by Scott Muniz | Sep 17, 2020 | Uncategorized
This article is contributed. See the original author and article here.
Sharpen your skills and add some new superpowers in the Learning Zone at the all-digital Microsoft Ignite September 22-24. No matter where you are in your journey as a developer, the Learning Zone has something to help you expand your toolkit. And Ignite is perfectly priced for students—it’s free.
Get in the zone
The Learning Zone is filled with sessions and workshops to help you take your skill set to the next level. Here’s a taste of what’s waiting for you:
Intro to Tech Skills
Explore key topics to help you kick off a career in tech. We’ll cover a variety of interests, job roles, and Microsoft technologies.
Learn Workshops
Get hands-on with online workshops hosted by experts who walk you through a Microsoft Learn module.
Cloud Skills Challenge
Apply and expand your skills through interactive learning modules and earn a free Microsoft Certification exam. You might even win some prizes!
Launch yourself into tech
You’re considering a career in technology. Exciting! But where do you start? Intro to Tech Skills is your chance to explore different paths and find your way forward.
Be sure to catch the Careers in Tech panels, where tech professionals from a variety of backgrounds share their own experiences. You’ll get some insight into the areas of tech that might interest you, things to expect along your journey, and what the current state of recruiting looks like, including the roles that companies are hiring for. You’ll also learn more about how Microsoft technologies and learning resources can help you get started.
Intro to Tech Skills also includes sessions that cover development tools, cloud computing, programming languages, sustainability, and powerful ways to use data. Exploring a career in IT? Join us for sessions on topics like business management, productivity, collaboration with Microsoft Teams, and security with Microsoft 365.
Watch Student Ambassadors in action
You can even see how Microsoft Learn Student Ambassadors help to make Microsoft events unique and inclusive. Many of the Learning Zone sessions will be redelivered by Student Ambassadors in different time zones around the world, in a variety of languages. For example, Ambassadors are redelivering an intro to Python in Spanish and a session on green development in Hindi and French.
Learn, grow, and enter to win
Show off your skills and aim for a shot at the grand prize. The Microsoft Ignite Cloud Skills Challenge is made up of six individual subject-level challenges, each based on a collection of Microsoft Learn modules. You can participate in as many challenges as you’d like, and each one that you complete earns you more sweepstakes entries.
After you’ve completed your first challenge, you’ll earn a free Microsoft Certification exam. And if the sweepstakes drawing goes your way, you could win a chance for you and four of your friends to spend time with a key leader at Microsoft!
Registration for the Cloud Skills Challenge goes live on September 22. To be one of the first to know when the challenge begins, sign up for notifications.
Let’s go!
Ignite is coming up soon—register now so you don’t miss it! We’ll see you there.
by Scott Muniz | Sep 17, 2020 | Azure, Technology, Uncategorized
This article is contributed. See the original author and article here.
In this episode with Rohit Nayak, we cover how to deny public network access settings for Azure SQL Database. Customers can use this setting to block all public access via firewall rules and exclusively rely on private endpoint connections.
Watch on Data Exposed
Resources:
Minimal TLS version
Even more Networking videos
View/share our latest episodes on Channel 9 and YouTube!
by Scott Muniz | Sep 17, 2020 | Uncategorized
This article is contributed. See the original author and article here.
There are some use cases in the SIEM (Security Information and Event Management) world that require correlation with alerts from an expert system like Office 365 Advanced Threat Protection (ATP). Now you can use the built-in data connector to collect alerts from Office 365 Advanced Threat Protection into Azure Sentinel.
Office 365 Advanced Threat Protection (ATP) safeguards your organization against malicious threats posed by email messages, links (URLs) and collaboration tools. By ingesting Office 365 ATP alerts into Azure Sentinel, you can incorporate information about email and URL based threats into your broader risk analysis and build response scenarios accordingly.
The following types of alerts are supported with the data collector:
- A potentially malicious URL click was detected
- Email messages containing malware removed after delivery
- Email messages containing phish URLs removed after delivery
- Email reported by user as malware or phish
- Suspicious email sending patterns detected
- User restricted from sending email
These alerts can be seen by Office 365 customers in the Office Security and Compliance Center as well.
