by Contributed | Apr 28, 2021 | Technology
This article is contributed. See the original author and article here.
This blog is part one of a three-part series detailing the journey we’re on to simplify configuration of threat protection capabilities in Office 365 to enable best-in class protection for our customers.
Effective security is a never-ending battle to achieve balance between security and productivity. If we apply too many security controls to an environment, we limit the ability of its users to function efficiently. And if we err on the side of restraint, we do not hinder users in any way, but we leave the door open to threats. Email security is complex and ever-changing. With over 90 percent of threats surfacing through email, it’s critical that organizations are empowered to configure security tools in a way that works for their environment.
Configuration is key
We’re committed to offering Office 365 customers the best email protection by continually focusing on improving the effectiveness of our solutions both within Exchange Online Protection (EOP) as well as Defender for Office 365. EOP has a rich legacy of policy granularity and customizations that help customers meet their unique needs. As we’ve built and innovated on Microsoft Defender for Office 365, we have applied those same principles to the new advanced protection capabilities we offered as part of Defender for Office 365, while still respecting many of the EOP settings.
This deeply customizable protection stack within Office 365 has allowed customers over the years to implement policies and rules that fulfill an endless list of requirements. The drawback here, however, is that as customizations are added, they require regular review, upkeep, modifications, and even removal over time. In the absence of that continued focus, there is a high risk of creating an overall reduced state of protection. And while that might sound counter-intuitive, we see this very often. Here are some examples of how these configurations can inadvertently get out of hand:
- An organization in Europe had configured 198 domains to be allowed to bypass our filters
- A firm in India had over 900 URLs stipulated to bypass by our detonation service per week
- An enterprise in Asia had over 50,000 known phishing URLs configured to bypass our filters
In each of these cases, the result was an increase in phishing campaigns making their way to end users. And these are just a few examples of what we see as a widespread problem – custom policies and configurations put in place with perhaps the best of intentions but without considering the immediate or long-term security impact of creating them or keeping them in place permanently.
Across Office 365, we estimate that 20% of phishing mails are delivered to user mailboxes as a result of poorly configured (often legacy) policies that haven’t been revisited for a long time. It was clear that we needed to help customers through this. It wasn’t sufficient that we educate customers of the problem, we had to actively help with getting customers to a more secure state. That started a series of efforts for the past many months that have resulted in capabilities, tools and changes in the product that we’ll walk you through in this blog series. But before we get into it, it might help to get a better appreciation for how the problem arises in the first place.
How did we get here?
The natural question to ask is, how did we arrive at a place where customer configuration could be a problem?
Historical settings can age
In some ways, Exchange Online represents the final frontier. The promise of the cloud is a world where upgrades to Exchange no longer occur every few years. Over the lifespan of Exchange, many customers have migrated with existing mail flow configurations and transport rules from Exchange 2010, to Exchange 2013, and ultimately ending up with Exchange Online in Office 365. Many of our customers reading this may have relied on Exchange versions long before Exchange 2010!
And these configurations and rules may have been implemented at a time where the worst thing that could happen as a result of an overly permissive policy was a spam email getting through. All of that has changed over the past few years.
New attack scenarios
Just as technology has evolved, so have attackers. A lot has changed since we first launched our advanced email security solution in 2015. Since then, email borne attacks have been increasing exponentially both in volumes and complexity. We’ve seen phishing evolve to become only the entry point for much more sophisticated attacks, like business email compromise. We’ve seen attackers pivot away from malware in favor of attacks that help them establish persistence through account compromise and external forwarding. We know that attackers are savvy cybercriminals that will continue to evolve their techniques to take advantage of email users. And one common path they look to exploit are these aging and overly permissive controls or poorly protected pockets within the organization.
New security controls
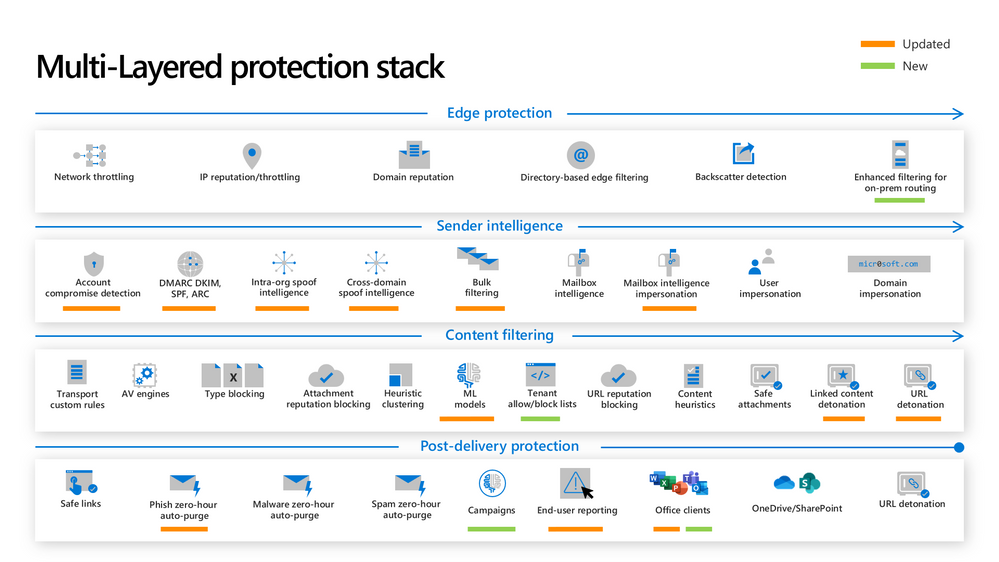
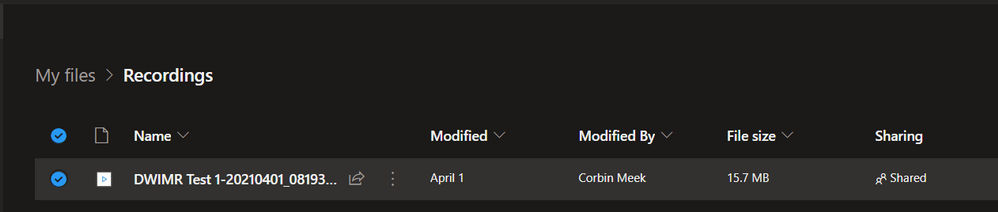
As the threat landscape evolves, so do our protections. Microsoft Defender for Office 365 employs a multi-layered protection stack that is always being updated to meet the needs of our customers. As we introduce new capabilities and make improvements to existing ones, it’s important that our customers are able to take advantage of these capabilities. That sometimes requires frequent evaluation of settings to ensure the latest protections are turned on. Failing that discipline, it’s possible that the latest protections are not being applied to all users in the organization.
Naturally, these three challenges signify the importance of secure posture. It’s more important than ever that configuring protection against threats is easy to achieve and maintain.
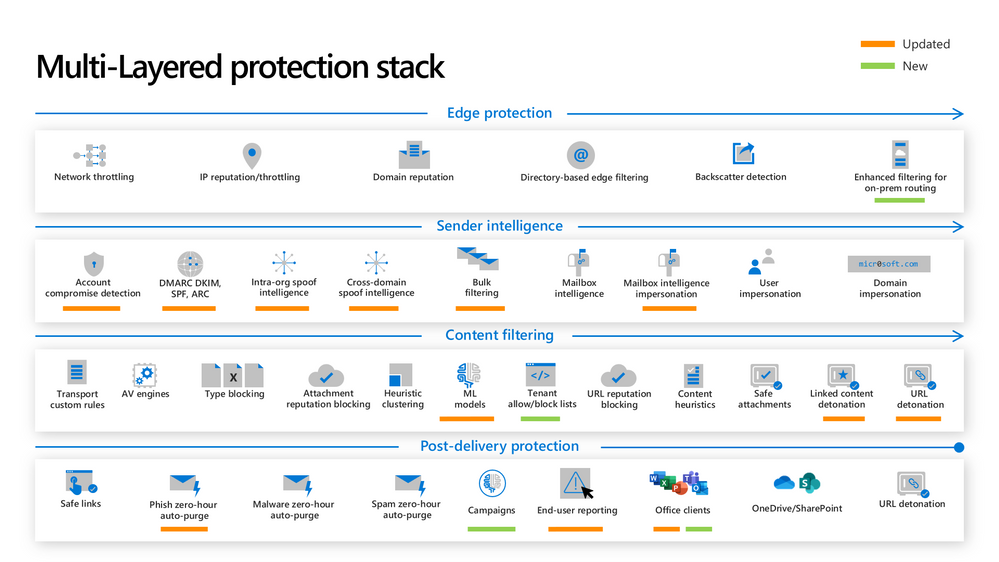 Figure 1: The new and updated layers of the Defender for Office 365 protection stack
Figure 1: The new and updated layers of the Defender for Office 365 protection stack
So how can we solve this problem?
Over the past many months, we’ve been on an aggressive journey to eliminate misconfigurations across Office 365 – to give customers the right tools to achieve secure posture simply and maintain these configurations over time. There are two broad categories of focus:
Eliminating overly permissive configurations
First, it’s critical that these (often) legacy settings or other inadvertent rules and policies don’t come in the way of us being able to keep users protected.
Preventing inadvertent gaps in protection coverage
Second, we want to make sure that organizations can easily protect all their users with the very best of protections that we offer as and when we make them available. This is critical in a fast-changing threat landscape where we’re constantly innovating to ensure users are protected.
