CISA Releases Capacity Enhancement Guides to Enhance Mobile Device Cybersecurity for Consumers and Organizations
This article is contributed. See the original author and article here.
This article is contributed. See the original author and article here.
This article is contributed. See the original author and article here.
VMware has released security updates to address multiple vulnerabilities in vCenter Server and Cloud Foundation. A remote attacker can exploit this vulnerability to obtain access to sensitive information.
CISA encourages users and administrators to review VMware Security Advisory VMSA-2021-0027 and apply the necessary updates.

This article was originally posted by the FTC. See the original article here.

Hanukkah is all about spending time with loved ones, celebrating traditions, and, for many, giving gifts. So, as you start preparing for all eight nights, here are some things you can do to avoid scammers when shopping online:
If you spot a scam or experience problems shopping online, the FTC wants to hear about it at ReportFraud.ftc.gov.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.

This article is contributed. See the original author and article here.
Any call center that uses unified routing to manage and assign incoming support requests is going to notice gains in efficiency. The core routing capabilities in Dynamics 365 Customer Service use skill matching and priority to help determine assignments. However, bringing intelligence to the challenge of efficient routing can move you closer to world-class service.
With the unified routing release in April of 2021, we introduced intelligent skill finder as the first capability related to intelligent work classification. It empowers organizations to identify which skills are required by the agent to address an incoming work item. AI models are trained to understand the skills required to address customer inquiries, and then a match is made to agent skills, helping to assign the calls to agents. In this new release, we’re adding two more capabilities to intelligent work classification: customer sentiment identification and effort estimation for routing. These capabilities will enable organizations to harness state-of-the-art AI to improve customer satisfaction and reduce resolution times.
Matching agents to calls based on skills is a basic capability in unified routing. What if you could also gauge customer sentiment based on keywords, and then route calls to agents best able to handle those various emotions?
Let’s better understand this with a scenario. Imagine Contoso Coffee is operating a support center and has implemented unified routing. They recently had a high volume of unhappy customers, and they brainstormed about how best to use their existing staff to address these concerns. Contoso Coffee realizes that customer sentiment could be used as a signal to influence call routing; some agents are better at managing unhappy customers. Contoso decides to adopt sentiment prediction in unified routing. They take a few simple steps:
As a result, Contoso Coffee was able to address the spike in unhappy customers, leveraging their agents to maintain customer satisfaction.
Learn more about using customer sentiment in classification in this short video introduction:
This embed requires accepting cookies from the embed’s site to view the embed. Activate the link to accept cookies and view the embedded content.
Read more in the documentation about using sentiment prediction-based model in work classification.
A key contributor to an effective contact center is understanding how long it will take to address support requests. Organizations do not have a simple way to understand how much time it will take agents to address incoming work items. Effort estimation replaces manual processes with the use of AI. This intelligence interprets the issue and uses historical support data to generate a work estimate.
Highlights of this capability include:
Learn more about effort-based routing in this short video introduction:
This embed requires accepting cookies from the embed’s site to view the embed. Activate the link to accept cookies and view the embedded content.
Read more in the documentation about using the effort estimation model in unified routing.
In any contact center, each agent will have a different set of skills to offer, and organizations should use those skills appropriately to best address customer requests. To maximize agent potential, it is critical for any organization to understand the skills required to address a work item and identify the agent that is best suited to address it. Intelligent skill finder takes the guesswork out of this by using AI to predict the skills required to address an incoming work item, and then matching those required skills to corresponding agents.
Highlights of this capability include:
Visit the Dynamics 365 Customer Service Community Forum to share your thoughts.
This blog post is part of a series of deep dives that will help you deploy and use unified routing at your organization. See other posts in the series to learn more.
The post Use intelligence to transform routing of service delivery requests appeared first on Microsoft Dynamics 365 Blog.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article was originally posted by the FTC. See the original article here.
