by Contributed | May 6, 2021 | Technology
This article is contributed. See the original author and article here.
Hello folks,
In the first post in this series, we explored the overall capabilities
ABC is the one single place for all simplified backup needs. As mentioned before, everything in one interface one place to discover and configure, to operate and to govern. This is all well and good, however you still need to report your statuses so you can effectively:
- Allocating and forecasting of cloud storage consumed.
- Auditing of backups and restores.
- Identifying key trends at various levels of granularity.
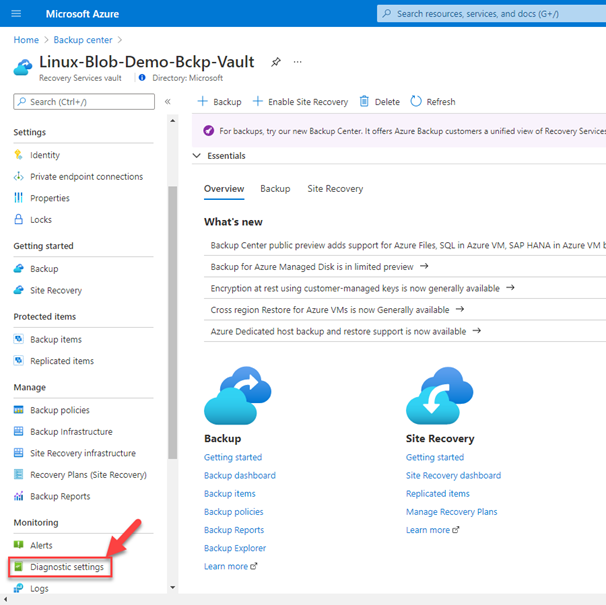
Therefore, in this final post we will review and dig into the optimization of those resources and capabilities. Like everything else in Azure, to analyze and report on resource usage, you need to link your operation to an Azure Monitor Logs workspace (formally Azure Log Analytics). The location and subscription where this Log Analytics workspace can be created is independent of the location and subscription where your vaults exist.
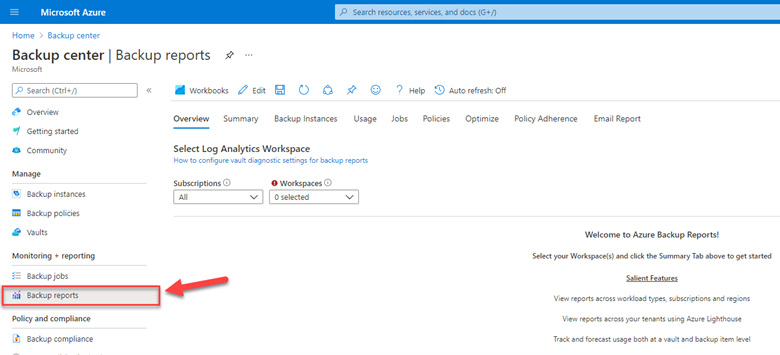
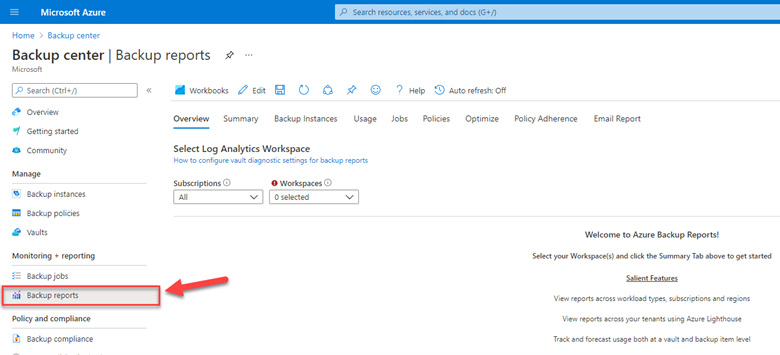
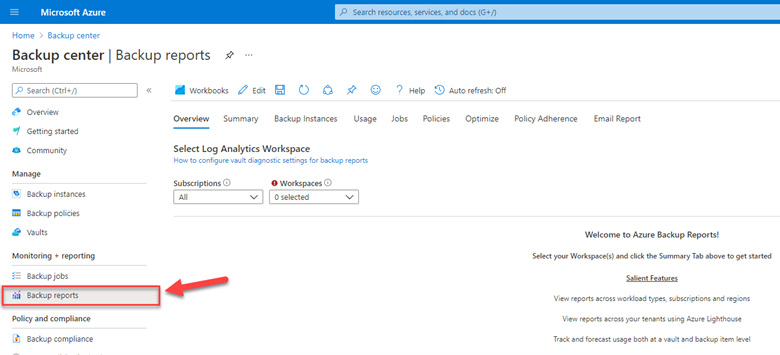
In ABC we view the integrated Backup reports from the vaults.
