How to recognize a fake Geek Squad renewal scam
This article was originally posted by the FTC. See the original article here.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article was originally posted by the FTC. See the original article here.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article is contributed. See the original author and article here.
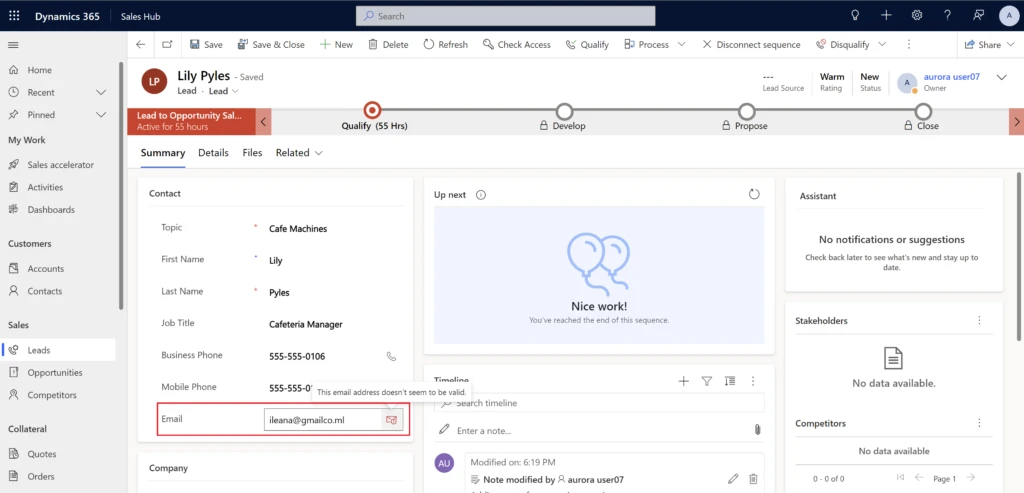
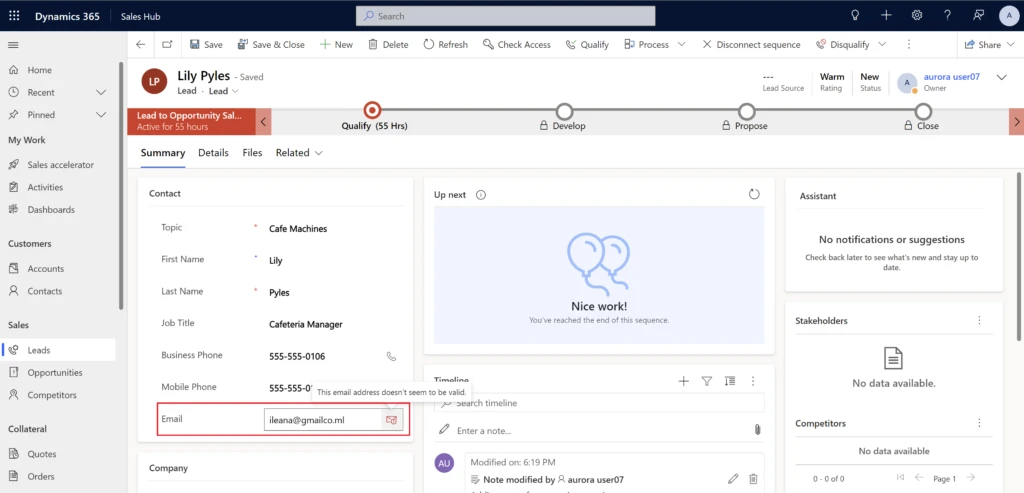
Sellers rely on email to reach out to contacts when working on deals. The new email address validation feature in Microsoft Dynamics 365 Sales flags email addresses in your customer relationship management (CRM) system that are in the wrong format or have an expired or fictitious domain. That lets your sellers connect with subscribers and boost their conversion rates without wasting time and energy trying to communicate with uninterested or non-existent customers.
Email address validation in Dynamics 365 Sales finds and removes non-working email addresses in your CRM. This lets your sellers prioritize leads that have a valid email address for lower email bounce rates, improved engagement, and a better return on their time.