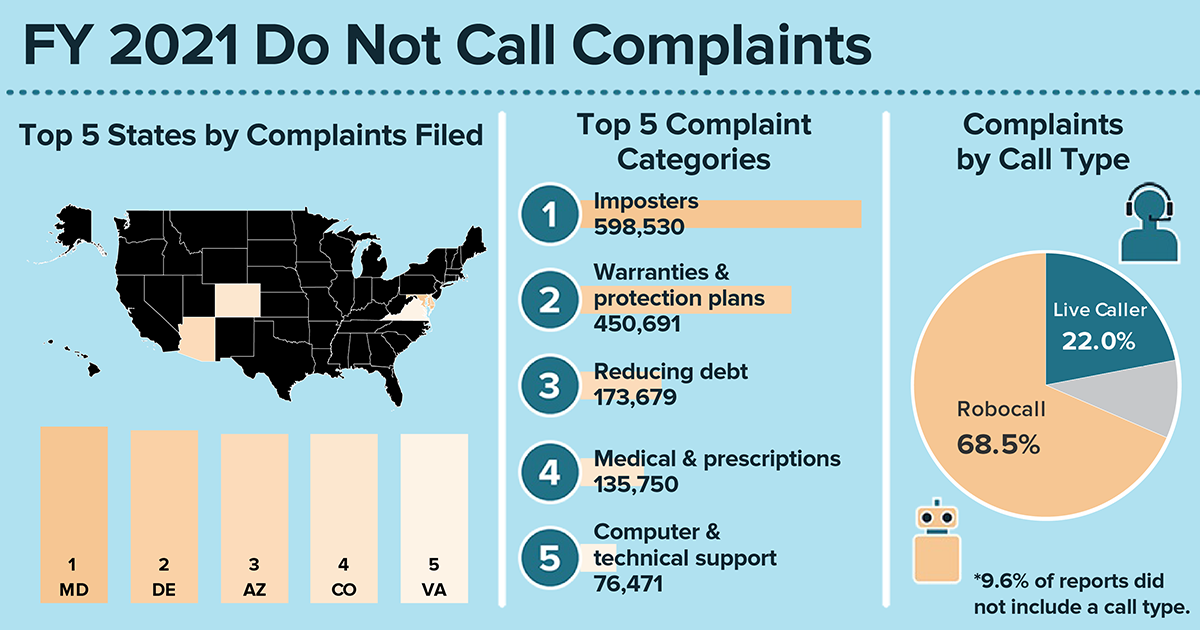 In the past 18 years of the National Do Not Call Registry, those of you signed up for the registry (244 million phone numbers right now) have reported millions upon millions of unwanted sales calls over the years. Here’s a quick look at what you’ve reported this year at DoNotCall.gov about the calls you’re getting:
In the past 18 years of the National Do Not Call Registry, those of you signed up for the registry (244 million phone numbers right now) have reported millions upon millions of unwanted sales calls over the years. Here’s a quick look at what you’ve reported this year at DoNotCall.gov about the calls you’re getting:
Learn more about these reports, including data for your state.
Your reports show what we all know — even if you’re on the registry, you’re still getting unwanted calls. Legitimate, law-abiding companies typically follow the Do Not Call rules. But scammers often ignore them. To get fewer calls, read about some steps you can take to block unwanted calls.
And please, keep reporting calls at DoNotCall.gov. The FTC and other law enforcement agencies analyze reports to identify and take action against the people responsible for illegal calls and scams. The FTC also takes the phone numbers you report and releases them each business day to help telecommunications carriers and other industry partners that are working on call-blocking and call-labeling solutions.
Learn more about blocking unwanted calls at ftc.gov/calls.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article is contributed. See the original author and article here.
Welcome to our new monthly blog series featuring the latest Security, Compliance, and Identity content updates on Microsoft Learn! This is our first post, and we’re highlighting recently released updates, including a new learning path we launched during Cybersecurity Awareness Month. Starting in January, we’ll highlight new learning paths, modules, and other content updates we make each month to give you the skills you need on your learning journey.
Read on to check out some of the latest updates from our Security, Compliance, and Identity portfolio.
Knowing the fundamentals of cybersecurity is a first step toward protecting against cyberthreats. Our new learning path—Describe the basic concepts of cybersecurity—delivers foundational knowledge about cybersecurity concepts including cryptography, authentication, and authorization, along with exploring ways to protect yourself and your business from cyberattacks.
This four-part series of learning paths will equip you with the knowledge you need to take Exam AZ-500.
This learning path will teach you how to secure Azure solutions with Azure Active Directory, implement hybrid identity, deploy Azure AD identity protection, and configure Azure AD privileged identity management.
