by Contributed | Dec 11, 2023 | Technology
This article is contributed. See the original author and article here.
Enhancing frontline manager productivity remains a critical priority for countless organizations and Microsoft. We are excited to introduce a range of new Shifts features to further empower our frontline heroes through seamless evolution that aligns perfectly with your ever-changing needs, all thanks to your invaluable feedback. Let’s unwrap some of the highlights.
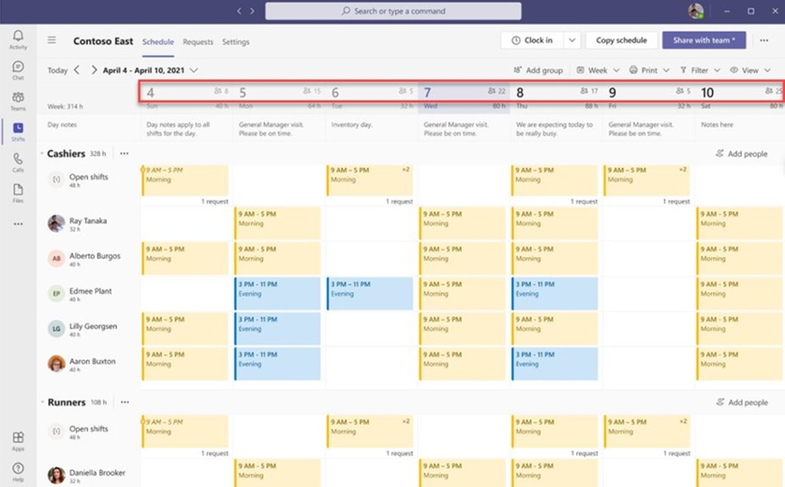
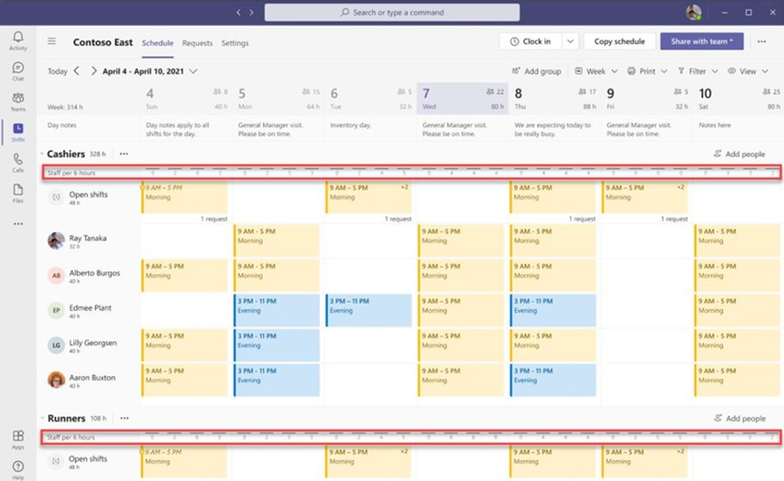
1. People Count Display on Shifts Calendar
Frontline managers (FLM) can now make informed staffing decisions with the introduction of the people count displayed on the Shifts calendar. This feature provides a clear view of staffing levels, ensuring that the right workforce is scheduled for the day, week, or month. Managers can now see the scheduled people count at both the team, and schedule group levels.
2. Core UX Improvements
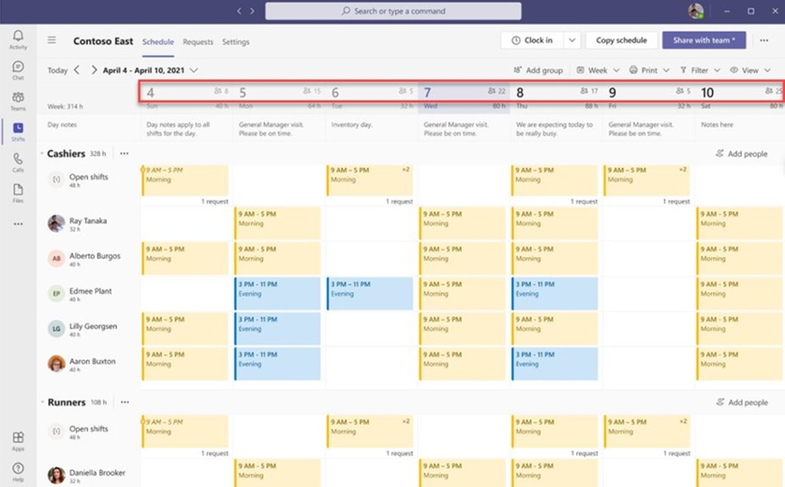
We’ve streamlined the user experience with some core improvements:
1) Full Name Display: Team members’ full names are now visible in the team schedule. This helps managers quickly identify staff members by their full names, even when names are lengthy, by toggling profile pictures on/off.
2) Saving Last Used Filter: We understand that frontline managers and workers use various filters to customize their Shifts view. Our latest feature automatically saves the last used filter, so when users relaunch the Shifts app, their preferred view from the last session is readily available.
3) Shifts notes in Day view: Day view shows the shift notes inline, which helps managers save time.
3. Manager-Controlled Settings
Frontline Managers now have additional controls on team-level settings that provide the ability to control all our Shifts marketplace and visibility capabilities.
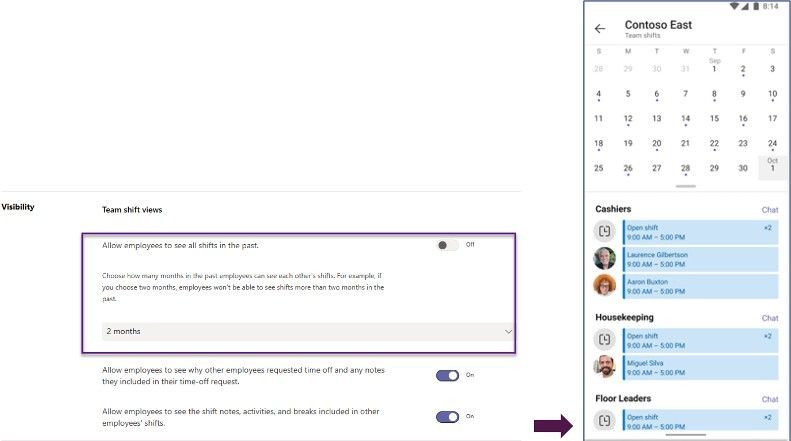
1) Visibility controls: Frontline managers can control shift information visibility for their Frontline Workers (FLW).
Limited Past Views: Managers can restrict how far back FLWs can view their coworkers’ schedules, ensuring historical data privacy.
When FLM configure the past schedule view up to certain months – FLWs cannot see other’s schedules beyond the configured duration.
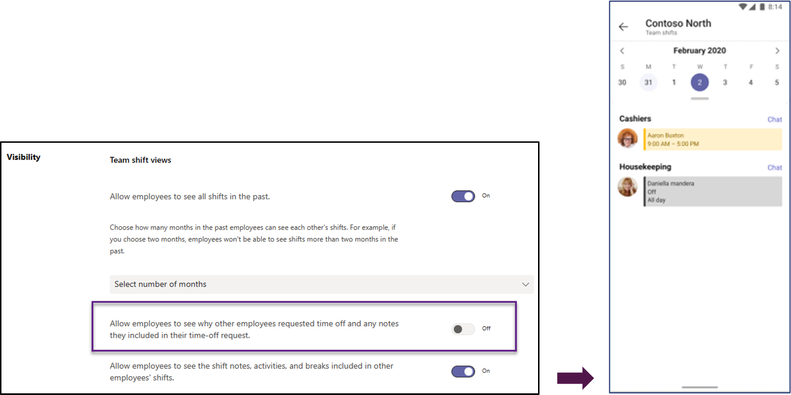
Generic Time Off View: FLWs can see their colleagues’ time off in a generic way, without access to specific reasons and notes.
When FLM’s disable the visibility of time off reason and notes – FLWs see a generic time off reason of other FLW’s.
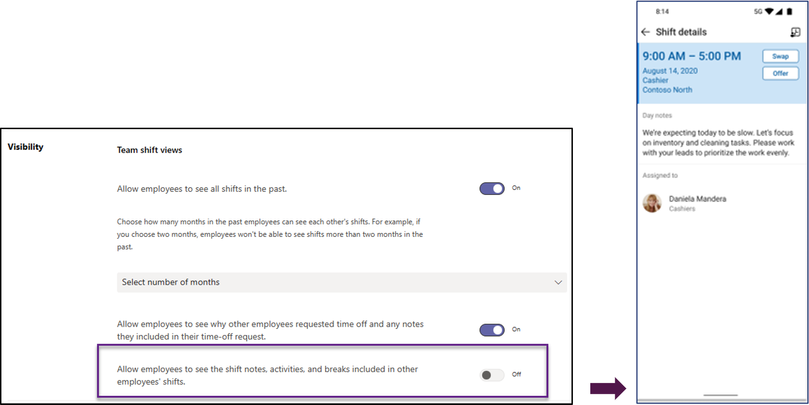
