It’s one of the toughest challenges for organizations today: how to foster collaboration in a workplace that is more decentralized than ever, with people scattered across offices and locations.
Working together to move business forward is nothing new, but the way we collaborate is changing dramaticallyno longer confined to face-to-face time in a conference room or even a virtual web conference. The future of collaboration for all of us is about seamlessly switching between individual work and collaborative activities in the momentin context with the business application on the screen. That’s how information, ideas, and knowledge are shared in a natural way without breaking the flow of work. Everyone can collaborate as one business, everywhere.
In this blog series, we’ll explore blueprints to build a culture of collaboration with Microsoft Dynamics 365 and Microsoft Teams, with examples of how one organization has woven cross-team collaboration into its DNA.
Before we get started, we encourage you to register for our upcoming session at Microsoft Ignite, “Accelerate cross-organization collaboration with Dynamics 365 and Microsoft 365,” where we’ll announce and demonstrate new integrations between Dynamics 365 and Microsoft 365. We’re unveiling a lot of new features in the 30-minute session, so be sure to tune in.
More than meetings: collaboration redefined
Before unrolling the blueprints, we need to set the stage with an updated look at how people collaborate in the workplace.
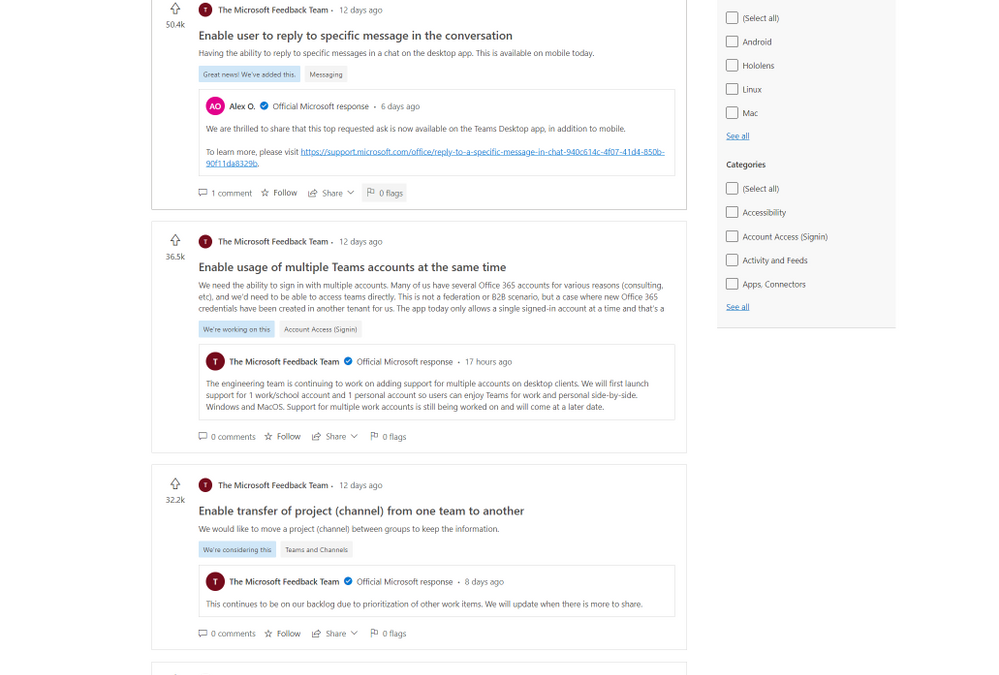
Collaboration needs no introduction. Many of us spend the day collaborating synchronouslylive, in real-timein-person or in online meetings, one-on-one or in groupswhere we plan, review, share, co-create content, brainstorm. All the familiar activities that have traditionally defined collaboration.
Real-time collaboration is just one way we work together. We also collaborate asynchronously, with ideas and interactions contributed over email or in response to a chat message as schedules permit, rather than in real-time.
![Infographic showing elements of collaboration]()
Whether working together synchronously or asynchronously, collaboration should feel natural and seamless, without breaking your focus. That’s why the business applications you use need to integrate collaborative experiences nativelyso that any person or information you need is immediately available in the moment.