As we’ve approached tackling both classes of problems, we’ve applied the following principles:
- Give customers the awareness and tools to get secure
- Actively help customers ‘get to secure’ through changes in the product
- Help customers with the right tools/guardrails to stay secure.
Through this blog series we’ll show how we’re applying all three principles to help customers.
What we have accomplished so far
We’ve been hard at work over the last year to achieve these goals of raising awareness on configuration gaps and preventing these gaps from inhibiting effective threat protection. I want to share with you some of the enhancements we’ve released.
Preset Security Policies
In order to help customers understand the impact of misconfigurations, we needed to do something fundamental – we had to establish what the ideal configuration looked like. Last year we released preset security policies for Exchange Online Protection and Defender for Office 365. These policies provide a simplified method to apply all of the recommended spam, malware, and phishing policies to users across your organization. Since different organizations have different security needs, we released these presets in multiple variations, and allow customers to apply our standard or our strict presets to their users as they see fit.
We’ve seen tremendous adoption of preset security policies since they launched in 2020, with over 18,000 tenants enabling a preset policy in their environment. Preset security policies not only give customers a choice, but they also help them stay up to speed with changing recommendations as the threat landscape evolves. To learn more about preset security policies, check out our documentation.
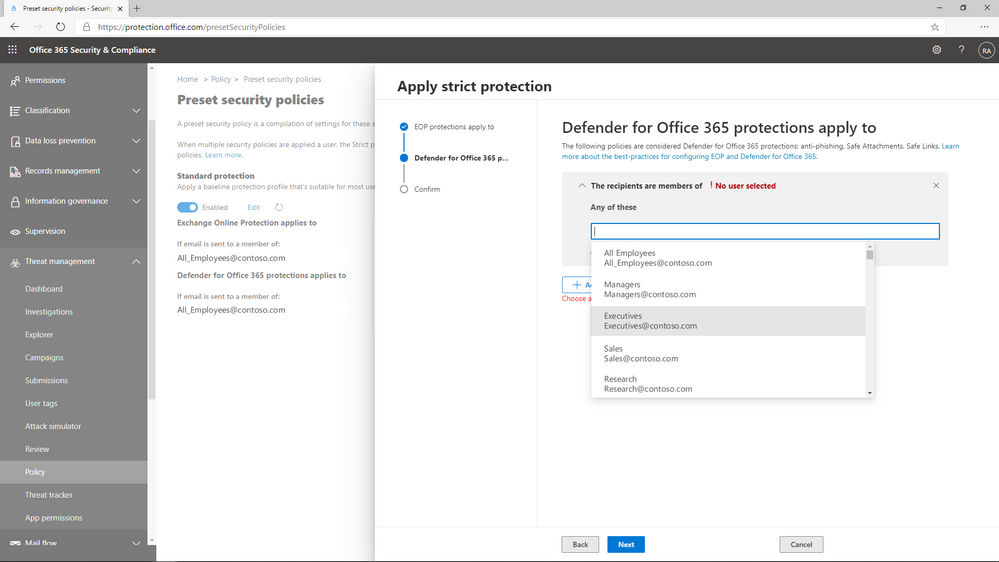 Figure 2: Preset policies can be applied to users, groups, or domains.
Figure 2: Preset policies can be applied to users, groups, or domains.
Configuration Analyzer
Once we’d established the ideal configuration based on our own recommendations, we needed to give customers the ability to identify the instances where their configurations deviate from our recommended settings, and a way to adopt these recommendations easily.
In 2019, we launched ORCA, the Office 365 Recommended Configuration Analyzer. ORCA gives customers a programmatic way to compare their current configuration settings against recommendations via PowerShell. As a result of the overwhelming success of ORCA, last year we built Configuration Analyzer right into the product. Customers can now view policy discrepancies right from within the admin portal, and can even choose to view recommended adjustments to reach our standard or our strict recommendations.
We’ve seen incredible adoption of the configuration analyzer as well, with 290,000 policy changes made across more than 26,000 tenants since we launched the capability last year! With a few clicks, policies can be updated to meet the recommended settings, and as a result, it’s never been easier to keep email security configurations up to date. Learn more about configuration analyzer here.
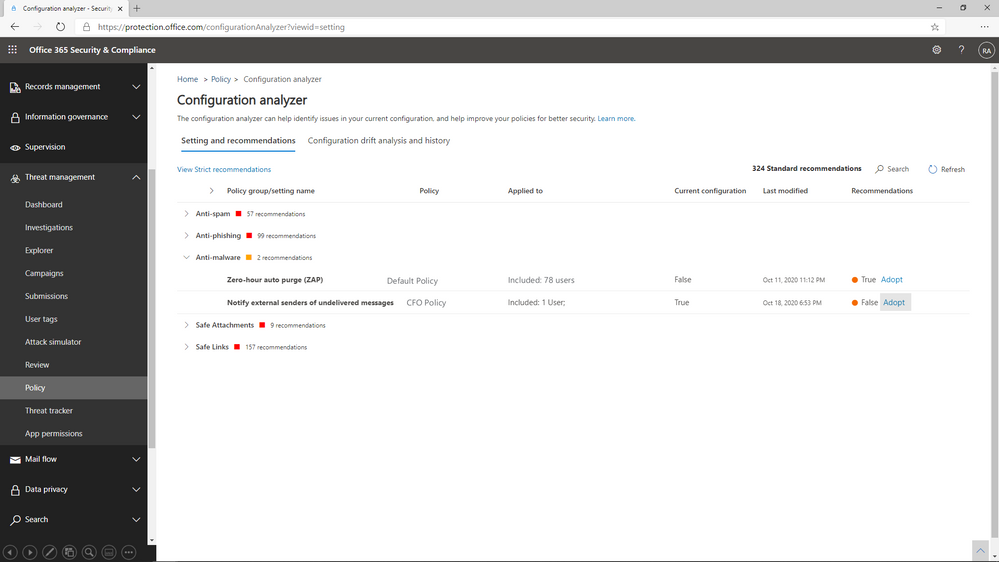 Figure 3: Configuration Analyzer shows policies that do not meet our recommended settings.
Figure 3: Configuration Analyzer shows policies that do not meet our recommended settings.
Overrides Reports and Alerts
You’ll hear us refer to overrides frequently throughout this series. We define overrides as tenant level or user level configurations that instruct Office 365 to deliver mail even when the system has determined that the message is suspicious or contains malicious content. Examples of overrides could be an Exchange transport rule that bypasses filtering for a specific range of IP addresses, or a user level policy like an allowed sender or domain at the mailbox level.
The thing to understand about overrides is that they represent scenarios where policies are properly configured, but other settings have neutralized their effect. It’s important that we allow organizations to customize their Office 365 environment to meet their needs, but that doesn’t mean we feel comfortable allowing malicious content like malware or phish to land in the inbox of users.
We’ve added a view to the Threat protection status report that allows you to view overrides across your environment. By filtering the report to view data by Message Override, you can view overrides over time by type of override, like Exchange transport rule or user safe sender, and you can dig deeper in the details table to identify the causes of these overrides.
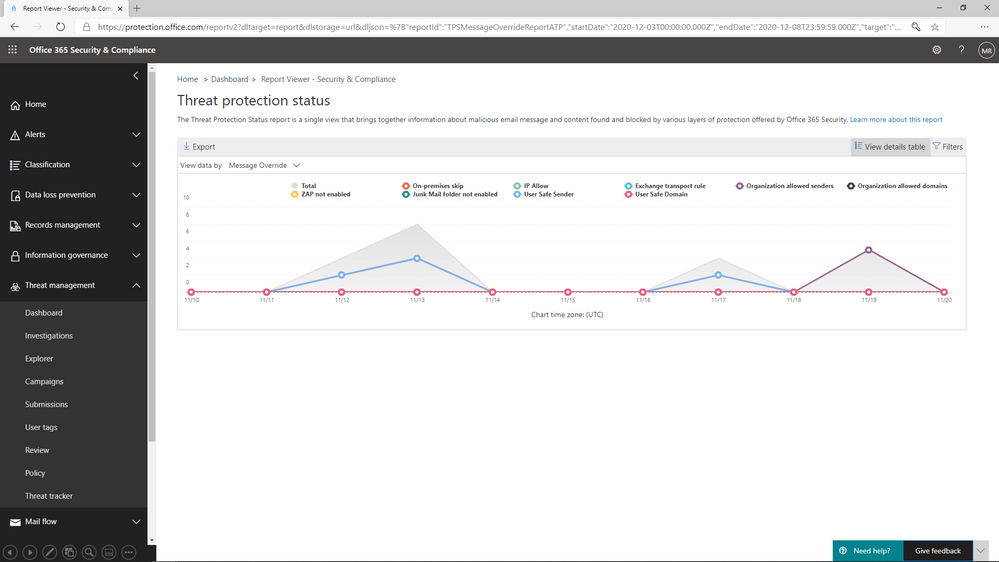 Figure 4: The Threat protection status report shows overrides by type and date
Figure 4: The Threat protection status report shows overrides by type and date
What comes next?
We’ve shared in this blog the steps we’ve taken to shed light on configuration gaps, and to help customers understand the impact configurations have on their environment. In the next blog, we will share details about the capabilities we are building to eliminate the legacy override problem, and what you can do to minimize the impact these overrides have on security posture.
Do you have questions or feedback about Microsoft Defender for Office 365? Engage with the community and Microsoft experts in the Defender for Office 365 forum.
by Contributed | Apr 28, 2021 | Technology
This article is contributed. See the original author and article here.