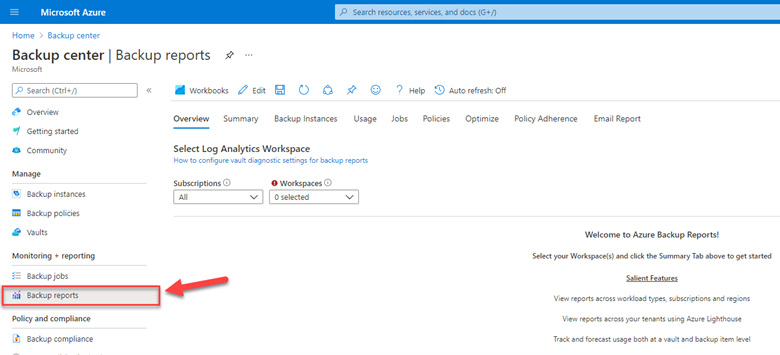
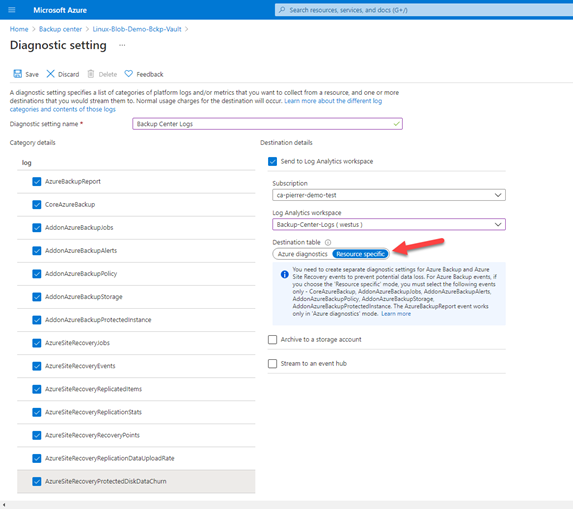
You’ll first need to configure your vaults to use an Azure Monitor Logs workspace in the vault’s diagnostic settings.
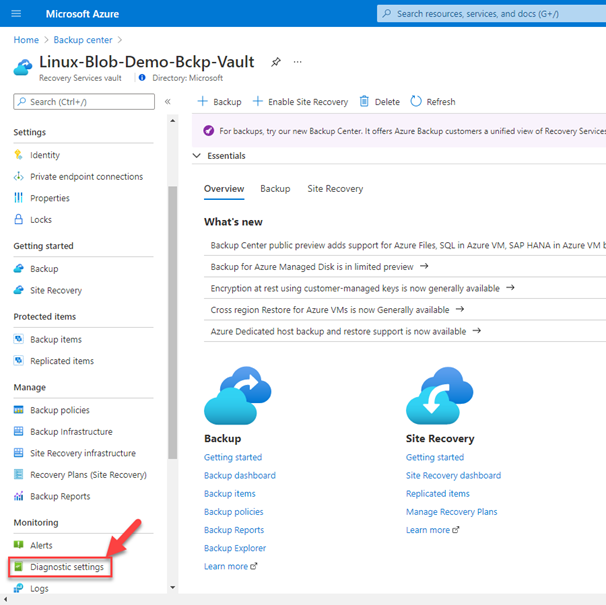
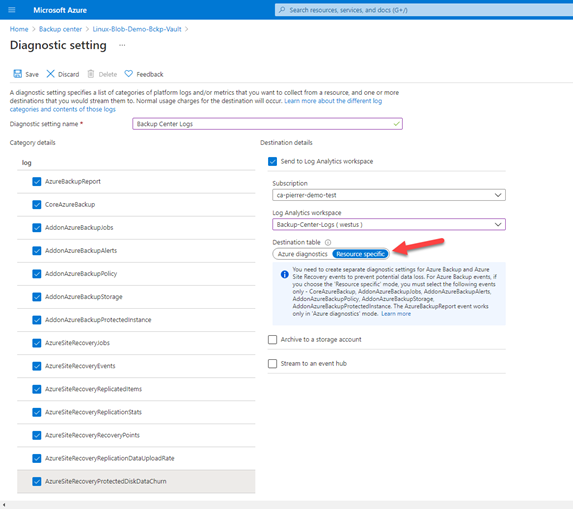
When configuring the vault’s diagnostics settings, you need to specify the logs you want to collect. You can pick from the list in the UI. (Remember that the data you ingest in Logs Analytics Workspace does come at a cost in the workspace.)
