Applications
|
 |
A10 Training – Virtual Lab (Japan): This virtual lab for A10 Networks’ Cloud Access Proxy and SSL Insight solutions allows users to customize the lab environment for troubleshooting, operational checks, and proofs of concept. This offer is available only in Japanese.
|
 |
Augury Machine Health: Augury’s Halo Machine Health combines advanced sensors with powerful AI-based diagnostics and collaboration tools to help teams understand when machines are at risk and how to intervene.
|
 |
Azure DevOps to Zendesk connector: This connector from IntegrateCloud integrates Microsoft Azure DevOps with Zendesk, allowing support agents to create Azure DevOps work items from Zendesk ticket forms.
|
 |
BHC3 AI Suite: BakerHughesC3.ai brings together the energy technology expertise of Baker Hughes with C3.ai’s AI software for digital transformation in the oil and gas industry. The core of BHC3 AI Suite is an extensible, model-driven abstraction layer that dramatically enhances data scientist and application developer productivity.
|
 |
Carebook Digital Pharmacy Platform: Carebook is an all-in-one, customer-facing digital pharmacy solution. Engage your customers, easily connect with patients, provide online prescription refills, and seamlessly integrate with third-party e-commerce and loyalty systems.
|
 |
Certis Smart Integrated Transport Hub: Smart Transport Hub from Certis delivers a platform capable of transforming traditional transportation frameworks into intelligent, proactive networks. Support effective project development and asset management while securing the long-term viability of your transportation system.
|
 |
Circit – Audit Confirmations: Circit, an open banking and audit platform, connects audit firms to banks and other evidence providers to facilitate more efficient and higher-quality audits. Circit automates the audit confirmation process using platform tools and open banking connectivity.
|
 |
Cloud-Native CMS/DXP for Drupal: This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides Drupal 9.1.2, Apache 2.4.46, MySQL 5.7.34, PHP 7.3.28, phpMyAdmin 5.1.0, and Docker 20.10.6 on CentOS 7.9.
|
 |
Cloud-Native Database for PostgreSQL: This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides PostgreSQL 9.4, 9.6, 10, or 11, along with pgAdmin 5.2 and Docker 20.10.6 on CentOS or Ubuntu.
|
 |
Cloud-Native Database for RethinkDB: This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides RethinkDB 2.4.1 and NGINX 1.20.0 on Ubuntu 20.04. RethinkDB is a NoSQL database that stores schema-less JSON documents.
|
 |
Cloud-Native In-memory Database for Redis: This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides Redis 3.0, 3.2, 4.0, 5.0, or 6.0, along with NGINX 1.20.0 and RedisInsight on CentOS or Ubuntu.
|
 |
Cloud-Native MQ for Apache ActiveMQ: This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides Apache ActiveMQ 5.16.1 and OpenJDK 1.8.0 on CentOS or Ubuntu. Apache ActiveMQ is a popular and powerful open-source messaging and integration patterns server.
|
 |
Collabspace ARCHIVE: Content Protection and Search: Collabspace ARCHIVE features versioning, email thread archiving, and file preview, along with data encryption and Write-Once-Read-Many (WORM) storage to prevent tampering or deletion.
|
 |
Compose Low-Code Platform on Azure: Governments and businesses alike can use Compose to achieve their digitization and productivity goals. The low-code application development platform is well-suited for data gathering, process automation, and case management.
|
 |
Content Collaboration Platform based on ownCloud: This image offered by VMLab provides version 10.7 of ownCloud on CentOS 7.9. ownCloud is client–server software for creating file-hosting services. Also included are Apache 2.4.46, PHP 7.4.19, MySQL 5.7.34, Redis 5.0.9, ONLYOFFICE Docs Community 6.1.1, phpMyAdmin 5.1.0, and Docker 20.10.6.
|
 |
Creative Work Subscription and Publishing Platform: This image offered by VMLab provides Ghost 4.5.0 on CentOS 7.9. Ghost is a headless Node.js content management system for professional publishing. Also included are NGINX 1.20.0, MySQL 5.7.34, Node.js 14.17, Docker 20.10.6, and phpMyAdmin 5.1.0.