The Office 365 ATP data connector in Azure Sentinel uses the Automated Investigation and Response API and ingest only alerts which are triggered by automatic investigation in Office 365 ATP.
This blog post covers the required steps to ingest Office 365 ATP alerts into sentinel and how to use the ingested alerts.
How to Enable Office 365 ATP alert ingestion in Azure Sentinel
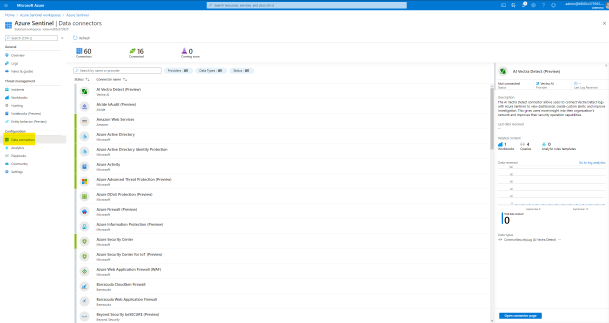
From the Azure Sentinel navigation menu, select Data connectors.

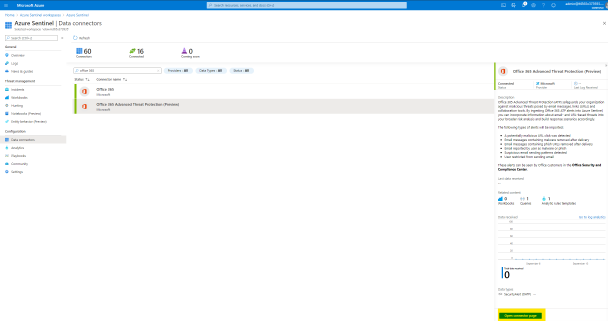
Select Office 365 Advanced Threat Protection (Preview) data connector, and then select Open Connector Page on the preview pane.
On the Office 365 Advanced Threat Protection (Preview) page, under Configuration select Connect.
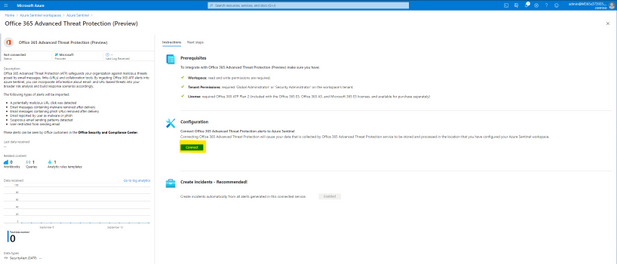
Select Next Steps and Create rule to enable and make adjustments for the relevant analytic rule template.
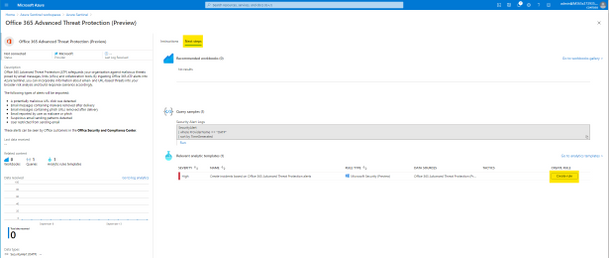
After successfully activation you will see the rule in your Active rules list in the Analytics page. This rule will make sure that all alerts generated by Office 365 ATP will also trigger an Incident in Azure Sentinel.
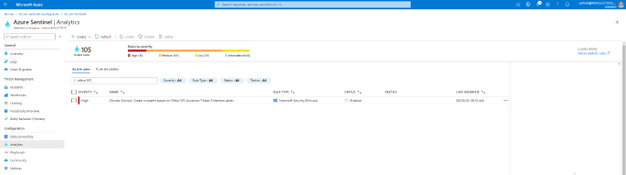
Now the Office 365 ATP alerts from your Office 365 tenant will be ingested into Azure Sentinel workspace and any generated alert in Office 365 ATP will also trigger an Incident in Azure Sentinel.