At Microsoft, we are prioritizing collaboration across the applications your organization uses every day, such as Dynamics 365 and Microsoft Teams. Collaborative apps ensure people engage and interact with each other naturally and spontaneously, in context with the task at hand. That’s the key to ensuring everyone achieves more together.
Introducing the blueprints for collaboration
Let’s take a closer look at one day in a typical organization with people scattered across headquarters, home offices, retail stores, and beyond.
A manufacturer of electric bicycles produces a growing line of brands sold online, in several flagship retail stores, and through dozens of retailers across North America. Many departments across the company rely on Dynamics 365 and Microsoft 365including Microsoft Teams and Office applicationsto keep up with demand for the company’s product line. Together, these seamlessly integrated applications keep the business moving in high gear by breaking down all the silos in the business, between data sources, people, processes, and insights.
Marketing
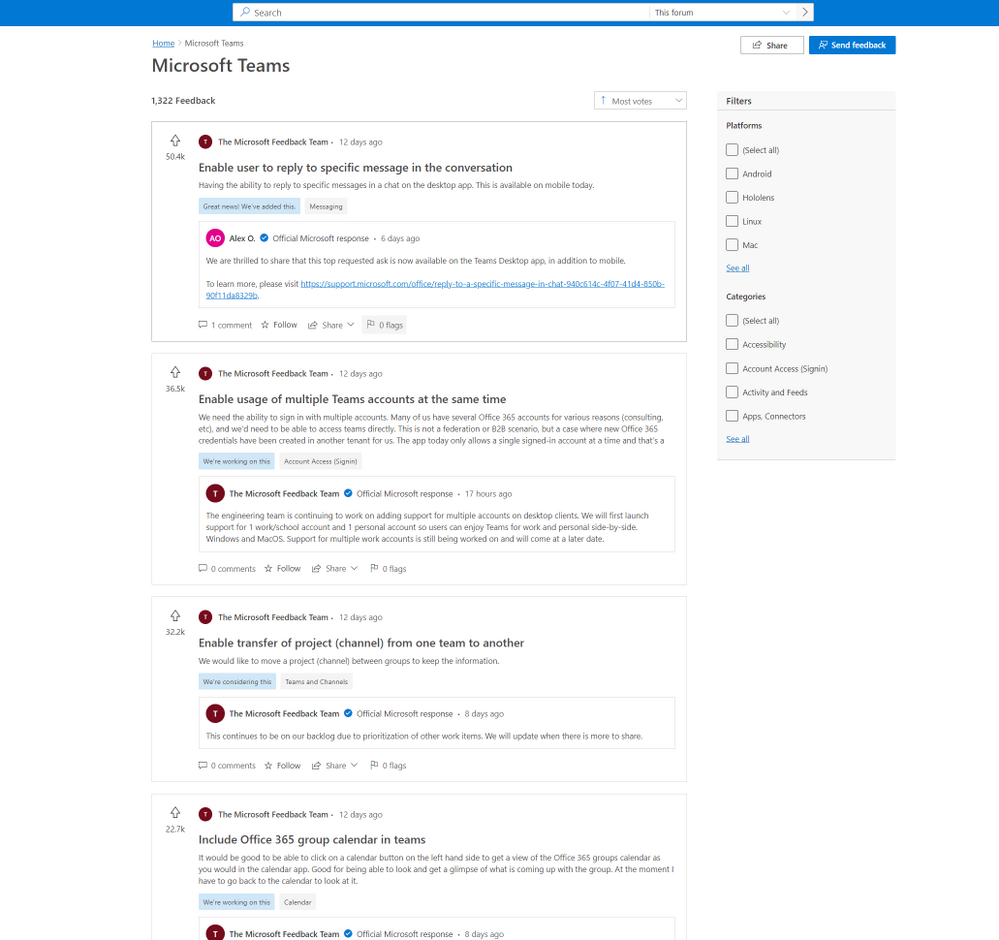
The marketing team hosts monthly webinars for prospective retail partners that showcase product innovation and partner incentives. In the past, planning, hosting, and promoting the presentations was a time and resource-intensive effort for two marketing managers and a third-party production vendor.
