
by Contributed | Mar 18, 2021 | Dynamics 365, Microsoft 365, Technology
This article is contributed. See the original author and article here.
Projects used to be a discrete subset of work people did every day, but the way we work is transforming. Organizations and individuals have taken incredible leaps to implement digital innovations to help employees work better together now that so many are working from home. Today, all work is project work, and everyone works on projects. Projects can range from ad hoc, involving a couple of people, to years’ long efforts and entire portfolios. “Today, all work is project work, and everyone works on projects.” Howard Crow, Head of Product for Microsoft Planner and Microsoft Project The transformation of projects from discrete activities to the work each of us does every day requires new approaches and a new generation of tools that can span an organization and meet people where they are working. To answer these challenges, Microsoft’s vision is connected project experiences that are simple enough for everyone to use and powerful enough to be a catalyst for business success across the world’s largest organizations. In a time when projects are the unifying thread woven throughout the fabric of modern work, Microsoft delivers the platform, tools, and capabilities teams need to eliminate complexity, clarify priorities, stay on top of tasks, and work together to achieve key strategic objectives. Our solutionsincluding Microsoft Planner, Microsoft Project, and Microsoft Dynamics 365 Project Operationsprovide the end-to-end management capabilities that teams and organizations of all sizes need to tackle projects of every level of complexity. Cut through complexity with connected project experiences Cutting through complexity starts with visibility, and Microsoft’s connected project experiences are designed to help you organize and view projects, schedules, and tasksor dive more deeply into all the details. They provide intelligent, data-driven operational insights so you can address emerging issues before they become problems and seize new opportunities quickly. They’re built so it is easy to take advantage of flexible solutions that map to your business processes and adapt to the way your teams work best. Microsoft’s connected project experiences help provide clear expectations about budgets and timelines, enable you to set your teams up to drive strategic outcomes that improve customer satisfaction, increase profitability, and reduce costs. Reducing complexity and increasing clarity will help you take an important step forward toward achieving the kinds of successful results that lead to happier, more engaged teams. We also know that solving today’s complexity challenges alone isn’t enough. Long-term business success is also built on a modern technology platform that supports a culture of innovation and offers the flexibility to grow and adapt. Microsoft’s connected project experiences also deliver a unified approach that brings together all your company’s data, to help you uncover insights. With simplified IT management and the security of Microsoft’s trusted cloud to protect your processes and intellectual propertyPlanner, Project, and Dynamics 365 Project Operationsmark the beginning of a new era of project experiences that will transform how teams and organizations manage their work. Join us for Reimagine Project Management with Microsoft Learn more about the connected project experience at Reimagine Project Management with Microsoft, now available as a free, on-demand event. You’ll learn the latest on Microsoft Planner, Microsoft Project, and Dynamics 365 Project Operationsthree solutions built to address and solve for your unique business needs. Although the event is completely digital, you’ll have opportunities to connect with Microsoft experts, technology partners, and peers to expand your network. Register for Reimagine Project Management with Microsoft to: Discovernew features and best practices from live demos and product walkthroughs with more than six hours of on-demand content. Connect with other attendees through round tables and board rooms. Don’t miss out on an opportunity to find the Microsoft connected project experience to equip your organization with everything needed to cut through complexity and successfully complete your project. Register now and watch on demand
The post Reimagine project management at our free digital event appeared first on Microsoft Dynamics 365 Blog.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.

by Contributed | Mar 18, 2021 | Technology
This article is contributed. See the original author and article here.
“We all deserve a seat at the table, we all have something important and unique, our own skills and perspectives are important to the development of our communities.”
This is the message from Data Platform MVP Mico Yuk and Developer Technologies MVP Diana Rodriguez as they each mentor women around the world about equality in tech. Here are their stories.
Mico is an accomplished public speaker and mentors analytics leaders from Fortune 1000 companies like Alimed, Mobile Mini and Intel through her BI Data Storytelling Mastery Accelerator Workshop VIP program. Unfortunately, it remains a sad truth that women and other underrepresented folks continue to face barriers to progressing in their tech careers, Mico says.
“Whether or not it’s apparent, there are many Fortune 1000 companies (especially the older ones) that still suffer from old-school, non-female-friendly male leadership,” Mico says.
“In addition, there are biases that exist. If you’re a black or brown female, you must come from a good school who got here because we need ‘diversity’. There is more of a tolerance than an acceptance, and it is felt.”
