CISA Releases Capacity Enhancement Guides to Enhance Mobile Device Cybersecurity for Consumers and Organizations
This article is contributed. See the original author and article here.
This article is contributed. See the original author and article here.
This article is contributed. See the original author and article here.
Data warehouse, data integration, and big data analytics together are continuing to grow at planetary scale in enterprises. Azure Synapse Analytics provides limitless analytics services to query data using different compute engines and programming languages. Azure Synapse workspaces allow the data engineering, machine learning, and BI projects to coexist without creating silos in experiences, processes, and tools. As data continues to explode and be used, it’s more important than ever to fully govern the data.
The Azure Purview integration in Azure Synapse provides a comprehensive data governance solution with a single pane of glass for all analytics workloads. Organizations can run a variety of analytics projects and put data to work much more quickly, productively, and securely, generating insights from all data sources. The embedded data discovery experience in Azure Synapse powered by Azure Purview further increases data agility and time to insights.
In this blog, you will learn how to govern your Azure Synapse workspace by connecting to Azure Purview for automated data discovery and classifications in the Purview Data Map. You can further use the Purview Data Catalog to search enterprise data and use contextual gestures to build analytics workloads.
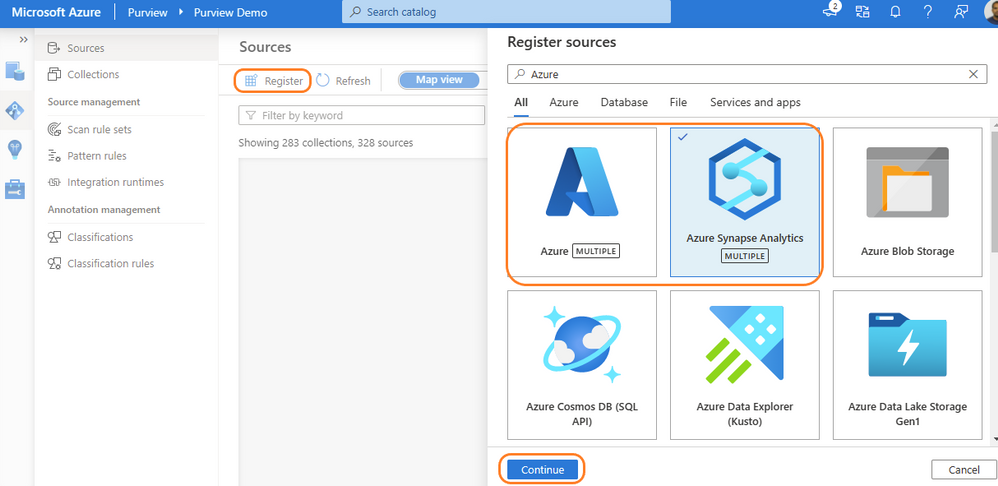
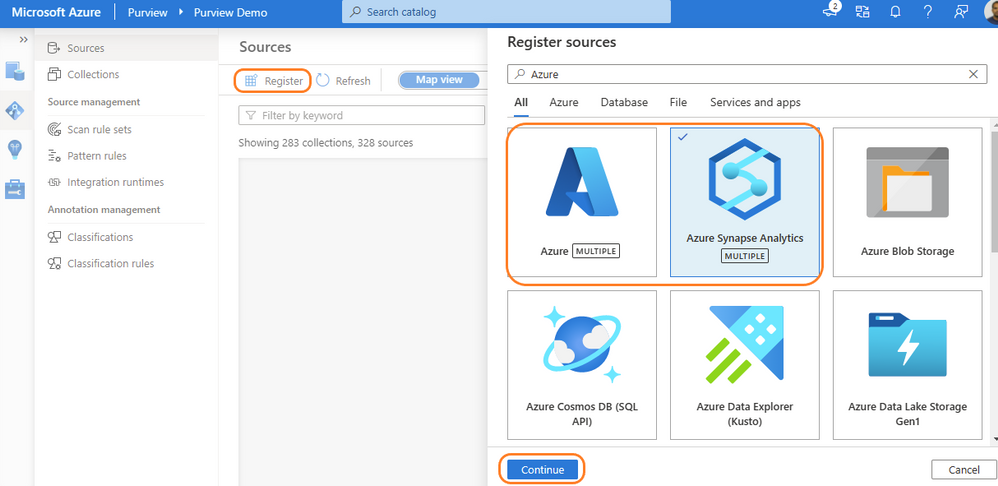
Purview data source administrators can start by registering an Azure Synapse workspace under a collection of the Purview Data Map. Admins can choose to register individual workspaces or simply register the Azure Subscription containing all Azure Synapse workspaces. With a few clicks, a recurring scan can be set for automated data discovery of technical metadata and classifications. Azure Purview can support 200-plus classifications that look for sensitive and PII data while scanning. The admin can configure specific databases of a workspace and credentials managed in Azure Key vault for secured connection while scanning. Creating a private endpoint is supported for scanning Azure Synapse workspaces behind VNET. Read more details on how to register and scan Azure Synapse Analytics workspaces.