|
 |
Data Exploration and Visualization for Superset: This preconfigured image offered by VMLab provides Apache Superset 1.0, NGINX 1.20.0, PostgreSQL 10.16, Docker 20.10.6, Redis 3.2.12, and PgAdmin 5.2 on Ubuntu 20.04. Apache Superset is an open-source app for data exploration and data visualization.
|
 |
DeepVu Aluminum Price Forecasting: DeepVu offers machine learning models to predict the price of a futures contract of a commodity that is traded on the Chicago Mercantile Exchange or the Shanghai Futures Exchange.
|
 |
DevOps Automation Server for Jenkins: This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides Jenkins 2.277.4, OpenJDK 1.8.0, and NGINX 1.20.0 on CentOS or Ubuntu. Jenkins is an automation server with a plug-in ecosystem for supporting delivery pipelines.
|
 |
EDB Enterprise Plan – PostgreSQL: The EDB Enterprise Plan features tools, support, and a PostgreSQL database extended by EDB’s enterprise-class software. This provides compatibility with Oracle Database, so you can migrate quickly to EDB on Microsoft Azure.
|
 |
EY OpsChain Traceability: EY OpsChain Traceability brings trust via transparency into any supply chain. The solution is part of the EY OpsChain product suite, built on the EY Blockchain SaaS platform, which is hosted on Microsoft Azure.
|
 |
Fortpress Starter: Fortpress is an all-in-one application management system for developing blogs, web apps, websites, APIs, and more. Fortpress provides an integrated code editor for HTML, JavaScript, and CSS.
|
 |
Hardened Windows Server 2019: This image of Windows Server 2019 is preconfigured by The Center for Internet Security (CIS) to the recommendations in the associated CIS Benchmark and the U.S. Department of Defense’s Security Technical Implementation Guide (STIG).
|
 |
HealthEC Population Health Management Platform: HealthEC’s population health management solution aggregates claims and clinical data to deliver key insights into cost drivers and evaluate quality measures that impact performance-based reimbursements while enabling the care team to be a change agent.
|
 |
Hólos – Fluxos: Hólos from MPS Informática provides the resources necessary for the development and implementation of business process management and electronic document management. This app is available only in Portuguese.
|
 |
Horizon Protection Engine: Horizon Protection Engine integrates with cloud, hybrid-cloud, and on-premises architectures and allows users to utilize Microsoft Azure Information Protection to secure their business applications. This app is available only in Italian.
|
 |
Incorta Intelligent Ingest for Microsoft Azure Synapse: With Incorta Intelligent Ingest, you can seamlessly integrate your Oracle application/ERP data into Microsoft Azure for rapid analytics in Azure Synapse. Incorta fast-tracks the process for preparing data by automating the data modeling and staging steps.
|
 |
IN-D Aadhaar Number Masking: Aadhaar is a random 12-digit number issued to residents of India. Banks, hotels, and many other companies store Aadhaar images of their customers. IN-D Aadhaar Number Masking can verify and mask these images at the click of a button, helping companies maintain regulatory compliance.
|
 |
Joshua Tree: Joshua Tree is an eco-design tool for clothing makers that collects and consolidates internal data as well as audit data carried out with suppliers, with a focus on environmental and social performance. This app is currently available only in French.
|
 |
LEA365: LEA is a chatbot included in Aurera’s MyCoach 365 change management solution. LEA integrates with Microsoft Teams to assist users and optimize their experience. This app is available in French.
|
 |
MAESTRO: Maestro is an IoT platform developed on Microsoft Azure components that provides end-to-end integration across operational, strategic, and tactical data flows. Sensors and machines can be managed and monitored remotely, alarms and notifications can be generated, and there is a dashboard for users.
|
 |
Magento Server: This server image offered by Cloud Infrastructure Services provides Magento Open Source, Apache Web Server, MySQL Server, ElasticSearch, and all the required PHP modules on Ubuntu Server 20.04. Magento Open Source is a free e-commerce platform.
|
 |
Mingdao APaaS and Zero-Code Platform: This preconfigured image offered by VMLab provides Mingdao On-Premise 2.4.1 and Docker 20.10.6 on CentOS 7.9. Mingdao is a rapid design and development tool for enterprise software. This app is available in English, Simplified Chinese, and Traditional Chinese.