Email address validation looks for the following errors:
You can view flagged email addresses on primary entity and sales insights forms as well as on the Up next widget and work list items.
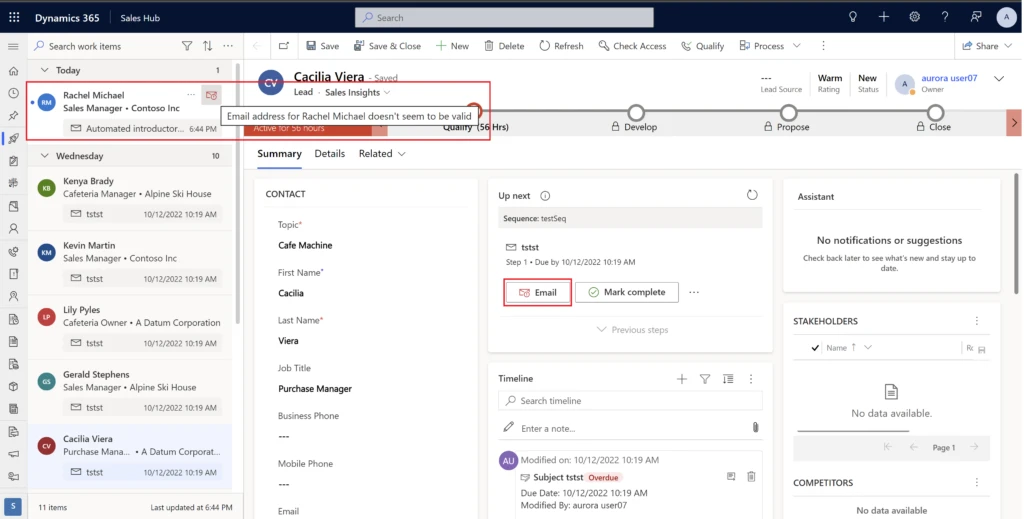
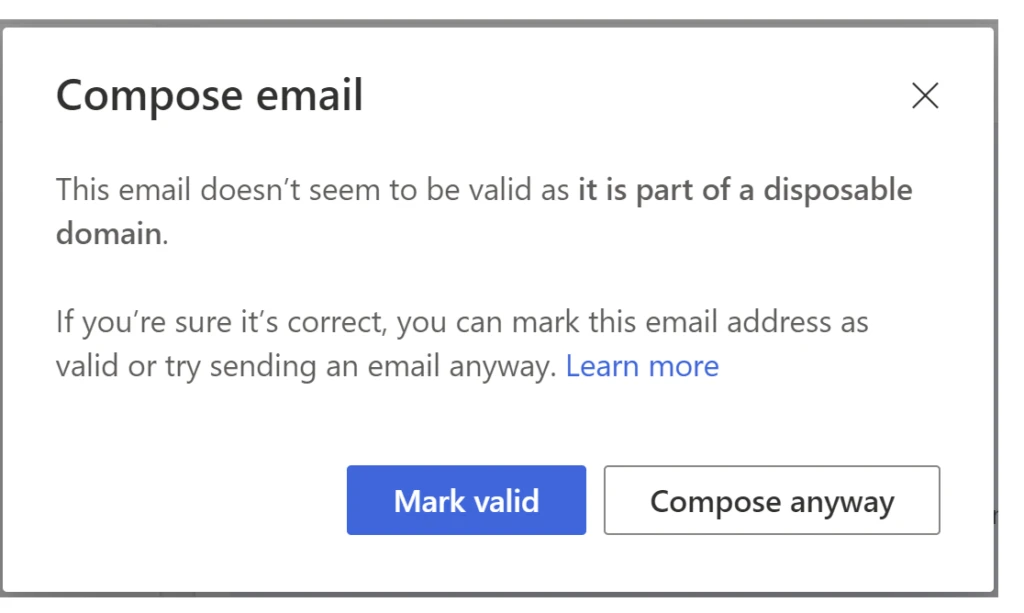
If you try to send an email to a flagged address, a notification gives you the reason the system marked the address as not valid.
