by Scott Muniz | Nov 15, 2021 | Security, Technology
This article is contributed. See the original author and article here.
| 404_to_301_project — 404_to_301 |
The 404 to 301 – Redirect, Log and Notify 404 Errors WordPress plugin before 3.0.9 does not have CSRF check in place when cleaning the logs, which could allow attacker to make a logged in admin delete all of them via a CSRF attack |
2021-11-08 |
4.3 |
CVE-2021-24766
MISC |
| airangel — hsmx-app-25_firmware |
Airangel HSMX Gateway devices through 5.2.04 have Hard-coded Database Credentials. |
2021-11-10 |
6.4 |
CVE-2021-40519
MISC
MISC |
| androidbubbles — wp_header_images |
The WP Header Images WordPress plugin before 2.0.1 does not sanitise and escape the t parameter before outputting it back in the plugin’s settings page, leading to a Reflected Cross-Site Scripting issue |
2021-11-08 |
4.3 |
CVE-2021-24798
MISC |
| apostrophecms — apostrophecms |
Apostrophe CMS versions between 2.63.0 to 3.3.1 affected by an insufficient session expiration vulnerability, which allows unauthenticated remote attackers to hijack recently logged-in users’ sessions. |
2021-11-08 |
6.4 |
CVE-2021-25979
MISC |
| azeotech — daqfactory |
Project files are stored memory objects in the form of binary serialized data that can later be read and deserialized again to instantiate the original objects in memory. Malicious manipulation of these files may allow an attacker to corrupt memory. |
2021-11-05 |
6.8 |
CVE-2021-42698
MISC |
| azeotech — daqfactory |
The affected product is vulnerable to cookie information being transmitted as cleartext over HTTP. An attacker can capture network traffic, obtain the user’s cookie and take over the account. |
2021-11-05 |
4.3 |
CVE-2021-42699
MISC |
| barrier_project — barrier |
An issue was discovered in Barrier before 2.3.4. The barriers component (aka the server-side implementation of Barrier) does not correctly close file descriptors for established TCP connections. An unauthenticated remote attacker can thus cause file descriptor exhaustion in the server process, leading to denial of service. |
2021-11-08 |
5 |
CVE-2021-42075
MLIST
MISC |
| barrier_project — barrier |
An issue was discovered in Barrier before 2.4.0. The barriers component (aka the server-side implementation of Barrier) does not sufficiently verify the identify of connecting clients. Clients can thus exploit weaknesses in the provided protocol to cause denial-of-service or stage further attacks that could lead to information leaks or integrity corruption. |
2021-11-08 |
6.5 |
CVE-2021-42072
MISC
MLIST |
| barrier_project — barrier |
An issue was discovered in Barrier before 2.4.0. An attacker can enter an active session state with the barriers component (aka the server-side implementation of Barrier) simply by supplying a client label that identifies a valid client configuration. This label is “Unnamed” by default but could instead be guessed from hostnames or other publicly available information. In the active session state, an attacker can capture input device events from the server, and also modify the clipboard content on the server. |
2021-11-08 |
5.8 |
CVE-2021-42073
CONFIRM
MLIST |
| barrier_project — barrier |
An issue was discovered in Barrier before 2.3.4. An attacker can cause memory exhaustion in the barriers component (aka the server-side implementation of Barrier) and barrierc by sending long TCP messages. |
2021-11-08 |
5 |
CVE-2021-42076
MLIST
MISC |
| barrier_project — barrier |
An issue was discovered in Barrier before 2.3.4. An unauthenticated attacker can cause a segmentation fault in the barriers component (aka the server-side implementation of Barrier) by quickly opening and closing TCP connections while sending a Hello message for each TCP session. |
2021-11-08 |
5 |
CVE-2021-42074
MLIST
MISC |
| batch_cat_project — batch_cat |
The Batch Cat WordPress plugin through 0.3 defines 3 custom AJAX actions, which both require authentication but are available for all roles. As a result, any authenticated user (including simple subscribers) can add/set/delete arbitrary categories to posts. |
2021-11-08 |
4 |
CVE-2021-24788
MISC |
| beeline — smart_box_firmware |
Beeline Smart Box 2.0.38 is vulnerable to Cross Site Scripting (XSS) via the choose_mac parameter to setup.cgi. |
2021-11-10 |
4.3 |
CVE-2021-41427
MISC
MISC
MISC |
| beeline — smart_box_firmware |
Beeline Smart box 2.0.38 is vulnerable to Cross Site Request Forgery (CSRF) via mgt_end_user.htm. |
2021-11-10 |
6.8 |
CVE-2021-41426
MISC
MISC
MISC |
| beescms — beescms |
BEESCMS v4.0 was discovered to contain an arbitrary file upload vulnerability via the component /admin/upload.php. This vulnerability allows attackers to execute arbitrary code via a crafted image file. |
2021-11-08 |
6.8 |
CVE-2020-23572
MISC |
| bookstackapp — bookstack |
bookstack is vulnerable to Improper Limitation of a Pathname to a Restricted Directory (‘Path Traversal’) |
2021-11-05 |
4 |
CVE-2021-3916
CONFIRM
MISC |
| casap_automated_enrollment_system_project — casap_automated_enrollment_system |
Multiple Cross Site Scripting (XSS) vulnerabilities exist in SourceCodester CASAP Automated Enrollment System 1.0 via the (1) user_username and (2) category parameters in save_class.php, the (3) firstname, (4) class, and (5) status parameters in student_table.php, the (6) category and (7) class_name parameters in add_class1.php, the (8) fname, (9) mname,(10) lname, (11) address, (12) class, (13) gfname, (14) gmname, (15) glname, (16) rship, (17) status, (18) transport, and (19) route parameters in add_student.php, the (20) fname, (21) mname, (22) lname, (23) address, (24) class, (25) fgname, (26) gmname, (27) glname, (28) rship, (29) status, (30) transport, and (31) route parameters in save_stud.php,the (32) status, (33) fname, and (34) lname parameters in add_user.php, the (35) username, (36) firstname, and (37) status parameters in users.php, the (38) fname, (39) lname, and (40) status parameters in save_user.php, and the (41) activity_log, (42) aprjun, (43) class, (44) janmar, (45) Julsep,(46) octdec, (47) Students and (48) users parameters in table_name. |
2021-11-08 |
4.3 |
CVE-2021-40261
MISC |
| chameleon_css_project — chameleon_css |
The Chameleon CSS WordPress plugin through 1.2 does not have any CSRF and capability checks in all its AJAX calls, allowing any authenticated user, such as subscriber to call them and perform unauthorised actions. One of AJAX call, remove_css, also does not sanitise or escape the css_id POST parameter before using it in a SQL statement, leading to a SQL Injection |
2021-11-08 |
6.5 |
CVE-2021-24626
MISC
MISC |
| cloudera — cloudera_manager |
Cloudera Manager 5.x, 6.x, 7.1.x, 7.2.x, and 7.3.x allows XSS. |
2021-11-08 |
4.3 |
CVE-2021-29243
MISC
MISC |
| cloudera — cloudera_manager |
Cloudera Manager 7.2.4 has Incorrect Access Control, allowing Escalation of Privileges to view the restricted Dashboard. |
2021-11-08 |
5 |
CVE-2021-32483
MISC
MISC |
| cloudera — cloudera_manager |
Cloudera Manager 5.x, 6.x, 7.1.x, 7.2.x, and 7.3.x allows XSS via the path parameter. |
2021-11-08 |
4.3 |
CVE-2021-32482
MISC
MISC |
| cloudera — hue |
Cloudera Hue 4.6.0 allows XSS via the type parameter. |
2021-11-08 |
4.3 |
CVE-2021-32481
MISC
CONFIRM |
| cloudera — hue |
Cloudera Hue 4.6.0 allows XSS. |
2021-11-08 |
4.3 |
CVE-2021-29994
CONFIRM
CONFIRM
MISC |
| codesupply — squaretype |
The Squaretype WordPress theme before 3.0.4 allows unauthenticated users to manipulate the query_vars used to retrieve the posts to display in one of its REST endpoint, without any validation. As a result, private and scheduled posts could be retrieved via a crafted request. |
2021-11-08 |
5 |
CVE-2021-24840
MISC |
| dolibarr — dolibarr |
Dolibarr ERP and CRM 13.0.2 allows XSS via object details, as demonstrated by > and < characters in the onpointermove attribute of a BODY element to the user-management feature. |
2021-11-10 |
4.3 |
CVE-2021-33618
MISC
MISC
MISC
FULLDISC |
| draftpress — header_footer_code_manager |
The Header Footer Code Manager WordPress plugin before 1.1.14 does not validate and escape the “orderby” and “order” request parameters before using them in a SQL statement when viewing the Snippets admin dashboard, leading to SQL injections |
2021-11-08 |
6.5 |
CVE-2021-24791
MISC |
| eclipse — theia |
In versions of the @theia/plugin-ext component of Eclipse Theia prior to 1.18.0, Webview contents can be hijacked via postMessage(). |
2021-11-10 |
4.3 |
CVE-2021-41038
CONFIRM
CONFIRM |
| engineers_online_portal_project — engineers_online_portal |
A SQL Injection vulnerability exists in Sourcecodester Engineers Online Portal in PHP via the id parameter to quiz_question.php, which could let a malicious user extract sensitive data from the web server and in some cases use this vulnerability in order to get a remote code execution on the remote web server. |
2021-11-05 |
6.5 |
CVE-2021-42666
MISC
MISC
MISC |
| engineers_online_portal_project — engineers_online_portal |
An incorrect access control vulnerability exists in Sourcecodester Engineers Online Portal in PHP in nia_munoz_monitoring_system/admin/uploads. An attacker can leverage this vulnerability in order to bypass access controls and access all the files uploaded to the web server without the need of authentication or authorization. |
2021-11-05 |
5 |
CVE-2021-42671
MISC
MISC |
| enrocrypt_project — enrocrypt |
EnroCrypt is a Python module for encryption and hashing. Prior to version 1.1.4, EnroCrypt used the MD5 hashing algorithm in the hashing file. Beginners who are unfamiliar with hashes can face problems as MD5 is considered an insecure hashing algorithm. The vulnerability is patched in v1.1.4 of the product. As a workaround, users can remove the `MD5` hashing function from the file `hashing.py`. |
2021-11-08 |
5 |
CVE-2021-39182
MISC
CONFIRM |
| feataholic — maz_loader |
The MAZ Loader – Preloader Builder for WordPress plugin before 1.3.3 does not validate or escape the loader_id parameter of the mzldr shortcode, which allows users with a role as low as Contributor to perform SQL injection. |
2021-11-08 |
6.5 |
CVE-2021-24669
MISC |
| flowpaper — pdf2json |
pdf2json v0.71 was discovered to contain a NULL pointer dereference in the component ObjectStream::getObject. |
2021-11-10 |
5 |
CVE-2020-23879
MISC
MISC |
| fullworks — redirect_404_error_page_to_homepage_or_custom_page_with_logs |
The Redirect 404 Error Page to Homepage or Custom Page with Logs WordPress plugin before 1.7.9 does not check for CSRF when deleting logs, which could allow attacker to make a logged in admin delete them via a CSRF attack |
2021-11-08 |
4.3 |
CVE-2021-24767
MISC |
| fusionpbx — fusionpbx |
An issue was discovered in FusionPBX before 4.5.30. The fax_post_size may have risky characters (it is not constrained to preset values). |
2021-11-05 |
6.5 |
CVE-2021-43406
MISC |
