by Contributed | Jun 14, 2021 | Technology
This article is contributed. See the original author and article here.
We are excited to announce the general availability of a new set of APIs for Microsoft threat and vulnerability management that allow security administrators to drive efficiencies and customize their vulnerability management program. While previous versions were dependable and feature-rich, we built the new APIs with enterprises in mind that are looking for economies of scale within their vulnerability management program and need to handle large datasets and device inventories daily. These new APIs provide the ability to design and export customized reports and dashboards, automate tasks, and allow teams to build or leverage existing integrations with third party tools.
Security teams will get detailed information as part of a full data snapshot or they can limit the dataset to only include changes since the last data download for a more focused view. Information from the following threat and vulnerability management areas is included:
- Vulnerabilities assessment – discovered vulnerabilities on devices
- Secure Configuration Assessment – detected misconfigurations on devices
- Software inventory – a full list of installed software products across devices
Now let’s look at how you can use these new APIs to boost and customize your vulnerability management program.
Create custom reports
Customized reports and dashboards enable you to pool the most meaningful data and insights about your organization’s security posture into a more focused view based on what your organization or specific teams and stakeholders need to know and care about most. Custom reports can increase the actionability of information and improve efficiencies across teams, because it reduces the workload of busy security teams and allows them to focus on the most critical vulnerabilities.
Before building custom views using tools such as PowerBI and Excel, you can enrich the native datasets provided by Microsoft’s threat and vulnerability management solution with additional data from Microsoft Defender for Endpoint or a third-party tool of your choice.
In addition, these reports/dashboards give you an easy way to report key information and trends to top management to track business KPIs and provide meaningful insights on the overall status of the vulnerability management program in your organization.
With a custom interface you can show the information that your teams need and nothing more, creating a simpler task view or list of day-to-day work items. It provides flexibility in using any of the solution’s components, such as vulnerability report, missing security updates, installed software, end-of-support products, and operating systems, and combining them with advanced filtering capabilities. This can help optimize and streamline the end user experience according to your organization’s needs.
Let’s look at examples of reports that you can create:
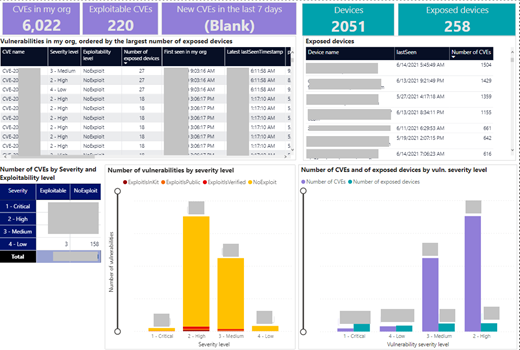
Vulnerabilities report
This report gives you a snapshot of the security posture of your organization and allows you to identify the most critical and exploitable vulnerabilities, see the most exposed devices distributed by OS, or drill down into specific CVEs. You can user filters to show when a CVE was detected for the first time, or use advanced properties such as Device tags, Device groups, Device health (activeinactive), and more.
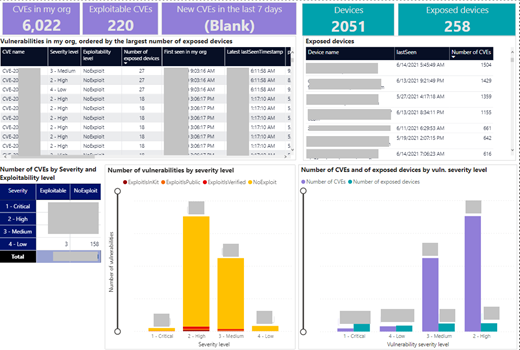 Image 1: Vulnerabilities report
Image 1: Vulnerabilities report
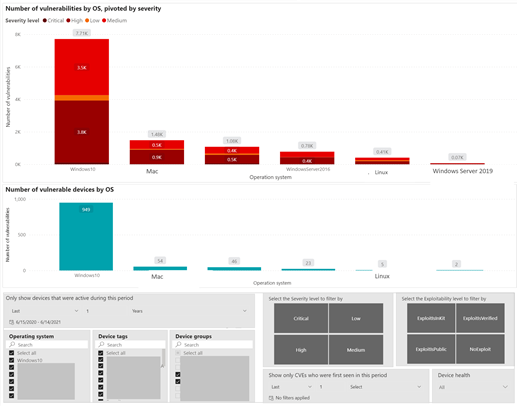 Image 2: Vulnerabilities report – severity and vulnerable devices by OS
Image 2: Vulnerabilities report – severity and vulnerable devices by OS
Missing Windows security updates
This report gives you a complete picture of all missing Windows security updates across your organization. You can see what the most exposed operating systems are, or search for a particular security update to show all affected devices.