In addition to email address validation, we have also implemented duplicate detection for leads. Dynamics 365 Sales uses AI and “fuzzy” matching algorithms to detect duplicate leads. By “fuzzy,” we mean that the system identifies as duplicates not only records that have exactly matching field values, but also records that have approximately matching field values. This helps sellers focus on the records that truly matter and clears out any “noise” that they would otherwise have to spend time manually reducing.
On top of that, we are continuously working on even more improvements to data hygiene in Dynamics 365 Sales to help your sellers be more focused and productive.
Increasing your sales team’s productivity could be as simple as eliminating leads with incomplete, non-working, or spam email addressesand Dynamics 365 Sales makes it easy.
To get started with email address validation, read the documentation:
Not a Dynamics 365 Sales customer yet? Take a guided tour and sign up for a free trial at Dynamics 365 Sales overview.
The post Email address validation improves seller conversion rates appeared first on Microsoft Dynamics 365 Blog.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article is contributed. See the original author and article here.
As part of Cybersecurity Awareness Month, explore the solutions that Microsoft Dynamics 365 Fraud Protection provides to help keep your organization’s data protected. Use the resources on Microsoft Learn to discover methods of supporting data security within your organization, whether you’re a functional consultant, a business user, a data analyst, or a developer. Learn how Fraud Protection helps safeguard customer accounts and build customer trust. Sandra Feinberg, Microsoft Principal Program Manager, offers insight on the subject. She observes that any enterprise using a Dynamics 365 Fraud Protection solution should consider that its high-quality data can be used not only to thwart fraud but also to make good decisions about customers while decreasing false positives. As she explains, “It’s not just about stopping bad transactions, but it’s uplifting those good transactions.”
What is Dynamics 365 Fraud Protection?
Dynamics 365 Fraud Protection helps you know your customers, decrease fraud costs, and improve the customer experience. Adaptive AI is an exciting technology that Fraud Prevention uses to learn fraud patterns as they continuously evolve and to prevent payment and account-creation fraud. For example, who is making the purchase? Is it a person? Sandra notes that businesses use this technology to help protect their accounts, saying, “Adaptive AI learns and adapts to patterns of legitimate and fraudulent account activities.” Importantly, she also points out, “Fraud protection is not just about knowing who the bad guys are, it’s about using the data to know who the good guys are, as well.”
To get an in-depth look at the innovative and advanced capabilities that Fraud Protection uses to help safeguard your data, explore the recently updated documentation, starting with Overview of Dynamics 365 Fraud Protection. For a deeper dive into Fraud Protection, work through these modules on Microsoft Learn:
If your organization already uses Dynamics 365 Commerce to deliver unified buying experiences for customers, the good news is that it’s easily integrated with Dynamics 365 Fraud Protection. Additionally, DFP is purpose built for Enterprise Retail, Gaming, Financial Institutions and Payment Service Providers. We are focused on building up our retail customer base to scale into new geographies.
To learn more about these integrations, read Dynamics 365 Fraud Protection integration with Dynamics 365 Commerce.
Explore a collection to discover more cybersecurity content
The documentation and other resources, such as learning paths and modules, on Microsoft Learn are helpful for gaining a basic understanding of Fraud Protection and other security offerings. Check out the Cybersecurity Awareness: Fraud Protection collection, which offers a variety of articles and training opportunities that can help you and your team learn about Fraud Protection capabilities.
Earn a Microsoft Certification
If Fraud Prevention is part of your Dynamics 365 toolkit, you can explore many pathways for validating your technical skills and earning recognition with globally recognized, industry-endorsed Microsoft Certifications. If you’re a seasoned data analyst, functional consultant, or solution architect, or if you work for a Microsoft Partner in one of these roles, a certification can help you advance in your career and build customer trust.
Keep building your Fraud Protection knowledge
To help keep your organization and customers secure, Sandra reiterates, “It’s really important to understand fraud and payments.” She recommends taking a Fraud 101 class, saying, “The broad Dynamics 365 Fraud Protection customer acquisition team will do those classes for our account teams.”
To learn more, discover blog posts, videos, events, and webinars—plus connect with peers and experts—join the Dynamics 365 Fraud Protection community.
