by Contributed | Nov 29, 2021 | Technology
This article is contributed. See the original author and article here.
We hope you enjoyed Ignite 2021! We loved hearing from you and learning how you’re using Azure Active Directory to implement Zero Trust to protect users and applications from threats. Many of you have asked for more empowering and easier to use tools for protection and investigation in your identity environment. So today we’re delighted to offer a closer look at the new Azure AD Conditional Access and Identity Protection capabilities that help you better protect your identities while making your job easier.
New capabilities in Azure AD Conditional Access and Identity Protection
This Ignite, we announced a powerful set of capabilities that make Conditional Access easier to use and empower you with insights that help accelerate your Zero Trust deployments and give you more comprehensive protection for key scenarios. The Conditional Access overview dashboard (in public preview) empowers you to quickly find gaps in your policy coverage, while templates make it much easier to deploy recommended policies. Filters for devices and filters for apps (generally available) unlock new scenarios like restricting admin access to privileged workstations, giving you more comprehensive scenario coverage in key scenarios. Finally, we have made it easier to export risk data (including the new token signals!) and built a really cool new workbook to give you insight on risks (and what to do about it)!
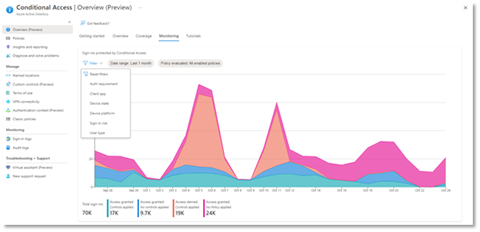
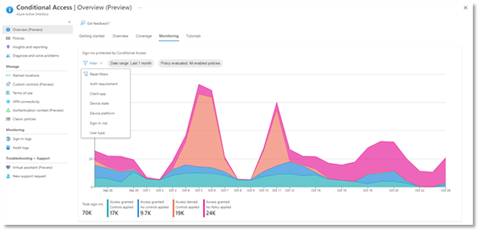
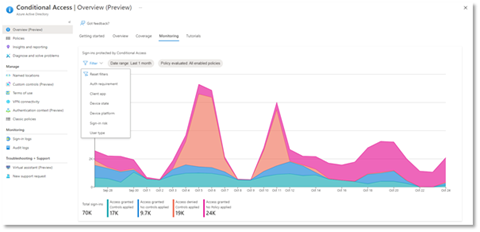
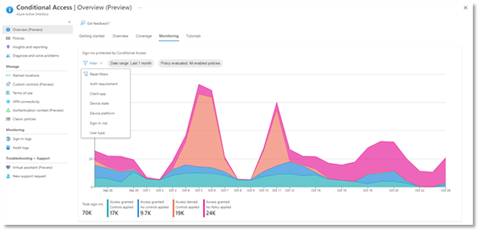
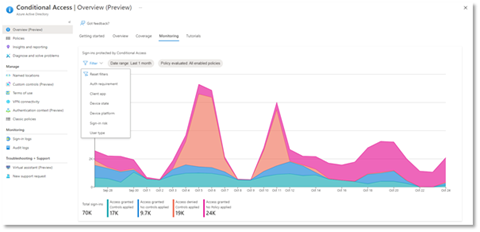
Conditional Access overview dashboard
Let’s dive into the Conditional Access overview dashboard first. As organizations deploy an increasing number of policies, one of the biggest challenges admins face is understanding whether their policies are truly protecting their entire organization. The new Conditional Access overview dashboard makes it easier than ever to deploy comprehensive policies by summarizing users, apps, and devices in scope of your policies and highlighting gaps in your policy coverage.
The dashboard is comprised of four main tabs:
- Getting started: If you are new to Conditional Access, learn about policy components and create a new policy.
- Overview: Get a quick summary of your users, devices, and applications protected by Conditional Access. You can also view policy recommendations based on sign-in activity data in your tenant and quickly deploy policies from policy templates.
- Coverage: Ensure the most commonly accessed applications in your tenant are protected by Conditional Access.
- Monitoring: Visualize the impact of each policy in your tenant and add filters to see trends like guest access, legacy authentication, risky sign-ins and unmanaged devices.
- Tutorials: Learn about commonly deployed Conditional Access policies and best practices.
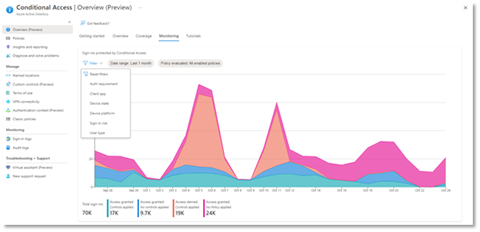
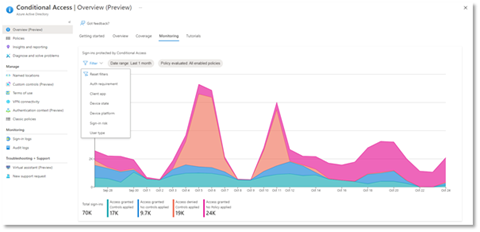
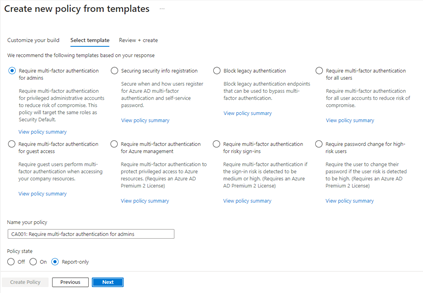
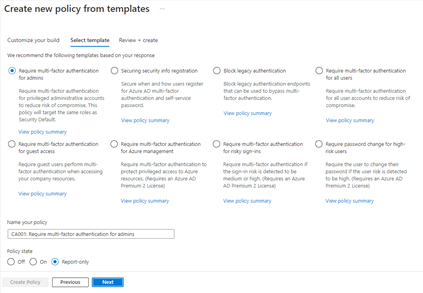
Conditional Access Templates
Additionally, to provide a simple and sample method for deploying new policies that align with Microsoft recommended best practices and help you respond to evolving threats, we also announced Conditional Access templates. These templates help you provide maximum protection for your users and devices and align with the commonly used policies across many different customer types and locations.
You can quickly create a new policy from any of the 14 built-in templates (we’ll add to these based on your input, new capabilities and in response to new attack types). Deploying your policies from templates is simple. It may be all you need to do, but you can also start from a template and custom tune it to meet your business needs.
