Change. Adapt. Grow. Words we have had to embrace over the past 15 months as we’ve had to change the way we do business. As we start to emerge from the pandemic’s isolation and restrictions, we’re entering a world of a new normal. As consumers, our expectations are higher. To meet ever-changing customer expectations, successful businesses are constantly going through the change, adapt, and grow cycle, especially when it comes to customer experience and virtual events. Many experts project that in-person events will gradually return but the prominence of virtual events is here to stay. And with that comes exciting new opportunities to elevate customer experiences.
To help businesses embrace those opportunities we are announcing the availability of enhanced integration of Microsoft Teams and Microsoft Dynamics 365 Marketing.
We are also announcing a special offer for Microsoft Teams webinar customers with commercial Office 365 E3/E5 or Microsoft 365 E3/E5 subscription with minimum 300 seats can take advantage of that integration by adding six months of Dynamics 365 Marketing at no additional cost to nurture up to 10,000 contacts with personalized emails and engaging customer journeys. This special offer is available through December 31, 2021. More details on the offer and eligibility can be found here.
Win customers and earn loyalty
The new Teams webinars capabilities are remarkable by themselves, but when you add the integration with Dynamics 365 Marketing, they are extraordinary. The power, flexibility, and unlimited possibilities that these two products working together can offer will change the way that you interact with your event attendees. Key capabilities include simplified event management, increased attendee engagement, and effortless follow-up to nurture relationships, win customers, and earn their loyalty faster.
Simplify event management
With the new Teams functionality, you have the power to host secure interactive meetings and webinars that include polls, video sharing, and reactions for up to 1,000 attendees.
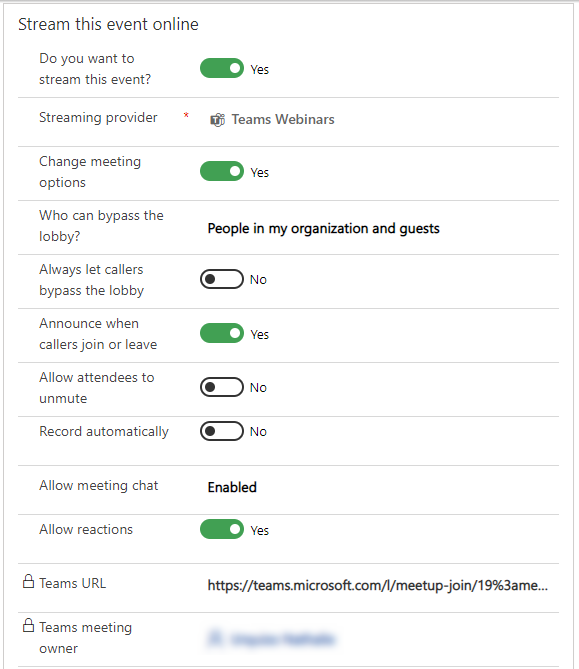
You have the flexibility to organize your webinar your wayfrom within Teams or from within Dynamics 365 Marketing, the option is yours. Both ways are easy and intuitive and have improved capabilities.
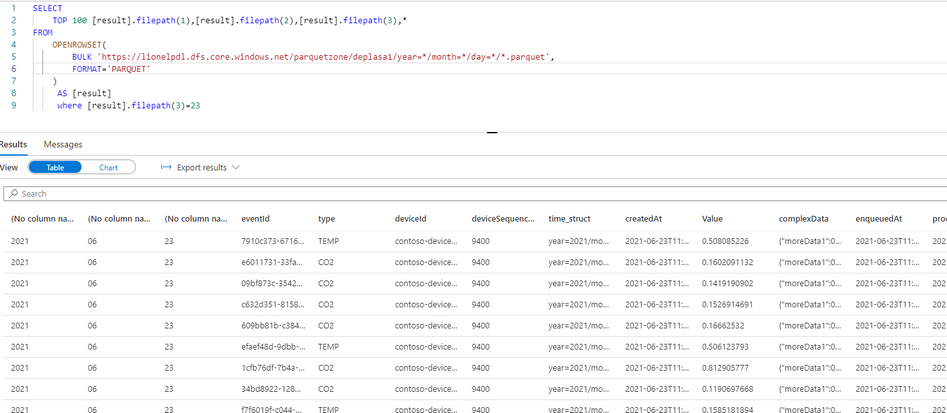
If you already use event management from within Dynamics 365 Marketing, you will now see a more robust set of event management options that allow you to have better control over your webinar.
