This article is contributed. See the original author and article here.
If you’re facing issues with Function App key creation, this document has a few troubleshooting tips that could help you fix it.
First, ensure you’ve reviewed these docs related to Function App storage connections:
- https://docs.microsoft.com/en-us/azure/azure-functions/storage-considerations#storage-account-requirements
- https://docs.microsoft.com/en-us/azure/azure-functions/functions-recover-storage-account
Symptom:
Host level and Function level Key creation failure in Function Apps
Issue verification:
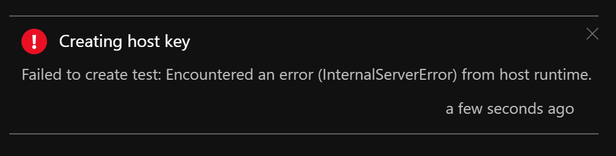
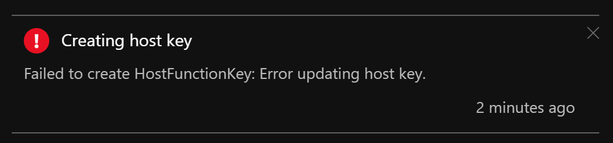
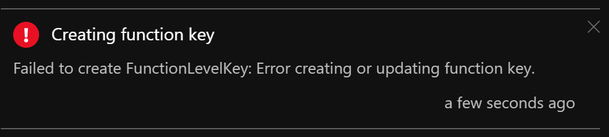
Portal – When your Function App is unable to create host level or function level keys, you may see these error messages:
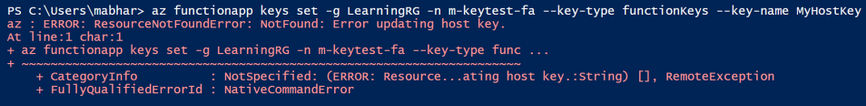
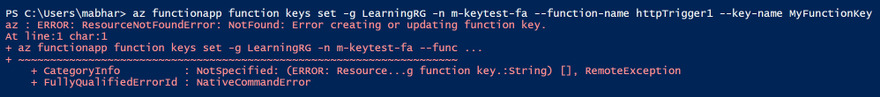
AzCLI – If key creation fails with AzCLI, the error messages are as below:
In addition to this, Function execution could also be returning HTTP 401 (HTTP 500) in some cases.
Troubleshooting:
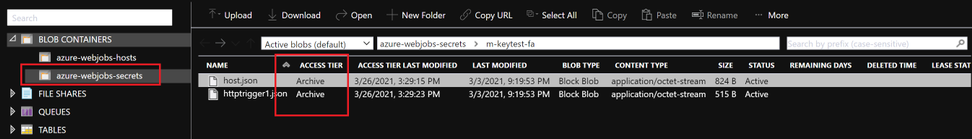
Function App keys are placed in the azure-webjobs-secrets folder in Blob Container. If this folder is missing, this could mean that the Function App is unable to connect to the storage account referenced by the Function App Application Setting “AzureWebJobsStorage”. This could happen either because of a network misconfiguration or because of an issue on the storage side. We will explore both these causes below.
- Know the outbound Connectivity path for your Function App: Ensure the storage account referenced by the Function App Application Setting “AzureWebJobsStorage” is reachable from the Function App.
- Does the storage account allow access to all networks? If not, what path do you expect the Function App to take to reach the Storage? (Internet/Virtual Network?)
- If you want the Function App to reach the storage account via its public IP, ensure the storage account allows all the IPs listed under outbound IPs in the Function App’s properties blade.
- If your App is integrated with a Virtual Network, ensure this subnet is allowed on the storage account firewall.
- Missing WebJobs secrets folder?
- Once you ensure network connectivity is present between the Function App and Storage, you should be able to see the azure-webjobs-secrets folder under Blob containers as seen below. If you don’t see this folder, it could be because of a missing Vnet integration.
- I’ve seen cases where the Vnet & Subnet are allowed on the Storage Account Firewall but customers sometimes forget to actually integrate the App with the Vnet. This causes the secrets folder to be absent on the storage.