GIF Demonstration – How to enable the Office 365 ATP data connector
How to Use this Data
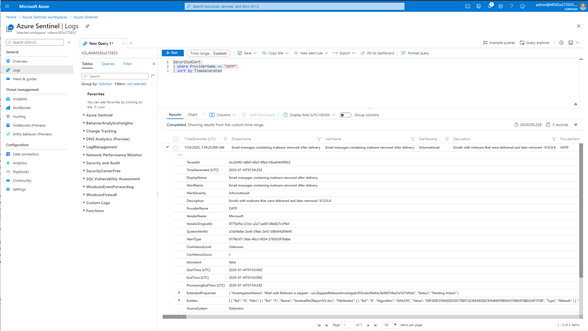
Once the data connector is functional you can query the Office 365 ATP alerts. The Office 365 ATP alerts will reside in the SecurityAlert table in Azure Sentinel workspace.
The following example query looks for the generated alerts for Office 365 ATP in Azure Sentinel.
SecurityAlert
| where ProviderName == “OATP”
| sort by TimeGenerated
GIF Demonstration – Query Office 365 ATP alerts in Azure Sentinel
GIF Demonstration – Sample Office 365 ATP Incident in Azure Sentinel
Summary
In this post I have shown how you can onboard Office 365 ATP alerts into Azure Sentinel and sample query how to use the data.
You can also contribute new connectors, workbooks, analytics and more in Azure Sentinel. Get started now by joining the Azure Sentinel Threat Hunters GitHub community and follow the guidance.
by Scott Muniz | Sep 17, 2020 | Azure, Technology, Uncategorized
This article is contributed. See the original author and article here.
Artificial intelligence (AI) opens doors into possibilities that might have seemed like science fiction only yesterday. Discover ways to improve your apps and take your development skills to the next level. Using AI, you can build solutions and advance technology in many fields, including healthcare, financial management, and environmental protection, to name just a few. Microsoft Azure provides easy-to-use services to help you get started.
Prove that you have the AI skills it takes to build a better world. Earning your certification in Azure AI Fundamentals can supply the foundation you need to build your career and demonstrate your knowledge of common AI and machine learning workloads—and how to implement them on Azure. Mastering the basics can help you jump-start your career and get ready to dive deeper into the other technical opportunities Azure offers.
The Azure AI Fundamentals certification validates your foundational knowledge of machine learning and AI concepts, along with related Azure services. You earn it by passing Exam AI-900: Microsoft Azure AI Fundamentals.
You can use Azure AI Fundamentals to prepare for other Azure role-based certifications, like Azure Data Scientist Associate or Azure AI Engineer Associate, but it’s not a prerequisite for any of them.
What are the prerequisites?
If you’re new to the cloud or just starting out with Azure, first choose Azure Fundamentals training and certification—find out how to Master the basics with Microsoft Certified: Azure Fundamentals.
The Azure AI Fundamentals certification is intended for candidates with both technical and non-technical backgrounds. Data science or software engineering experience are not required; however, some general programming knowledge or experience would be beneficial.
How can you get ready?
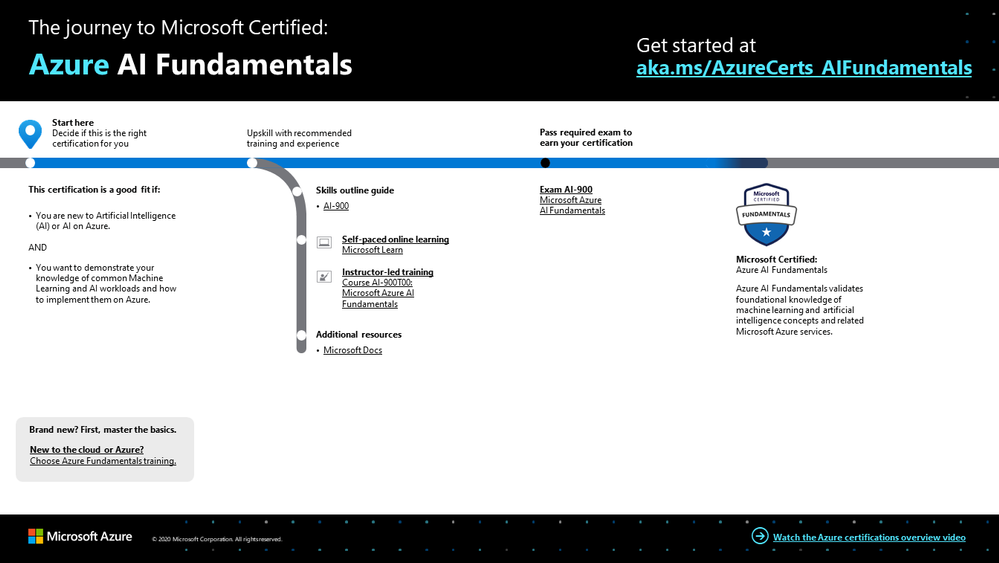
To help you plan your journey, check out our The journey to Microsoft Certified: Azure AI Fundamentals infographic. You can also find it in the resources section on the certification and exam pages, which contains other valuable help for Azure professionals.
