by Contributed | Jun 26, 2021 | Technology
This article is contributed. See the original author and article here.
Introduce the second source repository
Let’s go back to the YAML file editing interface and add the following paragraph after the trigger:- master segment at the beginning of the file:
resources:
repositories:
- repository: Angular
name: <YourProjectName>/ASP_Angular
type: git
ref: main
Here repository: Angular is a code name for the referenced source repository, which can be simply called later.
name: <OurProjectName>/ASP_Angular is the “project name / repository name” format.
ref: Main claims to use the main branch.
Then add after steps:
- checkout: Angular
displayName: 'checkout Angular'
- checkout: self
displayName: 'check Backend'
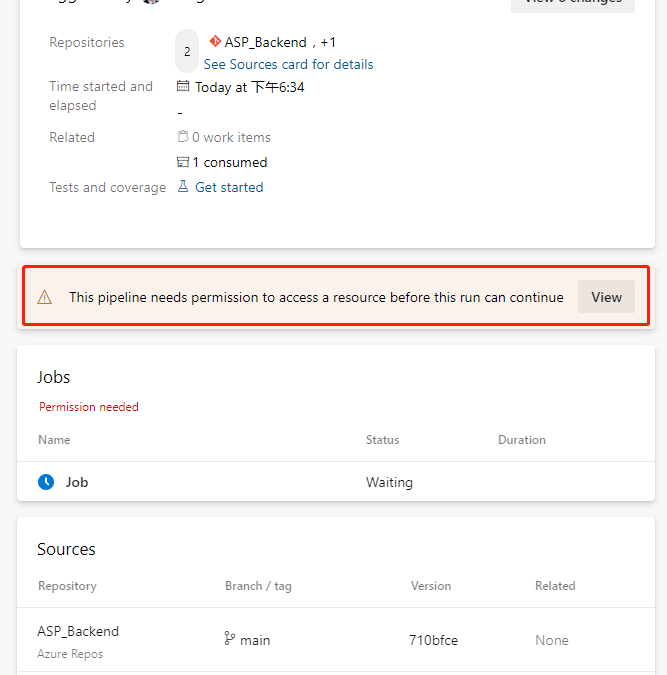
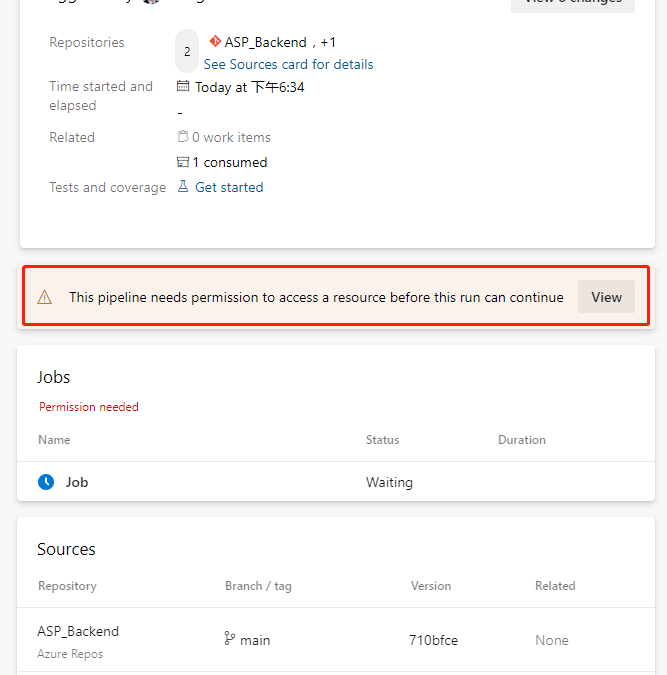
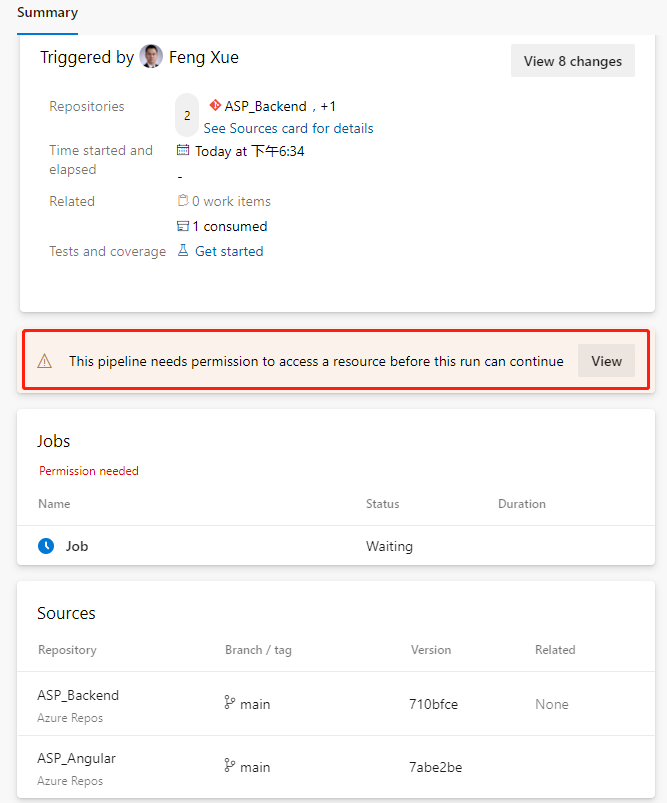
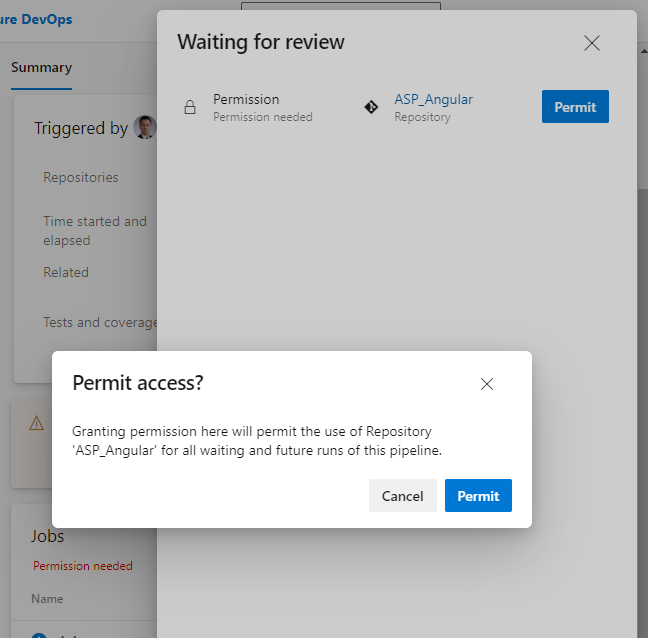
The task means checking out the front-end repository. Because a second source repository is introduced, the current repository itself also has a task – checkout:self to check out. Now save and run. Because a second source repository is included in the current pipeline, we will see a prompt to grant permission when we run this pipeline for the first time.
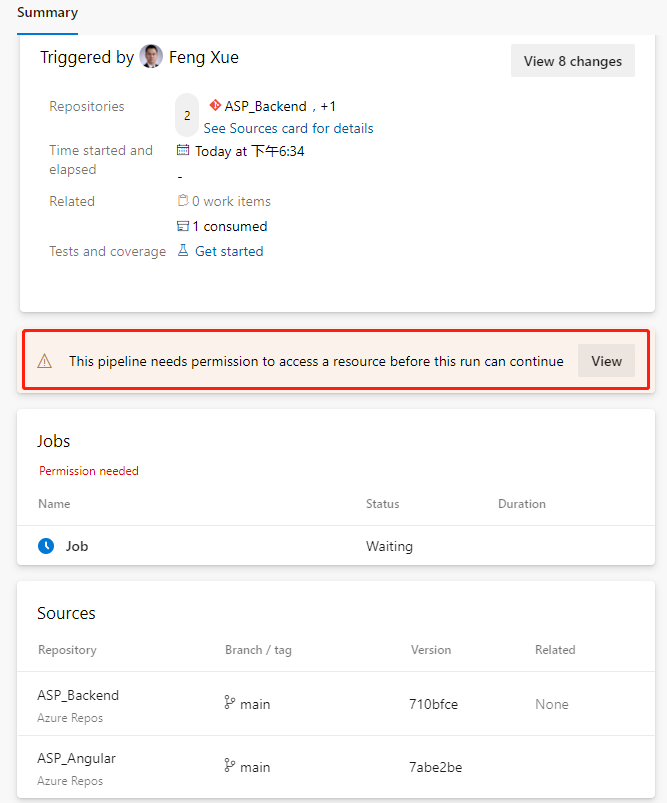
Click the View button.
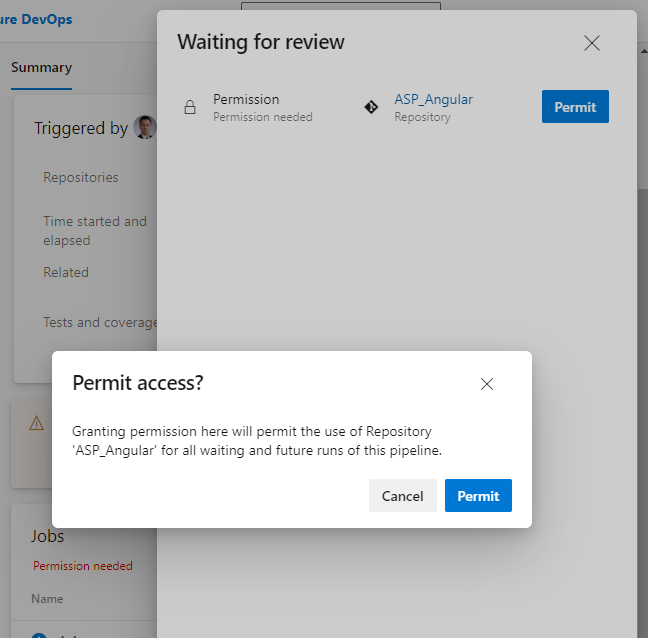
Just click the “Permit” button on the float layer. This permission only needs to be done the first time we add a task, and it won’t pop up again.
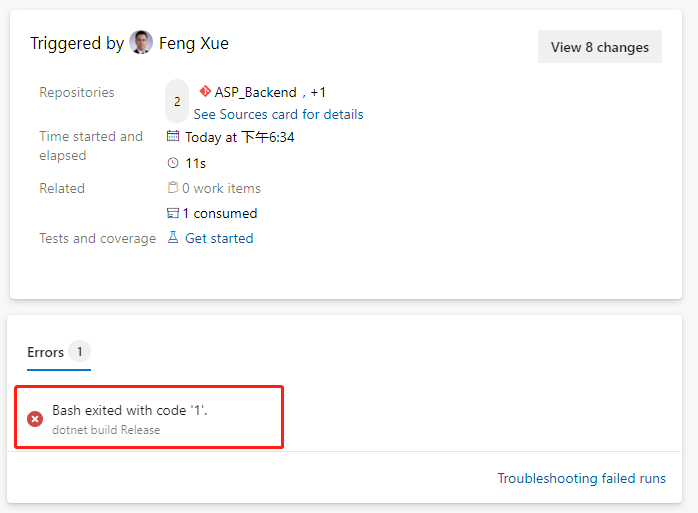
This execution probability will fail.
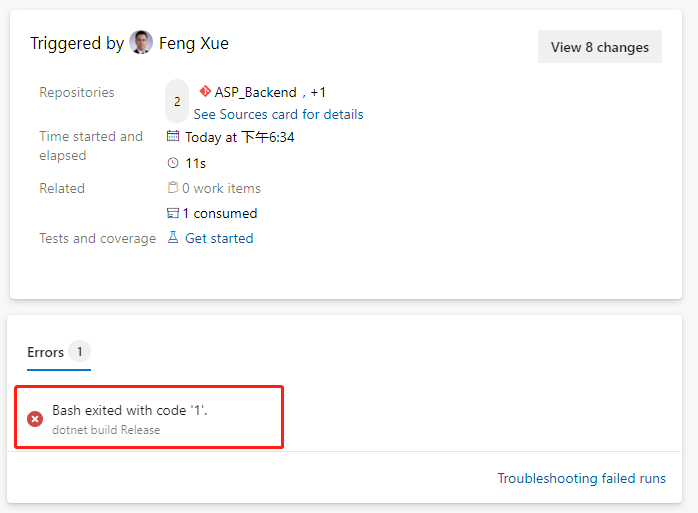
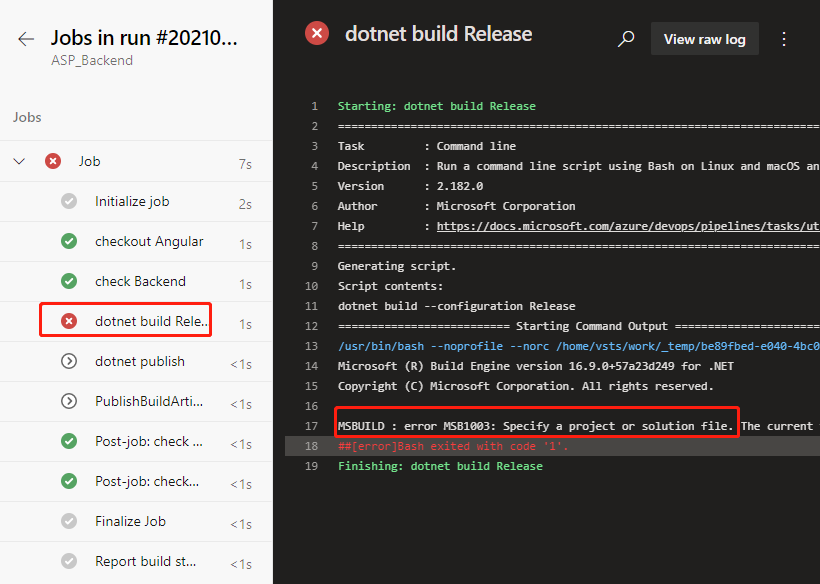
We click on this error message and jump directly to the specific error log.