You can filter the report by the associated CVE criticality, by age of each security update, or filter by advanced properties such as device tags, device groups, device health (activeinactive) and more.
 Image 3: Missing Windows security updates
Image 3: Missing Windows security updates
Software inventory
This report gives an overview of your software inventory. In addition to the org-level view, you can explore recent installations and on which devices, when, and in what version they were installed.
You can filter the report by number of the weaknesses associated with each software, by software namevendor, or filter by advanced properties such as Device tags, Device groups, Device health (activeinactive) and more.
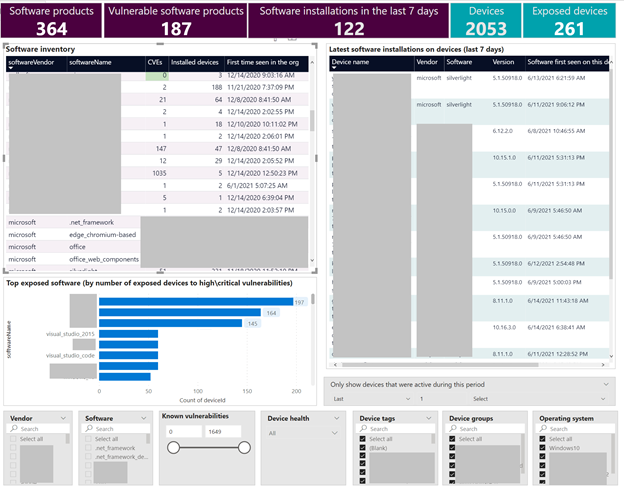 Image 4: Software inventory report
Image 4: Software inventory report
You can create your own reports, use any of the templates we have shown above, or check out more report templates in our GitHub library:
- End-of-support operating systems
- End-of-support software and versions
- Misconfigurations per device
- Software vulnerability recommendations
- Non-windows security updates
- Exposure score visualizations
Have you created your own report or used these published templates? We would love to see how you’re using these new capabilities!
Other resources:
Build OData queries with Microsoft Defender for Endpoint
Create custom reports using Microsoft Defender ATP APIs and Power BI
Automation and integrations
A big part of a successful vulnerability management (VM) program is the ability to automate tasks and reduce the manual workload of security and IT teams, as well as integrating the VM solution with existing tools that are part of an established workflow process in your organization.
Our new threat and vulnerability management APIs enable you to build a data exchange between natively provided data and your existing tools. At the same time, we are working with partners to continuously expand the portfolio of out-of-the-box integrations with third party solutions. You can already leverage our Skybox integration today and we are in the process of releasing additional integrations for ServiceNow VR and Kenna Security and in the coming weeks.
The Kenna Security partnership will strengthen the overall prioritization capabilities, combining threat and vulnerability management data with real-world threat and exploit intelligence and advanced data science to determine which vulnerabilities pose the highest risk to your organization. To learn more about the upcoming integration join our webinar on 6/24.
By integrating with ServiceNow Vulnerability Response you will be able to easily automate and track workflows. We will share more information soon!
While we will have more news on integrations and automation in the coming months, if there are specific integrations you would like to see on our roadmap, go to the Partner Application page in the Microsoft Defender Security Center, and click Recommend other partners.
More information and feedback
The threat and vulnerability management capabilities are part of Microsoft Defender for Endpoint and enable organizations to effectively identify, assess, and remediate endpoint weaknesses to reduce organizational risk.
Check out our documentation for a complete overview of how you can consume these new APIs.
We want to hear from you! If you have any suggestions, questions, or comments, please visit us on our Tech Community page.
by Contributed | Jun 14, 2021 | Technology
This article is contributed. See the original author and article here.