Claire Bonaci
You’re watching the Microsoft us health and life sciences, confessions of health geeks podcast, a show the offers Industry Insight from the health geeks and data freaks of the US health and life sciences industry team. I’m your host, Claire Bonaci. On episode two of the three part patient experience series guest host, Antoinette Thomas discusses health plan member experience with our Director of population health, Amy Burke.
Toni Thomas
Amy, thank you for joining. As we get started, it would be great to share a little bit about yourself with our guests.
Amy Berk
Wonderful, thank you so much for having me, Toni. So I am the new director of Population Health at Microsoft, I bring forth clinical and operational experience in the population health realm or ecosystem, I started my career as a nurse. So I am a clinican by background. And after graduate school, I embarked on a career in consulting, I’d been a healthcare consultant for 15 years. And the span of my work is cross payers and providers, looking at innovation of care delivery models, working domestically and internationally, working in the public and private sectors. So I feel that my experience is broad, but also very focused on population health.
Toni Thomas
So I’m really glad to be working with you. And as the person that’s really responsible for developing the point of view on experience for health and life sciences, I think it’s really important to, you know, work with all my colleagues on the industry, industry team across their subject matter to make sure we’re developing a holistic view of experience. And so if you would, um, can you share a little bit about traditional member experience? And what drives improvement of that experience inside health plan or per the purview of health plan? And the second part of that question is, does consumerism play a role?
Amy Berk
So thank you so much for that question. Toni, I’ve had some time to think about that question. And, in my mind, the traditional role of the member in a health plan is one that was very reactive versus proactive. We have care managers that are reaching out to engage our members in these programs. Oftentimes, members aren’t even aware of these programs. So how can the health plan really be more keen on outreach and targeting members for these type of programs, health care management, behavioral health programs, pharmacy programs, etc. You know, and even in the role, or probably even in the traditional realm of care management, it has been very much a telephonic model, and how much how much impact we have over the telephone versus how can we engage our members through digital mechanisms, digital modalities, pardon me, like virtual, like digital, etc. So really, you know, harnessing in on engaging that member more through more creative technologies, and I would say also, that it empowers the member, then to really have a responsibility to, you know, take care of themselves, right We are, we are putting the member in, in a place of power to really be able to, you know, engage to be proactive with their own healthcare. And I forgot to mention, but this is an important part as well, in terms of, you know, what’s out there in terms of remote patient monitoring. So, you know, really putting the onus on them to take care of their health in a way that they haven’t done before, and that, that spans across the entire continuum of health. And I would say even the, the entire continuum of demographics, through age and culture and gender, etc. So I think it’s really a good place for any consumer to be right now. Because consumers today have choices like they hadn’t had before. You can go on the internet and consumers can look up and, and really have a clear picture and understanding and knowledge of their disease course of their condition. They have, you know, knowledge of who their providers are against other providers, they can now look up price transparency, is becoming very prominent in terms of being able to look up costs. So that’s very important to consumers today. And I think that, you know, putting our consumers at the heart of what we do, both from a chronic care management perspective, as well as a member satisfaction perspective becomes quite important.
Toni Thomas
So in the hospital world, and the clinic world, we have, you know, the H caps measurements that measure how satisfied a patient might be with within certain realms of that experience. How, how do health plans, how do health plans solicit feedback from their members to understand how satisfied they are with the experience that they’re having within their care management program are within the health plan itself.
Amy Berk
So there are a couple of ways in which that happens. So there are h caps that applied to the member experience and a health plan also stars. So that’s a CMS quality measure for Medicare programs, member satisfaction is actually now weighted most heavily in those star measures. And thirdly, then, you know, through surveys that are solicited to members, through their net promoter scores, etc, that become quite relevant in terms of measuring member satisfaction.
Toni Thomas
That’s great, because I know some of the the listening audience might be Microsoft health and life science field sales teams who are really trying to understand a little bit more about how satisfaction is rated. So that’s helpful to them in their daily jobs, like certainly to understand specifically the star ratings that you referenced. Something that I’m personally interested in, and I think our audience would be interested in is the comparison or contrast between what healthcare system patient experiences and I think most people understand that, and health plan member experience, so if you could, you know, give a little bit of that picture of what that looks like, that’d be helpful.
Amy Berk
so I would say that, you know, a patient versus a member, if we want to put it in that perspective, a patient is often going to the hospital, for reasons in which they need to be taken care of. And they become a guest at that hospital in that, you know, they’re, they’re being taken care of by nurses, and there are physicians there that are treating them with protocols, etc. You know, and often this is in a place of sickness versus in health, right, so a patient is sick. And, you know, that in itself brings in a cadre of, of emotions and experiences of that patient in the hospital, right, where once that patient goes out of the hospital is discharged from the hospital, rather, their disposition to a post acute facility or to home. And they’re within an environment that, you know, they’re now on the road to recovery, and they’re well, and, you know, they’re getting healthy or healthier, shall I say. And it goes back to that first comment, which I said, where the member has more, I would say, power, more, you know, ability to manage their condition, right. And this of work becomes so important for our care managers that are out there to take a proactive approach with our members to engage them better in their care. So they can have that opportunity to self manage their care for better outcomes. So you know, now it’s more proactive, and I would say where I said, The patient is a guest of the hospital and that everything is directed by this interdisciplinary care team in, you know, how they deliver care. Now, it becomes a little bit different of a shift to now the care management team, the interdisciplinary team is a is a guest to that member’s home, even when the person or the member goes to see the provider. There’s it’s still a different dynamic, right? Because I think that that member is at the heart in the center of making key decisions and shared decision making. And that applies to to the provider side, right, there should be shared decision making in the hospital setting as well. But I think it’s even more elevated in the post acute setting in that members are on their way to becoming healthy. And a member has control over that pathway, more so than a patient, if that makes sense.
Toni Thomas
I think that’s really profound. And it’s it’s also very interesting, Amy because some of the things I’ve been doing a lot of reading and research on agency and like a personal agency. And I think what we’re seeing right now with patients, consumers, customers members is that They’re exhibiting more personal agency than they ever have before. People who study this aren’t really certain as to why that might be. I don’t think there’s one reason for it, I think there’s a multitude of reasons I’m having access to information technology. And also the fact that we have been living 12 months inside of a pandemic, where they really feel that they have to take control over their own health, their own wellness, their own decision making. And so what I’m starting to see in the provider or the healthcare systems, space is really kind of this movement that you were referencing about. Being a collaborator with someone in their health, health, knowing that person personally, to offer the guidance that they need to make the decisions about their health. So I’m really starting to see healthcare systems want to move in that direction, especially on how they’re communicating with patients, either who are trying to make appointments, or soliciting some advice on hospitals. And it’s just really interesting paradigm shift. So I’m excited to see what happens there. I think it’s important. And then lastly, what important lessons can the healthcare system world and the plan world learn from one another to improve this experience?
Amy Berk
Yeah, so thank you for that question. And this, again, centers around, we have to focus in on patient member centric care, and what that means and including the member in terms of or the patient, what matters most to them. In terms of their care journey, I would also say that, you know, we have to think about our patients slash members holistically. So we shouldn’t be focusing in on one disease we should be focusing in on if that person has co morbidities if that person has gaps in terms of social determinants of health, behavioral health, post pandemic, I mean, the, the crisis of mental health, as it has never been before is is a pandemic in itself, right. So, you know, really honing in on not just one disease or one condition or even that person’s clinical picture, but we have to think more broadly, in terms of that person holistically, right, and bring through those social determinants that have impact on their health outcomes, behavioral health, emotions, and, you know, and needs. So I would, I would say, that’s very important, and that spans across both provider and member and, you know, holistically, culturally, clinically, etc.
Toni Thomas
So that brings us to the end of our time together. But I do want to say I always enjoy speaking with you and asking you questions because I, I learn so much from you, Amy and I, I’ve learned things that will help me make me better in my job and also allow me to help the customers that I’m out there serving. So I really, really thank you for joining us for this session and contributing to patient experience. We thank you so much.
Claire Bonaci
Thank you all for watching. Please feel free to leave us questions or comments below and check back soon for more content from the HLS industry team.

by Contributed | Apr 28, 2021 | Technology
This article is contributed. See the original author and article here.
Guest post by Charlie Johnstone, Curriculum & Quality Leader for Computing, Film & TV at New College Lanarkshire: Microsoft Learn for Educator Ambassador

New College Lanarkshire is one of the largest colleges in Scotland, operating across Lanarkshire and East Dunbartonshire, we have 3 main campuses and 3 satellite campuses. Created in 2012 following the merger of Coatbridge College, Cumbernauld College and Motherwell College, we have more than 10,000 students enrolled on a mix of full-time, part-time, evening, and commercial courses.
We offer more than 600 courses across six faculties: Care & Science; Engineering & Automotive; Service Industries; Business, Social Science & Sport; Supported Learning; and Computing & Creative Industries.
The College was named ‘Best in the UK’ at the WorldSkills UK trade skills competition in Birmingham in November 2013, 2014, 2016 and 2019, in addition to finishing in the top three places in 2015, 2017 and 2018 and are recognised as a WorldSkills Centre of Excellence.
The Faculty of Computing and Creative Industries has a diverse portfolio embracing Computing, Sound Technology, Music Performance, Film & TV, Photography, Art & Design, Acting and Musical Theatre.
In computing, we offer courses ranging from beginners to BSc Computer Networking in partnership with University of the West of Scotland. The majority of our qualifications are awarded by the Scottish Qualifications Authority and the most popular qualification, HNC Computing (equivalent to 1st year BSc) is currently going through long overdue redevelopment which will give us more flexibility than we currently have.