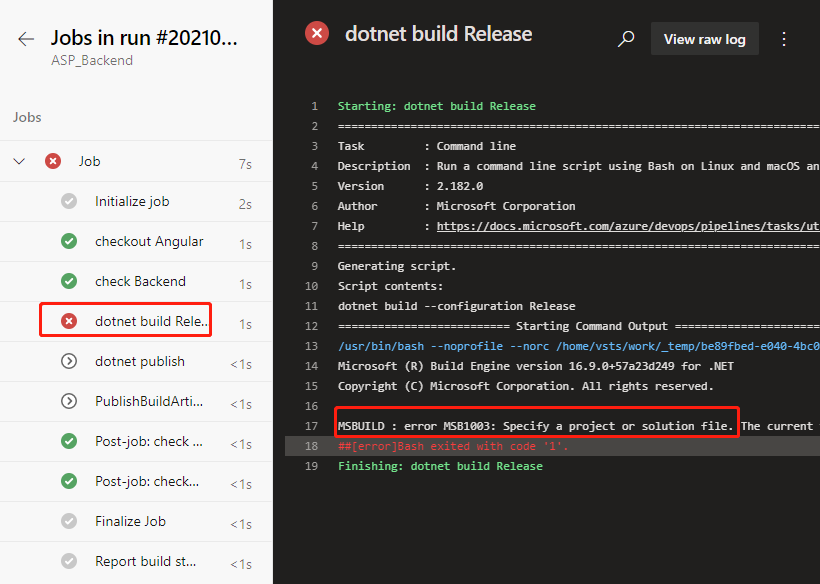
ASP build tasks that used to work properly did no work this time. Let’s locate the task that were previously built by the wizard.
- script: dotnet build --configuration $(buildConfiguration)
displayName: 'dotnet build $(buildConfiguration)'
Replace with this below.
- task: DotNetCoreCLI@2
displayName: 'dotnet build'
inputs:
command: 'build'
projects: '**/*.csproj'
arguments: '--configuration $(BuildConfiguration)'
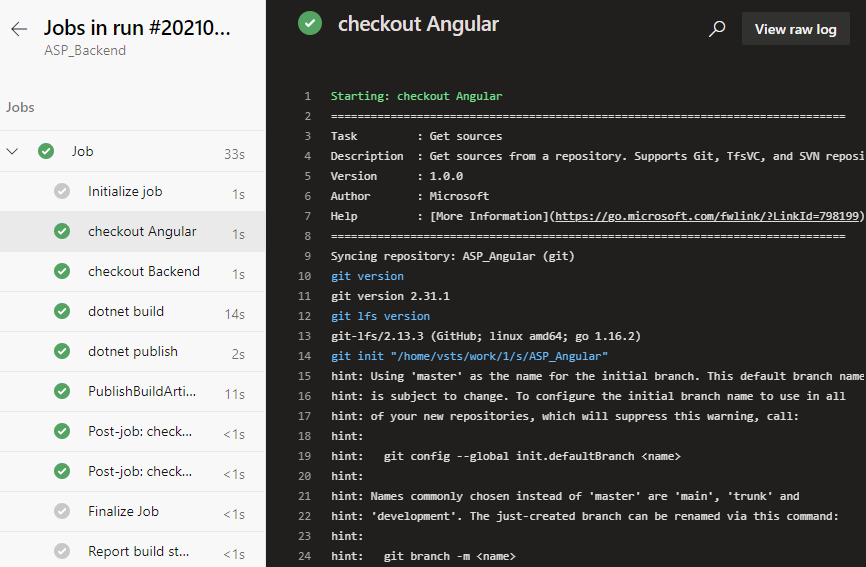
Save and run again and it works fine. We click on the Job link on the green check-in on the job run details page to see that the task of checking out the back-end repository of the front-end repository in the log is complete, and we can click on each task name to view the detailed log.
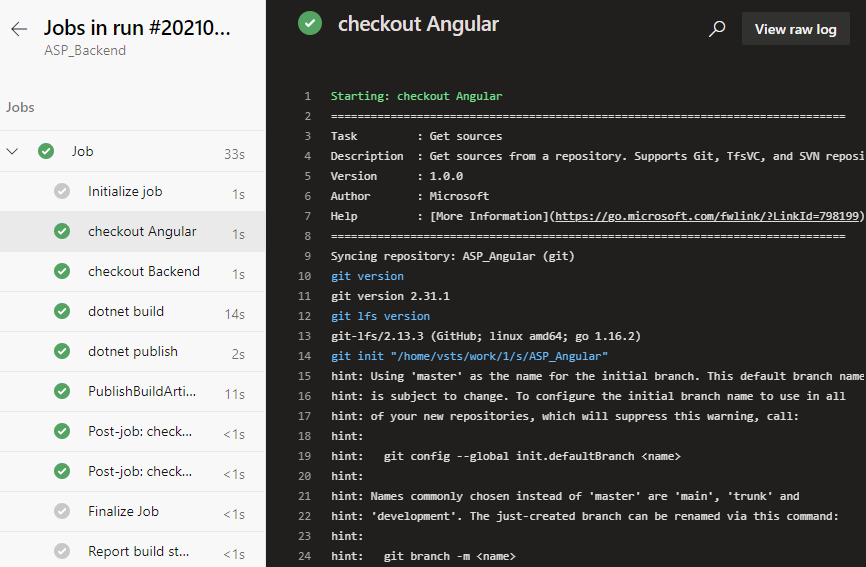
Note that there is a line in the log checked out by the front-end project here
git init “/home/vsts/work/1/s/ASP_Angular”
This means the path where the front-end code was saved in the container that our job was executed by the pipeline. We note this path down and we will need it to add build tasks later.
![[Guest Blog] At the Intersection of Mixed Reality and Business Applications: My Career Journey](https://www.drware.com/wp-content/uploads/2021/06/fb_image-1184.png)
by Contributed | Jun 25, 2021 | Technology
This article is contributed. See the original author and article here.
This article is written by Martin Heward, a Microsoft employee and long time professional in Business Applications, who shares his biz apps to mixed reality journey as a part of our Humans of Mixed Reality series. This blog is formatted in a Q&A style – please read Martin’s answers to questions around his career story.

Q: How did you get started in the MR space?
A: As a long time professional in Business Applications (as a customer, partner, now Global Black Belt aka GBB specialist), I am no stranger to emerging technology since during much of my career, I’ve seen many Dynamics 365 products start off as an incubation product just like our Mixed Reality business applications today. Not long after I joined Microsoft 3.5 years ago, I came across the concept of Mixed Reality and immediately was intrigued by its possibility to add unmatched business value for my customers and prospects. As a new employee with time to learn (remember those days?) in the summer of 2018, I jumped on the opportunity to be one of the early adopters and became Master-Certified in both Mixed Reality and the HoloLens.
As part of that process, I received an HoloLens (1st gen) for learning and pre-sales. However, I am glad that I was disciplined enough to not play with it, or even turn it on until I had completed the learning courses. I will NEVER forget that magical moment when I put it on for the first time after having some idea (albeit only 2-dimensional) about what to expect. Even though the HoloLens (1st gen) had some limitations with field of view and gesturing that was not exactly intuitive at the time, I was completely blown away with Mixed Reality in general. I know many people have already said this before, but it truly is one of those rare concepts that you can describe with words and human emotions all day long, but not understand until you experience it on your own.
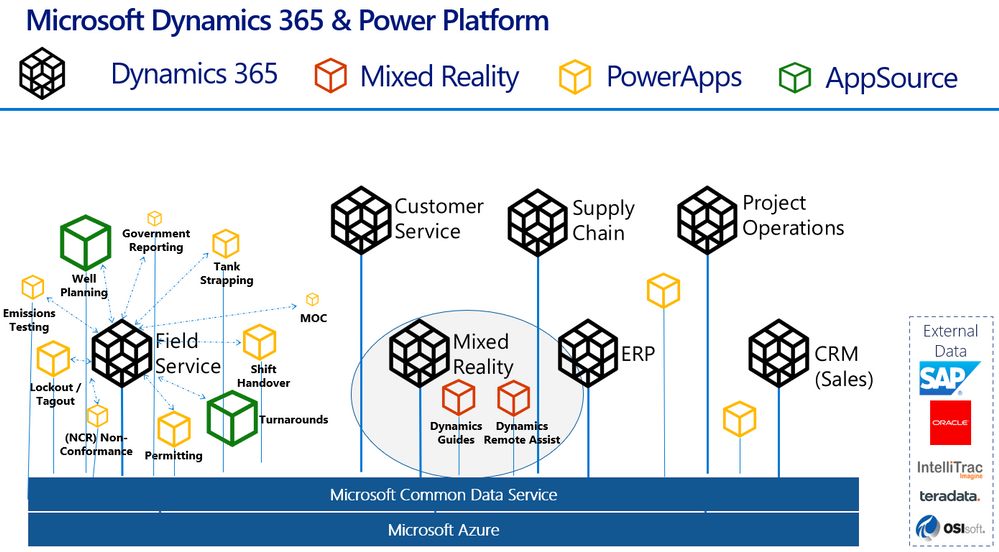
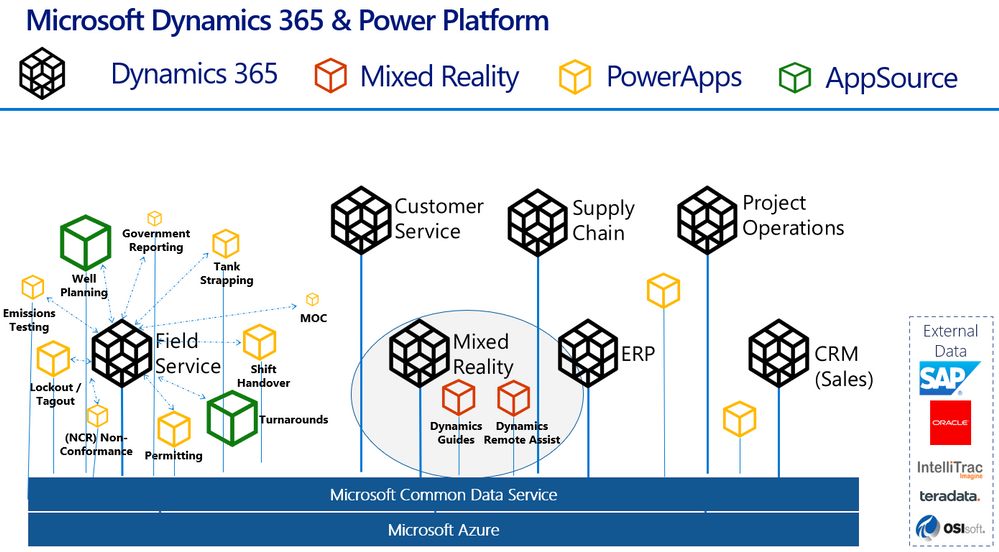
Here’s a handy diagram to illustrate where mixed reality business applications like Remote Assist and Guides come in the broader Dynamics 365 infrastructure:
Q: What excites you most about mixed reality?
A: Personally, mixed reality is exciting to me because of how relevant and complementary it is to core challenges that our Business Applications customers are tackling each day. Mixed Reality and the value it brings spans every industry we operate in. It is certainly extremely relevant in my focus industries of Process Manufacturing, Energy, and Utilities. From Health and Safety, to Production Optimization, to an aging workforce of frontline workers; these are fundamental issues discussed in board rooms at every single one of the customer organizations I interact with. My job is to create a vision of transformation of business processes with Dynamics 365 – adding in Mixed Reality to my messaging is a way of super-charging this message and making the previously perceived sci-fi-like future seem very possible and current.
Q: Why do you think mixed reality business applications are truly transformative for organizations?
A: We all know transformation may be one of the most overused terms in our industry, and perhaps the most vague. Business Applications is unique in the sense that it is not a commodity that we are delivering, instead it is more like a box of LEGO, if you will, that requires transformation of business processes that the configured Business App is meant to complement. This process of envisioning typically takes lots of time. What is so refreshing about Dynamics 365 mixed reality business applications such as Remote Assist and Guides is that they are much closer to a commodity than those of us in Business Applications are used to. Mixed Reality applications can transform business processes and be adopted quickly, sometimes even right out of the box.
This quick time to value is related to the fundamental nature of mixed reality apps. I’ve spoken with many individuals who experience mixed reality for the first time (be it at marketing shows and conferences) and they often have sentiment much like mine around “the experience” of learning in a completely different manner than we are used to. Everyone’s learning styles are quite different – I see this first hand with my own two kids. Some are traditional, others are kinesthetic and require movement to retain information. There is something profound and different about performing tasks on a HoloLens. Many, including myself seem to retain information in much greater quantity and specificity than traditional methods.
Here’s a nostalgic photo of me with my very first HoloLens (1st gen) device:

Q: What advice would you give to others considering careers in mixed reality, or exploring the use of mixed reality in their organizations?
A: As stated earlier, my advice about mixed reality is to first perform research and due diligence before jumping in and worrying about devices and your organizations specific use cases. The applications of mixed reality are vast, and just like any emerging technology, many decision makers within business see this as a future-state investment. For many, most unfortunately, this could mean months and years of pilots and proof of concepts. This is a medium that is proven to be transformational even in the most hard industrial environments within our customers operations. To avoid this perception of emerging versus ready, I would think outside the box and be very selective about the business problems you are aligning with. First impressions are quite powerful and can be a challenge to overcome if outcomes are not aligned with expectations. A good way of avoiding this is to weave it into messaging as matter of fact versus something profound and singled out.
Q: Do you have any useful resources you can share that have inspired you (links, e-books, podcasts etc)?
I hope you will be bold and experience mixed reality for yourself, and witness firsthand what it can do for industries worldwide!
