by Scott Muniz | Dec 6, 2021 | Security, Technology
This article is contributed. See the original author and article here.
| acronis — agent |
Sensitive information could be logged. The following products are affected: Acronis Agent (Windows, Linux, macOS) before build 27147 |
2021-11-29 |
5 |
CVE-2021-34800
MISC |
| acronis — cyber_protect |
DLL hijacking could lead to local privilege escalation. The following products are affected: Acronis Cyber Protect 15 (Windows) before build 28035 |
2021-11-29 |
4.4 |
CVE-2021-44198
MISC |
| acronis — cyber_protect |
Cross-site scripting (XSS) was possible in notification pop-ups. The following products are affected: Acronis Cyber Protect 15 (Windows, Linux) before build 28035 |
2021-11-29 |
4.3 |
CVE-2021-44201
MISC |
| actions-semi — ats2819p_firmware |
The Bluetooth Classic implementation on Actions ATS2815 chipsets does not properly handle the reception of continuous unsolicited LMP responses, allowing attackers in radio range to trigger a denial of service and shutdown of a device by flooding the target device with LMP_features_res packets. |
2021-11-30 |
6.1 |
CVE-2021-31787
MISC
MISC
MISC |
| afreecatv — afreecatv |
The vulnerability function is enabled when the streamer service related to the AfreecaTV communicated through web socket using 21201 port. A stack-based buffer overflow leading to remote code execution was discovered in strcpy() operate by “FanTicket” field. It is because of stored data without validation of length. |
2021-11-26 |
6.5 |
CVE-2020-7881
MISC |
| aomedia — aomedia |
AOM v2.0.1 was discovered to contain a NULL pointer dereference via the component av1/av1_dx_iface.c. |
2021-12-02 |
4.3 |
CVE-2020-36130
MISC |
| aomedia — aomedia |
AOM v2.0.1 was discovered to contain a NULL pointer dereference via the component rate_hist.c. |
2021-12-02 |
4.3 |
CVE-2020-36135
MISC |
| aomedia — aomedia |
AOM v2.0.1 was discovered to contain a stack buffer overflow via the component src/aom_image.c. |
2021-12-02 |
6.8 |
CVE-2020-36129
MISC |
| aomedia — aomedia |
AOM v2.0.1 was discovered to contain a stack buffer overflow via the component stats/rate_hist.c. |
2021-12-02 |
6.8 |
CVE-2020-36131
MISC |
| aomedia — aomedia |
AOM v2.0.1 was discovered to contain a global buffer overflow via the component av1/encoder/partition_search.h. |
2021-12-02 |
6.8 |
CVE-2020-36133
MISC |
| aomedia — aomedia |
AOM v2.0.1 was discovered to contain a segmentation violation via the component aom_dsp/x86/obmc_sad_avx2.c. |
2021-12-02 |
4.3 |
CVE-2020-36134
MISC |
| backstage — backstage |
@backstage/plugin-scaffolder-backend is the backend for the default Backstage software templates. In affected versions a malicious actor with write access to a registered scaffolder template is able to manipulate the template in a way that writes files to arbitrary paths on the scaffolder-backend host instance. This vulnerability can in some situation also be exploited through user input when executing a template, meaning you do not need write access to the templates. This method will not allow the attacker to control the contents of the injected file however, unless the template is also crafted in a specific way that gives control of the file contents. This vulnerability is fixed in version `0.15.14` of the `@backstage/plugin-scaffolder-backend`. This attack is mitigated by restricting access and requiring reviews when registering or modifying scaffolder templates. |
2021-11-29 |
5.5 |
CVE-2021-43783
CONFIRM
MISC |
| bandisoft — ark_library |
ARK library allows attackers to execute remote code via the parameter(path value) of Ark_NormalizeAndDupPAthNameW function because of an integer overflow. |
2021-11-26 |
6.8 |
CVE-2021-26615
MISC |
| bannersky — bsk_pdf_manager |
The BSK PDF Manager WordPress plugin before 3.1.2 does not validate and escape the orderby and order parameters before using them in a SQL statement, leading to a SQL injection issue |
2021-11-29 |
6.5 |
CVE-2021-24860
MISC |
| bluez — bluez |
A heap-based buffer overflow was discovered in bluetoothd in BlueZ through 5.48. There isn’t any check on whether there is enough space in the destination buffer. The function simply appends all data passed to it. The values of all attributes that are requested are appended to the output buffer. There are no size checks whatsoever, resulting in a simple heap overflow if one can craft a request where the response is large enough to overflow the preallocated buffer. This issue exists in service_attr_req gets called by process_request (in sdpd-request.c), which also allocates the response buffer. |
2021-11-29 |
5.8 |
CVE-2019-8922
MISC
CONFIRM |
| bookstackapp — bookstack |
bookstack is vulnerable to Improper Access Control |
2021-11-30 |
4 |
CVE-2021-4026
CONFIRM
MISC |
| bookstackapp — bookstack |
bookstack is vulnerable to Cross-Site Request Forgery (CSRF) |
2021-12-02 |
4 |
CVE-2021-3944
MISC
CONFIRM |
| browser_and_operating_system_finder_project — browser_and_operating_system_finder |
Cross-site request forgery (CSRF) vulnerability in Browser and Operating System Finder versions prior to 1.2 allows a remote unauthenticated attacker to hijack the authentication of an administrator via unspecified vectors. |
2021-12-01 |
6.8 |
CVE-2021-20851
MISC
MISC |
| bulk_datetime_change_project — bulk_datetime_change |
The Bulk Datetime Change WordPress plugin before 1.12 does not enforce capability checks which allows users with Contributor roles to 1) list private post titles of other users and 2) change the posted date of other users’ posts. |
2021-11-29 |
5.5 |
CVE-2021-24842
MISC
CONFIRM |
| businessdnasolutions — topease |
Incorrect Access Control in Web Applications operating on Business-DNA Solutions GmbH’s TopEase® Platform Version <= 7.1.27 allows an authenticated remote attacker to view the Shape Editor and Settings, which are functionality for higher privileged users, via identifying said components in the front-end source code or other means. |
2021-11-30 |
4 |
CVE-2021-42116
CONFIRM |
| businessdnasolutions — topease |
Missing HTTPOnly flag in Web Applications operating on Business-DNA Solutions GmbH’s TopEase® Platform Version <= 7.1.27 allows an unauthenticated remote attacker to escalate privileges from unauthenticated to authenticated user via stealing and injecting the session- independent and static cookie UID. |
2021-11-30 |
6.4 |
CVE-2021-42115
CONFIRM |
| businessdnasolutions — topease |
Unrestricted File Upload in Web Applications operating on Business-DNA Solutions GmbH’s TopEase® Platform Version <= 7.1.27 in the File Upload Functions allows an authenticated remote attacker with Upload privileges to upload files with any file type, enabling client-side attacks. |
2021-11-30 |
6.5 |
CVE-2021-42123
CONFIRM |
| businessdnasolutions — topease |
Insufficient Input Validation in Web Applications operating on Business-DNA Solutions GmbH’s TopEase® Platform Version <= 7.1.27 on an object’s date attribute(s) allows an authenticated remote attacker with Object Modification privileges to insert an unexpected format into date fields, which leads to breaking the object page that the date field is present. |
2021-11-30 |
4 |
CVE-2021-42121
CONFIRM |
| businessdnasolutions — topease |
Insufficient Input Validation in Web Applications operating on Business-DNA Solutions GmbH’s TopEase® Platform Version <= 7.1.27 allows an authenticated remote attacker with Object Modification privileges to insert arbitrary HTML without code execution. |
2021-11-30 |
4 |
CVE-2021-42117
CONFIRM |
| businessdnasolutions — topease |
Insufficient Input Validation in Web Applications operating on Business-DNA Solutions GmbH’s TopEase® Platform Version <= 7.1.27 on all object attributes allows an authenticated remote attacker with Object Modification privileges to insert arbitrarily long strings, eventually leading to exhaustion of the underlying resource. |
2021-11-30 |
4 |
CVE-2021-42120
CONFIRM |
| businessdnasolutions — topease |
Insufficient Input Validation in Web Applications operating on Business-DNA Solutions GmbH’s TopEase® Platform Version <= 7.1.27 on an object’s attributes with numeric format allows an authenticated remote attacker with Object Modification privileges to insert an unexpected format, which makes the affected attribute non-editable. |
2021-11-30 |
4 |
CVE-2021-42122
CONFIRM |
| bytecodealliance — lucet |
Lucet is a native WebAssembly compiler and runtime. There is a bug in the main branch of `lucet-runtime` affecting all versions published to crates.io that allows a use-after-free in an Instance object that could result in memory corruption, data race, or other related issues. This bug was introduced early in the development of Lucet and is present in all releases. As a result of this bug, and dependent on the memory backing for the Instance objects, it is possible to trigger a use-after-free when the Instance is dropped. Users should upgrade to the main branch of the Lucet repository. Lucet no longer provides versioned releases on crates.io. There is no way to remediate this vulnerability without upgrading. |
2021-11-30 |
6.8 |
CVE-2021-43790
CONFIRM
MISC
MISC |
| cbads — clickbank_affiliate_ads |
The ClickBank Affiliate Ads WordPress plugin through 1.20 does not have CSRF check when saving its settings, allowing attacker to make logged in admin change them via a CSRF attack. Furthermore, due to the lack of escaping when they are outputting, it could also lead to Stored Cross-Site Scripting issues |
2021-12-02 |
6.8 |
CVE-2015-20105
MISC
MISC
MISC |
| chamilo — chamilo |
chamilo-lms v1.11.14 is affected by a Cross Site Scripting (XSS) vulnerability in /plugin/jcapture/applet.php if an attacker passes a message hex2bin in the cookie. |
2021-12-01 |
4.3 |
CVE-2021-43687
MISC
MISC
MISC |
| cloverdx — cloverdx |
CloverDX Server before 5.11.2 and and 5.12.x before 5.12.1 allows XXE during configuration import. |
2021-12-01 |
6.8 |
CVE-2021-42776
CONFIRM
MISC |
| codesys — git |
Affected versions of CODESYS Git in Versions prior to V1.1.0.0 lack certificate validation in HTTPS handshakes. CODESYS Git does not implement certificate validation by default, so it does not verify that the server provides a valid and trusted HTTPS certificate. Since the certificate of the server to which the connection is made is not properly verified, the server connection is vulnerable to a man-in-the-middle attack. |
2021-12-01 |
5.8 |
CVE-2021-34599
CONFIRM |
| concretecms — concrete_cms |
An issue was discovered in Concrete CMS before 8.5.7. The Dashboard allows a user’s password to be changed without a prompt for the current password. |
2021-11-30 |
6.5 |
CVE-2021-40101
CONFIRM
MISC |
| contact_form_with_captcha_project — contact_form_with_captcha |
The Contact Form With Captcha WordPress plugin is vulnerable to Cross-Site Request Forgery due to missing nonce validation in the ~/cfwc-form.php file during contact form submission, which made it possible for attackers to inject arbitrary web scripts in versions up to, and including 1.6.2. |
2021-11-29 |
6.8 |
CVE-2021-42358
MISC
MISC |
| craftercms — crafter_cms |
Unauthenticated remote attackers can read textual content via FreeMarker including files /scripts/*, /templates/* and some of the files in /.git/* (non-binary). |
2021-12-02 |
5 |
CVE-2021-23263
MISC |
| craftercms — crafter_cms |
Installations, where crafter-search is not protected, allow unauthenticated remote attackers to create, view, and delete search indexes. |
2021-12-02 |
6.4 |
CVE-2021-23264
MISC |
| craftercms — crafter_cms |
Authenticated administrators may modify the main YAML configuration file and load a Java class resulting in RCE. |
2021-12-02 |
6.5 |
CVE-2021-23262
MISC |
| craftercms — crafter_cms |
Authenticated administrators may override the system configuration file and cause a denial of service. |
2021-12-02 |
4 |
CVE-2021-23261
MISC |
| craftercms — crafter_cms |
Authenticated users with Administrator or Developer roles may execute OS commands by Groovy Script which uses Groovy lib to render a webpage. The groovy script does not have security restrictions, which will cause attackers to execute arbitrary commands remotely(RCE). |
2021-12-02 |
6.5 |
CVE-2021-23259
MISC |
| craftercms — crafter_cms |
Authenticated users with Administrator or Developer roles may execute OS commands by SPEL Expression in Spring beans. SPEL Expression does not have security restrictions, which will cause attackers to execute arbitrary commands remotely (RCE). |
2021-12-02 |
6.5 |
CVE-2021-23258
MISC |
| cryptshare — cryptshare_server |
An open redirect through HTML injection in confidential messages in Cryptshare before 5.1.0 allows remote attackers (with permission to provide confidential messages via Cryptshare) to redirect targeted victims to any URL via the ‘<meta http-equiv=”refresh”‘ substring in the editor parameter. |
2021-11-30 |
4.9 |
CVE-2021-42564
MISC |
| dell — emc_streaming_data_platform |
Dell EMC Streaming Data Platform, versions prior to 1.3 contain an SSL Strip Vulnerability in the User Interface (UI). A remote unauthenticated attacker could potentially exploit this vulnerability, leading to a downgrade in the communications between the client and server into an unencrypted format. |
2021-11-30 |
4.3 |
CVE-2021-36326
MISC |
| dell — emc_streaming_data_platform |
Dell EMC Streaming Data Platform versions before 1.3 contain an Indirect Object Reference Vulnerability. A remote malicious user may potentially exploit this vulnerability to gain sensitive information. |
2021-11-30 |
4 |
CVE-2021-36329
MISC |
| dell — emc_streaming_data_platform |
Dell EMC Streaming Data Platform versions before 1.3 contain a Server Side Request Forgery Vulnerability. A remote unauthenticated attacker may potentially exploit this vulnerability to perform port scanning of internal networks and make HTTP requests to an arbitrary domain of the attacker’s choice. |
2021-11-30 |
5 |
CVE-2021-36327
MISC |
| dell — emc_streaming_data_platform |
Dell EMC Streaming Data Platform versions before 1.3 contain a SQL Injection Vulnerability. A remote malicious user may potentially exploit this vulnerability to execute SQL commands to perform unauthorized actions and retrieve sensitive information from the database. |
2021-11-30 |
6.5 |
CVE-2021-36328
MISC |
| discourse — discourse |
Discourse is an open source discussion platform. In affected versions an attacker can poison the cache for anonymous (i.e. not logged in) users, such that the users are shown a JSON blob instead of the HTML page. This can lead to a partial denial-of-service. This issue is patched in the latest stable, beta and tests-passed versions of Discourse. |
2021-12-01 |
5 |
CVE-2021-43794
CONFIRM
MISC |
| discourse — discourse |
Discourse is an open source discussion platform. In affected versions a vulnerability in the Polls feature allowed users to vote multiple times in a single-option poll. The problem is patched in the latest tests-passed, beta and stable versions of Discourse |
2021-12-01 |
4 |
CVE-2021-43793
CONFIRM
MISC
MISC |
| django-helpdesk_project — django-helpdesk |
django-helpdesk is vulnerable to Improper Neutralization of Input During Web Page Generation (‘Cross-site Scripting’) |
2021-12-01 |
6.8 |
CVE-2021-3994
MISC
CONFIRM |
| dzzoffice — dzzoffice |