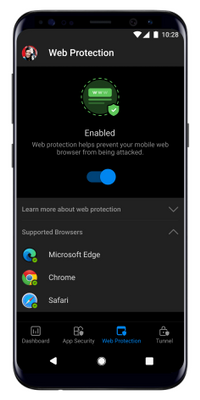
Today we are excited to announce new Microsoft Defender for Endpoint capabilities that are generally available for Android and iOS that provide additional breach protection, reduce risk in your organization, simplify the end user experience, and offer secure access to on-prem resources.
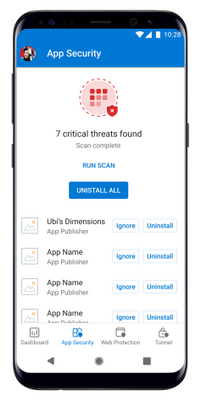
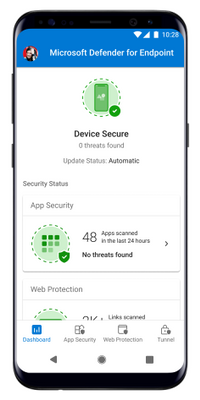
First, customers will notice an updated look to the Microsoft Defender for Endpoint mobile app. The new experience helps end users better understand the capabilities the app provides and enables the user to be more aware of the security threats to their device. Microsoft’s mobile threat defense solution will continue to offer:
- Protection against phishing coming from browsing, email, apps, and messaging platforms
- Scans for malware and potentially unwanted apps (on Android)
- Blocking of unsafe connections as well as access to sensitive data (on Android)
- A unified security experience for SecOps in Microsoft 365 Defender
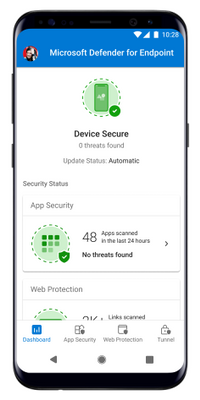
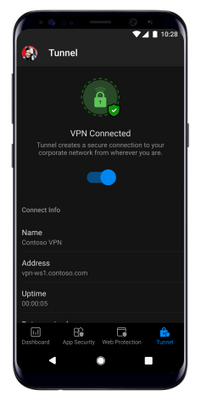
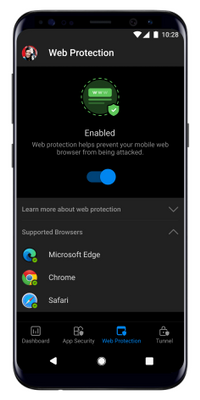
Figure 1: Microsoft Defender for Endpoint updated mobile app screens in light and dark mode.
Mobile application management support for non-Intune enrolled devices
We are pleased to announce the general availability of Microsoft Defender for Endpoint support for mobile application management (MAM) on Android and iOS. Prior to this update, Microsoft Defender for Endpoint worked on devices that were enrolled using Intune mobile device management (MDM) only.
With this update Microsoft Defender for Endpoint can protect an organization’s data within a managed application for those who aren’t using an MDM but are using Intune to manage mobile applications. It also extends support to customers who use other enterprise mobility management solutions such as AirWatch, MobileIron, MaaS360, and others, while still using Intune for mobile application management.
Microsoft Defender for Endpoint will continue to evaluate the device risk score based on threats identified on the device and will share that score with app protection policies. These polices provide an additional layer of breach protection by blocking access or selectively wiping a user’s corporate data.
For setup and configuration details read the blog post.
Jailbreak detection available for iOS
Jailbreaking an iOS device elevates root access that is granted to the user of the device. Once this happens, users can easily sideload potentially malicious applications and the iPhone won’t get critical, automatic iOS updates that may fix security vulnerabilities. These kinds of devices introduce additional risk and a higher probability of a breach to your organization. We are excited to share the general availability of the jailbreak detection capability in Microsoft Defender for Endpoint on iOS. This adds to the phishing protection that already exists.