#MixedReality #CareerJourney
by Contributed | Jun 25, 2021 | Technology
This article is contributed. See the original author and article here.
Hi All,
Last month we launched AKS on Azure Stack HCI. Since then we have been busily working with folk who have been trying it out and getting started on deploying their containerized applications on top of AKS on Azure Stack HCI. At the same time we have been busily working on the first update to AKS on Azure Stack HCI – which is now available! You can evaluate AKS-HCI by registering here: https://aka.ms/AKS-HCI-Evaluate.
With this update – we are bringing in the following changes:
Seamless update of Kubernetes clusters
One of the biggest items that we have been working on is ensuring that this update is completely seamless for our users. You can update our PowerShell, Windows Admin Center extension and the AKS on Azure Stack HCI host with zero impact to your running workloads. You can then decide when to update individual Kubernetes clusters.
As you update your Kubernetes clusters – we ensure that this is as low impact as possible by following a process where, for each worker node in the cluster we:
- Provision a new worker node that is based on the June update
- Join the new worker node to the Kubernetes cluster
- Drain the existing worker node
- Decommission the existing worker node
Note – all of this is handled seamlessly for you. You just say “Update”!
Prometheus now included
Monitoring the health, performance, and resource usage of the control plane and worker nodes of your AKS-HCI workload cluster is crucial in production environment. Prometheus, a Cloud Native Computing Foundation project, is an open-source toolkit that is particularly popular for monitoring Kubernetes. Prometheus works with different types of collectors and agents to collect metrics and store them in a database where you can query the data and view reports. While it has been available for use with AKS on Azure Stack HCI, in this latest version we have made the deployment of Prometheus even simpler. You can now deploy Prometheus when creating new workload cluster by passing -enableMonitoring parameter to New-AksHciCluster cmdlet. Or, you can deploy it on an existing workload cluster by using Install-AksHciMonitoring cmdlet.
Once deployed, Prometheus can be used as a data source for rich queries and visualization in Grafana. Please refer to our technical docs for more details.
Security and Stability improvements
A key part of this update is that we have included pertinent security updates that have been released for Windows, Linux, Kubernetes and all the OSS components that are included in AKS on Azure Stack HCI. At the same time we have been continuing to do security and stability testing on AKS on Azure Stack HCI ourselves – and this update includes fixes to address any issues that we have discovered.
Once you have downloaded and installed the AKS on Azure Stack HCI June 2021 Update – you can report any issues you encounter, and track future feature work on our GitHub Project at https://github.com/Azure/aks-hci. And, if you do not have the hardware handy to evaluate AKS on Azure Stack HCI you can follow our guide for evaluating AKS-HCI inside an Azure VM: https://aka.ms/aks-hci-evalonazure.
I look forward to hearing from you all!
Cheers,
Ben
by Contributed | Jun 25, 2021 | Technology
This article is contributed. See the original author and article here.
Dear IT Pros,
Today we discuss about All things about WDAC – Windows Defender Application Control.
WDAC was introduced with Windows 10 and could be applied to Windows server 2016 and later, its older name is Configurable Code Integrity (CCI). WDAC allows organizations to control which drivers and applications are allowed to run on devices.
- Windows Server 2016/2019 or anything before version 1903 only support legacy policies (aka 1 policy in place)
- Windows Server Core edition does support WDAC but some components that depends on AppLocker won’t work
WDAC policies apply to the managed computer as a whole and affects all users of the device. WDAC rules can be defined based on:
- Attributes of the codesigning certificate(s) used to sign an app and its binaries
- Attributes of the app’s binaries that come from the signed metadata for the files, such as Original Filename and version, or the hash of the file
- The reputation of the app as determined by Microsoft’s Intelligent Security Graph
- The identity of the process that initiated the installation of the app and its binaries (managed installer)
- The Folder or File path from which the app or file is launched (beginning with Windows 10 version 1903)
- The process that launched the app or binary
Multiple Policies and Supplemental Policy.
Beginning with Windows 10 version 1903, Windows server 2022, WDAC supports up to 32 active policies on a device at once. The following scenarios are supported:
- Enforce and Audit Side-by-Side
- Multiple Base Policies, users can enforce two or more base policies simultaneously in order to allow simpler policy targeting for policies with different scope/intent.
- If two base policies exist on a device, an application has to be allowed by both to run
- Supplemental Policies, users can deploy one or more supplemental policies to expand a base policy. For supplemental policies, applications that are allowed by either the base policy or its supplemental policy/policies are allowed to run
PLANNING.
Implementing application control can have unintended consequences, plan your deployment carefully.
- Decide what devices you will manage with WDAC and split them into deployment rings: Test, UAT and Prod ring, so you can control the scale of the deployment and respond if anything goes wrong.
- All WDAC policy changes should be deployed in audit mode before proceeding to enforcement. Carefully monitor events from devices where the policy has been deployed to ensure the block events you observe match your expectation before broadening the deployment to other deployment rings.
- If your organization uses Microsoft Defender for Endpoint, you can use the Advanced Hunting feature to centrally monitor WDAC-related events. Otherwise, we recommend using an event log forwarding solution to collect relevant events from your managed endpoints.
- Leverage medatada in the policies (version, policyID, description, etc) to keep track of which policies applied to what group of devices in production.
Options For WDAC Policy Creation:
The creation of an WDAC Policy depends on the level of restriction you may want to apply to your target devices. You could start with a pre-built template of Windows 10:
Level of Restriction
|
Template to be used (C:WindowsschemasCodeIntegrityExamplePolicies)
|
Allowed All Applications
|
AllowAll.xml
|
Allowed All Enabled HVCI
|
AllowAll_EnableHVCI.xml (Enable Hypervisor-Code-Integrity in Memory)
|
Allowed All Microsoft Applications
|
AllowMicrosoft.xml
|
Allowed All Microsoft and Good Reputation Applications
|
DefaultWindows_Enforced.xml or
DefaultWindows_Audit.xml
|
Deny All Applications but the one you choose
|
DenyAllAudit.xml
|
Other pre-built .xml template for Application or Script Control
|
Allowed Application deployed by Microsoft Endpoint Configuration Manager (MECM).
|
WDAC Policy deployed to Clients at directory location:
%OSDrive%WindowsCCMDeviceGuard
|
Device Guard Signing Service (DGSS) DefaultPolicy.xml
|
Including the rules from DefaultWindows and adds rules to trust apps signed with your organization-specific certificates issued by the DGSS version 2
|
- You could use WDAC Wizard to view and customize the allow or deny rules applied to different applications.
- Every WDAC policy is created with audit mode enabled by default. After you have successfully deployed and tested a WDAC policy in audit mode and are ready to test the policy in enforced mode, use WDAC Wizard to turn off Audit mode this will make the WDAC Policy become Enforced mode. You also could use command in an elevated Windows PowerShell session to make WDAC Policy in Enforced mode:
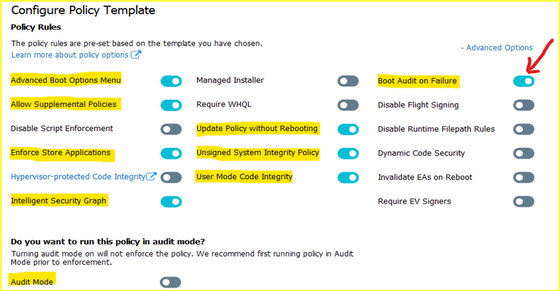
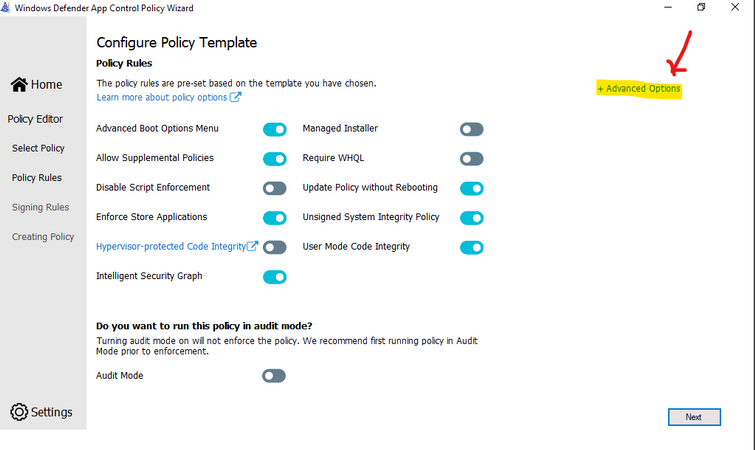
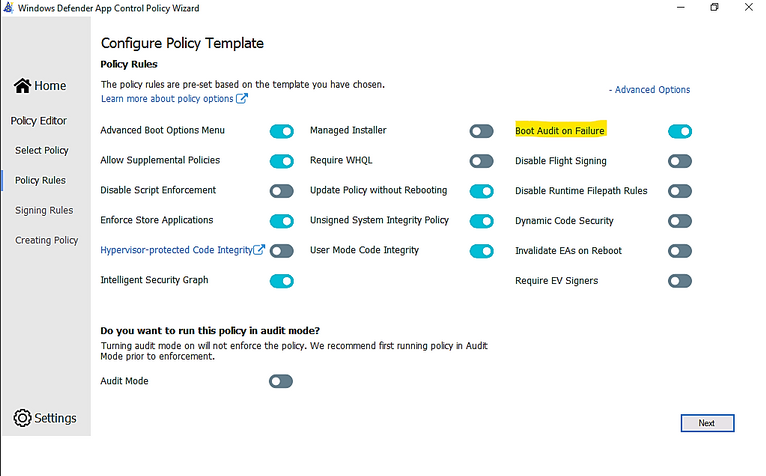
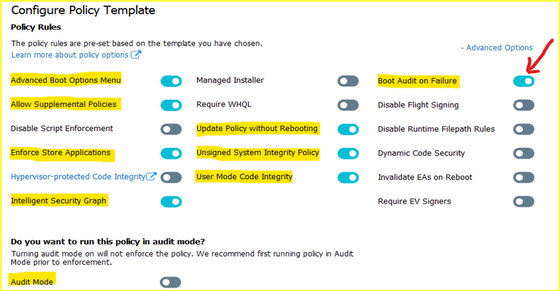
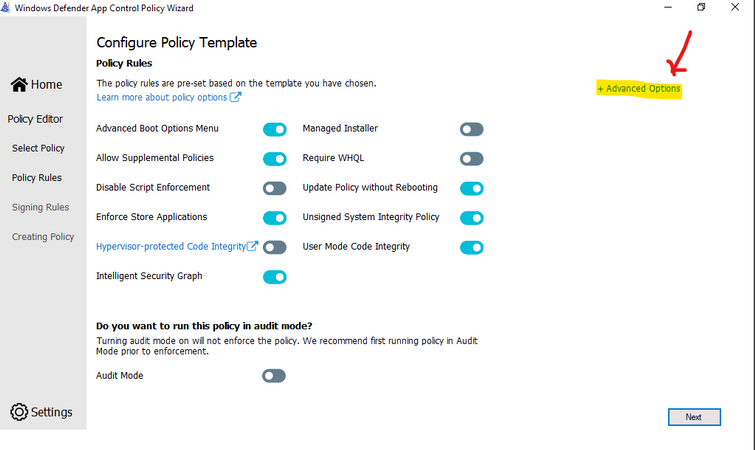
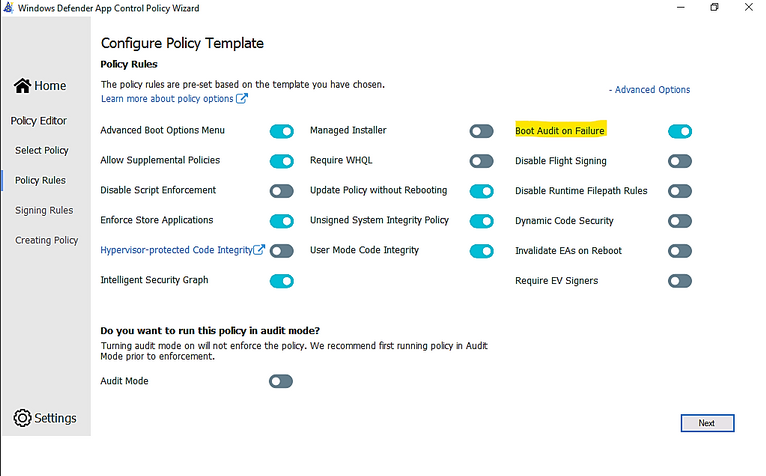
- Ensure that rule options 9 (“Advanced Boot Options Menu”) and 10 (“Boot Audit on Failure”) are set the way that you intend for this policy. We strongly recommend that you enable these rule options before you run any enforced policy for the first time. Enabling these options provides administrators with a pre-boot command prompt and allows Windows to start even if the WDAC policy blocks a kernel-mode driver from running. When ready for enterprise deployment, you can remove these options.
- To ensure that these options are enabled in a policy, use Set-RuleOption as shown in the following commands. You can run these commands even if you’re not sure whether options 9 and 10 are already enabled—if so, the commands have no effect.
> Set-RuleOption -FilePath InitialCIPolicy -Option 9
> Set-RuleOption -FilePath InitialCIPolicy -Option 10
- Copy the initial file to maintain an original copy:
> copy InitialCIPolicy.xml EnforcedCIPolicy.xml
- Use Set-RuleOption to delete the audit mode rule option:
> Set-RuleOption -FilePath EnforcedCIPolicy.xml -Option 3 -Delete
Note
To enforce a WDAC policy, you delete option 3, the Audit Mode Enabled option. There is no “enforced” option in a WDAC policy.
> ConvertFrom-CIPolicy EnforcedCIPolicy.xml EnforcedCIPolicy.bin
- Now that this policy is in enforced mode, you can deploy it to your test computers. Rename the policy to SIPolicy.p7b and copy it to C:WindowsSystem32CodeIntegrity for testing, or deploy the policy through Group Policy by following the instructions in Deploy and manage Windows Defender Application Control with Group Policy. You can also use other client management software to deploy and manage the policy.
