This article is contributed. See the original author and article here.
The results of current and past automatic investigations and remediation actions across your organization’s devices and mailboxes are visible in the Action center in Microsoft Threat Protection. The Action center provides a unified experience for remediation actions and an audit log. The Action center enables your security operations team to approve pending remediation actions and to remediate impacted assets. You can also review approved actions in an audit log. The Action center brings all this together across Microsoft Threat Protection security workloads, including Office 365 Advanced Threat Protection (Office 365 ATP) and Microsoft Defender Advanced Threat Protection (Microsoft Defender ATP).
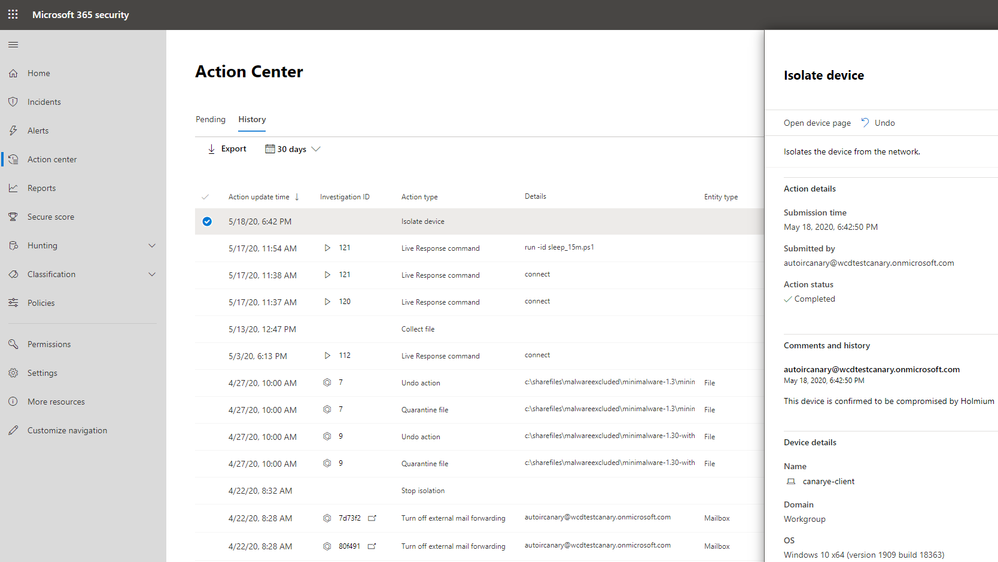
Furthermore, if you need to undo a remediation action that was taken by Microsoft Defender ATP, in most cases, you can do that in the Action center in Microsoft Threat Protection. The History tab tracks all remediation actions that were completed, and you can undo an action there.
But what about remediation actions that were taken manually or from an advanced hunting experience, such as isolating a device, or restricting app execution on a specific device? How do you view an audit log for those actions?
Suppose, for example, that in order to slow down the spread of ransomware, your security operations team decides to isolate all of the devices connected to specific subnet in your org. To take this action, you could use an advanced hunting custom detection with the predefined action, “Isolate device.” Such a custom detection might look like this:
DeviceNetworkEvents
| extend Subnet = extract(@”(?:(?:25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?).){3}”,0,LocalIP ) | where Subnet starts with “192.168.0.”
Or, maybe you use a slightly more advanced example with specific alert categories to view the list of devices, like this:
DeviceAlertEvents
| where Category in(“Credential access”, “Ransomware”) | join kind=leftouter(
DeviceNetworkEvents
| extend Subnet = extract(@”(?:(?:25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?).){3}”,0,LocalIP )
| where Subnet starts with “192.168.0.” )
, but how do you know which devices were isolated, and how do you undo device isolation if needed?
We’re happy to announce that you can now audit and undo manually taken actions in Microsoft Defender ATP in the Action center in Microsoft Threat Protection. This capability is in public preview now!
This capability provides you with one location to view an audit log of manually taken remediation actions that were performed in different portal experiences, such as the device page, file page, and advanced hunting. You can also undo certain actions, such as device isolation and app restriction, on the History tab in the Action center.
The full set of manual actions that are logged in the action center are :
- Collect investigation package
- Isolate device / Undo isolate device
- Offboard machine
- Release code execution
- Release from quarantine
- Request sample
- Restrict code execution / Undo restrict code execution
- Run antivirus scan
- Stop and quarantine
Want to see what this looks like? Here’s an example of an audit record showing device isolation:
Here’s an example of undoing an action to isolate device:
Make sure to opt in to preview features, and try it now!
Let us know what you think by leaving a comment below.
The Microsoft Threat Protection Team
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.


Recent Comments