Our Latest News
Using Service Principal with AzCopy & Azure CLI to manage blobs in Storage Account
In this blog we will look at using service principals with AzCopy and Azure CLI to connect to storage accounts and manage blob data. An Azure service principal is an identity created for use with applications, hosted services, and automated tools to access Azure...
API Management Policy for Access Token Acquisition, Caching and Renewal
Co-authors (alphabetical order): Dan Balma, Maarten Van De Bospoort, Vishnu Naga Praveen Deepthimahanthi, Nick Drouin, Kreig DuBose, David Giard, Michael Green, Binay Kumar, Hao Luo, Shubhaangi Mahajan, Andres Robinet, Jatin Sharma, Taru Sinha, David Triana, Jeremy...
Microsoft 365 user management versus Azure Active Directory
If your organization is using Microsoft 365, you already have Azure Active Directory. It's the identity platform that provides the authentication of your users' credentials when they sign and and the authorization to your Microsoft 365 SaaS applications. If you...
Lesson Learned #166: How to reduce the time inserting 10 millions of rows
Today, we had a very interesting service request that our customer requested to improve the process for inserting 10 millions of rows. In this type of situation, we need to think about the the time spent in networking roundtrips. In order to explain this...
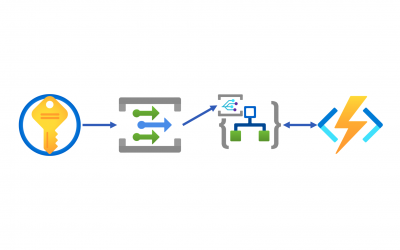
Event-Driven KeyVault Secrets Rotation Management
In my previous post, I discussed how all secrets in Azure Key Vault could automatically manage their versions to get disabled. While that approach was surely useful, it sometimes seems overkilling to iterate against all secrets at once. What if you can manage only a...
How to start a new SPFx web part project with Microsoft Graph Toolkit and React
How to start a new SPFx web part project with Microsoft Graph Toolkit and React ContextMicrosoft Graph Toolkit is a set of reusable components working with Microsoft Graph to accelerate your web developments with SharePoint Online, Microsoft Teams and more. With...
Whats new: Azure Sentinel and Microsoft 365 Defender incident integration
Harness the breadth and depth of integrated SIEM and XDR with new Microsoft 365 integration Building on our promise for a modernized approach to threat protection with integrated SIEM and XDR, we are happy to...
Advanced hunting: updates to threat and vulnerability management tables
We are happy to announce that Threat and Vulnerability Management (TVM) tables in advanced hunting are being updated with an improved structure and additional data – now available in public preview. The existing...
Improved support for Delta Lake added to data flows in ADF and Synapse
New options added to data flow sinks available in both Azure Data Factory and Azure Synapse Analytics will make writing data to ADLS Gen2 using Delta Lake much more efficient. Data flows will now natively support Delta auto compact and optimized write options in your...
Avoid Unnecessary Looping (Apply to each) in Power Automate
In this blog post I will show you how to avoid creating unnecessary apply to each loops in Power Automate which can slow down your flow and make it harder to read. Use CaseOften you want to retrieve just one item in a SharePoint list and then display the value of...
Microsoft IOC Detection Tool for Exchange Server Vulnerabilities
Official websites use .govA .gov website belongs to an official government organization in the United States. Secure .gov websites use HTTPS A lock () or https:// means you've safely connected to the .gov website. Share sensitive information only on official, secure...
Microsoft Releases Alternative Mitigations for Exchange Server Vulnerabilities
Official websites use .govA .gov website belongs to an official government organization in the United States. Secure .gov websites use HTTPS A lock () or https:// means you've safely connected to the .gov website. Share sensitive information only on official, secure...


Recent Comments