This article is contributed. See the original author and article here.
It’s a challenging time in software security; migration to the modern cloud, the largest number of remote workers ever, and a global pandemic impacting staffing and supply chains all contribute to changes in organizations. Unfortunately, these changes also give bad actors opportunities to exploit organizations:
“Cybercriminals are targeting and attacking all sectors of critical infrastructure, including healthcare and public health, information technology (IT), financial services, and energy sectors. Ransomware attacks are increasingly successful, crippling governments and businesses, and the profits from these attacks are soaring.” – Microsoft Digital Defense Report, Oct 2021 |
For years Microsoft Office has shipped powerful automation capabilities called active content, the most common kind are macros. While we provided a notification bar to warn users about these macros, users could still decide to enable the macros by clicking a button. Bad actors send macros in Office files to end users who unknowingly enable them, malicious payloads are delivered, and the impact can be severe including malware, compromised identity, data loss, and remote access. See more in this blog post.
“A wide range of threat actors continue to target our customers by sending documents and luring them into enabling malicious macro code. Usually, the malicious code is part of a document that originates from the internet (email attachment, link, internet download, etc.). Once enabled, the malicious code gains access to the identity, documents, and network of the person who enabled it.” – Tom Gallagher, Partner Group Engineering Manager, Office Security |
For the protection of our customers, we need to make it more difficult to enable macros in files obtained from the internet.
Changing Default Behavior
We’re introducing a default change for five Office apps that run macros:
VBA macros obtained from the internet will now be blocked by default.
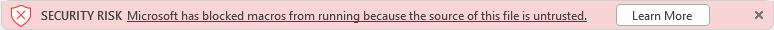
For macros in files obtained from the internet, users will no longer be able to enable content with a click of a button. A message bar will appear for users notifying them with a button to learn more. The default is more secure and is expected to keep more users safe including home users and information workers in managed organizations.
“We will continue to adjust our user experience for macros, as we’ve done here, to make it more difficult to trick users into running malicious code via social engineering while maintaining a path for legitimate macros to be enabled where appropriate via Trusted Publishers and/or Trusted Locations.” – Tristan Davis, Partner Group Program Manager, Office Platform |
This change only affects Office on devices running Windows and only affects the following applications: Access, Excel, PowerPoint, Visio, and Word. The change will begin rolling out in Version 2203, starting with Current Channel (Preview) in early April 2022. Later, the change will be available in the other update channels, such as Current Channel, Monthly Enterprise Channel, and Semi-Annual Enterprise Channel.
At a future date to be determined, we also plan to make this change to Office LTSC, Office 2021, Office 2019, Office 2016, and Office 2013.
End User Experience
Once a user opens an attachment or downloads from the internet an untrusted Office file containing macros, a message bar displays a Security Risk that the file contains Visual Basic for Applications (VBA) macros obtained from the internet with a Learn More button.
The Learn More button goes to an article for end users and information workers that contains information about the security risk of bad actors using macros, safe practices to prevent phishing & malware, and instructions on how to enable these macros by saving the file and removing the Mark of the Web (MOTW).
What is Mark of the Web (MOTW)?
The MOTW is an attribute added to files by Windows when it is sourced from an untrusted location (Internet or Restricted Zone). The files must be saved to a NTFS file system, the MOTW is not added to files on FAT32 formatted devices.
IT Administrator Options
This chart shows the evaluation flow for Office files with VBA macros and MOTW:
Evaluation flow for Office files with VBA macros and MOTW
Organizations can use the “Block macros from running in Office files from the Internet” policy to prevent users from inadvertently opening files from the internet that contain macros. Microsoft recommends enabling this policy, and if you do enable it, your organization won’t be affected by this default change.
“Setting policy is a powerful tool for IT Admins to protect their organizations. For years we’ve recommended blocking macros obtained from the internet in our security baselines, and many customers have done so. I’m pleased Microsoft is taking the next step to securing everyone with this policy by default!” – Hani Saliba, Partner Director of Engineering, Office Calc |
Additionally, there are two other options to know your files are safe:
- Opening files from a Trusted Location
- Opening files with digitally signed macros and providing the certificate to the user, who then installs it as a Trusted Publisher on their local machine
To learn more about how to get ready for this change and recommendations for managing VBA macros in Office files, read this article for Office admins.
Thank you,
Office Product Group
VBA Team & Office Security Team
More helpful information on the threats of Ransomware:
- The growing threat of ransomware, Microsoft “On the Issues” blog post on July 20, 2021
- Rapidly protect against ransomware and extortion
- 2021 Microsoft Digital Defense Report (see pages 10-19)
- Learn about threat analytics in Microsoft 365 Defender
- Microsoft’s DART ransomware approach and best practices
- Microsoft DART ransomware case study
Continue the conversation by joining us in the Microsoft 365 Tech Community! Whether you have product questions or just want to stay informed with the latest updates on new releases, tools, and blogs, Microsoft 365 Tech Community is your go-to resource to stay connected!
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.


Recent Comments