This article is contributed. See the original author and article here.
The volume of security events continues to grow, and the scope and sophistication of attacks are increasing. We can define the known attack scenarios, but how about the emerging and unknown threats in your environment?
We are excited to announce that we are releasing an extended Fusion ML detection capability that can help you find the emerging and unknown threats in your environment by applying extended ML analysis and by correlating a broader scope of anomalous signals, while keeping the alert fatigue low.
This release includes:
- A new set of machine learning algorithms that detect emerging threat patterns automatically to stop attacks at an early stage.
- Extended source signal coverage for all the assets monitored by the SOC team in a Microsoft Sentinel workspace by supporting custom scheduled rules, out-of-the box anomalies, and additional Microsoft products.
- A new configuration UI that allows security analysts to configure source signals and to exclude specific detection patterns that may not be applicable to your environment from Fusion detection to further reduce alert fatigue.
The new set of machine learning algorithms
Available at no additional cost to Microsoft Sentinel customers, Fusion runs at cloud scale and processes billions of signals daily. Fusion uses multiple machine learning algorithms and a probabilistic kill-chain to correlate signals across multiple-clouds, on-premises, and at Edge, to identify sophisticated and novel multistage attacks.
With this extended capability, our ML detections can go beyond the known attack scenarios. The new set of Fusion ML algorithms constantly learn from existing attacks, apply analysis based on how the real security analysts think, and find the threats we have not seen previously from millions of anomalous behaviors and suspicious activities across the kill-chain in your environment to help you stay one step ahead of the attackers.
As you investigate and close Fusion incidents, we encourage you to provide feedback on whether this incident was a True Positive, or a False Positive. Your incident conclusions in Microsoft Sentinel are used as labels in Fusion ML algorithms. The more accurate the conclusion, the better efficacy you get from Fusion in your environment.
Extended detection coverage for your assets
Alerts from the custom scheduled analytics rules
In Microsoft Sentinel, security analysts build KQL-based scheduled rules to monitor the assets in their environment. Oftentimes while investigating an incident triggered by scheduled rule, a security analyst starts with a single alert, runs multiple queries to gather related alerts and anomalies, and then manually associate those alerts and activities with the kill-chain to form a complete picture and the attack path.
Fusion ML algorithms take care of the manual analysis and correlations, making it easy to find a needle in a haystack. Now that Fusion has extended the coverage to all the built-in and custom scheduled rules, the detections can reach every asset monitored by the SOC team in an enterprise, including signals from end points, network, and multi-clouds. With organization and domain knowledge encoded in the custom rules, Fusion can identify the sophisticated emerging threats that are specific to the customer environment.
Identify emerging threats with out-of-the-box anomalies
Rule-based detections are efficient for detecting known attacks, but they do not always adapt to new attack techniques and patterns. With the ML-based out-of-the-box anomalies and the new set of ML algorithms in this release, Fusion can identify novel attacks by associating unusual behaviors in the environment with the learning from known attack patterns, IoCs, past incidents, customer feedback and the Microsoft internal security labels.
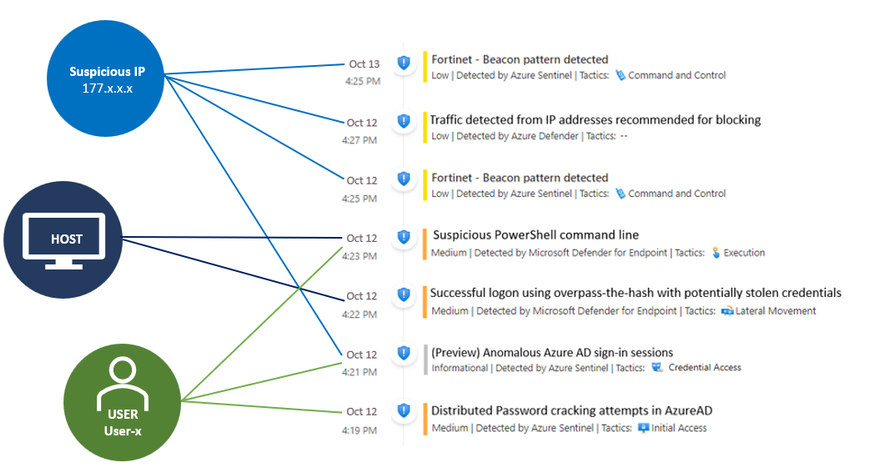
An example
The example below shows a possible attack started with initial access from the Cloud to end point execution, and then moved on to consistent beaconing from an internal IP address to a suspicious external one in roughly 24 hours. The Fusion ML algorithms detected this attack by correlating anomaly (Anomalous Azure AD sign-in sessions), as well as alerts from custom scheduled rules, Azure Defender, and Microsoft Defender for Endpoint.
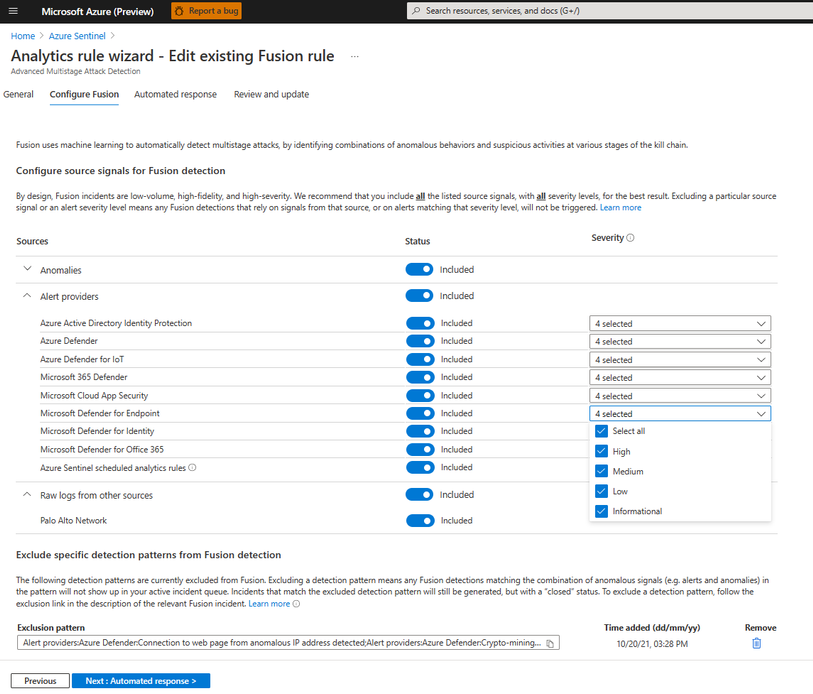
Customizable data sources and results
The new Fusion configuration UI allows security analysts to fine tune the input and output of Fusion. You can specify the input source signals to define the scope monitored by Fusion and exclude specific detection patterns that may not be applicable to your environment from Fusion detection.
We encourage you to try out the new capabilities and let us know what you think – provide your feedback when you close an incident and share additional insights on your product experience through “Guides & Feedback” in Sentinel. Your feedback is critical to help us shape the product!
For more information:
- Microsoft Sentinel Fusion
- Configure Fusion rule
- Sentinel uncovers the real threats hidden in billions of low fidelity signals
- Sentinel GitHub repo
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.


Recent Comments