Limited Shift Details: Managers can limit the level of detail available to FLWs about their coworkers’ schedules, excluding sensitive information like Shift notes, Activities, and break duration.
When FLM’s disable the visibility of shift notes, activities, break duration – FLWs cannot see the shift details of other FLWs.
2) Shifts marketplace controls: Your organization can pace the journey towards frontline self-serve capabilities through your frontline managers ability to choose which capabilities should be offered to their workers. We have added the following new controls:
Swap shift requests: Frontline managers can decide if workers can create requests to swap their shifts with other coworkers. The requests require managers’ approval before becoming effective on the Shifts calendar.
Offer shift requests: Frontline managers can decide if workers can create requests to offer their shifts to another coworker. The requests require managers’ approval before becoming effective on the Shifts calendar.
Time off requests: Frontline managers can decide if workers can create requests for time off work. The requests require managers’ approval before becoming effective on the Shifts calendar.
4. Graph API for Day Notes
Now, managers have the flexibility to add day notes using the Graph API, in addition to the Shifts app. This powerful capability allows customers to seamlessly integrate relevant day notes from third-party, or line-of-business applications, enhancing the Shifts experience.
dayNote resource type – Microsoft Graph beta | Microsoft Learn
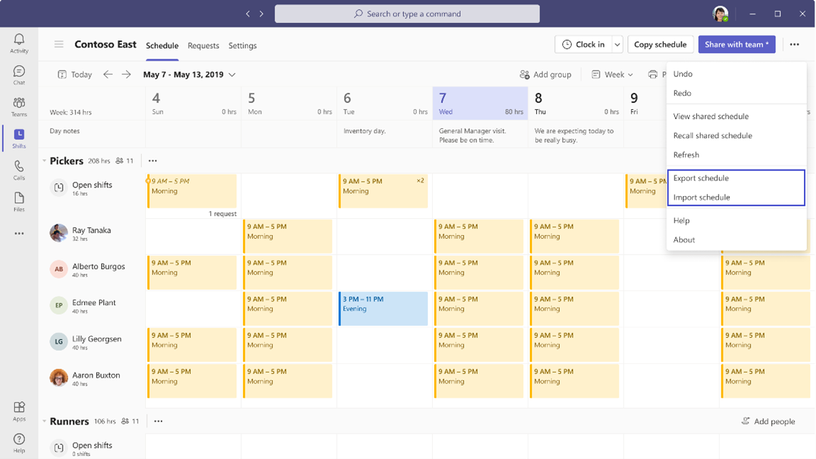
5. Import and export time offs and open shifts into Excel
Managers using Shifts web and desktop applications are now allowed to import not only assigned shifts, but also open shifts and time offs from Excel into Shifts. Additionally, these same schedule entities will be supported when managers export a schedule in a format compatible to the import.
What’s coming next –
Setting Availability by date: Frontline workers can set their availability on specific dates in addition to their recurring availability.
These enhancements are a result of listening to your feedback, and we’re committed to continuing to improve Shifts to meet your evolving needs. We hope these new features empower your frontline teams and streamline your workforce management processes.
We value your input! Please take a moment to share your thoughts via this brief survey and include your email for any further queries. We’re eager to connect with you!
by Contributed | Dec 10, 2023 | Technology
This article is contributed. See the original author and article here.
Unlocking Value with the Power Platform
