This article is contributed. See the original author and article here.
AKS-HCI integration with Azure Defender for Kubernetes bring security capabilities that cover both protection and detection controls.
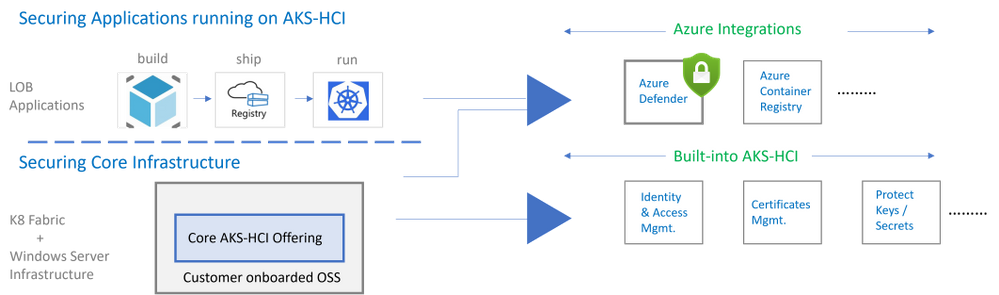
AKS-HCI security includes securing the K8 fabric and applications that are deployed on it. This is achieved by a combination of in-box/built-in security features and integration with Azure services as shown below.
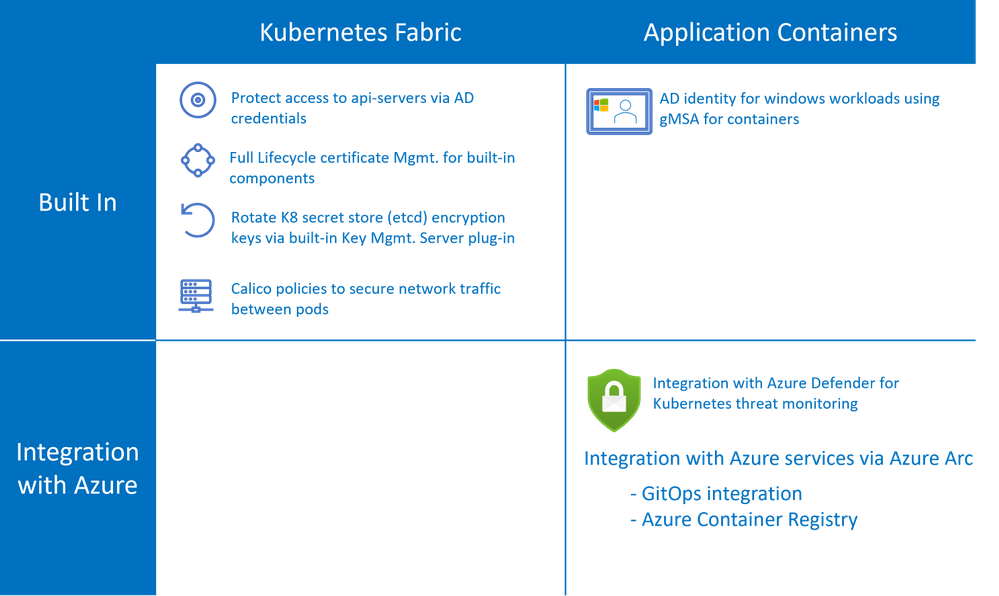
AKS-HCI is a validated Azure Arc Enabled Kubernetes distribution. Azure Arc enabled clusters are connected to Azure via Arc when they are deployed. This allows automatic deployment of specific Arc extensions that provide monitoring and observability out of the box. Extensions greatly simplify onboarding; customers can deploy Azure integrations with just a few clicks or API calls. Azure Arc enabled Kubernetes ensures that you always have the latest bits and can automatically apply updates as they become available.
Azure Defender is Azure Security Center‘s integrated cloud workload protection platform (CWPP), bringing advanced, intelligent, protection of Azure and hybrid resources and workloads.