dzzoffice 2.02.1_SC_UTF8 is affected by a Cross Site Scripting (XSS) vulnerability in explorerfile.php. The output of exit function will be print for the user exit(json_encode($return)). |
2021-12-03 |
4.3 |
CVE-2021-43673
MISC |
| eclipse — mosquitto |
In versions 1.6 to 2.0.11 of Eclipse Mosquitto, an MQTT v5 client connecting with a large number of user-property properties could cause excessive CPU usage, leading to a loss of performance and possible denial of service. |
2021-12-01 |
5 |
CVE-2021-41039
CONFIRM |
| elecom — wrc-1167gst2_firmware |
Improper access control vulnerability in ELECOM LAN routers (WRC-1167GST2 firmware v1.25 and prior, WRC-1167GST2A firmware v1.25 and prior, WRC-1167GST2H firmware v1.25 and prior, WRC-2533GS2-B firmware v1.52 and prior, WRC-2533GS2-W firmware v1.52 and prior, WRC-1750GS firmware v1.03 and prior, WRC-1750GSV firmware v2.11 and prior, WRC-1900GST firmware v1.03 and prior, WRC-2533GST firmware v1.03 and prior, WRC-2533GSTA firmware v1.03 and prior, WRC-2533GST2 firmware v1.25 and prior, WRC-2533GST2SP firmware v1.25 and prior, WRC-2533GST2-G firmware v1.25 and prior, and EDWRC-2533GST2 firmware v1.25 and prior) allows a network-adjacent authenticated attacker to bypass access restriction and to access the management screen of the product via unspecified vectors. |
2021-12-01 |
5.8 |
CVE-2021-20861
MISC
MISC |
| elecom — wrc-1167gst2_firmware |
Cross-site request forgery (CSRF) vulnerability in ELECOM LAN routers (WRC-1167GST2 firmware v1.25 and prior, WRC-1167GST2A firmware v1.25 and prior, WRC-1167GST2H firmware v1.25 and prior, WRC-2533GS2-B firmware v1.52 and prior, WRC-2533GS2-W firmware v1.52 and prior, WRC-1750GS firmware v1.03 and prior, WRC-1750GSV firmware v2.11 and prior, WRC-1900GST firmware v1.03 and prior, WRC-2533GST firmware v1.03 and prior, WRC-2533GSTA firmware v1.03 and prior, WRC-2533GST2 firmware v1.25 and prior, WRC-2533GST2SP firmware v1.25 and prior, WRC-2533GST2-G firmware v1.25 and prior, and EDWRC-2533GST2 firmware v1.25 and prior) allows a remote authenticated attacker to hijack the authentication of an administrator via a specially crafted page. |
2021-12-01 |
6.8 |
CVE-2021-20860
MISC
MISC |
| elecom — wrh-733gbk_firmware |
ELECOM LAN routers (WRH-733GBK firmware v1.02.9 and prior and WRH-733GWH firmware v1.02.9 and prior) allows a network-adjacent attacker with an administrator privilege to execute arbitrary OS commands via unspecified vectors. |
2021-12-01 |
5.2 |
CVE-2021-20854
MISC
MISC |
| elecom — wrh-733gbk_firmware |
Buffer overflow vulnerability in ELECOM LAN routers (WRH-733GBK firmware v1.02.9 and prior and WRH-733GWH firmware v1.02.9 and prior) allows a network-adjacent attacker with an administrator privilege to execute an arbitrary OS command via unspecified vectors. |
2021-12-01 |
5.2 |
CVE-2021-20852
MISC
MISC |
| elecom — wrh-733gbk_firmware |
ELECOM LAN routers (WRH-733GBK firmware v1.02.9 and prior and WRH-733GWH firmware v1.02.9 and prior) allows a network-adjacent attacker with an administrator privilege to execute arbitrary OS commands via unspecified vectors. |
2021-12-01 |
5.2 |
CVE-2021-20853
MISC
MISC |
| elgg — elgg |
elgg is vulnerable to Authorization Bypass Through User-Controlled Key |
2021-12-01 |
4.3 |
CVE-2021-3964
MISC
CONFIRM |
| emoji_button_project — emoji_button |
@joeattardi/emoji-button is a Vanilla JavaScript emoji picker component. In affected versions there are two vectors for XSS attacks: a URL for a custom emoji, and an i18n string. In both of these cases, a value can be crafted such that it can insert a `script` tag into the page and execute malicious code. |
2021-11-26 |
4.3 |
CVE-2021-43785
CONFIRM
MISC
MISC |
| f-secure — atlant |
A vulnerability affecting F-Secure antivirus engine was discovered whereby unpacking UPX file can lead to denial-of-service. The vulnerability can be exploited remotely by an attacker. A successful attack will result in denial-of-service of the antivirus engine. |
2021-11-26 |
4.3 |
CVE-2021-40833
MISC
MISC |
| firefly-iii — firefly_iii |
firefly-iii is vulnerable to Cross-Site Request Forgery (CSRF) |
2021-12-01 |
4.3 |
CVE-2021-4015
MISC
CONFIRM |
| fortinet — forticlient |
An unsafe search path vulnerability in FortiClientWindows 7.0.0, 6.4.6 and below, 6.2.x, 6.0.x and FortiClientEMS 7.0.0, 6.4.6 and below, 6.2.x, 6.0.x may allow an attacker to perform a DLL Hijack attack on affected devices via a malicious OpenSSL engine library in the search path. |
2021-12-01 |
6.9 |
CVE-2021-32592
CONFIRM |
| gnu — mailman |
In GNU Mailman before 2.1.38, a list member or moderator can get a CSRF token and craft an admin request (using that token) to set a new admin password or make other changes. |
2021-12-02 |
6.8 |
CVE-2021-44227
MISC |
| haschek — pictshare |
pictshare v1.5 is affected by a Cross Site Scripting (XSS) vulnerability in api/info.php. The exit function will terminate the script and print the message which has $_REQUEST[‘hash’]. |
2021-12-02 |
4.3 |
CVE-2021-43683
MISC |
| hashicorp — vault |
HashiCorp Vault and Vault Enterprise 0.11.0 up to 1.7.5 and 1.8.4 templated ACL policies would always match the first-created entity alias if multiple entity aliases exist for a specified entity and mount combination, potentially resulting in incorrect policy enforcement. Fixed in Vault and Vault Enterprise 1.7.6, 1.8.5, and 1.9.0. |
2021-11-30 |
6.4 |
CVE-2021-43998
MISC |
| huawei — ecns280_td_firmware |
Some Huawei products use the OpenHpi software for hardware management. A function that parses data returned by OpenHpi contains an out-of-bounds read vulnerability that could lead to a denial of service. Affected product versions include: eCNS280_TD V100R005C10; eSE620X vESS V100R001C10SPC200, V100R001C20SPC200, V200R001C00SPC300. |
2021-11-29 |
6.8 |
CVE-2021-39995
MISC |
| ibm — mq_appliance |
IBM MQ Appliance 9.2 CD and 9.2 LTS could allow a local privileged user to inject and execute malicious code. IBM X-Force ID: 212441. |
2021-11-30 |
4.6 |
CVE-2021-38967
XF
CONFIRM |
| ibm — qradar_security_information_and_event_manager |
IBM QRadar SIEM 7.3 and 7.4 is vulnerable to cross-site scripting. This vulnerability allows users to embed arbitrary JavaScript code in the Web UI thus altering the intended functionality potentially leading to credentials disclosure within a trusted session. IBM X-Force ID: 205281. |
2021-12-01 |
4.3 |
CVE-2021-29849
CONFIRM
XF |
| ibm — qradar_security_information_and_event_manager |
IBM QRadar SIEM 7.3 and 7.4 could allow an attacker to obtain sensitive information due to the server performing key exchange without entity authentication on inter-host communications using man in the middle techniques. IBM X-Force ID: 203033. |
2021-12-01 |
4.3 |
CVE-2021-29779
CONFIRM
XF |
| ibm — qradar_security_information_and_event_manager |
IBM QRadar SIEM 7.3 and 7.4 uses weaker than expected cryptographic algorithms that could allow an attacker to decrypt highly sensitive information. IBM X-Force ID: 196074. |
2021-12-01 |
5 |
CVE-2021-20400
XF
CONFIRM |
| ibm — qradar_security_information_and_event_manager |
IBM QRadar SIEM 7.3 and 7.4 is vulnerable to server side request forgery (SSRF). This may allow an authenticated attacker to send unauthorized requests from the system, potentially leading to network enumeration or facilitating other attacks. This vulnerability is due to an incomplete fix for CVE-2020-4786. IBM X-Force ID: 206087. |
2021-12-01 |
4 |
CVE-2021-29863
XF
CONFIRM |
| iptime — c200_firmware |
This issue was discovered when the ipTIME C200 IP Camera was synchronized with the ipTIME NAS. It is necessary to extract value for ipTIME IP camera because the ipTIME NAS send ans setCookie(‘[COOKIE]’) . The value is transferred to the –header option in wget binary, and there is no validation check. This vulnerability allows remote attackers to execute remote command. |
2021-11-30 |
6.8 |
CVE-2020-7879
MISC |
| ipuptime — pinkie |
Pinkie 2.15 allows remote attackers to cause a denial of service (daemon crash) via a TFTP read (RRQ) request, aka opcode 1. |
2021-11-29 |
5 |
CVE-2021-44428
MISC |
| issabel — pbx |
issabelPBX version 2.11 is affected by a Cross Site Scripting (XSS) vulnerability. In file page.backup_restore.php, the exit function will terminate the script and print the message to the user. The message will contain $_REQUEST without sanitization, then there is a XSS vulnerability. |
2021-11-29 |
4.3 |
CVE-2021-43695
MISC |
| jamf — jamf |
An issue was discovered in Jamf Pro before 10.32.0, aka PI-009921. An account can be granted incorrect privileges in response to authentication that uses specific sign-on workflows. |
2021-12-01 |
6.5 |
CVE-2021-40809
MISC
CONFIRM
MISC |
| kazencoders — url_shortify |
The URL Shortify WordPress plugin before 1.5.1 does not have CSRF check in place when bulk-deleting links or groups, which could allow attackers to make a logged in admin delete arbitrary link and group via a CSRF attack. |
2021-11-29 |
4.3 |
CVE-2021-24749
MISC |
| keepalived — keepalived |
In Keepalived through 2.2.4, the D-Bus policy does not sufficiently restrict the message destination, allowing any user to inspect and manipulate any property. This leads to access-control bypass in some situations in which an unrelated D-Bus system service has a settable (writable) property |
2021-11-26 |
5.5 |
CVE-2021-44225
MISC
MISC |
| kimai — kimai2 |
kimai2 is vulnerable to Improper Neutralization of Input During Web Page Generation (‘Cross-site Scripting’) |
2021-12-01 |
6 |
CVE-2021-3985
MISC
CONFIRM |
| kimai2_project — kimai2 |
kimai2 is vulnerable to Improper Access Control |
2021-12-01 |
4 |
CVE-2021-3992
CONFIRM
MISC |
| kimai2_project — kimai2 |
kimai2 is vulnerable to Improper Neutralization of Input During Web Page Generation (‘Cross-site Scripting’) |
2021-12-01 |
4.3 |
CVE-2021-3983
MISC
CONFIRM |
| librenms — librenms |
Librenms 21.11.0 is affected by a Cross Site Scripting (XSS) vulnerability in includes/html/forms/poller-groups.inc.php. |
2021-12-01 |
4.3 |
CVE-2021-44279
MISC |
| librenms — librenms |
Librenms 21.11.0 is affected by a Cross Site Scripting (XSS) vulnerability in includes/html/common/alert-log.inc.php. |
2021-12-01 |
4.3 |
CVE-2021-44277
MISC |
| linuxfoundation — auth_backend |
Backstage is an open platform for building developer portals. In affected versions the auth-backend plugin allows a malicious actor to trick another user into visiting a vulnerable URL that executes an XSS attack. This attack can potentially allow the attacker to exfiltrate access tokens or other secrets from the user’s browser. The default CSP does prevent this attack, but it is expected that some deployments have these policies disabled due to incompatibilities. This is vulnerability is patched in version `0.4.9` of `@backstage/plugin-auth-backend`. |
2021-11-26 |
4.3 |
CVE-2021-43776
CONFIRM
MISC |
| mahadiscom — mahavitaran |
Mahavitaran android application 7.50 and prior transmit sensitive information in URL parameters. This may lead to information disclosure if unauthorized parties have access to the URLs via server logs, referrer header, MITM or browser history. |
2021-12-02 |
4.3 |
CVE-2020-27414
MISC |
| manage_project — manage |
manage (last update Oct 24, 2017) is affected by a Cross Site Scripting (XSS) vulnerability in Application/Home/Controller/GoodsController.class.php. The exit function will terminate the script and print a message which have values from $_POST. |
2021-12-01 |
4.3 |
CVE-2021-43689
MISC |
| mandsconsulting — email_before_download |
The Email Before Download WordPress plugin before 6.8 does not properly validate and escape the order and orderby GET parameters before using them in SQL statements, leading to authenticated SQL injection issues |
2021-11-29 |
6.5 |
CVE-2021-24748
MISC |
| mycred — mycred |
The myCred WordPress plugin before 1.7.8 does not sanitise and escape the user parameter before outputting it back in the Points Log admin dashboard, leading to a Reflected Cross-Site Scripting |
2021-11-29 |
4.3 |
CVE-2017-20008
MISC
CONFIRM |
| mycred — mycred |
The myCred WordPress plugin before 2.3 does not validate or escape the fields parameter before using it in a SQL statement, leading to an SQL injection exploitable by any authenticated user |
2021-11-29 |
6.5 |
CVE-2021-24755
MISC |
| nextcloud — news |
nextcloud news-android is an Android client for the Nextcloud news/feed reader app. In affected versions the Nextcloud News for Android app has a security issue by which a malicious application installed on the same device can send it an arbitrary Intent that gets reflected back, unintentionally giving read and write access to non-exported Content Providers in Nextcloud News for Android. Users should upgrade to version 0.9.9.63 or higher as soon as possible. |
2021-11-30 |
5.8 |
CVE-2021-41256
MISC
MISC
CONFIRM |
| ninjaforms — ninja_forms |
The Ninja Forms Contact Form WordPress plugin before 3.6.4 does not escape keys of the fields POST parameter, which could allow high privilege users to perform SQL injections attacks |
2021-11-29 |
6.5 |
CVE-2021-24889
MISC |
| nodebb — nodebb |
Nodebb is an open source Node.js based forum software. In affected versions a prototype pollution vulnerability in the uploader module allowed a malicious user to inject arbitrary data (i.e. javascript) into the DOM, theoretically allowing for an account takeover when used in conjunction with a path traversal vulnerability disclosed at the same time as this report. The vulnerability has been patched as of v1.18.5. Users are advised to upgrade as soon as possible. |
2021-11-29 |
4.3 |
CVE-2021-43787
MISC
MISC
CONFIRM |
| nodebb — nodebb |
Nodebb is an open source Node.js based forum software. Prior to v1.18.5, a path traversal vulnerability was present that allowed users to access JSON files outside of the expected `languages/` directory. The vulnerability has been patched as of v1.18.5. Users are advised to upgrade as soon as possible. |
2021-11-29 |
4 |
CVE-2021-43788
MISC
CONFIRM
MISC |
| nodebb — nodebb |
Nodebb is an open source Node.js based forum software. In affected versions incorrect logic present in the token verification step unintentionally allowed master token access to the API. The vulnerability has been patch as of v1.18.5. Users are advised to upgrade as soon as possible. |
2021-11-29 |
5 |
CVE-2021-43786
CONFIRM
MISC
MISC |
| nttdocomo — wi-fi_station_sh-52a_firmware |
Cross-site scripting vulnerability in Wi-Fi STATION SH-52A (38JP_1_11G, 38JP_1_11J, 38JP_1_11K, 38JP_1_11L, 38JP_1_26F, 38JP_1_26G, 38JP_1_26J, 38JP_2_03B, and 38JP_2_03C) allows a remote unauthenticated attacker to inject an arbitrary script via WebUI of the device. |
2021-12-01 |
4.3 |
CVE-2021-20847
MISC
MISC |
| nzedb_project — nzedb |
nZEDb v0.4.20 is affected by a Cross Site Scripting (XSS) vulnerability in www/pages/api.php. The exit function will terminate the script and print the message which has the input $_GET[‘t’]. |
2021-12-02 |
4.3 |
CVE-2021-43686
MISC |
| omnipod — insulin_management_system_firmware |
Insulet Omnipod Insulin Management System insulin pump product ID 19191 and 40160 is designed to communicate using a wireless RF with an Insulet manufactured Personal Diabetes Manager device. This wireless RF communication protocol does not properly implement authentication or authorization. An attacker with access to one of the affected insulin pump models may be able to modify and/or intercept data. This vulnerability could also allow attackers to change pump settings and control insulin delivery. |