| fusionpbx — fusionpbx |
An issue was discovered in FusionPBX before 4.5.30. The fax_extension may have risky characters (it is not constrained to be numeric). |
2021-11-05 |
6.5 |
CVE-2021-43405
MISC
MISC |
| fusionpbx — fusionpbx |
An issue was discovered in FusionPBX before 4.5.30. The FAX file name may have risky characters. |
2021-11-05 |
6.5 |
CVE-2021-43404
MISC |
| g_auto-hyperlink_project — g_auto-hyperlink |
The G Auto-Hyperlink WordPress plugin through 1.0.1 does not sanitise or escape an ‘id’ GET parameter before using it in a SQL statement, to select data to be displayed in the admin dashboard, leading to an authenticated SQL injection |
2021-11-08 |
6.5 |
CVE-2021-24627
MISC
MISC |
| genetechsolutions — pie_register |
The Registration Forms – User profile, Content Restriction, Spam Protection, Payment Gateways, Invitation Codes WordPress plugin before 3.1.7.6 has a flaw in the social login implementation, allowing unauthenticated attacker to login as any user on the site by only knowing their user ID or username |
2021-11-08 |
6.8 |
CVE-2021-24647
MISC |
| genie_wp_favicon_project — genie_wp_favicon |
The Genie WP Favicon WordPress plugin through 0.5.2 does not have CSRF in place when updating the favicon, which could allow attackers to make a logged in admin change it via a CSRF attack |
2021-11-08 |
4.3 |
CVE-2021-24674
MISC |
| getgrav — grav |
grav is vulnerable to Improper Limitation of a Pathname to a Restricted Directory (‘Path Traversal’) |
2021-11-05 |
5 |
CVE-2021-3924
CONFIRM
MISC |
| gitlab — gitlab |
Improper access control in GitLab CE/EE version 10.5 and above allowed subgroup members with inherited access to a project from a parent group to still have access even after the subgroup is transferred |
2021-11-05 |
5 |
CVE-2021-39897
MISC
CONFIRM
MISC |
| gitlab — gitlab |
In all versions of GitLab CE/EE since version 10.6, a project export leaks the external webhook token value which may allow access to the project which it was exported from. |
2021-11-05 |
5 |
CVE-2021-39898
MISC
CONFIRM
MISC |
| gitlab — gitlab |
A potential DOS vulnerability was discovered in GitLab CE/EE starting with version 13.7. The stripping of EXIF data from certain images resulted in high CPU usage. |
2021-11-05 |
5 |
CVE-2021-39907
MISC
CONFIRM
MISC |
| gitlab — gitlab |
A potential DoS vulnerability was discovered in GitLab CE/EE starting with version 13.7. Using a malformed TIFF images was possible to trigger memory exhaustion. |
2021-11-05 |
5 |
CVE-2021-39912
CONFIRM
MISC
MISC |
| gitlab — gitlab |
An Improper Access Control vulnerability in the GraphQL API in GitLab CE/EE since version 13.1 allows a Merge Request creator to resolve discussions and apply suggestions after a project owner has locked the Merge Request |
2021-11-05 |
4 |
CVE-2021-39904
CONFIRM
MISC
MISC |
| gitlab — gitlab |
Improper validation of ipynb files in GitLab CE/EE version 13.5 and above allows an attacker to execute arbitrary JavaScript code on the victim’s behalf. |
2021-11-05 |
4.3 |
CVE-2021-39906
MISC
CONFIRM
MISC |
| gitlab — gitlab |
An improper access control flaw in GitLab CE/EE since version 13.9 exposes private email address of Issue and Merge Requests assignee to Webhook data consumers |
2021-11-05 |
4 |
CVE-2021-39911
MISC
CONFIRM |
| gitlab — gitlab |
An information disclosure vulnerability in the GitLab CE/EE API since version 8.9.6 allows a user to see basic information on private groups that a public project has been shared with |
2021-11-05 |
4 |
CVE-2021-39905
MISC
CONFIRM
MISC |
| gitlab — gitlab |
In all versions of GitLab CE/EE since version 11.10, an admin of a group can see the SCIM token of that group by visiting a specific endpoint. |
2021-11-05 |
4 |
CVE-2021-39901
MISC
CONFIRM
MISC |
| gnu — hurd |
An issue was discovered in GNU Hurd before 0.9 20210404-9. The use of an authentication protocol in the proc server is vulnerable to man-in-the-middle attacks, which can be exploited for local privilege escalation to get full root access. |
2021-11-07 |
6.9 |
CVE-2021-43414
MISC
MISC |
| golang — go |
Go before 1.16.10 and 1.17.x before 1.17.3 allows an archive/zip Reader.Open panic via a crafted ZIP archive containing an invalid name or an empty filename field. |
2021-11-08 |
4.3 |
CVE-2021-41772
MISC |
| golang — go |
ImportedSymbols in debug/macho (for Open or OpenFat) in Go before 1.16.10 and 1.17.x before 1.17.3 Accesses a Memory Location After the End of a Buffer, aka an out-of-bounds slice situation. |
2021-11-08 |
4.3 |
CVE-2021-41771
MISC |
| google — android |
Improper input validation vulnerability in HDCP prior to SMR Nov-2021 Release 1 allows attackers to arbitrary code execution. |
2021-11-05 |
4.6 |
CVE-2021-25503
MISC |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affected versions the code for boosted trees in TensorFlow is still missing validation. As a result, attackers can trigger denial of service (via dereferencing `nullptr`s or via `CHECK`-failures) as well as abuse undefined behavior (binding references to `nullptr`s). An attacker can also read and write from heap buffers, depending on the API that gets used and the arguments that are passed to the call. Given that the boosted trees implementation in TensorFlow is unmaintained, it is recommend to no longer use these APIs. We will deprecate TensorFlow’s boosted trees APIs in subsequent releases. The fix will be included in TensorFlow 2.7.0. We will also cherrypick this commit on TensorFlow 2.6.1, TensorFlow 2.5.2, and TensorFlow 2.4.4, as these are also affected and still in supported range. |
2021-11-05 |
4.6 |
CVE-2021-41208
MISC
CONFIRM |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affected versions several TensorFlow operations are missing validation for the shapes of the tensor arguments involved in the call. Depending on the API, this can result in undefined behavior and segfault or `CHECK`-fail related crashes but in some scenarios writes and reads from heap populated arrays are also possible. We have discovered these issues internally via tooling while working on improving/testing GPU op determinism. As such, we don’t have reproducers and there will be multiple fixes for these issues. These fixes will be included in TensorFlow 2.7.0. We will also cherrypick these commits on TensorFlow 2.6.1, TensorFlow 2.5.2, and TensorFlow 2.4.4, as these are also affected and still in supported range. |
2021-11-05 |
4.6 |
CVE-2021-41206
MISC
MISC
MISC
MISC
CONFIRM
MISC
MISC |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affected versions the code behind `tf.function` API can be made to deadlock when two `tf.function` decorated Python functions are mutually recursive. This occurs due to using a non-reentrant `Lock` Python object. Loading any model which contains mutually recursive functions is vulnerable. An attacker can cause denial of service by causing users to load such models and calling a recursive `tf.function`, although this is not a frequent scenario. The fix will be included in TensorFlow 2.7.0. We will also cherrypick this commit on TensorFlow 2.6.1, TensorFlow 2.5.2, and TensorFlow 2.4.4, as these are also affected and still in supported range. |
2021-11-05 |
4.3 |
CVE-2021-41213
MISC
CONFIRM |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affected versions the shape inference code for `tf.ragged.cross` has an undefined behavior due to binding a reference to `nullptr`. The fix will be included in TensorFlow 2.7.0. We will also cherrypick this commit on TensorFlow 2.6.1, TensorFlow 2.5.2, and TensorFlow 2.4.4, as these are also affected and still in supported range. |
2021-11-05 |
4.6 |
CVE-2021-41214
CONFIRM
MISC |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affected versions the shape inference function for `Transpose` is vulnerable to a heap buffer overflow. This occurs whenever `perm` contains negative elements. The shape inference function does not validate that the indices in `perm` are all valid. The fix will be included in TensorFlow 2.7.0. We will also cherrypick this commit on TensorFlow 2.6.1, TensorFlow 2.5.2, and TensorFlow 2.4.4, as these are also affected and still in supported range. |
2021-11-05 |
4.6 |
CVE-2021-41216
CONFIRM
MISC |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affeced versions during execution, `EinsumHelper::ParseEquation()` is supposed to set the flags in `input_has_ellipsis` vector and `*output_has_ellipsis` boolean to indicate whether there is ellipsis in the corresponding inputs and output. However, the code only changes these flags to `true` and never assigns `false`. This results in unitialized variable access if callers assume that `EinsumHelper::ParseEquation()` always sets these flags. The fix will be included in TensorFlow 2.7.0. We will also cherrypick this commit on TensorFlow 2.6.1, TensorFlow 2.5.2, and TensorFlow 2.4.4, as these are also affected and still in supported range. |
2021-11-05 |
4.6 |
CVE-2021-41201
MISC
CONFIRM |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affected versions the code for sparse matrix multiplication is vulnerable to undefined behavior via binding a reference to `nullptr`. This occurs whenever the dimensions of `a` or `b` are 0 or less. In the case on one of these is 0, an empty output tensor should be allocated (to conserve the invariant that output tensors are always allocated when the operation is successful) but nothing should be written to it (that is, we should return early from the kernel implementation). Otherwise, attempts to write to this empty tensor would result in heap OOB access. The fix will be included in TensorFlow 2.7.0. We will also cherrypick this commit on TensorFlow 2.6.1, TensorFlow 2.5.2, and TensorFlow 2.4.4, as these are also affected and still in supported range. |
2021-11-05 |
4.6 |
CVE-2021-41219
CONFIRM
MISC |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affected versions an attacker can trigger undefined behavior, integer overflows, segfaults and `CHECK`-fail crashes if they can change saved checkpoints from outside of TensorFlow. This is because the checkpoints loading infrastructure is missing validation for invalid file formats. The fixes will be included in TensorFlow 2.7.0. We will also cherrypick these commits on TensorFlow 2.6.1, TensorFlow 2.5.2, and TensorFlow 2.4.4, as these are also affected and still in supported range. |
2021-11-05 |
4.6 |
CVE-2021-41203
CONFIRM
MISC
MISC
MISC
MISC |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affected versions TensorFlow’s `saved_model_cli` tool is vulnerable to a code injection as it calls `eval` on user supplied strings. This can be used by attackers to run arbitrary code on the plaform where the CLI tool runs. However, given that the tool is always run manually, the impact of this is not severe. We have patched this by adding a `safe` flag which defaults to `True` and an explicit warning for users. The fix will be included in TensorFlow 2.7.0. We will also cherrypick this commit on TensorFlow 2.6.1, TensorFlow 2.5.2, and TensorFlow 2.4.4, as these are also affected and still in supported range. |