This article was originally posted by the FTC. See the original article here.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article is contributed. See the original author and article here.
Dashboards tell a story through visualizations, and are an excellent way to view your data and see all of your most important insights at a glance. Azure Data Explorer dashboards in the web UI natively support the Kusto Query Language over data hosted in Azure Data Explorer. These dashboards will help you progress quickly from raw data to shared insights.
In the new module, you will create a dashboard from a query in Azure Data Explorer web UI. Add new tiles. Create dashboard parameters, and cross-filters for the parameters.
Create dashboards in Azure Data Explorer
More ADX MS Learn modules:
This article is contributed. See the original author and article here.
After seeing everyone in person at the San Francisco VMware Explore event, we are even more excited for Barcelona! If you want to know about Azure, the work we are doing with VMware, or just have a great conversation, we’d love to talk to you so stop by our booth! We will even have some cool stickers too.
This year we will have a bunch of sessions with Microsoft employees on stage, so if you’re building out your schedule check them out:
Microsoft Keynote: Transform your VMware Workloads with Microsoft Azure
Speaker: Jeff Woolsey, Principal PM Manager, Microsoft
Date/Time: Wednesday, November 9 @ 9:00 – 10:00 CET
Jeff will share how customers can transform their on-prem VMware environments using Microsoft Azure. Keynote attendees will learn how to:
In addition, here are some other Microsoft Azure-related sessions that we highly recommend for learning more about Azure + VMware:
Time, Topic | Session Title |
Tuesday, November 8 11:00 – 12:00 CET Azure VMware Solution | Migrate and Modernize with Cloud Solutions from Microsoft Azure VMware |
Tuesday, November 8 11:15 – 12:45 CET Azure VMware Solution | Instructor-led Hands-On Lab: Learn how to integrate Azure VMware Solution with Native Azure Services |
Tuesday, November 8 11:45 – 12:15 CET Azure VMware Solution Azure Virtual Desktop | Hybrid, Multicloud, Windows Server & SQL Server 2012 End of Support |
Tuesday, November 8 12:30 – 13:30 CET Azure VMware Solution | What’s New in Azure VMware Solution |
Wednesday, November 9 9:00 – 10:00 CET Azure VMware Solution Horizon Cloud on Azure | Microsoft Keynote: Transform your VMware Workloads with Microsoft Azure |
Wednesday, November 9 10:30 – 11:30 CET Azure VMware Solution | Automating Azure VMware Solution Onboarding and Configure NVA Networking Demo |
Wednesday, November 9 12:00 – 13:00 CET Azure Arc + vSphere | Bring Azure ARC to Your VMware vSphere Environments |
Wednesday, November 9 13:00 – 13:30 CET Azure VMware Solution | “Ask Me Anything” With Microsoft Azure VMware Solution Experts |
Wednesday, November 9 13:30 – 14:30 CET Azure Virtual Desktop | Maximizing Azure Virtual Desktop performance with Intel powered VM’s |
Wednesday, November 9 15:00 – 16:00 CET Azure VMware Solution Azure Virtual Desktop | Hybrid & Multicloud Innovation with Microsoft |
Wednesday, November 9 15:15 – 16:45 CET Azure VMware Solution | Instructor-led Hands-On Lab: Learn how to integrate Azure VMware Solution with Native Azure Services |
This article is contributed. See the original author and article here.
CISA, the Federal Bureau of Investigation (FBI), and the Department of Health and Human Services (HHS) have released a joint Cybersecurity Advisory (CSA), #StopRansomware: Daixin Team to provide information on the “Daixin Team,” a cybercrime group actively targeting U.S. businesses, predominantly in the Healthcare and Public Health (HPH) Sector, with ransomware and data extortion operations. This joint CSA provides Daixin actors’ tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) obtained from FBI threat response activities and third-party reporting.
CISA encourages HPH Sector organizations to review #StopRansomware: Daixin Team and to apply the recommended Mitigations. See StopRansomware.gov for additional guidance on ransomware protection, detection, and response.
This article is contributed. See the original author and article here.