 Azure AI Fundamentals certification journey
Azure AI Fundamentals certification journey
To map out your journey, follow the sequence in the infographic. First, decide whether this is the right certification for you.
Next, to understand what you’ll be measured on when taking Exam AI-900, review the skills outline guide on the exam page.
Sign up for training that fits your learning style and experience:
After you pass the exam and earn your certification, continue mastering the basics with Azure Data Fundamentals, level up with the Azure AI Engineer Associate certification or the Azure Data Scientist Associate certification, or find the right Microsoft Azure certification for you, based on your profession (or the one you aspire to).
It’s time to master the basics!
Use your Azure AI Fundamentals certification as a starting point to explore deeper training for Azure technologies and to chart your path forward. Whether you’re looking to advance your career or to jump-start a new one, the message is the same: establish your foundations. Earn your certification and open up new possibilities for your career and for turning your AI and machine learning ideas into solutions on Azure.
Related posts
Understanding Microsoft Azure certifications
Finding the right Microsoft Azure certification for you
Master the basics of Microsoft Azure—cloud, data, and AI

by Scott Muniz | Sep 17, 2020 | Uncategorized
This article is contributed. See the original author and article here.
There is something about creating which ignites curiosity in kids.
Regardless of gender, children have an innate appetite for learning what they do not know and perfecting what excites them.
Developer Technologies MVP Sara Chipps found her passion in computing at age 12. Sara recalls that she simply could not believe that her inputs made the computer call another computer – so beginning a lifelong interest in building and coding.
Today, Sara is part of the two-thirds of professional coders who report being under 18 when they start coding. At the same time, however, Sara is part of the less than one in four coders who are women. It is this juxtaposition which drives Sara to inspire young girls just like her towards following their interest in STEM.
Sara’s answer to the gender gap in tech is Jewelbots. Founded in 2014 with Brooke Moreland and Maria Paula Saba, Jewelbots’ original product was a smart friendship bracelet. This soon evolved into science craft kits for budding inventors in geology, chemistry, and electronics.
Now, tens of thousands of girls in more than thirty countries have become coders, chemists, and creators through Jewelbots.
“Our goal is, and always will be, to ignite the curiosity and drive that comes with being a builder,” Sara says. “Consuming technology is ubiquitous in today’s generation. However, true influence lies in being builders and creators of technology. Together, we can eliminate the fear and stigma that can come with being young and science forward.”
Young builders and creators of technology are clearly enjoying the limitless possibilities of Jewelbots. One young girl, for example, took the electronic science kit and sewed its LEDs into a shirt to depict a starry night sky. It is stories like this which continue to drive Sara despite working another full-time job.
“It is always rewarding because the excitement in their eyes truly makes it worth it,” Sara says.
“Every time we get a video or a picture of a girl making something awesome that she is proud of is what gets us going. We couldn’t do what we do without that every day.”
Importantly, direct interaction between the Jewelbots creators and the Jewelbots users informs product development.
“It’s also been a long time since I have been a 10-year-old girl, and imagining the things that drive them is tough,” Sara says. “So, I’ve seen it is best to talk to them and hear about the things that get them excited.”
Jewelbots is but one of Sara’s initiatives to encourage young girls towards STEM. In 2010, Sara co-founded Girl Develop It, a non-profit focused on helping more women become software developers.