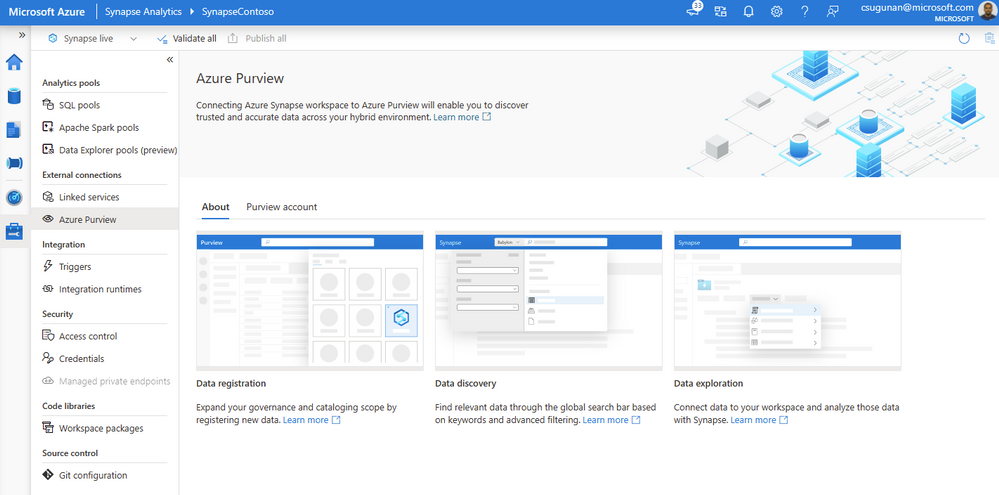
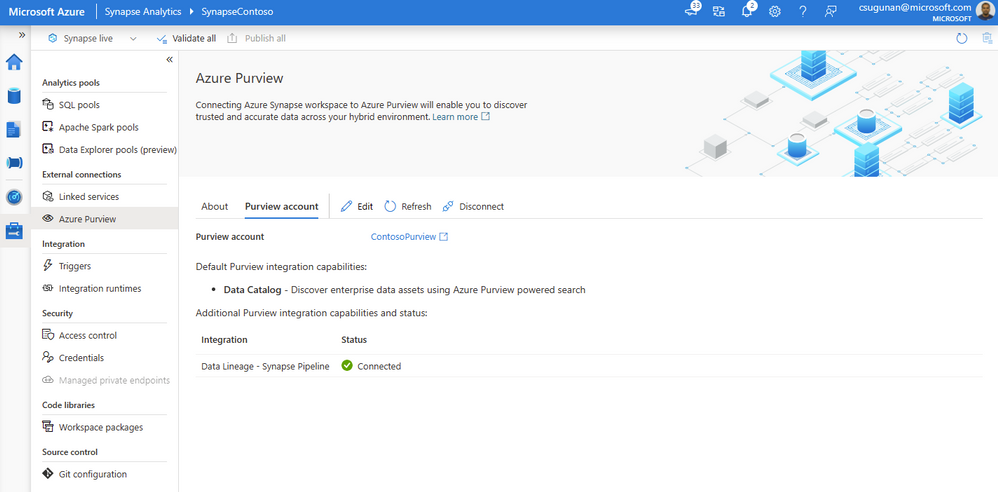
Azure Synapse contributors can register an Azure Purview account by navigating to Manage > External connections > Azure Purview. With a single click, the Azure Synapse workspace is integrated with Azure Purview for data governance. Azure Purview helps discover all data across your organization, track lineage of data, and create a business glossary wherever it is stored: on-premises, across clouds, in SaaS applications, and in Microsoft Power BI. Read step-by-step documentation to Connect Synapse workspace to Azure Purview.
Select a Purview account from the dropdown or enter the resource URI manually and click apply. To connect a Purview account behind VNET, read how to Access a secured Azure Purview account.