Cisco has released a security update to address vulnerabilities affecting Cisco Identity Services Engine (ISE). A remote attacker could exploit some of these vulnerabilities to take control of an affected system. For updates addressing high and low severity vulnerabilities, see the Cisco Security Advisories page.
CISA encourages users and administrators to review Cisco Advisory cisco-sa-ise-path-trav-Dz5dpzyM and apply the necessary updates.
This article is contributed. See the original author and article here.
Microsoft.Data.SqlClient 5.1 Preview 1 has been released. This release contains improvements and updates to the Microsoft.Data.SqlClient data provider for SQL Server.
Our plan is to provide GA releases twice a year with two or three preview releases in between. This cadence should provide time for feedback and allow us to deliver features and fixes in a timely manner. This third 5.0 preview includes fixes and changes over the previous preview release.
ReadAsync() behavior to register Cancellation token action before streaming results. #1781NullReferenceException when assigning null to SqlConnectionStringBuilder.Encrypt. #1778HostNameInCertificate property in .NET Framework Reference Project. #1776Microsoft.Data.SqlClient.SNI (.NET Framework dependency) and Microsoft.Data.SqlClient.SNI.runtime (.NET Core/Standard dependency) version to 5.1.0-preview1.22278.1. #1787 which includes TLS 1.3 Support and fix for AppDomain crash in issue #1418SqlConnectionEncryptOption string parser to public. #1771ExecuteNonQueryAsync to use async context object. #1692Encrypt=Strict with TLS v1.3, the TLS handshake occurs twice on initial connection on .NET Framework due to a timeout during the TLS handshake and a retry helper re-establishes the connection; however, on .NET Core, it will throw a System.ComponentModel.Win32Exception (258): The wait operation timed out. and is being investigated. If you’re using Microsoft.Data.SqlClient with .NET Core on Windows 11, you will need to enable the managed SNI on Windows context switch using following statement AppContext.SetSwitch(“Switch.Microsoft.Data.SqlClient.UseManagedNetworkingOnWindows”, true); to use TLS v1.3 or disabling TLS 1.3 from the registry by assigning 0 to the following HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSecurityProvidersSCHANNELProtocolsTLS 1.3ClientEnabled registry key and it’ll use TLS v1.2 for the connection. This will be fixed in a future release.
For the full list of changes in Microsoft.Data.SqlClient 5.1 Preview 1, please see the Release Notes.
To try out the new package, add a NuGet reference to Microsoft.Data.SqlClient in your application and pick the 5.1 preview 1 version.
We appreciate the time and effort you spend checking out our previews. It makes the final product that much better. If you encounter any issues or have any feedback, head over to the SqlClient GitHub repository and submit an issue.
David Engel
This article is contributed. See the original author and article here.
Actions to take today to mitigate cyber threats from ransomware:
• Install updates for operating systems, software, and firmware as soon as they are released.
• Require phishing-resistant MFA for as many services as possible.
• Train users to recognize and report phishing attempts.
Note: This joint Cybersecurity Advisory (CSA) is part of an ongoing #StopRansomware effort to publish advisories for network defenders that detail various ransomware variants and ransomware threat actors. These #StopRansomware advisories include recently and historically observed tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) to help organizations protect against ransomware. Visit stopransomware.gov to see all #StopRansomware advisories and to learn more about other ransomware threats and no-cost resources.
The Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Security Agency (CISA), and Department of Health and Human Services (HHS) are releasing this joint CSA to provide information on the “Daixin Team,” a cybercrime group that is actively targeting U.S. businesses, predominantly in the Healthcare and Public Health (HPH) Sector, with ransomware and data extortion operations.
This joint CSA provides TTPs and IOCs of Daixin actors obtained from FBI threat response activities and third-party reporting.
Download the PDF version of this report: pdf, 591 KB
Note: This advisory uses the MITRE ATT&CK® for Enterprise framework, version 11. See MITRE ATT&CK for Enterprise for all referenced tactics and techniques.