“It’s disgusting and I’ve seen it in and out of board rooms for the last 10 years. I’ve concluded that until this generation of decision-makers retires, this dominant underlying attitude will not be eliminated.”
Until that time comes, Mico believes the fastest and most effective solution will be to push for an agenda that focuses on more leadership that “looks and thinks like us.” Mentorship is vital to supporting women until then, Mico says.
“Mentorship is very much like therapy where it provides a ‘non-judgmental’ avenue to talk … with someone who has been there, done that, and is still thriving,” she says.
Likewise, Diana is inspired to encourage women that there is “room for everybody in the tech ecosystem.” With mentorship efforts ranging from Uruguay to Malaysia, Diana wants to inspire her students to achieve their potential and beyond.
“Sadly, there’s still so much ignorance to combat,” Diana says. “But it can be combated with knowledge, access to tools, learning resources, mentoring, job opportunities, and a welcoming environment.
“And, finally, getting rid of these toxic behaviours that reward unhealthy practices like working unreasonable hours, toxic masculinity, gender bias, and more.”
Diana is the education director of frontendfoxes, a charity that creates and hosts workshops to teach front-end technologies to women in an engaging way. The group – which is made for women, by women – is preparing to begin three cohorts of a free bootcamp in April.
Access to education, platforms and content help women to overcome the current barriers of tech, Diana says. “As a mentor, I like to pave the road for my mentees to succeed. I’m not the oracle and I may not have all answers, but I give my very best!
“It’s a learning experience for me, too. I like to see it as a win-win because I am sharing knowledge from a collection of personal experiences as a way to pave their success. At the same time, I gain new perspectives and insight, different and innovative ways to approach problems and think of solutions through code.”
For more on both mentoring efforts, visit Mico’s Twitter @MicoYuk and Diana’s GitHub.

by Contributed | Mar 18, 2021 | Technology
This article is contributed. See the original author and article here.
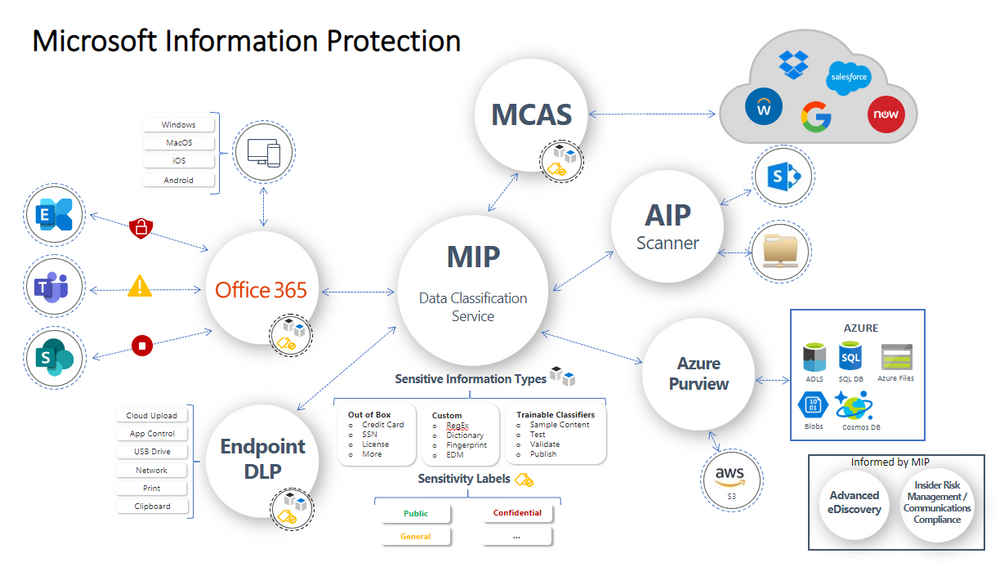
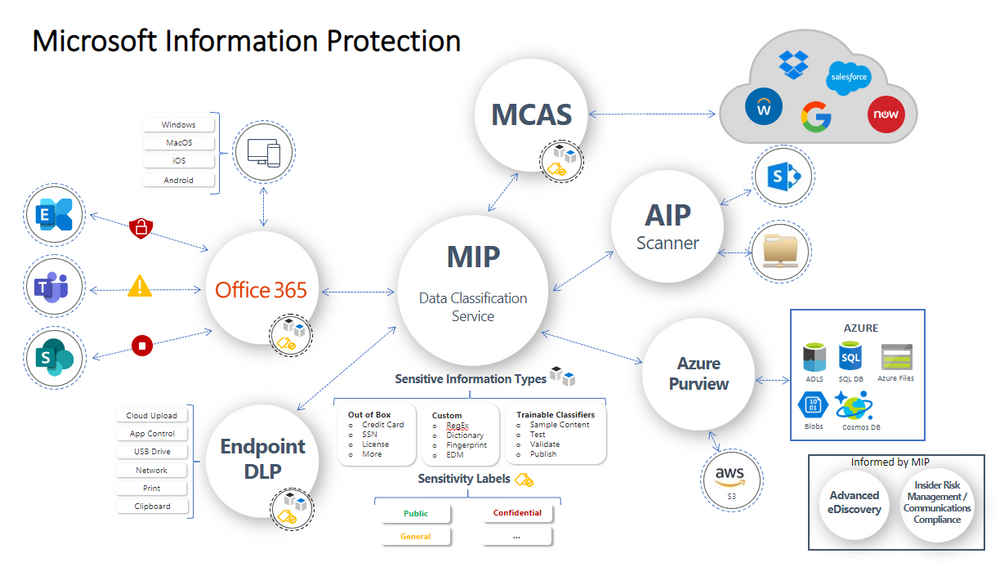
This webinar covers how to extend the capability of Microsoft Information Protection (MIP) by utilizing various third party solutions developed by Secude, Synergy Advisors, Cognni and Netwoven.
Resources:
Microsoft Information Protection (MIP) in Microsoft 365
Learn about sensitive information types
This webinar was presented on February 10, 2021, and the recording can be found here.
Attached to this post are:
- The FAQ document that summarizes the questions and answers that came up over the course of both Webinars.
- A PDF copy of the presentation.
Thanks to those of you who participated during the two sessions and if you haven’t already, don’t forget to check out our resources available on the Tech Community.
Thanks!
@Robin_Baldwin on behalf of the MIP and Compliance CXE team
by Contributed | Mar 18, 2021 | Technology