2021-11-05 |
4.6 |
CVE-2021-41228
MISC
CONFIRM |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affected versions the shape inference code for the `Cudnn*` operations in TensorFlow can be tricked into accessing invalid memory, via a heap buffer overflow. This occurs because the ranks of the `input`, `input_h` and `input_c` parameters are not validated, but code assumes they have certain values. The fix will be included in TensorFlow 2.7.0. We will also cherrypick this commit on TensorFlow 2.6.1, TensorFlow 2.5.2, and TensorFlow 2.4.4, as these are also affected and still in supported range. |
2021-11-05 |
4.6 |
CVE-2021-41221
CONFIRM
MISC |
| google — tensorflow |
TensorFlow is an open source platform for machine learning. In affected versions the async implementation of `CollectiveReduceV2` suffers from a memory leak and a use after free. This occurs due to the asynchronous computation and the fact that objects that have been `std::move()`d from are still accessed. The fix will be included in TensorFlow 2.7.0. We will also cherrypick this commit on TensorFlow 2.6.1, as this version is the only one that is also affected. |
2021-11-05 |
4.6 |
CVE-2021-41220
CONFIRM
MISC |
| gvectors — wpdiscuz |
The wpDiscuz WordPress plugin before 7.3.4 does check for CSRF when adding, editing and deleting comments, which could allow attacker to make logged in users such as admin edit and delete arbitrary comment, or the user who made the comment to edit it via a CSRF attack. Attackers could also make logged in users post arbitrary comment. |
2021-11-08 |
4.3 |
CVE-2021-24806
MISC |
| hitachi — vantara_pentaho |
An issue was discovered in Hitachi Vantara Pentaho through 9.1 and Pentaho Business Intelligence Server through 7.x. The Security Model has different layers of Access Control. One of these layers is the applicationContext security, which is defined in the applicationContext-spring-security.xml file. The default configuration allows an unauthenticated user with no previous knowledge of the platform settings to extract pieces of information without possessing valid credentials. |
2021-11-08 |
5 |
CVE-2021-31602
MISC
MISC |
| hitachi — vantara_pentaho |
UploadService in Hitachi Vantara Pentaho Business Analytics through 9.1 does not properly verify uploaded user files, which allows an authenticated user to upload various files of different file types. Specifically, a .jsp file is not allowed, but a .jsp. file is allowed (and leads to remote code execution). |
2021-11-08 |
6.5 |
CVE-2021-34685
MISC
MISC |
| hitachi — vantara_pentaho |
An issue was discovered in Hitachi Vantara Pentaho through 9.1 and Pentaho Business Intelligence Server through 7.x. A reports (.prpt) file allows the inclusion of BeanShell scripts to ease the production of complex reports. An authenticated user can run arbitrary code. |
2021-11-08 |
6.5 |
CVE-2021-31599
MISC
MISC |
| hitachi — vantara_pentaho |
An issue was discovered in Hitachi Vantara Pentaho through 9.1 and Pentaho Business Intelligence Server through 7.x. They implement a series of web services using the SOAP protocol to allow scripting interaction with the backend server. An authenticated user (regardless of privileges) can list all databases connection details and credentials. |
2021-11-08 |
4 |
CVE-2021-31601
MISC
MISC |
| hitachi — vantara_pentaho |
An issue was discovered in Hitachi Vantara Pentaho through 9.1 and Pentaho Business Intelligence Server through 7.x. They implement a series of web services using the SOAP protocol to allow scripting interaction with the backend server. An authenticated user (regardless of privileges) can list all valid usernames. |
2021-11-08 |
4 |
CVE-2021-31600
MISC
MISC |
| hospital_management_system_project — hospital_management_system |
Multiple Cross Site Scripting (XSS) vulnerabilities exist in PHPGurukul Hospital Management System 4.0 via the (1) searchdata parameter in (a) doctor/search.php and (b) admin/patient-search.php, and the (2) fromdate and (3) todate parameters in admin/betweendates-detailsreports.php. |
2021-11-05 |
4.3 |
CVE-2021-39411
MISC |
| hp — futuresmart_4 |
A potential security vulnerability has been identified for certain HP printers and MFPs with Troy solutions. For affected printers with FutureSmart Firmware bundle version 4.9 or 4.9.0.1 the potential vulnerability may cause instability in the solution. |
2021-11-09 |
4.6 |
CVE-2019-18912
MISC |
| ibm — business_automation_workflow |
IBM Business Automation Workflow 18. 19, 20, 21, and IBM Business Process Manager 8.5 and d8.6 transmits or stores authentication credentials, but it uses an insecure method that is susceptible to unauthorized interception and/or retrieval. |
2021-11-05 |
4.3 |
CVE-2021-29753
CONFIRM
XF |
| ibm — infosphere_information_server |
IBM InfoSphere Information Server 11.7 could allow an authenticated user to obtain sensitive information from application response requests that could be used in further attacks against the system. IBM X-Force ID: 209401. |
2021-11-10 |
4 |
CVE-2021-38887
CONFIRM
XF |
| ibm — mq_appliance |
IBM MQ 9.1 LTS, 9.1 CD, 9.2 LTS, and 9.2CD is vulnerable to a denial of service attack caused by an issue processing message properties. IBM X-Force ID: 205203. |
2021-11-08 |
4 |
CVE-2021-29843
XF
CONFIRM |
| ibm — qradar_network_security |
IBM QRadar Network Security 5.4.0 and 5.5.0 transmits sensitive or security-critical data in cleartext in a communication channel that can be obtained using man in the middle techniques. IBM X-Force ID: 17467. |
2021-11-08 |
4.3 |
CVE-2020-4152
CONFIRM
XF |
| ibm — qradar_network_security |
IBM QRadar Network Security 5.4.0 and 5.5.0 could allow a remote attacker to obtain sensitive information, caused by the failure to properly enable HTTP Strict Transport Security. An attacker could exploit this vulnerability to obtain sensitive information using man in the middle techniques. IBM X-Force ID: 174340. |
2021-11-08 |
4.3 |
CVE-2020-4160
XF
CONFIRM |
| igexsolutions — wpschoolpress |
The School Management System – WPSchoolPress WordPress plugin before 2.1.10 does not properly sanitize or use prepared statements before using POST variable in SQL queries, leading to SQL injection in multiple actions available to various authenticated users, from simple subscribers/students to teachers and above. |
2021-11-08 |
6.5 |
CVE-2021-24575
MISC |
| irfanview — irfanview |
Irfanview v4.53 allows attackers to execute arbitrary code via a crafted JPEG 2000 file. Related to a “Data from Faulting Address controls Branch Selection starting at JPEG2000!ShowPlugInSaveOptions_W+0x0000000000032850”. |
2021-11-05 |
6.8 |
CVE-2020-23565
MISC |
| irfanview — irfanview |
Irfanview v4.53 allows attackers to to cause a denial of service (DoS) via a crafted JPEG 2000 file. Related to “Integer Divide By Zero starting at JPEG2000!ShowPlugInSaveOptions_W+0x00000000000082ea” |
2021-11-05 |
4.3 |
CVE-2020-23567
MISC |
| irfanview — irfanview |
Irfanview v4.53 was discovered to contain an infinity loop via JPEG2000!ShowPlugInSaveOptions_W+0x1ecd8. |
2021-11-05 |
4.3 |
CVE-2020-23566
MISC |
| jetbrains — hub |
In JetBrains Hub before 2021.1.13690, information disclosure via avatar metadata is possible. |
2021-11-09 |
5 |
CVE-2021-43180
MISC |
| jetbrains — hub |
In JetBrains Hub before 2021.1.13690, stored XSS is possible. |
2021-11-09 |
4.3 |
CVE-2021-43181
MISC |
| jetbrains — hub |
In JetBrains Hub before 2021.1.13415, a DoS via user information is possible. |
2021-11-09 |
5 |
CVE-2021-43182
MISC |
| jetbrains — ktor |
In JetBrains Ktor before 1.6.4, nonce verification during the OAuth2 authentication process is implemented improperly. |
2021-11-09 |
5 |
CVE-2021-43203
MISC |
| jetbrains — teamcity |
In JetBrains TeamCity before 2021.1.2, some HTTP security headers were missing. |
2021-11-09 |
5 |
CVE-2021-43195
MISC |
| jetbrains — teamcity |
In JetBrains TeamCity before 2021.1.2, user enumeration was possible. |
2021-11-09 |
5 |
CVE-2021-43194
MISC |
| jetbrains — teamcity |
In JetBrains TeamCity before 2021.1.3, a newly created project could take settings from an already deleted project. |
2021-11-09 |
5 |
CVE-2021-43201
MISC |
| jetbrains — teamcity |
In JetBrains TeamCity before 2021.1, information disclosure via the Docker Registry connection dialog is possible. |
2021-11-09 |
5 |
CVE-2021-43196
MISC |
| jetbrains — teamcity |
In JetBrains TeamCity before 2021.1.2, permission checks in the Create Patch functionality are insufficient. |
2021-11-09 |
5 |
CVE-2021-43199
MISC |
| jetbrains — teamcity |
In JetBrains TeamCity before 2021.1.2, email notifications could include unescaped HTML for XSS. |
2021-11-09 |
4.3 |
CVE-2021-43197
MISC |
| jetbrains — youtrack_mobile |
In JetBrains YouTrack Mobile before 2021.2, the client-side cache on iOS could contain sensitive information. |
2021-11-09 |
5 |
CVE-2021-43187
MISC |
| jetbrains — youtrack_mobile |
In JetBrains YouTrack Mobile before 2021.2, task hijacking on Android is possible. |
2021-11-09 |
5 |
CVE-2021-43190
MISC |
| jetbrains — youtrack_mobile |
JetBrains YouTrack Mobile before 2021.2, is missing the security screen on Android and iOS. |
2021-11-09 |
5 |
CVE-2021-43191
MISC |
| jetbrains — youtrack_mobile |
In JetBrains YouTrack Mobile before 2021.2, iOS URL scheme hijacking is possible. |
2021-11-09 |
5 |
CVE-2021-43192
MISC |
| legalweb — wp_dsgvo_tools |
WP DSGVO Tools (GDPR) <= 3.1.23 had an AJAX action, ‘admin-dismiss-unsubscribe‘, which lacked a capability check and a nonce check and was available to unauthenticated users, and did not check the post type when deleting unsubscription requests. As such, it was possible for an attacker to permanently delete an arbitrary post or page on the site by sending an AJAX request with the “action” parameter set to “admin-dismiss-unsubscribe” and the “id” parameter set to the post to be deleted. Sending such a request would move the post to the trash, and repeating the request would permanently delete the post in question. |
2021-11-05 |
6.4 |
CVE-2021-42359
MISC |
| loco_translate_project — loco_translate |
The Loco Translate WordPress plugin before 2.5.4 mishandles data inputs which get saved to a file, which can be renamed to an extension ending in .php, resulting in authenticated “translator” users being able to inject PHP code into files ending with .php in web accessible locations. |
2021-11-08 |
4 |
CVE-2021-24721
MISC |
| lua — lua |
Stack overflow in lua_resume of ldo.c in Lua Interpreter 5.1.0~5.4.4 allows attackers to perform a Denial of Service via a crafted script file. |
2021-11-09 |
4.3 |
CVE-2021-43519
MISC
MISC |
| mcafee — drive_encryption |