- Windows Defender Application Control policy – policy rule options
WDAC – policy rule options
|
|
Rule option
|
Description
|
WDAC Wizard Icon
|
0 Enabled:UMCI
|
WDAC policies restrict both kernel-mode and user-mode binaries. By default, only kernel-mode binaries are restricted. Enabling this rule option validates user mode executables and scripts.
|
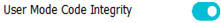
|
1 Enabled:Boot Menu Protection
|
This option is not currently supported.
|
|
2 Required:WHQL
|
By default, legacy drivers that are not Windows Hardware Quality Labs (WHQL) signed are allowed to execute. Enabling this rule requires that every executed driver is WHQL signed and removes legacy driver support. Kernel drivers built for Windows 10 should be WHQL certified.
|

|
3 Enabled:Audit Mode (Default)
|
Instructs WDAC to log information about applications, binaries, and scripts that would have been blocked if the policy was enforced. You can use this option to identify the potential impact of your WDAC policy, and use the audit events to refine the policy before enforcement. To enforce a WDAC policy, delete this option.
|

|
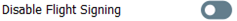
4 Disabled:Flight Signing
|
If enabled, WDAC policies will not trust flightroot-signed binaries. This option would be used by organizations that only want to run released binaries, not pre-release Windows builds.
|
|
5 Enabled:Inherit Default Policy
|
This option is reserved for future use and currently has no effect.
|
|
6 Enabled:Unsigned System Integrity Policy (Default)
|
Allows the policy to remain unsigned. When this option is removed, the policy must be signed and the certificates that are trusted for future policy updates must be identified in the UpdatePolicySigners section.
|
|
7 Allowed:Debug Policy Augmented
|
This option is not currently supported.
|
|
8 Required:EV Signers
|
This rule requires that drivers must be WHQL signed and have been submitted by a partner with an Extended Verification (EV) certificate. All Windows 10 and later drivers will meet this requirement.
|
|
9 Enabled:Advanced Boot Options Menu
|
The F8 preboot menu is disabled by default for all WDAC policies. Setting this rule option allows the F8 menu to appear to physically present users.
|

|
10 Enabled:Boot Audit on Failure
|
Used when the WDAC policy is in enforcement mode. When a driver fails during startup, the WDAC policy will be placed in audit mode so that Windows will be able to load at boot.
|
|
11 Disabled:Script Enforcement
|
This option disables script enforcement options. Unsigned PowerShell scripts and interactive PowerShell are no longer restricted to Constrained Language Mode. NOTE: This option is supported on 1709, 1803, and 1809 builds with the 2019 10C LCU or higher, and on devices with the Windows 10 May 2019 Update (1903) and higher. Using it on versions of Windows 10 without the proper update may have unintended results.
|

|
12 Required:Enforce Store Applications
|
WDAC policies will also apply to Universal Windows applications. (Microsoft Store App)
|
|
13 Enabled:Managed Installer
|
Use this option to automatically allow applications installed by a managed installer. For more information, see Authorize apps deployed with a WDAC managed installer
|

|
14 Enabled:Intelligent Security Graph Authorization
|
Use this option to automatically allow applications with “known good” reputation as defined by Microsoft’s Intelligent Security Graph (ISG).
|
|
15 Enabled:Invalidate EAs on Reboot
|
When the Intelligent Security Graph option (14) is used, WDAC sets an extended file attribute that indicates that the file was authorized to run. This option will cause WDAC to periodically revalidate the reputation for files that were authorized by the ISG upon Windows reboot.
|
|
16 Enabled:Update Policy No Reboot
|
Use this option to allow future WDAC policy updates to apply without requiring a system reboot. NOTE: This option is only supported on Windows 10, version 1709, and above.
|

|
17 Enabled:Allow Supplemental Policies
|
Use this option on a base policy to allow supplemental policies to expand it. NOTE: This option is only supported on Windows 10, version 1903, and above.
|
|
18 Disabled:Runtime FilePath Rule Protection
|
This option disables the default runtime check that only allows FilePath rules for paths that are only writable by an administrator. NOTE: This option is only supported on Windows 10, version 1903, and above.
|
|
19 Enabled:Dynamic Code Security
|
Enables policy enforcement for .NET applications and dynamically loaded libraries. NOTE: This option is only supported on Windows 10, version 1803, and above.
|

|
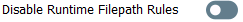
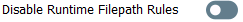
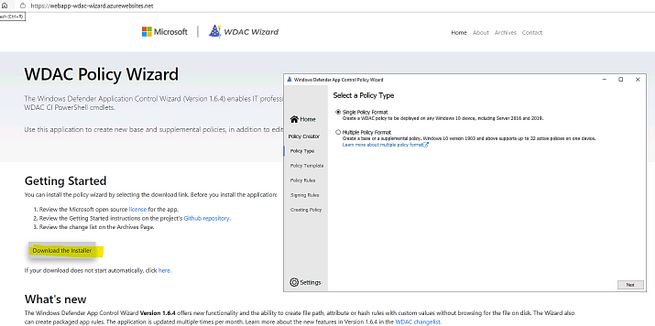
USING WDAC WIZARD TO CREATE POLICY
Steps to proceed with creating the WDAC Policy by Wizard:
- Download WDAC Wizard and install it.
The WDAC Wizard has 3 options for creating, modifying or merge 2 WDAC policies as shown here:
- Create WDAC policy by Wizard
You could create single base policy or multiple base policy or supplemental policies.
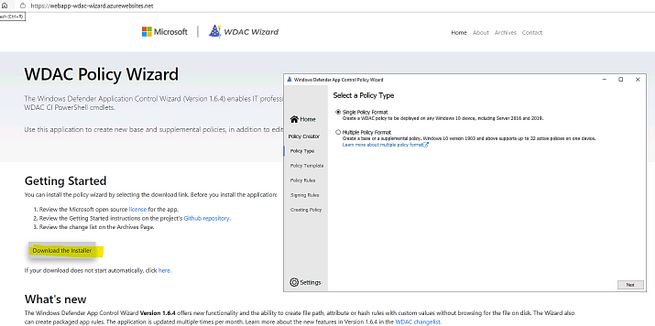
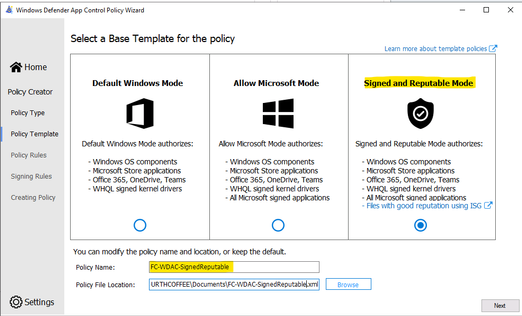
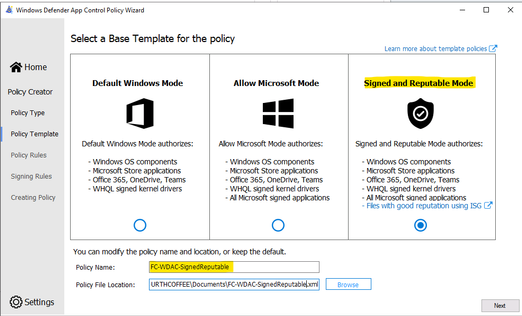
- Launch the WDAC Wizard and choose Single Policy Format
- Choose the Template named “Signed and Reputable Mode” for Microsoft and 3rd party Vendor Applications.
- Typing name for WDAC policy and directory location as shown:
- Choose the option for policy:
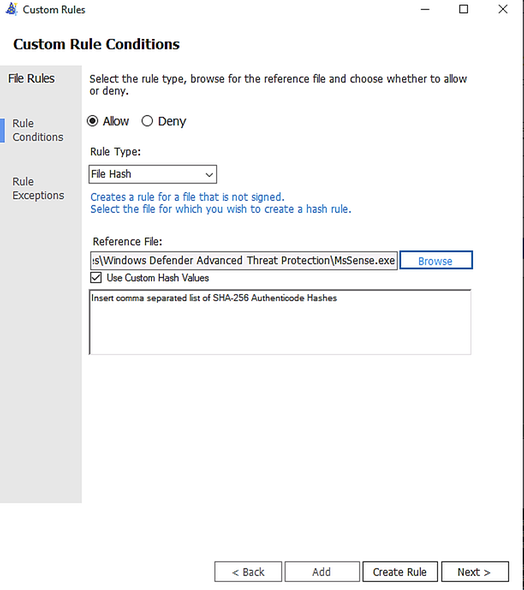
- Next, Adding Custom rule,
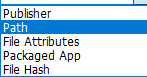
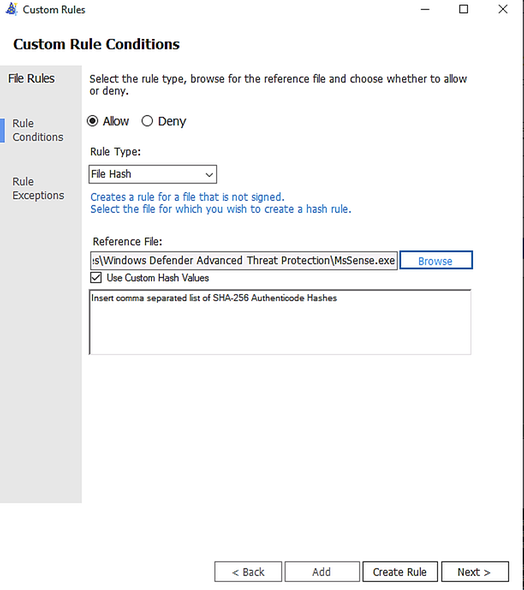
- Rule type: Choose how to identify the application by publisher name, by path to application executable file or folder, by File attributes, by Packaged App, by File
Hash:
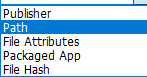
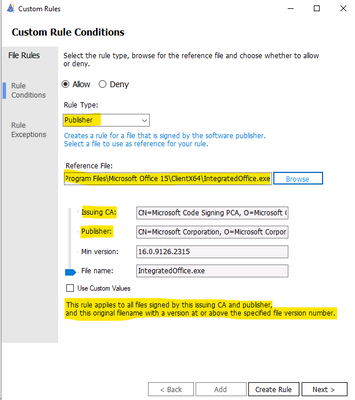
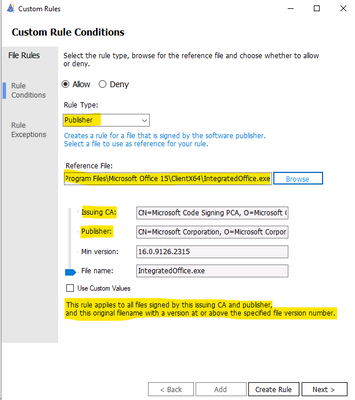
– Custom Rule by Publisher:
Enter the executable file of the related Publisher for the Wizard to collect the Publisher Sign in Code:
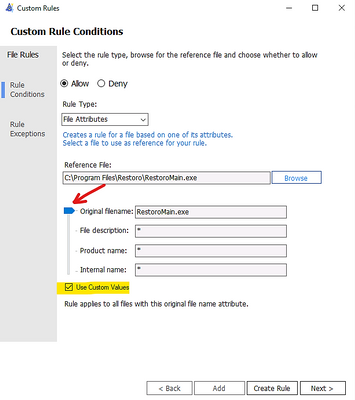
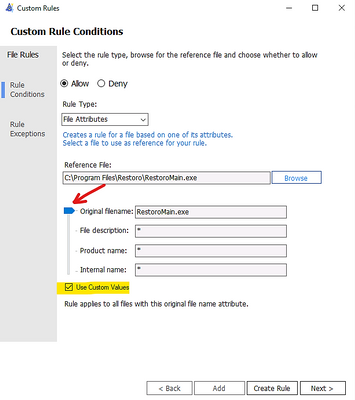
– Custom Rule by File Attribute
Checking the box “Use Custom Values” and Use the glider to choose the attribute as shown here
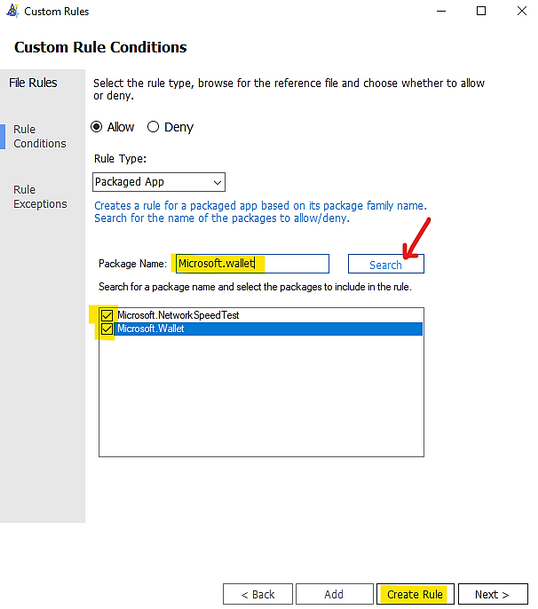
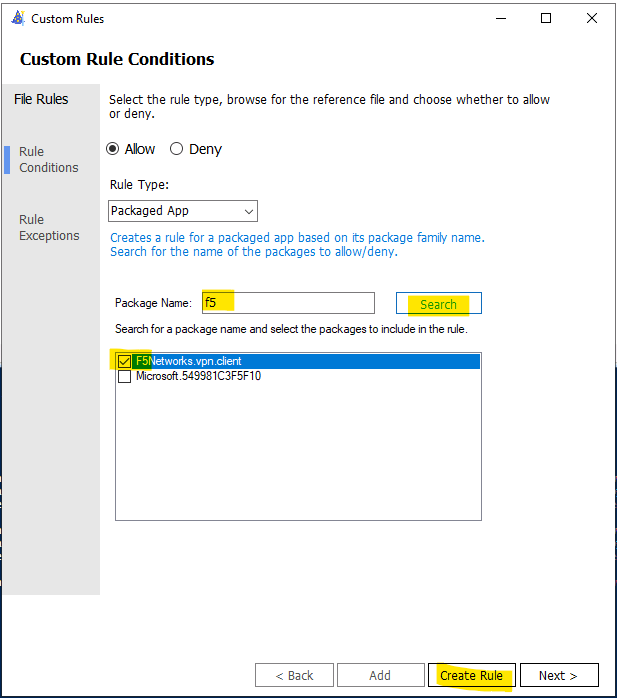
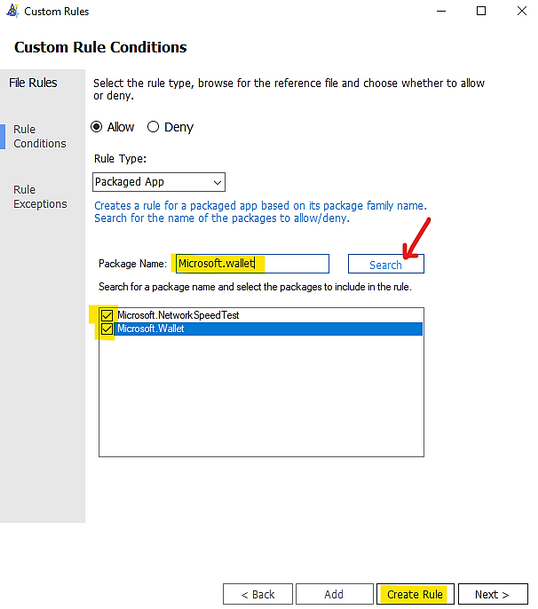
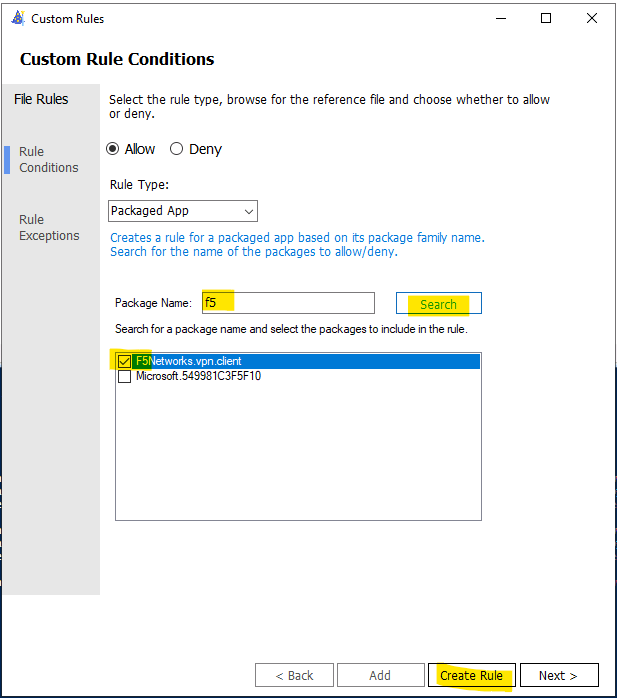
– Custom Rule by Package App (UWP)
Packaged apps, also known as Universal Windows apps, are based on a model that ensures all the files within an app package share the same identity.