This learning path will teach you how to lock down the infrastructure and network resources that are running in your Azure environment.
This learning path will teach you how to deploy and secure Azure Key Vault, configure application security features, implement storage security, and configure and manage SQL database security.
This learning path will teach you how to configure and manage Azure monitor, enable, and manage Azure Security Center, and configure and monitor Azure Sentinel.
You can take Exam AZ-500: Microsoft Azure Security Technologies once you have completed the learning path to earn a certification.
Microsoft Endpoint Configuration Manager—which is part of Microsoft Endpoint Manager—helps you protect the on-premises devices, apps, and data that the people at your organization use to stay productive. Our newest module, Understand co-management using Microsoft Endpoint Configuration Manager, provides an in-depth look at how to enable co-management based on the implementation path that best suits your organization. You’ll also:
We’re excited to hear how you use these updated resources on your journey to certification!
This article was originally posted by the FTC. See the original article here.
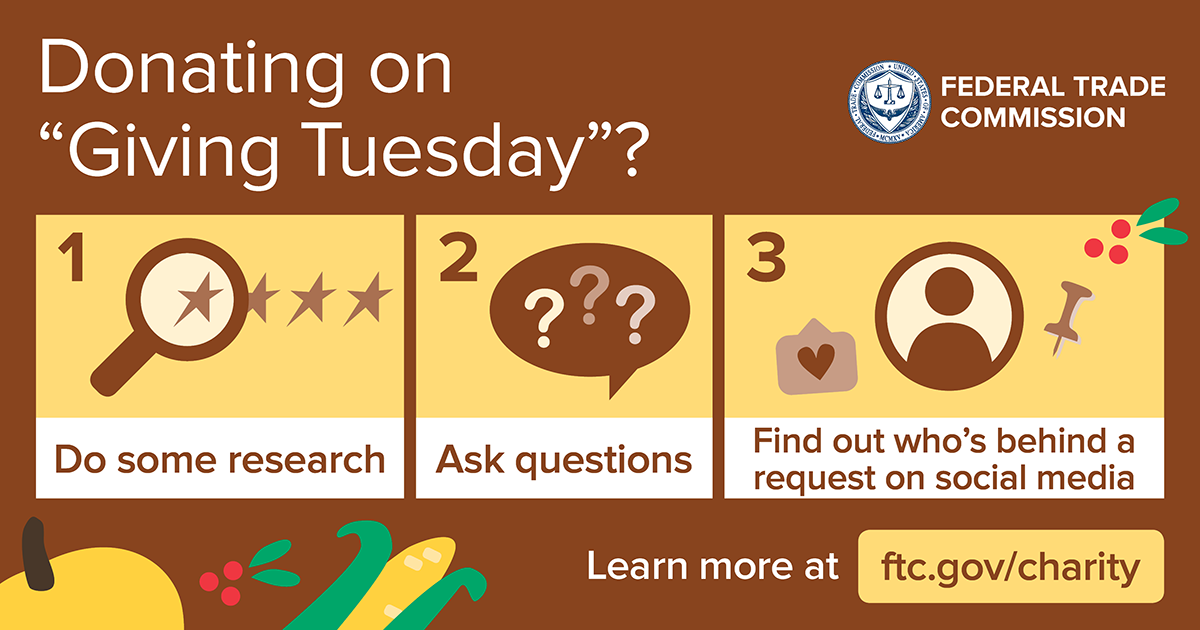
Giving Tuesday is a great time to show your gratitude by donating to help others. But you don’t want to give money to a fake charity or scammer (any day of the week).
Before you donate this Giving Tuesday ― and anytime you’re asked to give to charity:
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article is contributed. See the original author and article here.