DLL Search Order Hijacking Vulnerability in McAfee Drive Encryption (MDE) prior to 7.3.0 HF2 (7.3.0.183) allows local users to execute arbitrary code and escalate privileges via execution from a compromised folder. |
2021-11-10 |
4.6 |
CVE-2021-31853
CONFIRM |
| mendix — mendix |
A vulnerability has been identified in Mendix Applications using Mendix 8 (All versions < V8.18.13), Mendix Applications using Mendix 9 (All versions < V9.6.2). Applications built with affected versions of Mendix Studio Pro do not properly control read access for certain client actions. This could allow authenticated attackers to retrieve the changedDate attribute of arbitrary objects, even when they don’t have read access to them. |
2021-11-09 |
4 |
CVE-2021-42026
MISC |
| mendix — mendix |
A vulnerability has been identified in Mendix Applications using Mendix 8 (All versions < V8.18.13), Mendix Applications using Mendix 9 (All versions < V9.6.2). Applications built with affected versions of Mendix Studio Pro do not properly control write access for certain client actions. This could allow authenticated attackers to manipulate the content of System.FileDocument objects in some cases, regardless whether they have write access to it. |
2021-11-09 |
6.8 |
CVE-2021-42025
MISC |
| meross — mss550x_firmware |
Meross Smart Wi-Fi 2 Way Wall Switch (MSS550X), on its 3.1.3 version and before, creates an open Wi-Fi Access Point without the required security measures in its initial setup. This could allow a remote attacker to obtain the Wi-Fi SSID as well as the password configured by the user from Meross app via Http/JSON plain request. |
2021-11-05 |
4.3 |
CVE-2021-3774
CONFIRM |
| microsoft — 365_apps |
Microsoft Access Remote Code Execution Vulnerability |
2021-11-10 |
6.8 |
CVE-2021-41368
MISC
MISC |
| microsoft — 365_apps |
Microsoft Excel Security Feature Bypass Vulnerability |
2021-11-10 |
6.8 |
CVE-2021-42292
MISC |
| microsoft — 365_apps |
Microsoft Word Remote Code Execution Vulnerability |
2021-11-10 |
6.9 |
CVE-2021-42296
MISC |
| microsoft — 365_apps |
Microsoft Excel Remote Code Execution Vulnerability |
2021-11-10 |
6.8 |
CVE-2021-40442
MISC |
| microsoft — edge |
Microsoft Edge (Chrome based) Spoofing on IE Mode |
2021-11-10 |
4.3 |
CVE-2021-41351
MISC |
| microsoft — exchange_server |
Microsoft Exchange Server Remote Code Execution Vulnerability |
2021-11-10 |
6.5 |
CVE-2021-42321
MISC |
| microsoft — exchange_server |
Microsoft Exchange Server Spoofing Vulnerability This CVE ID is unique from CVE-2021-42305. |
2021-11-10 |
4.3 |
CVE-2021-41349
MISC |
| microsoft — power_bi_report_server |
Power BI Report Server Spoofing Vulnerability |
2021-11-10 |
6.8 |
CVE-2021-41372
MISC |
| microsoft — remote_desktop |
Remote Desktop Protocol Client Information Disclosure Vulnerability |
2021-11-10 |
4.3 |
CVE-2021-38665
MISC |
| microsoft — visual_studio |
Diagnostics Hub Standard Collector Elevation of Privilege Vulnerability |
2021-11-10 |
4.6 |
CVE-2021-42277
MISC
MISC |
| microsoft — windows_10 |
Chakra Scripting Engine Memory Corruption Vulnerability |
2021-11-10 |
5.1 |
CVE-2021-42279
MISC |
| microsoft — windows_10 |
Windows Core Shell SI Host Extension Framework for Composable Shell Elevation of Privilege Vulnerability |
2021-11-10 |
4.6 |
CVE-2021-42286
MISC |
| microsoft — windows_10 |
NTFS Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-41367, CVE-2021-41370. |
2021-11-10 |
4.6 |
CVE-2021-42283
MISC |
| microsoft — windows_10 |
Windows Feedback Hub Elevation of Privilege Vulnerability |
2021-11-10 |
4.6 |
CVE-2021-42280
MISC
MISC |
| microsoft — windows_10 |
Windows Installer Elevation of Privilege Vulnerability |
2021-11-10 |
4.6 |
CVE-2021-41379
MISC
MISC |
| microsoft — windows_10 |
Windows Fast FAT File System Driver Elevation of Privilege Vulnerability |
2021-11-10 |
4.6 |
CVE-2021-41377
MISC |
| microsoft — windows_10 |
Windows Desktop Bridge Elevation of Privilege Vulnerability |
2021-11-10 |
4.6 |
CVE-2021-36957
MISC |
| microsoft — windows_10 |
NTFS Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-41367, CVE-2021-42283. |
2021-11-10 |
4.6 |
CVE-2021-41370
MISC |
| microsoft — windows_10 |
Credential Security Support Provider Protocol (CredSSP) Elevation of Privilege Vulnerability |
2021-11-10 |
4.6 |
CVE-2021-41366
MISC |
| microsoft — windows_10 |
Microsoft COM for Windows Remote Code Execution Vulnerability |
2021-11-10 |
6.5 |
CVE-2021-42275
MISC |
| microsoft — windows_10 |
Windows NTFS Remote Code Execution Vulnerability |
2021-11-10 |
6.5 |
CVE-2021-41378
MISC |
| microsoft — windows_10 |
Remote Desktop Client Remote Code Execution Vulnerability |
2021-11-10 |
6.8 |
CVE-2021-38666
MISC |
| microsoft — windows_10 |
Microsoft Windows Media Foundation Remote Code Execution Vulnerability |
2021-11-10 |
6.8 |
CVE-2021-42276
MISC |
| microsoft — windows_10 |
Windows Denial of Service Vulnerability |
2021-11-10 |
5 |
CVE-2021-41356
MISC |
| microsoft — windows_10 |
NTFS Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-41370, CVE-2021-42283. |
2021-11-10 |
4.6 |
CVE-2021-41367
MISC |
| microsoft — windows_server |
Active Directory Domain Services Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-42278, CVE-2021-42287, CVE-2021-42291. |
2021-11-10 |
6.5 |
CVE-2021-42282
MISC |
| microsoft — windows_server |
Active Directory Domain Services Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-42278, CVE-2021-42282, CVE-2021-42291. |
2021-11-10 |
6.5 |
CVE-2021-42287
MISC |
| microsoft — windows_server |
Active Directory Domain Services Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-42278, CVE-2021-42282, CVE-2021-42287. |
2021-11-10 |
6.5 |
CVE-2021-42291
MISC |
| microsoft — windows_server_2008 |
Active Directory Domain Services Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-42282, CVE-2021-42287, CVE-2021-42291. |
2021-11-10 |
6.5 |
CVE-2021-42278
MISC |
| nlnetlabs — routinator |
In NLnet Labs Routinator prior to 0.10.2, a validation run can be delayed significantly by an RRDP repository by not answering but slowly drip-feeding bytes to keep the connection alive. This can be used to effectively stall validation. While Routinator has a configurable time-out value for RRDP connections, this time-out was only applied to individual read or write operations rather than the complete request. Thus, if an RRDP repository sends a little bit of data before that time-out expired, it can continuously extend the time it takes for the request to finish. Since validation will only continue once the update of an RRDP repository has concluded, this delay will cause validation to stall, leading to Routinator continuing to serve the old data set or, if in the initial validation run directly after starting, never serve any data at all. |
2021-11-09 |
5 |
CVE-2021-43173
MISC |
| nlnetlabs — routinator |
NLnet Labs Routinator versions 0.9.0 up to and including 0.10.1, support the gzip transfer encoding when querying RRDP repositories. This encoding can be used by an RRDP repository to cause an out-of-memory crash in these versions of Routinator. RRDP uses XML which allows arbitrary amounts of white space in the encoded data. The gzip scheme compresses such white space extremely well, leading to very small compressed files that become huge when being decompressed for further processing, big enough that Routinator runs out of memory when parsing input data waiting for the next XML element. |
2021-11-09 |
5 |
CVE-2021-43174
MISC |
| nlnetlabs — routinator |
NLnet Labs Routinator prior to 0.10.2 happily processes a chain of RRDP repositories of infinite length causing it to never finish a validation run. In RPKI, a CA can choose the RRDP repository it wishes to publish its data in. By continuously generating a new child CA that only consists of another CA using a different RRDP repository, a malicious CA can create a chain of CAs of de-facto infinite length. Routinator prior to version 0.10.2 did not contain a limit on the length of such a chain and will therefore continue to process this chain forever. As a result, the validation run will never finish, leading to Routinator continuing to serve the old data set or, if in the initial validation run directly after starting, never serve any data at all. |
2021-11-09 |
5 |
CVE-2021-43172
MISC |
| nomacs — nomacs |
A buffer overflow in Nomacs v3.15.0 allows attackers to cause a denial of service (DoS) via a crafted MNG file. |
2021-11-10 |
4.3 |
CVE-2020-23884
MISC
MISC
MISC |
| online_event_booking_and_reservation_system_project — online_event_booking_and_reservation_system |
An HTML injection vulnerability exists in Sourcecodester Online Event Booking and Reservation System in PHP/MySQL via the msg parameter to /event-management/index.php. An attacker can leverage this vulnerability in order to change the visibility of the website. Once the target user clicks on a given link he will display the content of the HTML code of the attacker’s choice. |
2021-11-05 |
4.3 |
CVE-2021-42663
MISC
MISC |
| opnsense — opnsense |
A Cross-site scripting (XSS) vulnerability was discovered in OPNsense before 21.7.4 via the LDAP attribute return in the authentication tester. |
2021-11-08 |
4.3 |
CVE-2021-42770
CONFIRM
MISC |
| oppia — oppia |
Oppia 3.1.4 does not verify that certain URLs are valid before navigating to them. |
2021-11-08 |
5.8 |
CVE-2021-41733
MISC |
| phoenix_media_rename_project — phoenix_media_rename |
The Phoenix Media Rename WordPress plugin before 3.4.4 does not have capability checks in its phoenix_media_rename AJAX action, which could allow users with Author roles to rename any uploaded media files, including ones they do not own. |
2021-11-08 |
4 |
CVE-2021-24816
MISC |
| php_event_calendar_project — php_event_calendar |
PHP Event Calendar through 2021-11-04 allows persistent cross-site scripting (XSS), as demonstrated by the /server/ajax/events_manager.php title parameter. This can be exploited by an adversary in multiple ways, e.g., to perform actions on the page in the context of other users, or to deface the site. |
2021-11-08 |
4.3 |
CVE-2021-42078
MISC
MISC |
| phpjabbers — fundraising_script |
Stivasoft (Phpjabbers) Fundraising Script v1.0 was discovered to contain a cross-site scripting (XSS) vulnerability via the pjActionLoadCss function. |
2021-11-05 |
4.3 |
CVE-2020-22222
MISC |
| phpjabbers — fundraising_script |
Stivasoft (Phpjabbers) Fundraising Script v1.0 was discovered to contain a cross-site scripting (XSS) vulnerability via the pjActionPreview function. |
2021-11-05 |
4.3 |
CVE-2020-22224
MISC |
| pomerium — pomerium |
Pomerium is an open source identity-aware access proxy. In affected versions changes to the OIDC claims of a user after initial login are not reflected in policy evaluation when using `allowed_idp_claims` as part of policy. If using `allowed_idp_claims` and a user’s claims are changed, Pomerium can make incorrect authorization decisions. This issue has been resolved in v0.15.6. For users unable to upgrade clear data on `databroker` service by clearing redis or restarting the in-memory databroker to force claims to be updated. |