Currently, Girl Develop It chapters are building strong, empowered communities in five cities across the US.
Likewise, Jewelbots grows from strength to strength. The creators look forward to expanding their science craft kits into biology and programming, and witnessing the output from the next generation of women scientists.
“We are excited to release more products and see more eyes light up as [girls] learn and make more things that ignite their imagination,” Sara says.
For more on Sara, check out Jewelbots or her Twitter @SaraJChipps


by Scott Muniz | Sep 17, 2020 | Uncategorized
This article is contributed. See the original author and article here.
Over the course of recent months, we have all embraced virtual events as an essential way to communicate and connect. Executive townhalls, employee training, digital conferences and customer engagements are just a few examples of popular scenarios. To simplify and accelerate your usage of Microsoft 365 for these scenarios we are delivering to you the Virtual Event Playbook. This comprehensive guidance provides you with information and tools to deliver seamless events easily and quickly for your audiences.
With Microsoft 365 you can focus on the content you are sharing and the attendee experience you want to create. Using Live Events, Microsoft Teams and other components of Microsoft 365 you can easily create experiences that will be meaningful to your audience and your business. We have organized the content by role and event phase to make it easy to find the information you need. To further support you we are also launching the Virtual Event forum within the Microsoft Technical Community so you can ask your questions, meet other event organizers, producers and IT professionals and participate in events with experts in the area.
This initial playbook covers the most common scenarios that we have seen and the guidance within it has been gathered from product engineering, field consultants, MVP’s, Microsoft Partners and others across our company. It is the comprehensive and official guidance from Microsoft for these services. We are currently working on additional modules for large scale custom events, device integration and industry specialties. We will be rapidly updating this content as new features become available.
More than anything we hope that you can use this guidance to continue connecting with the people that are important to your business, no matter where in the world they may be located. Events are no longer destinations. They are about the information shared and the connections nurtured through the available technology. Please use our resources, join the community, as always give us your feedback!
by Scott Muniz | Sep 17, 2020 | Azure, Technology, Uncategorized
This article is contributed. See the original author and article here.
Initial Update: Thursday, 17 September 2020 13:21 UTC
We are aware of issues within Log Analytics and are actively investigating. Some customers in Australia South East region may experience intermittent data access issues when accessing application data. Customers who have setup Log Search alerts in this region may also experience failures accessing alerts and action rules for the resources.
- Work Around: None
- Next Update: Before 09/17 15:30 UTC
We are working hard to resolve this issue and apologize for any inconvenience.
-Madhav
by Scott Muniz | Sep 17, 2020 | Uncategorized
This article is contributed. See the original author and article here.
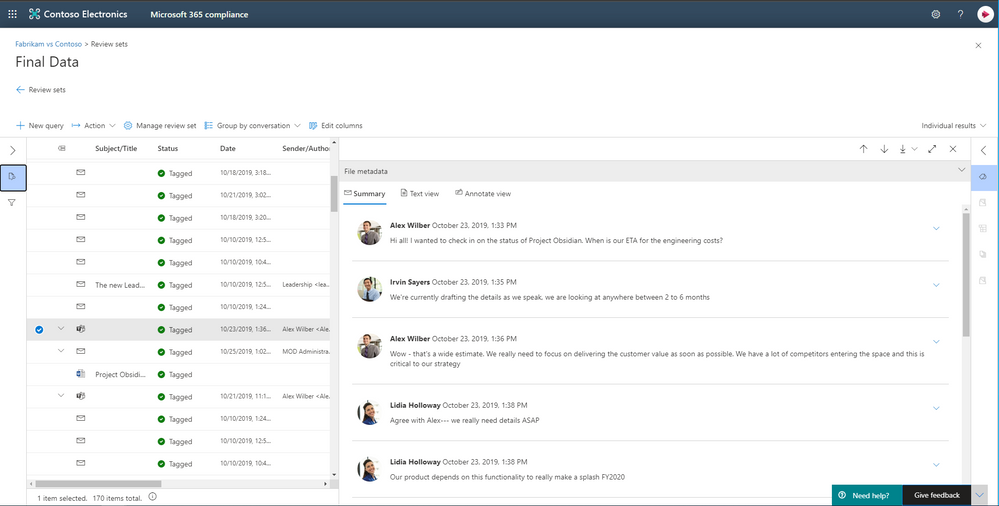
Today, more than ever, government organizations are facing increasing challenges associated with remote delivery of public services. The shift to support remote work has increased the need for government agencies to re-evaluate their security and compliance practices. Coupled with government employees accessing and sharing data remotely as well as collaborating in new ways using platforms like Microsoft Teams, government agencies need rich capabilities that help them efficiently discover relevant data. Public sector organizations are also under greater pressure to ensure they consistently meet industry compliance and security regulations. For example, many are required to respond quickly to Freedom of Information Act requests with relevant data.