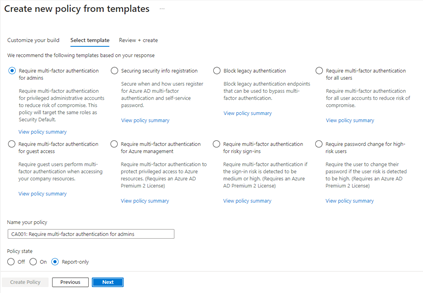 Figure 1: Admin experience for Conditional Access templates
Figure 1: Admin experience for Conditional Access templates
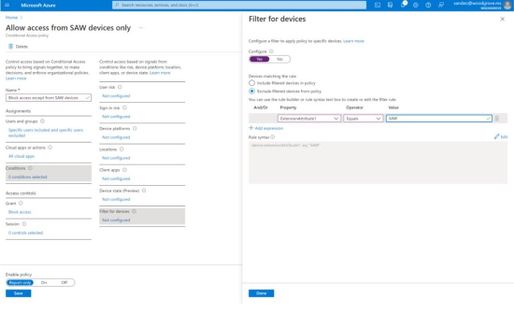
Conditional Access Filters for Devices
With filters for devices, security admins can target Conditional Access policies to a set of devices based on device attributes. This capability unlocks many new scenarios you have asked for, such as requiring privileged access workstations to access key resources. You can also use the device filters condition to secure the use of IoT devices (including Teams meeting rooms). Surface Hubs, Teams phones, Teams meeting rooms, and all sorts of IoT devices. We designed filters for devices to match the existing rule authoring experiences in Azure AD dynamic groups and Microsoft Endpoint Manager.
In addition to the built-in device properties such as device ID, display name, model, Mobile Device Management (MDM) app ID, and more, we’ve provided support for up to 15 additional extension attributes. Using the rule builder, admins can easily build device matching rules using Boolean logic, or they can edit the rule syntax directly to unlock even more sophisticated matching rules. We’re excited to see what scenarios this new condition unlocks for your organization!
 Figure 2: Admin experience for filters for devices
Figure 2: Admin experience for filters for devices
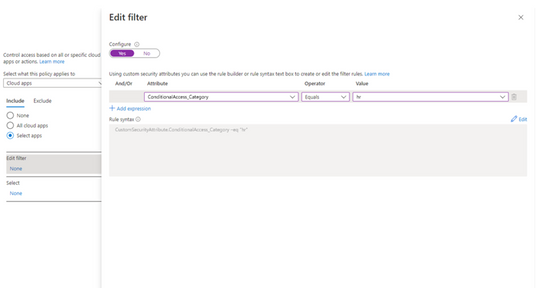
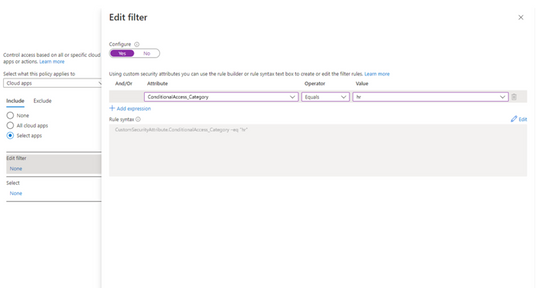
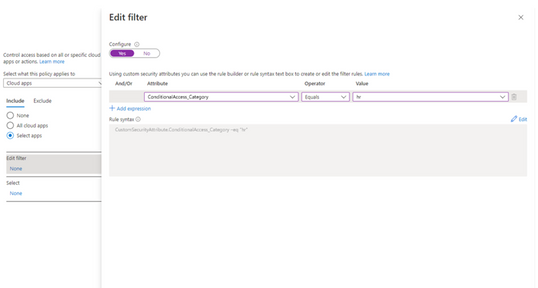
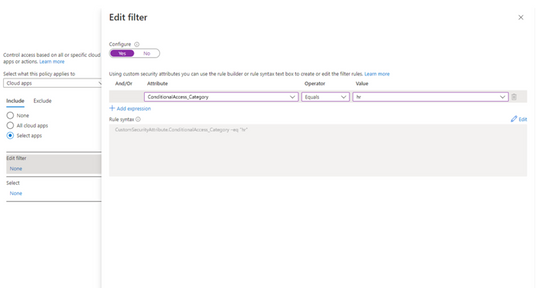
Filters for apps
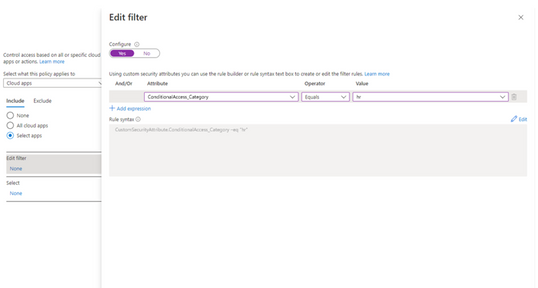
In addition to filters for devices, you can also use filters for applications in Conditional Access. We’ve heard from customers that with the explosion of apps in their tenants, they need an easier way to apply policies to their apps at scale. Filters for apps will allow improved Conditional Access app targeting based on custom security attributes. Simply tag groups of apps with a custom security attribute and then apply policy directly to apps with the attribute, rather than individually selecting all the apps. When new apps are onboarded, you only need to add the attribute to the app, rather than updating your policy.
Filters for apps use the new Azure AD custom security attributes. These are created and managed by each organization, so you can define attributes that work for you and use them in Conditional Access policy. Custom security attributes also support a rich delegation model, allowing you to select which users have permission to add specific attributes to apps and preventing app owners from making changes to these attributes. This makes it easy to have a set of admins manage app onboarding to Conditional Access policy without requiring them modify the policy and risk accidental changes. Conditional Access filters for apps will be available soon in public preview.
New export options in Diagnostic Settings
With our rich detections and signals in identity protection, we are now making it easier for you to leverage this risk data to understand trends in your environment with two major improvements.
The first improvement is expanded Diagnostic Settings, where we added new ways for you to export your risk data. Now with just one click, you can send your risky users and risk detections data to Log Analytics or your third party SIEM of choice. To address your need to retain this data beyond our built-in retention periods, we have enabled another simple click for you to send months of data to a storage account.
 Figure 3: Admin experience for identity protection diagnostic settings
Figure 3: Admin experience for identity protection diagnostic settings
Risk Analysis Workbook
We also heard your requests for deeper, easily configurable insights into risk trends in your organization. Built upon Log Analytics and the expanded Diagnostic Settings, we released a new Risk Analysis Workbook for Identity Protection. This workbook shows the types of risks that are most prevalent and where you are seeing them in the world. Additionally, you now have visibility into how effectively you are responding to risk detected in your environment and the workbook highlights opportunities for improved policy configuration.
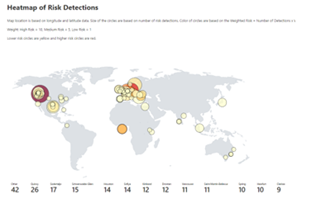
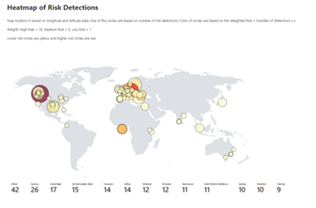
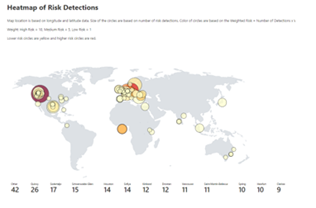 Figure 4. Admin experience for identity protection risk analysis workbook
Figure 4. Admin experience for identity protection risk analysis workbook
To use the new workbook
- Sign in to the Azure portal.