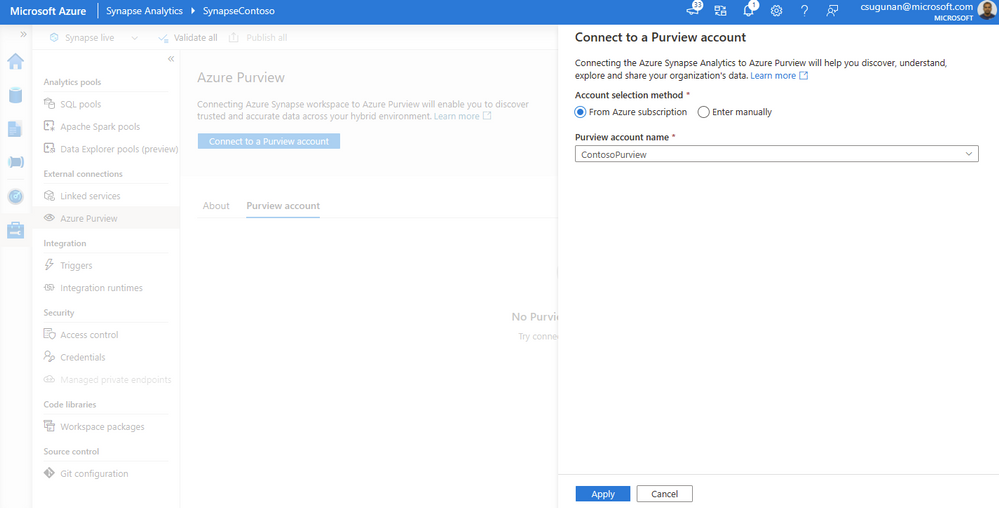
Once registration is complete, the connection and integration status are shown in the details section.
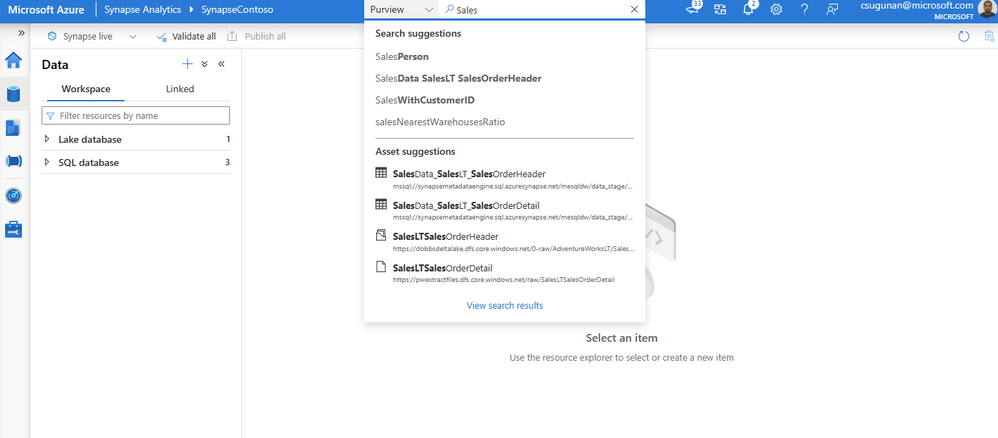
The search box in the Azure Synapse workspace menu bar is now powered by Azure Purview for the Data, Develop, and Integrate sections. Start typing the keyword in the search bar to let Purview’s intuitive search automatically complete and match the asset by relevance on name, classification, labels, contacts, and more.
Search results are displayed in a dedicated tab for Purview. The familiar search result page experience of Purview is retained inside the Azure Synapse workspace.
