Our Latest News
NSA-CISA Series on Securing 5G Cloud Infrastructures
The National Security Agency (NSA) and CISA have published the first of a four-part series, Security Guidance for 5G Cloud Infrastructures. Security Guidance for 5G Cloud Infrastructures – Part I: Prevent and Detect Lateral Movement provides recommendations for...
A blueprint for cross-organization collaboration: marketing and sales
It's one of the toughest challenges for organizations today: how to foster collaboration in a workplace that is more decentralized than ever, with people scattered across offices and locations.Working together to move business forward is nothing new, but the way we...
Cisco Releases Security Updates for Multiple Products
Cisco has released security updates to address vulnerabilities in multiple Cisco products. A remote attacker could exploit some of these vulnerabilities to take control of an affected system. For updates addressing lower severity vulnerabilities, see the Cisco...
ISC Releases Security Advisory for BIND
The Internet Systems Consortium (ISC) has released a security advisory that addresses a vulnerability affecting multiple versions of the ISC Berkeley Internet Name Domain (BIND). A remote attacker could exploit this vulnerability to cause a denial-of-service...
2021 CWE Most Important Hardware Weaknesses
The Homeland Security Systems Engineering and Development Institute, sponsored by the Department of Homeland Security and operated by MITRE, has released the 2021 Common Weakness Enumeration (CWE) Most Important Hardware Weaknesses List. The 2021 Hardware List is a...
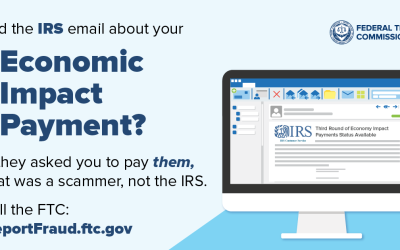
Scammers are sending fake IRS emails about Economic Impact Payments
There’s a fake IRS email that keeps popping into people’s inboxes. It says that you can get a third Economic Impact Payment (EIP) if you click a link that lets you “access the form for your additional information” and “get help” with the application. But the link is a...
The Google Voice scam: How this verification code scam works and how to avoid it
It’s Cyber Security Awareness month, so the tricks scammers use to steal our personal information are on our minds. If there’s one constant among scammers, it’s that they’re always coming up with new schemes, like the Google Voice verification scam. Have you heard...
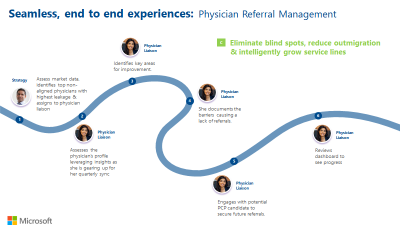
Voices of Healthcare Cloud brings you “ Physision Refferal & Relationship Management”
Voices of Healthcare Cloud is a webinar series hosted by myself, @Vasu Sharma & @Joshua Thompson. My name is Shelly Avery, I am currently a Dir, Healthcare Specialist for Health and Life Sciences focusing on the largest Payor and Provider customers in the US,...
Microsoft named a Leader in 2021 Gartner® Magic Quadrant™ for CRM Customer Engagement Center
The past year has presented enormous changes in both our personal and work lives. But one thing that hasn't changed is our desire for personalized service experiences and quick resolutions when we have issues. Service, which is often the face of a brand, plays a key...
FBI Releases Indicators of Compromise Associated with Ranzy Locker Ransomware
The Federal Bureau of Investigation (FBI) has released a Flash report detailing indicators of compromise (IOCs) associated with attacks using Ranzy Locker, a ransomware variant first identified targeting victims in the United States in late 2020.CISA encourages users...
Your guide to Dynamics 365 at Microsoft Ignite 2021
Microsoft Ignite kicks off in just a few days. This year's digital experience brings together a global community of technology professionals to learn where Business Applications technology is heading, and the tools and resources available to help you solve the...
FTC puts over 1,100 businesses on notice about deceptive money-making claims
Companies offering work, training, business opportunities, investments, or other money-making opportunities often try to grab your attention by talking about how much money you can make. But all too often, the potential earnings they describe are exaggerated or even...




Recent Comments