Have you been affected by a data breach? Read on
This article was originally posted by the FTC. See the original article here.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article was originally posted by the FTC. See the original article here.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
This article is contributed. See the original author and article here.
CISA, the Federal Bureau of Investigation (FBI), and the Department of Health and Human Services (HHS) have released a joint Cybersecurity Advisory (CSA), #StopRansomware: Daixin Team to provide information on the “Daixin Team,” a cybercrime group actively targeting U.S. businesses, predominantly in the Healthcare and Public Health (HPH) Sector, with ransomware and data extortion operations. This joint CSA provides Daixin actors’ tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) obtained from FBI threat response activities and third-party reporting.
CISA encourages HPH Sector organizations to review #StopRansomware: Daixin Team and to apply the recommended Mitigations. See StopRansomware.gov for additional guidance on ransomware protection, detection, and response.
This article is contributed. See the original author and article here.
Cisco has released a security update to address vulnerabilities affecting Cisco Identity Services Engine (ISE). A remote attacker could exploit some of these vulnerabilities to take control of an affected system. For updates addressing high and low severity vulnerabilities, see the Cisco Security Advisories page.
CISA encourages users and administrators to review Cisco Advisory cisco-sa-ise-path-trav-Dz5dpzyM and apply the necessary updates.
This article is contributed. See the original author and article here.
Actions to take today to mitigate cyber threats from ransomware:
• Install updates for operating systems, software, and firmware as soon as they are released.
• Require phishing-resistant MFA for as many services as possible.
• Train users to recognize and report phishing attempts.
Note: This joint Cybersecurity Advisory (CSA) is part of an ongoing #StopRansomware effort to publish advisories for network defenders that detail various ransomware variants and ransomware threat actors. These #StopRansomware advisories include recently and historically observed tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) to help organizations protect against ransomware. Visit stopransomware.gov to see all #StopRansomware advisories and to learn more about other ransomware threats and no-cost resources.
The Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Security Agency (CISA), and Department of Health and Human Services (HHS) are releasing this joint CSA to provide information on the “Daixin Team,” a cybercrime group that is actively targeting U.S. businesses, predominantly in the Healthcare and Public Health (HPH) Sector, with ransomware and data extortion operations.
This joint CSA provides TTPs and IOCs of Daixin actors obtained from FBI threat response activities and third-party reporting.
Download the PDF version of this report: pdf, 591 KB
Note: This advisory uses the MITRE ATT&CK® for Enterprise framework, version 11. See MITRE ATT&CK for Enterprise for all referenced tactics and techniques.
Cybercrime actors routinely target HPH Sector organizations with ransomware:
The Daixin Team is a ransomware and data extortion group that has targeted the HPH Sector with ransomware and data extortion operations since at least June 2022. Since then, Daixin Team cybercrime actors have caused ransomware incidents at multiple HPH Sector organizations where they have:
Daixin actors gain initial access to victims through virtual private network (VPN) servers. In one confirmed compromise, the actors likely exploited an unpatched vulnerability in the organization’s VPN server [T1190]. In another confirmed compromise, the actors used previously compromised credentials to access a legacy VPN server [T1078] that did not have multifactor authentication (MFA) enabled. The actors are believed to have acquired the VPN credentials through the use of a phishing email with a malicious attachment [T1598.002].
After obtaining access to the victim’s VPN server, Daixin actors move laterally via Secure Shell (SSH) [T1563.001] and Remote Desktop Protocol (RDP) [T1563.002]. Daixin actors have sought to gain privileged account access through credential dumping [T1003] and pass the hash [T1550.002]. The actors have leveraged privileged accounts to gain access to VMware vCenter Server and reset account passwords [T1098] for ESXi servers in the environment. The actors have then used SSH to connect to accessible ESXi servers and deploy ransomware [T1486] on those servers.