- Navigate to Azure Active Directory > Monitoring > Workbooks.
- Click on “Identity Protection Risk Analysis”
We hope these new capabilities in Conditional Access make it even easier for you to deploy Zero Trust and unlock a new wave of scenarios for your organization. And the two Identity Protection capabilities help you understand your environment with simplicity yet come with powerful insights. As always, we are actively listening to your feedback. Join the conversation in the Microsoft Tech Community and share your feedback and suggestions with us.
Learn more about Microsoft identity:
by Contributed | Nov 29, 2021 | Technology
This article is contributed. See the original author and article here.
We hope you enjoyed Ignite 2021! We loved hearing from you and learning how you’re using Azure Active Directory to implement Zero Trust to protect users and applications from threats. Many of you have asked for more empowering and easier to use tools for protection and investigation in your identity environment. So today we’re delighted to offer a closer look at the new Azure AD Conditional Access and Identity Protection capabilities that help you better protect your identities while making your job easier.
New capabilities in Azure AD Conditional Access and Identity Protection
This Ignite, we announced a powerful set of capabilities that make Conditional Access easier to use and empower you with insights that help accelerate your Zero Trust deployments and give you more comprehensive protection for key scenarios. The Conditional Access overview dashboard (in public preview) empowers you to quickly find gaps in your policy coverage, while templates make it much easier to deploy recommended policies. Filters for devices and filters for apps (generally available) unlock new scenarios like restricting admin access to privileged workstations, giving you more comprehensive scenario coverage in key scenarios. Finally, we have made it easier to export risk data (including the new token signals!) and built a really cool new workbook to give you insight on risks (and what to do about it)!
Conditional Access overview dashboard
Let’s dive into the Conditional Access overview dashboard first. As organizations deploy an increasing number of policies, one of the biggest challenges admins face is understanding whether their policies are truly protecting their entire organization. The new Conditional Access overview dashboard makes it easier than ever to deploy comprehensive policies by summarizing users, apps, and devices in scope of your policies and highlighting gaps in your policy coverage.
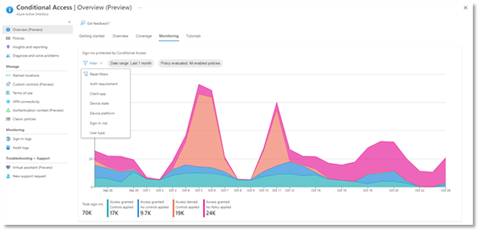
The dashboard is comprised of four main tabs:
- Getting started: If you are new to Conditional Access, learn about policy components and create a new policy.
- Overview: Get a quick summary of your users, devices, and applications protected by Conditional Access. You can also view policy recommendations based on sign-in activity data in your tenant and quickly deploy policies from policy templates.
- Coverage: Ensure the most commonly accessed applications in your tenant are protected by Conditional Access.
- Monitoring: Visualize the impact of each policy in your tenant and add filters to see trends like guest access, legacy authentication, risky sign-ins and unmanaged devices.
- Tutorials: Learn about commonly deployed Conditional Access policies and best practices.
Conditional Access Templates
Additionally, to provide a simple and sample method for deploying new policies that align with Microsoft recommended best practices and help you respond to evolving threats, we also announced Conditional Access templates. These templates help you provide maximum protection for your users and devices and align with the commonly used policies across many different customer types and locations.
You can quickly create a new policy from any of the 14 built-in templates (we’ll add to these based on your input, new capabilities and in response to new attack types). Deploying your policies from templates is simple. It may be all you need to do, but you can also start from a template and custom tune it to meet your business needs.
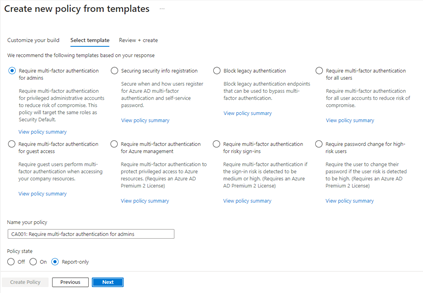 Figure 1: Admin experience for Conditional Access templates
Figure 1: Admin experience for Conditional Access templates
Conditional Access Filters for Devices
With filters for devices, security admins can target Conditional Access policies to a set of devices based on device attributes. This capability unlocks many new scenarios you have asked for, such as requiring privileged access workstations to access key resources. You can also use the device filters condition to secure the use of IoT devices (including Teams meeting rooms). Surface Hubs, Teams phones, Teams meeting rooms, and all sorts of IoT devices. We designed filters for devices to match the existing rule authoring experiences in Azure AD dynamic groups and Microsoft Endpoint Manager.
In addition to the built-in device properties such as device ID, display name, model, Mobile Device Management (MDM) app ID, and more, we’ve provided support for up to 15 additional extension attributes. Using the rule builder, admins can easily build device matching rules using Boolean logic, or they can edit the rule syntax directly to unlock even more sophisticated matching rules. We’re excited to see what scenarios this new condition unlocks for your organization!
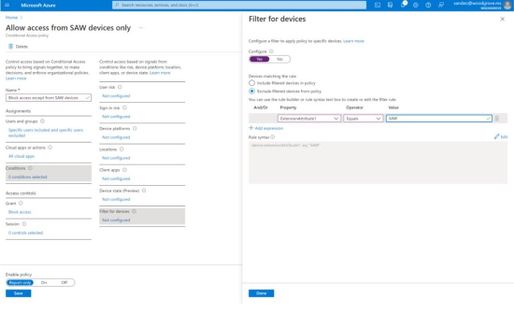 Figure 2: Admin experience for filters for devices
Figure 2: Admin experience for filters for devices
Filters for apps
In addition to filters for devices, you can also use filters for applications in Conditional Access. We’ve heard from customers that with the explosion of apps in their tenants, they need an easier way to apply policies to their apps at scale. Filters for apps will allow improved Conditional Access app targeting based on custom security attributes. Simply tag groups of apps with a custom security attribute and then apply policy directly to apps with the attribute, rather than individually selecting all the apps. When new apps are onboarded, you only need to add the attribute to the app, rather than updating your policy.
Filters for apps use the new Azure AD custom security attributes. These are created and managed by each organization, so you can define attributes that work for you and use them in Conditional Access policy. Custom security attributes also support a rich delegation model, allowing you to select which users have permission to add specific attributes to apps and preventing app owners from making changes to these attributes. This makes it easy to have a set of admins manage app onboarding to Conditional Access policy without requiring them modify the policy and risk accidental changes. Conditional Access filters for apps will be available soon in public preview.
New export options in Diagnostic Settings
With our rich detections and signals in identity protection, we are now making it easier for you to leverage this risk data to understand trends in your environment with two major improvements.
The first improvement is expanded Diagnostic Settings, where we added new ways for you to export your risk data. Now with just one click, you can send your risky users and risk detections data to Log Analytics or your third party SIEM of choice. To address your need to retain this data beyond our built-in retention periods, we have enabled another simple click for you to send months of data to a storage account.