Today we are excited to announce Advanced eDiscovery and Advanced Audit capabilities in Microsoft 365 are coming to Government Community Cloud (GCC), Government Community Cloud-High (GCC-H), and Department of Defense (DoD) environments. These new capabilities help organizations to efficiently respond to regulatory, legal, and forensic obligations with relevant data within the Microsoft 365 security and compliance boundary.
Discovering data where it lives with a more end–to–end eDiscovery solution
We often hear from customers that they are looking to reduce the complexity and cost of managing multiple solutions for their eDiscovery needs. In fact, according to Gartner, “by 2023, more than 70% of enterprise IT leaders will upgrade to an end-to-end e-discovery software.”
In April 2019, we delivered a new Advanced eDiscovery solution that supports the Electronic Discovery Reference Model by providing a more end-to-end workflow to identify, preserve, collect, process, review (early case assessment), and analyze data to help efficiently respond to legal and regulatory obligations or internal investigations.
To streamline the workflow, Advanced eDiscovery helps reduce the friction of identifying and collecting potential sources of relevant information by automatically mapping unique and shared data sources to the person of interest (custodian).
Additionally, native capabilities for Microsoft Teams, Yammer, SharePoint Online, OneDrive for Business, and Exchange Online further enhance data discovery by reconstructing Teams conversations instead of returning individual messages, or including the attachment and link in emails and Teams chats consistently without additional configuration.

Advanced eDiscovery also supports hundreds of non-Office 365 file types out of the box, and data connectors support additional third-party data sources such as Bloomberg, Facebook, and many more.
Intelligent, machine learning capabilities also help reduce the burden of review that traditionally happens one document at a time. Advanced eDiscovery provides a broad set of intelligent capabilities to help customers reduce and reduce large volumes of data to a relevant set. For example, an automatically generated query helps filter only for unique content by identifying near duplicates, which can help dramatically reduce data. You can learn more about this and other Advanced eDiscovery capabilities here.
Powering your forensic investigations with Audit
To help government customers understand the scope of a data breach and effectively respond to their regulatory, legal and internal obligations, we are also releasing Advanced Audit. Advanced Audit helps customers with their forensic investigations by providing access to additional audit events that are important to forensic investigations, extending audit log retention for up to 1 year, and offering faster access to management activity API.
With the new event in Advanced Audit, that means customers can understand when mail data was accessed using the “MailItemsAccessed” event. This new auditing action helps investigators determine the scope of compromise by identifying the specific mail items that may been accessed by a malicious attacker. It also helps organizations to defensibly assert that a specific piece of mail data was not compromised.
We also often hear from customers that they want to easily access historical audit log activities to support their forensic investigations. In fact, according to Ponemon Research, they estimate that the average time to identify and contain a data breach takes around 6 months. To help organizations conduct forensic investigations on audit log data beyond the default 90–days audit retention period, with Advanced Audit organizations can apply retention policy to their audit log data for up to one year. You can learn more about this and other Advanced Audit capabilities here.
Our commitment to our government and public sector customers
Moving forward, we are committed to delivering more capabilities in the Government Community Cloud, Government Community Cloud-High, and Department of Defense to ensure government entities can benefit from the compliance and risk management features within Microsoft 365.
The new features in Advanced eDiscovery and Advanced Audit will start rolling out to customer’s government cloud tenants in the coming weeks. To learn how government organizations are using technology to secure apps, devices, and data, read the “Digital Transformation in Government” e-book available at https://aka.ms/MicrosoftGovPlaybook. You can also find more information on how to use Microsoft 365 Compliance features in this video

by Scott Muniz | Sep 17, 2020 | Uncategorized
This article is contributed. See the original author and article here.