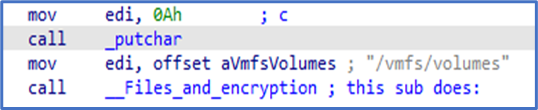
According to third-party reporting, the Daixin Team’s ransomware is based on leaked Babuk Locker source code. This third-party reporting as well as FBI analysis show that the ransomware targets ESXi servers and encrypts files located in /vmfs/volumes/ with the following extensions: .vmdk, .vmem, .vswp, .vmsd, .vmx, and .vmsn. A ransom note is also written to /vmfs/volumes/. See Figure 1 for targeted file system path and Figure 2 for targeted file extensions list. Figure 3 and Figure 4 include examples of ransom notes. Note that in the Figure 3 ransom note, Daixin actors misspell “Daixin” as “Daxin.”
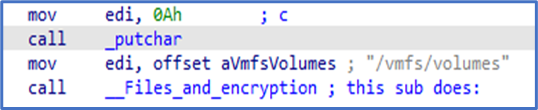
Figure 1: Daixin Team – Ransomware Targeted File Path
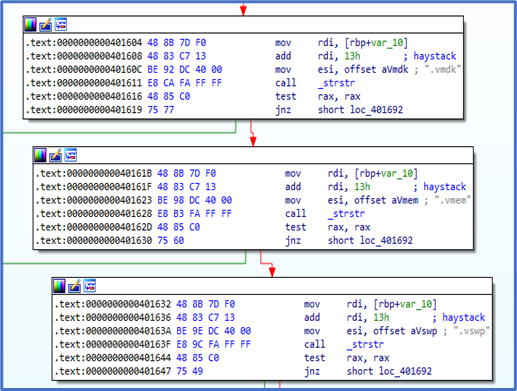
Figure 2: Daixin Team – Ransomware Targeted File Extensions
Figure 3: Example 1 of Daixin Team Ransomware Note
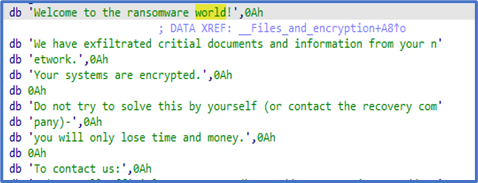
Figure 4: Example 2 of Daixin Team Ransomware Note
In addition to deploying ransomware, Daixin actors have exfiltrated data [TA0010] from victim systems. In one confirmed compromise, the actors used Rclone—an open-source program to manage files on cloud storage—to exfiltrate data to a dedicated virtual private server (VPS). In another compromise, the actors used Ngrok—a reverse proxy tool for proxying an internal service out onto an Ngrok domain—for data exfiltration [T1567].
See Table 1 for all referenced threat actor tactics and techniques included in this advisory.
Table 1: Daixin Actors’ ATT&CK Techniques for Enterprise
|
Reconnaissance |
||
|
Technique Title |
ID |
Use |
|
Phishing for Information: Spearphishing Attachment |
Daixin actors have acquired the VPN credentials (later used for initial access) by a phishing email with a malicious attachment. |
|
|
Initial Access |
||
|
Technique Title |
ID |
Use |
|
Exploit Public-Facing Application |
Daixin actors exploited an unpatched vulnerability in a VPN server to gain initial access to a network. |
|
|
Valid Accounts |
Daixin actors use previously compromised credentials to access servers on the target network. |
|
|
Persistence |
||
|
Technique Title |
ID |
Use |
|
Account Manipulation |
Daixin actors have leveraged privileged accounts to reset account passwords for VMware ESXi servers in the compromised environment. |
|
|
Credential Access |
||
|
Technique Title |
ID |
Use |
|
OS Credential Dumping |
Daixin actors have sought to gain privileged account access through credential dumping. |
|
|
Lateral Movement |
||
|
Technique Title |
ID |
Use |
|
Remote Service Session Hijacking: SSH Hijacking |
Daixin actors use SSH and RDP to move laterally across a network. |
|
|
Remote Service Session Hijacking: RDP Hijacking |
Daixin actors use RDP to move laterally across a network. |
|
|
Use Alternate Authentication Material: Pass the Hash |
Daixin actors have sought to gain privileged account access through pass the hash. |
|
|
Exfiltration |
||
|
Technique Title |
ID |
Use |
|
Exfiltration Over Web Service |
Daixin Team members have used Ngrok for data exfiltration over web servers. |
|
|
Impact |
||
|
Technique Title |
ID |
Use |
|
Data Encrypted for Impact |
Daixin actors have encrypted data on target systems or on large numbers of systems in a network to interrupt availability to system and network resources. |
|
See Table 2 for IOCs obtained from third-party reporting.