Cybercrime actors routinely target HPH Sector organizations with ransomware:
The Daixin Team is a ransomware and data extortion group that has targeted the HPH Sector with ransomware and data extortion operations since at least June 2022. Since then, Daixin Team cybercrime actors have caused ransomware incidents at multiple HPH Sector organizations where they have:
Daixin actors gain initial access to victims through virtual private network (VPN) servers. In one confirmed compromise, the actors likely exploited an unpatched vulnerability in the organization’s VPN server [T1190]. In another confirmed compromise, the actors used previously compromised credentials to access a legacy VPN server [T1078] that did not have multifactor authentication (MFA) enabled. The actors are believed to have acquired the VPN credentials through the use of a phishing email with a malicious attachment [T1598.002].
After obtaining access to the victim’s VPN server, Daixin actors move laterally via Secure Shell (SSH) [T1563.001] and Remote Desktop Protocol (RDP) [T1563.002]. Daixin actors have sought to gain privileged account access through credential dumping [T1003] and pass the hash [T1550.002]. The actors have leveraged privileged accounts to gain access to VMware vCenter Server and reset account passwords [T1098] for ESXi servers in the environment. The actors have then used SSH to connect to accessible ESXi servers and deploy ransomware [T1486] on those servers.
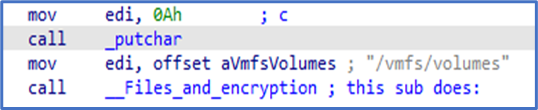
According to third-party reporting, the Daixin Team’s ransomware is based on leaked Babuk Locker source code. This third-party reporting as well as FBI analysis show that the ransomware targets ESXi servers and encrypts files located in /vmfs/volumes/ with the following extensions: .vmdk, .vmem, .vswp, .vmsd, .vmx, and .vmsn. A ransom note is also written to /vmfs/volumes/. See Figure 1 for targeted file system path and Figure 2 for targeted file extensions list. Figure 3 and Figure 4 include examples of ransom notes. Note that in the Figure 3 ransom note, Daixin actors misspell “Daixin” as “Daxin.”
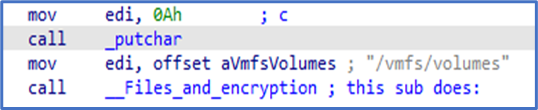
Figure 1: Daixin Team – Ransomware Targeted File Path
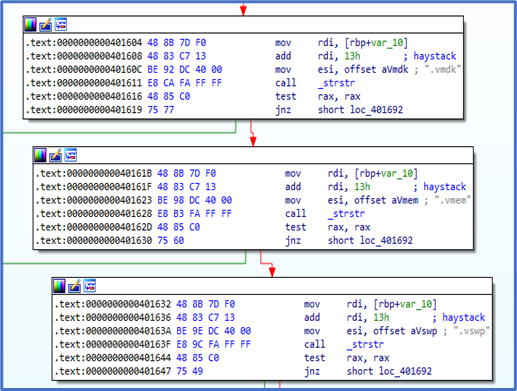
Figure 2: Daixin Team – Ransomware Targeted File Extensions
Figure 3: Example 1 of Daixin Team Ransomware Note
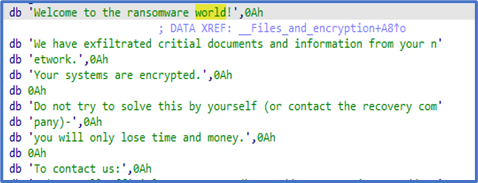
Figure 4: Example 2 of Daixin Team Ransomware Note
In addition to deploying ransomware, Daixin actors have exfiltrated data [TA0010] from victim systems. In one confirmed compromise, the actors used Rclone—an open-source program to manage files on cloud storage—to exfiltrate data to a dedicated virtual private server (VPS). In another compromise, the actors used Ngrok—a reverse proxy tool for proxying an internal service out onto an Ngrok domain—for data exfiltration [T1567].
See Table 1 for all referenced threat actor tactics and techniques included in this advisory.