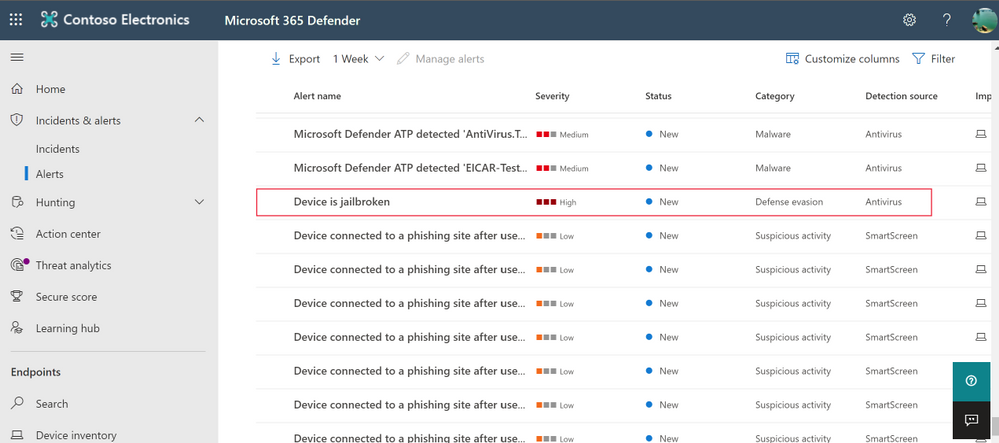
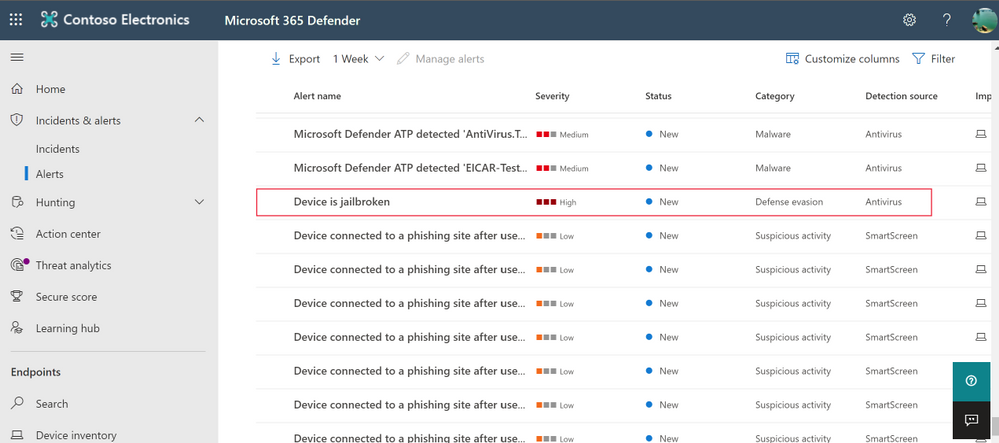
Figure 2: Jailbreak alert in Microsoft 365 Defender
With this change, Microsoft Defender for Endpoint on iOS will detect both unmanaged and managed devices that are jailbroken. If it’s detected that a device is jail broken, an alert is surfaced to the security team in Microsoft 365 Defender. The device will then be considered as a high risk device and this risk score is shared with your app protection or device compliance policies so that you can block it from accessing corporate resources.
For more details, please refer to the documentation here.
Simplified onboarding for iOS users
As a part of our commitment to continuously improve the experience for end users, we are now also simplifying end user onboarding. Until now, end users needed to provide VPN permissions to allow the iOS app to provide anti-phishing protection. With this update, admins will be able to setup configuration and push the VPN profile to enrolled devices so that VPN related permissions will not have to be provided by end users, thus simplifying their onboarding experience.
For more information, please refer to the documentation here.
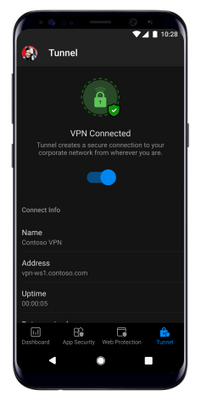
Microsoft Tunnel VPN integration
Finally, we’re excited to share the general availability of Microsoft Tunnel VPN capabilities unified in the Microsoft Defender for Endpoint app for Android. This unification enables organizations to offer a simplified end user experience with one security app – offering both mobile threat defense and the ability to access on-prem resources from their mobile device, while security and IT teams are able to maintain the same admin experiences they are familiar with.