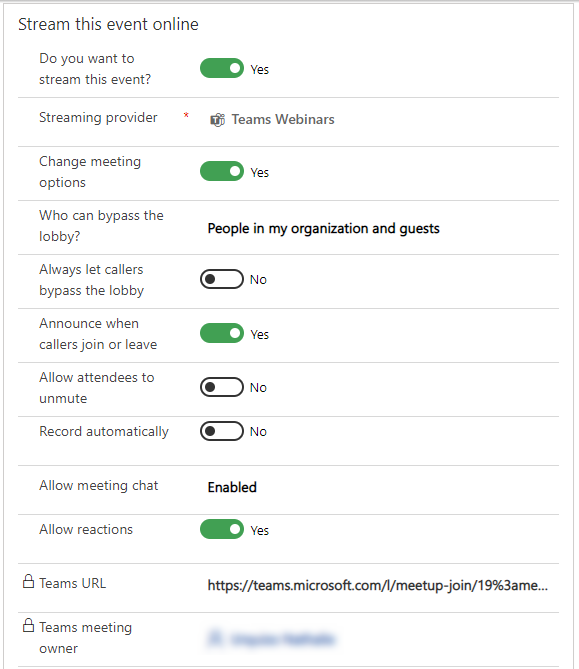
If you prefer to create events from within Teams, you will have the same high level of control, but you now have the optional integration and power of Dynamics 365 Marketing to use in elevating your customer journey experience.
Increase attendee engagement
Microsoft Teams makes it easy to catch the attention of your online audience and present like a pro. Use PowerPoint Live and Presenter Mode to deliver more impactful and engaging presentations, and