 Figure 3: Admin experience for identity protection diagnostic settings
Figure 3: Admin experience for identity protection diagnostic settings
Risk Analysis Workbook
We also heard your requests for deeper, easily configurable insights into risk trends in your organization. Built upon Log Analytics and the expanded Diagnostic Settings, we released a new Risk Analysis Workbook for Identity Protection. This workbook shows the types of risks that are most prevalent and where you are seeing them in the world. Additionally, you now have visibility into how effectively you are responding to risk detected in your environment and the workbook highlights opportunities for improved policy configuration.
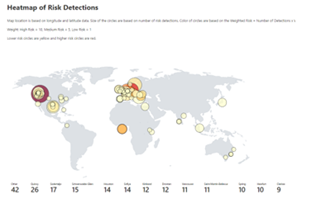 Figure 4. Admin experience for identity protection risk analysis workbook
Figure 4. Admin experience for identity protection risk analysis workbook
To use the new workbook
- Sign in to the Azure portal.
- Navigate to Azure Active Directory > Monitoring > Workbooks.
- Click on “Identity Protection Risk Analysis”
We hope these new capabilities in Conditional Access make it even easier for you to deploy Zero Trust and unlock a new wave of scenarios for your organization. And the two Identity Protection capabilities help you understand your environment with simplicity yet come with powerful insights. As always, we are actively listening to your feedback. Join the conversation in the Microsoft Tech Community and share your feedback and suggestions with us.
Learn more about Microsoft identity:
by Contributed | Nov 29, 2021 | Technology
This article is contributed. See the original author and article here.
We hope you enjoyed Ignite 2021! We loved hearing from you and learning how you’re using Azure Active Directory to implement Zero Trust to protect users and applications from threats. Many of you have asked for more empowering and easier to use tools for protection and investigation in your identity environment. So today we’re delighted to offer a closer look at the new Azure AD Conditional Access and Identity Protection capabilities that help you better protect your identities while making your job easier.
New capabilities in Azure AD Conditional Access and Identity Protection
This Ignite, we announced a powerful set of capabilities that make Conditional Access easier to use and empower you with insights that help accelerate your Zero Trust deployments and give you more comprehensive protection for key scenarios. The Conditional Access overview dashboard (in public preview) empowers you to quickly find gaps in your policy coverage, while templates make it much easier to deploy recommended policies. Filters for devices and filters for apps (generally available) unlock new scenarios like restricting admin access to privileged workstations, giving you more comprehensive scenario coverage in key scenarios. Finally, we have made it easier to export risk data (including the new token signals!) and built a really cool new workbook to give you insight on risks (and what to do about it)!
Conditional Access overview dashboard
Let’s dive into the Conditional Access overview dashboard first. As organizations deploy an increasing number of policies, one of the biggest challenges admins face is understanding whether their policies are truly protecting their entire organization. The new Conditional Access overview dashboard makes it easier than ever to deploy comprehensive policies by summarizing users, apps, and devices in scope of your policies and highlighting gaps in your policy coverage.
The dashboard is comprised of four main tabs:
- Getting started: If you are new to Conditional Access, learn about policy components and create a new policy.
- Overview: Get a quick summary of your users, devices, and applications protected by Conditional Access. You can also view policy recommendations based on sign-in activity data in your tenant and quickly deploy policies from policy templates.
- Coverage: Ensure the most commonly accessed applications in your tenant are protected by Conditional Access.
- Monitoring: Visualize the impact of each policy in your tenant and add filters to see trends like guest access, legacy authentication, risky sign-ins and unmanaged devices.
- Tutorials: Learn about commonly deployed Conditional Access policies and best practices.
Conditional Access Templates
Additionally, to provide a simple and sample method for deploying new policies that align with Microsoft recommended best practices and help you respond to evolving threats, we also announced Conditional Access templates. These templates help you provide maximum protection for your users and devices and align with the commonly used policies across many different customer types and locations.
You can quickly create a new policy from any of the 14 built-in templates (we’ll add to these based on your input, new capabilities and in response to new attack types). Deploying your policies from templates is simple. It may be all you need to do, but you can also start from a template and custom tune it to meet your business needs.
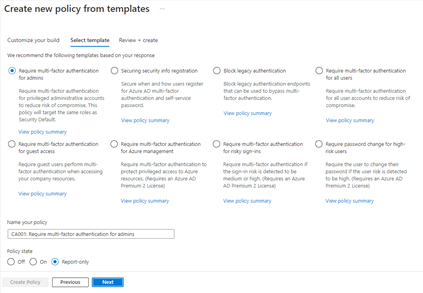 Figure 1: Admin experience for Conditional Access templates
Figure 1: Admin experience for Conditional Access templates
Conditional Access Filters for Devices
With filters for devices, security admins can target Conditional Access policies to a set of devices based on device attributes. This capability unlocks many new scenarios you have asked for, such as requiring privileged access workstations to access key resources. You can also use the device filters condition to secure the use of IoT devices (including Teams meeting rooms). Surface Hubs, Teams phones, Teams meeting rooms, and all sorts of IoT devices. We designed filters for devices to match the existing rule authoring experiences in Azure AD dynamic groups and Microsoft Endpoint Manager.
In addition to the built-in device properties such as device ID, display name, model, Mobile Device Management (MDM) app ID, and more, we’ve provided support for up to 15 additional extension attributes. Using the rule builder, admins can easily build device matching rules using Boolean logic, or they can edit the rule syntax directly to unlock even more sophisticated matching rules. We’re excited to see what scenarios this new condition unlocks for your organization!
 Figure 2: Admin experience for filters for devices
Figure 2: Admin experience for filters for devices
Filters for apps
In addition to filters for devices, you can also use filters for applications in Conditional Access. We’ve heard from customers that with the explosion of apps in their tenants, they need an easier way to apply policies to their apps at scale. Filters for apps will allow improved Conditional Access app targeting based on custom security attributes. Simply tag groups of apps with a custom security attribute and then apply policy directly to apps with the attribute, rather than individually selecting all the apps. When new apps are onboarded, you only need to add the attribute to the app, rather than updating your policy.
Filters for apps use the new Azure AD custom security attributes. These are created and managed by each organization, so you can define attributes that work for you and use them in Conditional Access policy. Custom security attributes also support a rich delegation model, allowing you to select which users have permission to add specific attributes to apps and preventing app owners from making changes to these attributes. This makes it easy to have a set of admins manage app onboarding to Conditional Access policy without requiring them modify the policy and risk accidental changes. Conditional Access filters for apps will be available soon in public preview.
New export options in Diagnostic Settings
With our rich detections and signals in identity protection, we are now making it easier for you to leverage this risk data to understand trends in your environment with two major improvements.
The first improvement is expanded Diagnostic Settings, where we added new ways for you to export your risk data. Now with just one click, you can send your risky users and risk detections data to Log Analytics or your third party SIEM of choice. To address your need to retain this data beyond our built-in retention periods, we have enabled another simple click for you to send months of data to a storage account.