|
 |
Motif Discovery Application: Improve productivity and learn more about your machine data with Motif Discovery Application, a tool that automatically processes time series data and creates training data for machine learning models. Discovered patterns are clustered based on similarity.
|
 |
Node.js Runtime for Web App: This image offered by VMLab provides Node.js 10, 12, or 13 on CentOS 7.9. Node.js is a JavaScript runtime. Also included are NGINX 1.20.0, MySQL 5.7, Redis 5.0.9, Docker 20.10.6, phpMyAdmin 5.1.0, adminMongo 0.0.23, PM2 4.5.6, Express 4.16.1, and your choice of several versions of MongoDB.
|
 |
Numerator Consumer Data Capture Link: Historically, consumer purchase data has been controlled by retailers, leaving brands with limited access. Numerator Link from Market Track democratizes data access (purchase or viewership), and brands can access consumer data from permissioned user accounts.
|
 |
Open-Source Agile and Scrum Project Management: This preconfigured image offered by VMLab provides Zentao 12.4.3 on CentOS 7.9. Zentao is open-source project management software. Also included are Apache 2.4.46, PHP 7.2.34, MySQL 5.6.51, Redis 5.0.9, phpMyAdmin 5.1.0, and Docker 20.10.6.
|
 |
Open-Source Cloud-Native ERP and CRM: This preconfigured image offered by VMLab provides Odoo Community Edition 12, 13, or 14 on Ubuntu 20.04. Odoo is a suite of open-source business apps. Also included in the image are NGINX 1.20.0, PostgreSQL 11.11, PgAdmin 5.2, and Docker 20.10.6.
|
 |
Open-Source Collaboration Platform for Developers: This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides Mattermost Team Edition 5.34.0, an open-source messaging platform, on Ubuntu 18.04. Also included are NGINX 1.20.0, MySQL 5.7.34, Docker 20.10.6, and phpMyAdmin 5.1.0.
|
 |
Open-Source IT Monitor Platform: This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides Zabbix 5.2 on Ubuntu 20.04. Zabbix is an open-source distributed monitoring solution. Also included in the image are NGINX 1.20.0, MySQL 8.0.25, phpMyAdmin 5.1.0, and Docker 20.10.6.
|
 |
petranna.db.MySQL managed service: The petranna.db.MySQL service allows an unlimited number of tenants on the same RDBMS instance, leading to a significant reduction in costs and faster time-to-market for SaaS applications.
|
 |
PHP Runtime for Web App (LAMP): This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides PHP 5.6, 7.0, 7.2, or 7.4, along with Apache 2.4.46, Redis 5.0.9, phpMyAdmin 5.1.0, and Docker 20.10.6 on CentOS 7.9. Also included is MySQL 5.7 or 8.0.
|
 |
PHP Runtime for Web App (LEMP): This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides PHP 5.6, 7.0, 7.2, or 7.4, along with NGINX 1.20, Redis 5.0.9, phpMyAdmin 5.1.0, and Docker 20.10.6 on CentOS 7.9. Also included is MySQL 5.7 or 8.0. |
 |
Pobuca Customer Voice: Pobuca Customer Voice helps you know your customers by collecting and processing their feedback. Analyze all customer communications in natural language from voice recordings, emails, chats, and social media, and extract customer experience alerts and insights.
|
 |
Pobuca Knowledge: Pobuca Knowledge leverages AI to analyze conversations from all customer touchpoints and extract Q&As, which you can use for your knowledge base and to engage your customer service agents.
|
 |
Redmine Open-Source Project Management: This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides Redmine 4.2.1, NGINX 1.20.0, MySQL 5.7.34, phpMyAdmin 5.1.0, and Docker 20.10.6 on Ubuntu 20.04. Redmine is a project management web app that uses the Ruby on Rails framework.
|
 |
Sail Indoor Positioning: Sail is an indoor positioning platform that enables mobile app developers to create indoor navigation, location analytics, and personalization services. Sail uses machine learning to continually reconfigure the system, removing the need for any fingerprinting or calibration.
|
 |
SailPoint Access Risk Management Solution: SailPoint Access Risk Management automates real-time access risk analysis, simplifies GRC (governance, risk, and compliance) processes, and identifies a potential user’s risks before access is granted.