As a team, we became aware of the Microsoft Learn for Educators (MSLE) curricula in June 2020 when most of the team attended Azure Fundamentals AZ-900 training, following this, and several calls with Andrew Bettany and Clare Riley from Microsoft UK, who assisted us in setting up Azure Lab Services, it was suggested that we join the MSLE Institutional programme, which we confirmed in December 2020.
Since then, a number of our staff have been delivering Azure Fundamentals AZ-900 and Azure AI Fundamentals AI-900 to principally our HNC and HND students, up until that point the students had little knowledge or experience of cloud technologies, I have also been delivering AZ-900 training to lecturers from two other colleges in Scotland.

This year, purely due to timing, we were unable to fully integrate the courses into the curriculum, however, we have offered them as add-on courses very successfully. At the moment we are planning for complete integration of at least AZ-900 into our Higher National Certificate courses next academic year.
With more than 10,000 students enrolled, the college is dedicated to continuous improvement, has invested in the latest technology and facilities across its campuses and is a leader in developing UK skills.
Integrating Microsoft skills into the curriculum
We are expecting to start delivering AZ-900 to local unemployed people in the next couple of weeks and are currently advertising the courses through a Scottish scheme known as the Flexible Workforce Development Fund, this is a fund created for SMEs to take advantage of the apprenticeship levy by accessing training up to the value of £5000.
In our experience since starting this process, the impact has been huge, the students are very much enjoying the courses and are engaging with us out with their normal class times to take extra classes in AZ-900 and AI-900. They have been giving us excellent feedback which goes to reinforce the idea that we (and Microsoft) are getting it right with an excellent balance of theory and practical through the labs, I have included a couple of students’ comments below
“When I first heard of the Cloud, I was interested because of how mysterious it seemed, but now that I am learning about it, it fascinates me more and more each day.” Tomas McHendry
“I think as students at the moment we are lucky to have people like Charlie and the other lecturers fighting for the evolution in education we need.” Karen Skinner
What we have learned as a college and as a team, is that if we want to do justice to our students and their aspirations, we need to move from what has essentially been a pilot programme this year to a fully integrated programme next year and beyond.
One of the greatest benefits of our engagement in the MSLE programmes has been the opportunity for staff development, previously it was very difficult for computing lecturers to access quality CPD, partly due to cost and partly due to timetabling, the MSLE programmes have made this easier by removing the largest part of the problem, the cost. As a result, most of my team are studying for at least one Microsoft Fundamentals course.
This does not end with MS Fundamentals, the college is in the process of creating a “CPD Academy”. It is my plan to leverage many more parts of Microsoft Learn to upskill non-technical teaching staff, students and our professional services staff as detailed in the learning pathways in “Digital Capabilities for a Cloud First, Mobile First Education”
Our short term goals have been achieved and considerably surpassed, so focusing on the medium term, my goal is for students to leave our college as “cloud natives”, so next year we plan to move our software development to cloud based using Azure and the associated tools. Moving on further, we are looking at delivering beyond the fundamentals so that the students can graduate with “Associate” qualifications.
We have various new initiatives under way as a result of our work with Microsoft, we are in the planning stages of a number of projects in order to take Microsoft Learn to a wider and more gender-neutral audience and greatly enhance our students’ employability.
The first project is centred around Computer Vision by creating an app in partnership with the college’s hairdressing staff and students, designed to enable students to identify hairstyles from photos (their own or downloaded). Part of the aim of the project is to engage the mostly female hairdressing students with ICT through AI.
The second project is aimed at improving our student’s employability. A major employer and Azure user in Scotland has offered to assist us in moving our software, project management, IT infrastructure and security to a DevOps model, similar to theirs and access to live anonymised data to work with. They have also offered that once we get under way, they will offer students paid internships between years 1 & 2, hopefully leading to employment. The organisations Cloud Manager stated that
“If you can sit a student in front of me for an interview and they can demonstrate that they can develop a data application in Azure and send the results over a VPN to another platform, I’ll employ them on the spot”
Case Study
Microsoft Customer Story-Leaping into a much better world
Achieving this ability and opportunity in our students is our ultimate goal.
by Contributed | Apr 28, 2021 | Technology
This article is contributed. See the original author and article here.
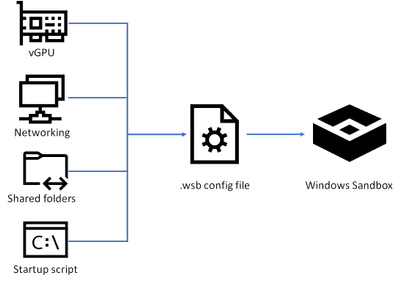
In this blog post, I will show you how you can set up, configure and customize Windows Sandbox in Windows 10 using advanced Windows Sandbox config files. Windows Sandbox is based on Hyper-V technology and allows you to spin up an isolated, temporary desktop environment where you can run untrusted software.
What is Windows Sandbox
Windows Sandbox provides a lightweight desktop environment to run applications in isolation safely. Software installed inside the Windows Sandbox environment remains “sandboxed” and runs separately from the host machine.
A sandbox is temporary. When it’s closed, all the software and files and the state are deleted. You get a brand-new instance of the sandbox every time you open the application.
Software and applications installed on the host aren’t directly available in the sandbox. If you need specific applications available inside the Windows Sandbox environment, they must be explicitly installed within the environment.
Windows Sandbox has the following properties:
- Part of Windows: Everything required for this feature is included in Windows 10 Pro and Enterprise. There’s no need to download a VHD.
- Pristine: Every time Windows Sandbox runs, it’s as clean as a brand-new installation of Windows.
- Disposable: Nothing persists on the device. Everything is discarded when the user closes the application.
- Secure: Uses hardware-based virtualization for kernel isolation. It relies on the Microsoft hypervisor to run a separate kernel that isolates Windows Sandbox from the host.
- Efficient: Uses the integrated kernel scheduler, smart memory management, and virtual GPU.
You can learn more about Windows Sandbox on Microsoft Docs and if you are interested in how Windows Sandbox works, check out the Windows architecture here.
How to install Windows Sandbox
To get started with Windows Sandbox, you will need to have the following prerequisites:
- Windows 10 Pro, Enterprise or Education build 18305 or later (Windows Sandbox is currently not supported on Home SKUs)
- 64-bit architecture
- Virtualization capabilities enabled in BIOS
- At least 4 GB of RAM (8 GB recommended)
- At least 1 GB of free disk space (SSD recommended)
- At least two CPU cores (four cores with hyperthreading recommended)
You can install Windows Sandbox as an additional feature in the Control Panel or by simply running the following PowerShell command as administrator:
Enable-WindowsOptionalFeature -FeatureName "Containers-DisposableClientVM" -All -Online
After running that command, you will need to restart your computer, and after the reboot, you can start using the Windows Sandbox directly from the Start menu.
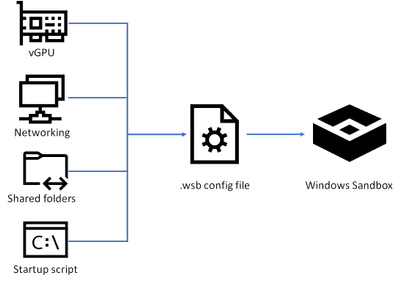
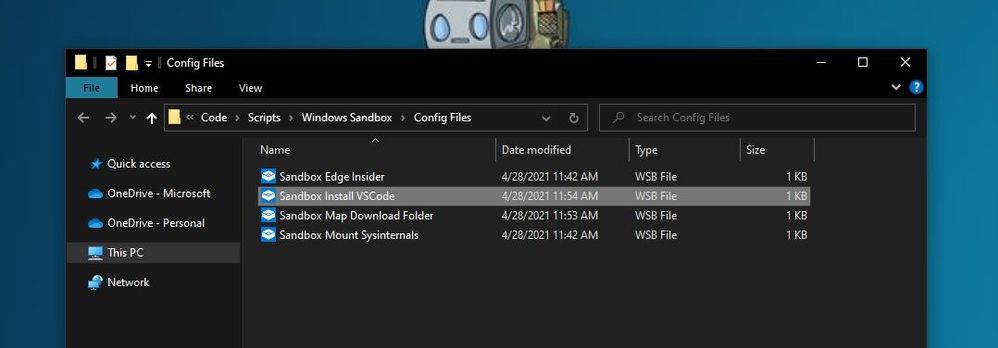
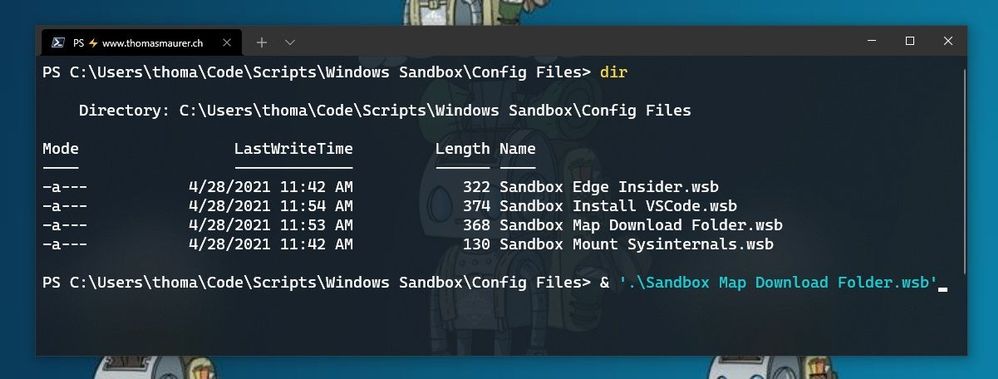
Customize Windows Sandbox with Configuration Files
By default, Windows Sandbox spins up a default image. However, in many cases, you want to spin up a customized environment with already preinstalled tools or access to local files. For that, you can use config files that allow you to customize the sandbox during startup. The sandbox configuration files are formatted as XML and use the .wsb file extension.
