This article is contributed. See the original author and article here.
Azure Policy for Azure Kubernetes Service (AKS) clusters now utilizes/extends Gatekeeper v3 (OPA). The overview, installation steps for the Azure Policy add-on, limitations and recommendations are documented here – https://aka.ms/kubepolicydoc
Azure Security Center actually requires the add-on to audit and enforce security capabilities and compliance inside your clusters.
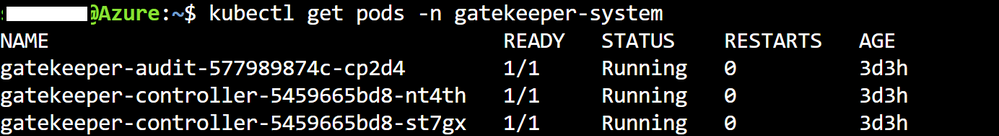
I am depicting the 3 Gatekeeper pods in the following image – which are utilized after the Azure Policy add-on has been enabled for an AKS cluster.
By installing / enabling the Azure Policy add-on customers can gain the inherent benefits of utilizing a managed add-on – the most important benefit being that – they would not need to resort to any manual upgrades if/when there is a version upgrade of Gatekeeper itself.
However, at present there are a few limitations. Let us focus on 2 limitations from the present list –
1.Installations of Gatekeeper outside of the Azure Policy Add-on aren’t supported. Uninstall any components installed by a previous Gatekeeper installation before enabling the Azure Policy Add-on.
2. Only built-in policy definitions are supported.
This means that the customer would not be able to utilize custom policies – considering – only built-in policies are supported + the usage of the add-on precludes any native Gatekeeper installation/usage.
So, for customers requiring policies beyond the list of built-in policies the overarching guidance is to use a combination of preventive and detective measures to achieve the same objective as their intended custom policies.
As an example – one of the customers wanted to take the policy driven route to ensure that the [default] namespace usage is always prohibited. At the time of this writing – it is not a built-in policy – so a preventive measure this customer could take is utilize Kubernetes native capabilities / RBAC as part of their deployment pipeline not allowing objects to be created in the [default] namespace.
Essentially, a preventive process enhancement to achieve their original objective.
The Azure Policy add-on is indeed an advantage-laden route to take – utilizing the set of built-in Kubernetes policies as applicable in combination with preventive and detective measures to achieve the any custom policy intent.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.


Recent Comments