|
 |
SDx Transact – Smart Cloud: HxGN SDx provides a central digital platform to optimize the design, engineering, construction, operation, and maintenance of industrial assets. Ensure safe and efficient operations in your facility.
|
 |
Seatti Desk Booking & Team Collaboration: Whether you’re working on-site, at home, on a business trip, or in a café, Seatti lets you plan your workspace locations and collaborate with your team. Stay connected in a hybrid, distributed workplace.
|
 |
Secure Store: The prescriptive analytics of Secure Store Version 5.4, built with artificial intelligence, allows retailers to make informed decisions to improve profitability, reduce shrink, and achieve rapid return on investment.
|
 |
Senserva for Azure: Senserva, a cloud security posture management solution, produces priority-based risk assessments for all the Microsoft Azure objects that Senserva manages, enabling customers to perform optimal discovery and remediation.
|
 |
Soft-ex Unified Analytics for Microsoft Teams: The latest release of Soft-ex’s unified communication analytics solution offers a new user interface with a widget-driven dashboard. The configurable solution integrates with Microsoft Teams to deliver granular visibility.
|
 |
TACHYUS. Production Optimization for Oil & Gas: The Tachyus platform and its Data Physics technology empower oil producers to make data-driven decisions that maximize asset value. Data Physics combines reservoir physics and machine learning to rapidly integrate data sources and identify optimal injection and drilling plans.
|
 |
TeamViewer IoT Edge: TeamViewer IoT lets you remotely control edge devices. To process events, such as machine failure or anomalies, TeamViewer IoT includes data processing on the edge as well as cloud-based predictive maintenance solutions.
|
 |
TelluCare Digital Supervision: Digital Supervision from Tellu allows healthcare personnel to use cameras to watch over patients in nursing homes or home-care environments. Camera images can also be anonymized for privacy reasons.
|
 |
Verita Research Partner (VRP) Isolation Service: The VRP Isolation Service uses novel AC electrokinetics-based microarrays to capture DNA fragments greater than 300 bp, which are primarily derived from cell necrosis or extracellular vesicles carrying proteins and RNA. After isolation, these biomarkers can be investigated using standard lab techniques.
|
 |
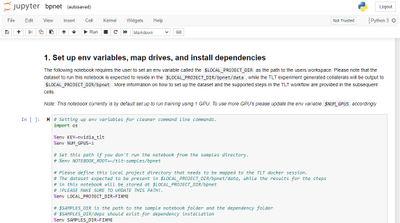
Visual Machine Learning Stack for TensorFlow: This preconfigured image offered by VMLab, an authorized reseller for Websoft9, provides TensorFlow 2.5.0, TensorBoard, NGINX 1.20.0, and Python 3.8.5 on Ubuntu 20.04. TensorFlow is an end-to-end open-source platform for machine learning.
|
 |
VMware Tanzu Standard: VMware Tanzu Standard Edition simplifies the operation of Kubernetes for multi-cloud and hybrid-cloud deployments, centralizing management and governance for many clusters and teams across Microsoft Azure and edge or on-premises environments.
|
 |
Windows Server 2019 with SQL Express: This image offered by Belinda CZ s.r.o. provides Windows Server 2019 with SQL Express. Also included is SQL Server Management Studio, an integrated environment to manage SQL bases.
|
 |
WordPress: This image offered by Niles Partners provides WordPress 5.7.1, a popular publishing platform for blogs and websites. WordPress offers customization through themes, extensions, and plug-ins.
|
Consulting services
|
 |
4-Week Data Science Proof of Concept: Hitachi Solutions experts will work with your team to identify data and deliver a robust modeling environment designed to accelerate your cloud journey using Hitachi Solutions Advanced Analytics DataLab and Microsoft Azure.
|
 |
App Modernization: 10-Day Assessment: Cloud Temple will help your modernization project into the Microsoft Azure cloud by defining stakes, realizing a target architecture, and building scenarios using services such as Azure Migrate. This offer is available only in France.
|
 |
Azure Backup: 1-Hour Briefing: Learn how Chunghwa Telecom can provide your enterprise with remote monitoring and management, restoration exercises, and disaster recovery execution to meet all your Microsoft Azure cloud backup needs. This offer is available only in Chinese.
|
 |
Azure Check-up: The Azure Check-up from Unica ICT Solutions is a quick and easy way to map the status of your Microsoft Azure environment based on criteria such as security, continuity, performance, and cost. This offer is available only in Dutch.