Table 1: Daixin Actors’ ATT&CK Techniques for Enterprise
|
Reconnaissance |
||
|
Technique Title |
ID |
Use |
|
Phishing for Information: Spearphishing Attachment |
Daixin actors have acquired the VPN credentials (later used for initial access) by a phishing email with a malicious attachment. |
|
|
Initial Access |
||
|
Technique Title |
ID |
Use |
|
Exploit Public-Facing Application |
Daixin actors exploited an unpatched vulnerability in a VPN server to gain initial access to a network. |
|
|
Valid Accounts |
Daixin actors use previously compromised credentials to access servers on the target network. |
|
|
Persistence |
||
|
Technique Title |
ID |
Use |
|
Account Manipulation |
Daixin actors have leveraged privileged accounts to reset account passwords for VMware ESXi servers in the compromised environment. |
|
|
Credential Access |
||
|
Technique Title |
ID |
Use |
|
OS Credential Dumping |
Daixin actors have sought to gain privileged account access through credential dumping. |
|
|
Lateral Movement |
||
|
Technique Title |
ID |
Use |
|
Remote Service Session Hijacking: SSH Hijacking |
Daixin actors use SSH and RDP to move laterally across a network. |
|
|
Remote Service Session Hijacking: RDP Hijacking |
Daixin actors use RDP to move laterally across a network. |
|
|
Use Alternate Authentication Material: Pass the Hash |
Daixin actors have sought to gain privileged account access through pass the hash. |
|
|
Exfiltration |
||
|
Technique Title |
ID |
Use |
|
Exfiltration Over Web Service |
Daixin Team members have used Ngrok for data exfiltration over web servers. |
|
|
Impact |
||
|
Technique Title |
ID |
Use |
|
Data Encrypted for Impact |
Daixin actors have encrypted data on target systems or on large numbers of systems in a network to interrupt availability to system and network resources. |
|
See Table 2 for IOCs obtained from third-party reporting.
Table 2: Daixin Team IOCs – Rclone Associated SHA256 Hashes
|
File |
SHA256 |
|
rclone-v1.59.2-windows-amd64git-log.txt |
9E42E07073E03BDEA4CD978D9E7B44A9574972818593306BE1F3DCFDEE722238 |
|
rclone-v1.59.2-windows-amd64rclone.1 |
19ED36F063221E161D740651E6578D50E0D3CACEE89D27A6EBED4AB4272585BD |
|
rclone-v1.59.2-windows-amd64rclone.exe |
54E3B5A2521A84741DC15810E6FED9D739EB8083CB1FE097CB98B345AF24E939 |
|
rclone-v1.59.2-windows-amd64README.html |
EC16E2DE3A55772F5DFAC8BF8F5A365600FAD40A244A574CBAB987515AA40CBF |
|
rclone-v1.59.2-windows-amd64README.txt |
475D6E80CF4EF70926A65DF5551F59E35B71A0E92F0FE4DD28559A9DEBA60C28 |
FBI, CISA, and HHS urge HPH Sector organizations to implement the following to protect against Daixin and related malicious activity:
If a ransomware incident occurs at your organization:
Note: FBI, CISA, and HHS strongly discourage paying ransoms as doing so does not guarantee files and records will be recovered. Furthermore, payment may also embolden adversaries to target additional organizations, encourage other criminal actors to engage in the distribution of ransomware, and/or fund illicit activities.
The FBI is seeking any information that can be shared, to include boundary logs showing communication to and from foreign IP addresses, a sample ransom note, communications with Daixin Group actors, Bitcoin wallet information, decryptor files, and/or a benign sample of an encrypted file. Regardless of whether you or your organization have decided to pay the ransom, the FBI, CISA, and HHS urge you to promptly report ransomware incidents to a local FBI Field Office, or CISA at cisa.gov/report.
FBI, CISA, and HHS would like to thank CrowdStrike and the Health Information Sharing and Analysis Center (Health-ISAC) for their contributions to this CSA.
The information in this report is being provided “as is” for informational purposes only. FBI, CISA, and HHS do not endorse any commercial product or service, including any subjects of analysis. Any reference to specific commercial products, processes, or services by service mark, trademark, manufacturer, or otherwise, does not constitute or imply endorsement, recommendation, or favoring by FBI, CISA, or HHS.
Initial Publication: October 21, 2022
This product is provided subject to this Notification and this Privacy & Use policy.
Recent Comments