You’ll also need to ensure that you select “Resource specific” in the destination table field to send vault diagnostics data to dedicated Log Analytics tables for backup. Resource specific tables are individual tables in the selected workspace for each category selected in the diagnostic setting. This is recommended because it makes it much easier to work with the data in log queries, it provides better discoverability of schemas and their structure, improves performance across both ingestion latency and query times, and the ability to grant Azure RBAC rights on a specific table.
The reports will give you all the info you need regarding:
- Backup Instances
- Usage
- Jobs
- Policies
- Optimize
- Policy Adherence
Having access to all this telemetry enables you to make decisions regarding strategy, allocation and forecasting of cloud storage consumed by your backups.
The point here, is that Azure Backup Center centralizes the access to those reports to your tasks of managing your protection strategy.
- Learn more and get started with Backup center.
- Tell us how we can improve Azure Backup by contributing new ideas and voting up existing ones in the Azure Backup feedback forum.
I really hope this series was valuable for you and that Azure Backup Center is on your list of services to investigate.
Cheers!

by Contributed | May 5, 2021 | Technology
This article is contributed. See the original author and article here.
Universal Print now supports Windows 10 on ARM devices, such as Surface Pro X. As a modern, cloud-based print solution, Universal Print removes the need for on-premises print servers and enables endpoints to print to Azure AD-registered printers. Universal Print is the perfect match for cloud-first devices like Surface Pro X and helps enterprises unblock their move to the cloud.
With Universal Print, workers benefit from driverless printing, streamlined location-based printer discovery, and an intuitive printing experience. With Azure AD integration, workers use existing AAD credentials to print from workplace-joined devices.
Universal Print allows IT departments to configure their organization’s printers so that employees can print seamlessly from any device, and for organizations to lower the cost of printing, while supporting their business needs. Administrators can manage print infrastructure from the Universal Print admin portal and connect printers with native support for Universal Print.
The Universal Print API expands the capability and reach with an existing robust ecosystem of partner solutions.
To learn more about getting started, check out the Universal Print FAQ.


by Contributed | May 5, 2021 | Technology
This article is contributed. See the original author and article here.
By Marc Nahum Sr Program Manager | Microsoft Endpoint Manager – Intune
Any enterprise or education institution that owns iOS/iPadOS devices can take advantage of automatic enrollment to Intune, as well as the extra features and controls that Apple’s Automated Device Enrollment (ADE) – previously known as Device Enrollment Program (DEP) – provides.
When ADE was first introduced, only Apple resellers or telecom carriers were able to add devices to Apple Business Manager or Apple School Manager. However, since the release of iOS 11, Apple supports the ability to manually add iOS and iPadOS devices yourself with the Apple Configurator 2.5 (AC2) tool. This means that, regardless of where the device was purchased, you can benefit from using ABM or ASM.
This article will help IT pros and mobile device administrators understand the steps required to manually add iOS and iPadOS devices to Apple Business Manager or Apple School Manager, as well as enrolling them into the Intune service.
Note: Manually adding devices (new or old) is not supported for macOS. For these devices, the reseller must carry this out for you, no matter when they have been purchased.
Warning: The devices will be fully wiped during the process. This happens because Apple treats a device being in ABM as proof of ownership.
Before proceeding, there are some configurations, constraints, and restrictions to understand, after which the process is straightforward.
Prerequisites:
- A Mac device (desktop or laptop), running at least macOS Catalina (macOS 10.15.6 or later). This is mandatory as AC2 only runs on macOS.