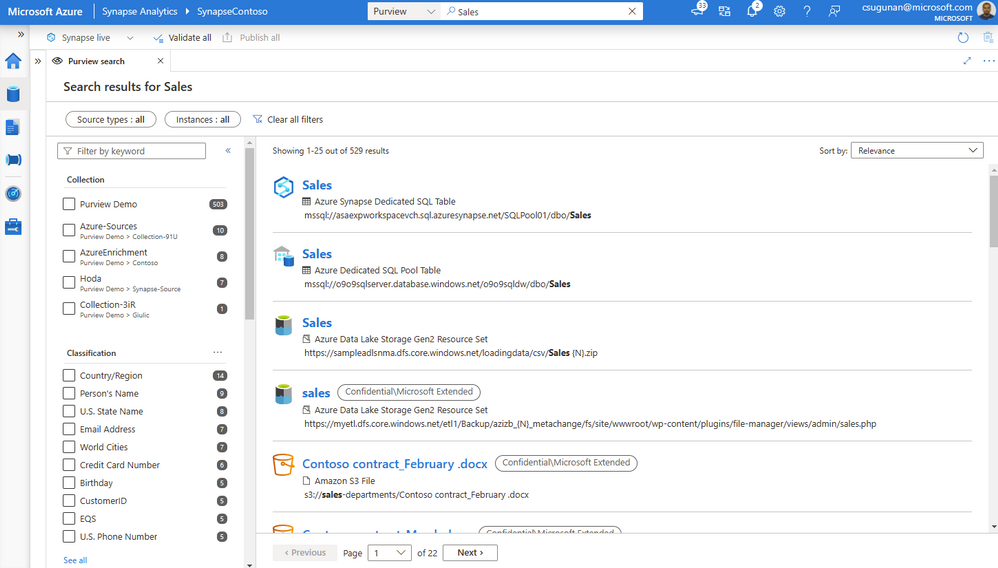
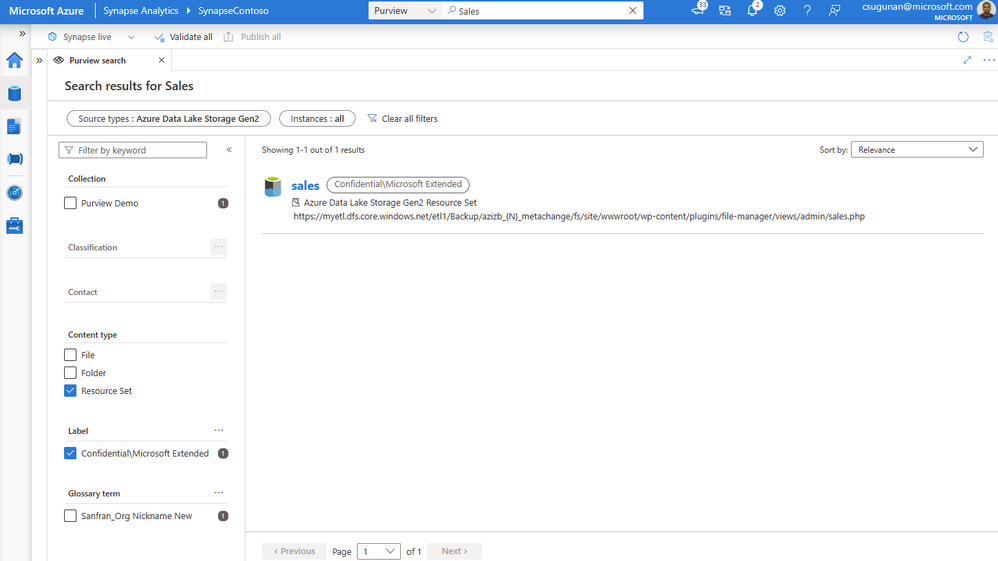
With a few clicks, narrow down the search results to exact assets in Purview.
In the asset details page, Azure Synapse users can perform a variety of contextual gestures to connect for further analytics. Depending on the asset type discovered, users can use the following gestures:
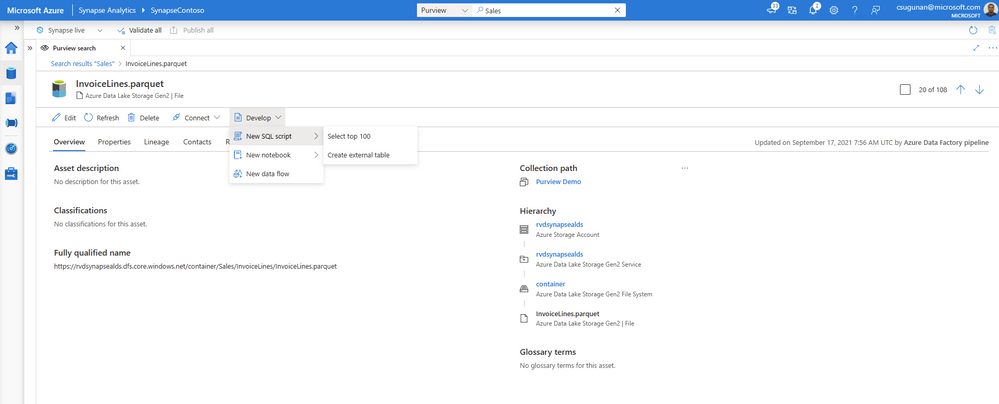
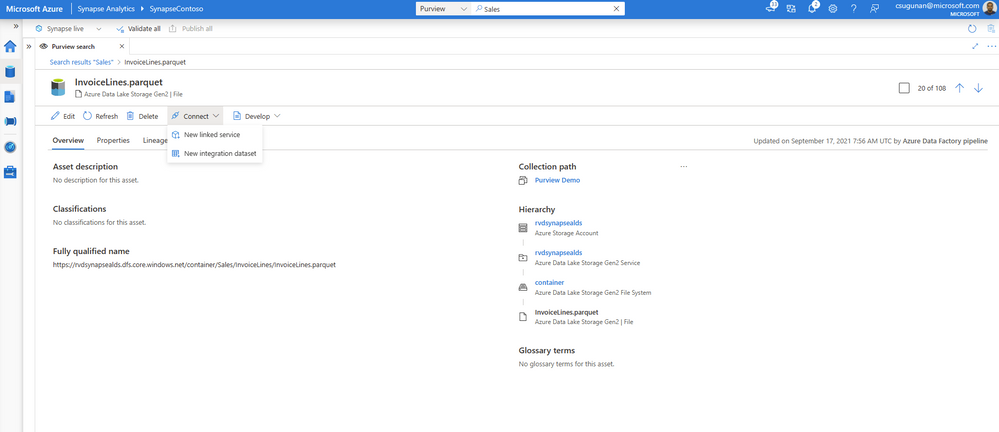
