This article is contributed. See the original author and article here.
Microsoft 365 Defender automatically expands incidents to tell the full story of an attack.
It does this by leveraging the unique position which enables it to look across workloads and automatically expand the incident story, after all malicious activities are not generated in a void – there is something out there, logged by another workload, which can add insights. And this is exactly what we are doing in Microsoft 365 Defender; generating incidents based on other alerts that are triggered from the different detection sources, like, MDE, MDO, MDI and MCAS.
We are excited to introduce a new alert page for these detections. The new page provides additional, enriched information providing greater context into an attack. Security professionals can now see which other triggered alert caused the current alert and all the affected entities and activities involved in the attack, including files, users and mailboxes.
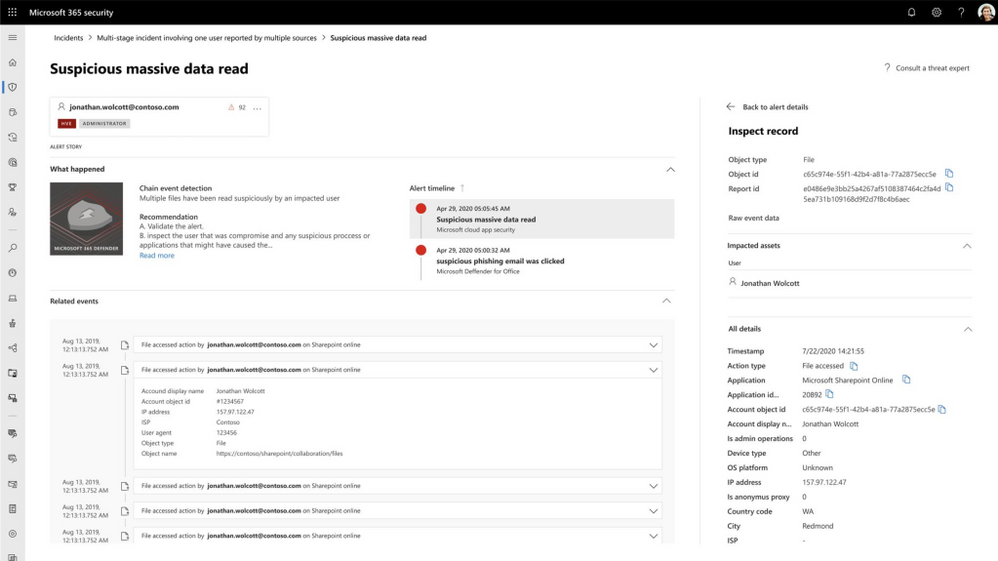
For example; an alert from Microsoft Defender for Office 365 might imply that a user’s credentials have been stolen. Once the alert is triggered, Microsoft 365 Defender will automatically search for other activities within the organization that are related to this user. This could include a mass data read event within several minutes of the credentials being breached.
Opening or viewing a large number of files may not be an indicator of a breach on its own but with the context of the credential theft alert it becomes a major concern. Microsoft 365 Defender recognizes the related context of these activities and the risk that an attacker is accessing large amounts of user data.
Using these alerts, the security analyst can see which files have been accessed, and in which applications and directories. They can also see the alerts and the relevant context. All of this information is correlated into a single incident that would also include other relevant alerts showing lateral movement, persistence, or further infiltration related to the same attack. With this breadth and depth of visibility the SOC can respond quickly and holistically across the entire attack from a single dashboard.
Microsoft 365 Defender leverages AI to automatically expand an investigation, just like an experienced analyst would. This allows your SOC team to focus on what matters: keeping your organization safe.
To learn more about incident in Microsoft Threat Protection go to the following links:
- Inside Microsoft Threat Protection: Correlating and consolidating attacks into incidents
- Inside Microsoft Threat Protection: Mapping attack chains from cloud to endpoint
- Inside Microsoft Threat Protection: Attack modeling for finding and stopping lateral movement
- Inside Microsoft Threat Protection: Solving cross-domain security incidents through the power of cor…
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.


Recent Comments