 Figure 3: Admin experience for identity protection diagnostic settings
Figure 3: Admin experience for identity protection diagnostic settings
Risk Analysis Workbook
We also heard your requests for deeper, easily configurable insights into risk trends in your organization. Built upon Log Analytics and the expanded Diagnostic Settings, we released a new Risk Analysis Workbook for Identity Protection. This workbook shows the types of risks that are most prevalent and where you are seeing them in the world. Additionally, you now have visibility into how effectively you are responding to risk detected in your environment and the workbook highlights opportunities for improved policy configuration.
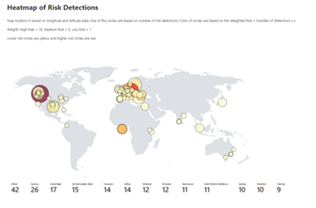 Figure 4. Admin experience for identity protection risk analysis workbook
Figure 4. Admin experience for identity protection risk analysis workbook
To use the new workbook
- Sign in to the Azure portal.
- Navigate to Azure Active Directory > Monitoring > Workbooks.
- Click on “Identity Protection Risk Analysis”
We hope these new capabilities in Conditional Access make it even easier for you to deploy Zero Trust and unlock a new wave of scenarios for your organization. And the two Identity Protection capabilities help you understand your environment with simplicity yet come with powerful insights. As always, we are actively listening to your feedback. Join the conversation in the Microsoft Tech Community and share your feedback and suggestions with us.
Learn more about Microsoft identity:

by Contributed | Nov 29, 2021 | Technology
This article is contributed. See the original author and article here.
Building fast, fluid Microsoft 365 web applications is one of our core focus areas on the SharePoint engineering team. Over the course of this year, we’ve double-downed on performance – making our web apps load faster, delivering up to a 57% improvement in page interactivity, along with the ability to work with data offline. We’re pleased to announce we’ve reached general availability for Microsoft Lists customers. The focus of this article is to share how it all works and how we went about designing and developing it.
 We’re pleased to announce that we’ve reached general availability for Microsoft Lists: Fast and offline.
We’re pleased to announce that we’ve reached general availability for Microsoft Lists: Fast and offline.
And we didn’t stop there. Our ambition is to deliver experiences that are consistently fast for every user on all kinds of networks and devices – even when there is no connection to the Internet. To help us accomplish this, we looked beyond the fundamentals to unlock new levels of web performance and enable new ways for our customers to experience Microsoft 365 web applications. We do this by blending Progressive Web Apps (PWAs) and expanding Project Nucleus.
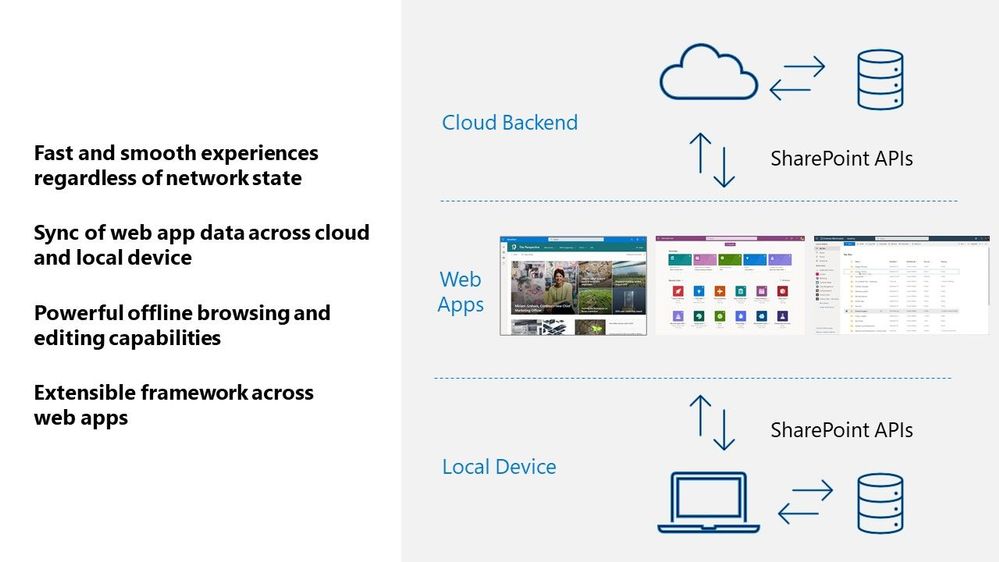
 The combination of Progressive Web Apps (PWAs) and the expansion of Project Nucleus enables faster Web applications – even when offline.
The combination of Progressive Web Apps (PWAs) and the expansion of Project Nucleus enables faster Web applications – even when offline.
Transforming Microsoft 365 apps into PWAs
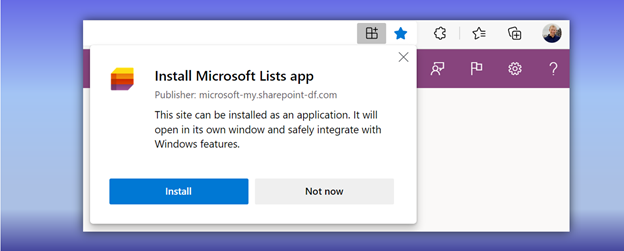
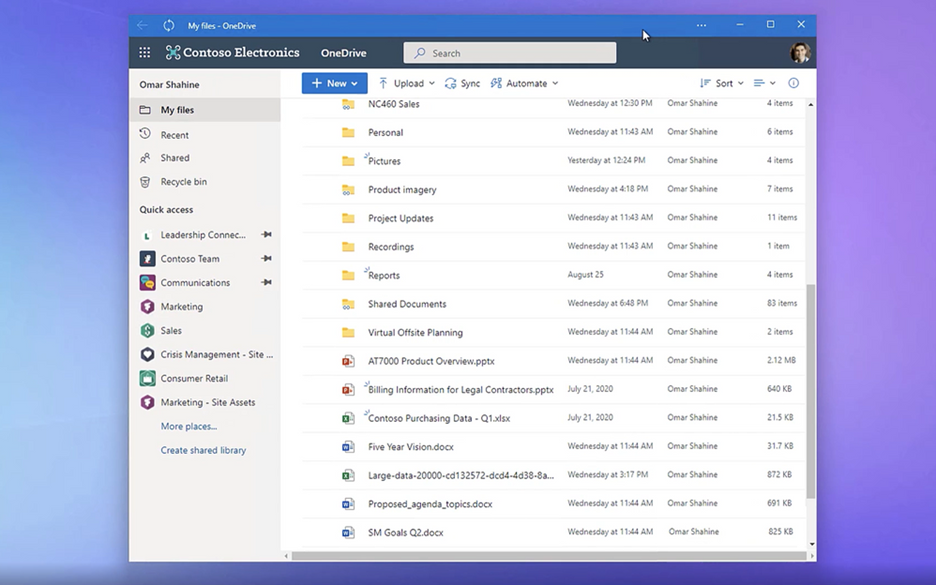
As part of our ongoing effort to improve performance and design new experiences, we began transforming our web applications into Progressive Web Apps (PWAs) starting with Microsoft Lists and OneDrive.