2021-12-01 |
4.8 |
CVE-2020-10627
MISC
MISC |
| os4ed — opensis |
A SQL injection vulnerability exists in version 8.0 of openSIS when MySQL or MariaDB is used as the application database. An attacker can then issue the SQL command through the /opensis/modules/users/Staff.php, staff{TITLE] parameter. |
2021-11-30 |
6.8 |
CVE-2021-41678
MISC |
| os4ed — opensis |
A SQL injection vulnerability exists in version 8.0 of openSIS when MySQL or MariaDB is used as the application database. An attacker can then issue the SQL command through the /opensis/functions/GetStuListFnc.php &Grade= parameter. |
2021-11-30 |
6.8 |
CVE-2021-41677
MISC |
| os4ed — opensis |
A SQL injection vulnerability exists in version 8.0 of openSIS when MySQL or MariaDB is used as the application database. An attacker can then issue the SQL command through the /opensis/modules/grades/InputFinalGrades.php, period parameter. |
2021-11-30 |
6.8 |
CVE-2021-41679
MISC |
| php — php |
In PHP versions 7.3.x below 7.3.33, 7.4.x below 7.4.26 and 8.0.x below 8.0.13, certain XML parsing functions, like simplexml_load_file(), URL-decode the filename passed to them. If that filename contains URL-encoded NUL character, this may cause the function to interpret this as the end of the filename, thus interpreting the filename differently from what the user intended, which may lead it to reading a different file than intended. |
2021-11-29 |
5 |
CVE-2021-21707
MISC |
| phpwhois_project — phpwhois |
phpWhois (last update Jun 30 2021) is affected by a Cross Site Scripting (XSS) vulnerability. In file example.php, the exit function will terminate the script and print the message to the user. The message will contain $_GET[‘query’] then there is a XSS vulnerability. |
2021-11-29 |
4.3 |
CVE-2021-43698
MISC |
| planetargon — oh_my_zsh |
Vulnerability in dirhistory plugin Description: the widgets that go back and forward in the directory history, triggered by pressing Alt-Left and Alt-Right, use functions that unsafely execute eval on directory names. If you cd into a directory with a carefully-crafted name, then press Alt-Left, the system is subject to command injection. Impacted areas: – Functions pop_past and pop_future in dirhistory plugin. |
2021-11-30 |
6.8 |
CVE-2021-3725
MISC |
| portswigger — burp_suite |
PortSwigger Burp Suite Enterprise Edition before 2021.11 on Windows has weak file permissions for the embedded H2 database, which might lead to privilege escalation. This issue can be exploited by an adversary who has already compromised a valid Windows account on the server via separate means. In this scenario, the compromised account may have inherited read access to sensitive configuration, database, and log files. |
2021-11-30 |
4 |
CVE-2021-44230
MISC |
| qnap — qvr |
An improper authentication vulnerability has been reported to affect QNAP device, VioStor. If exploited, this vulnerability allows attackers to compromise the security of the system. We have already fixed this vulnerability in the following versions of QVR: QVR FW 5.1.6 build 20211109 and later |
2021-11-26 |
6.8 |
CVE-2021-38686
CONFIRM |
| roundupwp — registrations_for_the_events_calendar |
The Registrations for the Events Calendar WordPress plugin before 2.7.5 does not escape the v parameter before outputting it back in an attribute, leading to a Reflected Cross-Site Scripting |
2021-11-29 |
4.3 |
CVE-2021-24876
MISC |
| s3scanner_project — s3scanner |
S3Scanner before 2.0.2 allows Directory Traversal via a crafted bucket, as demonstrated by a <Key>../ substring in a ListBucketResult element. |
2021-11-29 |
5 |
CVE-2021-32061
MISC
MISC
MISC |
| showdoc — showdoc |
showdoc is vulnerable to URL Redirection to Untrusted Site |
2021-12-01 |
5.8 |
CVE-2021-3989
MISC
CONFIRM |
| showdoc — showdoc |
showdoc is vulnerable to Cross-Site Request Forgery (CSRF) |
2021-12-01 |
4.3 |
CVE-2021-3993
CONFIRM
MISC |
| showdoc — showdoc |
showdoc is vulnerable to Use of Cryptographically Weak Pseudo-Random Number Generator (PRNG) |
2021-12-01 |
4.3 |
CVE-2021-3990
MISC
CONFIRM |
| showdoc — showdoc |
showdoc is vulnerable to Cross-Site Request Forgery (CSRF) |
2021-12-01 |
6.8 |
CVE-2021-4017
CONFIRM
MISC |
| sophos — unified_threat_management_up2date |
An authenticated user could potentially execute code via an SQLi vulnerability in the user portal of SG UTM before version 9.708 MR8. |
2021-11-26 |
6.5 |
CVE-2021-36807
CONFIRM |
| stetic — stetic |
The Stetic WordPress plugin is vulnerable to Cross-Site Request Forgery due to missing nonce validation via the stats_page function found in the ~/stetic.php file, which made it possible for attackers to inject arbitrary web scripts in versions up to, and including 1.0.6. |
2021-11-29 |
6.8 |
CVE-2021-42364
MISC
MISC |
| taogogo — taocms |
Taocms v2.5Beta5 was discovered to contain a blind SQL injection vulnerability via the function Article Search. |
2021-12-02 |
6.5 |
CVE-2021-25783
MISC |
| taogogo — taocms |
Taocms v2.5Beta5 was discovered to contain a blind SQL injection vulnerability via the function Edit Article. |
2021-12-02 |
6.5 |
CVE-2021-25784
MISC |
| thinkphp-bjyblog_project — thinkphp-bjyblog |
thinkphp-bjyblog (last update Jun 4 2021) is affected by a Cross Site Scripting (XSS) vulnerability in AdminBaseController.class.php. The exit function will terminate the script and print the message to the user which has $_SERVER[‘HTTP_HOST’]. |
2021-12-02 |
4.3 |
CVE-2021-43682
MISC |
| trendmicro — antivirus |
Trend Micro Antivirus for Mac 2021 v11 (Consumer) is vulnerable to an improper access control privilege escalation vulnerability that could allow an attacker to establish a connection that could lead to full local privilege escalation within the application. Please note that an attacker must first obtain the ability to execute low-privileged code on the target system in order to exploit this vulnerability. |
2021-11-30 |
4.6 |
CVE-2021-43771
MISC
MISC |
| twmap_project — twmap |
twmap v2.91_v4.33 is affected by a Cross Site Scripting (XSS) vulnerability. In file list.php, the exit function will terminate the script and print the message to the user. The message will contain $_REQUEST then there is a XSS vulnerability. |
2021-11-29 |
4.3 |
CVE-2021-43696
MISC |
| udisks_project — udisks |
A vulnerability found in udisks2. This flaw allows an attacker to input a specially crafted image file/USB leading to kernel panic. The highest threat from this vulnerability is to system availability. |
2021-11-29 |
6.3 |
CVE-2021-3802
MISC
MISC |
| vercot — serva |
Serva 4.4.0 allows remote attackers to cause a denial of service (daemon crash) via a TFTP read (RRQ) request, aka opcode 1, a related issue to CVE-2013-0145. |
2021-11-29 |
5 |
CVE-2021-44429
MISC |
| vim — vim |
vim is vulnerable to Heap-based Buffer Overflow |
2021-12-01 |
6.8 |
CVE-2021-4019
MISC
CONFIRM
FEDORA |
| vim — vim |
vim is vulnerable to Heap-based Buffer Overflow |
2021-12-01 |
6.8 |
CVE-2021-3984
MISC
CONFIRM |
| vmware — spring_advanced_message_queuing_protocol |
In Spring AMQP versions 2.2.0 – 2.2.19 and 2.3.0 – 2.3.11, the Spring AMQP Message object, in its toString() method, will create a new String object from the message body, regardless of its size. This can cause an OOM Error with a large message |
2021-11-30 |
4 |
CVE-2021-22095
MISC |
| wipro — holmes |
Wipro Holmes Orchestrator 20.4.1 (20.4.1_02_11_2020) allows remote attackers to read application log files containing sensitive information via a predictable /log URI. |
2021-11-29 |
5 |
CVE-2021-38283
MISC
MISC |
| wipro — holmes |
Wipro Holmes Orchestrator 20.4.1 (20.4.1_02_11_2020) allows remote attackers to download arbitrary files, such as reports containing sensitive information, because authentication is not required for API access to processexecution/DownloadExcelFile/Domain_Credential_Report_Excel, processexecution/DownloadExcelFile/User_Report_Excel, processexecution/DownloadExcelFile/Process_Report_Excel, processexecution/DownloadExcelFile/Infrastructure_Report_Excel, or processexecution/DownloadExcelFile/Resolver_Report_Excel. |
2021-11-29 |
5 |
CVE-2021-38147
MISC
MISC |
| workerman-thinkphp-redis_project — workerman-thinkphp-redis |
Workerman-ThinkPHP-Redis (last update Mar 16, 2018) is affected by a Cross Site Scripting (XSS) vulnerability. In file Controller.class.php, the exit function will terminate the script and print the message to the user. The message will contain $_GET{C(‘VAR_JSONP_HANDLER’)] then there is a XSS vulnerability. |
2021-11-29 |
4.3 |
CVE-2021-43697
MISC |
| wp-events-plugin — events_manager |
The Events Manager WordPress plugin before 5.9.8 does not sanitise and escape some search parameter before outputing them in pages, which could lead to Cross-Site Scripting issues |
2021-12-01 |
4.3 |
CVE-2020-35037
CONFIRM
MISC |
| wp-events-plugin — events_manager |
The Events Manager WordPress plugin before 5.9.8 does not sanitise and escape a parameter before using it in a SQL statement, leading to an SQL Injection |
2021-12-01 |
6.5 |
CVE-2020-35012
CONFIRM
MISC |
| youtubephpmirroring_project — youtube-php-mirroring |
youtube-php-mirroring (last update Jun 9, 2017) is affected by a Cross Site Scripting (XSS) vulnerability in file ytproxy/index.php. |
2021-11-29 |
4.3 |
CVE-2021-43692
MISC |
| yurunproxy_project — yurunproxy |
YurunProxy v0.01 is affected by a Cross Site Scripting (XSS) vulnerability in src/Client.php. The exit function will terminate the script and print a message which have values from the socket_read. |
2021-12-01 |
4.3 |
CVE-2021-43690
MISC |
| zblogcn — z-blogphp |
Z-BlogPHP v1.6.1.2100 was discovered to contain an arbitrary file deletion vulnerability via app_del.php. |
2021-12-02 |
6.4 |
CVE-2020-29177
MISC |
| zerodream — sakurapanel |
SakuraPanel v1.0.1.1 is affected by a Cross Site Scripting (XSS) vulnerability in /master/core/PostHandler.php. The exit function will terminate the script and print the message $data[‘proxy_name’]. |
2021-12-02 |
4.3 |
CVE-2021-43681
MISC |
| zohocorp — manageengine_supportcenter_plus |
Zoho ManageEngine SupportCenter Plus before 11016 is vulnerable to an SSRF attack in ActionExecutor. |
2021-11-30 |
5 |
CVE-2021-43296
MISC
CONFIRM |
| zohocorp — manageengine_supportcenter_plus |
Zoho ManageEngine SupportCenter Plus before 11016 is vulnerable to Reflected XSS in the Products module. |
2021-11-30 |
4.3 |
CVE-2021-43294
MISC
CONFIRM |
| zohocorp — manageengine_supportcenter_plus |
Zoho ManageEngine SupportCenter Plus before 11016 is vulnerable to Reflected XSS in the Accounts module. |
2021-11-30 |
4.3 |
CVE-2021-43295
MISC
MISC |
| zrlog — zrlog |
ZrLog 2.2.2 has a remote command execution vulnerability at plugin download function, it could execute any JAR file |
2021-11-28 |
6.8 |
CVE-2021-44094
MISC |
| zulip — zulip |
Zulip is an open source group chat application that combines real-time chat with threaded conversations. In affected versions expiration dates on the confirmation objects associated with email invitations were not enforced properly in the new account registration flow. A confirmation link takes a user to the check_prereg_key_and_redirect endpoint, before getting redirected to POST to /accounts/register/. The problem was that validation was happening in the check_prereg_key_and_redirect part and not in /accounts/register/ – meaning that one could submit an expired confirmation key and be able to register. The issue is fixed in Zulip 4.8. There are no known workarounds and users are advised to upgrade as soon as possible. |
2021-12-02 |
5 |
CVE-2021-43791
CONFIRM
MISC |
by Contributed | Dec 4, 2021 | Technology
This article is contributed. See the original author and article here.
Before implementing data extraction from SAP systems please always verify your licensing agreement. |
I hope you all enjoyed the summer with OData-based extraction and Synapse Pipelines. Time flies quickly, and we’re now in the fourth episode of this mini-blog series. You’ve learnt quite a lot! Initially, we built a simple pipeline with a single activity to copy data from the SAP system to data lake storage. But that solution evolved quickly, and now it supports storing metadata in an external store that decouples the management of OData services and pipelines. To extract data from a new service, you can just enter its name to the Azure Table Storage. You don’t have to make any changes in Synapse!
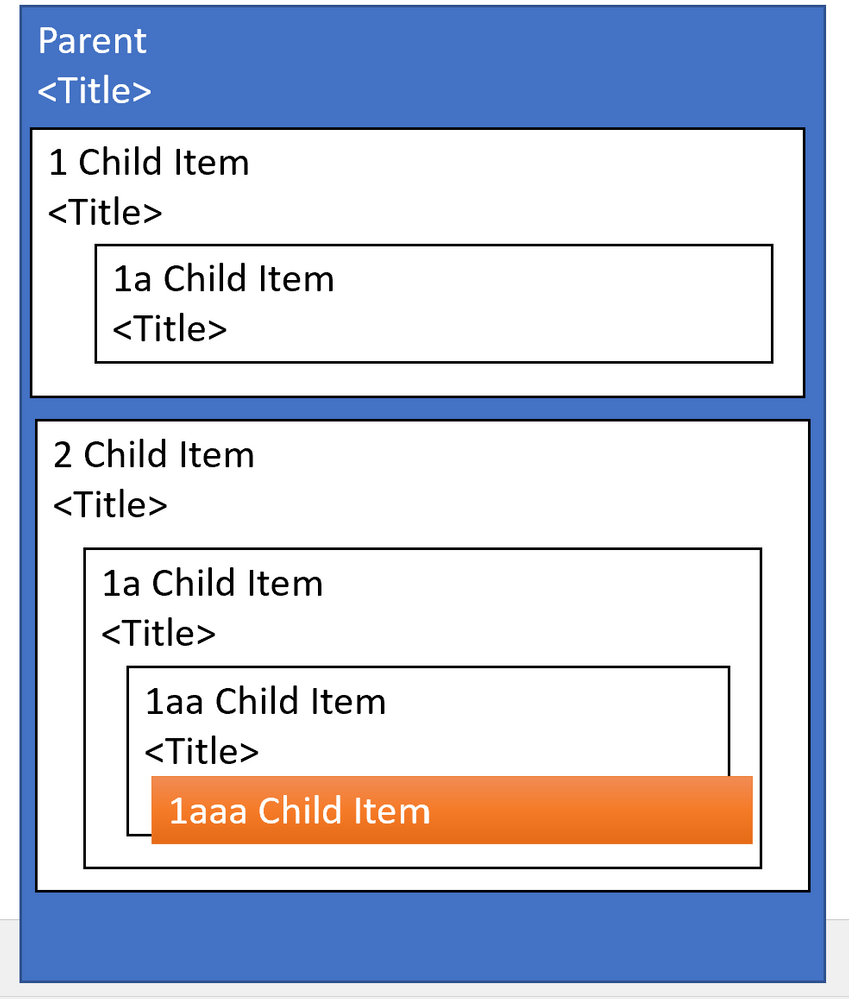
Today we continue our journey, and we’ll focus on optimizing the extraction performance of large datasets. When I first started working with OData-based extraction, it caused me a lot of challenges – have you ever tried to generate an OData payload for more than a million records? I can’t assure you – most of the time, it doesn’t end well!
But even if we forget about string size limitations, working with huge HTTP payloads causes problems in data transmission and processing. How should we then approach the data extraction from large OData sources?
CLIENT-SIDE PAGING
The solution to the above problem is pretty straightforward. If working with a large amount of data is causing us an issue, let’s split the dataset into a couple of smaller chunks. Then extract and process each part separately. You can even run each thread in parallel, improving the overall performance of the job.
There is a couple of ways how you can split the dataset. Firstly, the most obvious is to use business logic to provide rules. Using the Sales Orders as an example, we could chunk it into smaller pieces using the following keys:
- SalesOrganization
- SalesOrderType
- SoldToPary
Those are not the only business-related keys you can use to create partitions in your data. It’s a reliable approach, but it requires a lot of preparation and data discovery work. Fortunately, there is another solution.
When working with OData services, you can manipulate the amount of data to fetch within a single request using the $top query parameter. When you pass $top=25 you will only receive only 25 records in the response. But that’s not the end! We can also use the $skip parameter that indicates the first record to fetch. So, to process 15 records, you can send a single request, or we can chunk it into smaller pieces using the combination of $skip and $top parameters.

As sending a single request asking for large amounts of data is not the best approach, a similar danger comes from flooding the SAP system with a large number of tiny calls. Finding the right balance is the key!
The above approach is called Client-Side Paging. We will use the logic inside Synapse Pipeline to split the dataset into manageable pieces and then extract each of them. To implement it in the pipeline, we need three numbers:
- The number of records in the OData service
- Amount of data to fetch in a single request (batch size)
- Number of requests
Getting the number of records in the OData service is simple. You can use the $count option passed at the end of the URL. By dividing it by the batch size, which we define for each OData service and store in the metadata table, we can calculate the number of requests required to fetch the complete dataset.