Existing customers of Microsoft Defender for Endpoint, who are also licensed for Microsoft Tunnel, will see Tunnel capabilities in the Defender for Endpoint app on Android. Existing Tunnel customers will switch to using the Microsoft Defender for Endpoint app for VPN. They will not see any other changes to Tunnel features, it will simply now appear within the Defender for Endpoint app. IT administrators will be able to continue to use the Microsoft Endpoint Manager admin center to configure both Defender and Tunnel features. For additional details, read the blog announcing these changes.
We’re excited to share these new updates with you and continue to build on security capabilities across platforms. We look forward to hearing your feedback!
Microsoft Defender for Endpoint is an industry-leading, cloud-powered endpoint security solution offering vulnerability management, endpoint protection, endpoint detection and response, and mobile threat defense in a single unified platform. With our solution, threats are no match. If you are not yet taking advantage of Microsoft’s unrivaled threat optics and proven capabilities, sign up for a free trial of Microsoft Defender for Endpoint today.
by Contributed | Jun 14, 2021 | Technology
This article is contributed. See the original author and article here.
We’re pleased to announce the Microsoft Tunnel Gateway is now generally available!
Also, as announced at Ignite, we’ve been working on combining the Microsoft Defender for Endpoint and Microsoft Tunnel apps into a single unified Microsoft Defender for Endpoint client. We’re excited to announce that this new version of Microsoft Defender for Endpoint is available today for Android for all our customers and is no longer in preview.
Beyond what was mentioned in our Ignite announcement, there are some things you should know:
- If you’re using app configuration policy to configure settings for the Microsoft Defender for Endpoint app for Android Enterprise and are also using Tunnel today, in order to avoid conflict issues on personally-owned devices with work profiles, you’ll need to:
- Include the Microsoft Defender for Endpoint settings as custom settings in the Microsoft Tunnel VPN profile.
- Remove the app configuration policy.
Conflicting policies prevent the app from connecting to Microsoft Tunnel. These steps and settings are documented here.
- In order to deploy the new version of Microsoft Defender for Endpoint in Microsoft Intune, you’ll need to sync your apps in the managed Google Play store.
- If you’re previewing the Microsoft Defender for Endpoint app today, you’ll have the option to stay on the preview track and get the latest builds, or to move to the production track. To move to the production track, you’ll need to:
- Find your assignments for the Microsoft Defender for Endpoint app in the Microsoft Endpoint Manager admin center.
- For each assignment, click the list under Tracks and clear all checks in the list.
- Click OK, then Review + save, then Save.
While today we’re announcing that Microsoft Tunnel Gateway is generally available and are also releasing Microsoft Tunnel functionality in Microsoft Defender for Endpoint for Android, the Microsoft Tunnel client for iOS will remain in public preview for the time being.
The existing Microsoft Tunnel standalone client app for Android will be removed from the store after August 16, 2021, so if you’re previewing Tunnel today, be sure to move your users to the new Microsoft Defender for Endpoint client ahead of this date.
For more information, see:
by Contributed | Jun 14, 2021 | Technology
This article is contributed. See the original author and article here.
If you love Outlook or any of the Office apps, then you would look great in the front of any of these!
Download one or download all!

by Contributed | Jun 14, 2021 | Technology
This article is contributed. See the original author and article here.
This series highlights Microsoft Learn Student Ambassadors who achieved the Gold milestone and have recently graduated from university. Each blog features a different student and highlights their accomplishments, their experience with the Student Ambassadors community, and what they’re up to now.
Today we’d like to introduce Riya Mistry, who is from India and recently graduated from the Dharmsinh Desai Institute of Technology.

Responses have been edited for clarity and length.
When you became a Student Ambassador in 2019 in your third year of college, did you have any specific goals you wanted to reach, like attain a skill or work on a particular quality? What were they, and did being a Student Ambassador help you achieve them? How has being in the community impacted you in general?
Since the idea of global tech communities was not well known in my local college communities, my main goal was to first get familiar with the learning, growth, and opportunities provided by the Student Ambassadors community and then help to expand the reach of it to my college and people around me. The main technology that I was passionate about initially was cloud computing, and joining this community helped me greatly in terms of learning about Azure. I now even have the certification in it, so I was able to achieve that goal. Also, in general, being a member of this community helped me gain more confidence to speak up in public, which I had feared the most.