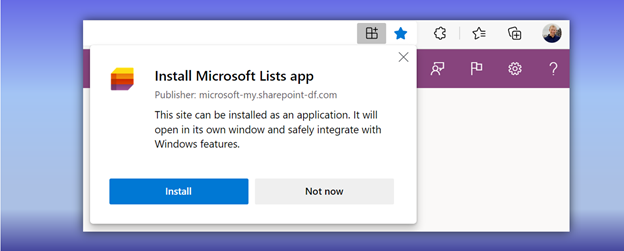 Install Microsoft Lists as a Progressive Web Apps (PWA) from your browser.
Install Microsoft Lists as a Progressive Web Apps (PWA) from your browser.
PWAs allow us to provide access to open web technologies for cross-platform interoperability. And in turn, you get an app-like experience customized for your devices. They are websites progressively enhanced to function like installed apps. PWAs allow us to combine the best of the web and native apps, like websites with app features: The ability to load offline, run within the local operating system, support push notifications and periodic background updates, access hardware features, and more.
When installed, PWAs are just like other apps on Windows. They can be added to the Start Menu, pinned to the Taskbar, work with files, run on user login, and more.
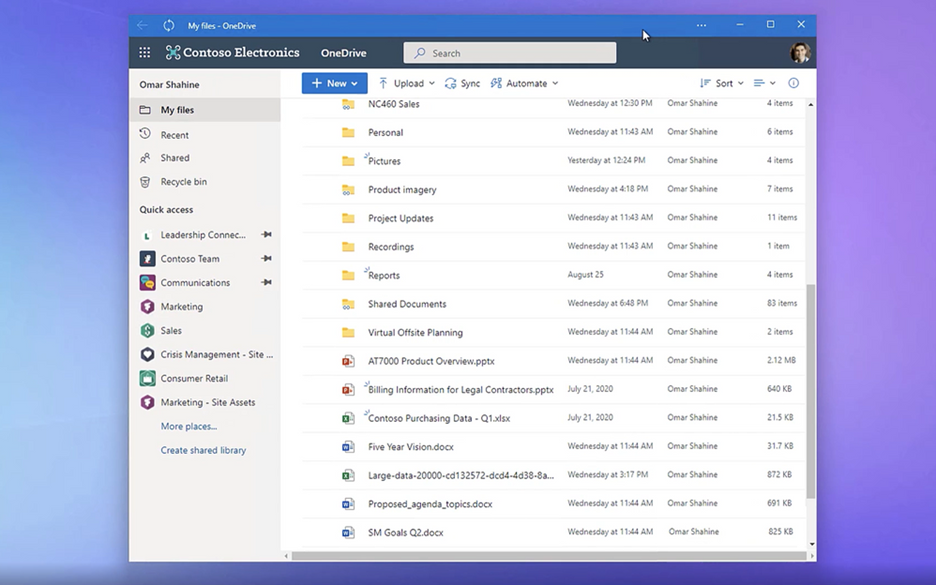 OneDrive as a PWA running on the Windows desktop.
OneDrive as a PWA running on the Windows desktop.
To build web experiences that load and function offline – including support for editing – we had to look beyond PWAs. Enter Project Nucleus.
It all started as ‘Project Nucleus’
Project Nucleus was the codename behind our initiative of building a new client-side component to supercharge existing web apps, like Microsoft Lists, by providing a consistently fast and smooth experience on all kinds of devices and networks – again, even working when offline.
By leveraging local storage for fast data retrieval, it also enables our customers to seamlessly work with large and complex datasets made available through our web apps, like Lists with hundreds or thousands of rows. Operations on web app data, like sort and filter, are blazing fast because they occur on the local device. All offline changes synchronize back to the cloud once reconnected to the Internet.
Behind Project Nucleus is Microsoft.SharePoint.exe, a new component delivered alongside OneDrive sync – leveraging the existing OneDrive install and update mechanism. Once installed, it links with the web app by making a smart cache of web app data on the local device. It then acts as a local web server by pulling and pushing data to and from that local cache, instead of the web app always retrieving it from the cloud. This enables offline editing; changes to content occur within the local cache first and then get pushed to the cloud once connection is restored. The result helps save on network bandwidth and eliminate bottlenecks, too.
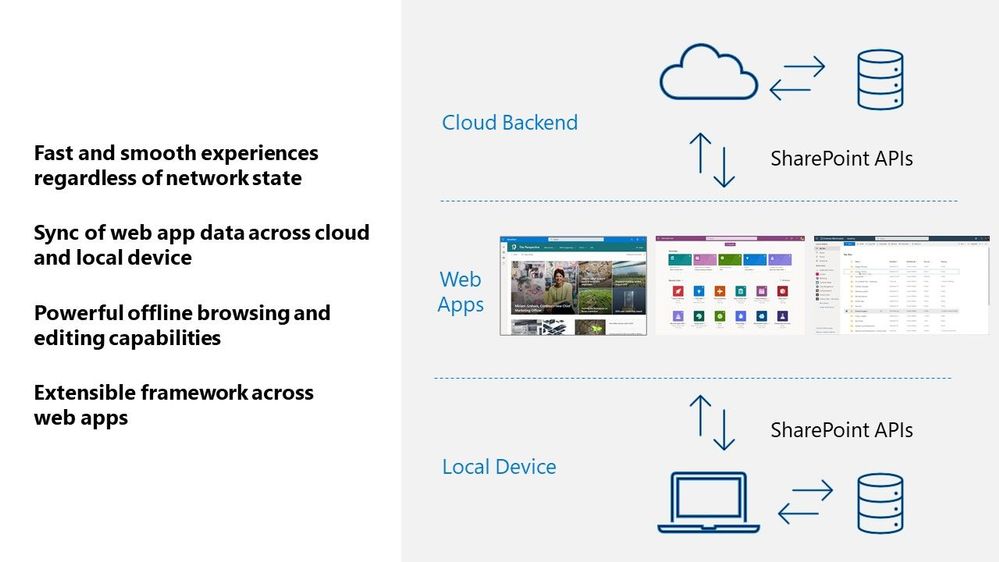 A visual diagram showing how web apps interact across your local Windows device and cloud services in Microsoft 365.
A visual diagram showing how web apps interact across your local Windows device and cloud services in Microsoft 365.
Microsoft Lists is our first web application that leverages these new capabilities. First, it means you can load the Lists app to view and edit list data whether your online or offline. Second, loading and interacting with lists gets supercharged in all modalities. Finally, views inside synced lists never get throttled – regardless of the number of items in the view or whether those columns are indexed.