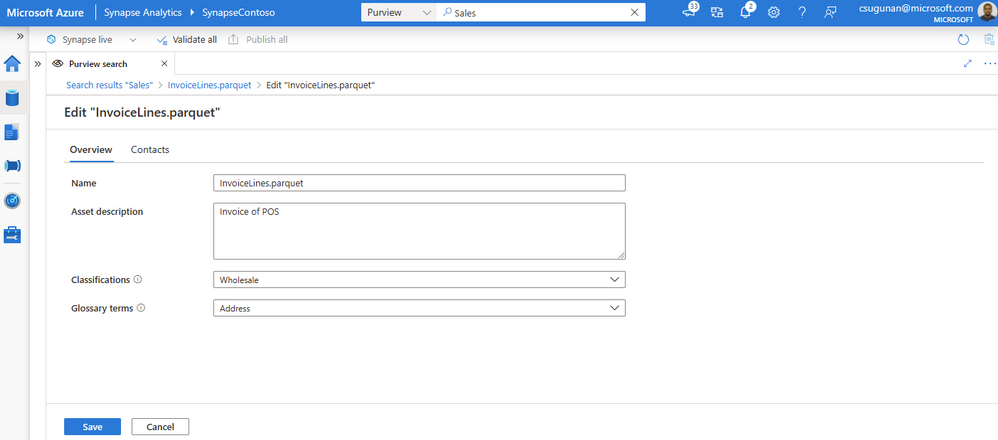
Data producers can directly edit the asset from the Azure Synapse workspace and curate by adding business glossary, description, classifications, and contact details.
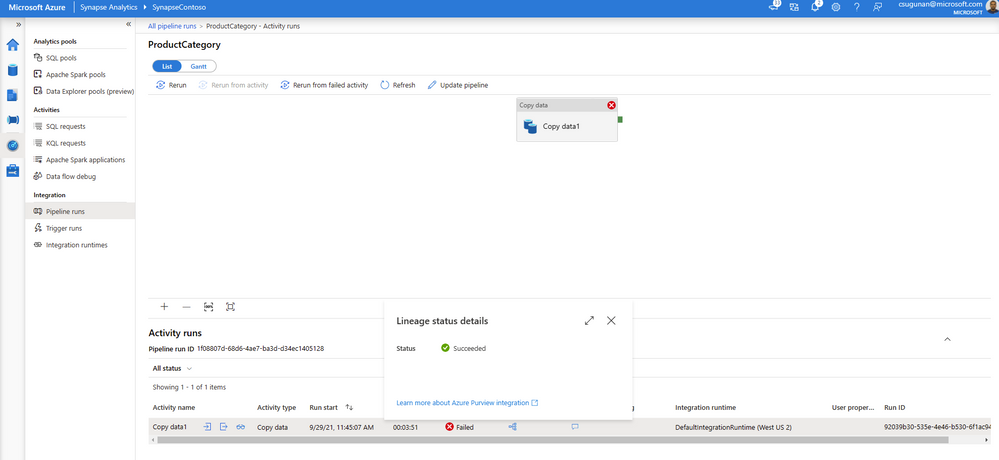
Data lineage from Azure Synapse are automatically pushed to the connected Purview account for copy and data flow activity. Detailed documents are available for Metadata and lineage from Azure Synapse Analytics.