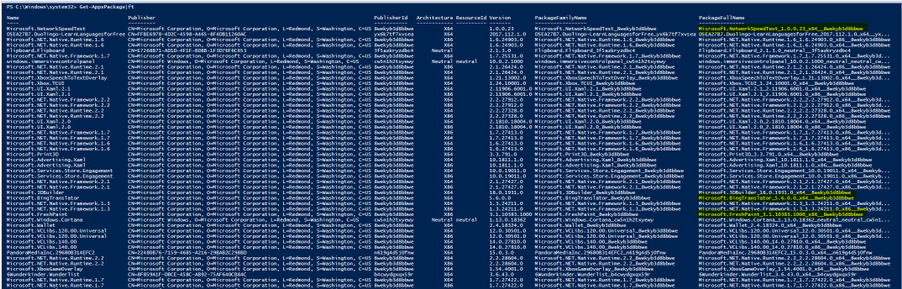
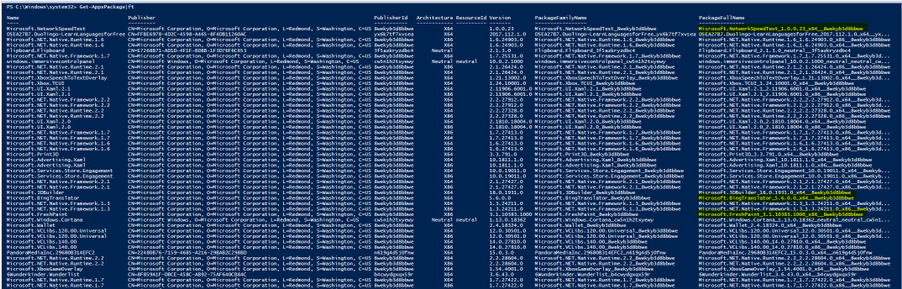
- To get a list of packaged apps run on a device, run command:
> Get-AppxPackage | ft
Typing the Package Name to the Wizard under “Package Name” and click Search button as shown:
You could add multiple file hash separated by comma with Custom rule or use the browser button and specify the file:
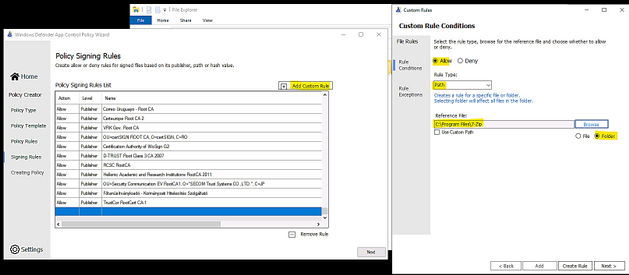
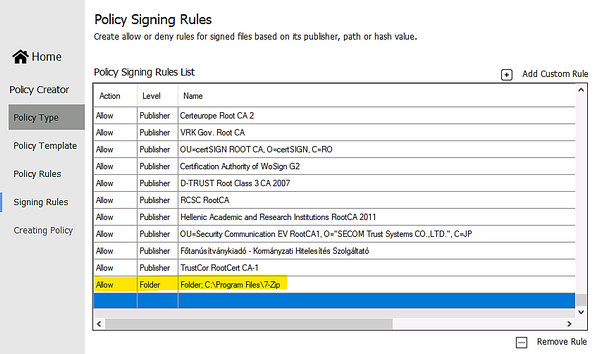
- Custom Rule by Folder Path or File Path:
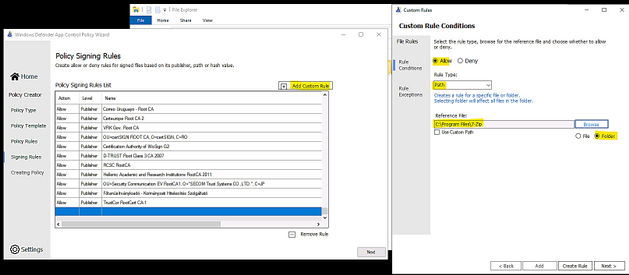
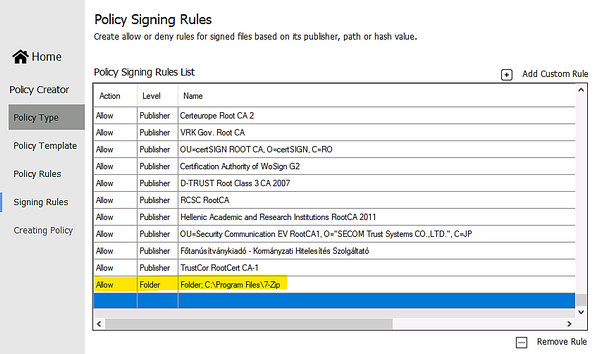
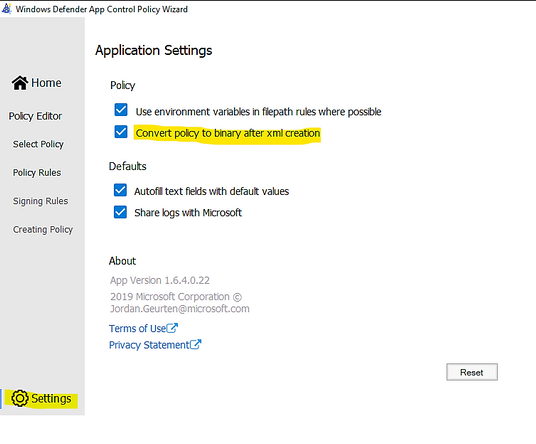
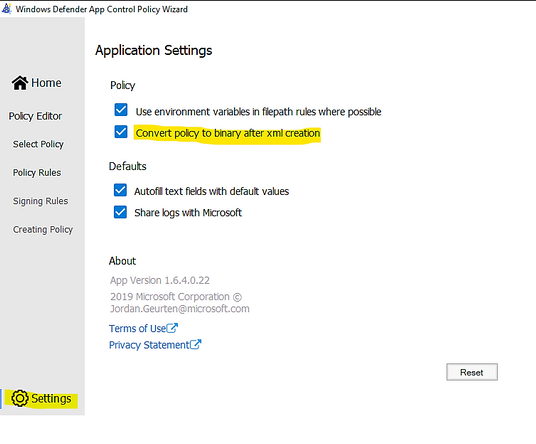
- Make sure to let WDAC Wizard to create the binary file if you need it in Settings – “Convert policy to binary after xml creation” as shown in the following:
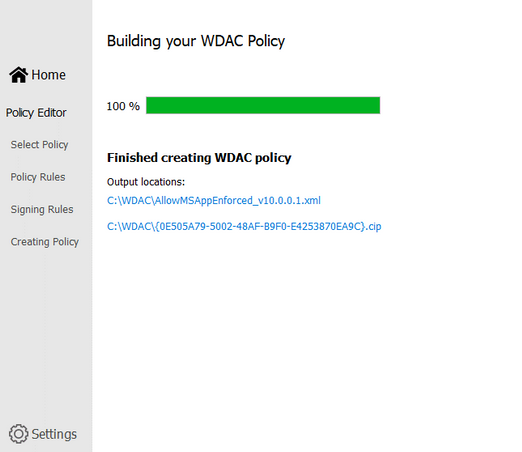
- Next, Wizard will build the WDAC Policy in xml format. You could close the Wizard once it finishes the task.
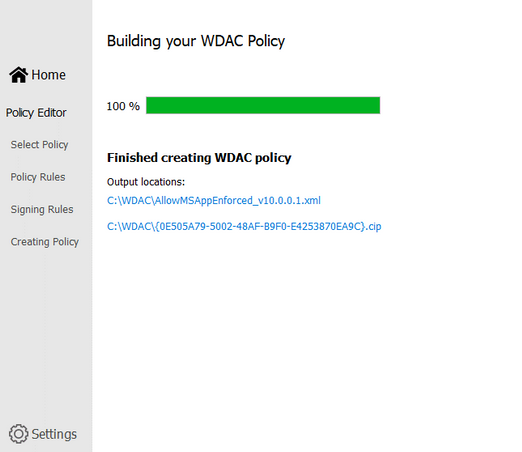
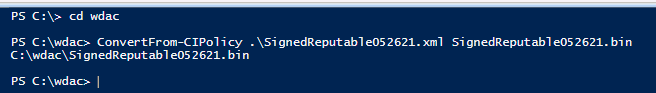
- Run Powershell, cd to the location of WDAC Policy
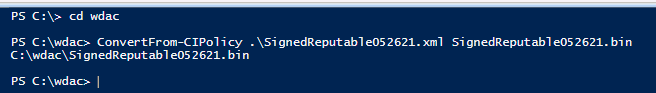
- Convert .xml policy to binary:
> ConvertFrom-CIPolicy .SignedReputable052621.xml SignedReputable052621.bin
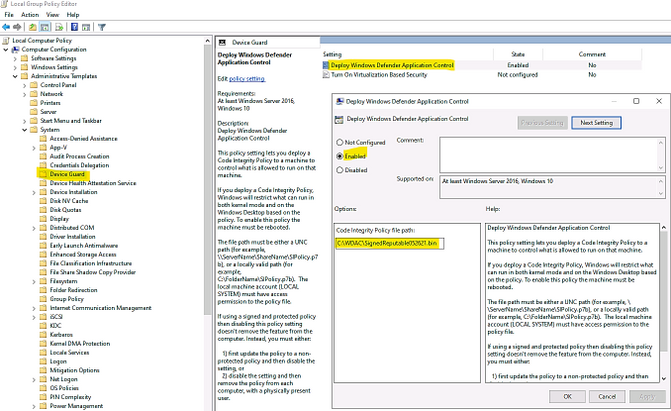
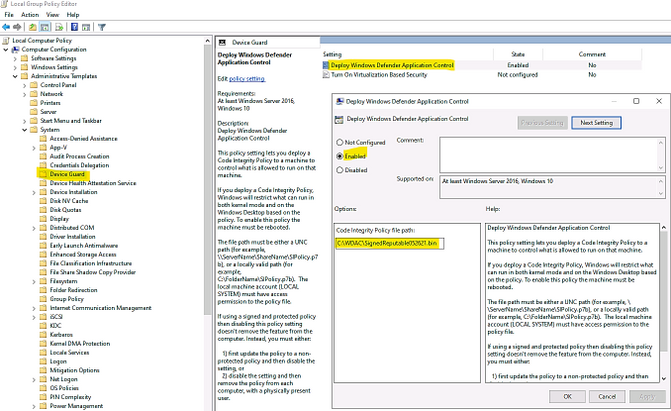
- Applying WDAC binary policy to targeted device by GPO or Local Group Policy:
- Result: After reboot the windows 10 device the first time (needed only once) for WDAC Policy to be applied. We could test the access.