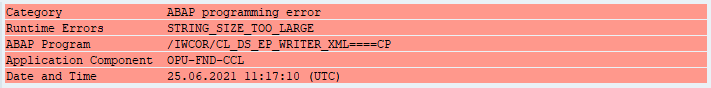
Open the Storage Explorer to alter the metadata table and add a new Batch property:
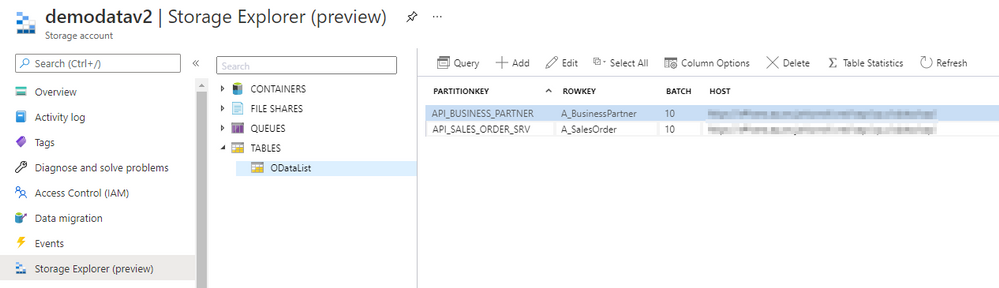
Now go to Synapse Studio and open the child pipeline. Add a new parameter to store the Batch size:
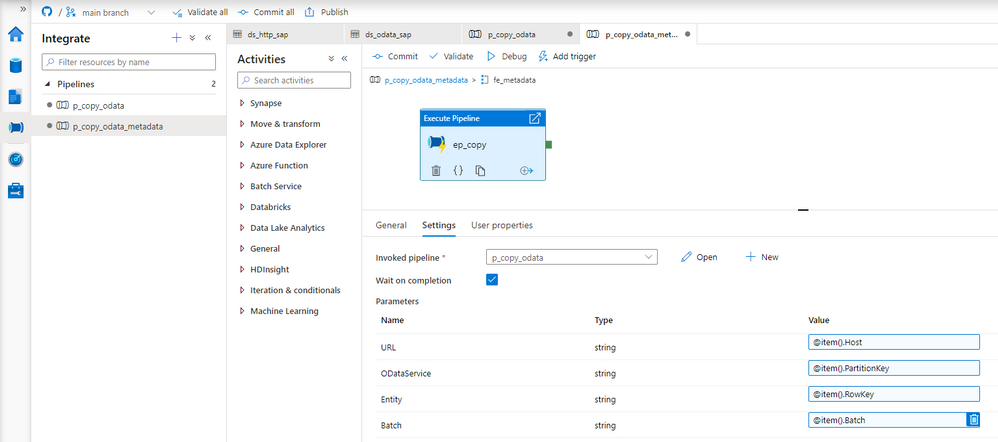
In the metadata pipeline, open the Execute Pipeline activity. The following expression will pass the batch size value from the metadata table. You don’t have to make any changes to the Lookup.
@item().Batch
There is a couple of ways to read the record count. Initially, I wanted to use the Lookup activity against the dataset that we already have. But, as the result of a $count is just a number without any data structure, the OData connector fails to interpret the value. Instead, we have to create another Linked Service and a dataset of type HTTP. It should point to the same OData Service as the Copy Data activity.
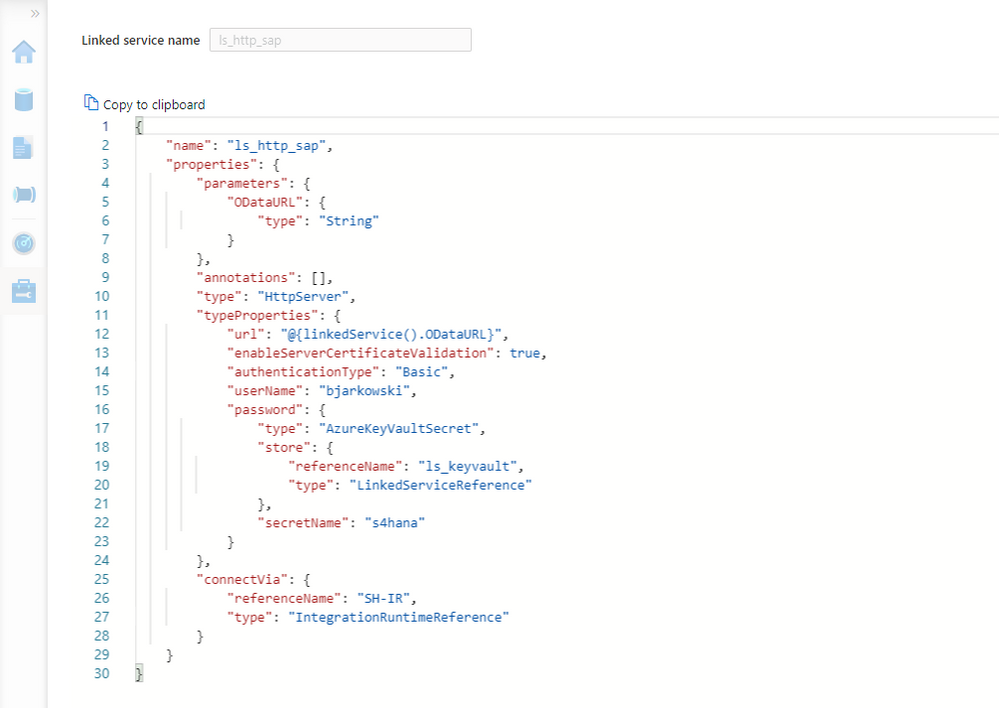
Create the new Linked Service of type HTTP. It should accept the same parameters as the OData one. Refer to the second episode of the blog series if you’d like to refresh your memory on how to add parameters to linked services.
{
"name": "ls_http_sap",
"properties": {
"parameters": {
"ODataURL": {
"type": "String"
}
},
"annotations": [],
"type": "HttpServer",
"typeProperties": {
"url": "@{linkedService().ODataURL}",
"enableServerCertificateValidation": true,
"authenticationType": "Basic",
"userName": "bjarkowski",
"password": {
"type": "AzureKeyVaultSecret",
"store": {
"referenceName": "ls_keyvault",
"type": "LinkedServiceReference"
},
"secretName": "s4hana"
}
},
"connectVia": {
"referenceName": "SH-IR",
"type": "IntegrationRuntimeReference"
}
}
}
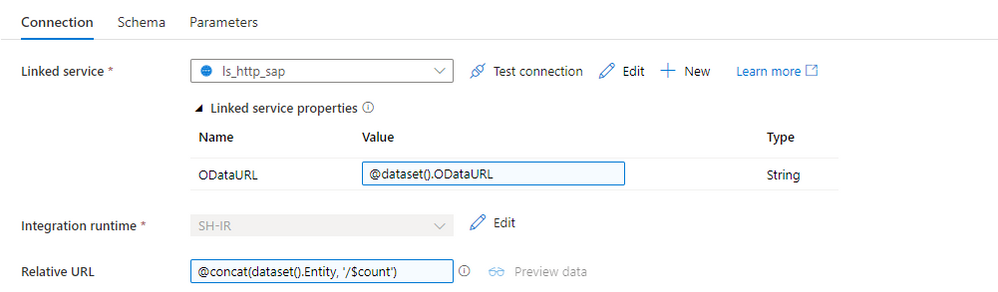
Now, let’s create the dataset. Choose HTTP as the type and DelimitedText as the file format. Add ODataURL and Entity parameters as we did for the OData dataset. On the Settings tab, you’ll find the field Relative URL, which is the equivalent of the Path from the OData-based dataset. To get the number of records, we have to concatenate the entity name with the $count. The expression should look as follows:
@concat(dataset().Entity, '/$count')
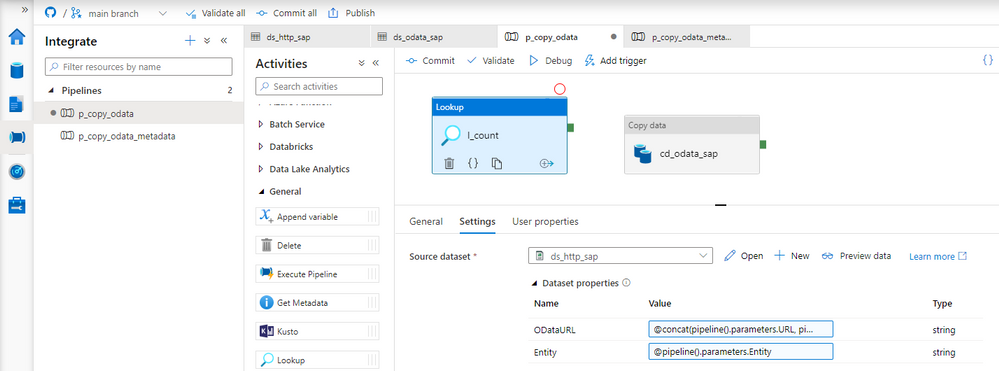
Perfect! We can now update the child pipeline that processes each OData service. Add the Lookup activity, but don’t create any connection. Both parameters on the Settings tab should have the same expression as the Copy Data activity. There is one difference. It seems there is a small bug and the URL in the Lookup activity has to end with a slash ‘/’ sign. Otherwise, the last part of the address may be removed, and the request may fail.
ODataURL: @concat(pipeline().parameters.URL, pipeline().parameters.ODataService, '/')
Entity: @pipeline().parameters.Entity
Difficult moment ahead of us! I’ll try to explain all the details the best I can. When the Lookup activity checks the number of records in the OData service, the response contains just a single value. We will use the $skip and $top query parameters to chunk the request into smaller pieces. The tricky part is how to model it in the pipeline. As always, there is no single solution. The easiest approach is to use the Until loop, which could check the number of processed rows at every iteration. But it only allows sequential processing, and I want to show you a more robust way of extracting data.
The ForEach loop offers parallel execution, but it only accepts an array as the input. We have to find a way on how to create one. The @range() expression can build an array of consecutive numbers. It accepts two parameters – the starting position and the length, which in our case will translate to the number of requests. Knowing the number of records and the batch size, we can easily calculate the array length. Assuming the OData service contains 15 elements and the batch size equals 5, we could pass the following parameters to the @range() function:
@range(0,3)
As the outcome we receive:
[0,1,2]
Each value in the array represents the request number. Using it, we can easily calculate the $skip parameter.
But there is one extra challenge. What if the number of records cannot be divided by the batch size without a remainder? As there is no rounding function, the decimal part of the result will be omitted, which means we’re losing the last chunk of data. To avoid that, I implemented a simple workaround – I always add 1 to the number of requests. Of course, you could think about a fancy solution using the modulo function, but I’m a big fan of simplicity. And asking for more data won’t hurt.
Add the ForEach loop as the successor of the Lookup activity. In the Items field, provide the following expression to create an array of requests. I’m using the int() function to cast the string value to the integer that I can then use in the div().
@range(0, add(div(int(activity('l_count').output.firstRow.Prop_0), int(pipeline().parameters.Batch)),1))
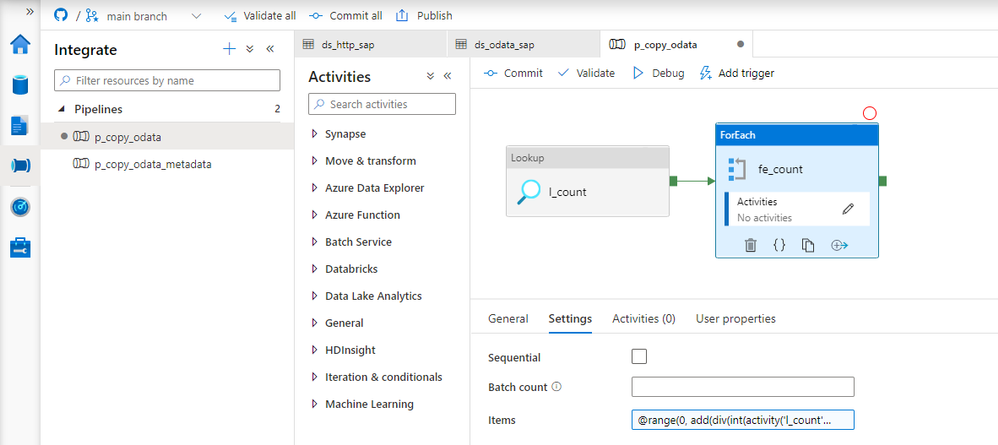
To send multiple requests to the data source, move the Copy Data activity to the ForEach loop. Every iteration will trigger a copy job – but we have to correctly maintain query parameters to receive just one chunk of data. To achieve it, we will use the $top and $skip parameters, as I mentioned earlier in the post.
The $top parameter is static and always equals the batch size. To calculate the $skip parameter, we will use the request number from the array passed to the loop multiplied by the batch size.
Open the Copy Data activity and go to the Settings tab. Change the field Use Query to Query and provide the following expression:
@concat('$top=',pipeline().parameters.Batch, '&$skip=',string(mul(int(item().value), int(pipeline().parameters.Batch))))
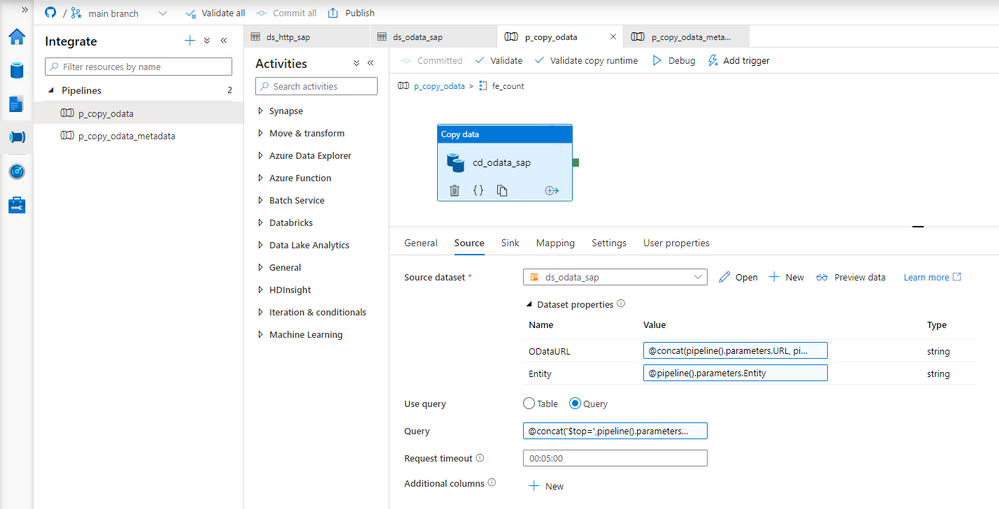
That was the last change to make. Let’s start the pipeline!
EXECUTION AND MONITORING
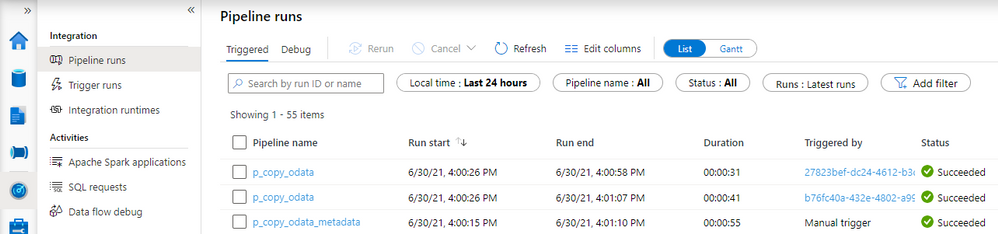
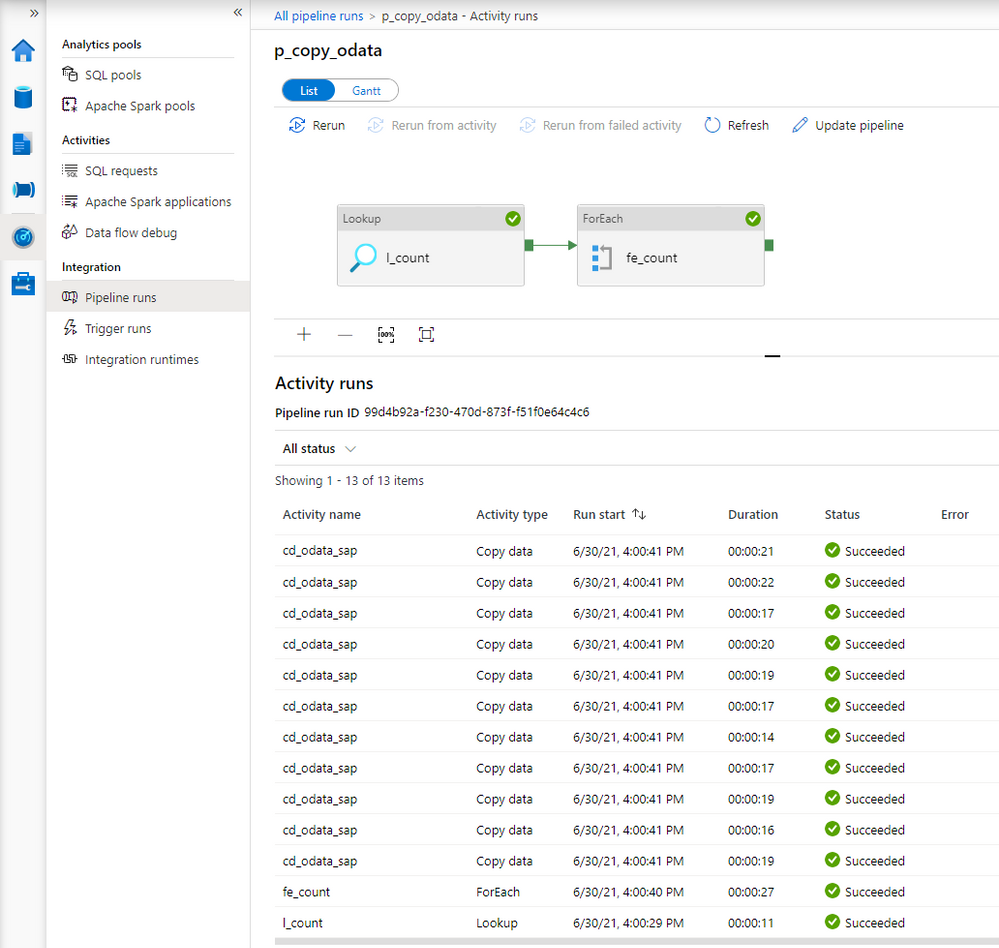
Once the pipeline processing finishes we can see successfully completed jobs in the monitoring view. Let’s drill down to see the details.