The lineage metadata is pushed to Purview in real time at the end of each pipeline run. It includes granular details such as column lineage, pipeline run status, row count, and additional metadata.
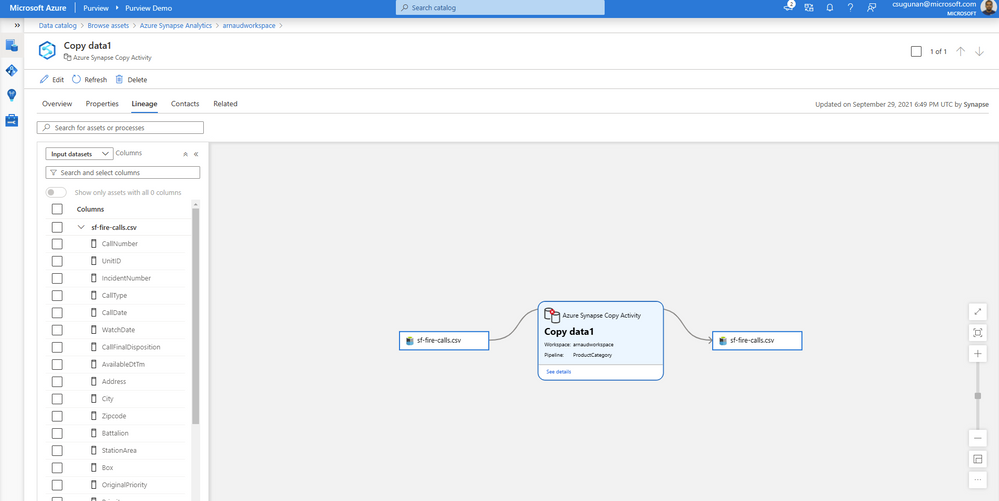
Lineage status is available from the pipeline run monitoring page of the Azure Synapse workspace.
This article is contributed. See the original author and article here.
VMware has released security updates to address multiple vulnerabilities in vCenter Server and Cloud Foundation. A remote attacker can exploit this vulnerability to obtain access to sensitive information.
CISA encourages users and administrators to review VMware Security Advisory VMSA-2021-0027 and apply the necessary updates.

This article is contributed. See the original author and article here.
Any call center that uses unified routing to manage and assign incoming support requests is going to notice gains in efficiency. The core routing capabilities in Dynamics 365 Customer Service use skill matching and priority to help determine assignments. However, bringing intelligence to the challenge of efficient routing can move you closer to world-class service.
With the unified routing release in April of 2021, we introduced intelligent skill finder as the first capability related to intelligent work classification. It empowers organizations to identify which skills are required by the agent to address an incoming work item. AI models are trained to understand the skills required to address customer inquiries, and then a match is made to agent skills, helping to assign the calls to agents. In this new release, we’re adding two more capabilities to intelligent work classification: customer sentiment identification and effort estimation for routing. These capabilities will enable organizations to harness state-of-the-art AI to improve customer satisfaction and reduce resolution times.
Matching agents to calls based on skills is a basic capability in unified routing. What if you could also gauge customer sentiment based on keywords, and then route calls to agents best able to handle those various emotions?
Let’s better understand this with a scenario. Imagine Contoso Coffee is operating a support center and has implemented unified routing. They recently had a high volume of unhappy customers, and they brainstormed about how best to use their existing staff to address these concerns. Contoso Coffee realizes that customer sentiment could be used as a signal to influence call routing; some agents are better at managing unhappy customers. Contoso decides to adopt sentiment prediction in unified routing. They take a few simple steps:
As a result, Contoso Coffee was able to address the spike in unhappy customers, leveraging their agents to maintain customer satisfaction.
Learn more about using customer sentiment in classification in this short video introduction:
This embed requires accepting cookies from the embed’s site to view the embed. Activate the link to accept cookies and view the embedded content.
Read more in the documentation about using sentiment prediction-based model in work classification.
A key contributor to an effective contact center is understanding how long it will take to address support requests. Organizations do not have a simple way to understand how much time it will take agents to address incoming work items. Effort estimation replaces manual processes with the use of AI. This intelligence interprets the issue and uses historical support data to generate a work estimate.
Highlights of this capability include:
Learn more about effort-based routing in this short video introduction:
This embed requires accepting cookies from the embed’s site to view the embed. Activate the link to accept cookies and view the embedded content.
Read more in the documentation about using the effort estimation model in unified routing.