- AC2 installed on the Mac from the App Store (Apple ID required). A version can be downloaded from the Apple developer site, but it requires an Apple developer membership account. This can be useful if you want to distribute the pkg with Intune on the Mac who will have to use it.
- Physical access to the iOS/iPadOS device, which must be connected to the Mac device running AC2. It must not have Apple’s “Find My” turned on (Activation Lock off).
- An ABM or ASM account with the role of “Device Enrollment Manager” assigned.
- A network profile in AC2 (steps detailed below) to allow the iOS or iPadOS device to connect to the Internet during the process.
- ABM or ASM configured with Microsoft Endpoint Manager as an MDM Server (Settings > Device Management Settings > Add MDM Server).
Preparing Apple Configurator:
There are a lot of options in AC2, so we will cover only the steps necessary to import the devices to ABM or ASM and assign them to the Microsoft Endpoint Manager MDM server. You can find full documentation from Apple here.
1. Creating a Wi-Fi profile
During the onboarding process, the device will need to connect to the internet. Therefore, it’s mandatory to have a Wi-Fi profile, which will allow it to automatically connect. The profile can be as complex as is required, but must not prompt the user for any action, or require a certificate to authenticate.
- In Apple Configurator go to the File menu and choose New Profile.
- Complete the Name of the profile in the mandatory General section.
- Complete the Wi-Fi section with your parameters.
- Once created, save it by clicking on the name on the top of the window. You can then close it and it will be used later.
 Screenshot of a Wi-Fi profile and configured settings in Apple Configurator 2
Screenshot of a Wi-Fi profile and configured settings in Apple Configurator 2
2. Generate MDM Server URL for Microsoft Endpoint Manager
Note: This step is not mandatory, but it will create a trusted configuration and avoid any doubts that the URL is the proper one.
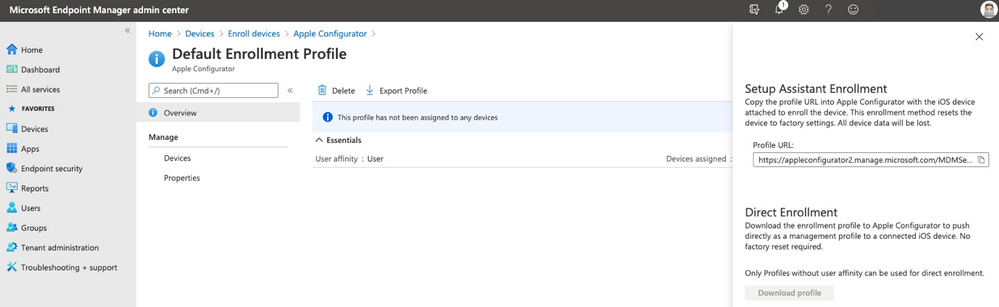
- Open Microsoft Endpoint Manager admin center.
- Select Devices, then navigate to Enroll devices > Apple enrollment > Apple Configurator.
- Select Profiles > Create.
- Complete all required fields with your desired configuration, then click Create.
- Select the profile you just created, then click Overview > Export Profile.
- Copy the Profile URL from the Setup Assistant Enrollment section on the right-hand side. This will be used later.
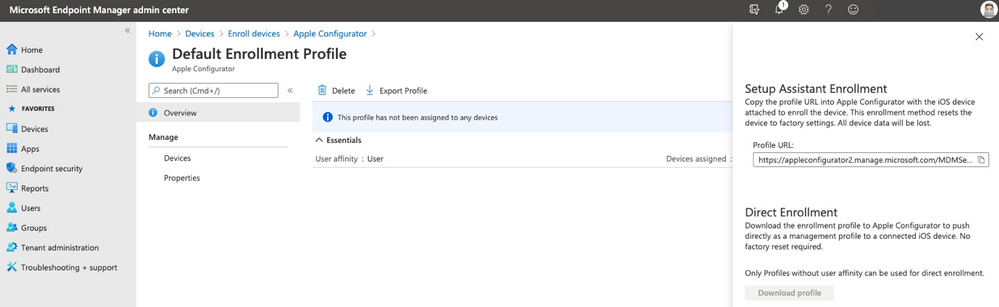 Screenshot of the Apple Configurator – Default Enrollment Profile in the Microsoft Endpoint Manager admin center
Screenshot of the Apple Configurator – Default Enrollment Profile in the Microsoft Endpoint Manager admin center
Connect the device to Apple Configurator
Important: The device will be fully wiped during this process.