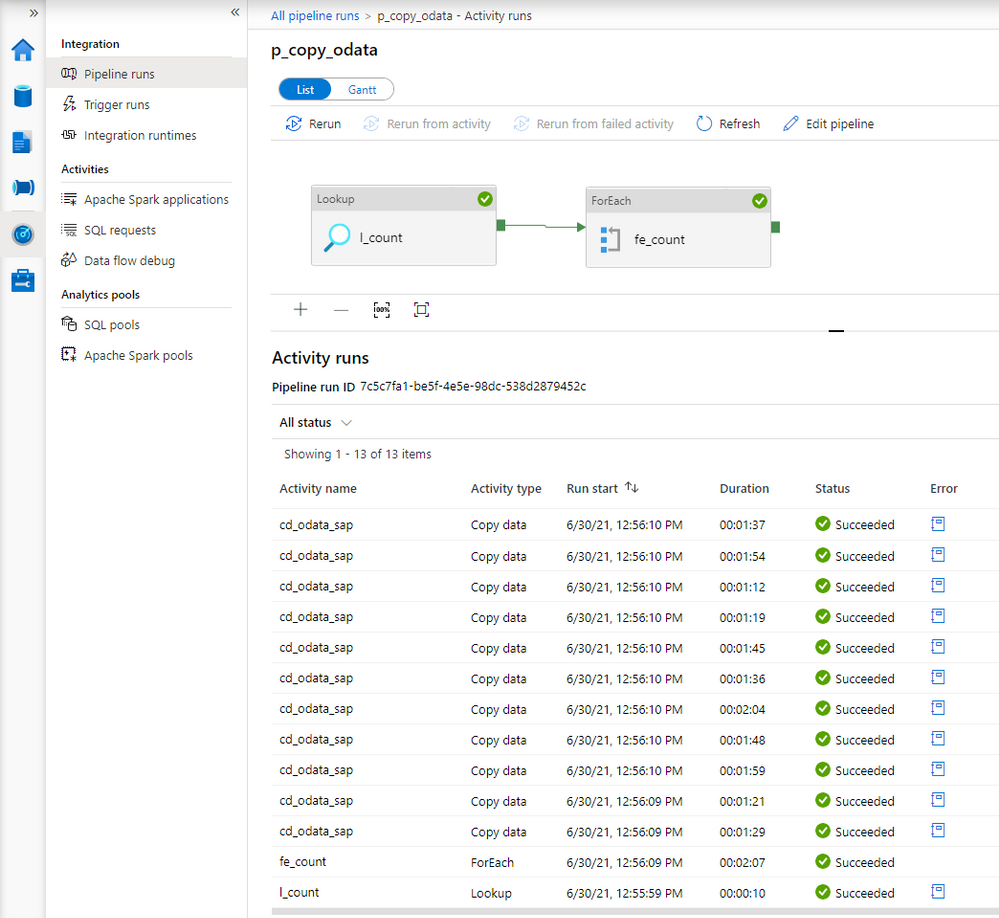
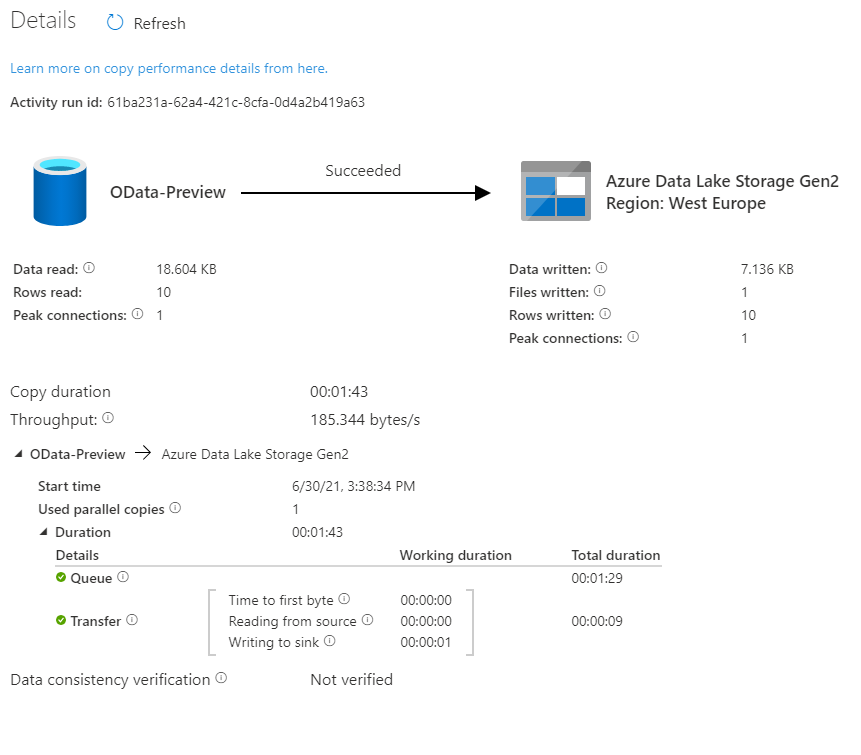
Comparing to the previous extraction, you can see the difference. Instead of just one, there are now multiple entries for the Copy Data activity. You may be slightly disappointed with the duration of each copy job. It takes much longer to extract every chunk of data – in the previous episode, it took only 36 seconds to extract all sales orders. This time every activity took at least a minute.
There is a couple of reasons why it happens. Let’s take a closer a closer look at the components of the extraction job to understand why the duration increased heavily.
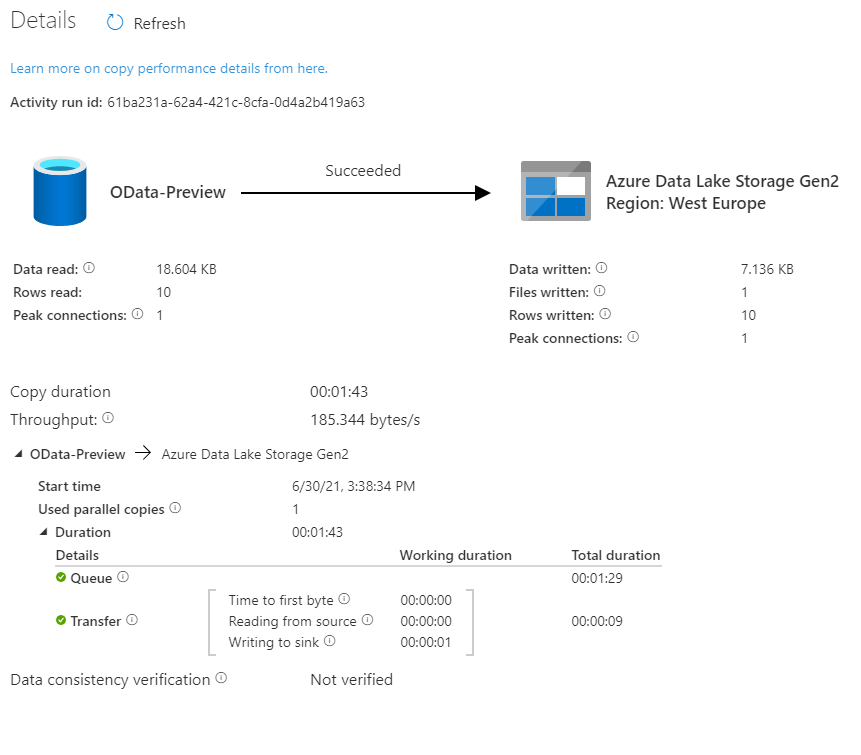
Look at the time analysis. Before the request was processed, it was in the Queue for 1 minute and 29 seconds. Extracting data took only 9 seconds. Why there is such a long wait time?
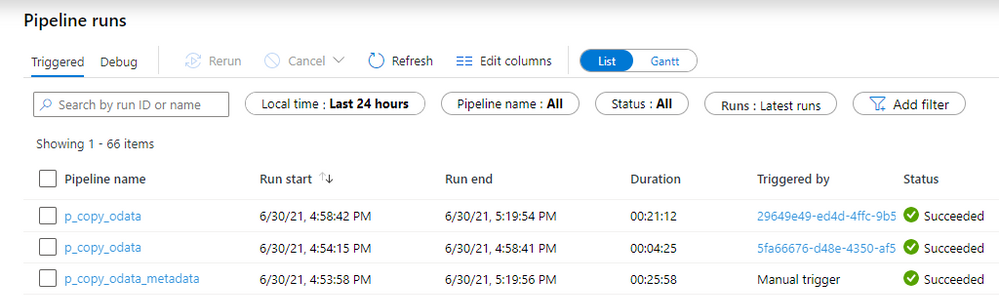
In the first episode of the blog series, I briefly explained the role of the integration runtime. It provides the computing resources for pipeline execution. To save cost, I host my integration runtime on a very tiny B2ms virtual machine. It provides enough power to process two or three activities at the same time, which means that extracting many chunks is rather sequential than parallel. To fix that, I’ve upgraded my virtual machine to a bigger one. The total duration to extract data decreased significantly as I could process more chunks at the same time.
Here is the duration of each Copy Data activity.
The request is in the queue only for a couple of seconds instead of over a minute.
Before we finish, I want to show you some results of processing a large dataset. In another system, I have over 1 million sales orders with more than 5 million line items. It wasn’t possible to extract it all in a single request as every attempt resulted in a short dump at the SAP side. I’ve adjusted the batch size to 100 000 which should be alright to process at a time. To further optimize the extraction, I changed the processing of OData services to Sequential, which means the job firstly extracts Sales Order headers before moving to line items. You can do it in the ForEach Loop in the metadata pipeline. To limit the impact of extraction to the SAP system, I also set a concurrency limit for the Copy Data activity (ForEach loop in the child pipeline).
It took 25 minutes to extract in total over 6 million records. Not bad.
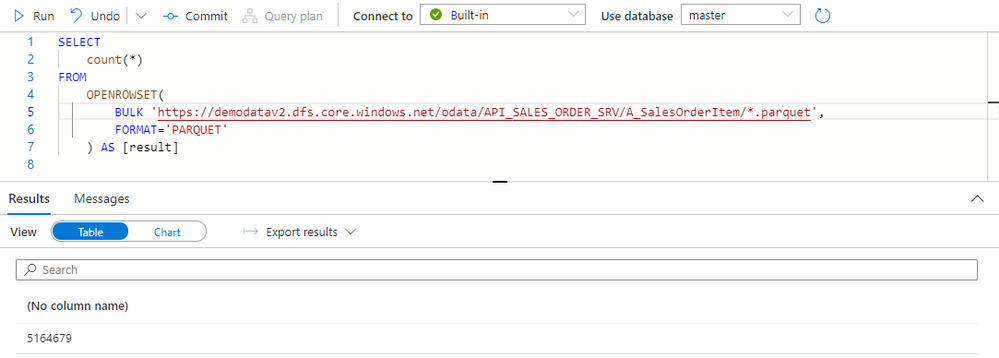
The extraction generated quite a lot of files on the data lake. Let’s count all records inside them and compare the number with what I have in my SAP system:
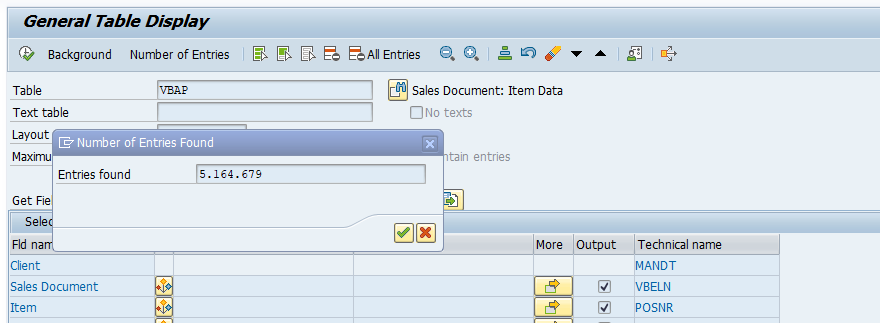
Both numbers match, which means we have the full dataset in the data lake. We could probably further optimize the extraction duration by finding the right number of parallel processes and identifying the best batch size.
Finally, before you even start the extraction, I recommend checking if you need all data. Trimming the dataset by setting filters on columns or extracting only a subset of columns can heavily improve the extraction duration. That’s something we’ll cover in the next episode!
by Contributed | Dec 3, 2021 | Technology
This article is contributed. See the original author and article here.
Overview
Many FHIR include complex nesting. For example the Item component of Questionnaire can either be a single item or an array of more items, which can themselves also be arrays of more items, with even more arrays below. Arrays all the way down! A previous post (FHIR + Blazor + Recursion = Rendering a Questionnaire ) showed a method to render objects with complex nesting: using Dynamic Fragments. This article shows an alternative method: using self-referential components.
Why use components?
Components will allow easier reuse than Dynamic Fragment rendered pages. Imagine a case where we want to both create new and allow updates of complex nested children. If we use components, we can easily adapt a component for both EDIT and CREATE. More reuse means less code!
How it’ll work
We’ll create a parent component. The parent component will render the child component.
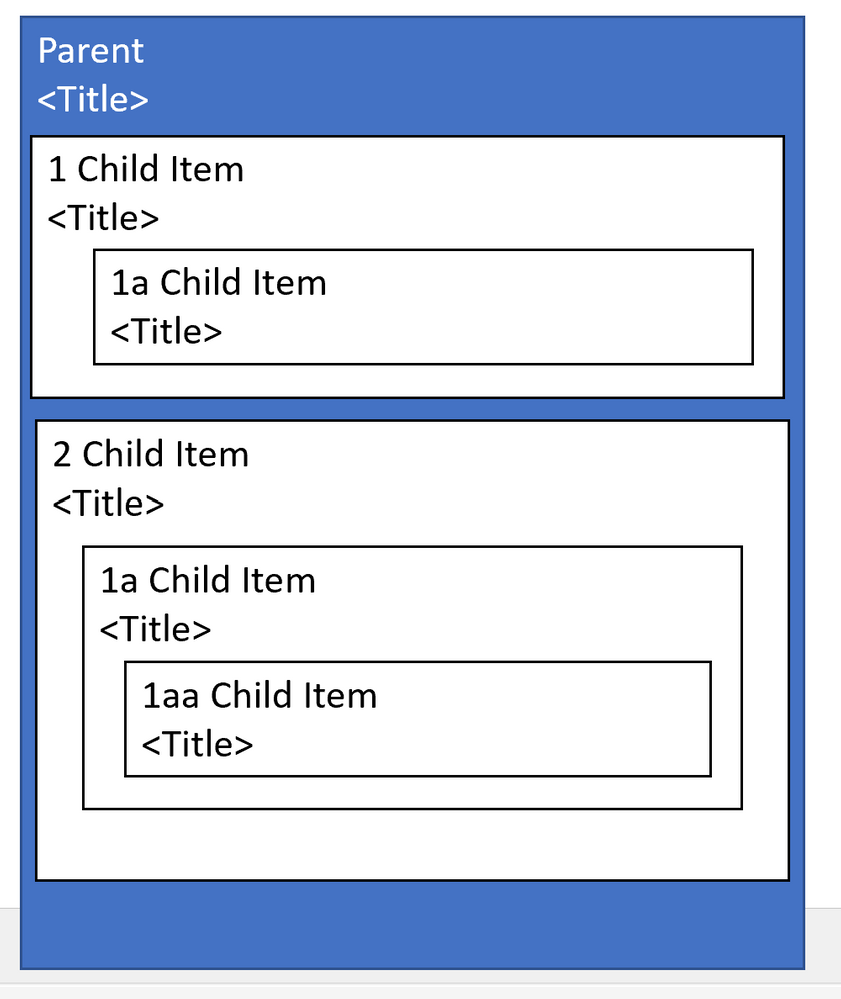
Parent Component;
<span>@Parent.Title</span>
<p>@Parent.Description</p>
@{
int childNum=1;
}
@foreach(var child in Parent.children){
Child #@childNum
ChildComponent child=child />
childNum++;
}
AND HERE’s THE MAGIC:
Child Component:
<span>@Child.Title</span>
@foreach(var child in Child.children){
<ChildComponent child=child />
}
The child component will render additional child components.
FHIR Specific Example
Check out the code below from (FHIRBlaze)
Parent Component (QuestionnaireComponent)
<EditForm Model=Questionnaire OnValidSubmit=Submit>
<label class="col-sm-2 form-label">Title:</label>
<InputText @bind-Value=Questionnaire.Title />
@foreach(var item in Questionnaire.Item)
{
<div class="border border-primary rounded-left rounded-right p-2">
<div class="row">
<div class="col-sm-12">@GetHeader(item)</div>
</div>
<div class="row">
<div class="col-sm-11">
<ItemDisplay ItemComponent=item/>
</div>
<div class="col-sm-1">
<button type="button" class="btn btn-primary" @onclick="()=>RemoveItem(item)">
<span class="oi oi-trash" />
</button>
</div>
</div>
</div>
}
<div>
<ItemTypeComponent ItemSelected="AddItem" />
</div>
<br/>
<button type="submit">Submit</button>
</EditForm>
Note the ItemDisplay component.