This article is contributed. See the original author and article here.
The Microsoft Federal Collaboration & Cybersecurity Summit is a FREE half-day virtual event designed to advance U.S. Federal agencies collaboration and cybersecurity initiatives.
Our theme this year is “Transforming Intergovernmental Collaboration and Cybersecurity.”
Leadership resiliency, today, in the face of unprecedented challenges is paramount. The high stakes of cybersecurity continue to increase and evolve – with no end in sight. The frequency of cybersecurity threats and their level of sophistication have and will continue to grow; and as the threat of cyber-breaches increase, so too does the need for intergovernmental collaboration, communications, and data sharing.
We are bringing together executives and leaders from the U.S. Federal agencies to deliver key insights, lessons learned, and practical guidance on:
- Advancing Cybersecurity in the Federal Government
- Cultural transformations that drive new ways of working and digital modernization
- Breaking down silos to facilitate partnership with industry and academia
- Connecting with people and information from the office or in the field to securely share and protect sensitive information
Microsoft can help Federal organizations respond, rebound, re-imagine modern collaboration, and accelerate the adoption of modern security compliance. During the Summit, Microsoft experts will speak to specific Microsoft 365, Microsoft Teams, Azure, and security capabilities that will allow you to accelerate delivery on your mandates and actively respond to real-world issues in the current environment.
We invite you and your team to join us at the Summit for live fireside chat, executive panel discussions, breakout sessions, and more….
Be on the lookout for an official invitation by the end of March!
This event is not open to the public.
If you have any questions, please contact us at MSFTFedCollab@service.onmicrosoft.com.
by Scott Muniz | Mar 18, 2021 | Security, Technology
This article is contributed. See the original author and article here.
Summary
This Alert announces the CISA Hunt and Incident Response Program (CHIRP) tool. CHIRP is a forensics collection tool that CISA developed to help network defenders find indicators of compromise (IOCs) associated with activity detailed in the following CISA Alerts:
Similar to Sparrow—which scans for signs of APT compromise within an M365 or Azure environment—CHIRP scans for signs of APT compromise within an on-premises environment.
In this release, CHIRP, by default, searches for IOCs associated with malicious activity detailed in AA20-352A and AA21-008A that has spilled into an on-premises enterprise environment.
CHIRP is freely available on the CISA GitHub Repository. Note: CISA will continue to release plugins and IOC packages for new threats via the CISA GitHub Repository.
CISA advises organizations to use CHIRP to:
- Examine Windows event logs for artifacts associated with this activity;
- Examine Windows Registry for evidence of intrusion;
- Query Windows network artifacts; and
- Apply YARA rules to detect malware, backdoors, or implants.