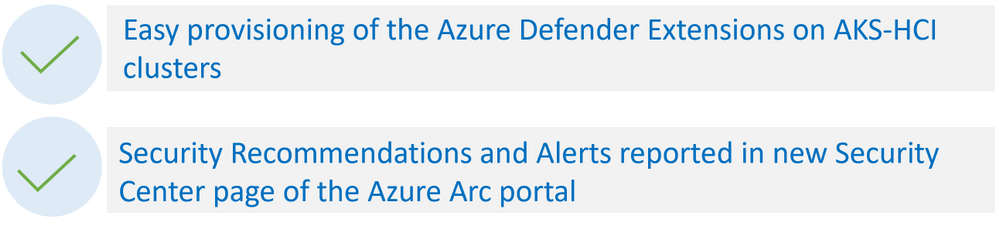
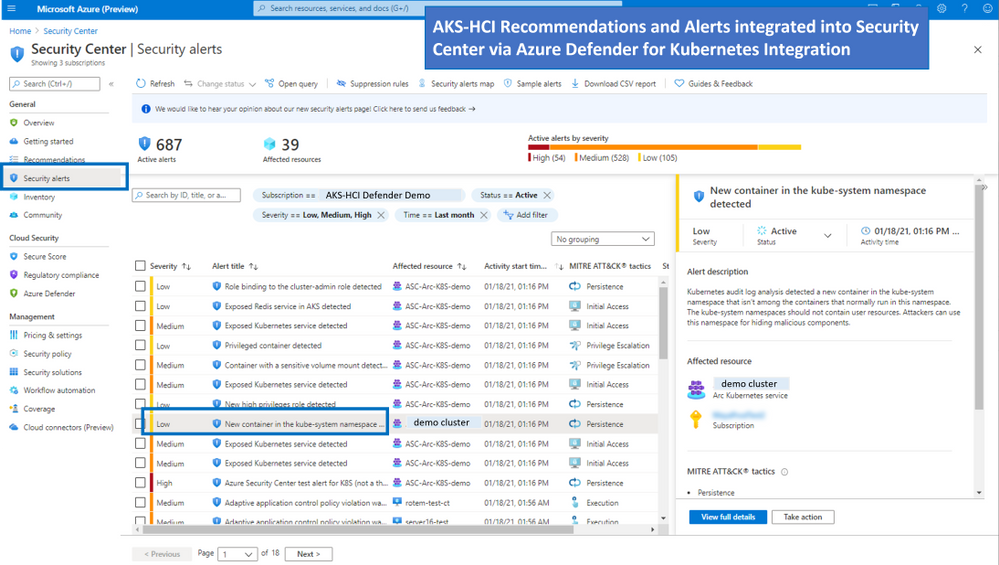
Azure Defender for Kubernetes is an Azure Defender service that continuously monitors for threat and raises alerts to defend Kubernetes clusters. Azure Defender for Kubernetes supports AKS-HCI clusters, leveraging Arc extensions capabilities. This integration between AKS-HCI and Azure Defender for Kubernetes brings the following two distinct advantages:
As shown in the figure below AKS-HCI clusters are integrated into the Azure Security Center portal
Types of Attacks on Kubernetes Containers detected by Azure Defender for Kubernetes
Azure Defender Kubernetes plan offers protection of Kubernetes clusters, both at the orchestration layer and at the node level. The orchestration layer protection monitors Kubernetes API operations to find suspicious and malicious activities in the Kubernetes control plane.
With MITRE ATT&CK’s approach of methodically outlining the possible threats, Microsoft built the Threat Matrix for Kubernetes, which the first attempts to systematically map the attack surface of Kubernetes. An updated version of the matrix was released earlier this year.
In this blog you can find more details on Azure Defender detections with their correlation to MITRE ATT&CK® for Containers matrix techniques.