For years now, the Power Platform has been a low code tool that unlocks value across your business by accelerating application & automation development to meet business demand faster. Whether you’re a professional developer, an IT admin, business analyst, or a non-technical employee, low code empowers you to create solutions in a fast, secure, and compliant fashion. Now with the rise of AI, organizations are moving quickly to embrace AI in order to usher in a new wave of growth and value creation.
Introducing the Livestream Series: Let’s Learn Power: A Real-life AI + Power Platform Use Case
With that, I am excited to announce a 3-part livestream series which will be hosted on the Microsoft Reactor channel that focuses on bringing the Power Platform and AI together. The series is titled Let’s Learn Power: A Real-life AI + Power Platform Use Case and it explores the integration of the Power Platform with advanced AI models to create a dynamic application inspired by Kevin Scott’s Microsoft Build 2023 demo. This application makes it easy to generate a social media post promoting a new episode of your podcast. Starting from a podcast URL, we journey through speech-to-text transcription to generate a transcript of the podcast, given that transcript, we perform guest identification and guest bio retrieval, followed by social media post generation with image creation, and finally, posting to LinkedIn from Power Apps or Copilot Studio. All powered by Azure OpenAI Service and the Power Platform AND I will walk you through it all from start to finish.
As mentioned, there will be 3 episodes livestreamed on the following dates and times:
Episode 1: Laying the Foundation: Azure Open AI Service and Power Platform
Dive into the world of Azure OpenAI Service. We introduce the service, describe the models, and guide you through creating deployments. Setting the stage for seamless AI integration.
11 December 2023 | 9AM PST | 7PM SAST
Episode 2: Bridging the Gap: .NET APIs, Azure, and Custom Connectors
We take a step further from Episode 1 by creating a .NET API using the .NET Azure OpenAI SDK, creating Azure Resources with the Azure Developer CLI, deploying the API to Azure App Service and Azure API Management and Creating a Custom Connector from API Management.
12 December 2023 | 9AM PST | 7PM SAST
Episode 3: The Final Touch: Power Apps and Microsoft Copilot Studio Integration
The final episode brings it all together. We will build the Power App UI, connect to the Custom Connector, and publish the social media post to LinkedIn. As a bonus, we will also see how to implement this workflow with a Microsoft Copilot Studio custom copilot.
13 December 2023 | 9AM PST | 7PM SAST
You can register to watch all 3 livestreams here: Register Now! and can’t wait to see you there!