2021-11-05 |
6.5 |
CVE-2021-41230
CONFIRM
MISC |
| post_content_xmlrpc_project — post_content_xmlrpc |
The Post Content XMLRPC WordPress plugin through 1.0 does not sanitise or escape multiple GET/POST parameters before using them in SQL statements in the admin dashboard, leading to an authenticated SQL Injections |
2021-11-08 |
6.5 |
CVE-2021-24629
MISC
MISC |
| publishpress — post_expirator |
The Post Expirator WordPress plugin before 2.6.0 does not have proper capability checks in place, which could allow users with a role as low as Contributor to schedule deletion of arbitrary posts. |
2021-11-08 |
4 |
CVE-2021-24783
MISC |
| remoteclinic — remote_clinic |
Multiple Cross Site Scripting (XSS) vulnerabilities exists in Remote Clinic v2.0 in (1) patients/register-patient.php via the (a) Contact, (b) Email, (c) Weight, (d) Profession, (e) ref_contact, (f) address, (g) gender, (h) age, and (i) serial parameters; in (2) patients/edit-patient.php via the (a) Contact, (b) Email, (c) Weight, Profession, (d) ref_contact, (e) address, (f) serial, (g) age, and (h) gender parameters; in (3) staff/edit-my-profile.php via the (a) Title, (b) First Name, (c) Last Name, (d) Skype, and (e) Address parameters; and in (4) clinics/settings.php via the (a) portal_name, (b) guardian_short_name, (c) guardian_name, (d) opening_time, (e) closing_time, (f) access_level_5, (g) access_level_4, (h) access_level_ 3, (i) access_level_2, (j) access_level_1, (k) currency, (l) mobile_number, (m) address, (n) patient_contact, (o) patient_address, and (p) patient_email parameters. |
2021-11-05 |
4.3 |
CVE-2021-39416
MISC
MISC
MISC |
| samsung — samsung_pass |
Improper authentication in Samsung Pass prior to 3.0.02.4 allows to use app without authentication when lockscreen is unlocked. |
2021-11-05 |
6.8 |
CVE-2021-25505
MISC |
| sap — abap_platform_kernel |
SAP ABAP Platform Kernel – versions 7.77, 7.81, 7.85, 7.86, does not perform necessary authorization checks for an authenticated business user, resulting in escalation of privileges. That means this business user is able to read and modify data beyond the vulnerable system. However, the attacker can neither significantly reduce the performance of the system nor stop the system. |
2021-11-10 |
5.5 |
CVE-2021-40501
MISC
MISC |
| sap — commerce |
SAP Commerce – versions 2105.3, 2011.13, 2005.18, 1905.34, does not perform necessary authorization checks for an authenticated user, resulting in escalation of privileges. Authenticated attackers will be able to access and edit data from B2B units they do not belong to. |
2021-11-10 |
6.5 |
CVE-2021-40502
MISC
MISC |
| sap — netweaver_application_server_for_abap |
A certain template role in SAP NetWeaver Application Server for ABAP and ABAP Platform – versions 700, 701, 702, 710, 711, 730, 731, 740, 750, 751, 752, 753, 754, 755, 756, contains transport authorizations, which exceed expected display only permissions. |
2021-11-10 |
4 |
CVE-2021-40504
MISC
MISC |
| schreikasten_project — schreikasten |
The Schreikasten WordPress plugin through 0.14.18 does not sanitise or escape the id GET parameter before using it in SQL statements in the comments dashboard from various actions, leading to authenticated SQL Injections which can be exploited by users as low as author |
2021-11-08 |
6.5 |
CVE-2021-24630
MISC
MISC |
| science-miner — pdf2xml |
pdf2xml v2.0 was discovered to contain a memory leak in the function TextPage::testLinkedText. |
2021-11-10 |
5 |
CVE-2020-23876
MISC
MISC |
| science-miner — pdf2xml |
A NULL pointer dereference in the function TextPage::restoreState of pdf2xml v2.0 allows attackers to cause a denial of service (DoS). |
2021-11-10 |
5 |
CVE-2020-23872
MISC
MISC |
| seopanel — seo_panel |
Multiple Cross Site Scripting (XSS) vulnerabilities exits in SEO Panel v4.8.0 via the (1) to_time parameter in (a) backlinks.php, (b) analytics.php, (c) log.php, (d) overview.php, (e) pagespeed.php, (f) rank.php, (g) review.php, (h) saturationchecker.php, (i) social_media.php, and (j) reports.php; the (2) from_time parameter in (a) backlinks.php, (b) analytics.php, (c) log.php, (d) overview.php, (e) pagespeed.php, (f) rank.php, (g) review.php, (h) saturationchecker.php, (i) social_media.php, (j) webmaster-tools.php, and (k) reports.php; the (3) order_col parameter in (a) analytics.php, (b) review.php, (c) social_media.php, and (d) webmaster-tools.php; and the (4) pageno parameter in (a) alerts.php, (b) log.php, (c) keywords.php, (d) proxy.php, (e) searchengine.php, and (f) siteauditor.php. |
2021-11-05 |
4.3 |
CVE-2021-39413
MISC |
| servicetonic — servicetonic |
Blind SQL injection in the login form in ServiceTonic Helpdesk software < 9.0.35937 allows attacker to exfiltrate information via specially crafted HQL-compatible time-based SQL queries. |
2021-11-08 |
5 |
CVE-2021-28022
MISC
MISC |
| shareaholic — similar_posts |
The Similar Posts WordPress plugin through 3.1.5 allow high privilege users to execute arbitrary PHP code in an hardened environment (ie with DISALLOW_FILE_EDIT, DISALLOW_FILE_MODS and DISALLOW_UNFILTERED_HTML set to true) via the ‘widget_rrm_similar_posts_condition’ widget setting of the plugin. |
2021-11-08 |
6 |
CVE-2021-24537
MISC |
| shopping_portal_project — shopping_portal |
Multiple Cross Site Scripting (XSS) vulnerabilities exists in PHPGurukul Shopping v3.1 via the (1) callback parameter in (a) server_side/scripts/id_jsonp.php, (b) server_side/scripts/jsonp.php, and (c) scripts/objects_jsonp.php, the (2) value parameter in examples_support/editable_ajax.php, and the (3) PHP_SELF parameter in captcha/index.php. |
2021-11-05 |
4.3 |
CVE-2021-39412
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). When processing a DHCP OFFER message, the DHCP client application does not validate the length of the Vendor option(s), leading to Denial-of-Service conditions. (FSMD-2021-0008) |
2021-11-09 |
5 |
CVE-2021-31881
MISC
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). FTP server does not properly validate the length of the “MKD/XMKD” command, leading to stack-based buffer overflows. This may result in Denial-of-Service conditions and Remote Code Execution. (FSMD-2021-0018) |
2021-11-09 |
6.5 |
CVE-2021-31888
MISC
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus ReadyStart V4 (All versions < V4.1.1), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). ICMP echo packets with fake IP options allow sending ICMP echo reply messages to arbitrary hosts on the network. (FSMD-2021-0004) |
2021-11-09 |
5 |
CVE-2021-31344
MISC
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus ReadyStart V4 (All versions < V4.1.1), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). TFTP server application allows for reading the contents of the TFTP memory buffer via sending malformed TFTP commands. (FSMD-2021-0009) |
2021-11-09 |
5 |
CVE-2021-31885
MISC
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). FTP server does not properly validate the length of the “PWD/XPWD” command, leading to stack-based buffer overflows. This may result in Denial-of-Service conditions and Remote Code Execution. (FSMD-2021-0016) |
2021-11-09 |
6.5 |
CVE-2021-31887
MISC
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). When processing a DHCP ACK message, the DHCP client application does not validate the length of the Vendor option(s), leading to Denial-of-Service conditions. (FSMD-2021-0013) |
2021-11-09 |
5 |
CVE-2021-31883
MISC
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). The total length of an UDP payload (set in the IP header) is unchecked. This may lead to various side effects, including Information Leak and Denial-of-Service conditions, depending on a user-defined applications that runs on top of the UDP protocol. (FSMD-2021-0006) |
2021-11-09 |
6.4 |
CVE-2021-31345
MISC
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus ReadyStart V4 (All versions < V4.1.1), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). The total length of an ICMP payload (set in the IP header) is unchecked. This may lead to various side effects, including Information Leak and Denial-of-Service conditions, depending on the network buffer organization in memory. (FSMD-2021-0007) |
2021-11-09 |
6.4 |
CVE-2021-31346
MISC
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). The DHCP client application does not validate the length of the Domain Name Server IP option(s) (0x06) when processing DHCP ACK packets. This may lead to Denial-of-Service conditions. (FSMD-2021-0011) |
2021-11-09 |
5 |
CVE-2021-31882
MISC
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). Malformed TCP packets with a corrupted SACK option leads to Information Leaks and Denial-of-Service conditions. (FSMD-2021-0015) |
2021-11-09 |
6.4 |
CVE-2021-31889
MISC
MISC |
| siemens — capital_vstar |
A vulnerability has been identified in APOGEE MBC (PPC) (BACnet) (All versions), APOGEE MBC (PPC) (P2 Ethernet) (All versions), APOGEE MEC (PPC) (BACnet) (All versions), APOGEE MEC (PPC) (P2 Ethernet) (All versions), APOGEE PXC Compact (BACnet) (All versions), APOGEE PXC Compact (P2 Ethernet) (All versions), APOGEE PXC Modular (BACnet) (All versions), APOGEE PXC Modular (P2 Ethernet) (All versions), Capital VSTAR (All versions), Nucleus NET (All versions), Nucleus ReadyStart V3 (All versions < V2017.02.4), Nucleus ReadyStart V4 (All versions < V4.1.1), Nucleus Source Code (All versions), TALON TC Compact (BACnet) (All versions), TALON TC Modular (BACnet) (All versions). The total length of an TCP payload (set in the IP header) is unchecked. This may lead to various side effects, including Information Leak and Denial-of-Service conditions, depending on the network buffer organization in memory. (FSMD-2021-0017) |
2021-11-09 |
6.4 |
CVE-2021-31890
MISC
MISC |
| siemens — climatix_pol909_firmware |
A vulnerability has been identified in Climatix POL909 (AWM module) (All versions < V11.34). The web server of affected devices transmits data without TLS encryption. This could allow an unauthenticated remote attacker in a man-in-the-middle position to read sensitive data, such as administrator credentials, or modify data in transit. |
2021-11-09 |
5.8 |
CVE-2021-40366
MISC |
| siemens — simatic_pcs_7 |
A vulnerability has been identified in SIMATIC PCS 7 V8.2 and earlier (All versions), SIMATIC PCS 7 V9.0 (All versions), SIMATIC PCS 7 V9.1 (All versions), SIMATIC WinCC V15 and earlier (All versions), SIMATIC WinCC V16 (All versions), SIMATIC WinCC V17 (All versions), SIMATIC WinCC V7.4 and earlier (All versions), SIMATIC WinCC V7.5 (All versions < V7.5 SP2 Update 5). When downloading files, the affected systems do not properly neutralize special elements within the pathname. An attacker could then cause the pathname to resolve to a location outside of the restricted directory on the server and read unexpected critical files. |