If this is the first time you are connecting the device to the Mac, a pop up will appear asking for the Mac to be trusted, select Trust. Now the device is ready to be prepared.
- In Apple Configurator, select Prepare from the toolbar or by doing a secondary click on the picture of the device.
 Screenshot of Apple Configurator 2 with an arrow pointing to the “Prepare” option
Screenshot of Apple Configurator 2 with an arrow pointing to the “Prepare” option
- The below settings must be selected:
- Manual Configuration.
- Add to Apple School Manager or Apple Business Manager.
- Allow devices to pair with other computers.
Do not select:
- Activate and complete enrollment.
- Enable Shared iPad.
 Apple Configurator 2 – Prepare Devices” menu
Apple Configurator 2 – Prepare Devices” menu
- If this is the first time the operation is run on this Mac, you will have to create a “New Server” with the following details:
Name: “Microsoft Endpoint Management”
URL: The one created in the step “Generate MDM Server URL for MEM
Example URL: https://appleconfigurator2.manage.microsoft.com/MDMServiceConfig?id=<Intune_tenant_ID>&AADTenantId=<AAD_tenant_ID>
 Apple Configurator 2 – “Define an MDM Server” menu
Apple Configurator 2 – “Define an MDM Server” menu
Note: If you decided to skip the step of creating the dedicated URL from the Intune portal, you can simply use “https://endpoint.microsoft.com” and acknowledge the warning “Unable to verify the enrollment URL” as per below:
 Apple Configurator 2 – “Define an MDM Server” menu with the warning text: “Unable to verify the enrollment URL”
Apple Configurator 2 – “Define an MDM Server” menu with the warning text: “Unable to verify the enrollment URL”
- Add trust anchor certificate for MDM server.
- Select the one with the Microsoft or Azure name on the list (this should be appleconfigurator2.manage.microsoft.com or portal.azure.com or endpoint.microsoft.com)
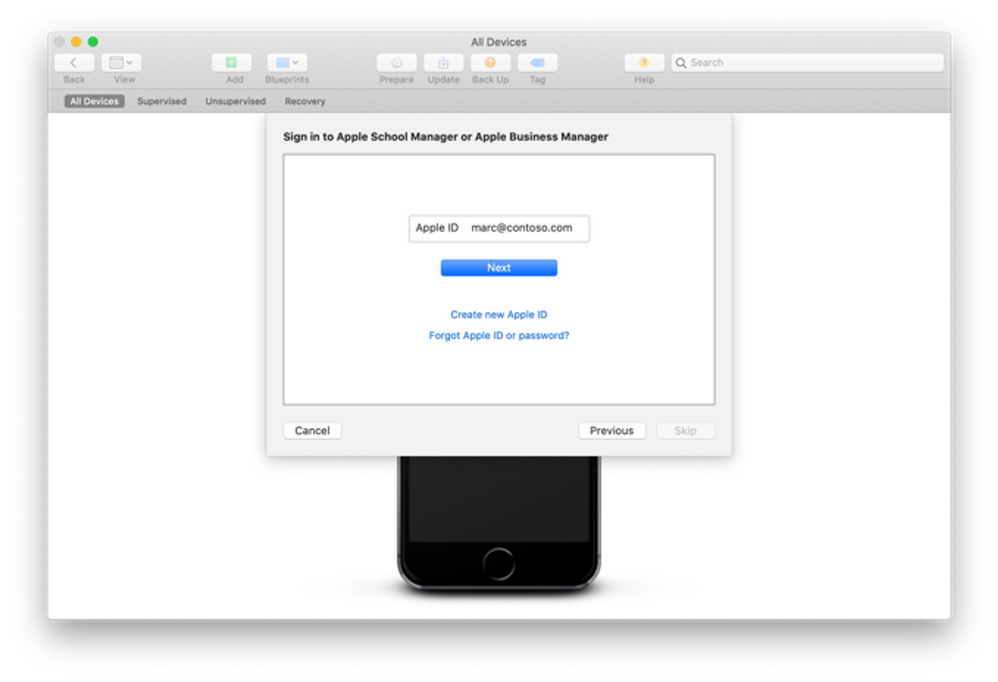
- Attach the device to your organization.