|
 |
Azure Datacenter Foundation – Implementation: This one-week implementation by timengo includes a roadmap report with recommendations and configurations for a Microsoft Azure foundation based on timengo’s reference architecture. This offer is available only in Danish.
|
 |
Azure Quick Start: 4-Day Implementation Service: Bytes Software Services will explain Microsoft Azure capabilities and how they relate to your strategic adoption of the cloud platform, giving you an understanding of the requirements and blockers for implementation.
|
 |
Azure Virtual Desktop: 2-Week Implementation: This implementation by Cloud Services provides your organization with assessment, configuration, cost estimates, testing, and fine-tuning to set up and manage compliant and fully secured virtualized desktop environments.
|
 |
Azure Virtual Desktop: 3-Day Assessment: This assessment by +Aliance provides a cost estimate for transitioning to Azure Virtual Desktop, allowing you to enable remote work, reduce office costs, and combine offices in one infrastructure. This offer is available only in Russian.
|
 |
Azure Virtual Desktop: 5-Day Proof of Concept: This offer from Cisilion provides everything you need (demo, design, deployment, configuration, testing, and handover) to understand and prove the value of Azure Virtual Desktop across key stakeholders within your organization.
|
 |
Azure VMware Solutions: 4-Week Implementation: The Logicalis Azure VMware Solution (AVS) combines best-in-class technologies with a proven methodology so you can innovate, optimize your business, and achieve your transformation vision without a hassle.
|
 |
Celonis Proof of Value (1 Week): This offer from diconium digital solutions proves the value of Celonis big data technology process mining, helping you visualize your business processes like never before and turn them into extraordinary experiences. This offer is available only in German.
|
 |
Cloud Readiness-Check: 4-Hour Assessment: Experts from redIT will examine your infrastructure and apps, then show you how to optimally move local IT to the cloud with a combination of Microsoft Azure, Microsoft 365, and Dynamics 365. This offer is available only in German.
|
 |
Cloud Security: 1-Week Assessment: This Ironstone offer provides a thorough analysis of, and useful insights into, your cloud security setup. Get a clear report assessing cloud security risks, recommendations, and actions so your organization can take a proactive approach.
|
 |
Cogmation: 2-Week Implementation: This offer from L&T Technology Services provides end-to-end test automation for multipurpose applications and embedded devices via Cogmation on Azure Virtual Machines, a highly customizable and easily deployable test automation solution.
|
 |
Confidential Compute 10-Week Assessment: Does your data require conclusive assurances of security and fall under specific regulatory demands? This offer from PwC can help you exercise full control over your data in the cloud and utilize it to further enable your business.
|
 |
Corrosion Detection Using Azure 8-Week Proof of Concept: This consulting offer from Affine shows how Microsoft Azure deep learning can detect and classify corrosion via imagery. The solution uses Azure IoT Hub, Azure Machine Learning, Azure Synapse Analytics, and more.
|
 |
Data Analytics on Azure: 2-Week Implementation: Turn raw data into insights that drive decision-making and revenue with Navisite services and Microsoft Azure. Navisite data experts will help you define, design, and build a transformative analytics-driven organization.
|
 |
DIP Capital Markets: 4-Week Proof of Concept: Neudesic experts will help you deliver next-level insights across private equity assets by using its Document Intelligence Platform, knowledge mining framework, and preconfigured architectures to quickly deploy AI and use cases.
|
 |
DynTek Managed Security Services: Using the power of Azure Sentinel, DynTek will actively monitor your environment to help you sort through the noise of false positives in order to hunt for security threats and turn alerts into actionable intelligence.
|
 |
Easy Cloud and Applications: 3-Weeks Briefing: Over the course of this three-week consulting engagement, the experts at RCR will help you create and build sustainable, scalable, and cost-efficient cloud applications using all the power that Microsoft Azure has to offer.
|
 |
EPAM Azure Security: 6-Weeks Assessment: EPAM’s security assessment uses a combination of industry best practices and frameworks to understand the current security posture, critical gaps, and future state of your enterprise Microsoft Azure cloud environment.