 Customize Windows Sandbox with Configuration Files
Customize Windows Sandbox with Configuration Files
Today, you can configure four different settings to configure the Windows Sandbox.
- vGPU (virtualized GPU): Enable or disable the virtualized GPU. If vGPU is disabled, the sandbox will use Windows Advanced Rasterization Platform (WARP).
- Networking: Enable or disable network access within the sandbox.
- Mapped folders: Share folders from the host with read or write permissions. Note that exposing host directories may allow malicious software to affect the system or steal data.
- Logon command: A command that’s executed when Windows Sandbox starts.
- Audio input: Shares the host’s microphone input into the sandbox.
- Video input: Shares the host’s webcam input into the sandbox.
- Protected client: Places increased security settings on the RDP session to the sandbox.
- Printer redirection: Shares printers from the host into the sandbox.
- Clipboard redirection: Shares the host clipboard with the sandbox so that text and files can be pasted back and forth.
- Memory in MB: The amount of memory, in megabytes, to assign to the sandbox.
To create a configuration file, open your editor of choice and create a file with the file extension “.wsb”. Now you can start building the config using XML.
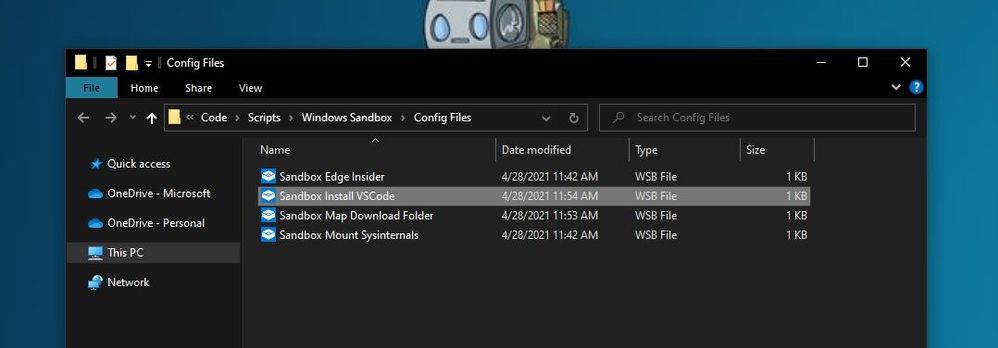 Windows Sandbox Configuration Files WSB Files
Windows Sandbox Configuration Files WSB Files
Let’s start with a simple configuration file, which mounts the Downloads folder of the local machine into the Windows Sandbox as read-only. This allows you to use the files from your Downloads folder in your Sandbox. However, the Sandbox cannot write back to that folder.
In addition, we also use the Command part to open up the explorer.exe with the mounted Downloads folder when the Windows Sandbox starts.
<Configuration>
<VGpu>Default</VGpu>
<Networking>Default</Networking>
<MappedFolders>
<MappedFolder>
<HostFolder>C:UsersthomaDownloads</HostFolder>
<ReadOnly>true</ReadOnly>
</MappedFolder>
</MappedFolders>
<LogonCommand>
<Command>explorer.exe C:usersWDAGUtilityAccountDesktopDownloads</Command>
</LogonCommand>
</Configuration>
I saved this as “Sandbox Map Download Folder.wsb“. To start Windows Sandbox with the configuration file, double click the configuration file or open it up in the console.
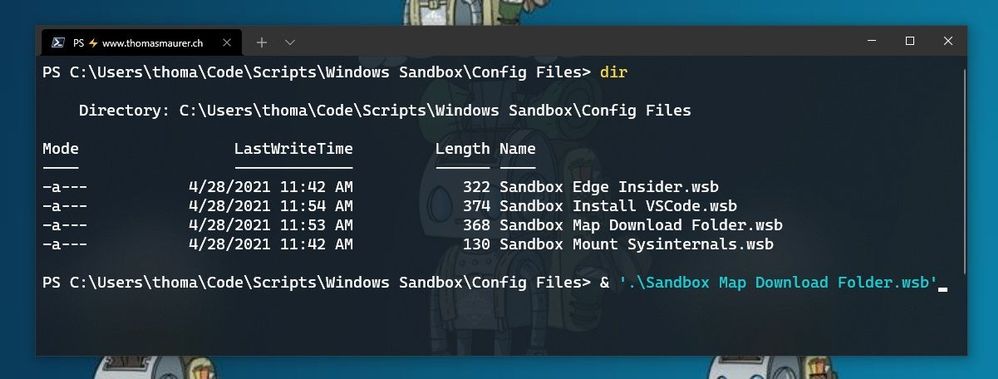 Windows Sandbox Configuration Files start from Windows Terminal
Windows Sandbox Configuration Files start from Windows Terminal
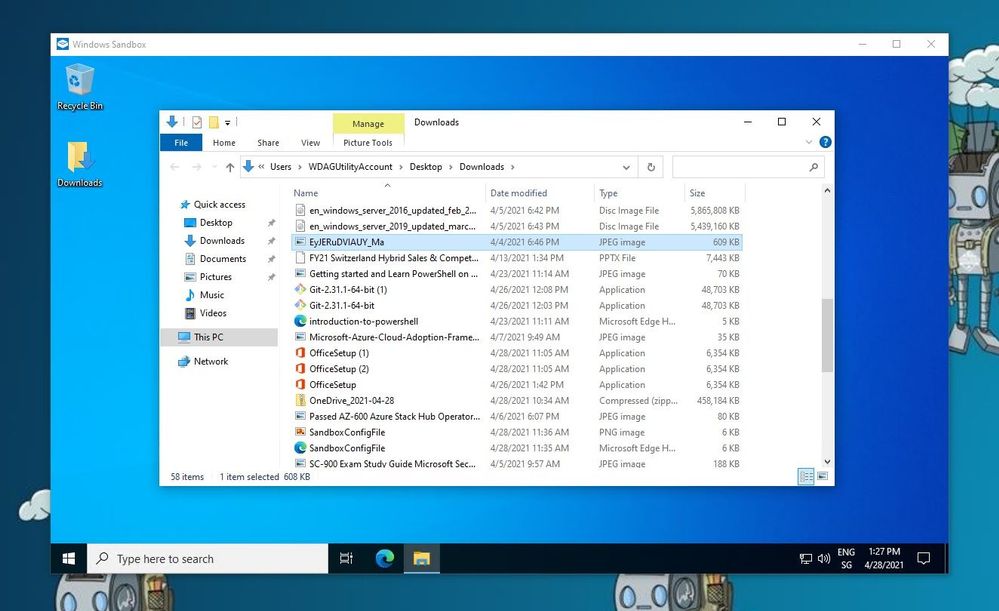
After that, Windows Sandbox will open with the mounted Downloads folder.
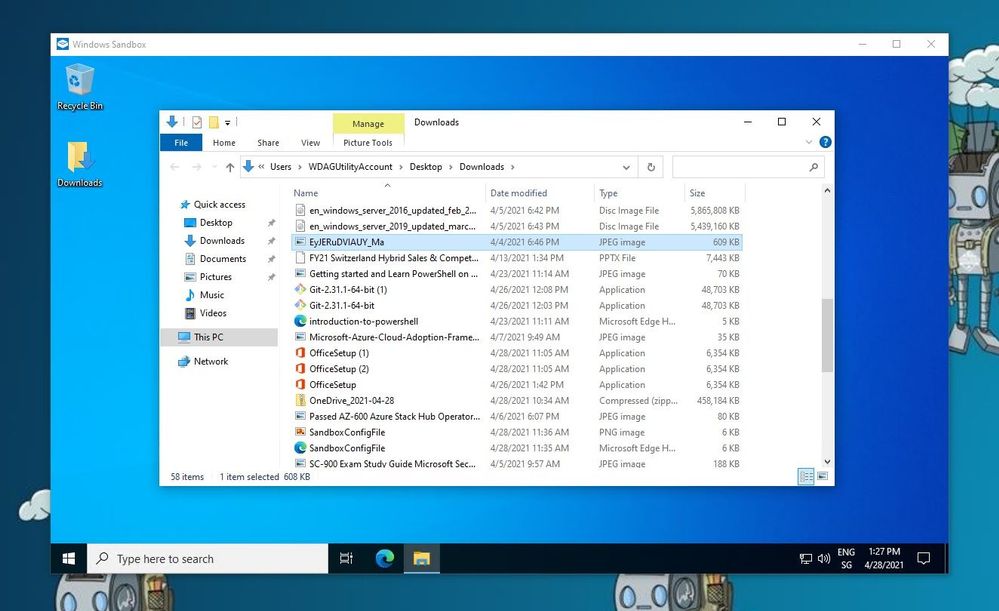 Windows Sandbox Mounted Folder
Windows Sandbox Mounted Folder
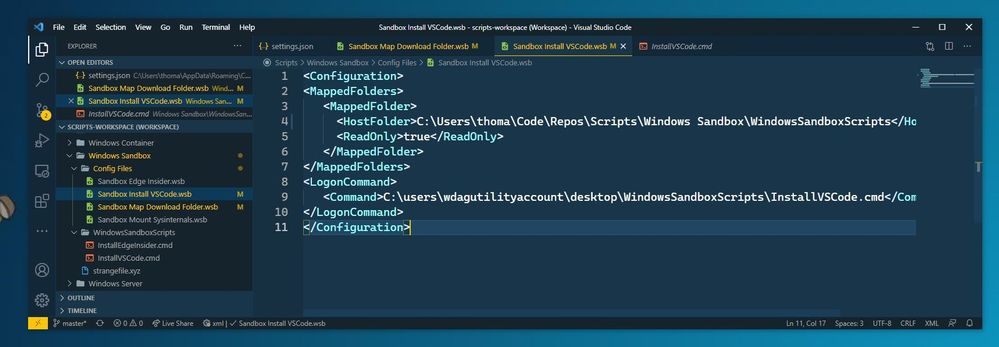
Another example I want to share here is how you can run a script to modify or installed software. In this case, I want to have a Windows Sandbox with Visual Studio Code installed. For that, I use the folder option to mount a folder with a script, and within that script, I have the installation commands. After the Windows Sandbox has started, it will run the script from the mounted folder using the command option.