- Next, authenticate to ABM/ASM with an account with the “Device Enrollment Manager” role assigned.
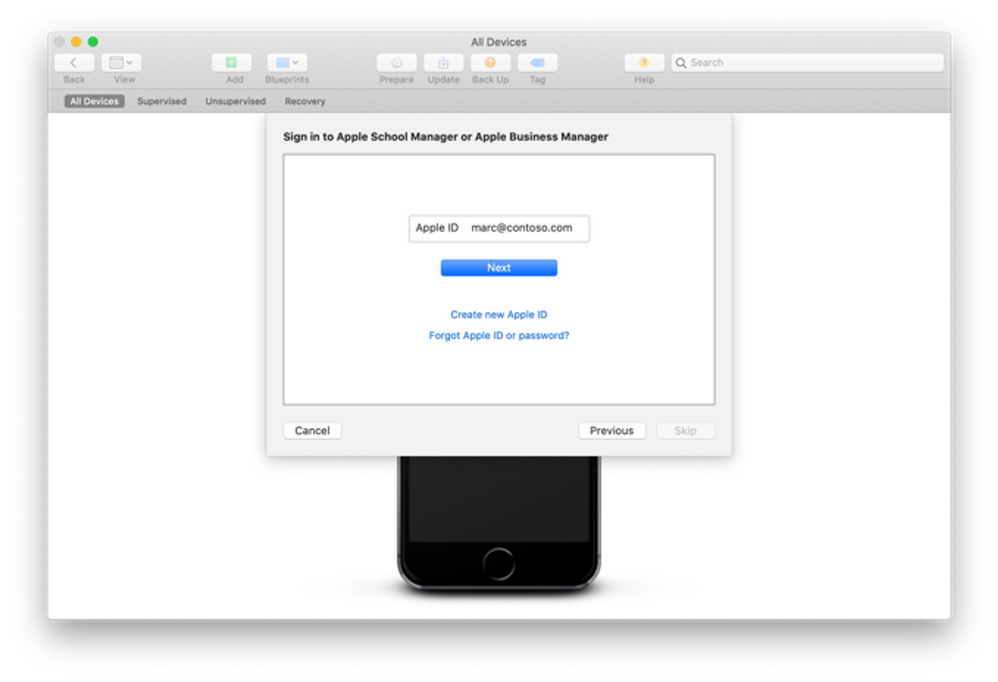 Apple Configurator 2 – Sign in to Apple School Manager or Apple Business Manager menu
Apple Configurator 2 – Sign in to Apple School Manager or Apple Business Manager menu
If you did not set up the organization name, you will need to do that next. That Organization name will be displayed on the device.
The iOS setup assistant steps selected on the next screen are not important as they will be defined in Intune later.
Next, select the Network Profile previously created and, when prompted, enter your local password to initiate the process.
At this point, the device will be erased. When the device has restarted, steps in AC2 are complete.
Log on your Apple management console
You now need to assign it to Intune in the ABM/ASM console. By default, it’s assigned to an MDM server configuration named “Apple Configurator 2”:
 Screenshot of an Apple iPhone 6 device in the ABM/ASM console Screenshot of an Apple iPhone 6 device in the ABM/ASM console |
 Screenshot of the ABM/ASM console with associated Apple devices Screenshot of the ABM/ASM console with associated Apple devices |
You can reassign 1 device by selecting that device and choosing:
Edit Device Management > Assign to server and select the proper Intune one. |
You can reassign multiple devices by doing the same with filters and choose “Edit Device Management” > “Apple Configurator 2” |
Microsoft Endpoint Manager admin center
Once the device is assigned it will need to be synchronized. This occurs automatically every 12 hours or you can manually trigger the synchronization in Microsoft Endpoint Manager admin center:
- Navigate to Devices > Enroll devices > Apple Enrollment> Enrollment program tokens and select your token name.
- Navigate to Devices and click Sync.
Note: You can manually synchronize the devices from ABM/ASM to Intune at a maximum frequency of every 15 minutes.
At this point you should have successfully added your ADE device to Intune.
Let us know if you have any questions by replying to this post or reaching out to @IntuneSuppTeam on Twitter.
![[Guest Blog] Stretch Goals will change your life](https://www.drware.com/wp-content/uploads/2021/05/fb_image-313.png)
by Contributed | May 5, 2021 | Technology
This article is contributed. See the original author and article here.