What were some of the accomplishments that you’re proudest of and why?
There are many accomplishments, but the one I am most proud about was the day when it was announced that I had reached the Gold milestone [editor’s note: this is the highest level one can attain as a Student Ambassador]. After joining this community and then getting to know about the different milestones, I never thought I would be able to reach the Gold one. Apparently, my hard work and passion for the community caught the attention of the program’s Community Program Managers, who recommended that I be promoted to the status of Gold Ambassador.
The second accomplishment is the event which I hosted, “Introduction to Apache Spark”. It was approximately a 1.5hr event and had the highest number of attendees out of events organized in my institution, even in the lockdown; attendees showed keen interest in learning until the very end. It felt like a huge accomplishment that I had helped people to get familiar with something new.
What do you have planned after graduation? What’s next for you?
I have joined as a Software Engineer Intern at Crest Data Systems, a leading provider of custom solutions in the areas of data analytics, cybersecurity, ITOps/AIOps, DevOps, and cloud. I help them with security analytics and automation projects to detect real-time threats using cloud technology. In my free time, I do a little bit of coding and give back to the community by conducting sessions and helping others new in the Student Ambassadors program to get familiar with what is required.
If you could redo your time in the Student Ambassador community, is there anything you would have done differently?
I am mostly satisfied with the time and opportunities I had being in the program, so I don’t think I would redo anything, although I do feel if something can be changed, I might have joined the community a little bit earlier, in my 2nd year of college.
If you were to describe the community to a student who is considering joining, what would you say to convince them to join?