2021-11-09 |
5 |
CVE-2021-40359
MISC |
| siemens — simatic_pcs_7 |
A vulnerability has been identified in SIMATIC PCS 7 V8.2 and earlier (All versions), SIMATIC PCS 7 V9.0 (All versions), SIMATIC PCS 7 V9.1 (All versions), SIMATIC WinCC V15 and earlier (All versions), SIMATIC WinCC V16 (All versions), SIMATIC WinCC V17 (All versions), SIMATIC WinCC V7.4 and earlier (All versions), SIMATIC WinCC V7.5 (All versions < V7.5 SP2 Update 5). The affected systems store sensitive information in log files. An attacker with access to the log files could publicly expose the information or reuse it to develop further attacks on the system. |
2021-11-09 |
5 |
CVE-2021-40364
MISC |
| speex — speex |
A stack buffer overflow in speexenc.c of Speex v1.2 allows attackers to cause a denial of service (DoS) via a crafted WAV file. |
2021-11-10 |
4.3 |
CVE-2020-23904
MISC |
| tailor_management_system_project — tailor_management_system |
Multiple Cross Site Scripting (XSS) vulnerabilities exist in SourceCodester Tailor Management 1.0 via the (1) eid parameter in (a) partedit.php and (b) customeredit.php, the (2) id parameter in (a) editmeasurement.php and (b) addpayment.php, and the (3) error parameter in index.php. |
2021-11-08 |
4.3 |
CVE-2021-40260
MISC |
| thruk — thruk |
Thruk 2.40-2 allows /thruk/#cgi-bin/extinfo.cgi?type=2&host={HOSTNAME]&service={SERVICENAME]&backend={BACKEND] Reflected XSS via the host or service parameter. An attacker could inject arbitrary JavaScript into extinfo.cgi. The malicious payload would be triggered every time an authenticated user browses the page containing it. |
2021-11-09 |
4.3 |
CVE-2021-35489
MISC
MISC |
| thruk — thruk |
Thruk 2.40-2 allows /thruk/#cgi-bin/status.cgi?style=combined&title={TITLE] Reflected XSS via the host or title parameter. An attacker could inject arbitrary JavaScript into status.cgi. The payload would be triggered every time an authenticated user browses the page containing it. |
2021-11-09 |
4.3 |
CVE-2021-35488
MISC
MISC |
| tipsandtricks-hq — simple_download_monitor |
The Simple Download Monitor WordPress plugin before 3.9.6 allows users with a role as low as Contributor to remove thumbnails from downloads they do not own, even if they cannot normally edit the download. |
2021-11-08 |
4 |
CVE-2021-24698
MISC |
| tipsandtricks-hq — simple_download_monitor |
The Simple Download Monitor WordPress plugin before 3.9.5 does not escape the 1) sdm_active_tab GET parameter and 2) sdm_stats_start_date/sdm_stats_end_date POST parameters before outputting them back in attributes, leading to Reflected Cross-Site Scripting issues |
2021-11-08 |
4.3 |
CVE-2021-24697
MISC |
| tipsandtricks-hq — simple_download_monitor |
The Simple Download Monitor WordPress plugin before 3.9.5 does not escape the “File Thumbnail” post meta before outputting it in some pages, which could allow users with a role as low as Contributor to perform Stored Cross-Site Scripting attacks. Given the that XSS is triggered even when the Download is in a review state, contributor could make JavaScript code execute in a context of a reviewer such as admin and make them create a rogue admin account, or install a malicious plugin |
2021-11-08 |
6 |
CVE-2021-24693
MISC |
| tipsandtricks-hq — simple_download_monitor |
The Simple Download Monitor WordPress plugin before 3.9.6 saves logs in a predictable location, and does not have any authentication or authorisation in place to prevent unauthenticated users to download and read the logs containing Sensitive Information such as IP Addresses and Usernames |
2021-11-08 |
5 |
CVE-2021-24695
MISC |
| unlimited_popups_project — unlimited_popups |
The Unlimited PopUps WordPress plugin through 4.5.3 does not sanitise or escape the did GET parameter before using it in a SQL statement, available to users as low as editor, leading to an authenticated SQL Injection |
2021-11-08 |
6.5 |
CVE-2021-24631
MISC
MISC |
| vfront — vfront |
Multiple Cross Site Scripting (XSS) vulnerabilities exist in VFront 0.99.5 via the (1) s parameter in search_all.php and the (2) msg parameter in add.attach.php. |
2021-11-08 |
4.3 |
CVE-2021-39420
MISC |
| vim — vim |
vim is vulnerable to Stack-based Buffer Overflow |
2021-11-05 |
4.6 |
CVE-2021-3928
CONFIRM
MISC
FEDORA |
| vim — vim |
vim is vulnerable to Heap-based Buffer Overflow |
2021-11-05 |
6.8 |
CVE-2021-3927
CONFIRM
MISC
FEDORA |
| vmware — spring_cloud_gateway |
Applications using Spring Cloud Gateway are vulnerable to specifically crafted requests that could make an extra request on downstream services. Users of affected versions should apply the following mitigation: 3.0.x users should upgrade to 3.0.5+, 2.2.x users should upgrade to 2.2.10.RELEASE or newer. |
2021-11-08 |
4 |
CVE-2021-22051
MISC |
| wclovers — frontend_manager_for_woocommerce_along_with_bookings_subscription_listings_compatible |
The WCFM – Frontend Manager for WooCommerce along with Bookings Subscription Listings Compatible WordPress plugin before 6.5.12, when used in combination with another WCFM – WooCommerce Multivendor plugin such as WCFM – WooCommerce Multivendor Marketplace, does not escape the withdrawal_vendor parameter before using it in a SQL statement, allowing low privilege users such as Subscribers to perform SQL injection attacks |
2021-11-08 |
6.5 |
CVE-2021-24835
MISC |
| web-dorado — spidercatalog |
The SpiderCatalog WordPress plugin through 1.7.3 does not sanitise or escape the ‘parent’ and ‘ordering’ parameters from the admin dashboard before using them in a SQL statement, leading to a SQL injection when adding a category |
2021-11-08 |
6.5 |
CVE-2021-24625
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A buffer overflow in WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted JPG file. Related to Data from Faulting Address is used as one or more arguments in a subsequent Function Call starting at JPGCodec+0x753648. |
2021-11-10 |
4.3 |
CVE-2020-23890
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV in Editor+0x5d15 of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tga file. |
2021-11-10 |
4.3 |
CVE-2020-23901
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV in Editor+0x576b of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tiff file. |
2021-11-10 |
4.3 |
CVE-2020-23896
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV in Editor!TMethodImplementationIntercept+0x3c3682 of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tiff file. |
2021-11-10 |
4.3 |
CVE-2020-23893
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV in Editor+0x5cd7 of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tiff file. |
2021-11-10 |
4.3 |
CVE-2020-23891
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV in Editor!TMethodImplementationIntercept+0x53f6c3 of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted psd file. |
2021-11-10 |
4.3 |
CVE-2020-23888
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV in ntdll!RtlpCoalesceFreeBlocks+0x268 of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tiff file. |
2021-11-10 |
4.3 |
CVE-2020-23894
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV starting at Editor!TMethodImplementationIntercept+0x4189c6 of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted ico file. |
2021-11-10 |
4.3 |
CVE-2020-23889
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A buffer overflow in WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tga file. Related to Data from Faulting Address may be used as a return value starting at Editor!TMethodImplementationIntercept+0x528a3. |
2021-11-10 |
4.3 |
CVE-2020-23902
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV in Editor+0x76af of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tiff file. |
2021-11-10 |
4.3 |
CVE-2020-23895
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A buffer overflow in WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tga file. Related to Data from Faulting Address controls Code Flow starting at Editor!TMethodImplementationIntercept+0x57a3b. |
2021-11-10 |
4.3 |
CVE-2020-23900
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV in Editor+0x5f91 of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tga file. |
2021-11-10 |
4.3 |
CVE-2020-23899
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV in Editor+0x5ea2 of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tga file. |
2021-11-10 |
4.3 |
CVE-2020-23898
MISC
MISC |
| wildbit-soft — wildbit_viewer |
A User Mode Write AV in Editor!TMethodImplementationIntercept+0x54dcec of WildBit Viewer v6.6 allows attackers to cause a denial of service (DoS) via a crafted tga file. |
2021-11-10 |
4.3 |
CVE-2020-23897
MISC
MISC |
| wow-company — wow_forms |
The Wow Forms WordPress plugin through 3.1.3 does not sanitise or escape a ‘did’ GET parameter before using it in a SQL statement, when deleting a form in the admin dashboard, leading to an authenticated SQL injection |
2021-11-08 |
6.5 |
CVE-2021-24628
MISC
MISC |
| wp-buy — visitor_traffic_real_time_statistics |
The Visitor Traffic Real Time Statistics WordPress plugin before 3.9 does not validate and escape user input passed to the today_traffic_index AJAX action (available to any authenticated users) before using it in a SQL statement, leading to an SQL injection issue |
2021-11-08 |
6.5 |
CVE-2021-24829
MISC |
| wp_seo_redirect_301_project — wp_seo_redirect_301 |
The WP SEO Redirect 301 WordPress plugin before 2.3.2 does not have CSRF in place when deleting redirects, which could allow attackers to make a logged in admin delete them via a CSRF attack |
2021-11-08 |
4.3 |
CVE-2021-24832
MISC |
| wp_survey_plus_project — wp_survey_plus |
The WP Survey Plus WordPress plugin through 1.0 does not have any authorisation and CSRF checks in place in its AJAX actions, allowing any user to call them and add/edit/delete Surveys. Furthermore, due to the lack of sanitization in the Surveys’ Title, this could also lead to Stored Cross-Site Scripting issues |
2021-11-08 |
4.3 |
CVE-2021-24801
MISC |
| wpaffiliatemanager — affiliates_manager |
The Affiliates Manager WordPress plugin before 2.8.7 does not validate the orderby parameter before using it in an SQL statement in the admin dashboard, leading to an SQL Injection issue |
2021-11-08 |
6.5 |
CVE-2021-24844
CONFIRM
MISC |
| xorux — lpar2rrd |
A password mismanagement situation exists in XoruX LPAR2RRD and STOR2RRD before 7.30 because cleartext information is present in HTML password input fields in the device properties. (Viewing the passwords requires configuring a web browser to display HTML password input fields.) |
2021-11-08 |
4.3 |
CVE-2021-42370
CONFIRM
CONFIRM |
by Contributed | Nov 14, 2021 | Technology
This article is contributed. See the original author and article here.