To Generate new WDAC Policy from current Audit Policy
While a WDAC policy is running in audit mode, any application that runs but are supposed to be denied according to WDAC Audit Policy, is logged in the
Applications and Services LogsMicrosoftWindowsCodeIntegrityOperational event log. Script and MSI are logged in the
Applications and Services LogsMicrosoftWindowsAppLockerMSI and Script event log. These events can be used to generate a new WDAC policy that can be merged with the original Base policy or deployed as a separate Supplemental policy, if allowed.
You must have already deployed a WDAC audit mode policy to use this process.
- To generate new policy from current one by Powershell:
- In an elevated PowerShell session, run the following commands to initialize variables used by this procedure. This procedure builds upon the Lamna_FullyManagedClients_Audit.xml policy introduced in Create a WDAC policy for fully managed devices and will produce a new policy called EventsPolicy.xml.
PowerShell
$PolicyName= “Lamna_FullyManagedClients_Audit”
$LamnaPolicy=$env:userprofile+”Desktop”+$PolicyName+”.xml”
$EventsPolicy=$env:userprofile+”DesktopEventsPolicy.xml”
$EventsPolicyWarnings=$env:userprofile+”DesktopEventsPolicyWarnings.txt”
- Use New-CIPolicy to generate a new WDAC policy from logged audit events. This example uses a FilePublisher file rule level and a Hash fallback level. Warning messages are redirected to a text file EventsPolicyWarnings.txt.
PowerShell
> New-CIPolicy -FilePath $EventsPolicy -Audit -Level FilePublisher -Fallback Hash –UserPEs -Mul
More detail here.
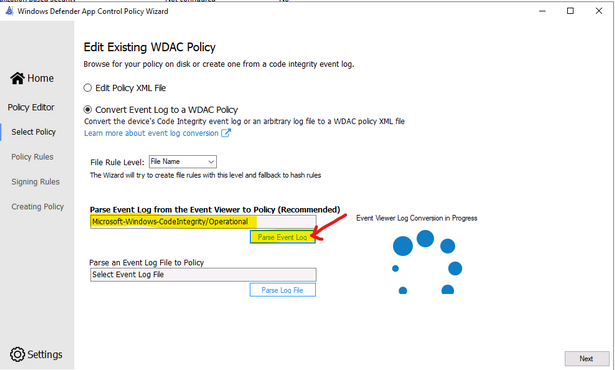
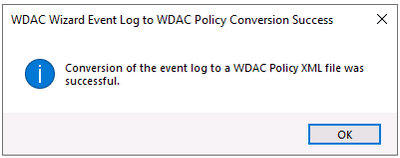
- To generate new policy from current one by WDAC Wizard:
- Run the WDAC Wizard, Policy Editor
- Enter the Event log and click “Parse…”
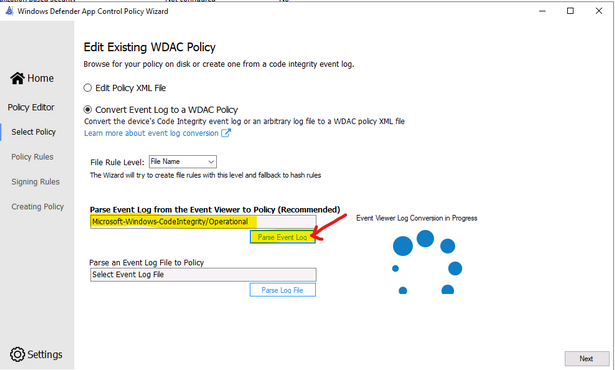
- When get the prompt, click OK, Next
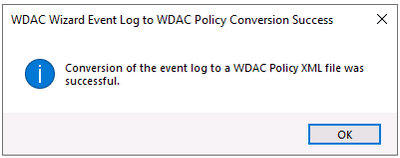
- Next, … and close the Wizard after policy is created.
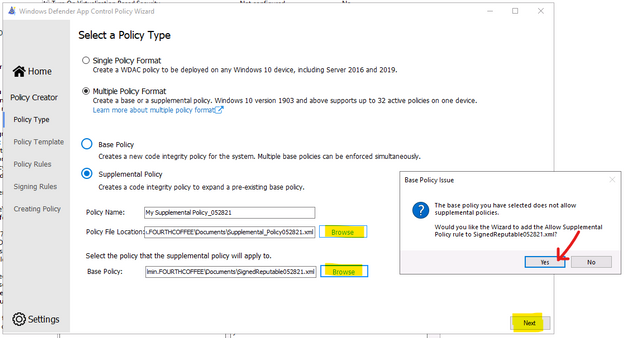
To Create Suplemental Policy from a base policy by WDAC Wizard
- Run WDAC Wizard from Windows Start Menu.
- Choose Policy Creator mode
- Click Multiple Policy Format
- Choose Supplemental Policy
- Browse to Supplemental Policy location
- Browse to Base Policy location
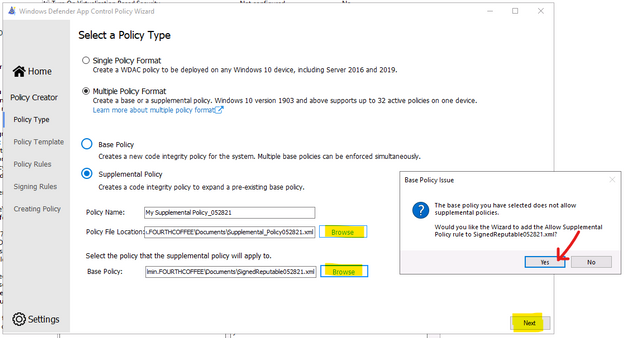
- Next, Create policy and close the Wizard.
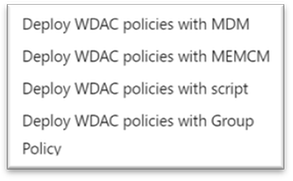
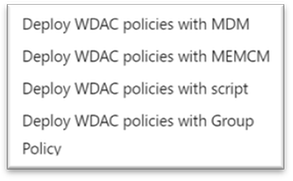
DEPLOYING WDAC POLICY
There are 4 ways to deploy WDAC:
To activate the WDAC Policy binary file to WMI repository.
- Another option is using Github AaronLocker Script, You can easily customize rules for your specific requirements with simple text-file edits. AaronLocker includes scripts that document AppLocker and WDAC policies and capture event data into Excel workbooks that facilitate analysis and policy maintenance. AaronLocker is designed to restrict program and script execution by non-administrative users.
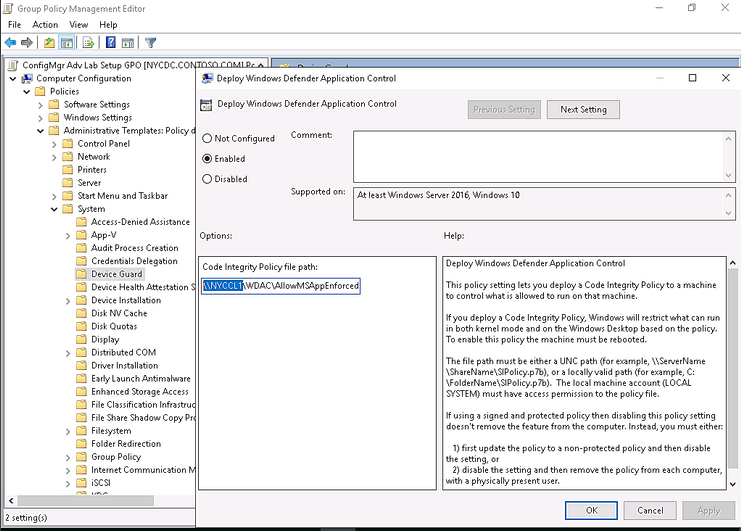
- Deploying WDAC Policy by GPO for Domain’s devices.
Group Policy-based deployment of WDAC policies only supports single-policy format WDAC policies. To deploy multiple policy for Windows 10 version 1903 and later, you will need to use other deploying mechanisms.
You can copy the WDAC policies to a file share to which all computer accounts have access, e.g: NYCCL1WDACAllowMSAppEnforcedV3.bin:
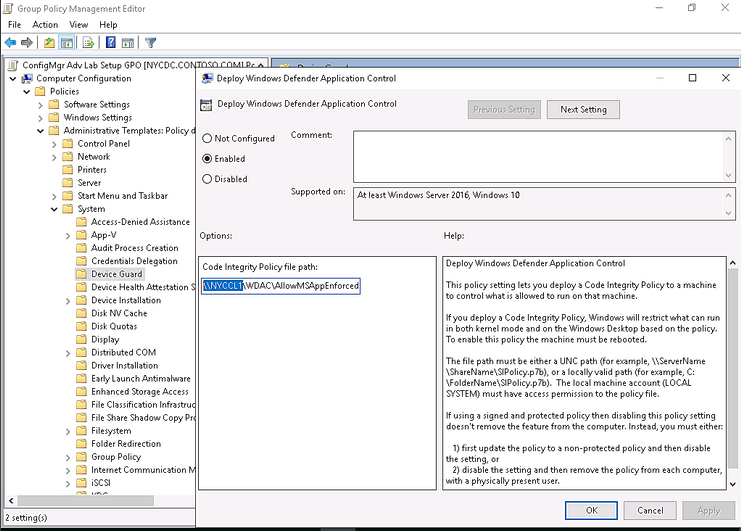
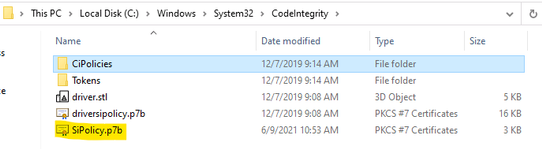
- Regardless of the type of policy you deploy (.bin, .p7b, or .p7), they are all converted to SIPolicy.b7p in directory WindowsSystem32CodeIntegrity when WDAC is applied to Client Windows 10
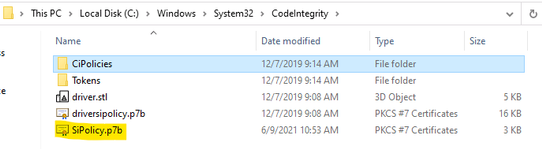
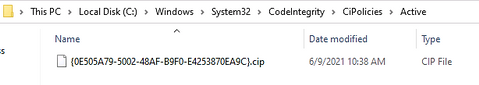
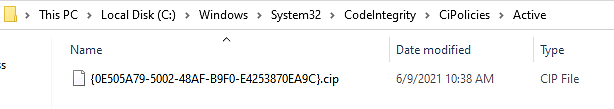
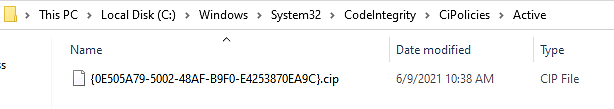
- For multiple policies, they are in {Policy GUID}.cip policy files found in the WindowsSystem32CodeIntegrityCIPoliciesActive folder once WDAC Policy is applied to Client Windows 10.
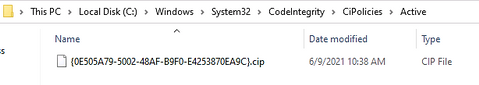
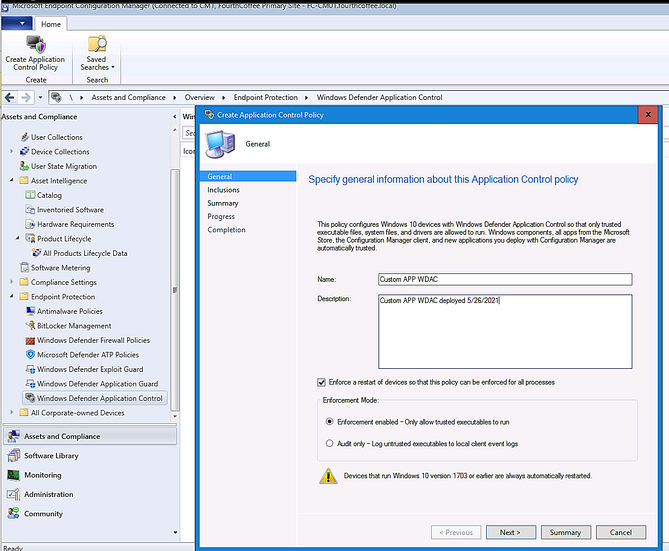
- Deploying WDAC Policy by MECM (SCCM) for Device Collection.
An Example is shown here:
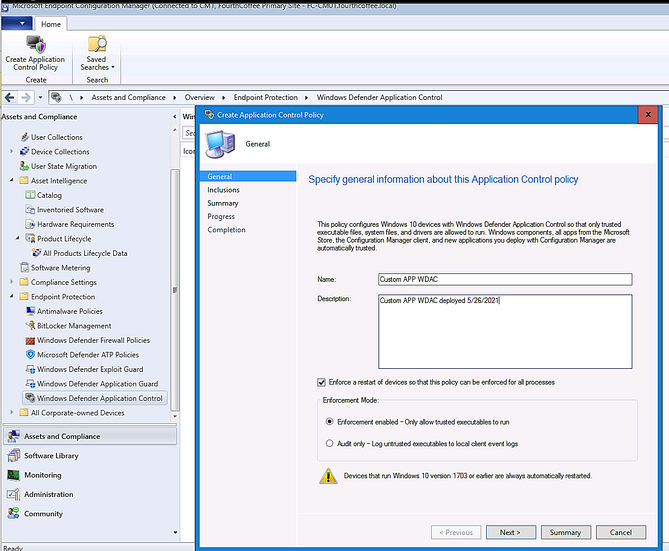
> Adding File or Folder path as shown here:
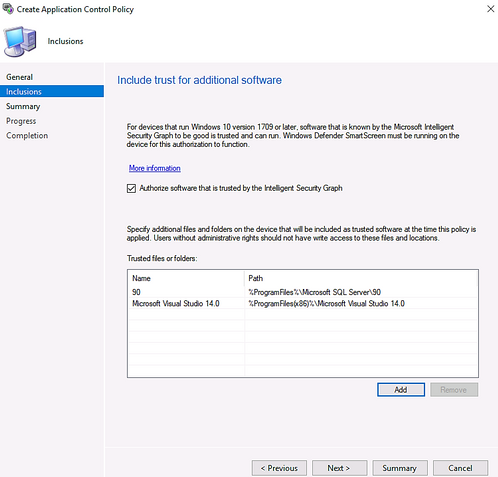
> Next and Close.