by Contributed | Dec 9, 2023 | Technology
This article is contributed. See the original author and article here.
Embark on a Holiday Coding Adventure with GitHub Copilot
Hello students! Are you looking for a fun and engaging way to learn new coding concepts and languages over the holiday season? If so, you might want to check out Microsoft Copilot Adventures, a series of coding challenges powered by GitHub Copilot, an AI pair programmer that assists you in writing better code.
In this article, we’ll show you how to start your adventure, choose from different levels of difficulty and topics, and use GitHub Copilot hints to help you write your code. You’ll also learn how to share your solution with others and get feedback.
Whether you’re a beginner or an expert, Microsoft Copilot Adventures will help you improve your coding skills and have fun at the same time. So, what are you waiting for? Start your adventure today!

Welcome to Coding Adventure with GitHub Copilot
We are going to introduce you to an exciting series of coding adventures that will help you learn new concepts and languages over you holiday vacation period. This adventure experience and activities is brought to you by none other than GitHub Copilot, an AI pair programmer that assists you in writing better code.
What is GitHub Copilot?
GitHub Copilot is a tool designed to assist you in writing code. It’s like having a pair programmer who’s always ready to help.Whether you’re a beginner just starting out or an experienced coder looking to learn a new language, GitHub Copilot can be a valuable companion on your coding journey
How to Start Your Adventure
To get started, you’ll need to enter the “adventure area”. This is done by creating a GitHub Codespace Don’t worry, you can use 60 hours of GitHub Codespaces for free each month and if your registered GitHub Student Education pack user you get FREE access to codespaces Alternatively, you can clone the repo and run it locally.
Choose Your Adventure
Once you’ve set up your environment, it’s time to choose your adventure. There are several adventures available, each designed to challenge your coding skills and help you learn new concepts
Beginner Adventures
Intermediate Adventures
Advanced Adventures
Start Coding
After choosing your adventure, you’ll be given a description, high-level tasks to perform, and GitHub Copilot hints to help you write your code. You can use any language you’d like.If you’re up for a challenge, try learning a new language.
Share Your Adventure
If you’d like to share your solution with others, you can publish your adventure solution to a GitHub repo. Then, visit the issues page and select ‘New Issue’. Use the following naming convention for the issue title: ‘Solution for [Name of Your Adventure]’. Replace ‘[Name of Your Adventure]’ with the adventure name you chose to solve .
Conclusion
Embarking on a Holiday coding adventure with GitHub Copilot is a fun and engaging way to learn new coding concepts and languages. So, what are you waiting for? Start your adventure today!
Happy coding!

