by Scott Muniz | Feb 14, 2023 | Security, Technology
This article is contributed. See the original author and article here.
Mozilla has released security updates to address vulnerabilities in Firefox 110 and Firefox ESR. An attacker could exploit these vulnerabilities to take control of an affected system.
CISA encourages users and administrators to review Mozilla’s security advisories for Firefox 110 and Firefox ESR 102.8 for more information and apply the necessary updates.
by Scott Muniz | Feb 14, 2023 | Security, Technology
This article is contributed. See the original author and article here.
Citrix has released security updates to address high-severity vulnerabilities (CVE-2023-24486, CVE-2023-24484, CVE-2023-24485, and CVE-2023-24483) in Citrix Workspace Apps, Virtual Apps and Desktops. A local user could exploit these vulnerabilities to take control of an affected system.
CISA encourages users and administrators to review Citrix security bulletins CTX477618, CTX477617, and CTX477616 for more information and to apply the necessary updates.
by Contributed | Feb 14, 2023 | Technology
This article is contributed. See the original author and article here.
Introducing the New Post-delivery Activities Report in Microsoft Defender for Office 365
Attackers are always evolving to adapt to the newest protections enacted by security teams and the products they rely on. Today, attackers frequently attempt to bypass security tools by sending messages that only become malicious after they have been delivered. This requires a robust post-delivery detection and response mechanism. In this blog, we will explore the evolution of an attack, how Defender for Office 365 provides out of the box post-delivery protection, and how you can see this value for your organization. Today we’re announcing a new report in Microsoft Defender for Office 365 that highlights messages that have been acted upon or moved by Microsoft after they have been delivered to the inbox.
Post-delivery activities
Before diving into this new report, we want to start by covering post-delivery activities – what they are and how they work in Defender for Office 365.
How do attacks land in the mailbox?
Threat actors work on the fact that they can send messages and weaponize them later. Attackers frequently send messages with an inactive URL which won’t be detected at time of delivery, and once the messages have been delivered to inboxes, the URLs are then weaponized. This puts your end users at risk of credential theft and your organization at risk of a widespread attack. Threats can also be reclassified post-delivery, based on this weaponization by attackers.
That’s where Zero-Hour Auto Purge (ZAP) comes in to protect your organization from these types of attacks. ZAP is powered by Microsoft’s advanced security graph to detect and neutralize threats. ZAP is constantly reviewing your messages to identify and neutralize these threats.
How does Defender for Office 365 detect and respond to these attacks?
Microsoft Defender for Office 365 includes ZAP, a post-delivery activity which acts on malicious messages after delivery. Upon identifying a malicious Indicator of Compromise (IoC), ZAP can find all messages in user mailboxes that contain the malicious IOC. Once the messages are identified, ZAP acts on the message based on the specific policy action, securing your end users and your organization. With secure by default, our filtering will keep many potentially dangerous or unwanted messages out of your mailboxes. The secure by default feature enables malware and high confidence phishing messages detected post-delivery to be sent to quarantine by ZAP, with no additional configurations required.
ZAP receives signals from our advanced security graph and utilizes this threat intelligence to remove malicious messages from the inbox, providing out of the box post-delivery protection for all customers. And this isn’t just for Defender for Office 365 customers; we provide ZAP actions for all Microsoft email services, including Exchange Online Protection and even Outlook.com consumer accounts. The quick system-driven actions reduce the exposure time of your end users, securing your organization in a timely and effective way. There is no need for any admin intervention to identify and trigger an action. Upon detection of the malicious content, ZAP removes the message from the inbox.
Post-delivery protection with ZAP
Where can I review messages that were neutralized by ZAP?
With our Microsoft Defender for Office 365 P2 and E5 licenses, you can review messages that are neutralized by ZAP within Advanced Hunting and Threat Explorer. You can learn more here.
Introducing the new Post-delivery activity report
We’ve heard customer feedback that understanding when ZAP took action can be challenging. As a result, we’re happy to announce the launch of a new Post-delivery activity report. The report will display all the ZAP events that occurred in your organization. If the verdict assigned to a message has been changed, the new report will display this updated data, making it easier to investigate the messages.
You can find the Post-delivery activities report under Email & collaboration reports.
