Our Latest News
Sarah Romotsky of Headspace addresses selfcare for national nurses week
Claire Bonaci You're watching the Microsoft us health and life sciences, confessions of health geeks podcast, a show that offers Industry Insight from the health geeks and data freaks of the US health and life sciences industry team. I'm your host Claire Bonaci....
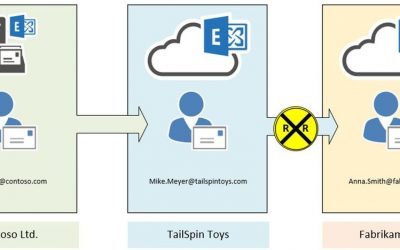
Loop Prevention in Exchange Online Demystified
We often get questions regarding mail forwarding in Exchange Online. As you already know, Exchange Online is a shared service. We must take care that users cannot take the service down by creating mail loops. It is sometimes a little confusing for our customers that...
Vulnerability Summary for the Week of April 26, 2021
akuvox -- c315 Akuvox C315 115.116.2613 allows remote command Injection via the cfgd_server service. The attack vector is sending a payload to port 189 (default root 0.0.0.0). 2021-04-25 not yet calculated CVE-2021-31726MISCMISC ambarella --...
Log Analytics pinned parts now works with Azure Dashboard filters
Intro: As we continue to improve our Log Analytics pinned parts experience to Azure Dashboards, we are happy to announce integration with dashboard filters. Integration with Dashboard filters: Log Analytics pinned parts are now integrated with dashboard...
Log Analytics UI – New experience for Custom Logs
Intro We continue to improve our experiences!The Custom Logs and custom fields screens get a new, dedicated experience in your log Analytics workspace. The new Custom Logs Blade: Reach your custom logs blade from the left hand navigation bar in your...
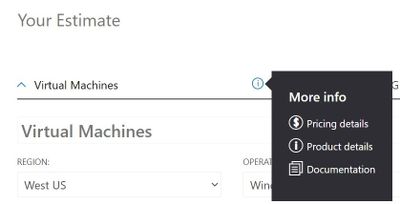
Understanding Microsoft Azure Virtual Machine sizes
Having an on-premises infrastructure background, I’m used to scoping hardware by defining the specifications (CPU, memory etc) we’ll need to run the applications and expected concurrent users and allowing for some growth. Then we’d often buy a box that would give us...
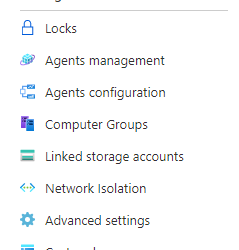
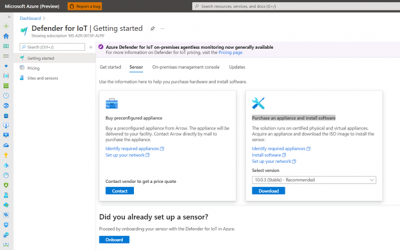
How to Quick Start with Defender for IoT Sensor onboarding and integration into Azure Sentinel
Azure Defender for IoT is a unified security solution for identifying IoT/OT devices, vulnerabilities, and threats. It enables organizations to secure entire IoT/OT environments, whether there is a need to protect existing IoT/OT devices or build security into new IoT...
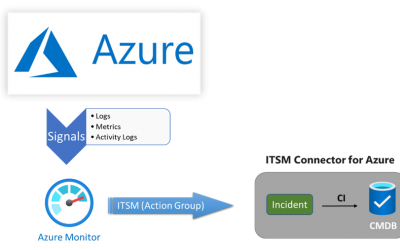
Set Your Alert State Using Azure Automation
Hello blog readers One of recurring questions during my customer engagements on Azure Monitor is: how do I set alert state to either Acknowledged or Closed with no manual intervention? This question is broader and deeper than it appears. In fact, linked...
Meet a Recent Microsoft Learn Student Ambassador Graduate: Ayush Chauhan
This is the next installment of our blog series highlighting Microsoft Learn Student Ambassadors who achieved the Gold milestone and have recently graduated from university. Each blog in the series features a different student and highlights their...
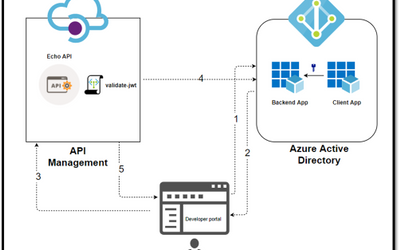
Protect API's using OAuth 2.0 in APIM
The API Management is a proxy to the backend APIs, it’s a good practice to implement security mechanism to provide an extra layer of security to avoid unauthorized access to APIs. Configuring OAuth 2.0 Server in APIM merely enables the Developer...
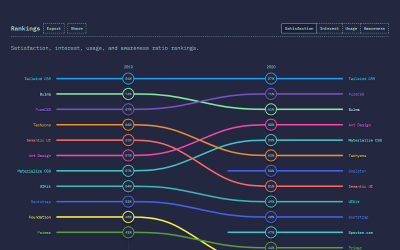
How to Set Up Tailwind CSS in a SPFx Project
In the State of CSS 2020 survey, the Tailwind CSS becomes the number 1 CSS Framework in terms of Satisfaction and Interest in the last 2 years. It also gets the awards for The Most Adopted Technology. It seems a lot of developers like this framework. Based on my...
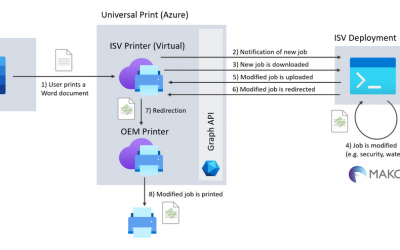
Enhance your Universal Print integration with the Mako SDK
The Mako™ Core SDK from Global Graphics Software is perfectly placed to help software vendors and service providers integrate with Universal Print. Our SDK can help developers analyze, edit, and convert the documents at the heart of Universal Print workflows. Case...



Recent Comments