- Deploy WDAC Policy by MDM (Intune)
Intune includes native support for WDAC which can be a helpful starting point, but customers may find the available circle-of-trust options too limiting. To deploy a custom policy through Intune and define your own circle of trust, you can configure a profile using Custom OMA-URI.
An Example:
- OMA-URI: ./Vendor/MSFT/ApplicationControl/Policies/Policy GUID/Policy
- Data type: Base64
- Certificate file: upload your binary format policy file. You do not need to upload a Base64 file, as Intune will convert the uploaded .bin file to Base64 on your behalf.
After the first reboot to apply the WDAC Policy, then, only Office 365 applications, and Allowed Applications ( Acrobat DC) are able to run. Others (like Chrome) will be blocked as shown here:
Also, you could download and install applications but you could not run it as shown here:
To Monitor WDAC Events
A Windows Defender Application Control (WDAC) policy logs events locally in Windows Event Viewer in either enforced or audit mode. These events are generated under two locations:
- Event IDs beginning with 30 appear in Applications and Services logs – Microsoft – Windows – CodeIntegrity – Operational
- Event IDs beginning with 80 appear in Applications and Services logs – Microsoft – Windows – AppLocker – MSI and Script
Microsoft Windows CodeIntegrity Operational log event IDs
Event ID
|
Explanation
|
3076
|
Audit executable/dll file
|
3077
|
Block executable/dll file
|
3089
|
Signing information event correlated with either a 3076 or 3077 event. One 3089 event is generated for each signature of a file. Contains the total number of signatures on a file and an index as to which signature it is.
Unsigned files will generate a single 3089 event with TotalSignatureCount 0. Correlated in the “System” portion of the event data under “Correlation ActivityID”.
|
3099
|
Indicates that a policy has been loaded
|
Microsoft Windows Applocker MSI and Script log event IDs
Event ID
|
Explanation
|
|
8028
|
Audit script/MSI file generated by Windows LockDown Policy (WLDP) being called by the scripthosts themselves. Note: there is no WDAC enforcement on 3rd party scripthosts.
|
|
8029
|
Block script/MSI file
|
|
8038
|
Signing information event correlated with either a 8028 or 8029 event. One 8038 event is generated for each signature of a script file.
Unsigned script files will generate a single 8038 event with TotalSignatureCount 0.
|
|
Optional Intelligent Security Graph (ISG) or Managed Installer (MI) diagnostic events 3090, 3091, 3092
Event ID
|
Explanation
|
3090
|
Allow executable/dll file
|
3091
|
Audit executable/dll file
|
3092
|
Block executable/dll file
|
- The SmartLocker template which appears in the event should indicate why the binary passed/failed. Only one event is generated per binary pass/fail.
- If both ISG and MI are disabled, 3090, 3091, and 3092 events will not be generated.
Enabling ISG and MI diagnostic events
- In order to enable 3091 audit events and 3092 block events, you must create a TestFlags regkey with a value of 0x100.
- reg add hklmsystemcurrentcontrolsetcontrolci -v TestFlags -t REG_DWORD -d 0x100
- In order to enable 3090 allow events as well as 3091 and 3092 events, you must instead create a TestFlags regkey with a value of 0x300.
o reg add hklmsystemcurrentcontrolsetcontrolci -v TestFlags -t REG_DWORD -d 0x300
WDAC Tips
- Quick WDAC Policy applied to a testing Windows 10 device without GPO or Deployment Mechanism:
To apply the policy immediately,
- copy the {Policy GUID}.cip binary policy created by the WDAC Wizard location to the CodeIntergrity Active Foder in :
WindowsSystem32CodeIntegrityCIPoliciesActive folder
- Reboot device after copying policy to the above folder.
- To Control Application Installation – Managed Installer:
- Specify managed installers by using the Managed Installer rule collection in AppLocker policy.
- Enable service enforcement in AppLocker policy.
- Enable the managed installer option in a WDAC policy.
Detailed steps as in Microsoft document “Configure a WDAC managed installer (Windows 10)”
- To prevent machine unbootable to Windows OS during WDAC testing period.
The denied rule of WDAC Policy related to system driver may cause a loss of OS on testing device.
In WDAC Wizard’ Settings, please make sure to enable “Boot Audit on Failure” feature, it will automatically switch policy mode from enforcement to audit if the system drivers failed to load due to denied rule of Policy. This will save OS from loss because of driver failure in boot procedure.
To prevent loss of OS :
- On testing device, run WDAC Wizard – Policy Editor
- Select your Policy xml file to open it
- Policy Rules, click Advanced Options as shown here:
- Click to turn on “Boot Audit on Failure”
- Next and close the Wizard.
- In WindowsSystem32CodeIntegrityCIPoliciesActive folder, replace the old .cip policy with new cip policy and reboot the device to apply new WDAC policy.
- To Generate an WDAC rule for Universal App WUA based on package name:
- Run WDAC Wizard and Create a Custom Rule based on package App as shown here:
- Type a word related name of package e.g: F5
- Search (button)
- Create Rule
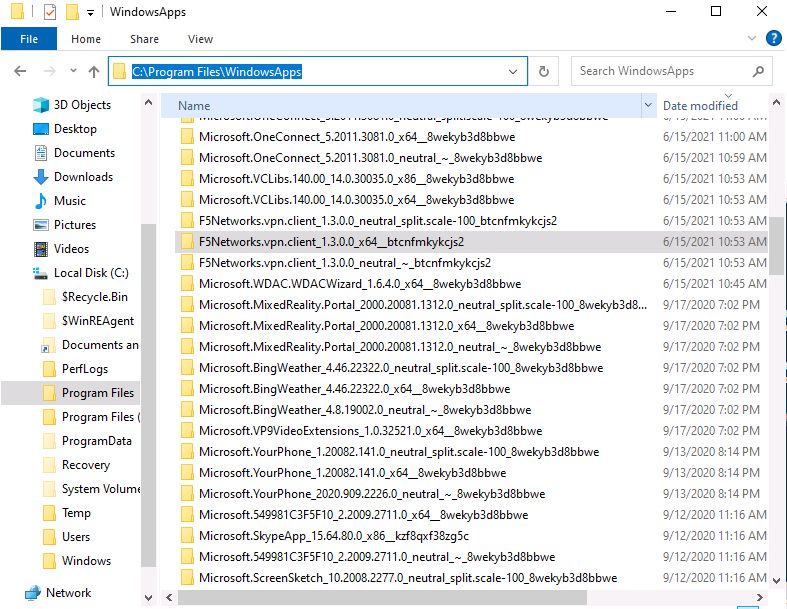
To view the name of your package if you do not know the exact name of WUA
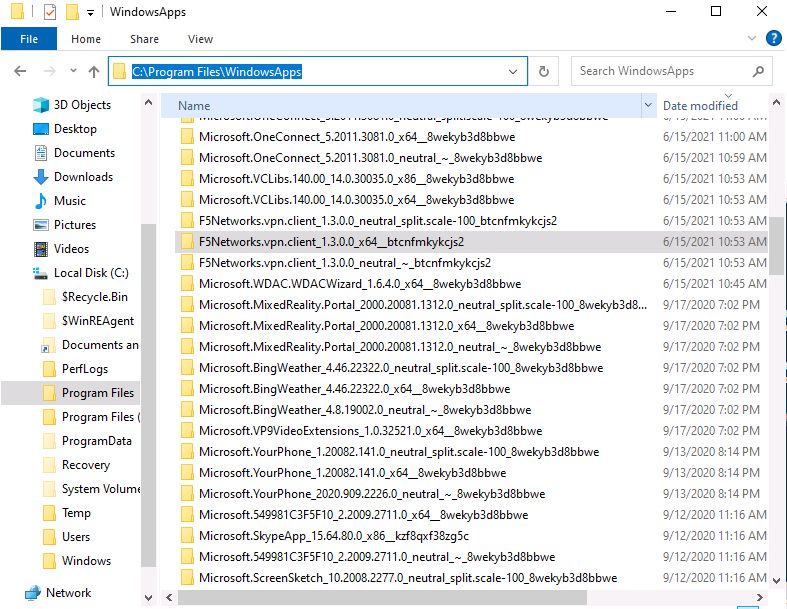
- Go to C:Program FilesWindowsApps
- View your WUA apps ID
I hope the information is useful for your WDAC deployment. Then, until next time.
Reference:
Disclaimer
- The sample scripts are not supported under any Microsoft standard support program or service. The sample scripts are provided AS IS without warranty of any kind. Microsoft further disclaims all implied warranties including, without limitation, any implied warranties of merchantability or of fitness for a particular purpose. The entire risk arising out of the use or performance of the sample scripts and documentation remains with you. In no event shall Microsoft, its authors, or anyone else involved in the creation, production, or delivery of the scripts be liable for any damages whatsoever (including, without limitation, damages for loss of business profits, business interruption, loss of business information, or other pecuniary loss) arising out of the use of or inability to use the sample scripts or documentation, even if Microsoft has been advised of the possibility of such damages.
by Contributed | Jun 25, 2021 | Technology
This article is contributed. See the original author and article here.
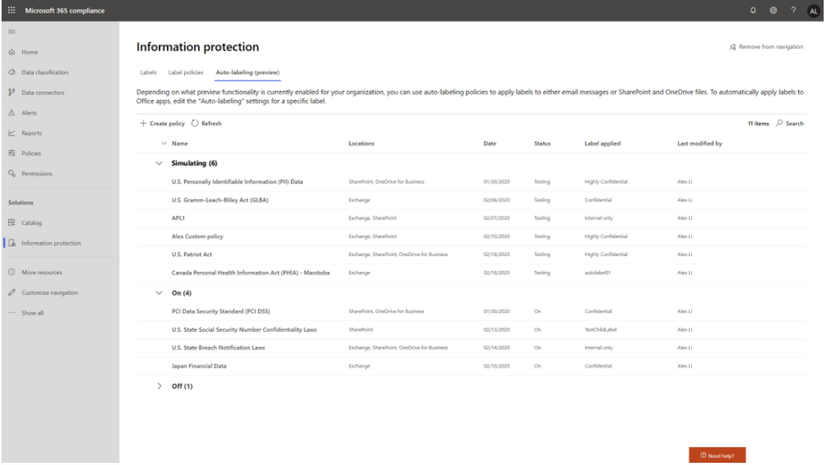
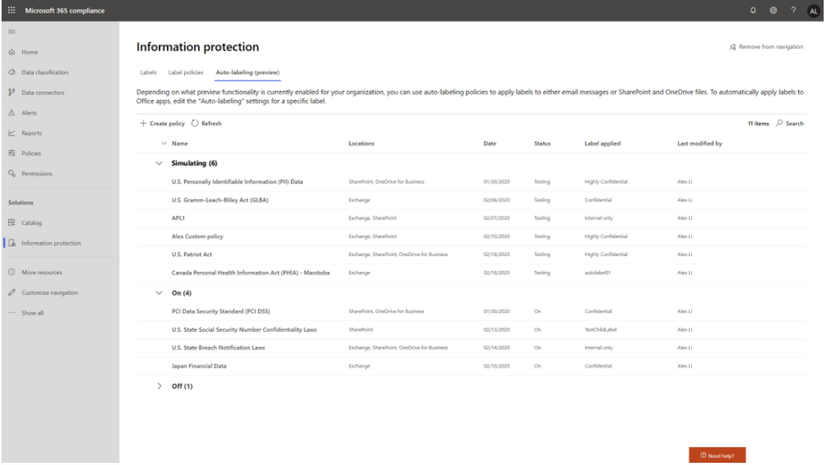
Throughout the last several months there have been many new features, updates, and happenings in the world of Information Protection at Microsoft. As we continue to build out more of this story, we wanted to use this opportunity to connect with customers, partners, and more on some of these updates to keep you informed and provide a single pane of glass on everything we have been working on for the last several months. In addition, we hope to give you some insight into the next big things being built within MIP overall.