Child Component ( ItemDisplay )
<div class="card-body">
<label class="sr-only" >@GetTitleText(ItemComponent)</label>
<input type='text' required class='form-control' id='question' placeholder=@GetTitleText(ItemComponent) @bind-value='ItemComponent.Text' >
<label class="sr-only">LinkId:</label>
<input type='text' required class='form-control' placeholder='linkId' @bind-value='ItemComponent.LinkId'>
@switch (ItemComponent.Type)
{
case Questionnaire.QuestionnaireItemType.Group:
foreach(var groupitem in ItemComponent.Item)
{
<div class="border border-primary rounded-left rounded-right p-2">
<div class="row">
<div class="col-sm">@GetHeader(groupitem)</div>
</div>
<div class="row">
<div class="col-sm-11">
<ItemDisplay ItemComponent=groupitem/>
</div>
<div class="col-sm">
<button type="button" class="btn btn-primary" @onclick="()=>ItemComponent.Item.Remove(groupitem)">
<span class="oi oi-trash" />
</button>
</div>
</div>
</div>
}
break;
case Questionnaire.QuestionnaireItemType.Choice:
int ansnum= 1;
@foreach (var opt in ItemComponent.AnswerOption)
{
<div class="row">
<form class="form-inline">
<div class="col-sm-1">#@ansnum</div>
<div class="col-sm-10"><AnswerCoding Coding=(Coding)opt.Value /></div>
<div class="col-sm-1"><button type="button" class="btn btn-primary" @onclick="()=>ItemComponent.AnswerOption.Remove(opt)"><span class="oi oi-trash" /></button></div>
</form>
</div>
ansnum++;
}
<button type="button" @onclick=AddAnswer >Add Choice</button>
break;
default:
break;
}
@if (ItemComponent.Type.Equals(Questionnaire.QuestionnaireItemType.Group))
{
<div>
<ItemTypeComponent ItemSelected="AddItem" />
</div>
}
</div>
Line 58 is the key line. This component renders itself!
Caveats
With this you should be able to quickly render nested Item after nested Item. But there are some caveats you should know.
#1: Memory Consumption
As you render each nesting- all those objects are loaded into memory. If a FHIR has an unknown number of children- each of which could have its own children, you could potentially consume large amounts of memory. This is a particular problem because you could be rendering on a phone.
Suggested Mitigation: Consider rendering to a max depth and a max number of children. Render “see more” type links to allow the user to see remaining children
#2: Display Clipping
The standard approach is to indent children. But if you have 5 levels of nesting and the app is rendered on mobile than your 5th level children may show up in a single character column. If you render 100 levels of nested children, your final level may not render at all.
Suggested Mitigation: Consider an alternative to displaying all children. For example- consider using collapsible sections to show children.
#3: Labeling Problems
If you’re allowing Edit of a component with complex nesting it may be difficult for a user to remember which level of children, they are in. For example, imagine the following are rendered as cards: Parent 1: Child 1: Child 2: Child 3: Child 4: Child 5.
Suggested Mitigation: Consider using borders and labeling to help users determine which child is currently selected
by Scott Muniz | Dec 2, 2021 | Security, Technology
This article is contributed. See the original author and article here.
Summary
This joint Cybersecurity Advisory uses the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK®) framework, Version 9. See the ATT&CK for Enterprise framework for referenced threat actor techniques and for mitigations.
This joint advisory is the result of analytic efforts between the Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) to highlight the cyber threat associated with active exploitation of a newly identified vulnerability (CVE-2021-44077) in Zoho ManageEngine ServiceDesk Plus—IT help desk software with asset management.
CVE-2021-44077, which Zoho rated critical, is an unauthenticated remote code execution (RCE) vulnerability affecting all ServiceDesk Plus versions up to, and including, version 11305. This vulnerability was addressed by the update released by Zoho on September 16, 2021 for ServiceDesk Plus versions 11306 and above. The FBI and CISA assess that advanced persistent threat (APT) cyber actors are among those exploiting the vulnerability. Successful exploitation of the vulnerability allows an attacker to upload executable files and place webshells, which enable the adversary to conduct post-exploitation activities, such as compromising administrator credentials, conducting lateral movement, and exfiltrating registry hives and Active Directory files.
The Zoho update that patched this vulnerability was released on September 16, 2021, along with a security advisory. Additionally, an email advisory was sent to all ServiceDesk Plus customers with additional information. Zoho released a subsequent security advisory on November 22, 2021, and advised customers to patch immediately.
The FBI and CISA are aware of reports of malicious cyber actors likely using exploits against CVE-2021-44077 to gain access [T1190] to ManageEngine ServiceDesk Plus, as early as late October 2021. The actors have been observed using various tactics, techniques and procedures (TTPs), including:
- Writing webshells [T1505.003] to disk for initial persistence
- Obfuscating and Deobfuscating/Decoding Files or Information [T1027 and T1140]
- Conducting further operations to dump user credentials [T1003]
- Living off the land by only using signed Windows binaries for follow-on actions [T1218]
- Adding/deleting user accounts as needed [T1136]
- Stealing copies of the Active Directory database (
NTDS.dit) [T1003.003] or registry hives
- Using Windows Management Instrumentation (WMI) for remote execution [T1047]
- Deleting files to remove indicators from the host [T1070.004]
- Discovering domain accounts with the net Windows command [T1087.002]
- Using Windows utilities to collect and archive files for exfiltration [T1560.001]
- Using custom symmetric encryption for command and control (C2) [T1573.001]
The FBI and CISA are proactively investigating this malicious cyber activity:
- The FBI leverages specially trained cyber squads in each of its 56 field offices and CyWatch, the FBI’s 24/7 operations center and watch floor, which provides around-the-clock support to track incidents and communicate with field offices across the country and partner agencies.
- CISA offers a range of no-cost cyber hygiene services to help organizations assess, identify, and reduce their exposure to threats. By requesting these services, organizations of any size could find ways to reduce their risk and mitigate attack vectors.
Sharing technical and/or qualitative information with the FBI and CISA helps empower and amplify our capabilities as federal partners to collect and share intelligence and engage with victims, while working to unmask and hold accountable those conducting malicious cyber activities.
A STIX file will be provided when available.
For a downloadable pdf of this CSA, click here.
Technical Details
Compromise of the affected systems involves exploitation of CVE-2021-44077 in ServiceDesk Plus, allowing the attacker to:
- Achieve an unrestricted file upload through a POST request to the ServiceDesk REST API URL and upload an executable file,
C:ManageEngineServicedeskbinmsiexec.exe, with a SHA256 hash of ecd8c9967b0127a12d6db61964a82970ee5d38f82618d5db4d8eddbb3b5726b7. This executable file serves as a dropper and contains an embedded, encoded Godzilla JAR file.
- Gain execution for the dropper through a second POST request to a different REST API URL, which will then decode the embedded Godzilla JAR file and drop it to the filepath
C:ManageEngineServiceDesklibtomcattomcat-postgres.jar with a SHA256 hash of 67ee552d7c1d46885b91628c603f24b66a9755858e098748f7e7862a71baa015.
Confirming a successful compromise of ManageEngine ServiceDesk Plus may be difficult—the attackers are known to run clean-up scripts designed to remove traces of the initial point of compromise and hide any relationship between exploitation of the vulnerability and the webshell.
Targeted Industries
APT cyber actors have targeted Critical Infrastructure Sector industries, including the healthcare, financial services, electronics and IT consulting industries.
Indicators of Compromise
Hashes
Webshell:
67ee552d7c1d46885b91628c603f24b66a9755858e098748f7e7862a71baa015
068D1B3813489E41116867729504C40019FF2B1FE32AAB4716D429780E666324
759bd8bd7a71a903a26ac8d5914e5b0093b96de61bf5085592be6cc96880e088
262cf67af22d37b5af2dc71d07a00ef02dc74f71380c72875ae1b29a3a5aa23d
a44a5e8e65266611d5845d88b43c9e4a9d84fe074fd18f48b50fb837fa6e429d
ce310ab611895db1767877bd1f635ee3c4350d6e17ea28f8d100313f62b87382
75574959bbdad4b4ac7b16906cd8f1fd855d2a7df8e63905ab18540e2d6f1600
5475aec3b9837b514367c89d8362a9d524bfa02e75b85b401025588839a40bcb
Dropper:
ecd8c9967b0127a12d6db61964a82970ee5d38f82618d5db4d8eddbb3b5726b7
Implant:
009d23d85c1933715c3edcccb46438690a66eebbcccb690a7b27c9483ad9d0ac
083bdabbb87f01477f9cf61e78d19123b8099d04c93ef7ad4beb19f4a228589a
342e85a97212bb833803e06621170c67f6620f08cc220cf2d8d44dff7f4b1fa3
NGLite Backdoor:
805b92787ca7833eef5e61e2df1310e4b6544955e812e60b5f834f904623fd9f
3da8d1bfb8192f43cf5d9247035aa4445381d2d26bed981662e3db34824c71fd
5b8c307c424e777972c0fa1322844d4d04e9eb200fe9532644888c4b6386d755
3f868ac52916ebb6f6186ac20b20903f63bc8e9c460e2418f2b032a207d8f21d
342a6d21984559accbc54077db2abf61fd9c3939a4b09705f736231cbc7836ae
7e4038e18b5104683d2a33650d8c02a6a89badf30ca9174576bf0aff08c03e72
KDC Sponge:
3c90df0e02cc9b1cf1a86f9d7e6f777366c5748bd3cf4070b49460b48b4d4090
b4162f039172dcb85ca4b85c99dd77beb70743ffd2e6f9e0ba78531945577665
e391c2d3e8e4860e061f69b894cf2b1ba578a3e91de610410e7e9fa87c07304c
Malicious IIS Module:
bec067a0601a978229d291c82c35a41cd48c6fca1a3c650056521b01d15a72da
Renamed WinRAR:
d0c3d7003b7f5b4a3bd74a41709cfecfabea1f94b47e1162142de76aa7a063c7
Renamed csvde:
7d2780cd9acc516b6817e9a51b8e2889f2dec455295ac6e6d65a6191abadebff
Network Indicators
POST requests sent to the following URLs:
/RestAPI/ImportTechnicians?step=1
Domains:
seed.nkn[.]org
Note: the domain seed.nkn[.]org is a New Kind of Network (NKN) domain that provides legitimate peer to peer networking services utilizing blockchain technology for decentralization. It is possible to have false positive hits in a corporate network environment and it should be considered suspicious to see any software-initiated contacts to this domain or any subdomain.
Log File Analysis
- Check serverOut*.txt log files under C:ManageEngineServiceDesklogs for suspicious log entries matching the following format:
[<time>]|[<date>]|[com.adventnet.servicedesk.setup.action.ImportTechniciansAction]|[INFO]|[62]: fileName is : msiexec.exe]
Filepaths
C:ManageEngineServiceDeskbinmsiexec.exe
C:ManageEngineServiceDesklibtomcattomcat-postgres.jar
C:WindowsTempScriptModule.dll
C:ManageEngineServiceDeskbinScriptModule.dll
C:Windowssystem32ME_ADAudit.exe
c:Users[username]AppDataRoamingADManagerME_ADManager.exe
%ALLUSERPROFILE%MicrosoftWindowsCachessystem.dat
C:ProgramDataMicrosoftCryptoRSAkey.dat
c:windowstempccc.exe
Tactics, Techniques, and Procedures
- Using WMI for lateral movement and remote code execution (in particular,
wmic.exe)
- Using plaintext credentials for lateral movement
- Using
pg_dump.exe to dump ManageEngine databases
- Dumping
NTDS.dit and SECURITY/SYSTEM/NTUSER registry hives
- Active credential harvesting through
LSASS (KDC Sponge)
- Exfiltrating through webshells
- Conducting exploitation activity often through other compromised U.S. infrastructure
- Dropping multiple webshells and/or implants to maintain persistence
- Using renamed versions of
WinRAR, csvde, and other legitimate third-party tools for reconnaissance and exfiltration
Yara Rules
rule ReportGenerate_jsp {
strings:
$s1 = “decrypt(fpath)”
$s2 = “decrypt(fcontext)”
$s3 = “decrypt(commandEnc)”
$s4 = “upload failed!”
$s5 = “sevck”
$s6 = “newid”
condition:
filesize < 15KB and 4 of them
}
rule EncryptJSP {
strings:
$s1 = “AEScrypt”
$s2 = “AES/CBC/PKCS5Padding”
$s3 = “SecretKeySpec”
$s4 = “FileOutputStream”
$s5 = “getParameter”
$s6 = “new ProcessBuilder”
$s7 = “new BufferedReader”
$s8 = “readLine()”
condition:
filesize < 15KB and 6 of them
}
rule ZimbraImplant {
strings:
$u1 = “User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36”
$u2 = “Content-Type: application/soap+xml; charset=UTF-8”
$u3 = “/service/soap”
$u4 = “Good Luck :::)”
$s1 = “zimBR”
$s2 = “log10”
$s3 = “mymain”
$s4 = “urn:zimbraAccount”
$s5 = “/service/upload?fmt=extended,raw”
$s6 = “<query>(in:”inbox” or in:”junk”) is:unread</query>”
condition:
(uint16(0) == 0x5A4D and uint32(uint32(0x3C)) == 0x00004550) and filesize < 2MB and 1 of ($u*) and 3 of ($s*)
}
rule GodzillaDropper {
strings:
$s1 = “UEsDBAoAAAAAAI8UXFM” // base64 encoded PK/ZIP header
$s2 = “../lib/tomcat/tomcat-postgres.jar”
$s3 = “RunAsManager.exe”
$s4 = “ServiceDesk”
$s5 = “C:Userspwndocumentsvisual studio 2015Projectspayloaddll”
$s6 = “CreateMutexA”
$s7 = “cplusplus_me”
condition:
(uint16(0) == 0x5A4D and uint32(uint32(0x3C)) == 0x00004550) and filesize < 350KB and 4 of them
}
rule GodzillaJAR {
strings:
$s1 = “org/apache/tomcat/SSLFilter.class”
$s2 = “META-INF/services/javax.servlet.ServletContainerInitializer”
$s3 = “org/apache/tomcat/MainFilterInitializer.class”
condition:
uint32(0) == 0x04034B50 and filesize < 50KB and all of them
}
rule APT_NGLite {
strings:
$s1 = “/mnt/hgfs/CrossC2-2.2”
$s2 = “WHATswrongwithU”
$s3 = “//seed.nkn.org:”
$s4 = “Preylistener”
$s5 = “preyid”
$s6 = “Www-Authenticate”
condition:
(uint16(0) == 0x5A4D and uint32(uint32(0x3C)) == 0x00004550) and filesize < 15MB and 4 of them
}
rule KDCSponge {
strings:
$k1 = “kdcsvc.dll”
$k2 = “kdccli.dll”
$k3 = “kdcsvs.dll”
$f1 = “KerbHashPasswordEx3”
$f2 = “KerbFreeKey”
$f3 = “KdcVerifyEncryptedTimeStamp”
$s1 = “download//symbols//%S//%S//%S” wide
$s2 = “KDC Service”
$s3 = “system.dat”
condition:
(uint16(0) == 0x5A4D and uint32(uint32(0x3C)) == 0x00004550) and filesize < 1MB and 1 of ($k*) and 1 of ($f*) and 1 of ($s*)
Mitigations
Compromise Mitigations
Organizations that identify any activity related to ManageEngine ServiceDesk Plus indicators of compromise within their networks should take action immediately.
Zoho ManageEngine ServiceDesk Plus build 11306, or higher, fixes CVE-2021-44077. ManageEngine initially released a patch for this vulnerability on September 16, 2021. A subsequent security advisory was released on November 22, 2021, and advised customers to patch immediately. Additional information can be found in the Zoho security advisory released on November 22, 2021.
In addition, Zoho has set up a security response plan center that provides additional details, a downloadable tool that can be run on potentially affected systems, and a remediation guide.
FBI and CISA also strongly recommend domain-wide password resets and double Kerberos TGT password resets if any indication is found that the NTDS.dit file was compromised.
Note: Implementing these password resets should not be taken as a comprehensive mitigation in response to this threat; additional steps may be necessary to regain administrative control of your network. Refer to your specific products mitigation guidance for details.
Actions for Affected Organizations
Immediately report as an incident to CISA or the FBI (refer to Contact information section below) the existence of any of the following:
- Identification of indicators of compromise as outlined above.
- Presence of webshell code on compromised ServiceDesk Plus servers.
- Unauthorized access to or use of accounts.
- Evidence of lateral movement by malicious actors with access to compromised systems.
- Other indicators of unauthorized access or compromise.
Contact Information
Recipients of this report are encouraged to contribute any additional information that they may have related to this threat.
For any questions related to this report or to report an intrusion and request resources for incident response or technical assistance, please contact:
Revisions
December 2, 2021: Initial version
This product is provided subject to this Notification and this Privacy & Use policy.