<Configuration>
<MappedFolders>
<MappedFolder>
<HostFolder>C:UsersthomaCodeReposScriptsWindows SandboxWindowsSandboxScripts</HostFolder>
<ReadOnly>true</ReadOnly>
</MappedFolder>
</MappedFolders>
<LogonCommand>
<Command>C:userswdagutilityaccountdesktopWindowsSandboxScriptsInstallVSCode.cmd</Command>
</LogonCommand>
</Configuration>
The InstallVSCode.cmd looks like the following:
REM Download VSCode
curl -L "https://update.code.visualstudio.com/latest/win32-x64-user/stable" --output C:usersWDAGUtilityAccountDesktopvscode.exe
REM Install and run VSCode
C:usersWDAGUtilityAccountDesktopvscode.exe /verysilent /suppressmsgboxes
These are just some of the examples of how you can customize your Windows Sandbox environments. If you want to learn more, check out Microsoft Docs.
Make Visual Studio Code handle .wsb file with XML
By default, editors don’t necessarily know about the wsb file extension and that this includes XML syntax. In Visual Studio Code, you can open up the Settings (JSON) and add the following to the files.associations.
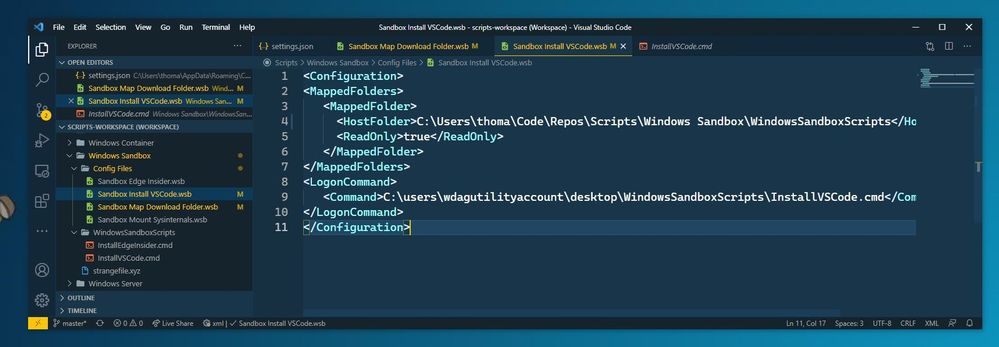 Visual Studio Code
Visual Studio Code
In the JSON settings, search for files.associations. Note: The searched section might be there or not.
If it is not there, add the following:
"files.associations": {
"*.wsb": "xml"
}
Conclusion
I hope this provides you with a short overview of how you can customize the Windows Sandbox. I am interested in what customization you are running. If you have any questions, feel free to leave a comment or share your customization.
by Contributed | Apr 28, 2021 | Technology
This article is contributed. See the original author and article here.
Hi Teams Community,
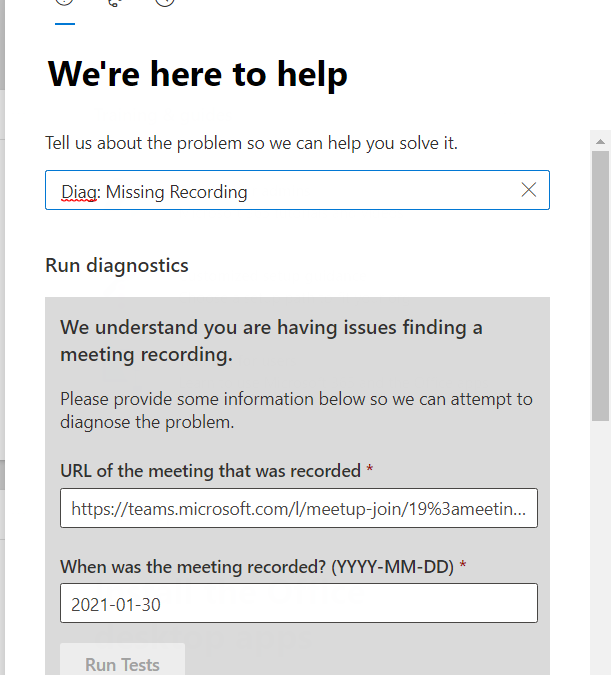
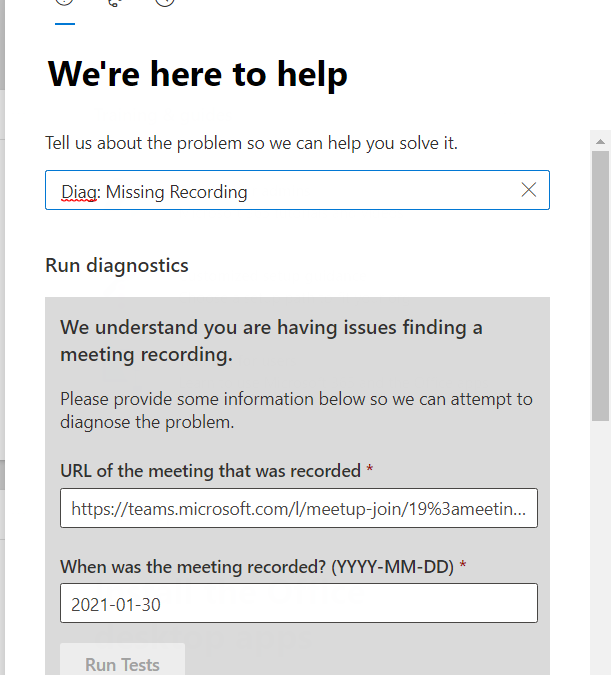
Our team has just released a new diagnostic, Teams Meeting Missing Recording. Thanks to @Sorin Duta for coding this one up!
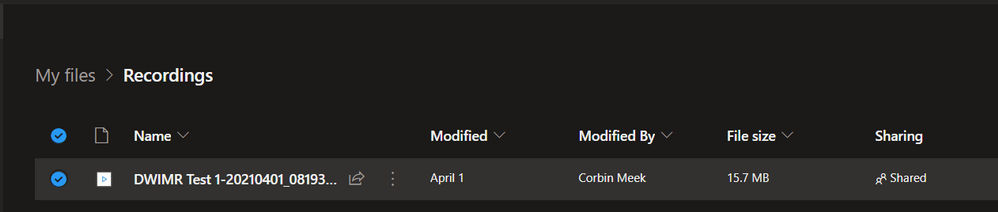
With the ongoing shift of Teams Meeting Recording storage from Stream to OneDrive SharePoint, sometimes a Meeting Recording file can become misplaced. We discuss some known issues and troubleshooting options in the following Article: Issues with Meeting Recordings
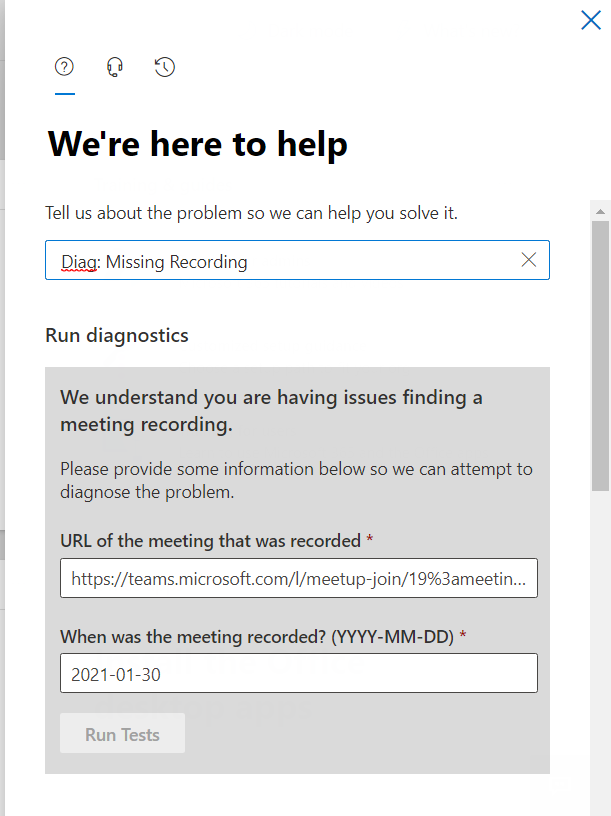
This new Diagnostic can find missing Meeting Recordings in the event they are lost or misplaced. To access the Diagnostic in your M365 Admin Portal, type Diag: Missing Recording into the Need Help or New Service Request description box:
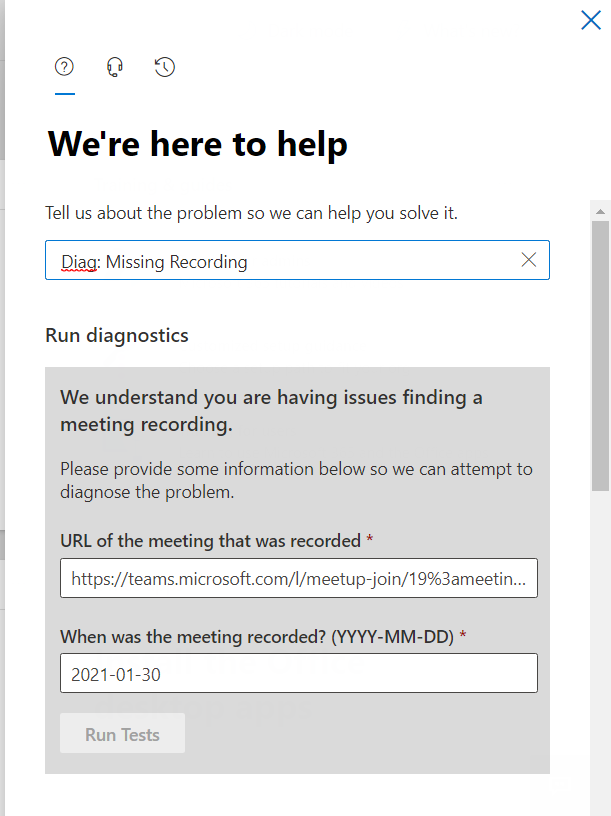
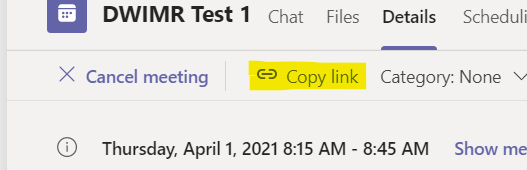
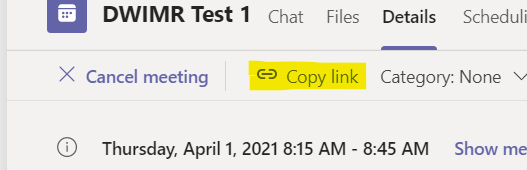
Notice that the Diagnostic requires a Meeting Join URL, one way to get that is from the Meeting details page in the Teams client. Find the Meeting Chat, then click on the three lines top right:

And then you can copy the link:
From there, you simply need the Date the meeting occurred. Note that we only keep Meeting Recording telemetry for 30 days, so if the meeting recording is older than 30 days, you’ll need to try one of the manual methods in the troubleshooting article linked above.