This blog is written by Jerry Weinstock, Microsoft Business Applications MVP. He shares how he set and pursued stretch goals to become a Business Applications MVP and author a white paper for Microsoft.

When you hear the term “Stretch Goals” it is usually in the context of performance metrics for sales people on quota or commission. I am going to tell you two stories where I have used stretch goals to take my career to the so-called next level by getting me out of my comfort zone and accomplishing bucket list items. Stretch goals are also for technology people!
When we think about goals they are generally conservative, somewhat routine and tend to be achievable and perhaps expected to be accomplished. Do not confuse it with “doing your job” and getting a positive review along with the standard merit increase. New Year’s Resolutions are not stretch goals!
A stretch goal is an objective that you set for yourself that is extremely difficult to achieve. It is over and above your normal activities or the results that others expect you to achieve. While there are many ways to define a stretch goal, in my life I have defined it by two criteria; it will take me well out of my comfort zone, requiring me to “stretch” well past my current level of activities and skill level; and it will be something when achieved, is “braggable” either in a personal or business setting. It could also be a bucket list accomplishment but not everything that might fall into a bucket list checklist is a stretch goal.
So now that we have a baseline for stretch goals, let me tell you about two stretch goals that took me well out of my comfort zone, provided some things I could brag about, and catapulted my career to another level.
Microsoft CRM Team Blog – My path to becoming a MVP
Back in the early days – circa 2007-2009, the Microsoft CRM Team Blog (that was its’ name then) was just about the only place online that you could find new product information being posted. We did not have Facebook or Twitter the way it’s used today, nor Linkedin. Additionally, very few people were blogging on their own website. It was the one place you went to almost every day to get the latest CRM news.
I had been voraciously consuming the blog posts as soon as they came out, applying the new found knowledge to projects for my clients. I had noticed a pattern that some of the posts were being made by non-Microsoft people and labeled as “guest posts”. After a while of seeing these posts, I began to think that I had equally good information to share as these guest bloggers. I just had never done anything like that before and I had no clue how to break into the process. All I knew was that all the guest bloggers were MVPs. While I had no direct exposure to these people I knew from seeing them at events and their entourage that they seemed a step ahead of all the other consultants.
So while I had given no thought to becoming an MVP, I also had no clue where to begin the process. I got it in my head that if I tried, I could write equally valuable blog content. I started working on several candidate posts that went through dozens of iterations. Finally, when I had something that I thought might work, I tracked down Jim Glaas who, at the time, ran the MVP program and managed the team blog. After pinging him with emails, I finally connected with him and we started the process. The first post I submitted was turned down because it was based on what the product team assessed as unsupported methods. I was devastated and almost retreated. The second submission I came up with was accepted and on September 9, 2009 the first post appeared – A Plethora of Phone Attributes.
After successfully getting one post accepted and basking in the glory for a few minutes (my family wasn’t impressed), I set out to see if I could continue to stretch and repeat the accomplishment. I had several more published, one of them is as follows:

Concurrent with the posting of the Marketing list post, I received an email from Jim asking why I wasn’t a CRM MVP. He advised that if I spent a lot of time in the CRM forum, it would greatly boost my chances. I took him up on it without knowing much about the MVP program, but I felt confident that if I pushed myself, I could demonstrate I was equally qualified.
I received the MVP Application form in January 2010. I then set out to diligently become more active on the community forums. Every morning, as soon as I got to the office, I went to the forums and tried to answer the questions that had been posted the night before. In many cases I actually had to create the submitters’ scenario in CRM to come up with the answer. This went on for months, sometimes my real work didn’t get started for 2+ hours after the day began.
I applied to the MVP program with the formal application in April and was notified that I had been turned down and to re-apply. I decided to ramp it up even more and delivered another guest post and stretched myself to answer even more complex questions on the forums.
On October 1, 2010 I received the email letting me know that I had been recognized for my community activities and entered the MVP program. It is coming up on 11 years now and I consider it the single biggest professional stretch goal I have accomplished. It has had more impact on my business and personal life than any other career event. Put your mind to it and stretch yourself, you can do it also if you want it.