The figure below describes the progression of single alert across the different phases (as defined in the MITRE ATT&CK framework)
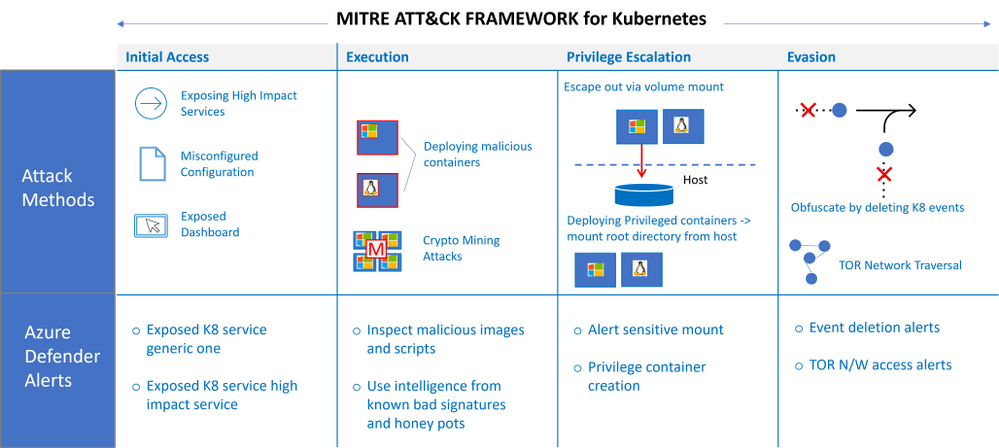
Some examples of attacks that could be potentially high risk
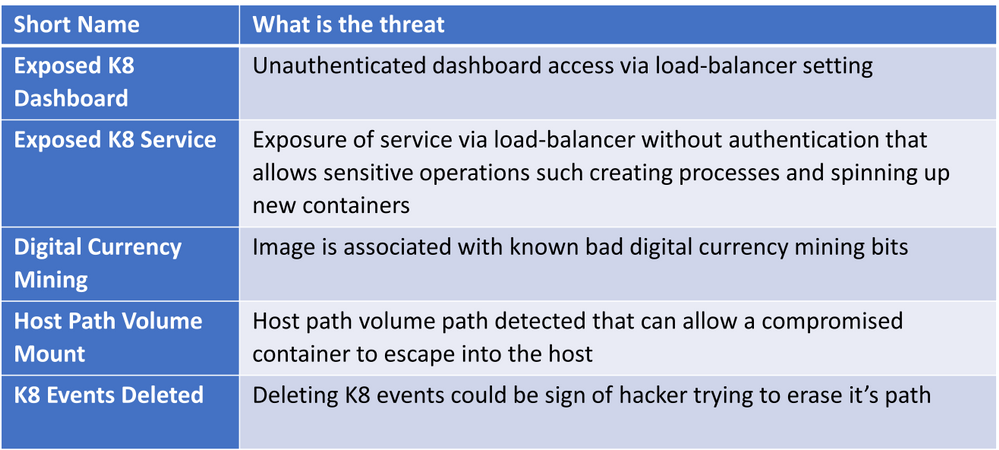
For the full list of Kubernetes security alerts along with their relevance to MITRE tactics see: Azure Defender page
FAQs
How does Azure Defender for Kubernetes work under the hood
You can refer to the architectural overview in this link. Further details in a blog from Yossi Weizman.
Q: Do I need to subscribe to Azure Defender before I can add Azure Defender Extension to my Arc enabled Kubernetes Cluster
AKS-HCI is an Azure Arc enabled Kubernetes distribution with an Azure subscription provided as part of the set-up process. To use Azure Defender for Kubernetes threat monitoring the admin needs to add Azure Defender for Kubernetes to the Azure subscription. For more information refer to this link.
Q: Is there is free tier for Azure Defender for Arc enabled Kubernetes
Currently, Azure Defender for Azure Arc Enabled Kubernetes is in public preview, during public preview there is no charge for AKS-HCI clusters. The pricing details will be available when the feature is Generally Available.
Q: Where can I find deployment steps
AKS-HCI is a validated Azure Arc enabled Kubernetes deployment, the deployment steps can be found on this link.
Q: Does Azure Defender for Kubernetes generate alerts for both windows and linux worker nodes
Orchestration level alerts that come from api-server and K8 apis are supported agonistic of Operating System. Run-time alerts such as process inspections for malware, privilege escalations etc are OS dependent. Run-time alerts are planned in the near future.
Q: Does integration with Azure Defender for Kubernetes cover alerts for servers
No, there is a separate subscription for covering alerts for server, for more information on Azure Defender for servers please refer to this link here
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.


Recent Comments