
by Contributed | Oct 12, 2022 | Technology
This article is contributed. See the original author and article here.
 Join us Oct 19th
Join us Oct 19th
Please join us for our next Federal Business Applications Webinar on October 19th where the Microsoft team will be joined by partner NetImpact Strategies.
NetImpact Strategies will showcase two Microsoft Store approved software solutions built on top of the Power Platform.
First, DX360 Security ARMOR intelligent automation for Cyber compliance and continuous monitoring including RMF ATO and FedRAMP authorizations and defensive cyber operations.
Second, Public Sector Case Management (PSCM) suite that provides fully configurable life cycle case management processes for various case types including Investigative, FOIA, Benefits and Grants. PSCM also provides secure public portal to enable citizen (G2C) and business (G2B) interfaces for delivery of case management services.
Agenda:
- Product & Community Updates
- NetImpact Strategies Demonstration
- Question and Answer Session
To register for this event, please go to the signup link below,
https://aka.ms/FedBizAppsWebinar
All of our past webinar events and recordings can be found in the link below,
https://github.com/microsoft/Federal-Business-Applications/blob/main/whitepapers/webinar-series/README.md
by Scott Muniz | Oct 11, 2022 | Security, Technology
This article is contributed. See the original author and article here.
Adobe has released security updates to address multiple vulnerabilities in Adobe software. An attacker can exploit some of these vulnerabilities to take control of an affected system.
CISA encourages users and administrators to review Adobe Security Bulletins and apply the necessary updates.
• Adobe Cold Fusion APSB22-44
• Adobe Acrobat and Reader APSB22-46
• Adobe Commerce and Magneto Open Source APSB22-48
• Adobe Dimension APSB22-57

by Scott Muniz | Oct 11, 2022 | Security, Technology
This article is contributed. See the original author and article here.

Official websites use .gov
A .gov website belongs to an official government organization in the United States.