 FTC research confirms what we’ve known for some time: that we hear from people in Latino communities less frequently than the general population. But reporting and experiencing fraud are two different things.
FTC research confirms what we’ve known for some time: that we hear from people in Latino communities less frequently than the general population. But reporting and experiencing fraud are two different things.
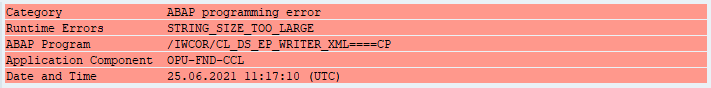

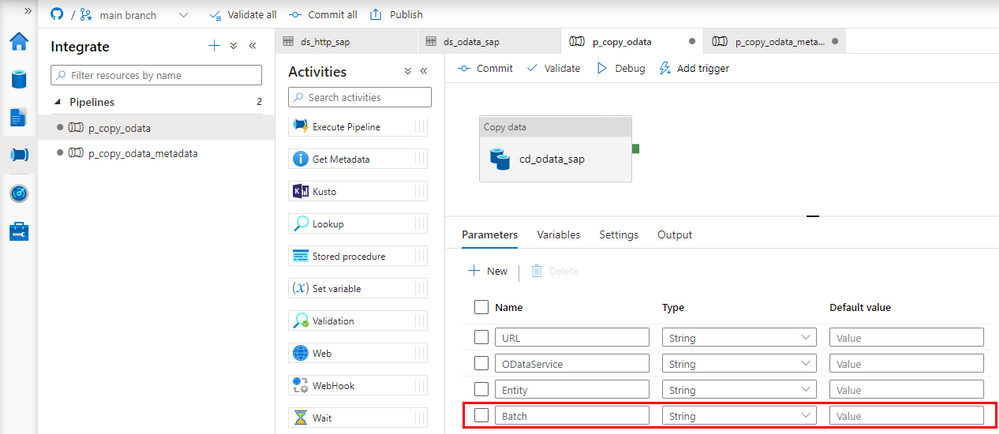
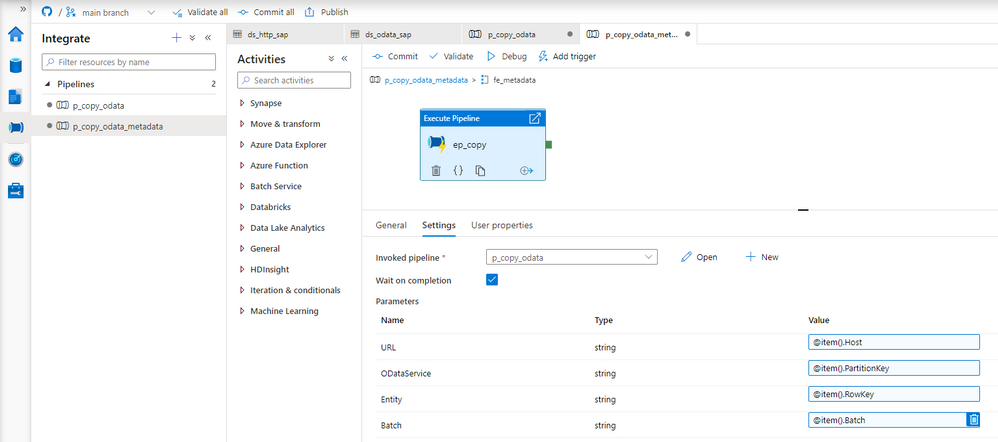
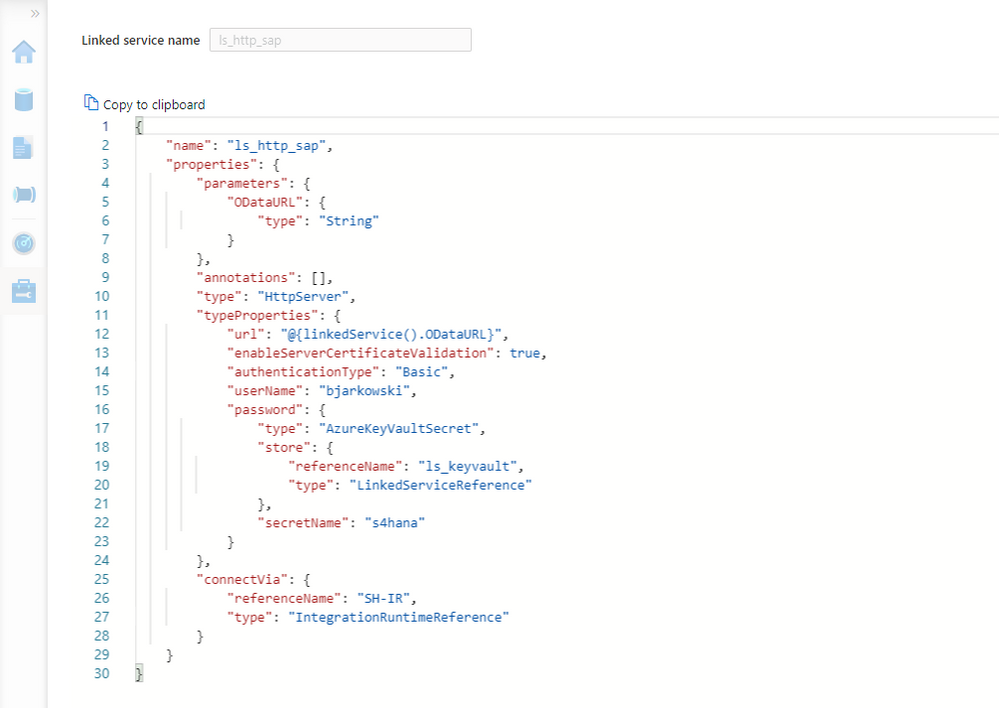
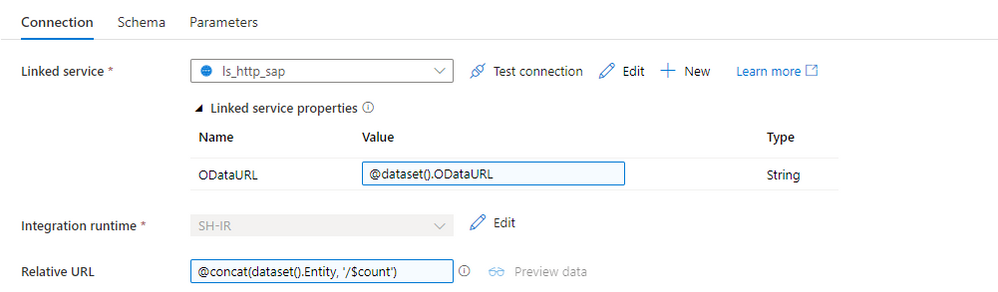