Microsoft Information Protection:
General Availability: Mandatory Labeling
General Availability: Improvements for Exchange Online service side auto-labeling
Public Preview: Co-authoring
- Co-authoring and AutoSave on Microsoft Information Protection-encrypted documents
- Client-based automatic and recommended labeling on Mac
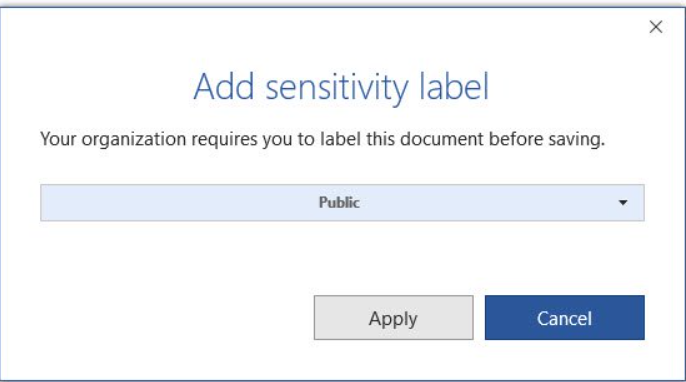
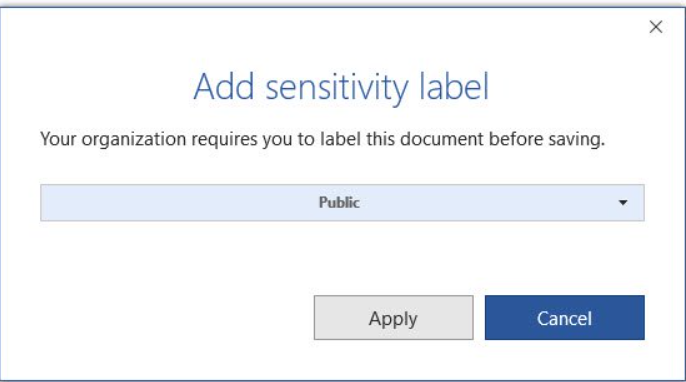
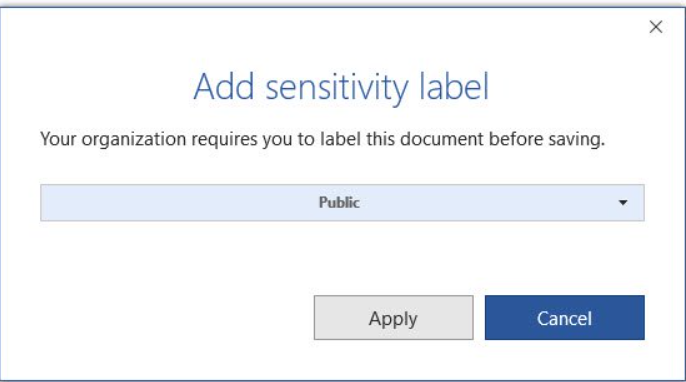
- Mandatory labeling requiring users to apply a label to their email and documents
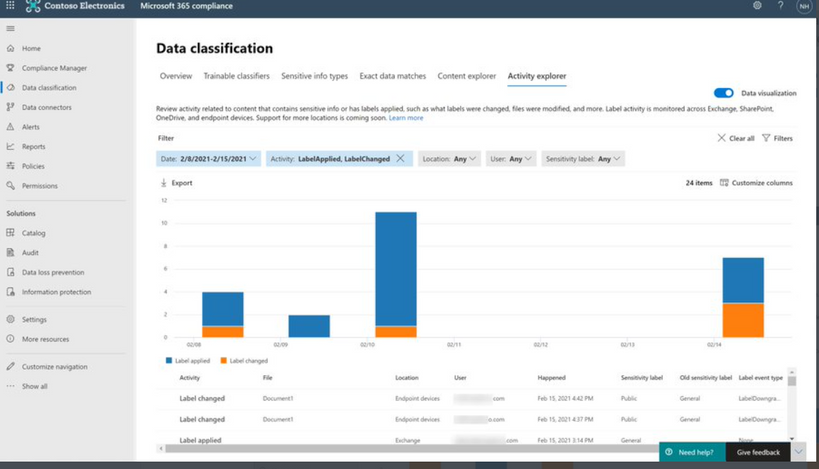
- Availability of audit label activities in Activity Explorer
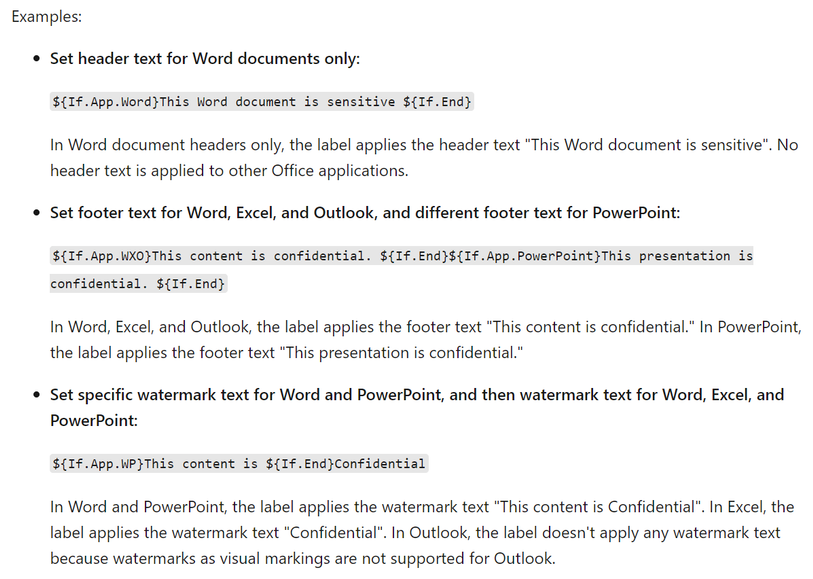
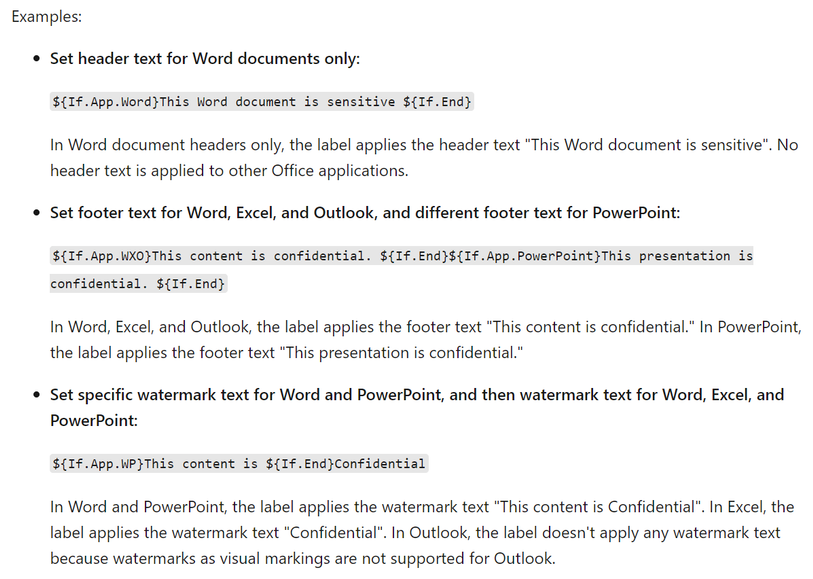
- Native support for variables and per-app content marking
- You can leverage co-authoring using:
- Production or test tenant
- Microsoft 365 apps with the following versions:
- Windows – Current Channel 16.0.14026.20270+ (2105)
- Mac: 16.50.21061301+
- If AIP Unified Labeling Client Version is in use, verify that in addition to the updated Microsoft 365 app, you use version 2.10.46.0 of the Unified Labeling client.
- PLEASE NOTE: That Co-authoring for Native/Built-In Labeling will be added in the upcoming Current Channel within 2 weeks
Read more about the feature at Enable co-authoring for documents encrypted by sensitivity labels in Microsoft 365 – Microsoft 365 Compliance | Microsoft Docs
Public Preview: AIP Audit Logs in Activity Explorer
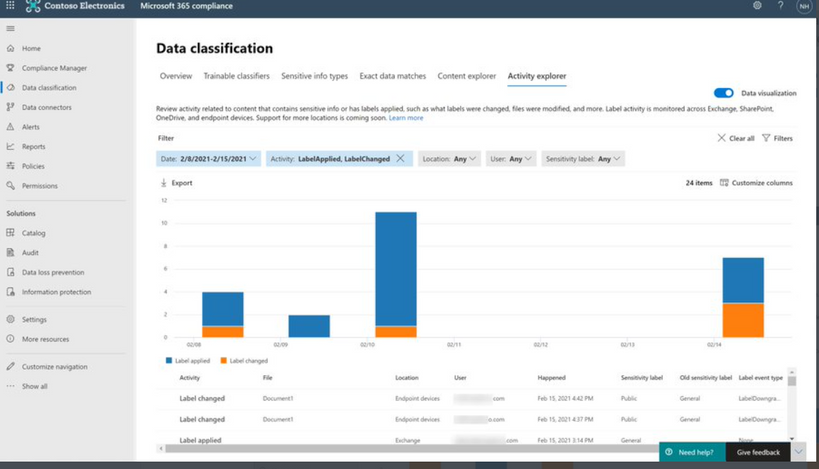
General Availability: Dynamic Markings with Variables within native labeling across all platforms
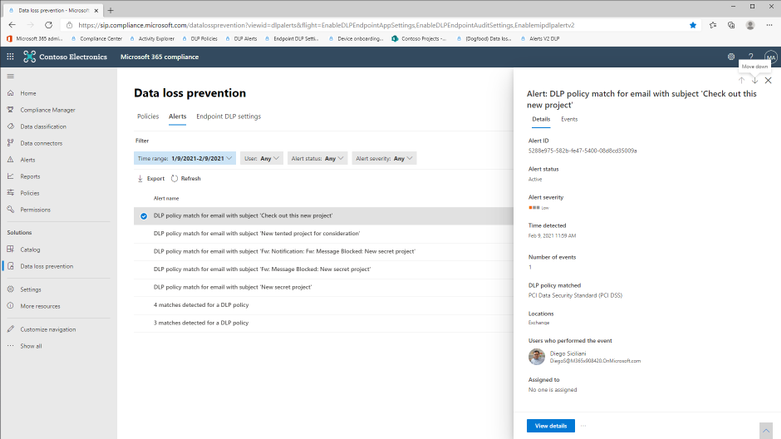
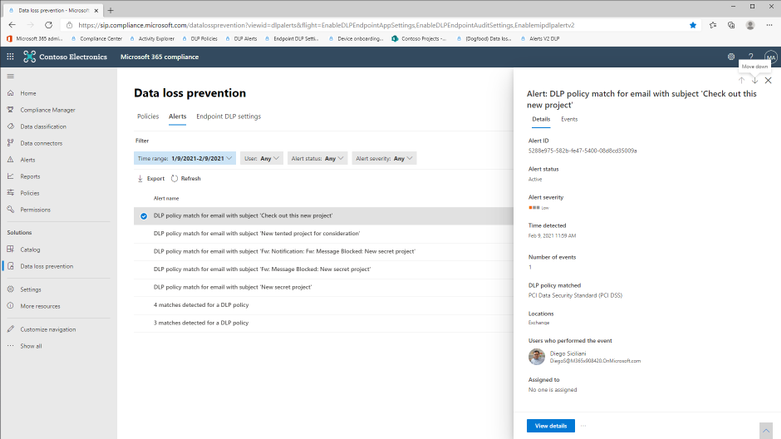
GA: DLP Alerts
Microsoft announces the General Availability of the Microsoft Data Loss Prevention Alerts Dashboard. This latest addition in the Microsoft’s data loss prevention solution provides customers with the ability to holistically investigate DLP policy violations across:
- Exchange
- SharePoint Online
- OneDrive
- Teams
- Devices
- Cloud apps
- On-premises file shares
Learn more about the feature at: Learn about the data loss prevention Alerts dashboard – Microsoft 365 Compliance | Microsoft Docs
Azure Information Protection:
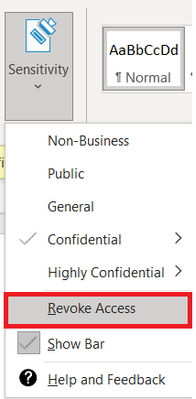
GA: Track and Revoke
- Document tracking provides information for administrators about when a protected document was accessed.
- If necessary, both admins and users can revoke document access for protected tracked documents.
- This feature is available for AIP UL client version 2.9.111.0 or later
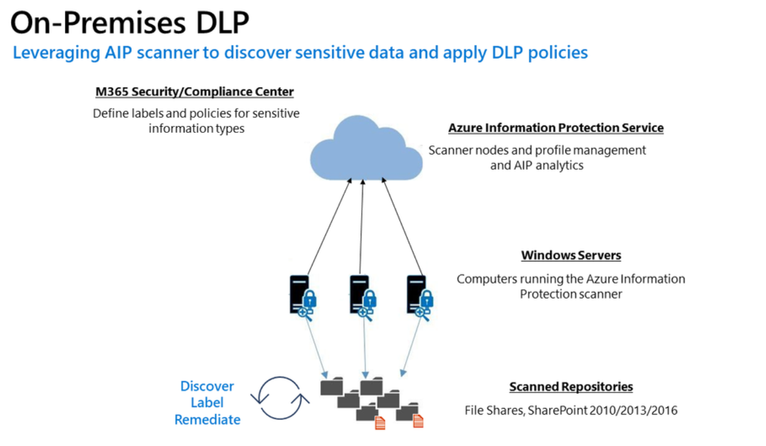
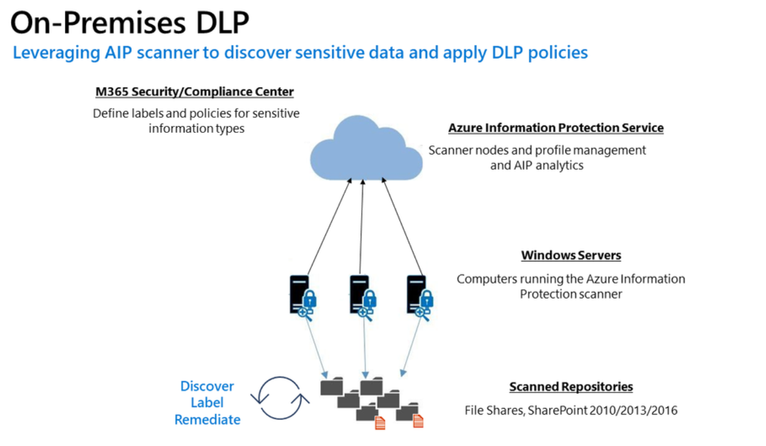
Public Preview: DLP On-Prem
- The DLP on-premises scanner crawls on-premises data-at-rest in file shares and SharePoint document libraries and folders for sensitive items that, if leaked, would pose a risk to your organization or pose a risk of compliance policy violation
- This gives you the visibility and control you need to ensure that sensitive items are used and protected properly, and to help prevent risky behavior that might compromise them
- You need to leverage the Scanner binaries from AIP UL Client Version 2.10.43.0

![[Guest Blog] At the Intersection of Mixed Reality and Business Applications: My Career Journey](https://www.drware.com/wp-content/uploads/2021/06/fb_image-1184.png)









Recent Comments