Secure .gov websites use HTTPS
A
lock ( )
) or
https:// means you’ve safely connected to the .gov website. Share sensitive information only on official, secure websites.
by Contributed | Oct 11, 2022 | Technology
This article is contributed. See the original author and article here.
Microsoft has released Security Updates (SUs) for vulnerabilities found in:
- Exchange Server 2013
- Exchange Server 2016
- Exchange Server 2019
SUs are available in a self-extracting auto-elevating .exe package, as well as the original update packages (.msp files), which can be downloaded from the Microsoft Update Catalog.
The October 2022 SUs are available for the following specific versions of Exchange Server:
The SUs address vulnerabilities responsibly reported to Microsoft by security partners and found through Microsoft’s internal processes. Our recommendation is to immediately install these updates to protect your environment.
These vulnerabilities affect Exchange Server. Exchange Online customers are already protected from the vulnerabilities addressed in these SUs and do not need to take any action other than updating any Exchange servers in their environment.
NOTE The October 2022 SUs do not contain fixes for the zero-day vulnerabilities reported publicly on September 29, 2022 (CVE-2022-41040 and CVE-2022-41082). Please see this blog post to apply mitigations for those vulnerabilities. We will release updates for CVE-2022-41040 and CVE-2022-41082 when they are ready.
Also note that we have re-released some CVEs published in August 2022, to highlight the resolution of known issue. More details about specific CVEs can be found in the Security Update Guide (filter on Exchange Server under Product Family).
Enable Windows Extended Protection
Starting with the August 2022 SUs, Exchange Server supports the Windows Extended Protection (EP) feature, which can help you protect your environments from authentication relay or “man in the middle” (MitM) attacks. If you have not yet enabled EP in your environment, please install the October SUs which address a known issue in Exchange EP support (see below). Then, review the information in the Manual Enablement of Extended Protection section of our August announcement for more details.
Customers who have already installed the August 2022 SUs and have enabled EP do not need to re-run the EP script after installing the October SUs.
Update installation
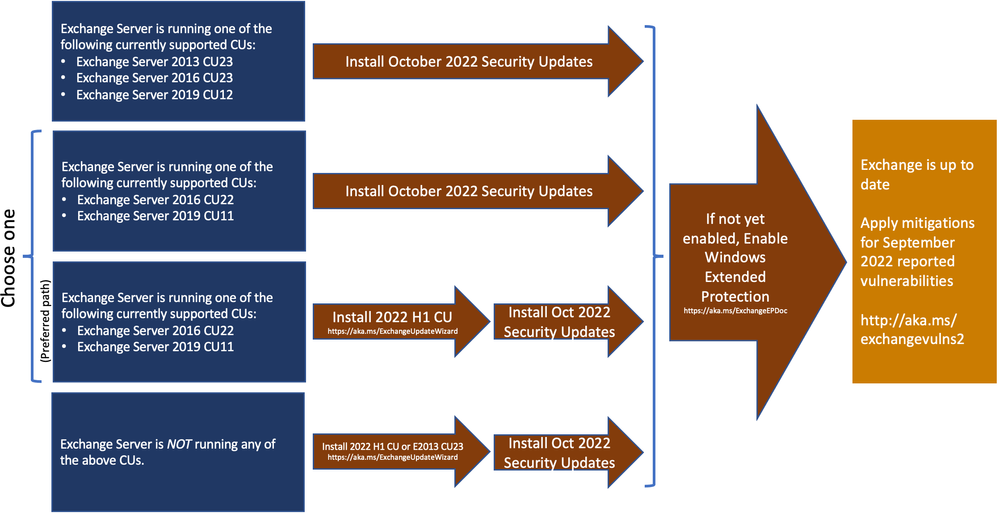
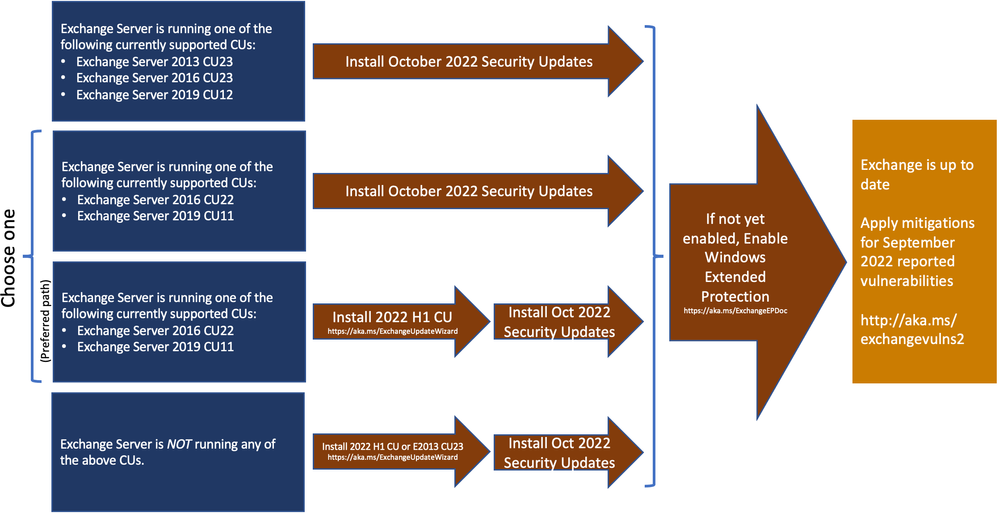
The following update paths are available:
Known issues with this release
We are not aware of any known issues with this release.
Issues resolved by this release
- In Exchange 2013, Exchange 2016, and Exchange 2019 various Outlook and compliance-related monitoring probes show as Failed once EP is enabled.
FAQs
My organization is in Hybrid mode with Exchange Online. Do I need to do anything?
Exchange Online is already protected, but the October 2022 SUs need to be installed on your Exchange servers, even if they are used only for management purposes. You do not need to re-run the Hybrid Configuration Wizard after installing these updates.
Do I need to install the updates on ‘Exchange Management Tools only’ workstations?
Servers and workstations running only the Management tools role (no Exchange services) do not need these updates.
This post might receive future updates; they will be listed here (if available).
The Exchange Server Team
by Scott Muniz | Oct 11, 2022 | Security, Technology
This article is contributed. See the original author and article here.
CISA has added one new vulnerability to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. This type of vulnerability is a frequent attack vector for malicious cyber actors and pose significant risk to the federal enterprise. Note: To view the newly added vulnerabilities in the catalog, click on the arrow in the “Date Added to Catalog” column, which will sort by descending dates.
Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the Known Exploited Vulnerabilities Catalog as a living list of known CVEs that carry significant risk to the federal enterprise. BOD 22-01 requires FCEB agencies to remediate identified vulnerabilities by the due date to protect FCEB networks against active threats. See the BOD 22-01 Fact Sheet for more information.
Although BOD 22-01 only applies to FCEB agencies, CISA strongly urges all organizations to reduce their exposure to cyberattacks by prioritizing timely remediation of Catalog vulnerabilities as part of their vulnerability management practice. CISA will continue to add vulnerabilities to the Catalog that meet the specified criteria.
Join us Oct 19th


Recent Comments