If you love to be around a community of like-minded people, if you love new technology and like to explore each and every new thing you hear, then this is the best place you can join. Come be a part of the most diverse community where you will learn communication, management, marketing–and don’t forget–technical skills. It’s the best experience someone could wish for as a student.
And what advice would you give to new Student Ambassadors?
My advice to new Student Ambassadors is to keep learning new things, talk to folks, ask questions if you have any. There are plenty of people here to help you out in the community. And most importantly, be active in the program, as opportunities are innumerable each and every day. Organize your first event, take part in Hackathons, and contribute to your best to give back to the community.
Do you have a motto in life, a guiding principle that drives you?
My motto for life is “Every expert was once a beginner”. That helps me learn and explore new things without having the fear of failure.
Lastly, on a lighter note, can you share a random fun fact about yourself that few people are aware of?
Apart from technology, I enjoy cooking and trying different cuisines and creating my own version of it. Also anything is delicious when cheese is added to it! Bit of a cheese lover.
Thank you, Riya, and good luck to you in all your future endeavors!
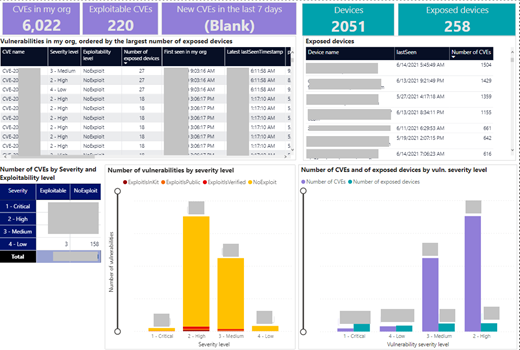
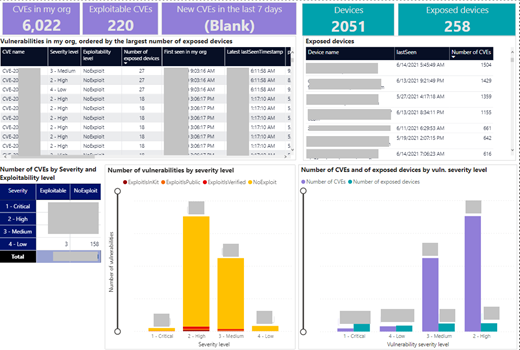 Image 1: Vulnerabilities report
Image 1: Vulnerabilities report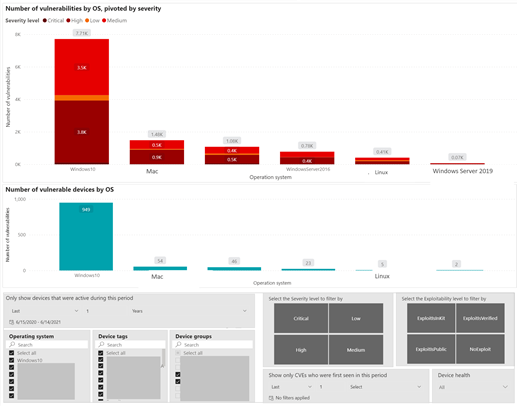 Image 2: Vulnerabilities report – severity and vulnerable devices by OS
Image 2: Vulnerabilities report – severity and vulnerable devices by OS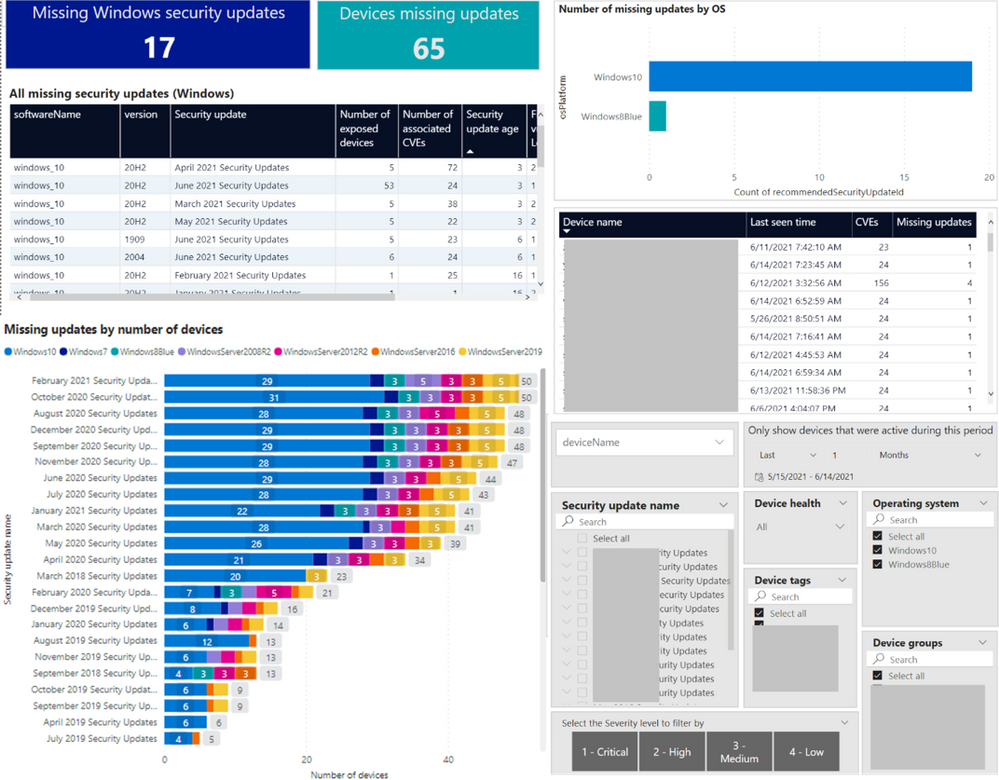 Image 3: Missing Windows security updates
Image 3: Missing Windows security updates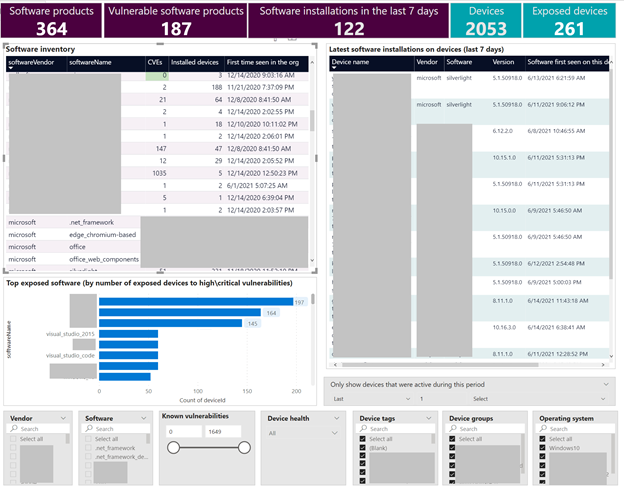 Image 4: Software inventory report
Image 4: Software inventory report


Recent Comments