This article is contributed. See the original author and article here.
This installment is part of a broader series to keep you up to date with the latest features in Azure Sentinel. The installments will be bite-sized to enable you to easily digest the new content.
NOTE: Microsoft 365 Defender was formerly known as Microsoft Threat Protection or MTP. Microsoft Defender for Endpoint was formerly known as Microsoft Defender Advanced Threat Protection or MDATP.
We’re very pleased to announce that the public preview of the new Microsoft 365 Defender connector is now available, alongside a new Azure Sentinel benefit for Microsoft 365 E5 customers! The M365 Defender connector lets you stream advanced hunting logs – a type of raw event data – from Microsoft 365 Defender into Azure Sentinel. Click here to look at Microsoft documentation page on this connector.
With the integration of Microsoft Defender for Endpoint (MDATP) into the Microsoft 365 Defender security umbrella, you can now collect your Microsoft Defender for Endpoint advanced hunting events using the Microsoft 365 Defender connector, and stream them straight into new purpose-built tables in your Azure Sentinel workspace. These tables are built on the same schema that is used in the Microsoft 365 Defender portal, giving you complete access to the full set of advanced hunting logs, and allowing you to do the following:
- Easily copy your existing Microsoft Defender ATP advanced hunting queries into Azure Sentinel.
- Use the raw event logs to provide additional insights for your alerts, hunting, and investigation, and correlate events with data from additional data sources in Azure Sentinel.
- Store the logs with increased retention, beyond Microsoft Defender for Endpoint or Microsoft 365 Defender’s default retention of 30 days. You can do so by configuring the retention of your workspace or by configuring per-table retention in Log Analytics.
How to enable the Microsoft 365 Defender connector in Azure Sentinel
Prerequisites
- You must have a valid license for Microsoft Defender for Endpoint, as described in Set up Microsoft Defender for Endpoint deployment.
- Your user must be assigned the Global Administrator role on the tenant (in Azure Active Directory).
- From the Azure Sentinel navigation menu, select Data connectors.
- Select Microsoft 365 Defender from the data connectors gallery, and then select Open Connector Page on the preview pane.
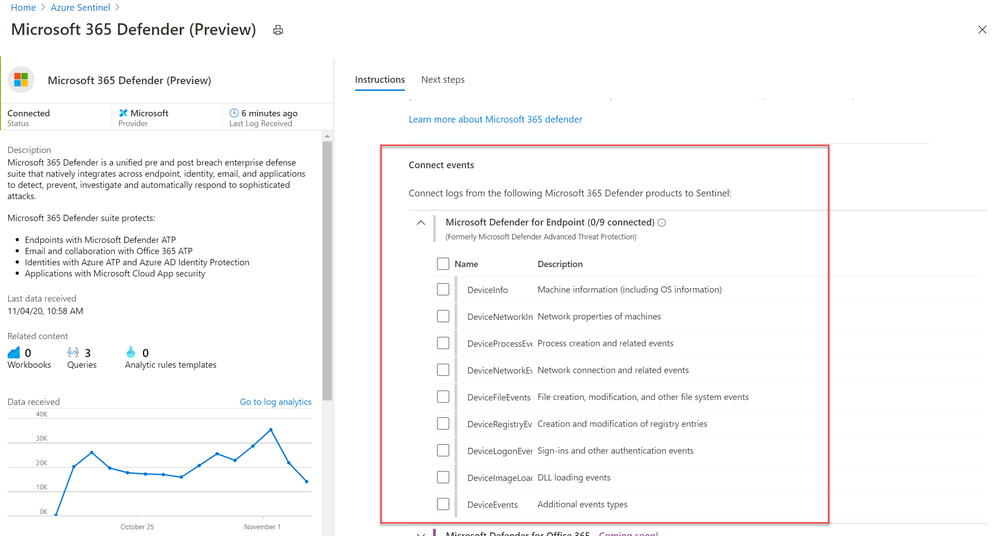
- On the Microsoft 365 Defender connector page, under Connect events and Microsoft Defender for Endpoint tick the boxes for the types of logs you would like to be sent to Azure Sentinel and select Apply Changes.
And that’s it! You will now have Microsoft Defender for Endpoint logs connected to your Sentinel workspace.
A new Azure Sentinel benefit for Microsoft 365 E5 customers
With this new offer, you can take advantage of end-to-end integrated security and save significant costs when ingesting Microsoft 365 data into Azure Sentinel. From November 1, 2020 through May 1, 2021, Microsoft 365 E5 and Microsoft 365 E5 Security customers can receive a data grant of up to 100 MB per user/month to ingest Microsoft 365 data, including Microsoft 365 advanced hunting data (including Microsoft Defender for Endpoint logs) described in this blog. For more details, please visit the M365 E5 Sentinel benefit website.
Get started today!
Try out the new connector and let us know your feedback using any of the channels listed in the Resources.
You can also contribute new connectors, workbooks, analytics and more in Azure Sentinel. Get started now by joining the Azure Sentinel Threat Hunters GitHub community!
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.


Recent Comments