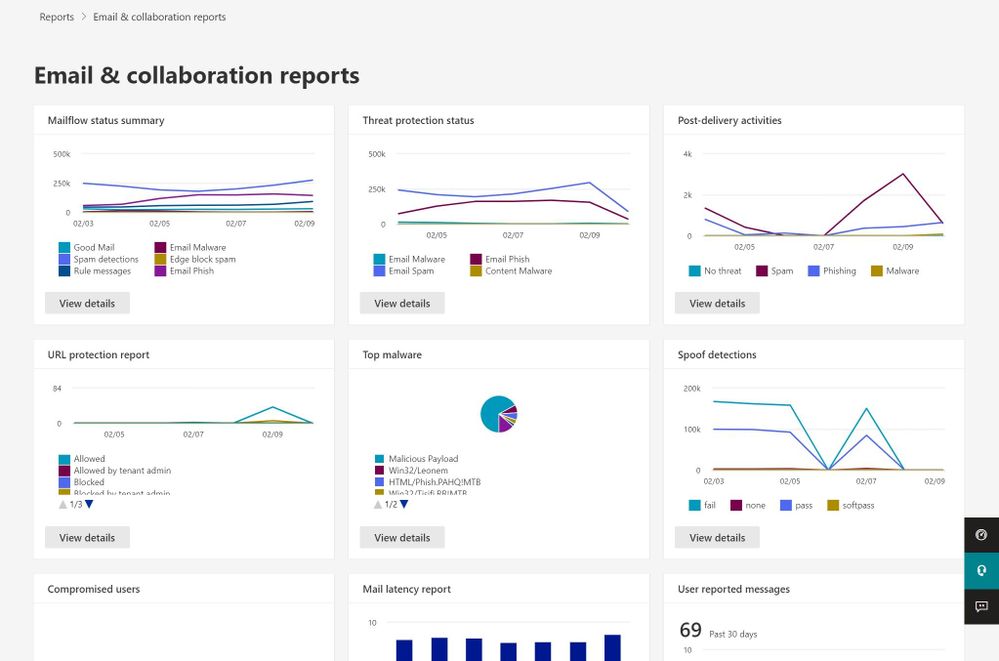
Figure 1: Access the Post-delivery activities report under Email & collaboration reports
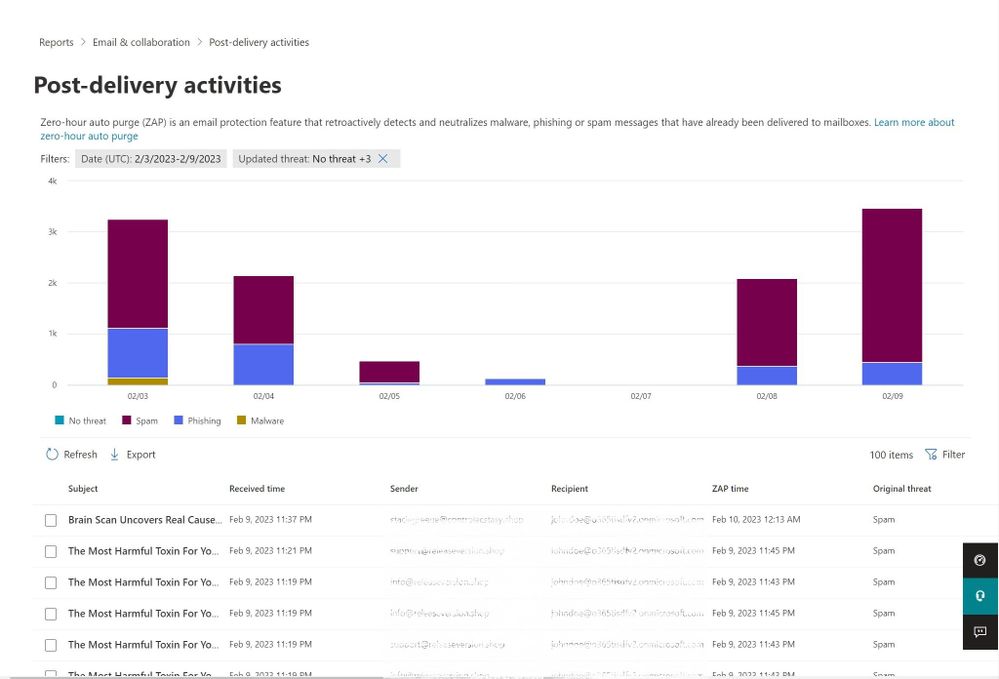
Figure 2: Post-delivery activities report
From the report, you have direct access to the email entity side panel to review additional information about the message:
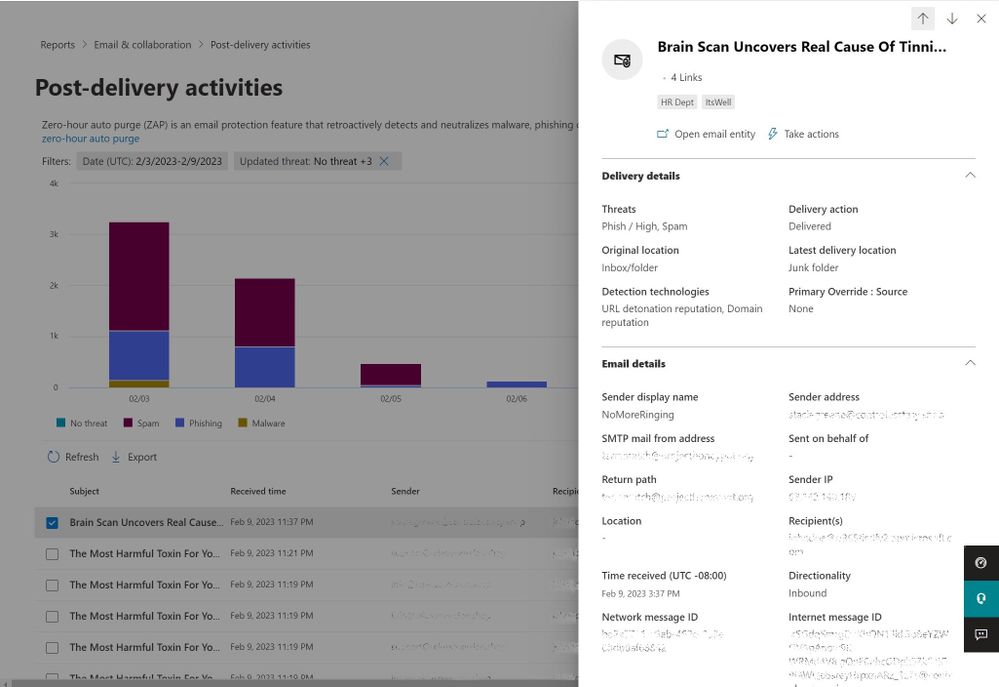
Figure 3: Access the email entity summary panel from the report view
Learn more about the report by viewing our documentation.
You can use the following PowerShell cmdlets to access the report information for your organization.
- GetAggregateZapReport
- GetDetailZapReport
You can learn more about these PowerShell cmdlets here.
If you are part of a Security Operations team or a Cyber Threat Intelligence team, get started by navigating to security.microsoft.com/reports/PostDeliveryActivities, to review the messages we have blocked in your organization post-delivery.
For questions or feedback about Microsoft Defender for Office 365, engage with the community and Microsoft experts in the Defender for Office 365 forum.
by Scott Muniz | Feb 14, 2023 | Security, Technology
This article is contributed. See the original author and article here.
Apple has released security updates to address vulnerabilities in multiple products. An attacker could exploit these vulnerabilities to take control of an affected device.