In any contact center, each agent will have a different set of skills to offer, and organizations should use those skills appropriately to best address customer requests. To maximize agent potential, it is critical for any organization to understand the skills required to address a work item and identify the agent that is best suited to address it. Intelligent skill finder takes the guesswork out of this by using AI to predict the skills required to address an incoming work item, and then matching those required skills to corresponding agents.
Highlights of this capability include:
Visit the Dynamics 365 Customer Service Community Forum to share your thoughts.
This blog post is part of a series of deep dives that will help you deploy and use unified routing at your organization. See other posts in the series to learn more.
The post Use intelligence to transform routing of service delivery requests appeared first on Microsoft Dynamics 365 Blog.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article is contributed. See the original author and article here.
Welcome to our new monthly blog series featuring the latest Security, Compliance, and Identity content updates on Microsoft Learn! This is our first post, and we’re highlighting recently released updates, including a new learning path we launched during Cybersecurity Awareness Month. Starting in January, we’ll highlight new learning paths, modules, and other content updates we make each month to give you the skills you need on your learning journey.
Read on to check out some of the latest updates from our Security, Compliance, and Identity portfolio.
Knowing the fundamentals of cybersecurity is a first step toward protecting against cyberthreats. Our new learning path—Describe the basic concepts of cybersecurity—delivers foundational knowledge about cybersecurity concepts including cryptography, authentication, and authorization, along with exploring ways to protect yourself and your business from cyberattacks.
This four-part series of learning paths will equip you with the knowledge you need to take Exam AZ-500.
This learning path will teach you how to secure Azure solutions with Azure Active Directory, implement hybrid identity, deploy Azure AD identity protection, and configure Azure AD privileged identity management.
This learning path will teach you how to lock down the infrastructure and network resources that are running in your Azure environment.
This learning path will teach you how to deploy and secure Azure Key Vault, configure application security features, implement storage security, and configure and manage SQL database security.
This learning path will teach you how to configure and manage Azure monitor, enable, and manage Azure Security Center, and configure and monitor Azure Sentinel.
You can take Exam AZ-500: Microsoft Azure Security Technologies once you have completed the learning path to earn a certification.
Microsoft Endpoint Configuration Manager—which is part of Microsoft Endpoint Manager—helps you protect the on-premises devices, apps, and data that the people at your organization use to stay productive. Our newest module, Understand co-management using Microsoft Endpoint Configuration Manager, provides an in-depth look at how to enable co-management based on the implementation path that best suits your organization. You’ll also:
We’re excited to hear how you use these updated resources on your journey to certification!
This article is contributed. See the original author and article here.
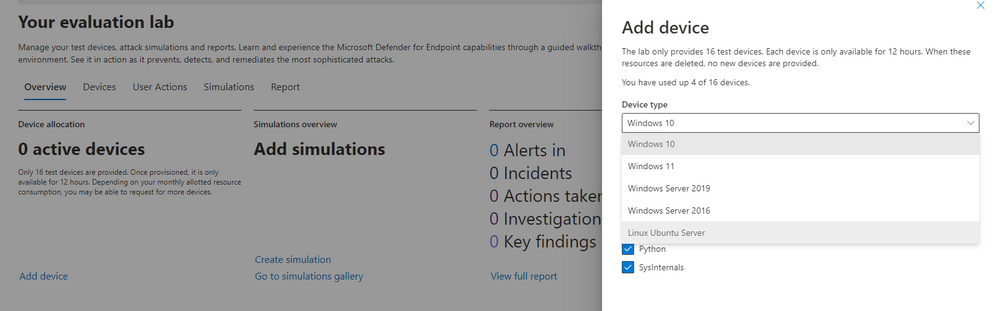
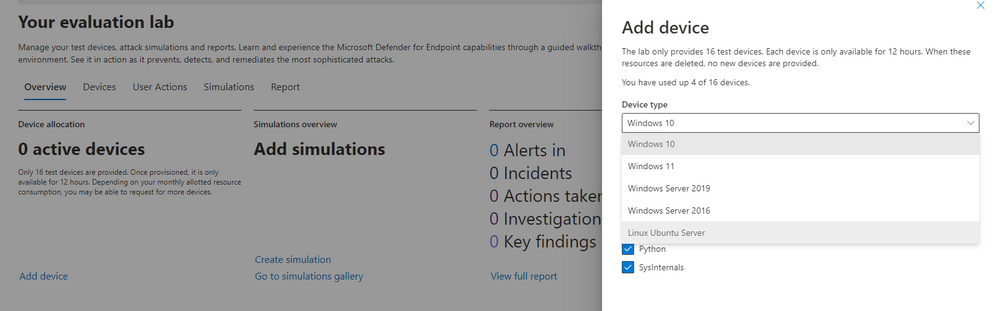
Microsoft Defender for Endpoint’s Evaluation Lab is an environment that allows security teams to seamlessly test their defense against threats. We are excited to share that the Evaluation Lab now supports adding Windows 11, Windows Server 2016, and Linux devices. In addition, we’d also like to announce a new partnership with Red Canary’s open-source simulation library, Atomic Red Team!