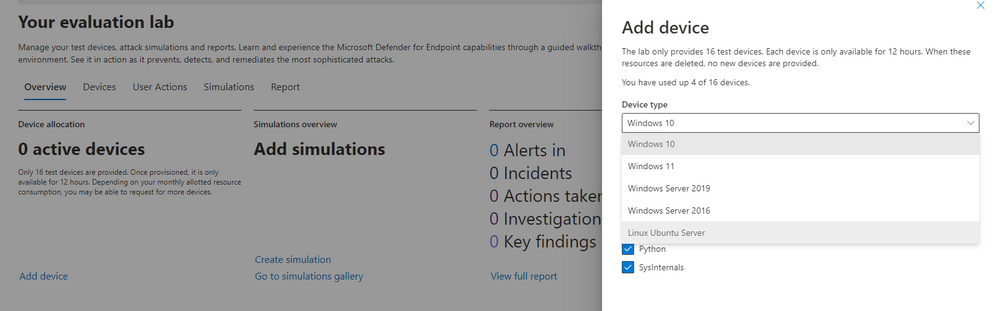
Microsoft Defender for Endpoint’s Evaluation Lab is an environment that allows security teams to seamlessly test their defense against threats. We are excited to share that the Evaluation Lab now supports adding Windows 11, Windows Server 2016, and Linux devices. In addition, we’d also like to announce a new partnership with Red Canary’s open-source simulation library, Atomic Red Team!
NOTE: Both updates are only available in the Microsoft 365 Defender portal at security.microsoft.com.
The evaluation lab now supports the following operating systems: Windows 10, Windows 11, Windows Server 2019, Windows Server 2016 and Linux (Ubuntu). To create a new device, simply select it within the “Add device” wizard. The new device will automatically be onboarded with no required additional steps.
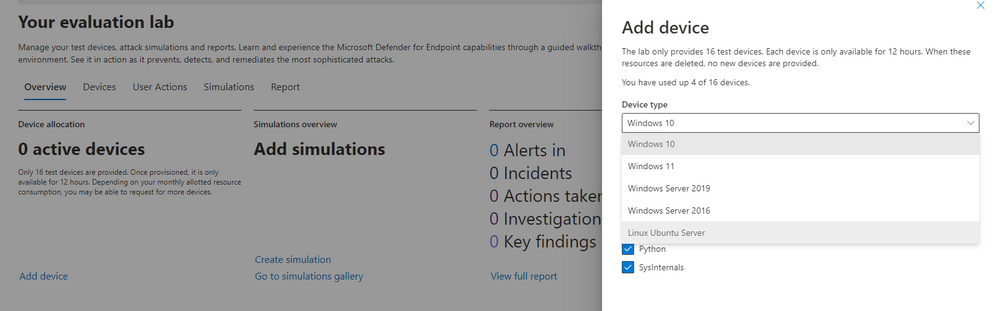
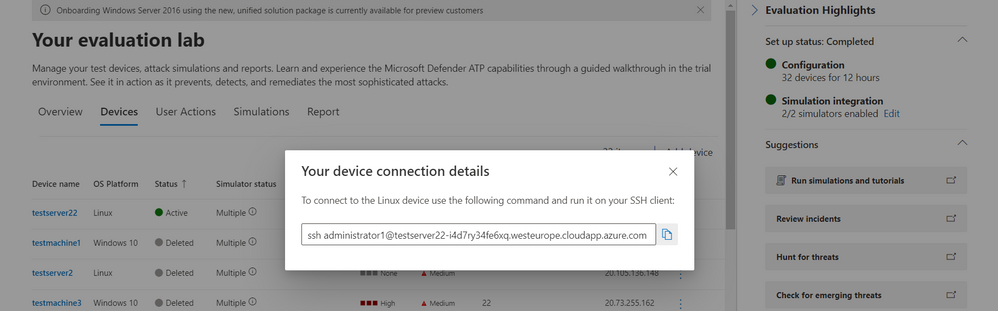
Once created, you can connect to the device via RDP (Windows) or SSH (Linux). You can connect to a Linux device using any SSH client.
Powered by Red Canary, Atomic Red Team is an open-source library of tests that security teams can use to simulate adversarial activity in their environments. Atomic tests are simple – each test is mapped to a single MITRE ATT&CK® technique or sub-technique, most of them have no prerequisites, and many come with easy-to-use configuration and cleanup commands.
Evaluation Lab users can now use Atomic Red Team simulations to evaluate Microsoft Defender for Endpoint’s detection capabilities against both Windows and Linux threats. The simulations are provided as script files, so that security teams can choose to run them in the Evaluation lab or any other testing environment of their choice.