Network defenders should review and confirm any post-compromise threat activity detected by the tool. CISA has provided confidence scores for each IOC and YARA rule included with CHIRP’s release. For confirmed positive hits, CISA recommends collecting a forensic image of the relevant system(s) and conducting a forensic analysis on the system(s).
If an organization does not have the capability to follow the guidance in this Alert, consider soliciting third-party IT security support. Note: Responding to confirmed positive hits is essential to evict an adversary from a compromised network.
Click here for a PDF version of this report.
Technical Details
How CHIRP Works
CHIRP is a command-line executable with a dynamic plugin and indicator system to search for signs of compromise. CHIRP has plugins to search through event logs and registry keys and run YARA rules to scan for signs of APT tactics, techniques, and procedures. CHIRP also has a YAML file that contains a list of IOCs that CISA associates with the malware and APT activity detailed in CISA Alerts AA20-352A and AA21-008A.
Currently, the tool looks for:
- The presence of malware identified by security researchers as TEARDROP and RAINDROP;
- Credential dumping certificate pulls;
- Certain persistence mechanisms identified as associated with this campaign;
- System, network, and M365 enumeration; and
- Known observable indicators of lateral movement.
Network defenders can follow step-by-step instructions on the CISA CHIRP GitHub repository to add additional IOCs, YARA rules, or plugins to CHIRP to search for post-compromise threat activity related to the SolarWinds Orion supply chain compromise or new threat activity.
Compatibility
CHIRP currently only scans Windows operating systems.
Instructions
CHIRP is available on CISA’s GitHub repository in two forms:
-
A compiled executable
-
A python script
CISA recommends using the compiled version to easily scan a system for APT activity. For instructions to run, read the README.md in the CHIRP GitHub repository.
If you choose to use the native Python version, see the detailed instructions on the CHIRP GitHub repository.
Mitigations
Interpreting the Results
CHIRP provides results of its scan in JSON format. CISA encourages uploading the results into a security information and event management (SIEM) system, if available. If no SIEM system is available, results can be viewed in a compatible web browser or text editor. If CHIRP detects any post-compromise threat activity, those detections should be reviewed and confirmed. CISA has provided confidence scores for each IOC and YARA rule included with CHIRP’s release. For confirmed positive hits, CISA recommends collecting a forensic image of the relevant system(s) and conducting a forensic analysis on the system(s).
If you do not have the capability to follow the guidance in this Alert, consider soliciting third-party IT security support. Note: Responding to confirmed positive hits is essential to evict an adversary from a compromised network.
Frequently Asked Questions
- What systems should CHIRP run on?
Systems running SolarWinds Orion or believed to be involved in any resulting lateral movement.
- What should I do with results?
Ingest the JSON results into a SIEM system, web browser, or text editor.
- Are there existing tools that CHIRP complements and/or provide the same benefit as CHIRP?
-
Antivirus software developers may have begun to roll out detections for the SolarWinds post-compromise activity. However, those products can miss historical signs of compromise. CHIRP can provide a complementary benefit to antivirus when run.
-
CISA previously released the Sparrow tool that scans for APT activity within M365 and Azure environments related to activity detailed in CISA Alerts AA20-352A and AA21-008A. CHIRP provides a complementary capability to Sparrow by scanning for on-premises systems for similar activity.
- How often should I run CHIRP?
CHIRP can be run once or routinely. Currently, CHIRP does not provide a mechanism to run repeatedly in its native format.
- Do I need to configure the tool before I run it?
No.
- Will CHIRP change or affect anything on the system(s) it runs on?
No, CHIRP only scans the system(s) it runs on and makes no active changes.
- How long will it take to run CHIRP?
CHIRP will complete its scan in approximately 1 to 2 hours. Duration will be dependent on the level of activity, the system, and the size of the resident data sets. CHIRP will provide periodic progress updates as it runs.
- If I have questions, who do I contact?
For general questions regarding CHIRP, please contact CISA via email at central@cisa.dhs.gov or by phone at 1-888-282-0870. For reporting indicators of potential compromise, contact us by submitting a report through our website at https://us-cert.cisa.gov/report. For all technical issues or support for CHIRP, please submit issues at the CISA CHIRP GitHub Repository.
Revisions
March 18, 2021: Initial Publication
This product is provided subject to this Notification and this Privacy & Use policy.



Recent Comments