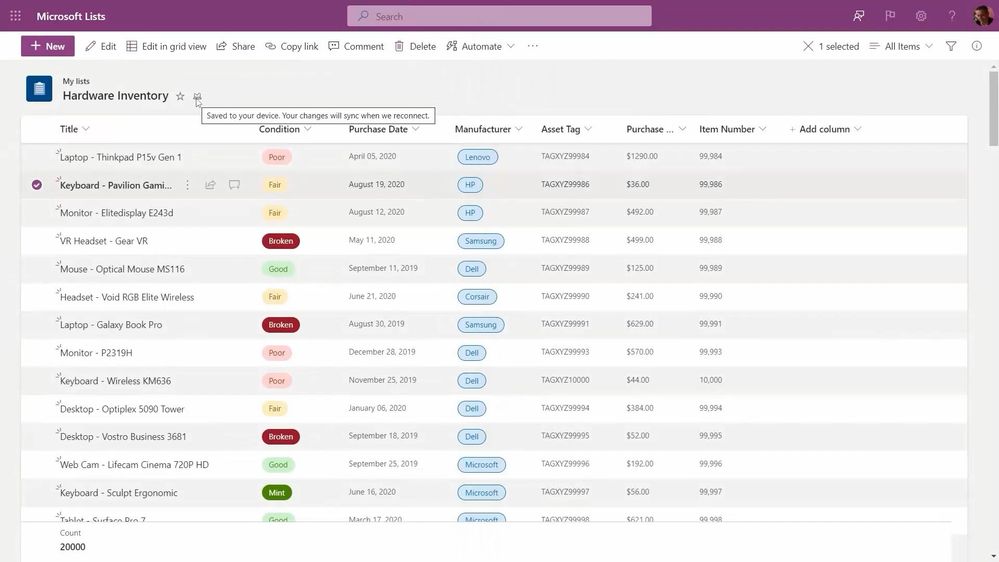
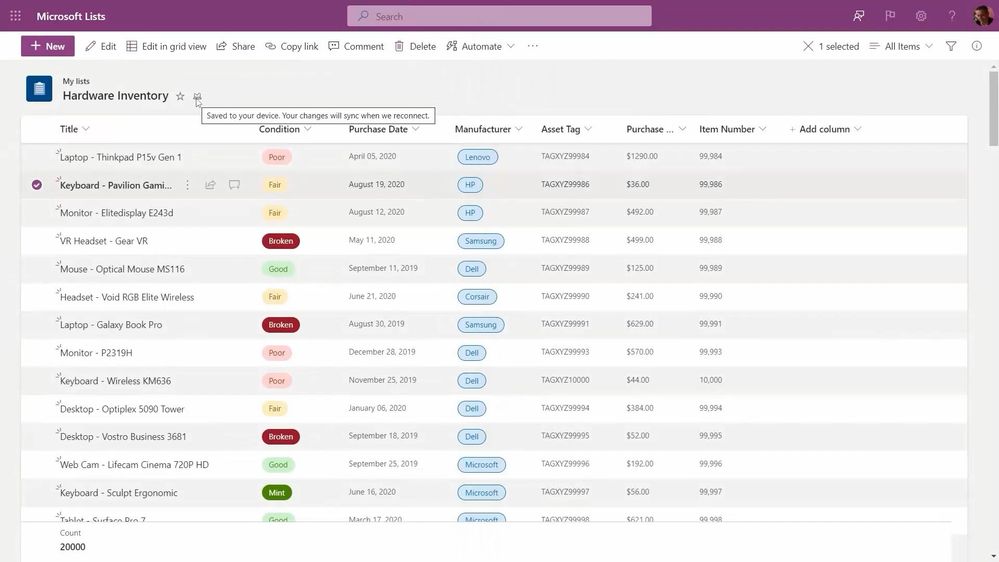 New Lists indicators show when your items are being save to your device (offline; as shown above), when the list is synchronizing, and when all is up to date (synced).
New Lists indicators show when your items are being save to your device (offline; as shown above), when the list is synchronizing, and when all is up to date (synced).
Moving forward…
In short, your lists are always on, lightning fast, and less impacted by service-imposed limitations. This is where we start, and we plan to bring these benefits to other web apps over time. Stay tuned – online or offline – for future updates in this space.
Learn more about Progressive Web Apps, including ‘how to’ information for end users. Review all Microsoft Lists new from Microsoft Ignite – including the general availability announcement for Microsoft Lists: Fast and offline [Roadmap ID: 68809]. We have a new end-user ‘how to’ edit lists offline. And admins can review policies to control Lists sync settings.
Take a peek at the technology in action from the related Microsoft Ignite session, “What’s new with Microsoft Lists” (published on November 2nd, 2021 – jump to 13:30 to see the “Fast and offline access to list data” segment):
Thanks for your time to learn more, Andrey Esipov – Principal program manager, Microsoft
by Contributed | Nov 28, 2021 | Technology
This article is contributed. See the original author and article here.
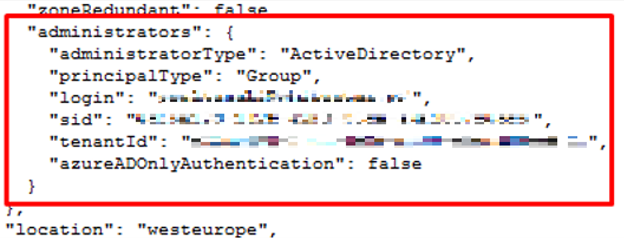
I worked on a service request where customer is getting the below error when trying to automate scale up/down for SQL Managed Instance using Azure Automation/Runbook.
Applies to:
- Performing management operations on SQL Managed instances using Azure Runbook (PowerShell).
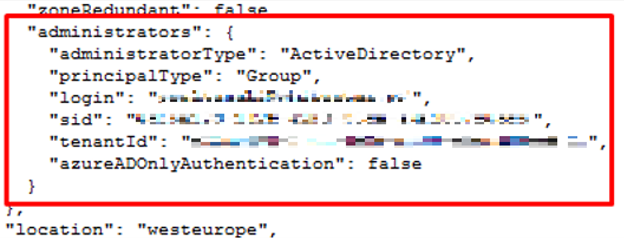
- SQL Managed Instance has an AAD admin set.
- Automation account identity is set to user assigned.
Error:
set-AzSqlInstance : Cannot find the Azure Active Directory object ‘<removed>. Please make sure that the user or group or application you are authorizing is registered in the current subscription’s Azure Active directory.