take advantage of new innovations like Standout Mode which enables presenters to appear over content.
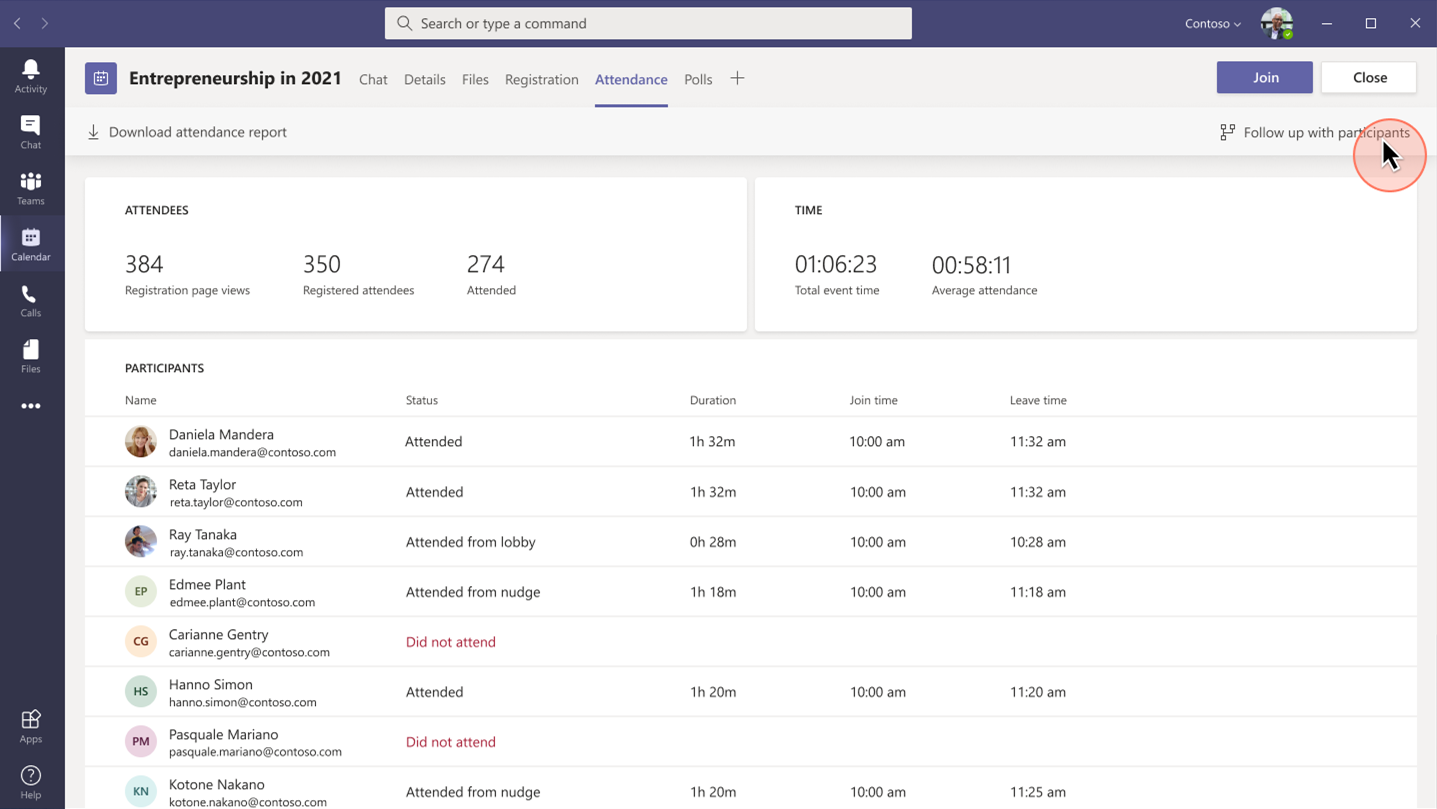
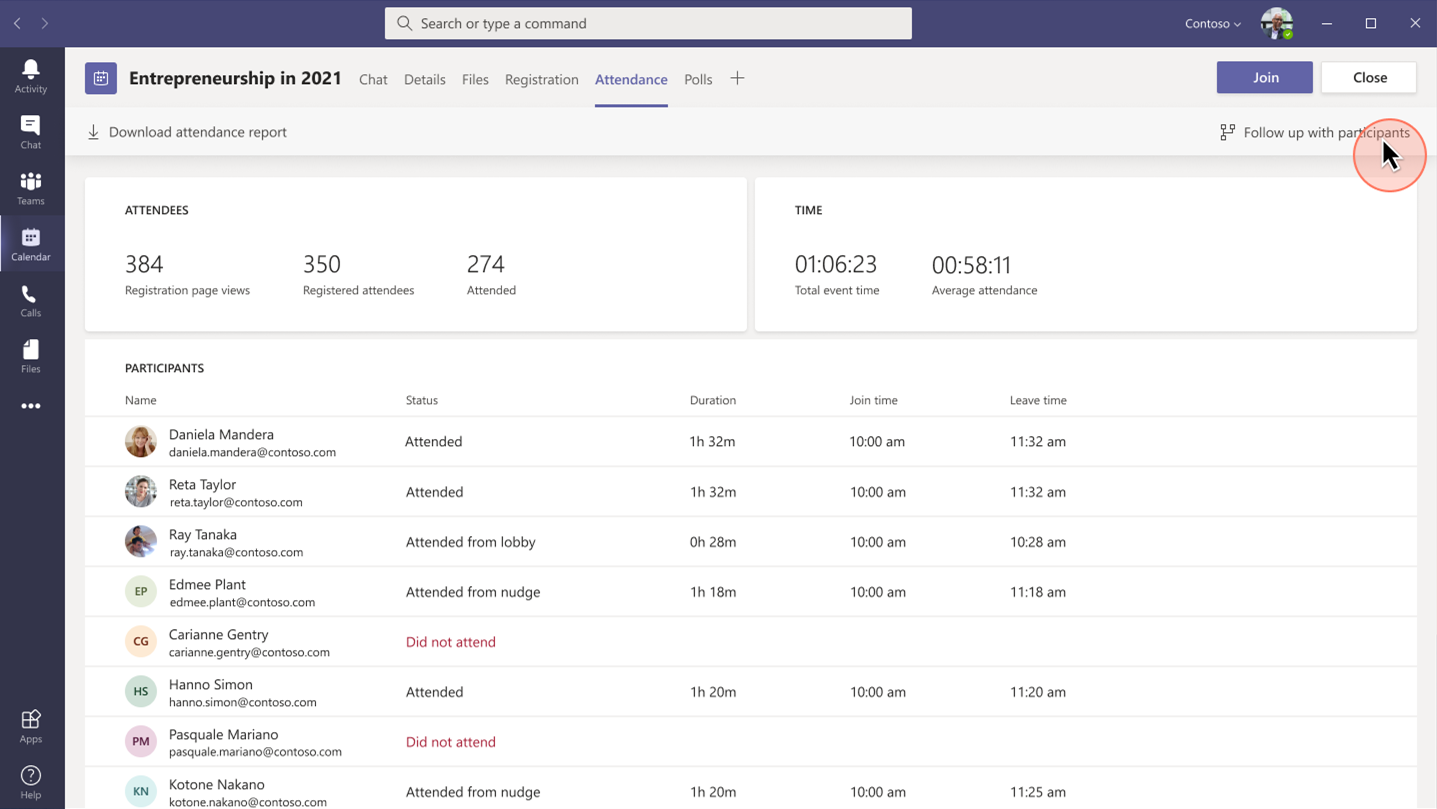
Whether it’s before, during, or after your event, you can easily gain insightful information from attendees with real-time polls and surveys from within Teams. Reports that track attendance are also readily available. Use that information to shape your presentation delivery and personalize post-event follow-up.