- Also, ensure Service Endpoints/Private Endpoints are configured correctly.
- Erroneous storage connection string?
- Ensure the correct storage connection string from here: https://docs.microsoft.com/en-us/azure/storage/common/storage-account-keys-manage?toc=%2Fazure%2Fstorage%2Fblobs%2Ftoc.json&tabs=azure-portal#view-account-access-keys is added to the AppSetting AzureWebJobsStorage in your Function App configuration
- Archived Blob Storage?
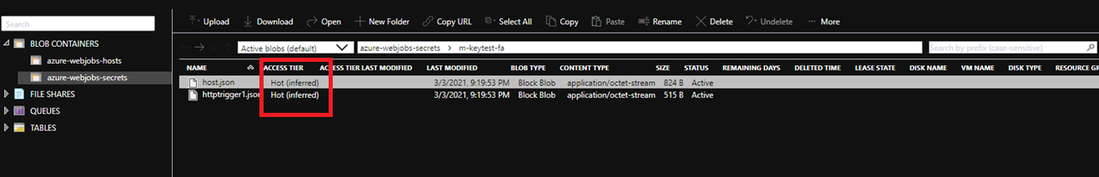
- Check access tier for files inside azure-webjobs-secrets folder:
- Only applicable to Blob Storage and General Purpose v2 (GPv2) accounts. General Purpose v1 (GPv1) accounts don’t support tiering.
- Ensure access tier for host.json file and function json files is set to Hot and not to Archived. Read more about Archive access tier here: Access tiers for Azure Blob Storage – hot, cool, and archive | Microsoft Docs
- When a blob is in archive storage, the blob data is offline and can’t be read or modified. To read or download a blob in archive, you must first rehydrate it to an online tier. You can’t take snapshots of a blob in archive storage.
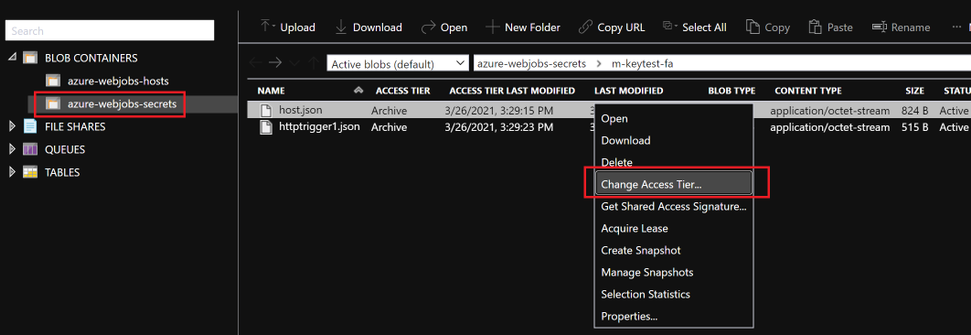
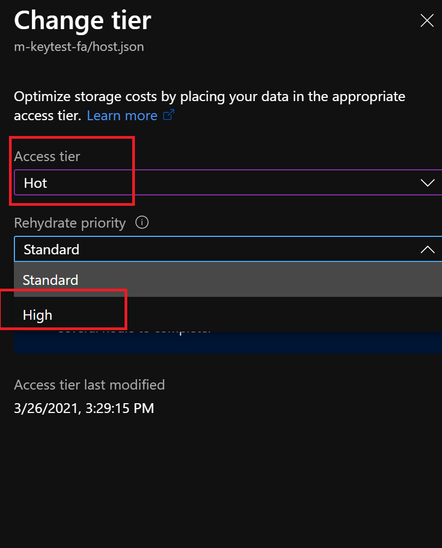
- Solution: Rehydrated storage blobs to Hot – High priority mode. After about 75mins, the blobs will be ready with the modified access tier. Function Key creation will succeed now and the issue with HTTP 401 and HTTP 500 should be resolved.
I hope this helps!
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.


Recent Comments