Runbook content:
$connectionName = “AzureRunAsConnection”
$servicePrincipalConnection=Get-AutomationConnection -Name $connectionName
Add-AzAccount -ServicePrincipal -Tenant $servicePrincipalConnection.TenantId -ApplicationId $servicePrincipalConnection.ApplicationId -CertificateThumbprint $servicePrincipalConnection.CertificateThumbprint
#Scale-up SQLMI
set-AzSqlInstance -Name “SQLMI1” -ResourceGroupName “RGName” -VCore 16 -Force
Debug:
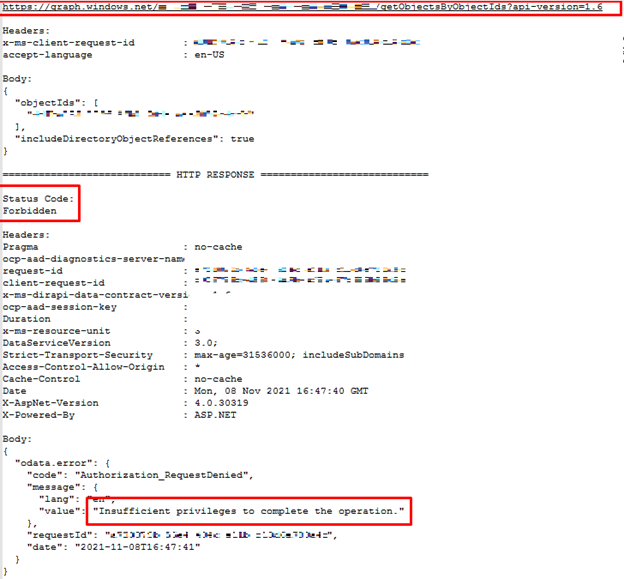
We identified the issue by enabling debug mode on the PowerShell command:
Add -Debug -Confirm:$false to the PS command to capture API call to see what is the exact action is failing.
#Scale-up SQLMI debug enabled
set-AzSqlInstance -Name “SQLMI1” -ResourceGroupName “RGName” -VCore 16 -Force -Debug -Confirm:$false
From the debug results, we can see that client first gets the managed instance with its admins:
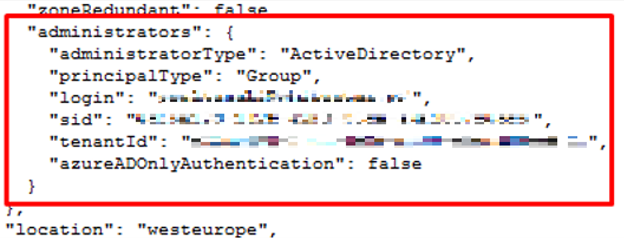
Since the admin is set, following requests have been sent to get its details:
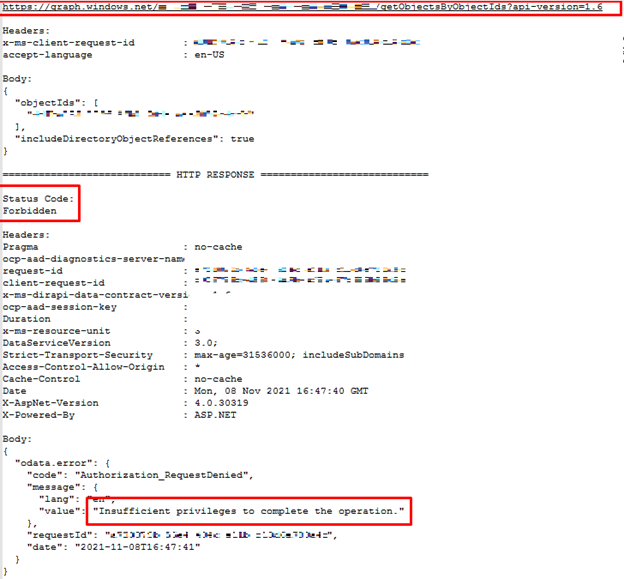
The requests failed with the HTTP status code 403 (Forbidden).
Cause:
The Automation Account’s service principal doesn’t have an AAD reader permission to get the SQLMI AAD admin information.
Resolution:
To fix the issue, you can assign a User Administrator, or Directory Reader build in role to the service principle on the subscription level following these steps: https://docs.microsoft.com/en-us/azure/role-based-access-control/role-assignments-portal?tabs=current
User Administrator: https://docs.microsoft.com/en-us/azure/active-directory/roles/permissions-reference#user-administrator
Or, Directory Reader: https://docs.microsoft.com/en-us/azure/active-directory/roles/permissions-reference#directory-readers
Thank you,
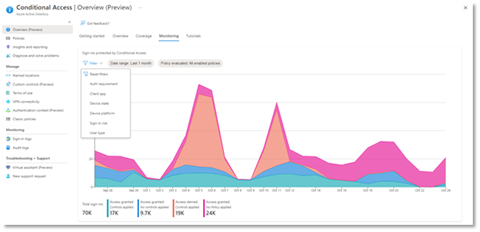
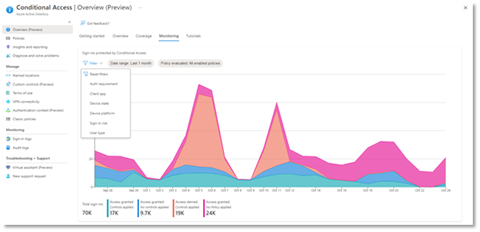
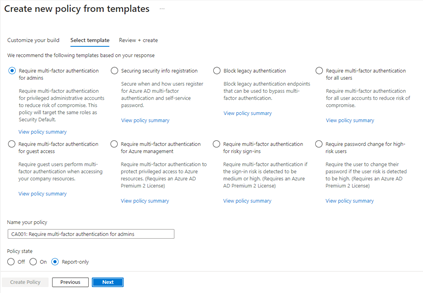 Figure 1: Admin experience for Conditional Access templates
Figure 1: Admin experience for Conditional Access templates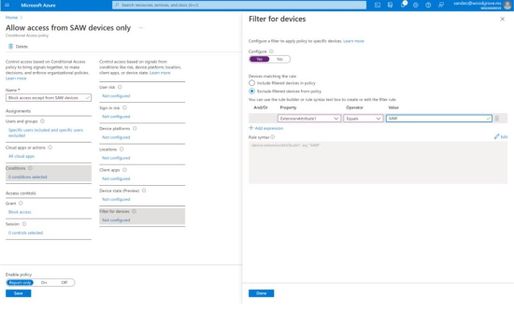 Figure 2: Admin experience for filters for devices
Figure 2: Admin experience for filters for devices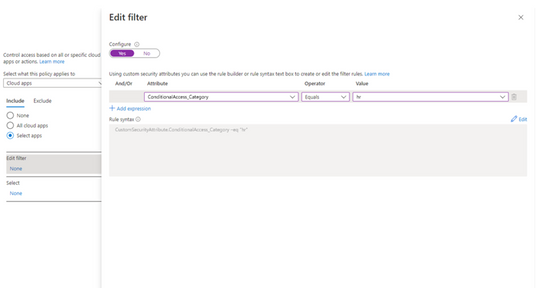
 Figure 3: Admin experience for identity protection diagnostic settings
Figure 3: Admin experience for identity protection diagnostic settings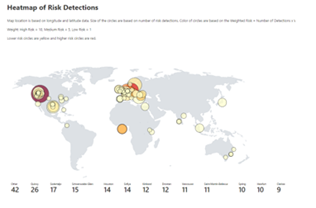 Figure 4. Admin experience for identity protection risk analysis workbook
Figure 4. Admin experience for identity protection risk analysis workbook


Recent Comments