CISA encourages users and administrators to review the Apple security updates page for the following products and apply the necessary updates as soon as possible:
• Safari 16.3.1
• iOS 16.3.1 and iPadOS 16.3.1
• macOS 13.2.1
by Contributed | Feb 13, 2023 | Technology
This article is contributed. See the original author and article here.
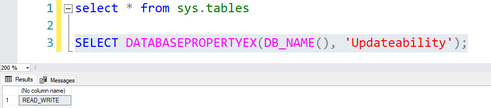
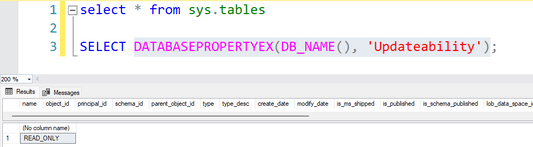
Today, we got a question where our customer asked that if using ApplicationIntent=ReadWrite with an user with db_datareader permision, the results of DATABASEPROPERTYEX(DB_NAME(), ‘Updateability’) will be affected or not.
In this situation, let’s try to create a business critical database with readscale out enabled and create the following user. Right now, the answer is not affected.
create user UserName with password = 'PasswordX2X3X1!'
alter role db_datareader add member UserName
Once we have established the connection using SQL SERVER Management Studio using this user and execute the query
SELECT DATABASEPROPERTYEX(DB_NAME(), 'Updateability');
The results will be:
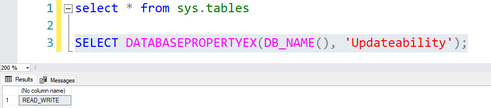
However, using applicationIntent=Readonly with the same user the results will be the expected one:
Additionaly, I would like to share an article that explain the behaviour when we are using Transparent Failover Group and ApplicationIntent at the same time – Lesson Learned #131: ReadScale Out and Failover Group – Microsoft Community Hub
Enjoy!


Recent Comments