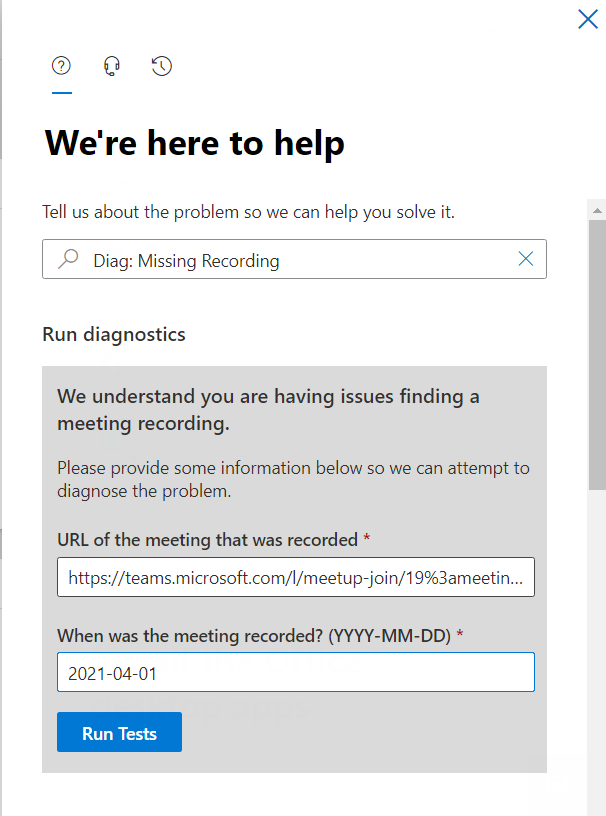
Enter your meeting join URL and date in YYYY-MM-DD format:
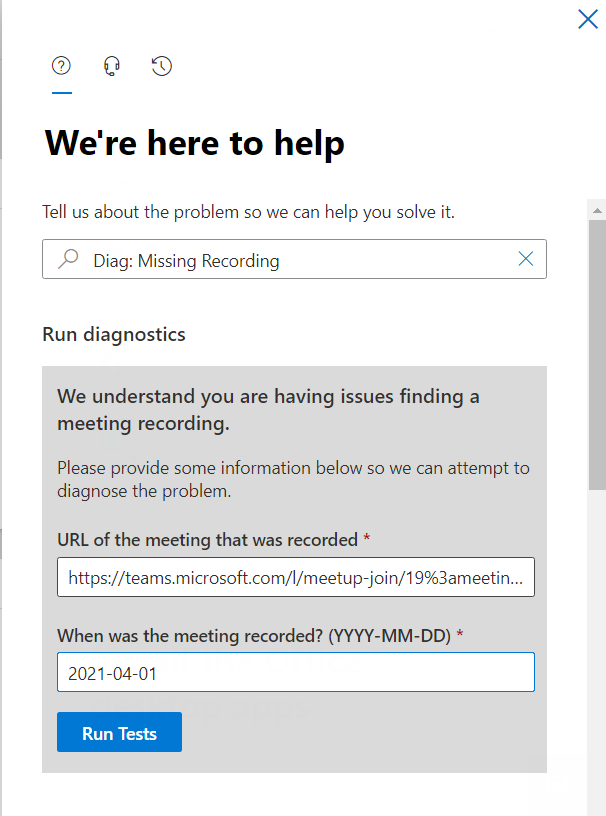
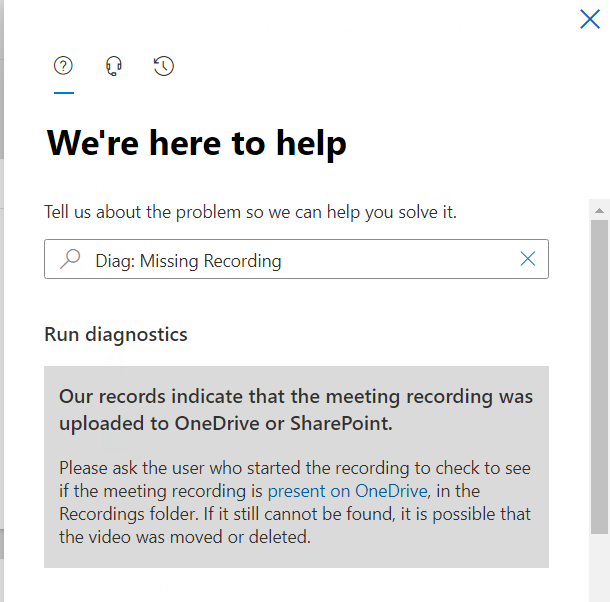
And then click on Run Tests. In my case, here is the result:
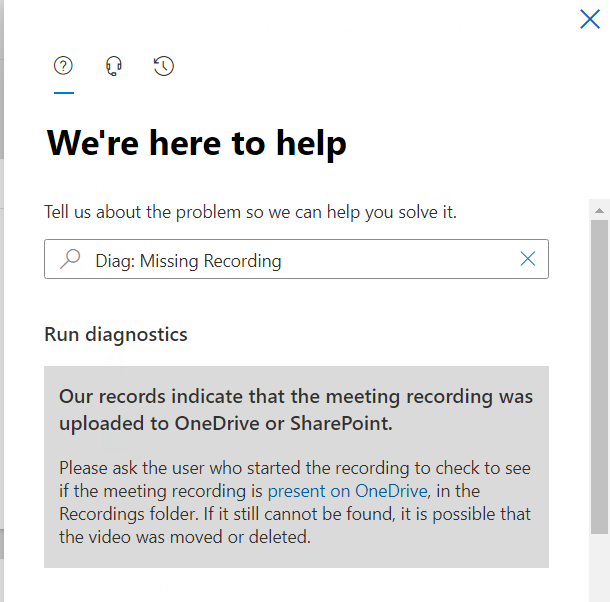
And this indicates that my Meeting Recording was saved to OneDrive, and provides a link to our troubleshooting article with instructions on how to go find it in OneDrive. The Diagnostic can detect if the user’s storage is still Stream as well, and those instructions (how to find the recording file in Stream) are there too. For this example, here’s where I found my missing recording:
We hope this Diagnostic is helpful in situations where the Meeting Recording file can’t be found after a meeting. Please give it a try and let us know how it went in the comments below.
As a reminder, all of our Microsoft Teams Diagnostics are listed in the following article: Self-help diagnostics for Microsoft Teams administrators
Thanks!