NOTE: Both updates are only available in the Microsoft 365 Defender portal at security.microsoft.com.
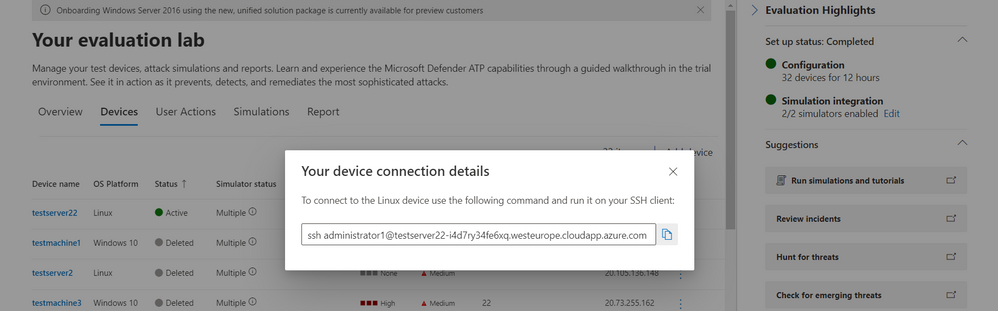
The evaluation lab now supports the following operating systems: Windows 10, Windows 11, Windows Server 2019, Windows Server 2016 and Linux (Ubuntu). To create a new device, simply select it within the “Add device” wizard. The new device will automatically be onboarded with no required additional steps.
Once created, you can connect to the device via RDP (Windows) or SSH (Linux). You can connect to a Linux device using any SSH client.
Powered by Red Canary, Atomic Red Team is an open-source library of tests that security teams can use to simulate adversarial activity in their environments. Atomic tests are simple – each test is mapped to a single MITRE ATT&CK® technique or sub-technique, most of them have no prerequisites, and many come with easy-to-use configuration and cleanup commands.
Evaluation Lab users can now use Atomic Red Team simulations to evaluate Microsoft Defender for Endpoint’s detection capabilities against both Windows and Linux threats. The simulations are provided as script files, so that security teams can choose to run them in the Evaluation lab or any other testing environment of their choice.
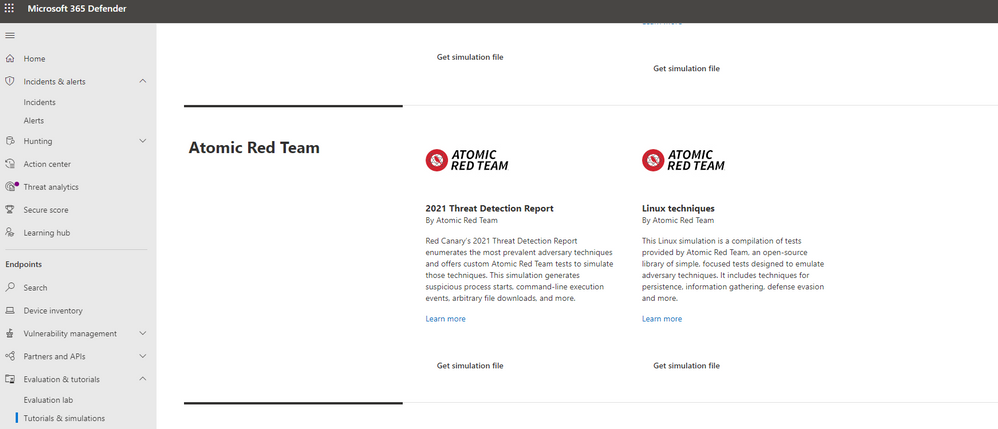
The first simulation, 2021 Threat Detection Report, executes tests according to Red Canary’s latest report of top Windows techniques associated with confirmed threats, as compiled from roughly 20,000 confirmed threats detected across customer environments.
The second simulation, Linux techniques, is a collection of simple tests compiled to allow security teams to evaluate Microsoft Defender for Endpoint’s detection capabilities against common Linux persistence, discovery, and defense evasion techniques.
We’re looking forward to you trying out the Evaluation Lab updates. Let us know your thoughts and feedback in the comments below or through the feedback tool in the portal!
Recent Comments