Summary: This article discusses using TF902 as a quick workaround to bring up your SQL Server service if it fails to be started due to post upgrade script failure after installing SQL Server patch. Further troubleshooting steps to address the post upgrade script failure have been discussed in later part of this article.
Please be noted that it is not suggested to keep your SQL Server service in this state for long since your SQL Server is in an incomplete patch installation status and considered instable for your production environment. This is because part of your SQL DLL files, MSP files or related registry key record might have already been upgraded while a few other files or metadata are not upgraded.
Why We Need To Run Post Upgrade Script After SQL Patch?
——————————————————————
After you have finished most part of installing the SQL patch (the scenarioengine.exe process and a few other related SQL and Windows process finished the change made to MSP file, registry key, and DLL files), SQL Server service (sqlservr.exe) still needs to perform another step – to run a few post upgrade TSQL scripts – to successfully complete the change made by patch installation. This is because the patch installation process mainly makes change to the related MSP files, registry key, and DLL files. We still need to apply a few remaining changes made in DLL into SQL database level by running a few system TSQL scripts. Major part of these TSQL scripts are stored in the ‘Install’ folder for your SQL instance while another part of them are encrypted (i.e. C:Program FilesMicrosoft SQL ServerMSSQL15.MSSQLSERVERMSSQLInstall). If the post upgrade script cannot be successfully finished , SQL Server service cannot be started successfully after the patch as the system databases’ status are not ready to be started on service startup process.
Symptom
======
After installing SQL Patch, your SQL Server service cannot be started.
SQL Server service can still generate new ERROR LOG on starting up attempt.
In the latest SQL ERROR LOG file, you found below error as ‘Script level upgrade for database ‘**’ failed’ indicating that SQL Server failed to perform the script level upgrade for a specific system database and caused subsequent shut down(Below are sample testing error from my LAB when reproducing the same issue)
2021-10-14 11:27:02.98 spid7s Error: 912, Severity: 21, State: 2.
2021-10-14 11:27:02.98 spid7s Script level upgrade for database ‘%’ failed because upgrade step ‘%’ encountered error 3930, state 1, severity 16. This is a serious error condition which might interfere with regular operation and the database will be taken offline. If the error happened during upgrade of the ‘master’ database, it will prevent the entire SQL Server instance from starting. Examine the previous errorlog entries for errors, take the appropriate corrective actions and re-start the database so that the script upgrade steps run to completion.
2021-10-14 11:27:02.98 spid7s Error: 3417, Severity: 21, State: 3.
2021-10-14 11:27:02.99 spid7s Cannot recover the master database. SQL Server is unable to run. Restore master from a full backup, repair it, or rebuild it. For more information about how to rebuild the master database, see SQL Server Books Online.
2021-10-14 11:27:02.99 spid7s SQL Server shutdown has been initiated
Quick Workaround To Bring Up SQL Service(Not Suggested to Keep it for Long)
=====================================================
We can add trace flag 902 to SQL Server service startup parameter to skip the script upgrade process in order to bring up your SQL Server service.