Microsoft Teams Support
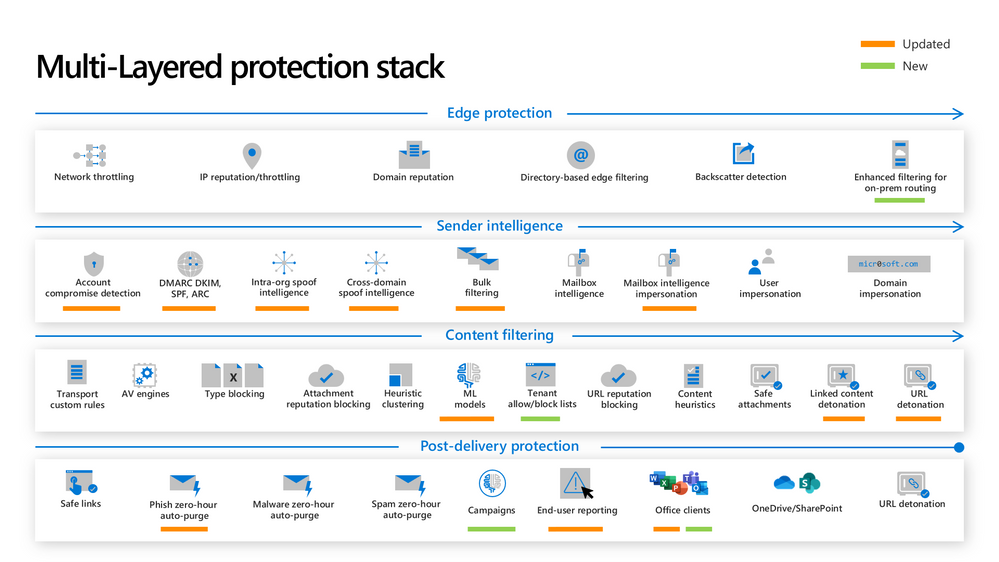
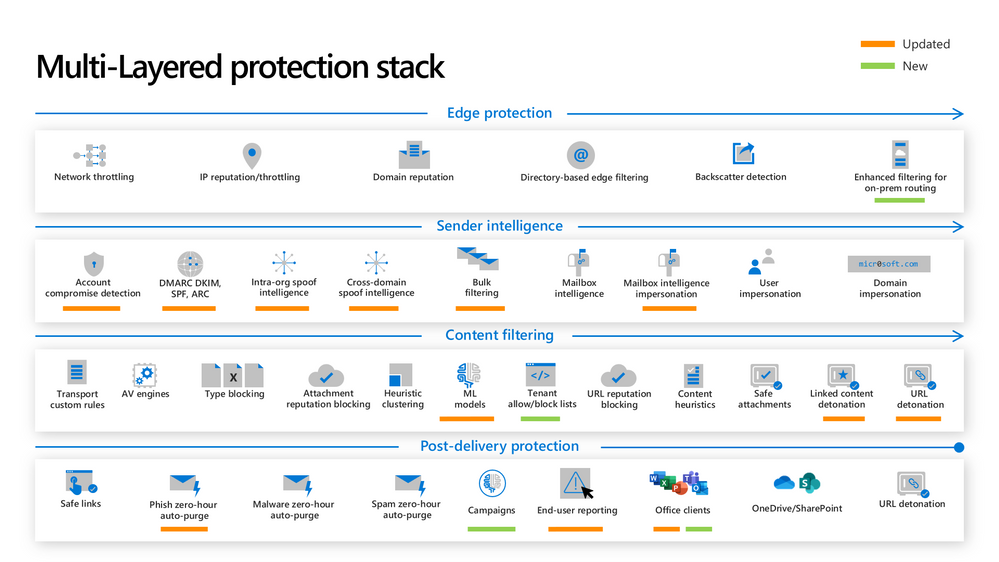 Figure 1: The new and updated layers of the Defender for Office 365 protection stack
Figure 1: The new and updated layers of the Defender for Office 365 protection stack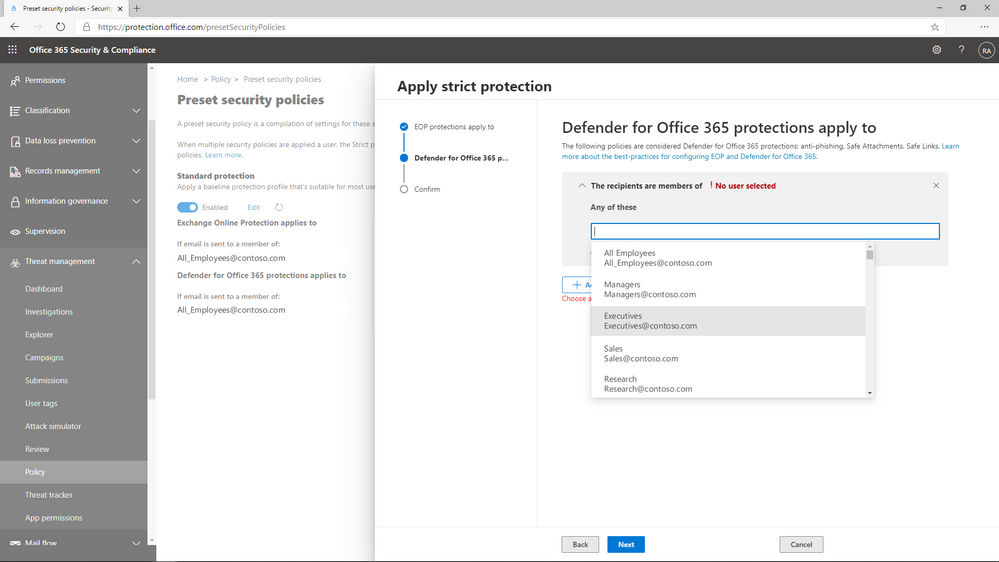 Figure 2: Preset policies can be applied to users, groups, or domains.
Figure 2: Preset policies can be applied to users, groups, or domains.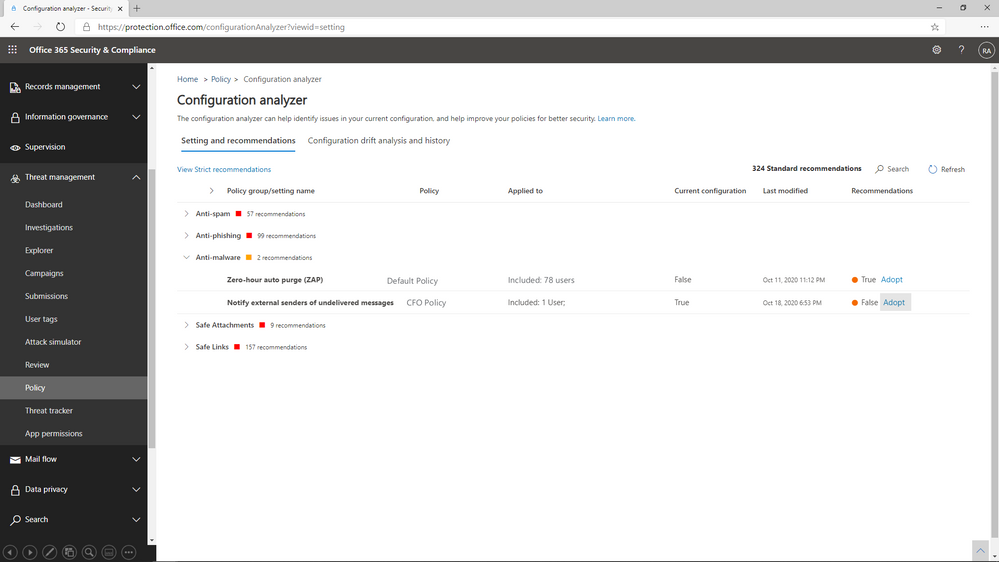 Figure 3: Configuration Analyzer shows policies that do not meet our recommended settings.
Figure 3: Configuration Analyzer shows policies that do not meet our recommended settings.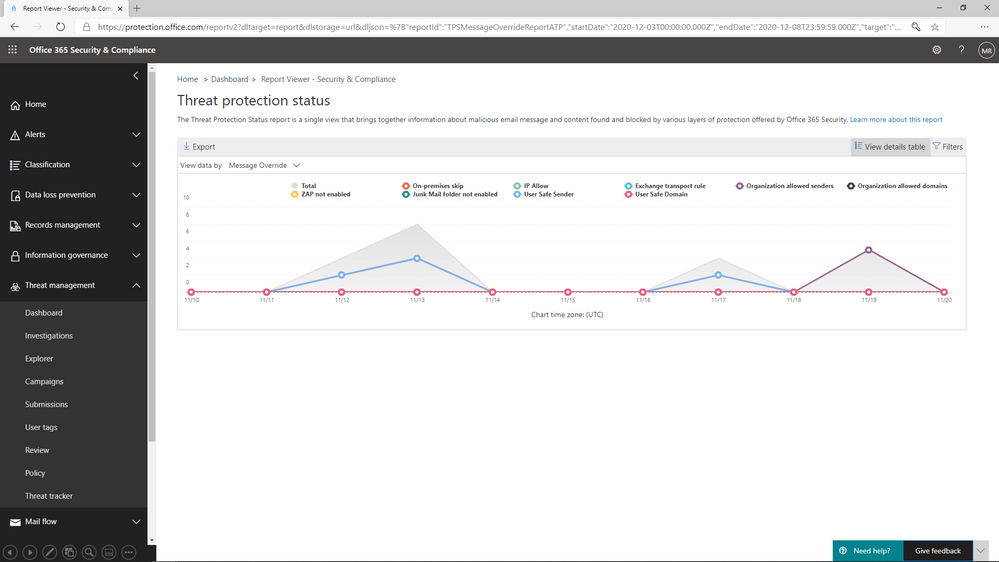 Figure 4: The Threat protection status report shows overrides by type and date
Figure 4: The Threat protection status report shows overrides by type and date




Recent Comments