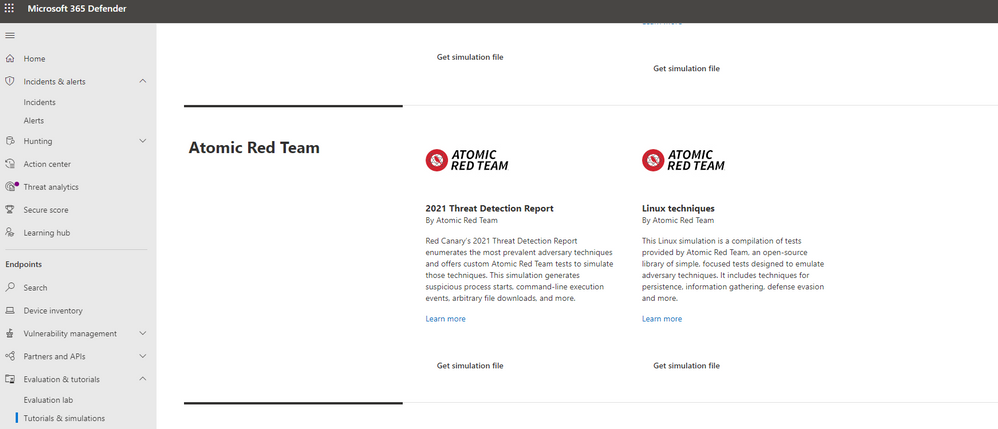
The first simulation, 2021 Threat Detection Report, executes tests according to Red Canary’s latest report of top Windows techniques associated with confirmed threats, as compiled from roughly 20,000 confirmed threats detected across customer environments.
The second simulation, Linux techniques, is a collection of simple tests compiled to allow security teams to evaluate Microsoft Defender for Endpoint’s detection capabilities against common Linux persistence, discovery, and defense evasion techniques.
We’re looking forward to you trying out the Evaluation Lab updates. Let us know your thoughts and feedback in the comments below or through the feedback tool in the portal!

This article is contributed. See the original author and article here.
Marketing professionals go to great lengths to understand customers. Detailed personas are written to identify the motivations, interests, and buying patterns of prospects and customers. But all too often, these personasand their resulting customer journeysare informed by data points important to the organization, not the customer. You cannot claim to be customer-centric, customer-first, or customer-obsessed if all the data you track is company-centric.
You may be thinking your organization is ahead of the customer journey curve here. After all, you’re already tracking customer-centric metrics such as net promoter score, customer satisfaction score, and customer effort score. But take a second look. These key performance indicators (KPIs) still ultimately measure benchmarks important to the organization, not the customer.
Nobody is arguing that an organization shouldn’t have a robust set of KPIs focused on measuring the fulfillment of important company objectives. But your toolbox of performance indicators doesn’t have to end thereand neither do the possibilities for the customer journey. Rather, take things to a whole new level by also measuring the fulfillment of customers’ objectives and optimizing the journey with the help of Microsoft Dynamics 365 Marketing.
Customer performance indicators (CPIs) quantify and measure outcomes that are desired by customers. These outcomes could include time savings, cost savings, convenience, flexibility, a sense of security, or any number of other outcomes customers deem valuable in the context of your product or service. There’s no cookie-cutter set of CPIs; they will vary widely across industries, organizations, products, and regions.
Consider the scenario of a retailer whose shoppers especially value speed. Acknowledging their shoppers’ priorities along with the need to balance services with expectations, the retailer tracks customers’ wait-time for curbside pick-up. They discover that wait times occasionally go beyond customer expectations. In response, the retailer implements a new feature that sends a flash promotional offer to high-value customers, when they are on their way during busy periods, for a complimentary drink redeemable from the in-store bar when they switch to in-store pickup. It’s a personalized gesture that acknowledges the retailer fell short of expectations but is trying to do its best to make it up to the customer. By optimizing the metrics that reflect what is important to the customer, the retailer can positively impact a whole host of KPIs, from customer satisfaction and customer loyalty to sales revenueand more.
There is a strong correlation between CPIs and KPIs. As illustrated by our retailer example, meeting the objective of a CPI is likely to boost associated KPIs. In fact, CPIs have been identified as powerful predictors of growth. Similarly, declining CPIs are likely to drag down associated KPIs.
CPIs also uncover insights about KPIs. Take customer satisfaction as an example. A high customer satisfaction score (a common KPI) indicates that an organization is doing something well. And while that’s critical information, this KPI on its own may not be able to provide visibility into what that something is. Or whether that something is even important to the customer. But a set of CPIs designed to measure desired customer outcomes such as personalized touches or chat availability can identify where the strongest correlations lie between what is important to the customer and what is important to the company.