Microsoft White Paper – Power Automate Flow
Just like I had been observing the guest posts by MVPs circa 2008, I had been consuming Microsoft White Papers. I always marveled over the value of the content along with the prestige that seemed to come to people that were skilled enough to put them together. I had jumped on Microsoft Flow when it was first introduced and felt it was the most powerful tool that the product team had given to functional consultants in the life of the product. After blogging, speaking, and answering forum questions for the first two years I believed I had defined myself as the go to person in the community for Flow and Dynamics 365.
I decided to set my next stretch goal – to firmly establish myself at the pinnacle of Flow and Dynamics 365. After a long and brand new process that took me through selling the idea to Microsoft and then actually delivering on what I told them I could do, in August of 2009 the Flow white paper was released. Did I stretch myself? You bet, the paper went through four iterations with Microsoft and I invested three times the amount of hours that I had originally estimated but I was ecstatic when it was released. It certainly falls into the braggable category. Would I do it again? I could but probably wouldn’t and perhaps that is the third criteria of a stretch goal – something you achieve but only need to do once.
So that kind of sums it up – get out of the routine, think big, take yourself to the next level, accomplish something that no one around you has, look to the leaders that you know, set a stretch goal for yourself and when you achieve it – tell the world. You will have a smiling grin on your face.
by Contributed | May 5, 2021 | Technology
This article is contributed. See the original author and article here.
Last year we released the Reply-all Storm Protection feature to help protect your organization from unwanted reply-all storms. This feature uses global settings applicable to all Microsoft 365 customers for reply-all storm detection and for how long the feature will block subsequent reply-alls once a storm has been detected. Today we’re pleased to announce you’ll now have the ability to make these settings specific to your Microsoft 365 organization; email admins will have the flexibility to enable/disable the feature, and set customized detection thresholds and block duration time. This not only makes it more flexible to tailor for your organization, but it also allows more Microsoft 365 customers to take advantage of the Reply-all Storm Protection feature since the minimum number of reply-all recipients for detection can now be as low as 1000 when previously it was hard-coded at 5000.
The current Reply-all Storm Protection settings for Microsoft 365 are as follows:
Setting
|
Default
|
Enabled/disabled
|
Enabled
|
Minimum number of recipients
|
5000
|
Minimum number of reply-alls
|
10
|
Detection time sliding window
|
60 minutes
|
Block duration (once detected)
|
4 hours
|
Based on our telemetry and customer feedback we’re also taking this opportunity to update a few of the default settings. Once this change has rolled out, the default settings for each Microsoft 365 organization will be the following:
Setting
|
Default
|
Enabled/disabled
|
Enabled
|
Minimum number of recipients
|
2500 (previously 5000)
|
Minimum number of reply-alls
|
10
|
Detection time sliding window
|
60 minutes
|
Block duration (once detected)
|
6 hours (previously 4 hours)
|
The customizations possible for each setting will be as follows:
Setting
|
Customizable options
|
Enabled/disabled
|
Enabled or Disabled
|
Minimum number of recipients
|
1000 to 5000
|
Minimum number of reply-alls
|
5 to 20
|
Detection time sliding window
|
60 minutes (not customizable)
|
Block duration (once detected)
|
1 to 12 hours
|
Admins will be able to use the Set-TransportConfig Remote PowerShell cmdlet to update the settings for their organization:
Setting
|
Cmdlet
|
Enabled/disabled
|
Set-TransportConfig -ReplyAllStormProtectionEnabled [$True:$False]
|
Number of recipients threshold
|
Set-TransportConfig -ReplyAllStormDetectionMinimumRecipients [1000 – 5000]
|
Number of reply-alls threshold
|
Set-TransportConfig -ReplyAllStormDetectionMinimumReplies [5 – 20]
|
Block duration
|
Set-TransportConfig -ReplyAllStormBlockDuration [1 – 12]
|
These updates are rolling out now and should be fully available to all Microsoft 365 customers by mid-June. While this should come as a welcome update for customers wanting to better take advantage of the Reply-all Storm Protection feature, we are not done yet! In future updates we plan to provide an insight, report, and optional notifications for the feature as well. And if there’s enough customer feedback for it, we’ll consider also exposing the ability to customize these settings in the Exchange Admin Center. Let us know what you think!
The Exchange Transport Team









![[Guest Blog] Stretch Goals will change your life](https://www.drware.com/wp-content/uploads/2021/05/fb_image-313.png)


Recent Comments