Today, one marketing manager, Taylor, runs the entire show.
Taylor uses Microsoft PowerPoint, Microsoft Teams, and Dynamics 365 to produce, host, promote and engage attendees for each monthly webinar. At each step, he can pull in experts when needed right from within the application on the screen, without breaking the flow of the task at hand. The entire marketing team also has a clear view of engagements that the sales team is working on and can recommend or prioritize marketing tactics based on the sales stage for each engagement.
After the event, Taylor follows up with the event participants by sending personalized emails and orchestrating customer journeys using Dynamics 365 Marketing. For this marketing team, webinars aren’t just another marketing tacticthey are one of the best performing tactics to expand its retail footprint across North America. Dozens of qualified leads are delivered to the sales teama seamless hand-off between Dynamics 365 Marketing and Dynamics 365 Sales that lets the sales team rapidly nurture, further qualify and convert opportunities to customers.
![Infographic showing how to produce and host webinars]()
Sales
The marketing webinars are a hit. Leads are flowing in; so many, in fact, that the sales team has been inundated, including opportunities ready for a proposal. It’s a good problem to have, but one that would traditionally lead to a push for quantity over quality.
With Dynamics 365 and Microsoft Teams, the sales team doesn’t need to compromise on detailsfrom the proposed solution to pricingthat can make or break a deal. Right from within Dynamics 365, a sales manager can reach out to experts across the company and quickly get the guidance and information needed to create an unbeatable offer.
Joanna, a sales manager, gets started by browsing a prioritized list of opportunities in Dynamics 365 Sales. Since the marketing and sales teams both use Dynamics 365, they can access a single source of trutha unified record of leads and customers, at every stage of the journey, from the very first engagement to purchase, service, and renewals.
Joanna has been nurturing a warm lead, a prospective customer ready for a quote. With familiar Microsoft Teams capabilities natively integrated in Dynamics 365 Sales, it’s a breeze to find the right people and information needed to create a quote custom-fit for the prospect’s unique challenges and needs.
In our blueprint for team selling (below) Joanna can see who has been engaging with the prospect or working similar deals, as well as any subject matter experts who can offer insights into the prospect’s business or industry. People and related documents discussed on Teams chats and channels are visible right from the customer record within Dynamics 365 Sales.
As Joanna mobilizes the team, she can share the opportunity record in Dynamics 365 to anyone in the company within a Teams chat. Without leaving Teamsand without the need for Dynamics 365anyone on the organization’s Teams domain can directly view details in the shared recordfrom contact details to engagement history, purchases, account notes, and more. They can see the very latest context needed to provide Joanna with informed and relevant guidance.
With collaboration, sharing, and communication capabilities integrated into Dynamics 365, It no longer takes hours or days to hunt down the right people and information across email chains, meetings, and callscollaborative activities are brought to Joanna front and center in the application she depends on to move deals through the funnel.
![Infographic showing how to develop a proposal]()
Once she shares the quote with the customer, it’s just as easy to bring together her team of experts and the prospective customer on a Teams meetingagain, right from within Dynamics 365 Sales. Together, they walk the prospect through quotes and address any questions and concerns. Conversation intelligence transcribes the call and provides meaningful insights and analyzes content, sentiment, and behavioral stylesuch as competitors and keywords that the prospect mentions during the call. AI-guided live feedback and suggestions can help sellers adjust their sales pitch, as well as provide managers with a way to track team performance and provide valuable coaching to help boost customer satisfaction.
The result: an unbeatable proposal, insights to optimize future quotes and sales processes, and plenty of time in the week to convert more webinar attendees.
Up next: blueprints to elevate collaboration across retail and customer service
In the next installment, we’ll share blueprints to elevate collaboration with Microsoft Dynamics 365 and Microsoft Teams on the customer frontlines, from retail storefronts to customer service. Until then, we invite you to explore the four essentials to collaborate as one business, everywhere and take a behind-the-scenes look at two companies reinventing how people collaborate across the organization.
The post A blueprint for cross-organization collaboration: marketing and sales appeared first on Microsoft Dynamics 365 Blog.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.




Recent Comments