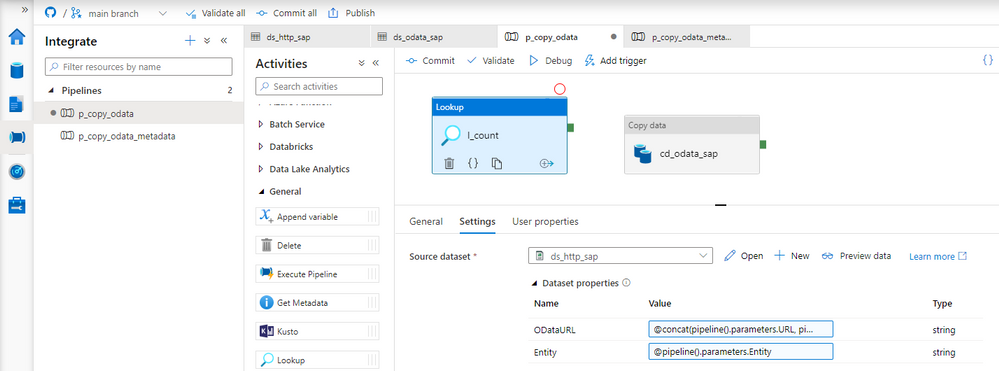
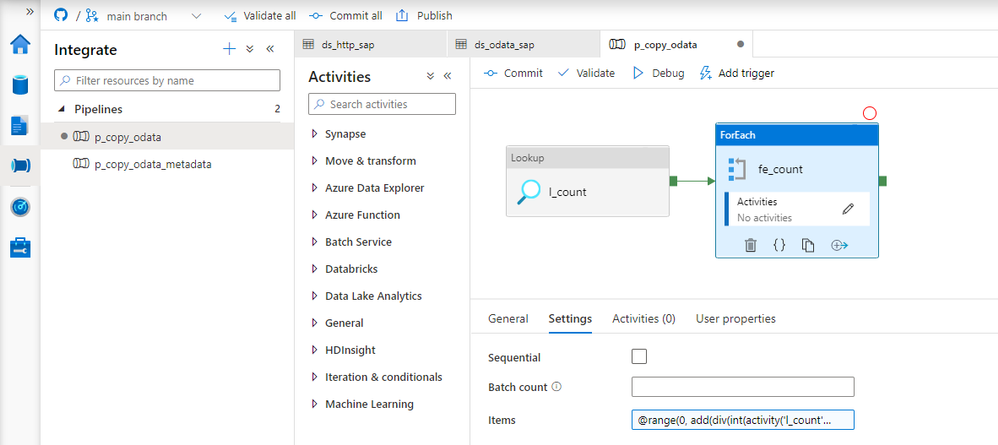
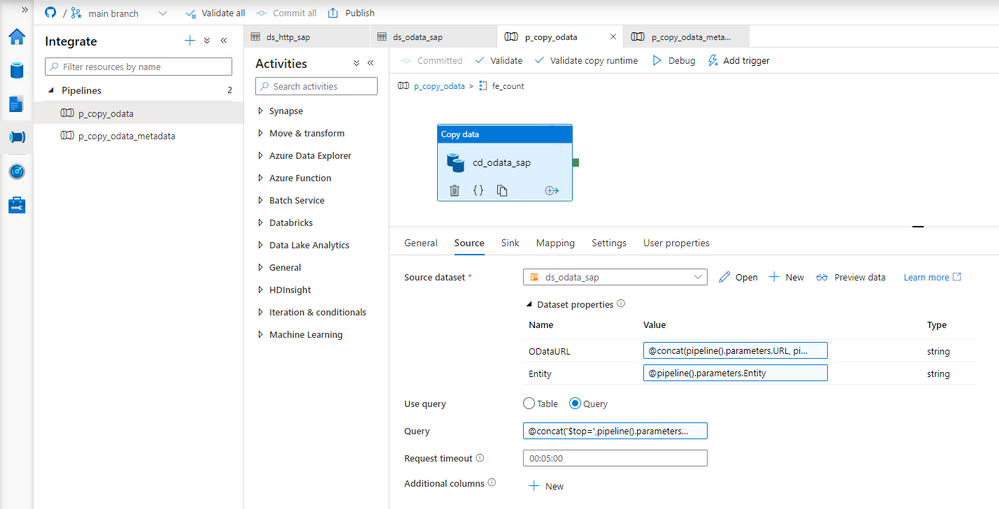
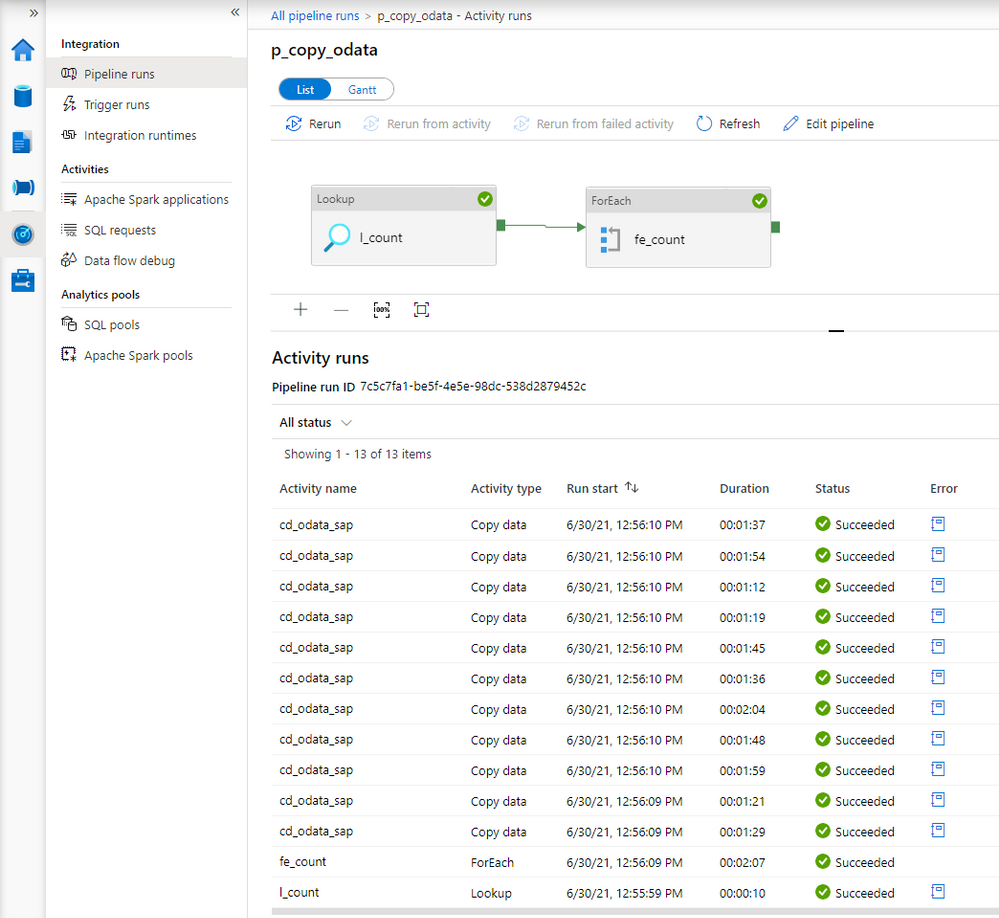
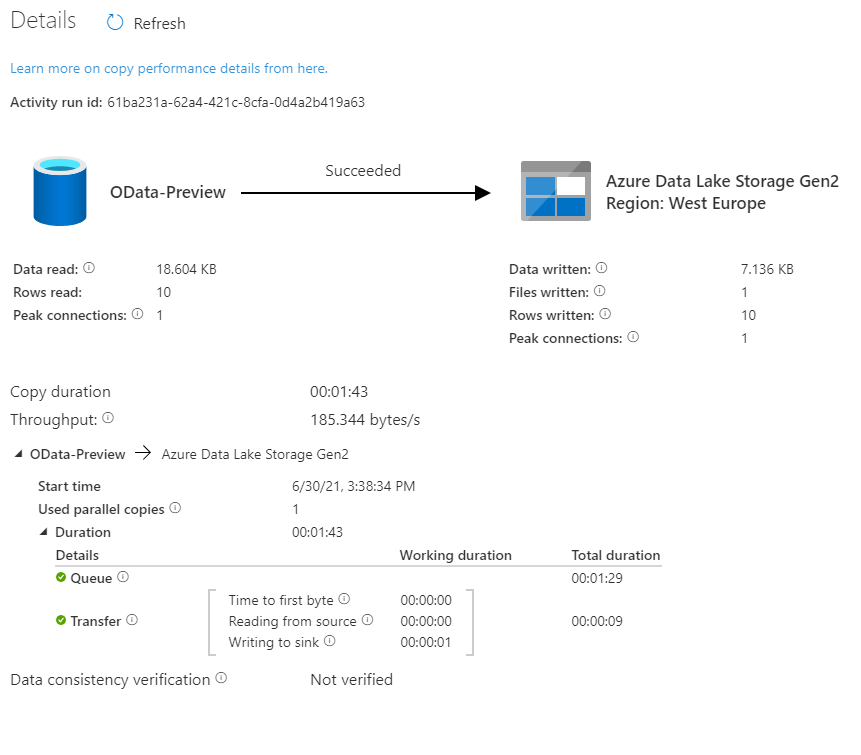
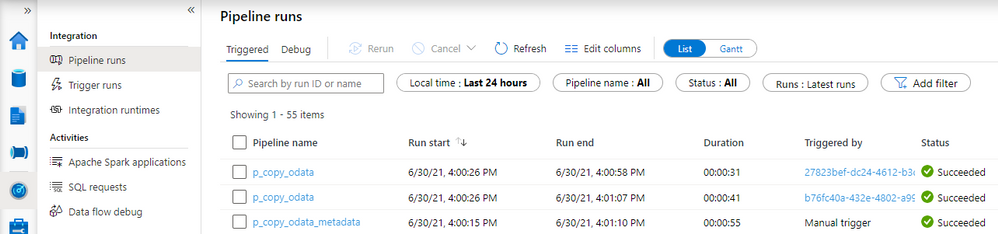
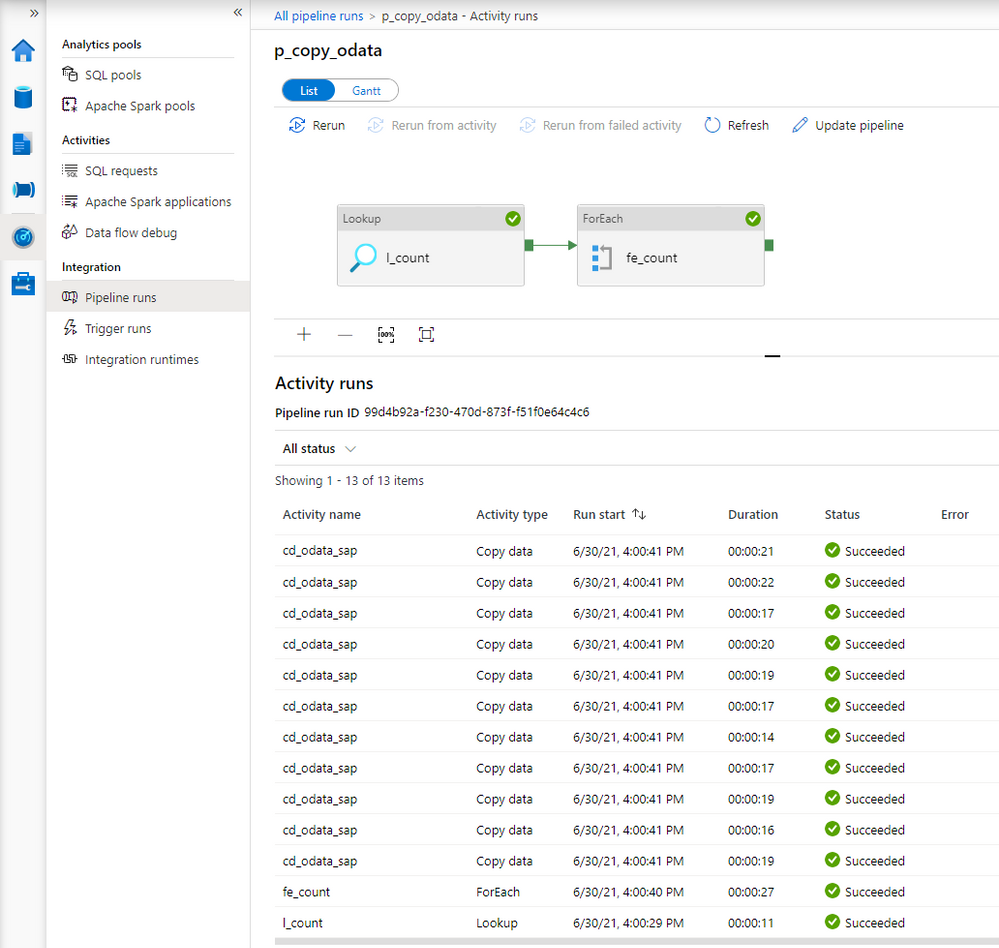
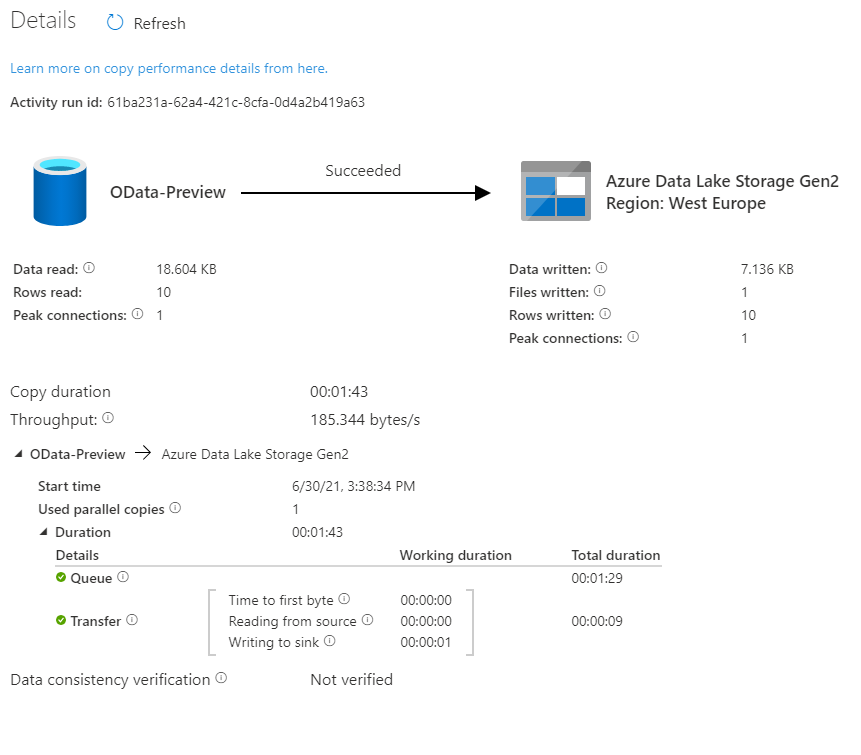
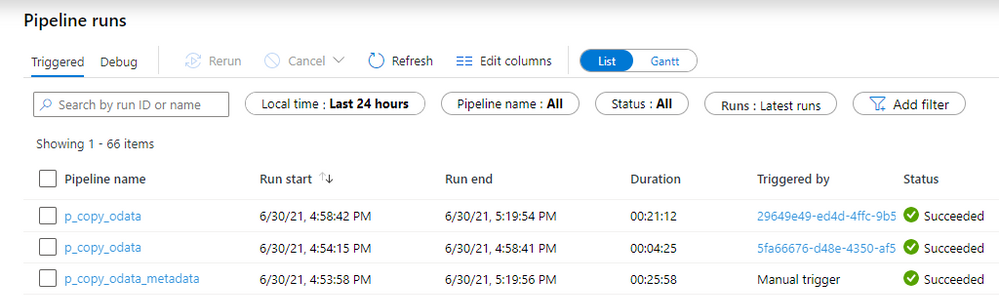
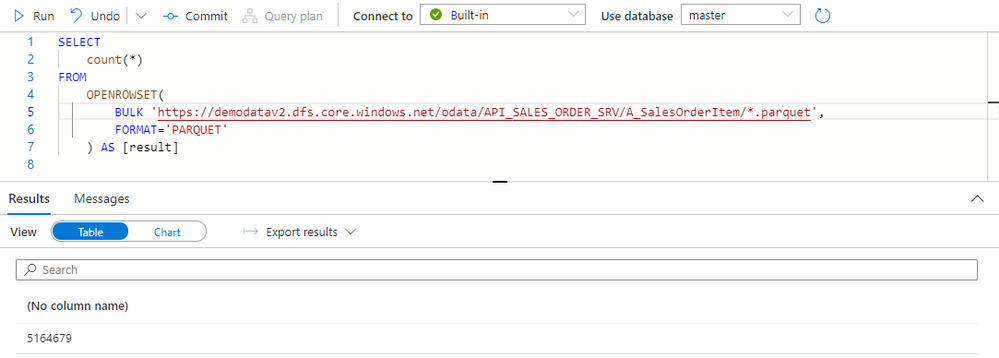
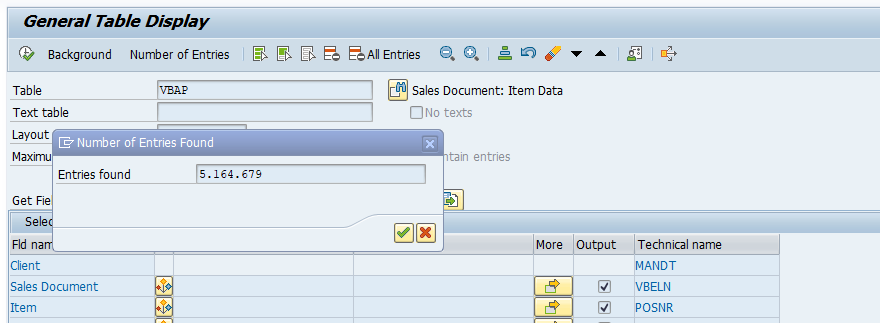

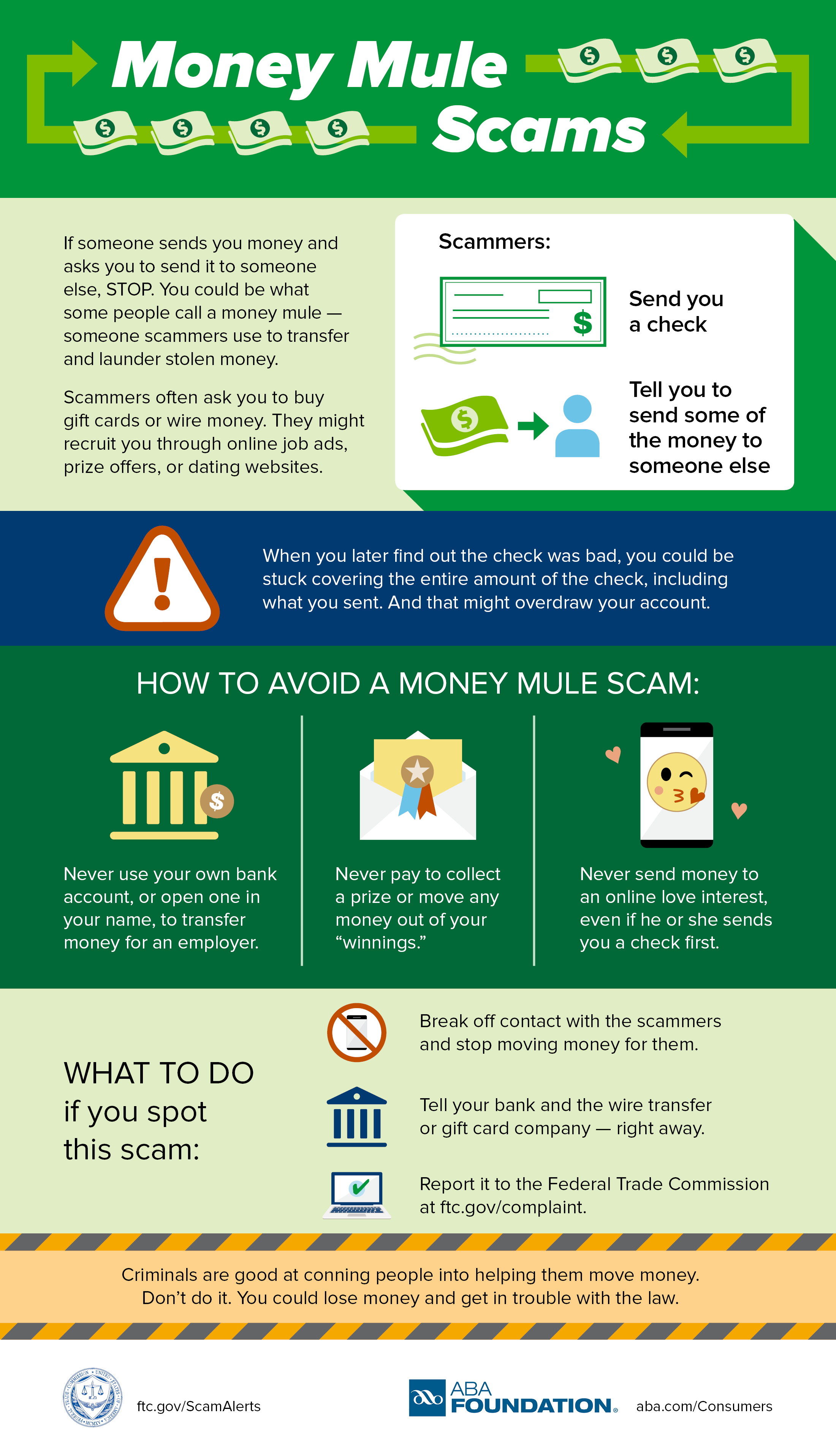
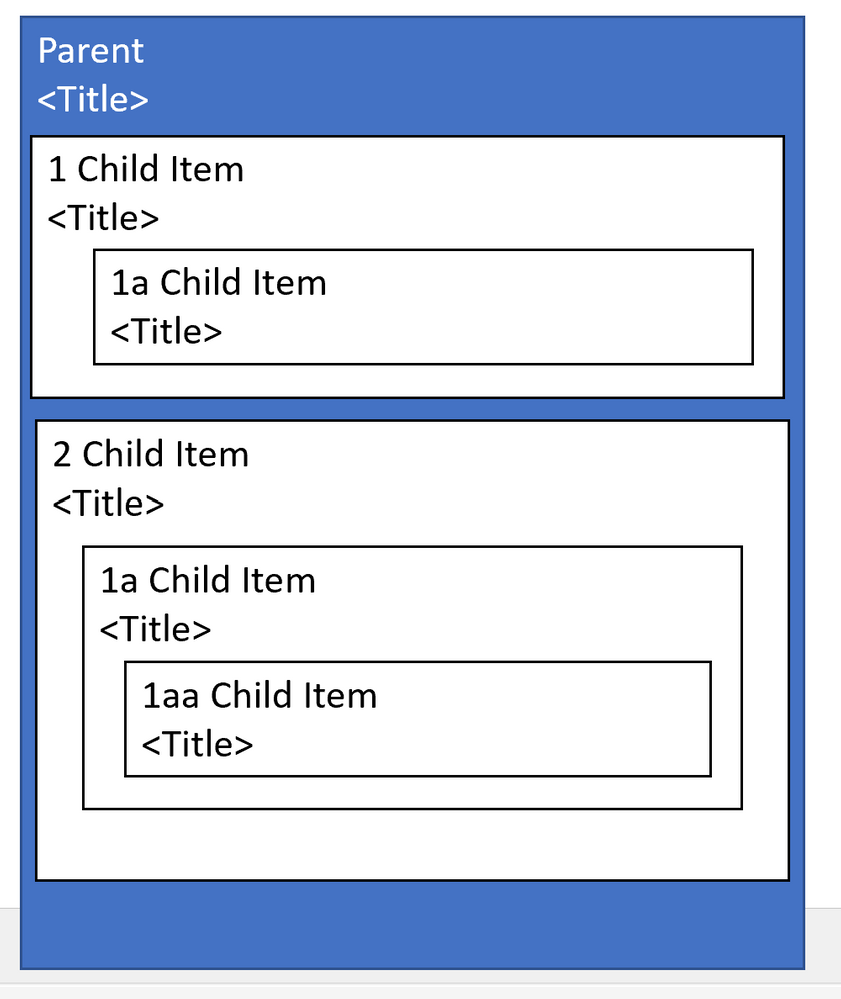
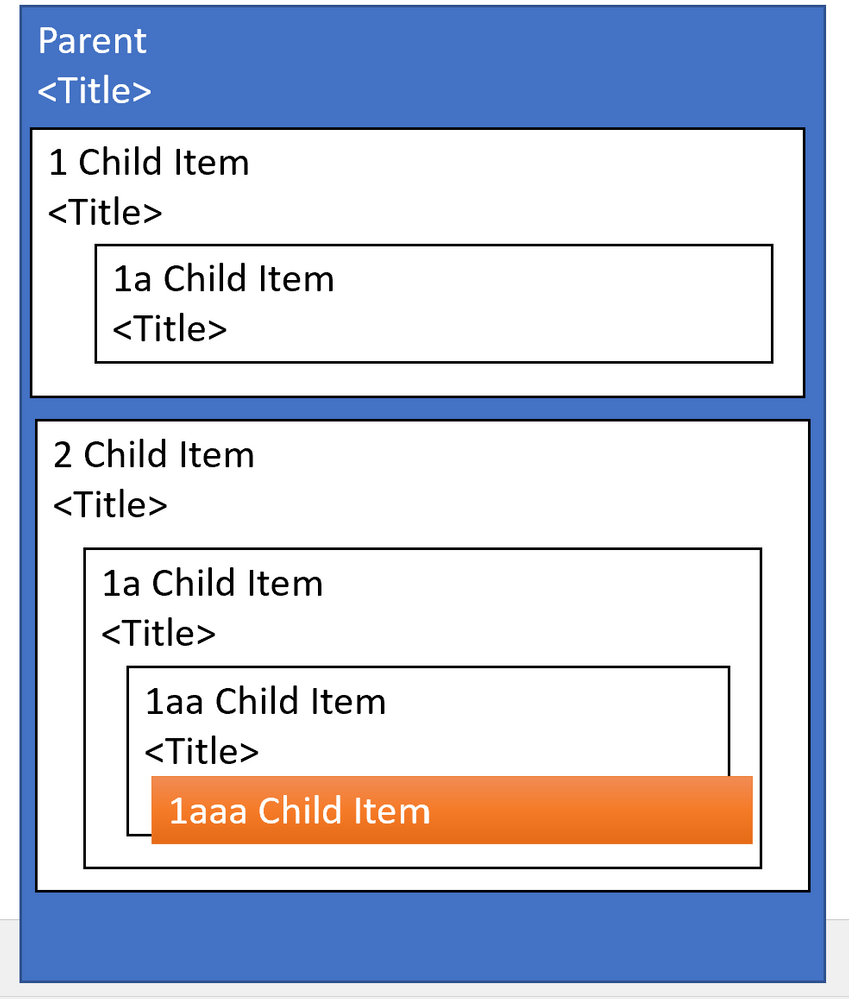



Recent Comments