoint solution provider, and Matthew Littleton (LinkedIn), Global Advanced Compliance Specialist at Microsoft.
In our inaugural episode we tried to focus on Microsoft Ignite, but as the Government Community is used to, there were not a lot of GCC, GCC-H, or DOD announcements last week. So, after a brief “what was cool and exciting” segment (have you seen Mesh? or Viva? And yes, we’re assured Viva for GCC is … on the way), we moved on to Government News from February and March. Here’s a list of topics and some related links, to make sure you caught everything!
M365 Gov Community Calendar
Also, as part of our monthly community call we aim to provide a list of DC-area or Government specific events to ensure you know what is happening in the community. See below for events through the end of March:
Putting the “Community” in the Community Call
The M365 Gov Community Call is all about YOU – GCC, GCC-H, and DOD users in the Microsoft cloud, and we want to make sure you have a voice!
Monthly, second Tuesday, 11:30am Eastern
Each month we will release a new episode on the SECOND TUESDAY at 11:30am. These will go live on this M365 Gov Community Call playlist – make sure you subscribe to get notifications! And seriously, this is happening and this is YOUR CALL.
Have questions? Post them here and tag myself or @Sarah Gilbert! Tag any of us on Twitter: @geekwithin | @rimazima | @singingtech | @jayleask | @AvePointGov
Have an event? Again, let us know and we’d be THRILLED to include you in our Community Events segment!

by Contributed | Mar 12, 2021 | Technology
This article is contributed. See the original author and article here.

Building micro services through Event Driven Architecture part14 : Query API.
Gora Leye is a Solutions Architect, Technical Expert and Devoper based in Paris. He works predominantly in Microsoft stacks: Dotnet, Dotnet Core, Azure, Azure Active Directory/Graph, VSTS, Docker, Kubernetes, and software quality. Gora has a mastery of technical tests (unit tests, integration tests, acceptance tests, and user interface tests). Follow him on Twitter @logcorner.

A brief history of the Microsoft MVP Program
Hal Hostetler is an Office Apps and Services MVP who has been in the MVP program since 1996. Now retired, Hal is a Certified Professional Broadcast Engineer and remains the regional engineer for Daystar Broadcasting and a senior consultant for Roland, Schorr, & Tower. He lives in Tucson, Arizona. For more on Hal, check out his Twitter @TVWizard

Securing Microsoft Teams
Tobias Zimmergren is a Microsoft Azure MVP from Sweden. As the Head of Technical Operations at Rencore, Tobias designs and builds distributed cloud solutions. He is the co-founder and co-host of the Ctrl+Alt+Azure Podcast since 2019, and co-founder and organizer of Sweden SharePoint User Group from 2007 to 2017. For more, check out his blog, newsletter, and Twitter @zimmergren

Unit testing: How to write your first unit test for T-SQL code
Sergio Govoni is a graduate of Computer Science from “Università degli Studi” in Ferrara, Italy. Following almost two decades at Centro Software, a software house that produces the best ERP for manufacturing companies that are export-oriented, Sergio now manages the Development Product Team and is constantly involved on several team projects. For the provided help to technical communities and for sharing his own experience, since 2010 he has received the Microsoft Data Platform MVP award. During 2011 he contributed to writing the book: SQL Server MVP Deep Dives Volume 2. Follow him on Twitter or read his blogs in Italian and English.

Teams Real Simple with Pictures: App Customisation with Praise
Chris Hoard is a Microsoft Certified Trainer Regional Lead (MCT RL), Educator (MCEd) and Teams MVP. With over 10 years of cloud computing experience, he is currently building an education practice for Vuzion (Tier 2 UK CSP). His focus areas are Microsoft Teams, Microsoft 365 and entry-level Azure. Follow Chris on Twitter at @Microsoft365Pro and check out his blog here.


Recent Comments