by Contributed | Dec 8, 2023 | Technology
This article is contributed. See the original author and article here.
In this blog series dedicated to Microsoft’s technical articles, we’ll highlight our MVPs’ favorite article along with their personal insights.
Sangkon Han, Developer Technologies MVP, Korea

Write your first code using C# (Get started with C#, Part 1) – Training | Microsoft Learn
“Although it is a beginner-level document provided by Microsoft, it is difficult for all beginners to read such documents. Therefore, as someone who is also learning C# for the first time, I have organized the contents of this document into a video. I hope that beginner C# learners can learn C# more easily and enjoyably, and I want to share this content with many people.”
(In Korean, MS에서 제공하는 초급자 문서이지만, 모든 초급자는 이러한 문서 조차 읽기 어렵습니다. 그래서 저도 C#을 처음 배운다는 입장에서 해당 문서의 내용을 영상으로 정리하였습니다. C# 초급 입문자가 조금 더 쉽고, 즐겁게 C#을 배울 수 있기를 희망하며 이 컨텐츠를 많은 사람들에게 알리고자 합니다.)
*Relevant Activity: This is my YouTube video .NET Starter 2023 – YouTube which explains this document.
(In Korean, 문서보다는 YouTube 영상을 통해서 진행하였습니다. 영상의 링크는 .NET Starter 2023 – YouTube 입니다.)
Elie Karkafy, Security, Enterprise Mobility MVP, United States

Azure updates | Microsoft Azure
“Get the latest updates on Azure products and features to meet your cloud investment needs.”
Takashi Takebayashi, Microsoft Azure MVP, Japan

Tutorial – Add app authentication to a web app on Azure App Service – Azure App Service | Microsoft Learn
“If we develop our own application that maintains unique usernames and passwords, the administrative burden becomes significant when adding or removing users across multiple applications. We also have to handle situations where a user forgets their email address. Alternatively, we can delegate this responsibility to a centralized ID provider, but many ID providers are very expensive. However, Microsoft’s authentication and authorization system is very affordable and easy to implement. Therefore, it’s content that many people should be aware of.”
(In Japanese, 独自のユーザー名とパスワードの情報を保持するアプリケーションを自分たちで開発した場合、複数のアプリケーションにまたがってユーザーを追加・削除するときに管理上の負担が大きくなります。またメールアドレスをユーザーが忘れた場合の対処も自分たちでしなくてはなりません。代わりにその責任を一元化された ID プロバイダーに委任できますが、多くの ID プロバイダーは非常に高額です。しかし、Microsoft の認証認可システムは非常に安価であり、簡単に実装もできます。そのため、多くの人に知ってもらいたいコンテンツです。)
Yutaro Tamai, Enterprise Mobility, Windows and Devices MVP, Japan

MD-102 1-Deploy Devices using Windows Autopilot – Training | Microsoft Learn
“In this eta, managing Windows devices is required for cloud-native management approach. This is good content to learn about device setup through Windows Autopilot. Why not start by getting familiar with Windows Autopilot and deepening your understanding of the latest device setup methods?”
(In Japanese: Windows デバイスの管理もクラウド ネイティブの管理手法が求められる時代です。その中で、Windows Autopilot によるデバイス セットアップの手法を学ぶに良いコンテンツです。まずは、Windows Autopilot に触れ、最新のデバイス セットアップの手法に理解を深めてみませんか。)

by Contributed | Dec 7, 2023 | Business, Gartner Magic Quadrant, Microsoft 365, Technology
This article is contributed. See the original author and article here.
We are honored to announce that Gartner® has recognized Microsoft as a Leader in the 2023 Gartner® Magic Quadrant™ for Unified Communications as a Service (UCaaS)—this is the fifth consecutive year we’ve received this recognition.
The post Microsoft named a Leader in 2023 Gartner® Magic Quadrant™ for Unified Communications as a Service for the fifth year in a row appeared first on Microsoft 365 Blog.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.


Recent Comments