Table 2: Daixin Team IOCs – Rclone Associated SHA256 Hashes
|
File |
SHA256 |
|
rclone-v1.59.2-windows-amd64git-log.txt |
9E42E07073E03BDEA4CD978D9E7B44A9574972818593306BE1F3DCFDEE722238 |
|
rclone-v1.59.2-windows-amd64rclone.1 |
19ED36F063221E161D740651E6578D50E0D3CACEE89D27A6EBED4AB4272585BD |
|
rclone-v1.59.2-windows-amd64rclone.exe |
54E3B5A2521A84741DC15810E6FED9D739EB8083CB1FE097CB98B345AF24E939 |
|
rclone-v1.59.2-windows-amd64README.html |
EC16E2DE3A55772F5DFAC8BF8F5A365600FAD40A244A574CBAB987515AA40CBF |
|
rclone-v1.59.2-windows-amd64README.txt |
475D6E80CF4EF70926A65DF5551F59E35B71A0E92F0FE4DD28559A9DEBA60C28 |
FBI, CISA, and HHS urge HPH Sector organizations to implement the following to protect against Daixin and related malicious activity:
If a ransomware incident occurs at your organization:
Note: FBI, CISA, and HHS strongly discourage paying ransoms as doing so does not guarantee files and records will be recovered. Furthermore, payment may also embolden adversaries to target additional organizations, encourage other criminal actors to engage in the distribution of ransomware, and/or fund illicit activities.
The FBI is seeking any information that can be shared, to include boundary logs showing communication to and from foreign IP addresses, a sample ransom note, communications with Daixin Group actors, Bitcoin wallet information, decryptor files, and/or a benign sample of an encrypted file. Regardless of whether you or your organization have decided to pay the ransom, the FBI, CISA, and HHS urge you to promptly report ransomware incidents to a local FBI Field Office, or CISA at cisa.gov/report.
FBI, CISA, and HHS would like to thank CrowdStrike and the Health Information Sharing and Analysis Center (Health-ISAC) for their contributions to this CSA.
The information in this report is being provided “as is” for informational purposes only. FBI, CISA, and HHS do not endorse any commercial product or service, including any subjects of analysis. Any reference to specific commercial products, processes, or services by service mark, trademark, manufacturer, or otherwise, does not constitute or imply endorsement, recommendation, or favoring by FBI, CISA, or HHS.
Initial Publication: October 21, 2022
This product is provided subject to this Notification and this Privacy & Use policy.
This article is contributed. See the original author and article here.
CISA has added two vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. These types of vulnerabilities are a frequent attack vector for malicious cyber actors and pose significant risk to the federal enterprise. Note: to view the newly added vulnerabilities in the catalog, click on the arrow in the “Date Added to Catalog” column, which will sort by descending dates.
Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the Known Exploited Vulnerabilities Catalog as a living list of known CVEs that carry significant risk to the federal enterprise. BOD 22-01 requires FCEB agencies to remediate identified vulnerabilities by the due date to protect FCEB networks against active threats. See the BOD 22-01 Fact Sheet for more information.
Although BOD 22-01 only applies to FCEB agencies, CISA strongly urges all organizations to reduce their exposure to cyberattacks by prioritizing timely remediation of Catalog vulnerabilities as part of their vulnerability management practice. CISA will continue to add vulnerabilities to the Catalog that meet the specified criteria.
Recent Comments