|
 |
ETL Conversion to ADF: 2-Day Assessment: Bitwise will provide a high-level time and cost estimate to migrate your on-premises data integration jobs to Microsoft Azure Data Factory using automated extract-transform-load (ETL) conversion.
|
 |
Evolution ASEINFO: Implementation in 4 Weeks: Simplify your organization’s personnel records management, payroll, recruitment, evaluation, training, and more with this offer from Asesores en Informática, available only in Spanish, to implement Evolution ASEINFO on Microsoft Azure.
|
 |
F&R Starter Kit Proof of Concept: 4-Hour Proof of Concept: This proof of concept from Bardess Group delivers dynamic finance, accounting, and reporting charts to compare results to prior period, budget, and/or forecast without all the traditional manual work required.
|
 |
FAR Accelerator – A 1-Day Project Scope Workshop: Learn how you can benefit from Bardess Group’s finance, accounting, and reporting accelerator on Microsoft Azure to pull data from various sources for presentation in browser-based applications that are accessible anywhere.
|
 |
Image Analytics: 2-Week Proof of Concept: The experts from Cognilytic Technologies will work with you to build cutting-edge facial recognition or object detection scenarios to extract specific information using Microsoft Azure Cognitive Services pretrained models.
|
 |
Innovation Factory: 6-Week Implementation: Create cloud-native applications running on Microsoft Azure with Devoteam Alegri’s Innovation Factory. The dedicated packages of this offer will help you understand, explore, and realize your business case.
|
 |
Managed IT Services: Big Idea Technology provides complete outsourced IT management services (virtual CIO, network monitoring, backup and disaster recovery, and more) to small to midsized businesses, and performs project-based engagements in most IT disciplines.
|
 |
Managed Services for Azure from CentriLogic: CentriLogic’s certified experts will work with you to design, deploy, and continuously support a right-sized environment on Microsoft Azure that is suited to your organization’s workloads and applications.
|
 |
Microsoft 365 Cloud Security: 1-Day Assessment: Direkt Gruppe experts will provide concrete recommendations for your organization to deploy specific security features (Azure Information Protection, Advanced Threat Protection, and more) in your Microsoft 365 environment.
|
 |
Modern Data Platform Pilot: 8-Week Implementation: Digia’s fast-track implementation of a modern data platform on Microsoft Azure and Microsoft Power BI empowers a future of data-driven decision-making through dashboards and key performance indicators (KPIs).
|
 |
NNIT Managed Azure Virtual Desktop Service: NNIT provides a coherent approach to optimize your virtual desktop solution, focusing on operational value and consistent processes. NNIT can also handle round-the-clock day-to-day operations and required governance processes.
|
 |
Promotions Optimization Using Azure: 6-Week Proof of Concept: Affine offers robust marketing campaign design and management to consumer and retail-sector firms with this solution that uses Microsoft Azure services such as Azure Data Factory and Azure Functions.
|
 |
Satisnet Cyber Security Gap Analysis Assessment: Satisnet provides a complete cybersecurity gap analysis to highlight where your organization should focus. Deliverables include a report on how to use the Microsoft security stack, namely Azure Defender and Microsoft 365 Defender.
|
 |
Smart SAP on Azure: 4-Week Implementation: Streamline your transformation to SAP HANA with Microsoft Azure via myCloudDoor, which has implemented hundreds of SAP on Azure solutions and earned the SAP on Azure advanced specialization designation from Microsoft.
|
 |
Threat Management Assessment: IBM’s three-day assessment identifies gaps in your Microsoft Azure hybrid-cloud security program and provides directional recommendations to improve security operations, incident response, compliance, and governance.
|
 |
Web Application Modernization: 1-Day Assessment: In this session, Sela’s experts will use tools and discussions to assess your web application’s readiness for modernization to Microsoft Azure Web Apps, which can greatly improve scalability and availability.
|
 |
Windows Server and SQL Migration: 1-Hour Assessment: Zones offers services to enhance your security posture and extend the life of your Windows Server 2008 and SQL 2008 family of products by assessing, designing, and implementing their migration to Microsoft Azure.
|































































































Recent Comments