Follow-up to nurture relationships
Keep the lines of communication active after your Teams webinar concludes. With a single mouse click, attendee engagement data is transferred seamlessly into Dynamics 365 Marketing and automatically populated into pre-built, commonly used segments. Each of those segments corresponds to a built-in, ready-to-send, editable email template for personalized post-event communications and customer journey orchestration. Leverage the dashboards and analytics to gain insights about attendees to further personalize and drive post-event engagement.
Project Management Institute boosts events participation and member experience
“Since we were already familiar with Dynamics 365 and Teams, we were able to pivot quickly to provide virtual events for our members.With Dynamics 365, we’ve removed the struggle from our marketing efforts.”Glory Ikeata, Chair of Volunteer Services Committee, Project Management InstituteMinnesota
Project Management InstituteMinnesota (PMI-MN) provides value to members by sharing project management information and is among the largest PMI chapters in size and member events. PMI-MN aspired to further engage its members and inform them about seminars, certifications, and educational events.
To meet that aspiration, PMI-MN needed a way to centralize disparate member data and use that data to better understand how members interact with their organization. They worked collaboratively with cloud solutions provider TrimaxSecure to implement a comprehensive solution with Microsoft Dynamics 365, Microsoft Teams, and Microsoft Power BI to increase member engagement.
PMI-MN used Dynamics 365 Marketing to build sophisticated marketing journeys to connect with their members via relevant email marketing and the app’s event management capabilities to create event portals to simplify event management for members, volunteers, and speakers.
During the COVID-19 crisis, the chapter was able to shift from in-person to virtual events because it had reliable cloud-based tools to continue to engage its members. PMI-MN used Microsoft Teams for remote events and sent the Teams meeting links through email.
By connecting their event and email marketing efforts, PMI-MN now offers a richer member experience and increased participation in events and workshops. Staff can now quickly and easily manage member information. The chapter has seen retained events revenue increase by almost 90 percent.
Microsoft Core Marketing Engineering turns audiences into customers

“By carefully combining technology solutions in our events platform, including Dynamics 365 and Teams, we’ve enabled our marketing business to generate a 400 percent increase in attendees and a 500 percent increase in new known leads.”Vinh Nguyen, Principal Program Manager, Microsoft
The Core Marketing Engineering (CME) unit at Microsoft wanted to enhance event marketing capabilities, reduce operational complexity around in-person and digital events, and explore Microsoft technology for event management. The business unit accelerated the process when it needed to quickly shift from holding in-person events to hosting them digitally due to COVID-19.
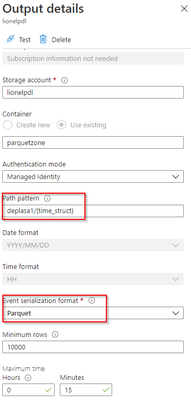
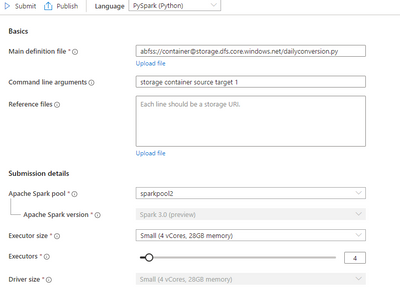
It adopted Microsoft Dynamics 365 Marketing and used the event management capabilities to create an event management center. CME gets additional value from Dynamics 365 Marketing by combining it with Microsoft Teams event functionality, Azure Data Lake Storage, and Power Apps portals.
“By using Dynamics 365 and Teams together, we’ve centralized everything for our marketers, so they no longer have to spend time navigating to an outside system when they want to build a digital event,” says Sanarya Salah, Program Manager at Microsoft.
CME reduced its number of third-party tools, cutting costs and removing complexity for its marketers. It now creates more engaging and interactive events, which has led to better customer engagement and increased leads.
Strengthen customer relationships
The powerful integration of Teams and Dynamics 365 Marketing allows you to convert a single interaction into an ongoing relationship to win customers and earn their loyalty. The limited-time special offer for Microsoft Teams customers presents a unique opportunity to use that integration in your own environmentthe possibilities are extraordinary.
Get started with Microsoft Teams and Dynamics 365 Marketing today.
Learn more
We are always looking for feedback and would like to hear from you. Please head to the Dynamics 365 Community to start a discussion, ask questions, and tell us what you think.
The post Turn attendees into loyal customers with Microsoft Teams and Dynamics 365 Marketing appeared first on Microsoft Dynamics 365 Blog.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.




Recent Comments