This LIVE online event will take place on Thursday 1st October
We’re only just starting to understand the true potential of technology at the intersection of Artificial Intelligence, MLOps (Machine Learning & DevOps), Cloud Computing and Edge Computing – but the possibilities are endless.
For the past few years, our AI Engineers, Data Scientists and Cloud Advocates at Microsoft have been working with the University of Oxford to further the development of these technologies and further the practical application of these in the world.
The collaboration has resulted in the University of Oxford offering specific courses on AI and Cloud/Edge computing – and on the development of the AI Edge Engineer Learning Path on Microsoft Learn.
The interplay between AI, cloud, and edge is a rapidly evolving domain. Currently, many IoT solutions are based on basic telemetry. The telemetry function captures data from edge devices and stores it in a data store. Our approach extends beyond basic telemetry. We aim to model problems in the real world through machine learning and deep learning algorithms and implement the model through AI and Cloud on to edge devices. The model is trained in the cloud and deployed on the edge device. The deployment to the edge provides a feedback loop to improve the business process (digital transformation).
In the AI Edge Engineering learning path, we take an interdisciplinary engineering approach. We aspire to create a standard template for many complex areas for deployment of AI on edge devices such as Drones, Autonomous vehicles etc. The learning path presents implementation strategies for an evolving landscape of complex AI applications. Containers are central to this approach. When deployed to edge devices, containers can encapsulate deployment environments for a range of diverse hardware. CICD (Continuous integration – continuous deployment) is a logical extension to deploying containers on edge devices. In future modules in this learning path, we may include other techniques such as serverless computing and deployment on Microcontroller Units.
The engineering-led approach underpins themes / pedagogies for engineering education such as
- Systems thinking
- Experimentation and Problem solving
- Improving through experimentation
- Deployment and analysis through testing
- Impact on other engineering domains
- Forecasting behaviour of a component or system
- Design considerations
- Working within constraints/tolerances and specific operating conditions – for example, device constraints
- Safety and security considerations
- Building tools which help to create the solution
- Improving processes – Using edge(IoT) to provide an analytics feedback loop to the business process to drive processes
- The societal impact of engineering
- The aesthetical impact of design and engineering
- Deployments at scale
- Solving complex business problems by an end-to-end deployment of AI, edge, and cloud.
Ultimately, AI, cloud, and edge technologies deployed as containers in CICD mode can transform whole industries by creating an industry-specific, self-learning ecosystem spanning the entire value chain. We aspire to design such a set of templates/methodologies for the deployment of AI to edge devices in the context of the cloud. In this learning path, you will:
- Learn about creating solutions using IoT and the cloud
- Understand the process of deploying IoT based solutions on edge devices
- Learn the process of implementing models to edge devices using containers
- Explore the use of DevOps for edge devices
Produced in partnership with the University of Oxford – Ajit Jaokar Artificial Intelligence: Cloud and Edge Implementations course
Now, we’re bringing together the team at Microsoft and the academics at University of Oxford that worked to build this learning path – and you can meet them and find out more about this free Learning Path, as well as some of the amazing applications of these technologies, at our event on 1st October.
Our event will take place LIVE on Microsoft Learn Live TV at the times below and there is no cost to attend.
Thursday 1st October 2020
| Mumbai |
Tel Aviv |
Berlin |
London |
NYC |
Seattle |
| 10.30pm |
8pm |
7pm |
6pm |
1pm |
10am |
by Scott Muniz | Sep 17, 2020 | Azure, Technology, Uncategorized
This article is contributed. See the original author and article here.
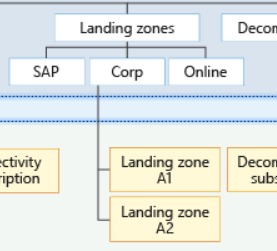
Building Azure landing zones means to leverage a scalable, modular approach to building out your environment based on a common set of design areas. Consequently, knowing and understanding the type of the application and workload (consequently called archetype) is important, as some of the Azure services do have specific requirements and platform dependencies.