However, we suggest to resolve the failure for finishing the post upgrade script as we cannot leave SQL Server service in this state with TF902 for long. It is an incomplete upgrade state and considered unstable. This is because part of your DLL files might have already been upgraded while a few other files or metadata are not upgraded.
Further Troubleshooting Steps for Post Upgrade Script Failure
=========================================
The failure of post upgrade script can be caused by issue at database level in finishing the scripts or failure at patch installation level.
The latter indicates that the post upgrade failure is actually a consequence of an earlier exception in patch installation phase rather than the root cause of the patch installation failure. To go further, we need to investigate the actual exception that causes the subsequent failure.
Phase 1: Directly check the error and failed script steps for post upgrade script failure issue
1. As the post upgrade script will also be performed at the end of the patch installation process, you can check the latest SQL Setup Bootstrap log folder for ERRORLOG file details to see in which step and in which script do we encounter the error.
One of the common causes can be an orphaned SQL login which cannot be dropped and recreated when running a few of these post upgrade scripts.
2. If we don’t have the detailed ERRORLOG that records the script upgrade failure details, we can find a down time , remove trace flag 902 from SQL startup parameter and add trace flag 3601 to SQL Server startup parameter. Then we can try to start SQL Server service to reproduce the issue. Trace flag 3601 will dump script level upgrade details to the SQL Error Log. This is a trace flag used by Microsoft for internal troubleshooting purpose. Please use it under instruction and avoid using it in your PRODUCTION environment. Alternatively, we can configure X-event on service startup to check the errors and TSQL script details when we reproduce the issue. Please be noted that part of these scripts are encrypted.
Phase 2: Check the Setup Bootstrap logs for more details of the exception on SQL Server patch installation process
If the post upgrade script is actually a consequence of failure encountered during SQL patch installation process , then the issue is not at database level but patch installation phase. We need to investigate the exception encountered on patch installation process in order to address the issue.
If this is the case, check the ‘Detials.txt’ and other logs on the Setup Bootstrap ‘Log’ folder for this issued patch installation and investigate further.(Default path: “C:Program FilesMicrosoft SQL Server<YourSQLVersion>Setup BootstrapLog<YourIssuedPatchInstallationTime>”)
In some simple scenarios, minor failure can be caused by file in use or lack of permission issue and can be quickly resolved by ‘Repair’ option in ‘setup.exe’ program to repair the corrupted patch installation.
DISCLAIMER : THIS CODE AND INFORMATION IS PROVIDED “AS IS” WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE.
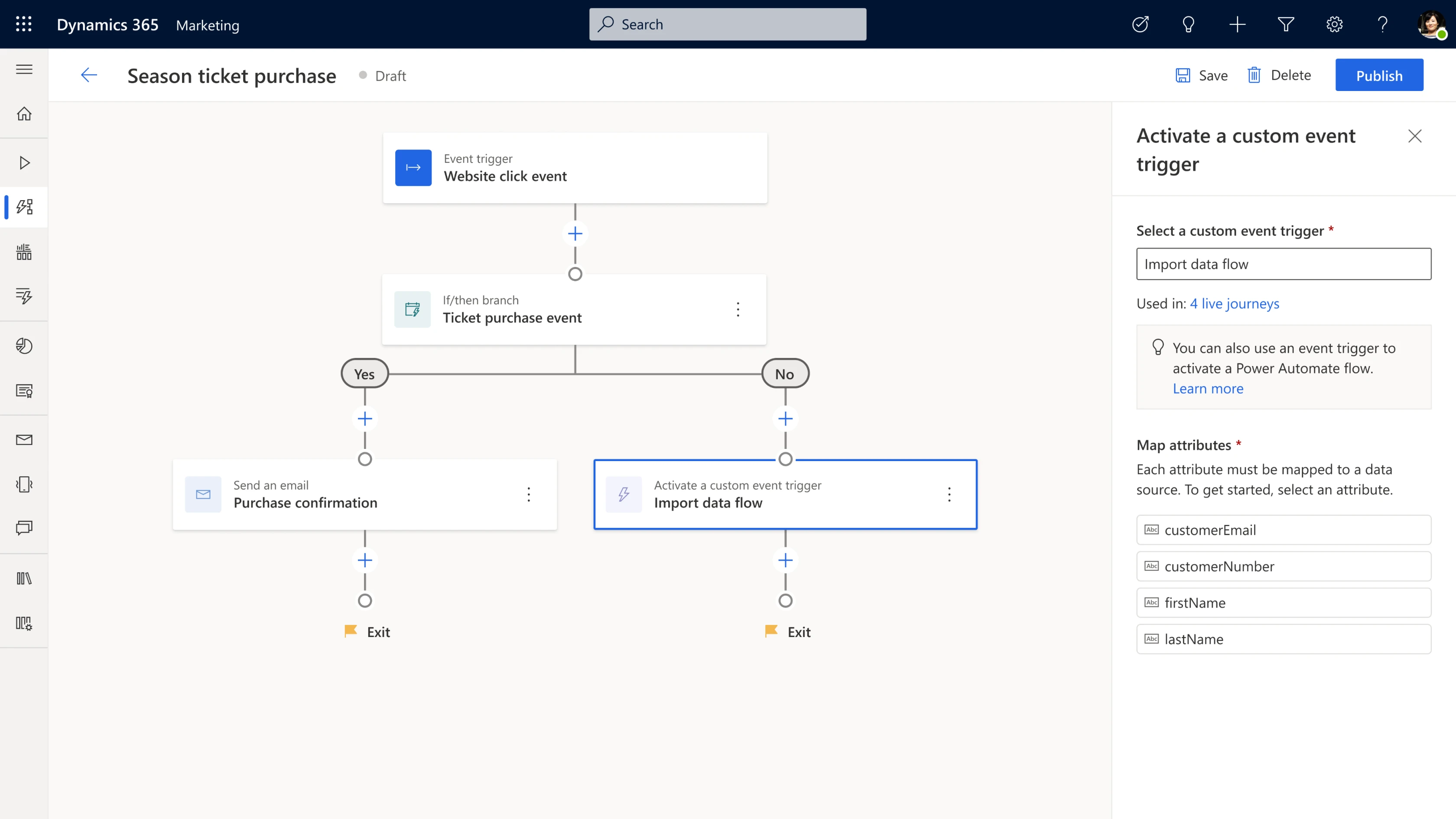

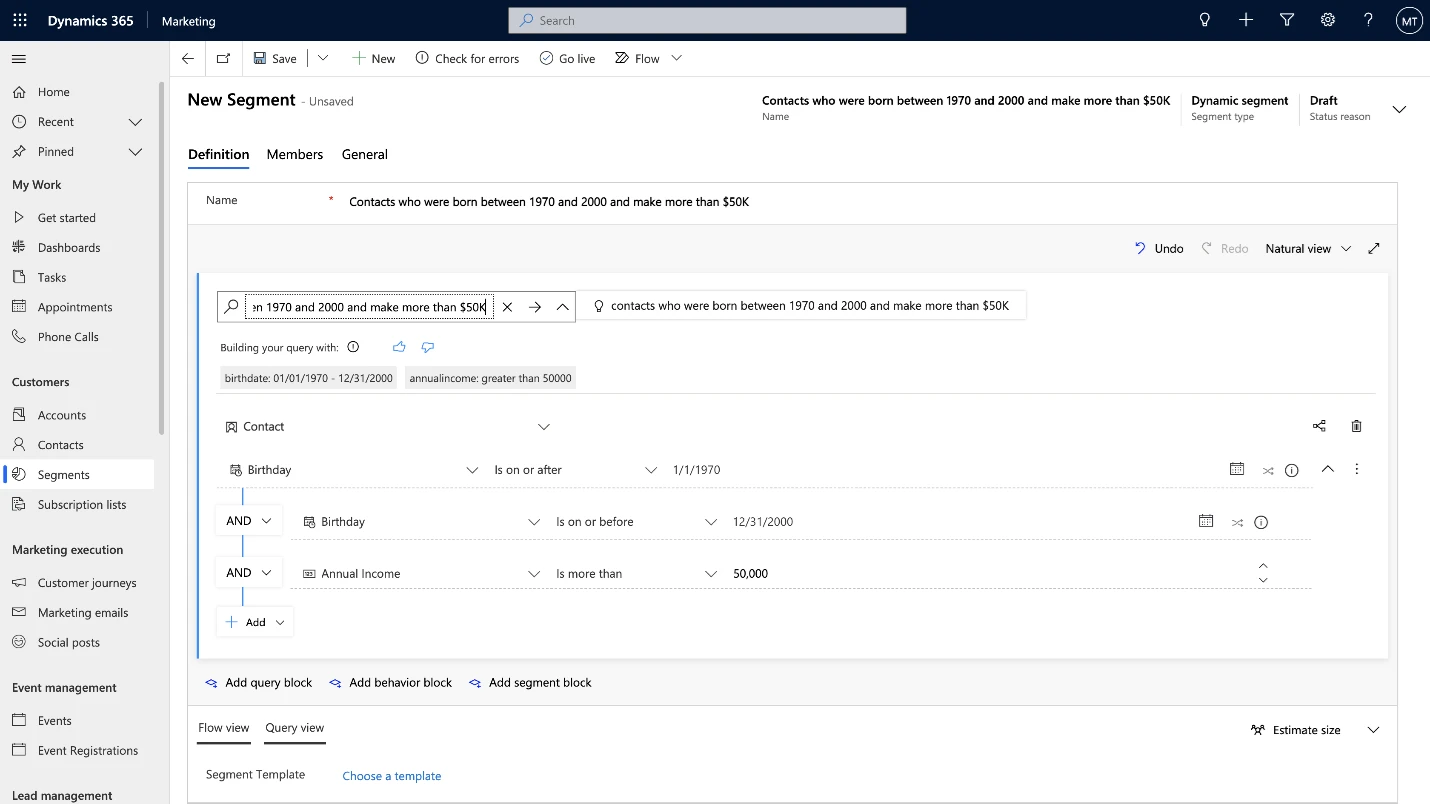
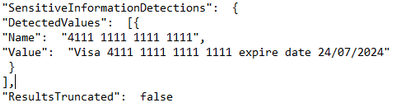
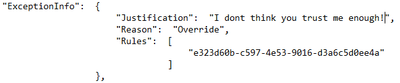
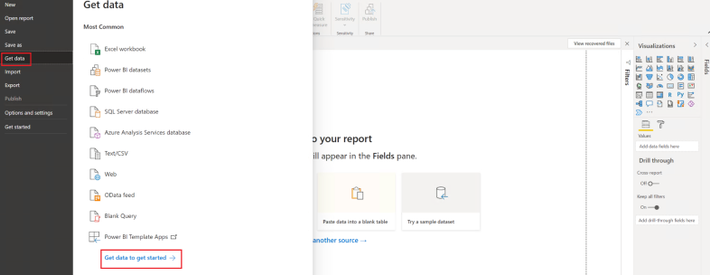
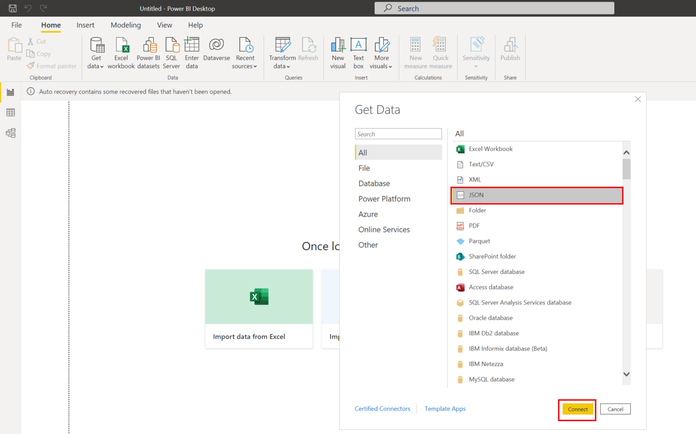
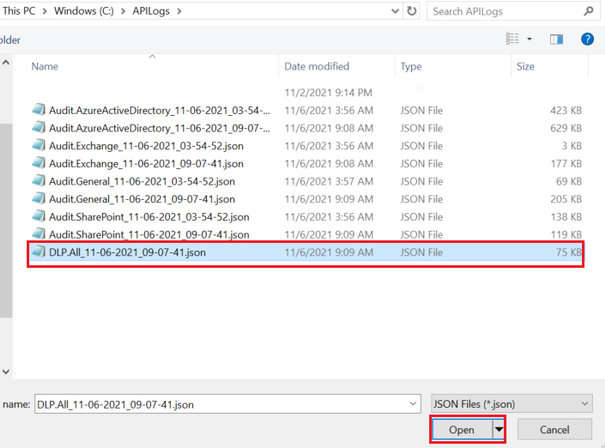
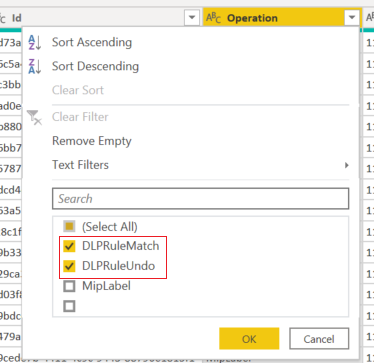
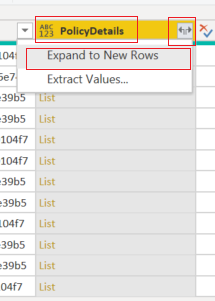
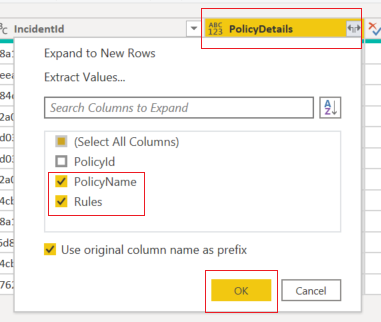
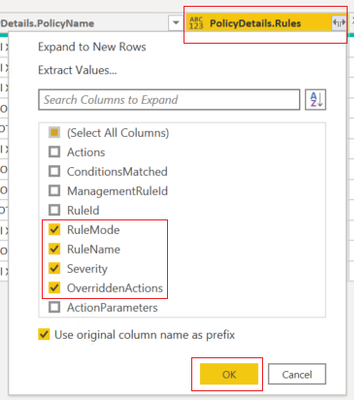
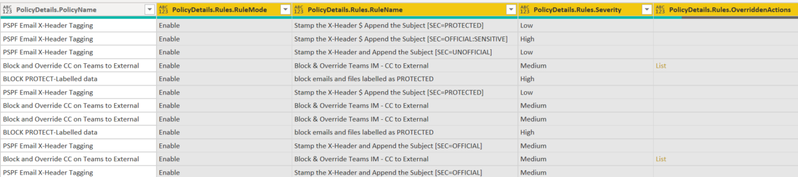
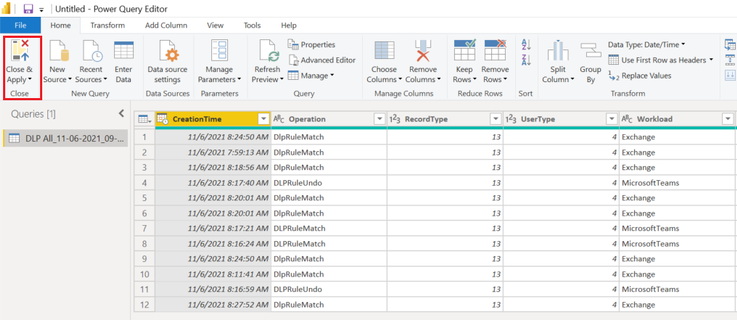
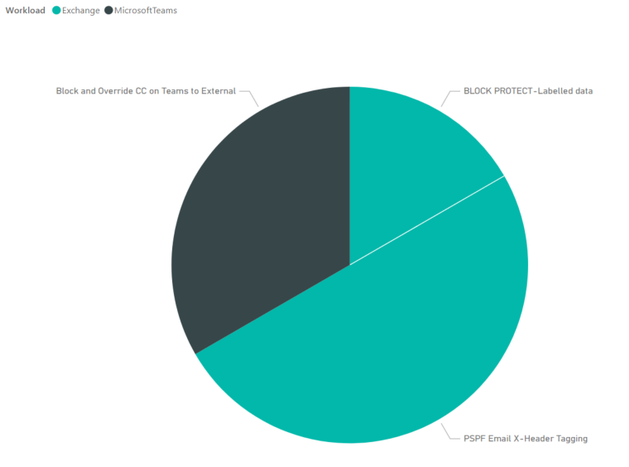
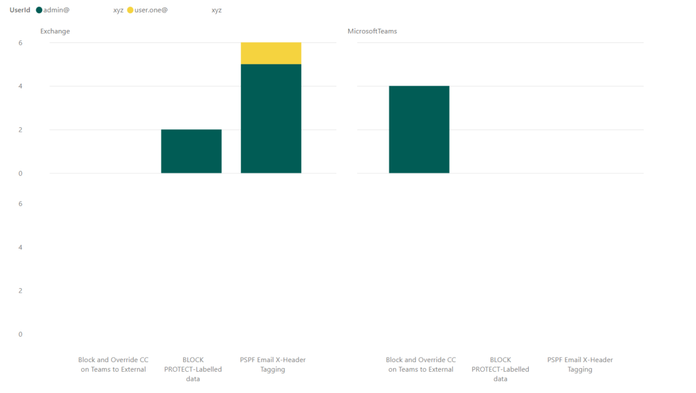
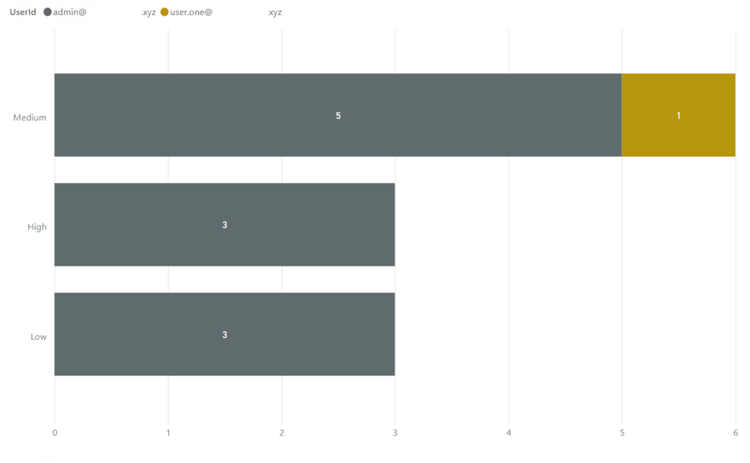


Recent Comments