CPIs and KPIs have a lot in common. They both measure performance, they both demonstrate progress toward an intended result, and they both impact the bottom line. For this reason, they can be difficult to distinguish from one another.
In the following table, we identify a few common KPIs. Alongside each KPI, we list one or more CPIs that could be used to enhance the understanding or performance of the associated KPI.
| KPI | CPI | How CPI supports KPI |
| Customer lifetime value | Value customer receives | Customer lifetime value can be increased if there’s focus on ensuring there is a minimum, measurable value provided to the customer as well. For example, a loyalty card program could strive to save customers at least $100 a year. |
| Customer satisfaction score |
In-person customer touches Online chat availability |
Do your customers value personalized, dedicated attention or the ability to quickly query representatives via informal chat applications? Understand the type of service interactions the customer values and implement CPIs to ensure you’re meeting expectations. |
| Product return rate |
Ease of product return Expense of product return |
Is product return rate low because the product is superior or because the return process is unwieldy or expensive? By additionally tracking and optimizing the return experience of customers, you’ll have greater insight into the reasons behind your product return rate. |
| Quote to close ratio | Quote turnaround time | There are many factors influencing quote to close ratio. Find out what your customers valuewhether it be fast quote turnaround, flexible pricing plans, or something elseand start measuring it. |
Find your customer performance indicators
What outcomes do your customers value? When you have the answer to that question, you can focus on delivering those outcomes. Every CPI identified, quantified, and measured brings new discoveries, new opportunities, and new levers to pull. Every CPI optimized is one more personalization you can bring to the customer journey, from brand voice and quote delivery to product bundling and customer service availability.
In short, it’s not enough to measure what’s important to your organizationnot if you want to optimize the customer journey and exceed customer expectations. You must also measure what’s important to your customers.
Learn how Dynamics 365 Marketing helps your organization optimize the CPIs that lead to elevated experiences.
The post The most important customer experience metrics (that you’re not tracking yet) appeared first on Microsoft Dynamics 365 Blog.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article is contributed. See the original author and article here.
As Americans prepare to hit the highways and airports this Thanksgiving holiday, CISA and the Federal Bureau of Investigation (FBI) are reminding critical infrastructure partners that malicious cyber actors aren’t making the same holiday plans as you. Recent history tells us that this could be a time when these persistent cyber actors halfway across the world are looking for ways—big and small—to disrupt the critical networks and systems belonging to organizations, businesses, and critical infrastructure.
There are actions that executives, leaders, and workers in any organization can take proactively to protect themselves against cyberattacks, including possible ransomware attacks, during the upcoming holiday season—a time during which offices are often closed, and employees are home with their friends and families. Although neither CISA nor the FBI currently have identified any specific threats, recent 2021 trends show malicious cyber actors launching serious and impactful ransomware attacks during holidays and weekends, including Independence Day and Mother’s Day weekends.
CISA and the FBI strongly urge all entities–especially critical infrastructure partners–to examine their current cybersecurity posture and implement best practices and mitigations to manage the risk posed by cyber threats. Specifically, CISA and the FBI urge users and organizations to take the following actions to protect themselves from becoming the next victim:
Additionally, CISA and the FBI recommend maintaining vigilance against the multiple techniques cybercriminals use to gain access to networks, including:
Finally—to reduce the risk of severe business/functional degradation should your organization fall victim to a ransomware attack—review and, if needed, update your incident response and communication plans. These plans should list actions to take—and contacts to reach out to—should your organization be impacted by a ransomware incident. Note: for assistance, review available incident response guidance, such as the Ransomware Response Checklist in the CISA-MS-ISAC Joint Ransomware Guide, the Public Power Cyber Incident Response Playbook, and the new Federal Government Cybersecurity Incident and Vulnerability Response Playbooks.
CISA and the FBI urge users and organizations to take these actions immediately to protect themselves against this threat. For a comprehensive overview, see the joint Cybersecurity Advisory Ransomware Awareness for Holidays and Weekends. For more information and resources on protecting against and responding to ransomware, visit StopRansomware.gov, a centralized, whole-of-government webpage providing ransomware resources and alerts.
Recent Comments