The importance of the archetype also called out in the critical design areas, for example Red Hat OpenShift with regards to the DNS infrastructure.[1] Furthermore, this is also one of the reasons why you see different management groups below the landing zone management group.[2] In this specific case, which basically is the Contoso reference implementation, there are three specific landing zones: SAP, Corp and Online.
 Figure 1: Proposed management group structure with the Contoso reference implementation.
Figure 1: Proposed management group structure with the Contoso reference implementation.
From the Contoso reference implementation:[3]
- Corp Landing Zones will include all Virtual Networks that do not expose public endpoints and that require connectivity to on-premises, as well as connectivity to other Landing Zones.
- Online Landing Zones include all Virtual Networks that have internet-facing applications via an Azure Application Gateway (v2).
- SAP represents a workload that merits separation given the implied specialization.
How to build archetype landing zones?
In order to build landing zones for used archetype, you need to understand all the specific requirements and dependencies. Unfortunately, there is no single place where you can find this information, but you need to gather this information for every Azure service used.
However, a general recommendation is to leverage the Azure Architecture Center where you can find many useful information. One specific example I would like to mention is Azure Kubernetes Service (AKS) within the Architecture Center.[4]
In the AKS production baseline (reference architecture), a baseline infrastructure that deploys an AKS cluster is built, with focus on security. The baseline includes recommendations for networking, security, identity, management, and monitoring of the cluster. Consequently, it’s aligned with the critical design areas in Enterprise-Scale.
Let’s look at one of the covered topics, which is networking security. The documented ingress and egress traffic flow are aligned with the recommendation you will find in Enterprise-Scale.[7][8] To be specific, using an Application Gateway and Web Application Firewall (WAF) to protect ingress traffic and use a Firewall, deployed in the (managed) hub, to protect egress traffic. But something that you will not find mentioned specifically in Enterprise-Scale are the recommended Azure Policy add-on for AKS.[6] Although policy-driven governance is one design principles in Enterprise-Scale, at this juncture you may have to build a specific landing zone including all the required policy and also role configurations. This may include network, storage, RBAC, and others.
Thus, in a nutshell, and also my personal approach:
- Assess the required archetype-specific policyDefinition, policyAssignments, roleDefinitions and roleAssignments.
- Assess whether there are overlaps with existing landing zones (management groups) and policyAssignments and roleAssignments.
- Assess whether a new dedicated management group, including the policyAssignments and roleAssignments, does not make the management more complicated (no need to create the same assignments on multiple management groups).
The role of Well-Architected Framework
The AKS production baseline mentioned above also follows the Azure Well-Architected Framework.[5] Though this is an AKS specific use case, all the deployed applications should follow the Well-Architected Framework, and therefore should address:
- Cost optimization
- Operation excellence
- Performance efficiency
- Reliability
- Security
Or in other words: Enterprise-Scale provides the all important recommendations for the platform engineering, the Well-Architected Framework all important recommendations for applications and workloads.
[1] https://docs.microsoft.com/en-us/azure/cloud-adoption-framework/ready/enterprise-scale/network-topology-and-connectivity#configure-dns-and-name-resolution-for-on-premises-and-azure-resources
[2] https://docs.microsoft.com/en-us/azure/cloud-adoption-framework/ready/enterprise-scale/management-group-and-subscription-organization
[3] https://github.com/Azure/Enterprise-Scale/blob/main/docs/reference/contoso/Readme.md
[4] https://docs.microsoft.com/en-us/azure/architecture/reference-architectures/containers/aks/secure-baseline-aks
[5] https://docs.microsoft.com/en-us/azure/architecture/framework/
[6] https://docs.microsoft.com/en-us/azure/governance/policy/concepts/policy-for-kubernetes
[7] https://docs.microsoft.com/en-us/azure/architecture/reference-architectures/containers/aks/secure-baseline-aks#secure-the-network-flow
[8] https://docs.microsoft.com/en-us/azure/cloud-adoption-framework/ready/enterprise-scale/network-topology-and-connectivity#plan-for-inbound-and-outbound-internet-connectivity








Recent Comments